| File name: | eld3.exe |
| Full analysis: | https://app.any.run/tasks/32638428-cc4e-4994-8cfa-970305fa0047 |
| Verdict: | Malicious activity |
| Analysis date: | December 21, 2025, 06:15:21 |
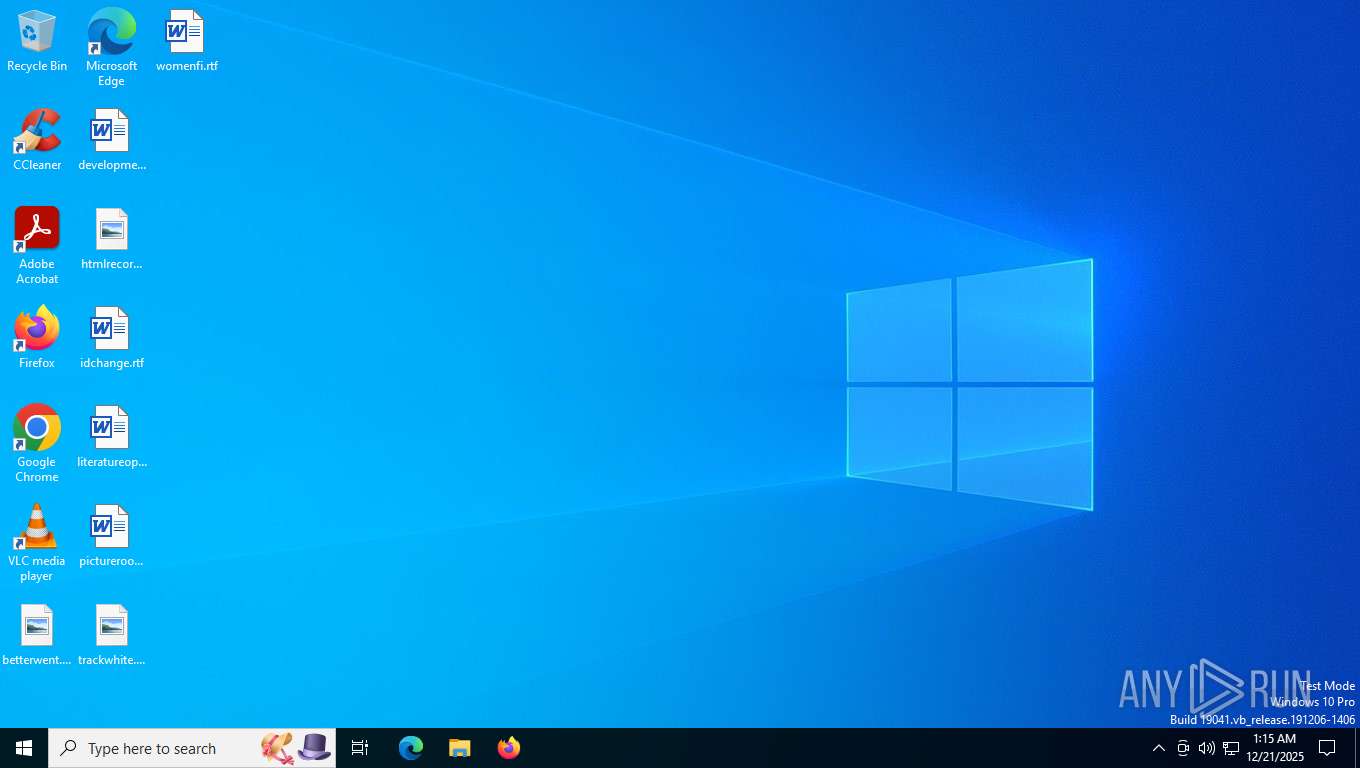
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | CDB67B1C54903F223F7DCCA14AEA67DF |
| SHA1: | DAC11017ABB2D6D196A527C2101AA7077EBC8910 |
| SHA256: | 4FF37E0D4B7D74C84BD26AE956A71441D8595F22C4EF1C9DB6FBFC1EE2325F5F |
| SSDEEP: | 98304:AO0/TtJF80nZZ3NteNQCrak9Sz4yEtZxrSxdG2i+6Y0YTShZMPeZznZXgD5x932N:0TLKZUbmIaUkM0 |
MALICIOUS
Changes the autorun value in the registry
- eld3.exe (PID: 7532)
SUSPICIOUS
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 7552)
Process drops python dynamic module
- eld3.exe (PID: 7512)
Starts CMD.EXE for commands execution
- eld3.exe (PID: 7532)
Loads Python modules
- eld3.exe (PID: 7532)
Executable content was dropped or overwritten
- eld3.exe (PID: 7512)
The process drops C-runtime libraries
- eld3.exe (PID: 7512)
Application launched itself
- eld3.exe (PID: 7512)
Process drops legitimate windows executable
- eld3.exe (PID: 7512)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 7608)
INFO
Launching a file from a Registry key
- eld3.exe (PID: 7532)
Reads the computer name
- eld3.exe (PID: 7532)
- eld3.exe (PID: 7512)
Checks supported languages
- eld3.exe (PID: 7532)
- eld3.exe (PID: 7512)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7608)
Reads the machine GUID from the registry
- eld3.exe (PID: 7532)
The sample compiled with english language support
- eld3.exe (PID: 7512)
Create files in a temporary directory
- eld3.exe (PID: 7512)
Checks proxy server information
- eld3.exe (PID: 7532)
PyInstaller has been detected (YARA)
- eld3.exe (PID: 7512)
- eld3.exe (PID: 7532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2021:04:15 05:29:57+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.28 |
| CodeSize: | 134656 |
| InitializedDataSize: | 141312 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x88fc |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
148
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5408 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7512 | "C:\Users\admin\AppData\Local\Temp\eld3.exe" | C:\Users\admin\AppData\Local\Temp\eld3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7532 | "C:\Users\admin\AppData\Local\Temp\eld3.exe" | C:\Users\admin\AppData\Local\Temp\eld3.exe | eld3.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7552 | C:\WINDOWS\system32\cmd.exe /c "wmic csproduct get uuid" | C:\Windows\System32\cmd.exe | — | eld3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7560 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7608 | wmic csproduct get uuid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
759
Read events
758
Write events
1
Delete events
0
Modification events
| (PID) Process: | (7532) eld3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | autogen |
Value: C:\Users\admin\AppData\Local\Temp\eld3.exe | |||
Executable files
14
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7512 | eld3.exe | C:\Users\admin\AppData\Local\Temp\_MEI75122\_bz2.pyd | executable | |
MD5:4079B0E80EF0F97CE35F272410BD29FE | SHA256:466D21407F5B589B20C464C51BFE2BE420E5A586A7F394908448545F16B08B33 | |||
| 7512 | eld3.exe | C:\Users\admin\AppData\Local\Temp\_MEI75122\libssl-1_1-x64.dll | executable | |
MD5:4EC3C7FE06B18086F83A18FFBB3B9B55 | SHA256:9D35D8DD9854A4D4205AE4EAFE28C92F8D0E3AC7C494AC4A6A117F6E4B45170C | |||
| 7512 | eld3.exe | C:\Users\admin\AppData\Local\Temp\_MEI75122\select.pyd | executable | |
MD5:C30E5ECCF9C62B0B0BC57ED591E16CC0 | SHA256:56D1A971762A1A56A73BDF64727E416FFA9395B8AF4EFCD218F5203D744E1268 | |||
| 7512 | eld3.exe | C:\Users\admin\AppData\Local\Temp\_MEI75122\_ctypes.pyd | executable | |
MD5:2F21F50D2252E3083555A724CA57B71E | SHA256:09887F07F4316057D3C87E3A907C2235DC6547E54ED4F5F9125F99E547D58BCE | |||
| 7512 | eld3.exe | C:\Users\admin\AppData\Local\Temp\_MEI75122\VCRUNTIME140.dll | executable | |
MD5:0E675D4A7A5B7CCD69013386793F68EB | SHA256:BF5FF4603557C9959ACEC995653D052D9054AD4826DF967974EFD2F377C723D1 | |||
| 7512 | eld3.exe | C:\Users\admin\AppData\Local\Temp\_MEI75122\_queue.pyd | executable | |
MD5:2325DAB36242FC732C85914AB7CE25AF | SHA256:2FFA512A2A369CCD3713419C6D4E36C2BD5D1967E046663D721D7E7AC9E4AB59 | |||
| 7512 | eld3.exe | C:\Users\admin\AppData\Local\Temp\_MEI75122\_hashlib.pyd | executable | |
MD5:C3B19AD5381B9832E313A448DE7C5210 | SHA256:BDF4A536F783958357D2E0055DEBDC3CF7790EE28BEB286452EEC0354A346BDC | |||
| 7512 | eld3.exe | C:\Users\admin\AppData\Local\Temp\_MEI75122\_lzma.pyd | executable | |
MD5:A567A2ECB4737E5B70500EAC25F23049 | SHA256:A4CBA6D82369C57CB38A32D4DACB99225F58206D2DD9883F6FC0355D6DDAEC3D | |||
| 7512 | eld3.exe | C:\Users\admin\AppData\Local\Temp\_MEI75122\_ssl.pyd | executable | |
MD5:D429FF3FD91943AD8539C076C2A0C75F | SHA256:45C8B99BA9E832CAB85E9D45B5601B7A1D744652E7F756EC6A6091E1D8398DD4 | |||
| 7512 | eld3.exe | C:\Users\admin\AppData\Local\Temp\_MEI75122\libcrypto-1_1-x64.dll | executable | |
MD5:022A61849ADAB67E3A59BCF4D0F1C40B | SHA256:2A57183839C3E9CC4618FB1994C40E47672A8B6DAFFAA76C5F89CF2542B02C2F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
28
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
1784 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
1784 | svchost.exe | GET | 200 | 72.246.29.11:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
508 | SIHClient.exe | GET | 200 | 20.242.39.171:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
508 | SIHClient.exe | GET | 200 | 20.165.94.63:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
508 | SIHClient.exe | GET | 304 | 20.165.94.63:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
7072 | svchost.exe | POST | 200 | 20.190.160.2:443 | https://login.live.com/RST2.srf | US | xml | 11.0 Kb | whitelisted |
7072 | svchost.exe | POST | 200 | 20.190.160.2:443 | https://login.live.com/RST2.srf | US | xml | 10.3 Kb | whitelisted |
508 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | US | binary | 419 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
1784 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6500 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7532 | eld3.exe | 94.75.227.181:80 | peerycli.com | LEASEWEB-NL-AMS-01 Netherlands | NL | whitelisted |
7072 | svchost.exe | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7072 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1784 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
peerycli.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |