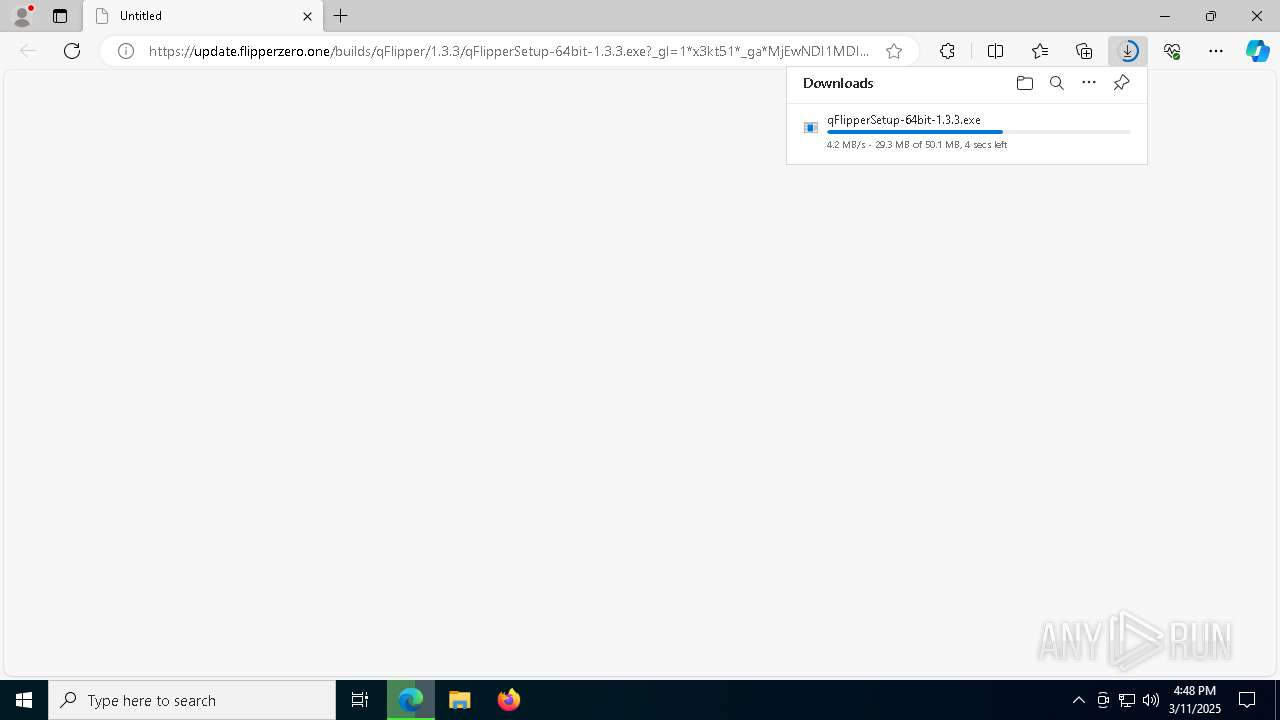
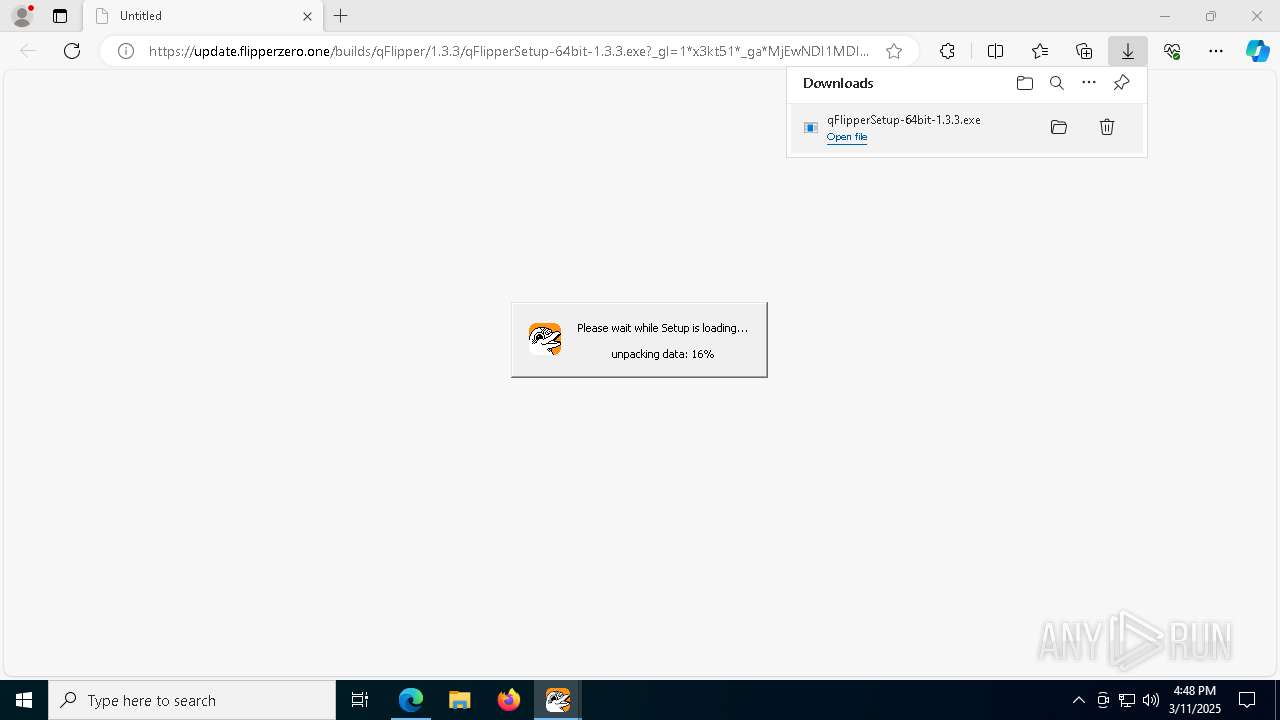
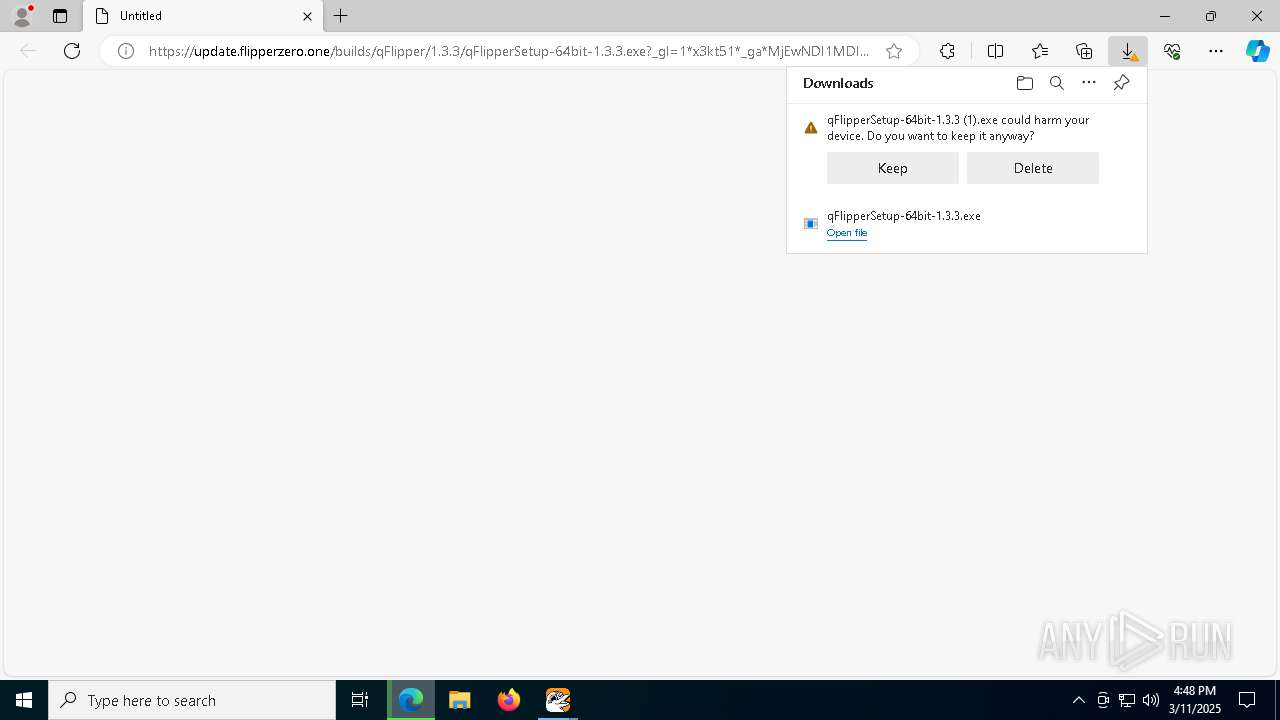
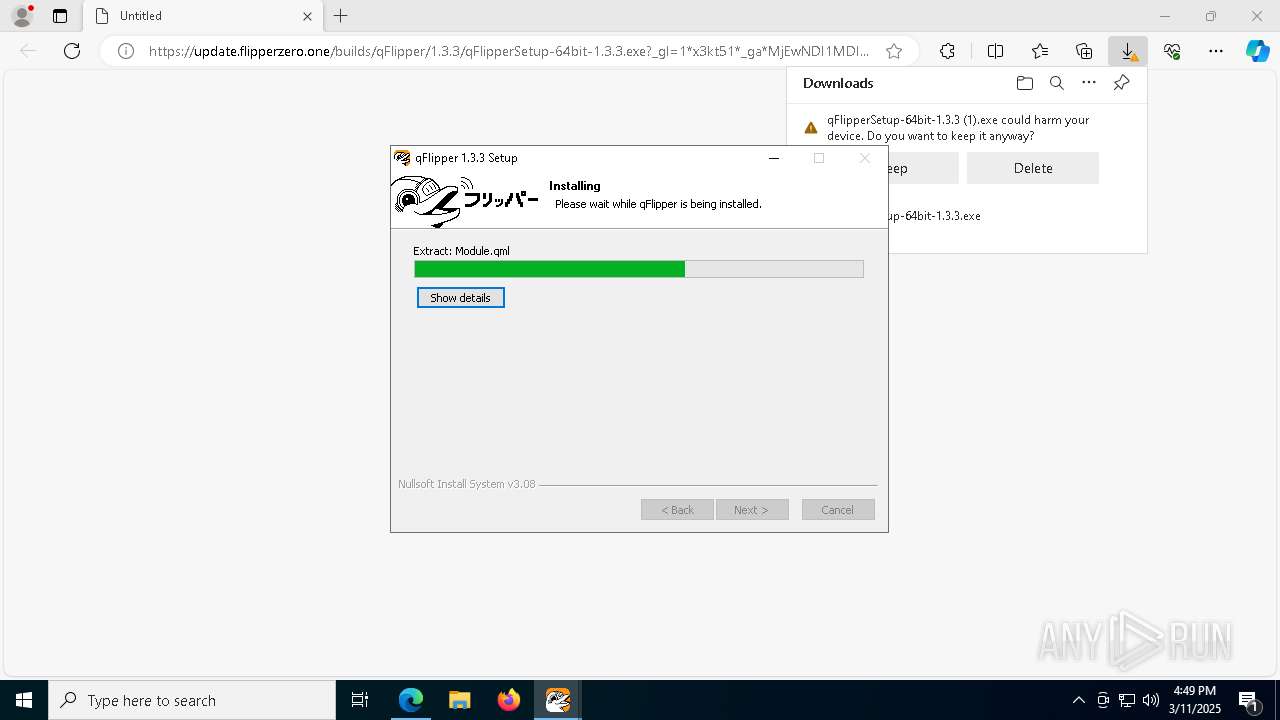
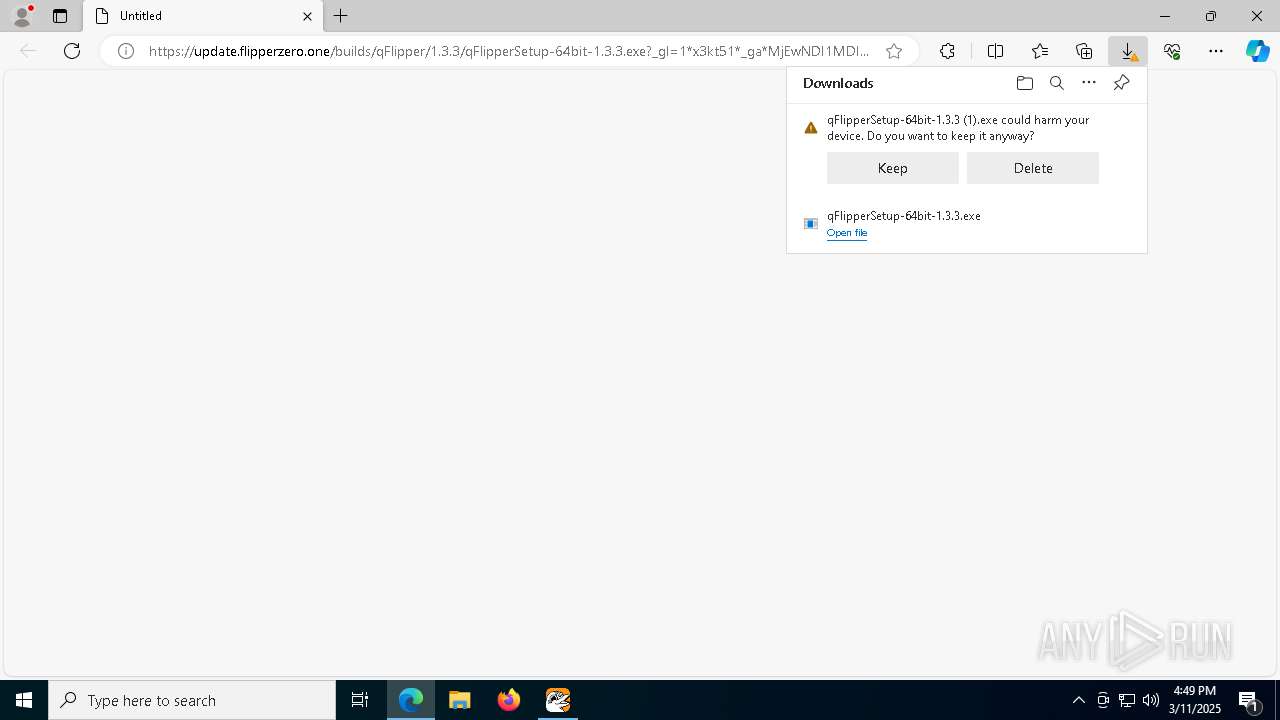
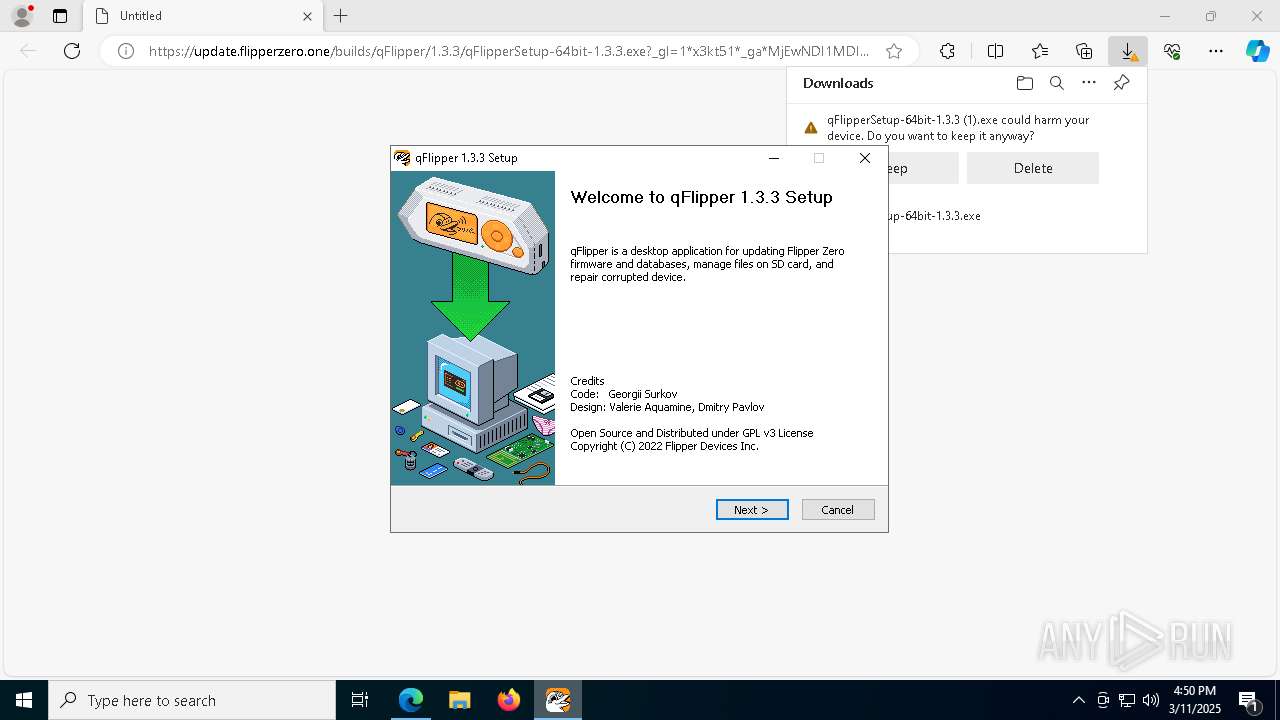
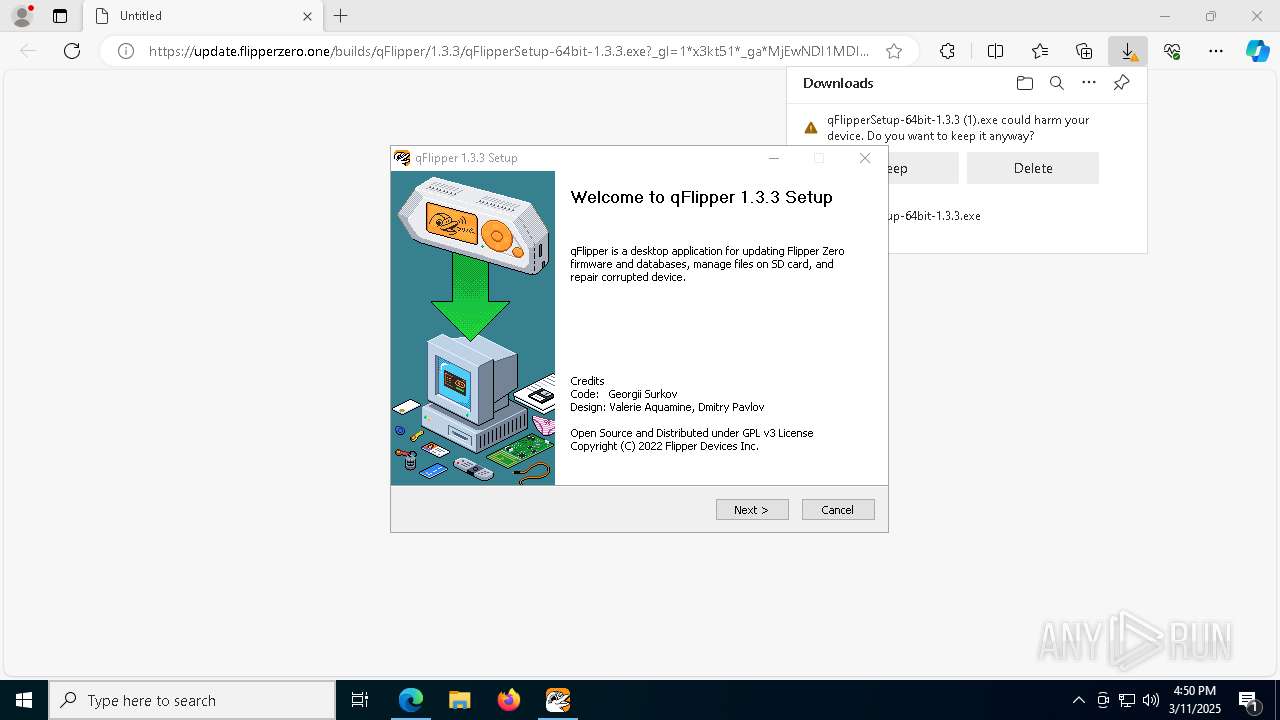
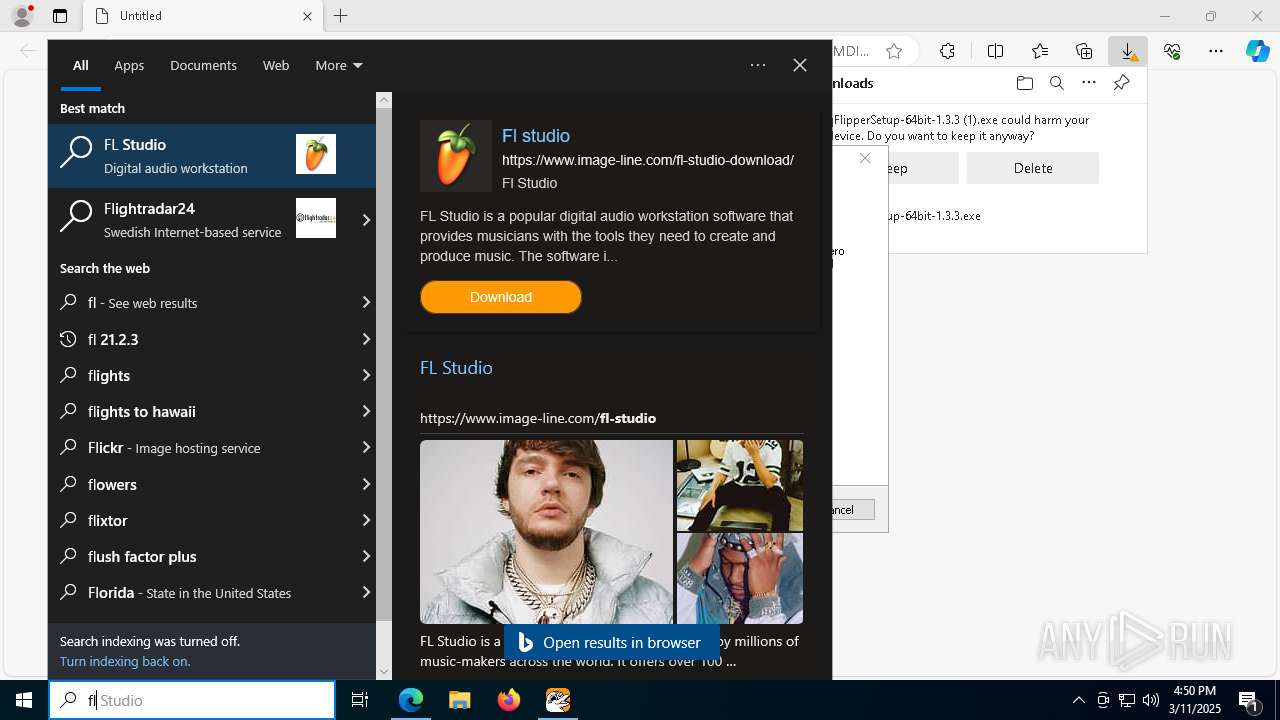
| URL: | https://update.flipperzero.one/builds/qFlipper/1.3.3/qFlipperSetup-64bit-1.3.3.exe?_gl=1*x3kt51*_ga*MjEwNDI1MDI4NC4xNzQxNzExNTky*_ga_GM78S6JK0K*MTc0MTcxMTU5Mi4xLjAuMTc0MTcxMTYyOC4yNC4wLjA. |
| Full analysis: | https://app.any.run/tasks/c7645796-5f83-4e52-8b92-1f745de7f829 |
| Verdict: | Malicious activity |
| Analysis date: | March 11, 2025, 16:47:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 0561D6D1E2C472628DAEEE037DF94172 |
| SHA1: | 2286166DB550B9E00B87E72AD6BA059CD0E8690D |
| SHA256: | 4FF9E3A677BAACD9FF87E98ABD46AC385E7838EE01FEFADC8C1AA86CEC5A9575 |
| SSDEEP: | 3:N8vRASVi+0ggXKSWLWXRQIw2YUPj0SgSrlNmxigrhPU0T6GVnqhiAqi6n:2vnZ0gSzW0RdSMAS7fmLPfT6GVnq/qi6 |
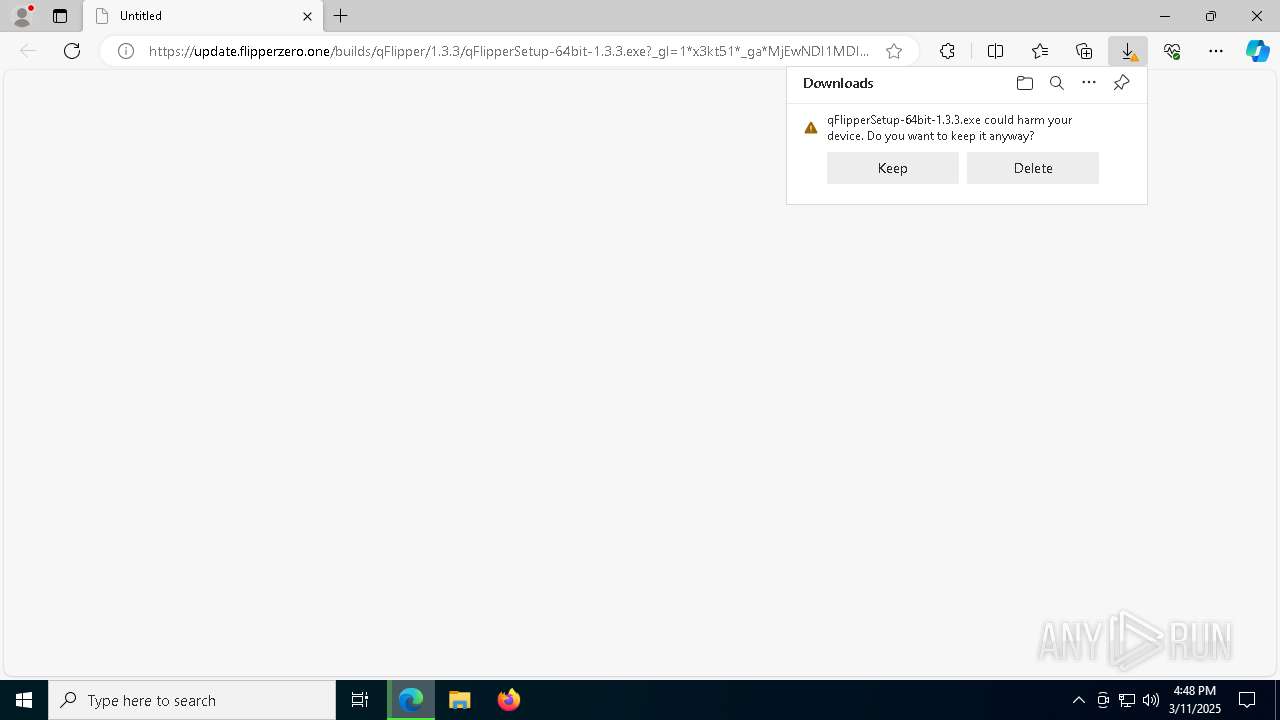
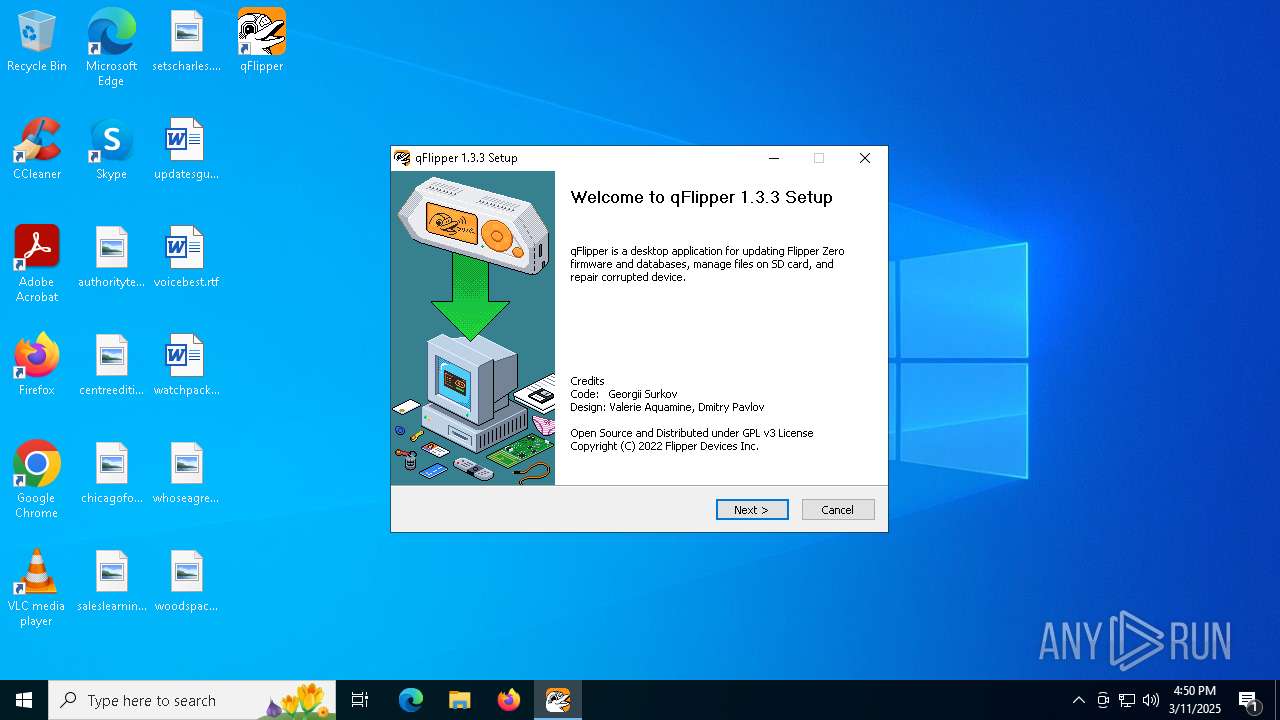
MALICIOUS
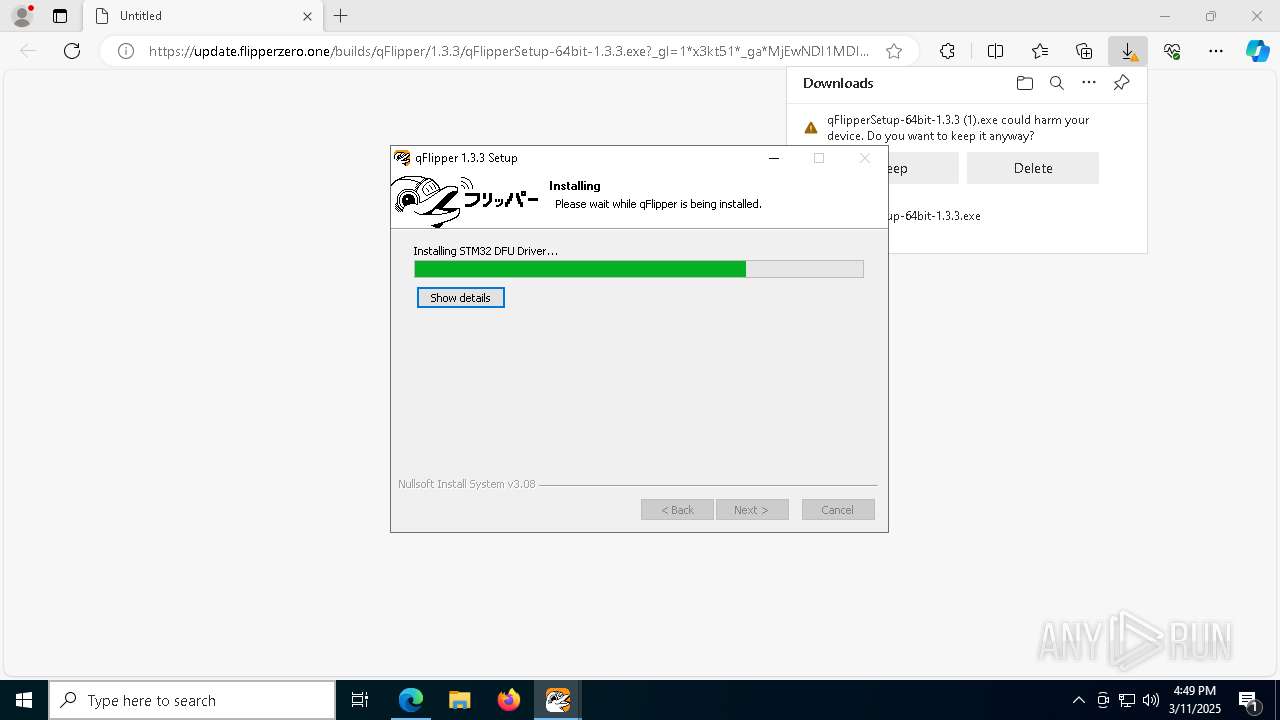
Executing a file with an untrusted certificate
- qFlipperSetup-64bit-1.3.3.exe (PID: 4448)
- qFlipperSetup-64bit-1.3.3.exe (PID: 5008)
- qFlipperSetup-64bit-1.3.3.exe (PID: 2140)
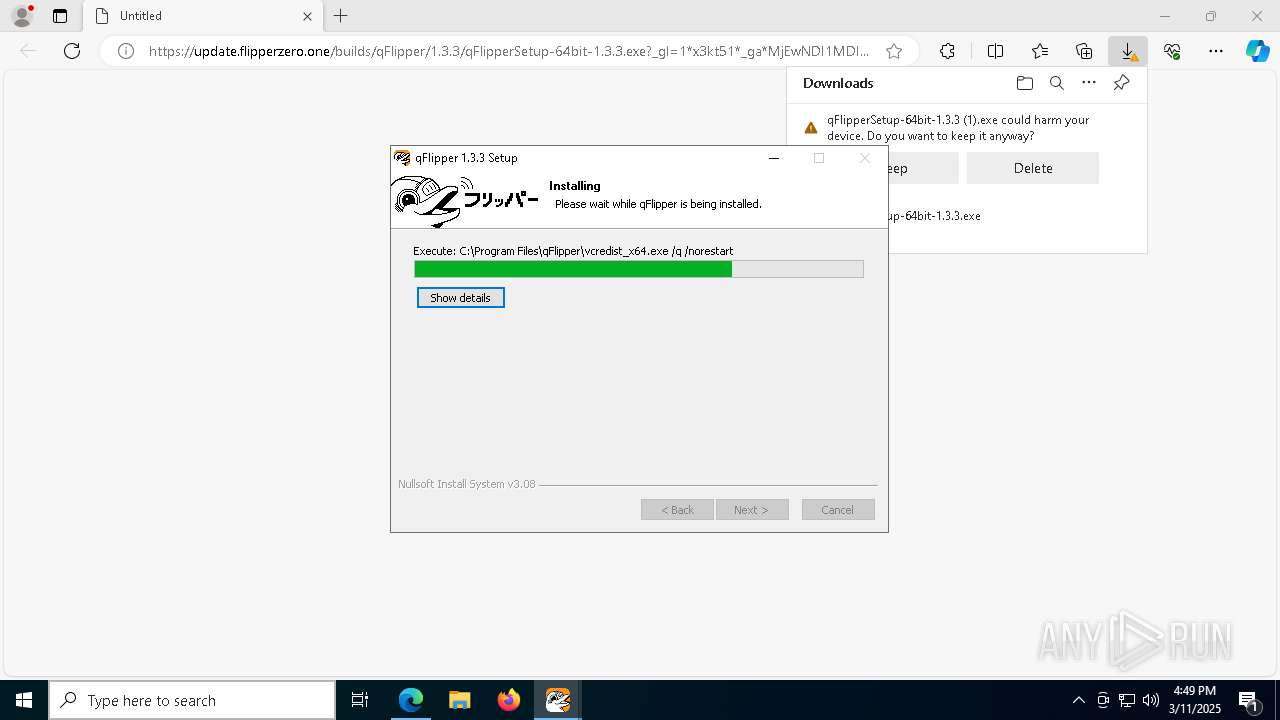
- vcredist_x64.exe (PID: 8056)
- qFlipperSetup-64bit-1.3.3.exe (PID: 3140)
- Setup.exe (PID: 7732)
- qFlipper.exe (PID: 7248)
- qFlipper.exe (PID: 7296)
SUSPICIOUS
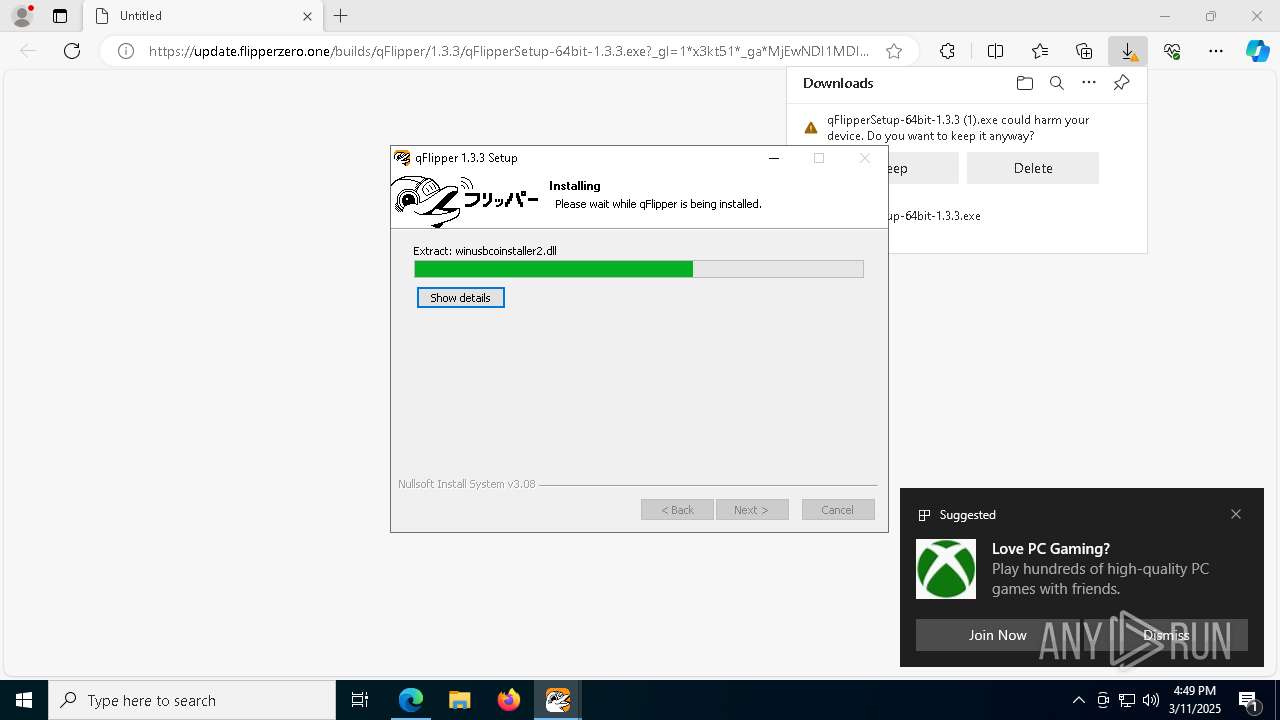
Executable content was dropped or overwritten
- qFlipperSetup-64bit-1.3.3.exe (PID: 4448)
- qFlipperSetup-64bit-1.3.3.exe (PID: 3140)
- vcredist_x64.exe (PID: 8056)
- pnputil.exe (PID: 6228)
- drvinst.exe (PID: 7848)
The process creates files with name similar to system file names
- qFlipperSetup-64bit-1.3.3.exe (PID: 4448)
- qFlipperSetup-64bit-1.3.3.exe (PID: 3140)
Malware-specific behavior (creating "System.dll" in Temp)
- qFlipperSetup-64bit-1.3.3.exe (PID: 3140)
- qFlipperSetup-64bit-1.3.3.exe (PID: 4448)
There is functionality for taking screenshot (YARA)
- qFlipperSetup-64bit-1.3.3.exe (PID: 4448)
- qFlipperSetup-64bit-1.3.3.exe (PID: 3140)
Uses WMIC.EXE to obtain data on processes
- qFlipperSetup-64bit-1.3.3.exe (PID: 4448)
Process drops legitimate windows executable
- qFlipperSetup-64bit-1.3.3.exe (PID: 4448)
- vcredist_x64.exe (PID: 8056)
- msiexec.exe (PID: 8124)
- drvinst.exe (PID: 7848)
Creates file in the systems drive root
- vcredist_x64.exe (PID: 8056)
The process drops C-runtime libraries
- msiexec.exe (PID: 8124)
Creates files in the driver directory
- drvinst.exe (PID: 7848)
The process executes via Task Scheduler
- default-browser-agent.exe (PID: 5812)
Loads DLL from Mozilla Firefox
- default-browser-agent.exe (PID: 5812)
INFO
Reads the computer name
- identity_helper.exe (PID: 4464)
- qFlipperSetup-64bit-1.3.3.exe (PID: 4448)
- qFlipperSetup-64bit-1.3.3.exe (PID: 3140)
- ShellExperienceHost.exe (PID: 744)
- msiexec.exe (PID: 8124)
Executable content was dropped or overwritten
- msedge.exe (PID: 3956)
- msiexec.exe (PID: 8124)
- msedge.exe (PID: 6980)
Create files in a temporary directory
- qFlipperSetup-64bit-1.3.3.exe (PID: 4448)
- qFlipperSetup-64bit-1.3.3.exe (PID: 3140)
- Setup.exe (PID: 7732)
- pnputil.exe (PID: 6228)
Reads Environment values
- identity_helper.exe (PID: 4464)
Checks supported languages
- qFlipperSetup-64bit-1.3.3.exe (PID: 4448)
- qFlipperSetup-64bit-1.3.3.exe (PID: 3140)
- identity_helper.exe (PID: 4464)
- msiexec.exe (PID: 8124)
- qFlipper.exe (PID: 7248)
- qFlipper.exe (PID: 7296)
Application launched itself
- msedge.exe (PID: 3956)
- msedge.exe (PID: 4724)
- firefox.exe (PID: 5544)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 2600)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 720)
- BackgroundTransferHost.exe (PID: 4488)
- BackgroundTransferHost.exe (PID: 1812)
- BackgroundTransferHost.exe (PID: 2600)
- WMIC.exe (PID: 2552)
- BackgroundTransferHost.exe (PID: 6652)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 2600)
- msiexec.exe (PID: 8124)
- qFlipperSetup-64bit-1.3.3.exe (PID: 4448)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 2600)
Creates files in the program directory
- qFlipperSetup-64bit-1.3.3.exe (PID: 4448)
The sample compiled with english language support
- qFlipperSetup-64bit-1.3.3.exe (PID: 4448)
- vcredist_x64.exe (PID: 8056)
- msiexec.exe (PID: 8124)
- pnputil.exe (PID: 6228)
- drvinst.exe (PID: 7848)
- msedge.exe (PID: 6980)
Reads the machine GUID from the registry
- vcredist_x64.exe (PID: 8056)
- Setup.exe (PID: 7732)
- msiexec.exe (PID: 8124)
The sample compiled with japanese language support
- vcredist_x64.exe (PID: 8056)
- msiexec.exe (PID: 8124)
The sample compiled with korean language support
- vcredist_x64.exe (PID: 8056)
- msiexec.exe (PID: 8124)
The sample compiled with german language support
- vcredist_x64.exe (PID: 8056)
- msiexec.exe (PID: 8124)
The sample compiled with chinese language support
- vcredist_x64.exe (PID: 8056)
- msiexec.exe (PID: 8124)
The sample compiled with spanish language support
- vcredist_x64.exe (PID: 8056)
- msiexec.exe (PID: 8124)
The sample compiled with russian language support
- vcredist_x64.exe (PID: 8056)
- msiexec.exe (PID: 8124)
The sample compiled with Italian language support
- vcredist_x64.exe (PID: 8056)
- msiexec.exe (PID: 8124)
The sample compiled with french language support
- vcredist_x64.exe (PID: 8056)
- msiexec.exe (PID: 8124)
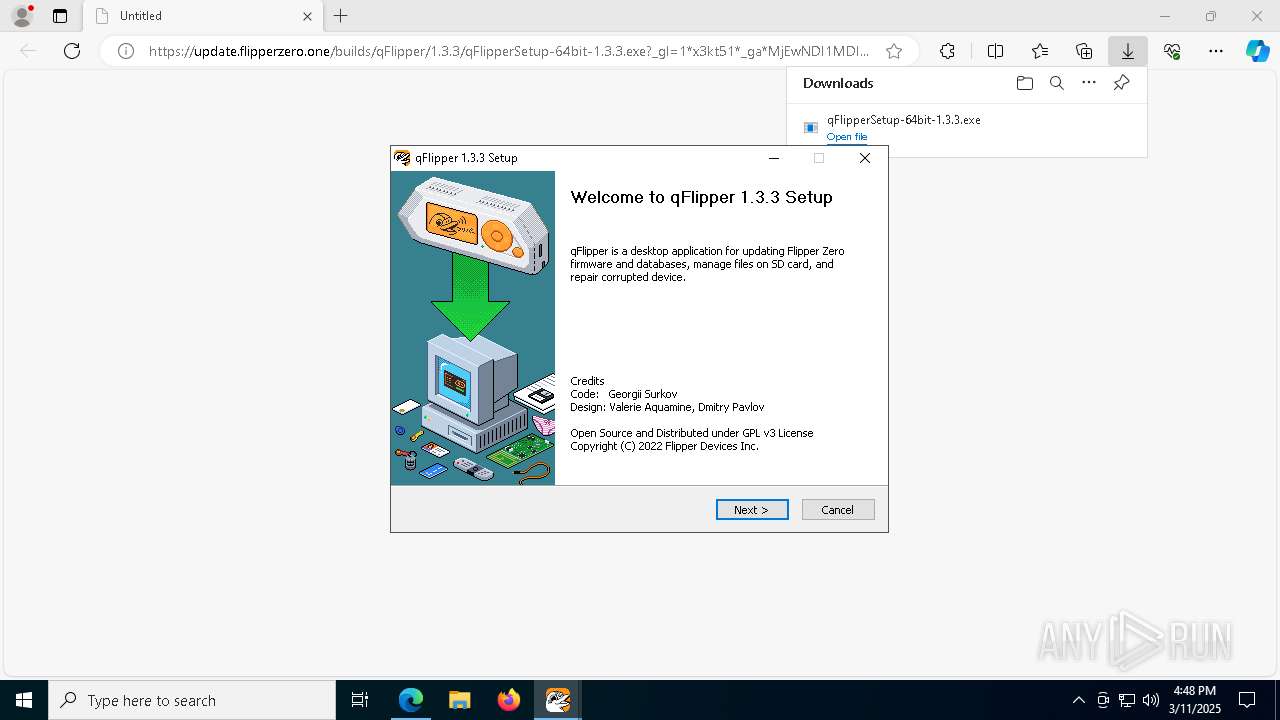
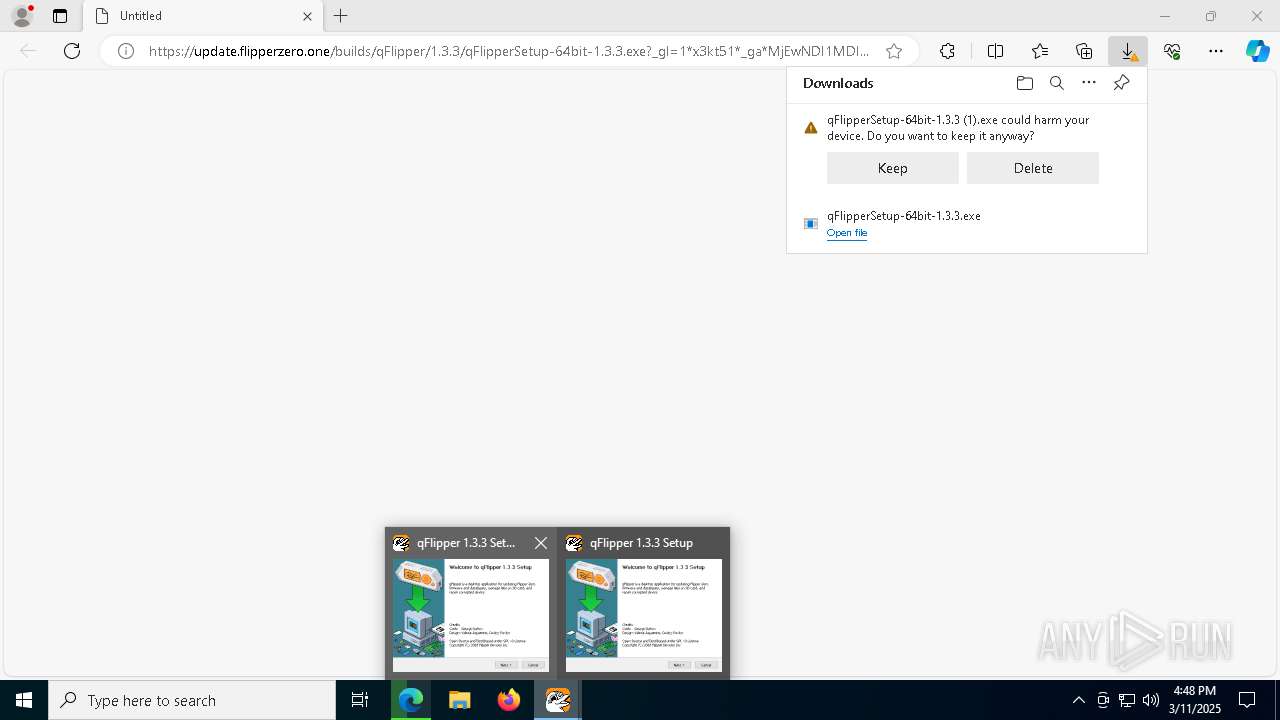
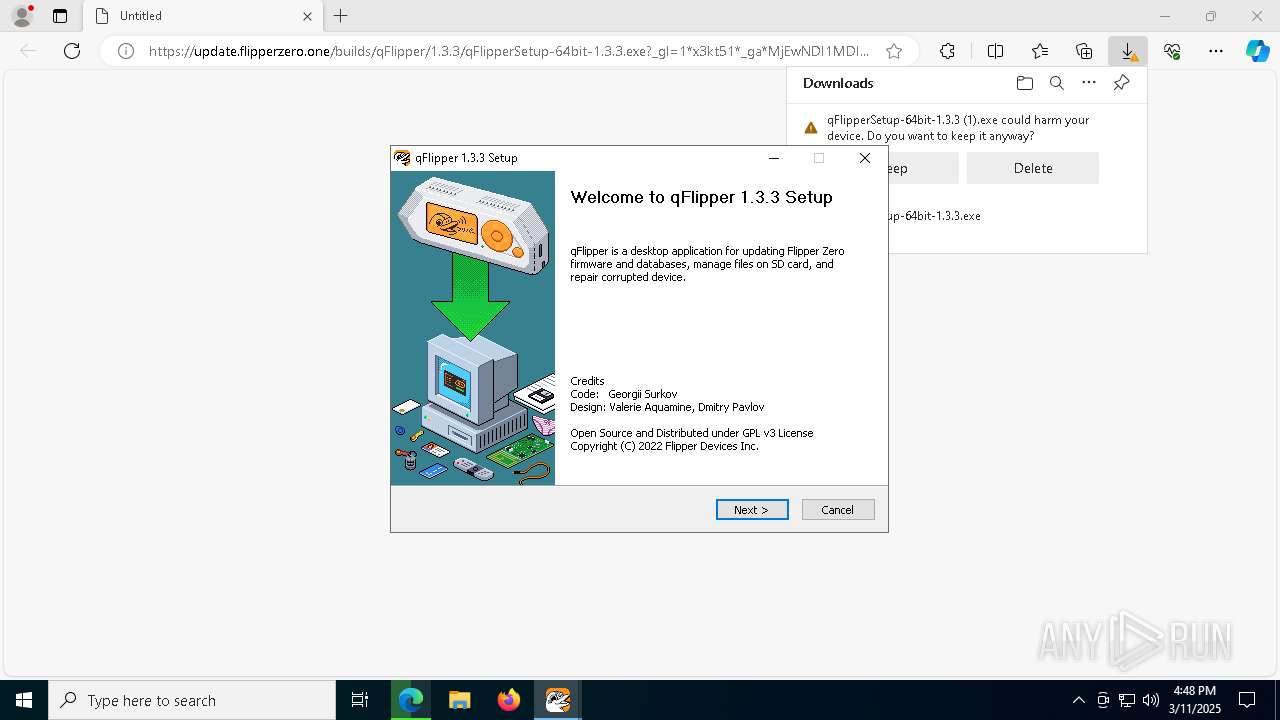
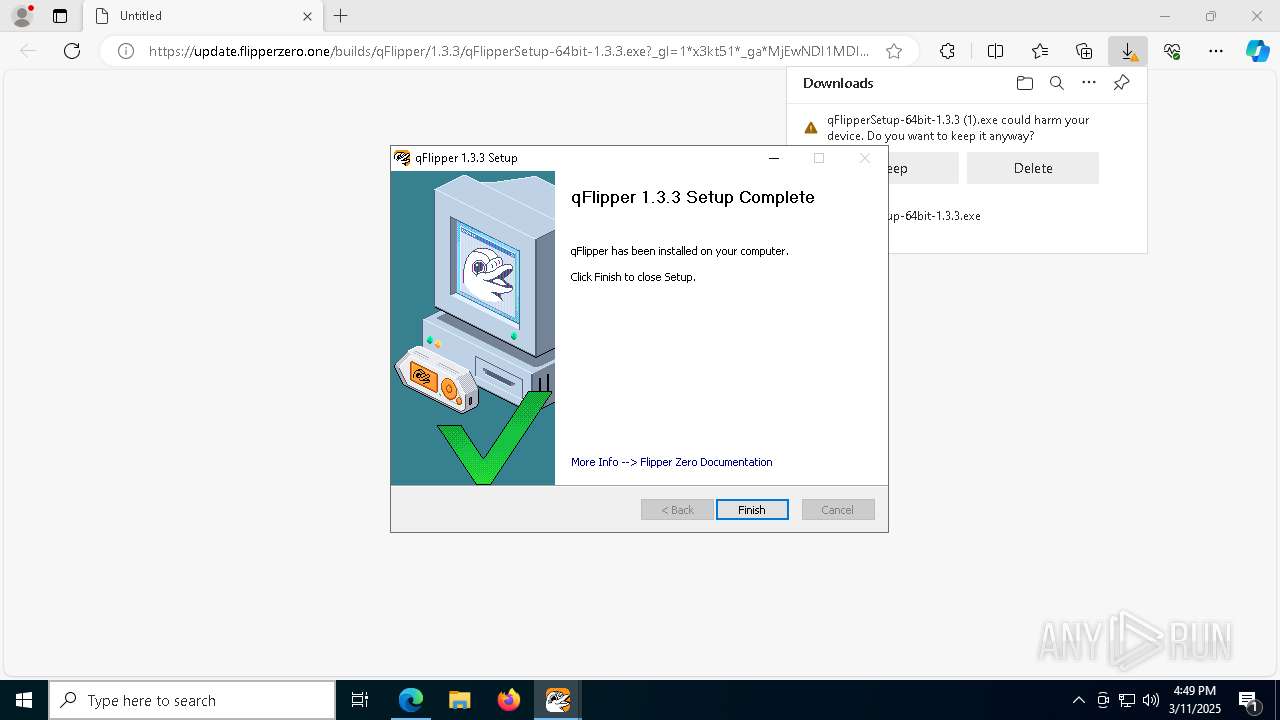
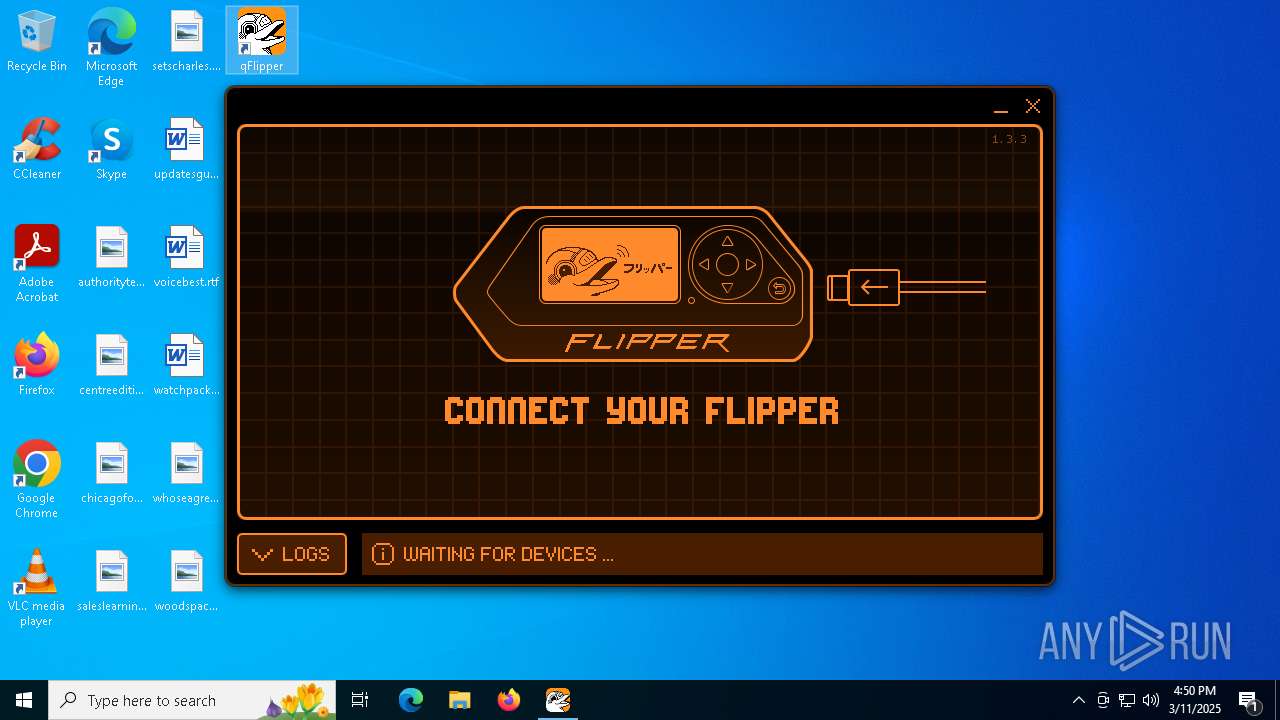
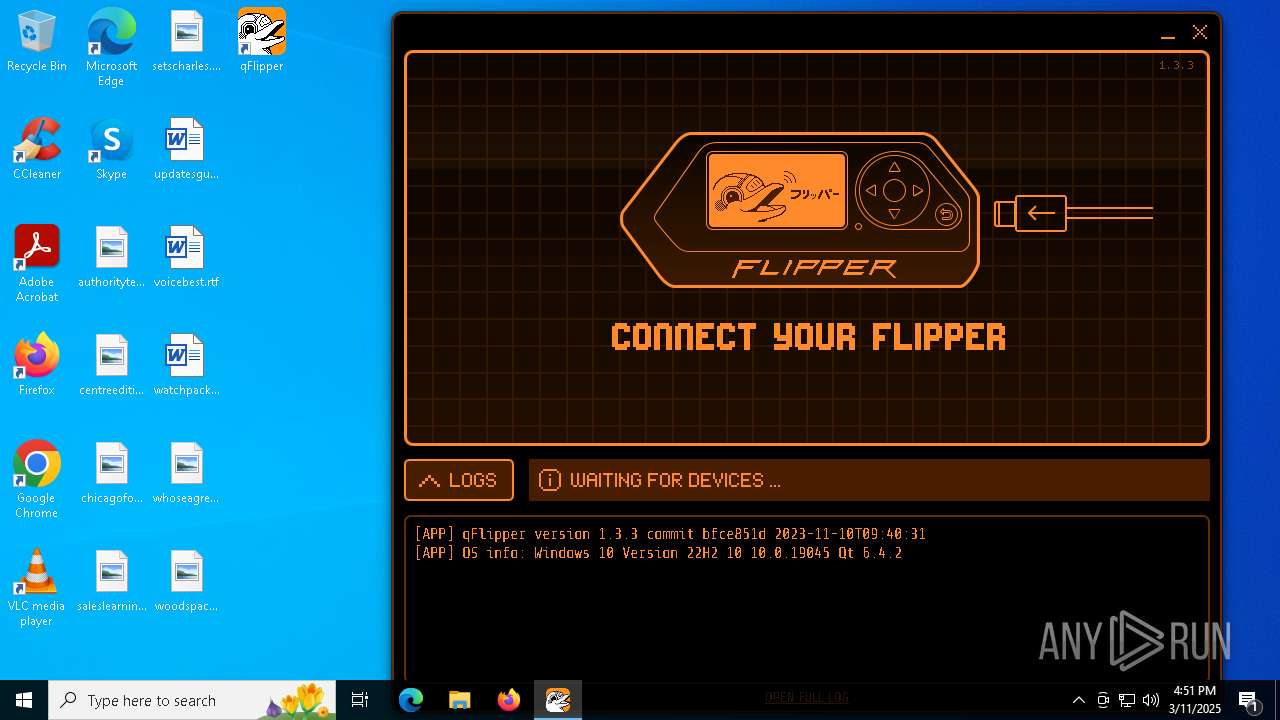
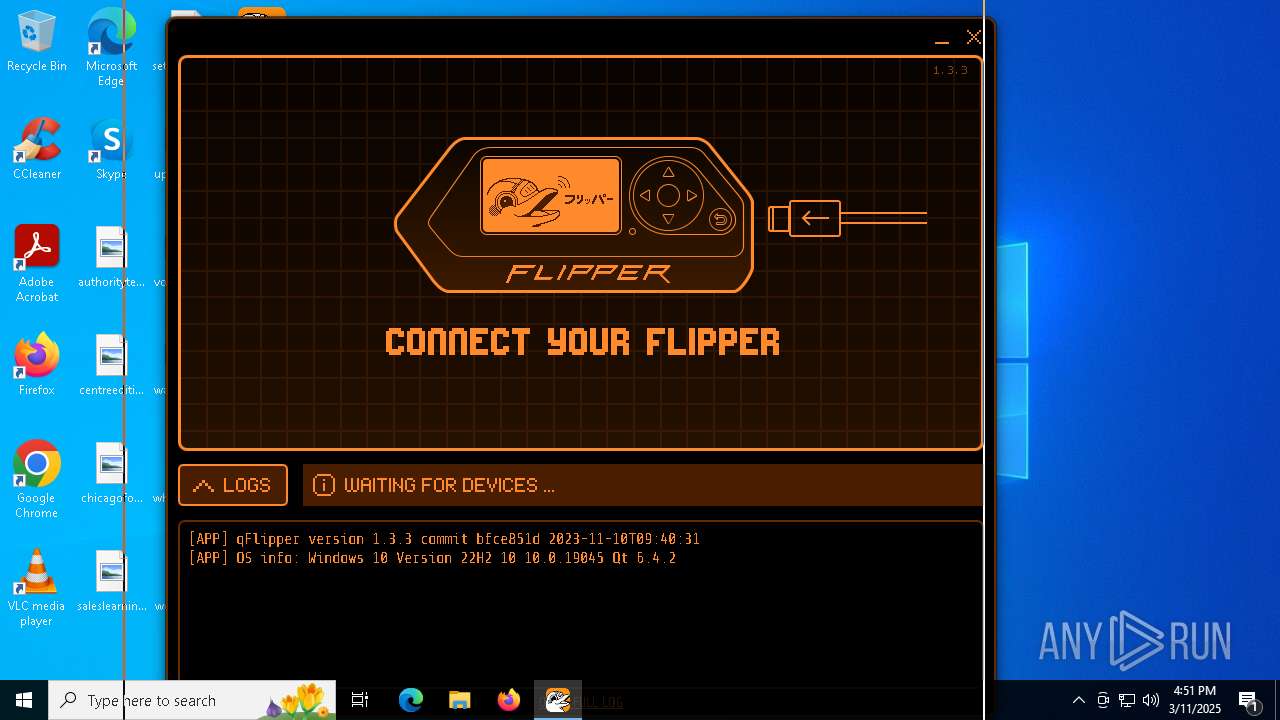
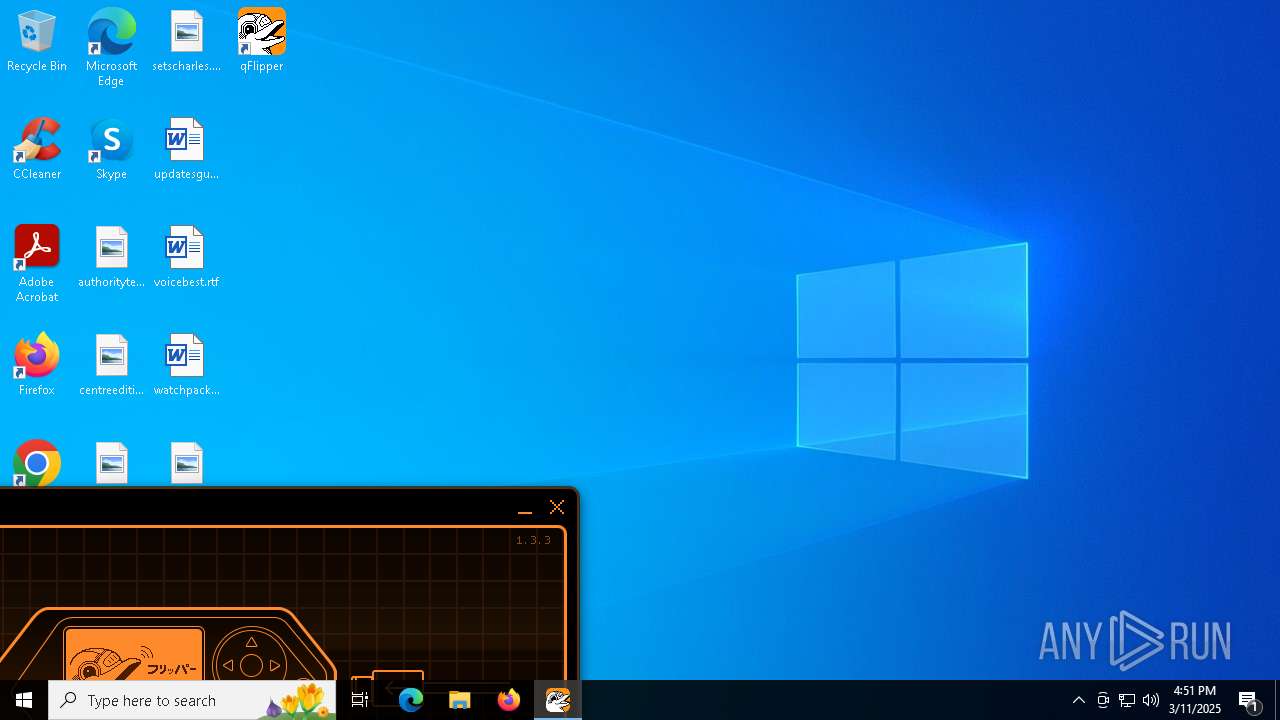
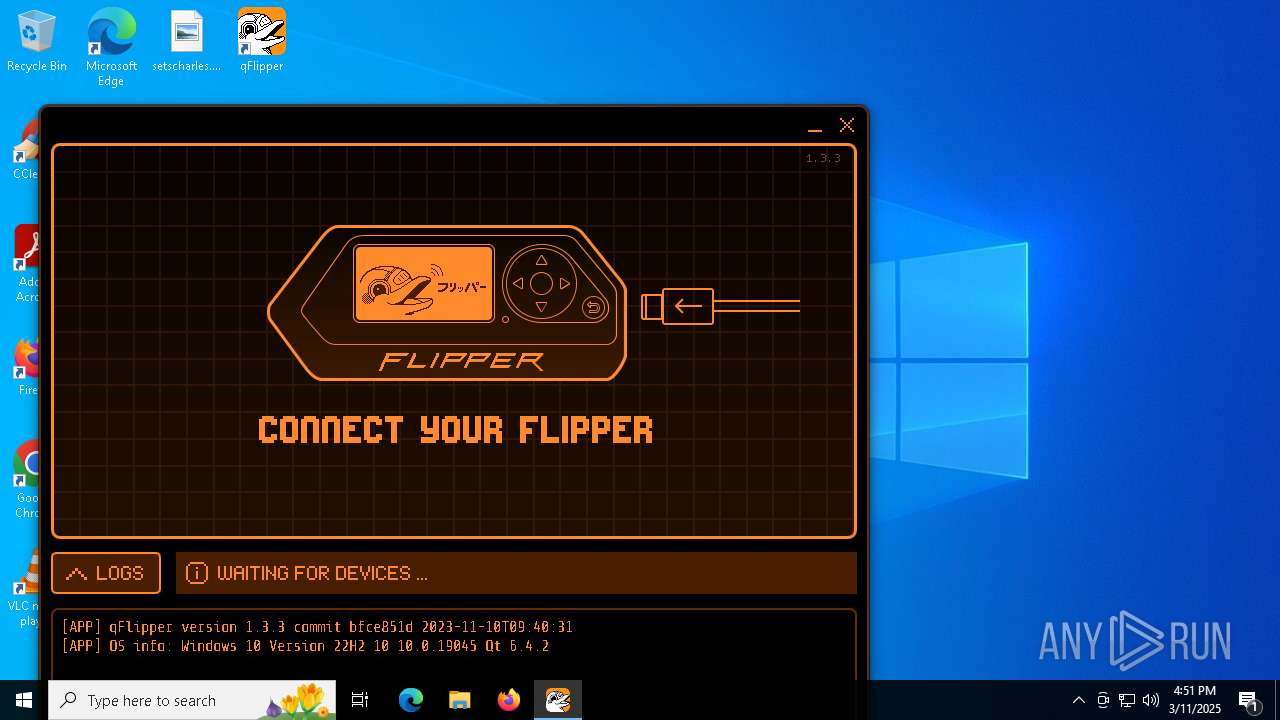
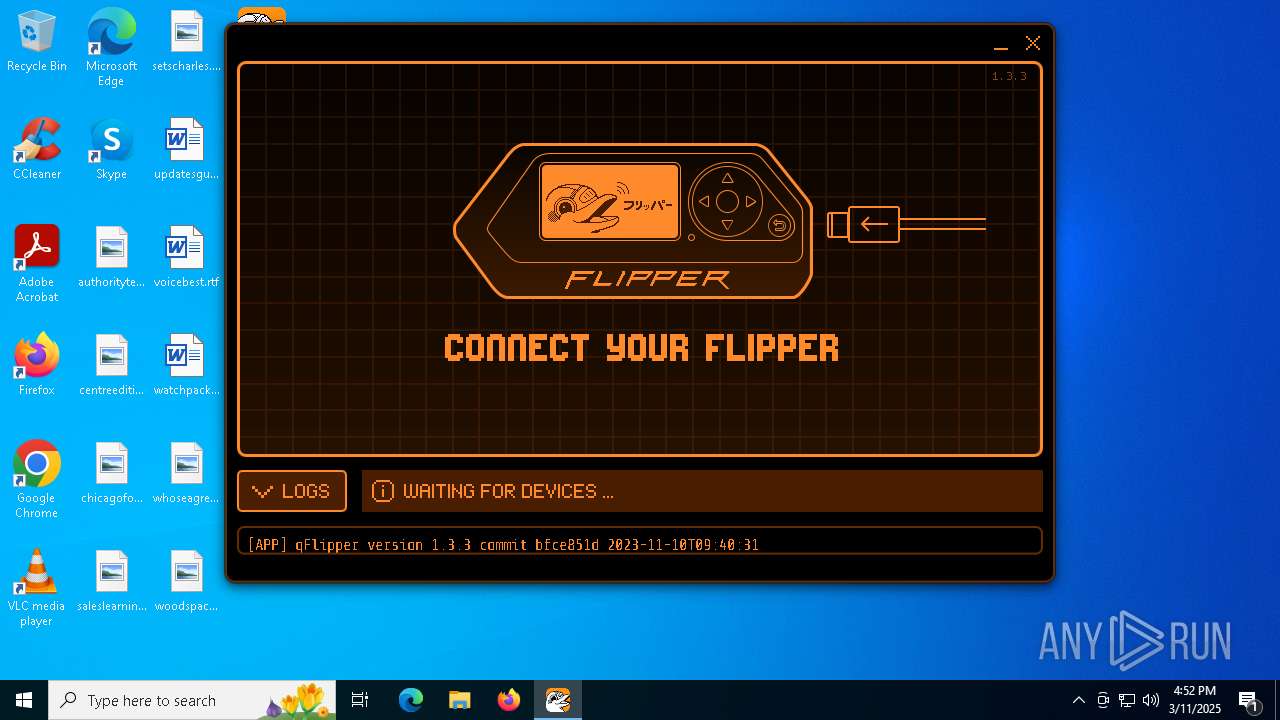
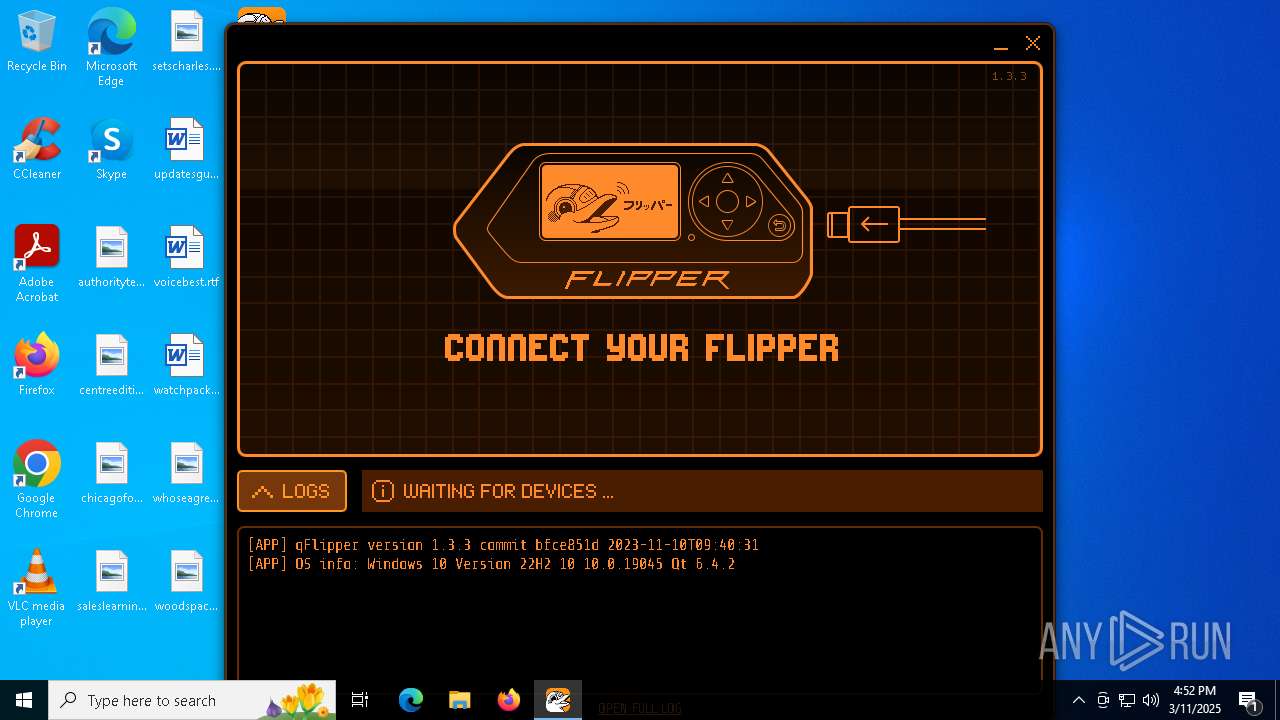
Manual execution by a user
- qFlipper.exe (PID: 7248)
- qFlipper.exe (PID: 7296)
Reads the time zone
- qFlipper.exe (PID: 7248)
- qFlipper.exe (PID: 7296)
Process checks computer location settings
- qFlipper.exe (PID: 7248)
- qFlipper.exe (PID: 7296)
Qt framework related mutex has been found
- qFlipper.exe (PID: 7296)
- qFlipper.exe (PID: 7248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
248
Monitored processes
100
Malicious processes
7
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4956 --field-trial-handle=2432,i,15992855300832106589,814247772803804661,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5436 --field-trial-handle=2400,i,13533955028828764558,14261821916882969620,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x290,0x294,0x298,0x288,0x2a4,0x7ffc886a5fd8,0x7ffc886a5fe4,0x7ffc886a5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 720 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4072 --field-trial-handle=2432,i,15992855300832106589,814247772803804661,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 744 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | pnputil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2428 --field-trial-handle=2432,i,15992855300832106589,814247772803804661,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
186 589
Read events
186 018
Write events
548
Delete events
23
Modification events
| (PID) Process: | (4844) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4844) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4844) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4844) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4844) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (4844) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (3956) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9D04F922AA8E2F00 | |||
| (PID) Process: | (3956) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0ECCB89A-F5B9-46B1-8077-32B54417D0C9} | |||
| (PID) Process: | (3956) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4B388A0A-B938-413C-89B8-EED4C3FC79DC} | |||
| (PID) Process: | (3956) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
186
Suspicious files
657
Text files
649
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ccd7.TMP | — | |
MD5:— | SHA256:— | |||
| 3956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10ccd7.TMP | — | |
MD5:— | SHA256:— | |||
| 3956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ccd7.TMP | — | |
MD5:— | SHA256:— | |||
| 3956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ccd7.TMP | — | |
MD5:— | SHA256:— | |||
| 3956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ccd7.TMP | — | |
MD5:— | SHA256:— | |||
| 3956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
90
DNS requests
84
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6184 | backgroundTaskHost.exe | GET | — | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6564 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6564 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2600 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8168 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1741788558&P2=404&P3=2&P4=gkEvjLwu2oGrlKXF2OCyMP72RO2Hzi7OsXP4obdv4TULOOGEII5rTf5hlu7PbwOhrztZHlM7AAiRenIIG8XXlw%3d%3d | unknown | — | — | whitelisted |
8168 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1741788558&P2=404&P3=2&P4=gkEvjLwu2oGrlKXF2OCyMP72RO2Hzi7OsXP4obdv4TULOOGEII5rTf5hlu7PbwOhrztZHlM7AAiRenIIG8XXlw%3d%3d | unknown | — | — | whitelisted |
8168 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1741788558&P2=404&P3=2&P4=gkEvjLwu2oGrlKXF2OCyMP72RO2Hzi7OsXP4obdv4TULOOGEII5rTf5hlu7PbwOhrztZHlM7AAiRenIIG8XXlw%3d%3d | unknown | — | — | whitelisted |
8168 | svchost.exe | HEAD | 200 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1741788558&P2=404&P3=2&P4=gkEvjLwu2oGrlKXF2OCyMP72RO2Hzi7OsXP4obdv4TULOOGEII5rTf5hlu7PbwOhrztZHlM7AAiRenIIG8XXlw%3d%3d | unknown | — | — | whitelisted |
8168 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1741788558&P2=404&P3=2&P4=gkEvjLwu2oGrlKXF2OCyMP72RO2Hzi7OsXP4obdv4TULOOGEII5rTf5hlu7PbwOhrztZHlM7AAiRenIIG8XXlw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.31.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3956 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7332 | msedge.exe | 172.67.69.58:443 | update.flipperzero.one | — | — | unknown |
7332 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
update.flipperzero.one |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |