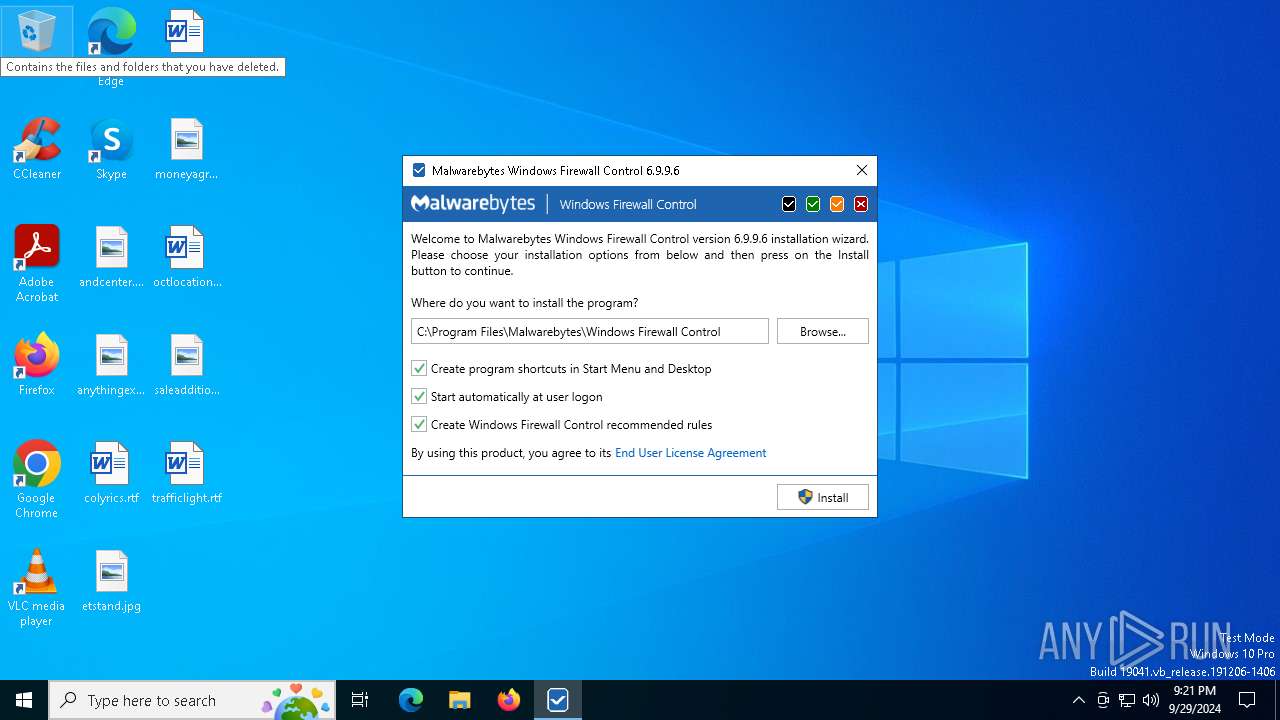
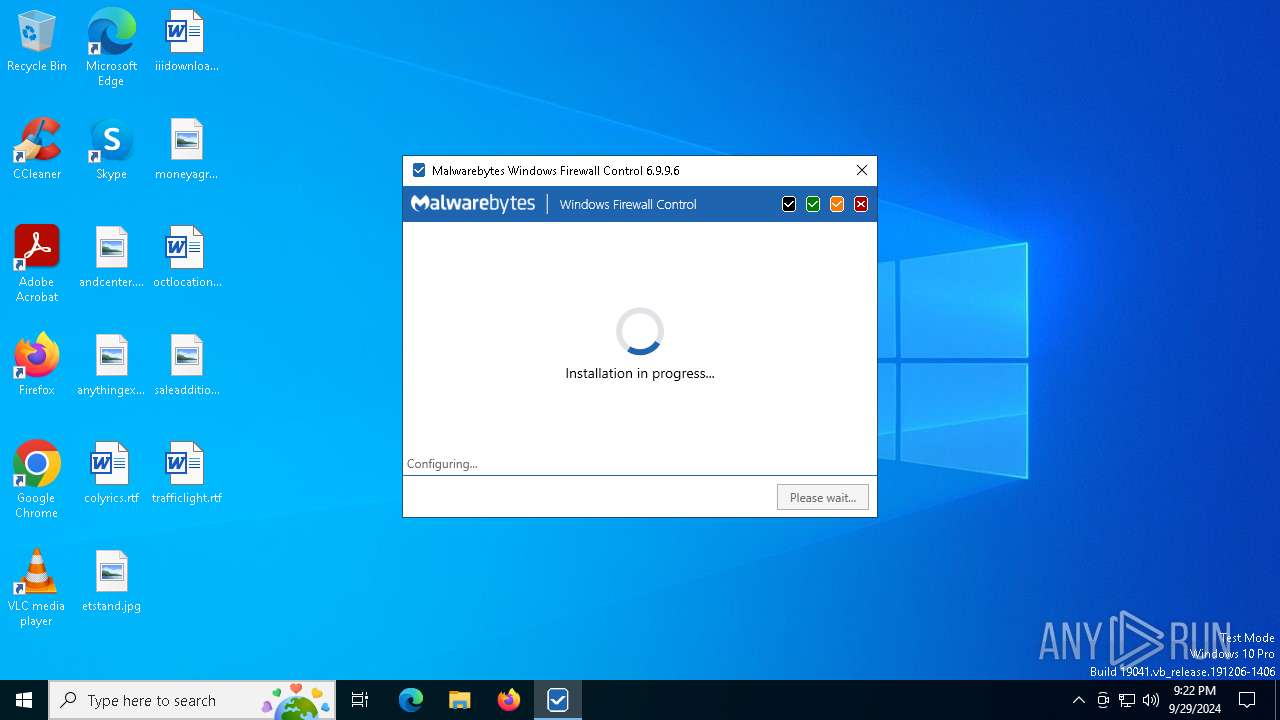
| File name: | wfc6setup.exe |
| Full analysis: | https://app.any.run/tasks/ff95a7c8-ee6b-4bbe-9f8c-971545451ed7 |
| Verdict: | Malicious activity |
| Analysis date: | September 29, 2024, 21:21:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable PE32 executable (GUI) Intel 80386, for MS Windows, MZ for MS-DOS |
| MD5: | 3D853BDADB5374A2787BBBBF7D9C77AA |
| SHA1: | A2179B6C2DEE1FF8DBF5A3B2D5DFB490C3677882 |
| SHA256: | 4FECBCA7A9831F0DAFF57F512ABECDD1E9A99813ADC0DE5A7CE150A485E8A98F |
| SSDEEP: | 98304:5cT22Hs3aavVG08sCixK1opWEbJm7sMNZ7pU2qvMFBKcLZPFjhTts7UTyGkX303j:Stl2JnOT |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- wfc6setup.exe (PID: 5364)
Starts itself from another location
- wfc6setup.exe (PID: 4100)
- icsys.icn.exe (PID: 1280)
- spoolsv.exe (PID: 5476)
- explorer.exe (PID: 6980)
- svchost.exe (PID: 4284)
Executable content was dropped or overwritten
- wfc6setup.exe (PID: 4100)
- icsys.icn.exe (PID: 1280)
- spoolsv.exe (PID: 5476)
- explorer.exe (PID: 6980)
- wfc6setup.exe (PID: 5364)
Starts application with an unusual extension
- wfc6setup.exe (PID: 4100)
Uses TASKKILL.EXE to kill process
- wfc6setup.exe (PID: 5364)
Starts SC.EXE for service management
- wfc6setup.exe (PID: 5364)
Process drops legitimate windows executable
- wfc6setup.exe (PID: 5364)
Suspicious use of NETSH.EXE
- wfc6setup.exe (PID: 5364)
Executes as Windows Service
- wfcs.exe (PID: 440)
INFO
Checks supported languages
- wfc6setup.exe (PID: 4100)
- wfc6setup.exe (PID: 5364)
Create files in a temporary directory
- wfc6setup.exe (PID: 4100)
Reads the computer name
- wfc6setup.exe (PID: 5364)
Reads the machine GUID from the registry
- wfc6setup.exe (PID: 5364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:04:01 07:08:22+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 106496 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x290c |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | Project1 |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | TJprojMain |
| OriginalFileName: | TJprojMain.exe |
Total processes
157
Monitored processes
27
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 400 | "C:\WINDOWS\system32\netsh.exe" advfirewall export "C:\Program Files\Malwarebytes\Windows Firewall Control\restore.wfw" | C:\Windows\System32\netsh.exe | — | wfc6setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 440 | "C:\Program Files\Malwarebytes\Windows Firewall Control\wfcs.exe" | C:\Program Files\Malwarebytes\Windows Firewall Control\wfcs.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Malwarebytes Integrity Level: SYSTEM Description: Malwarebytes Windows Firewall Control Service Version: 6.9.9.6 Modules
| |||||||||||||||
| 1132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | C:\Windows\Resources\Themes\icsys.icn.exe | C:\Windows\Resources\Themes\icsys.icn.exe | wfc6setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1336 | "C:\WINDOWS\system32\sc.exe" start wfcs | C:\Windows\System32\sc.exe | — | wfc6setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1656 | "C:\WINDOWS\system32\sc.exe" config MpsSvc start= auto | C:\Windows\System32\sc.exe | — | wfc6setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | "C:\WINDOWS\system32\sc.exe" failure wfcs reset= 3600 actions= restart/60000/restart/60000// | C:\Windows\System32\sc.exe | — | wfc6setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2480 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3456 | "C:\WINDOWS\system32\auditpol.exe" /set /subcategory:{0CCE9226-69AE-11D9-BED3-505054503030} /failure:enable /success:enable | C:\Windows\System32\auditpol.exe | — | wfc6setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Audit Policy Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 430
Read events
4 852
Write events
549
Delete events
29
Modification events
| (PID) Process: | (4100) wfc6setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (1280) icsys.icn.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (6980) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (6980) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (6980) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (6980) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
| (PID) Process: | (4284) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (4284) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (4284) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (4284) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
Executable files
16
Suspicious files
7
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4100 | wfc6setup.exe | C:\Users\admin\AppData\Local\Temp\wfc6setup.exe | executable | |
MD5:C987C099C664B77B1C6D4FE27C5A6AC0 | SHA256:ACCB7D4CCD9E6C5C1988C1BFE8015B2E459E52B3F8A965BD086A4746000524E6 | |||
| 1280 | icsys.icn.exe | C:\Users\admin\AppData\Local\Temp\~DF9B18D53CCBFF718D.TMP | binary | |
MD5:7F1171A536C738EEE660AED4F6D3A39A | SHA256:CA0A3EF86F90EC06C08644441F28AB22D070BEEF309E80F720066825CBCFB934 | |||
| 5364 | wfc6setup.exe | C:\Program Files\Malwarebytes\Windows Firewall Control\mbcut.dll | executable | |
MD5:8953CA0009CB62892B2A93E8B05D3042 | SHA256:153C721F3CB258B56CE009A3BCA0A3D98E4E3CD3799CBC6E69C4E349C4C38E79 | |||
| 4100 | wfc6setup.exe | C:\Windows\Resources\Themes\icsys.icn.exe | executable | |
MD5:BED1F5FABAEC1D483BDBA2F31E77843C | SHA256:D20A723F539FE1BA2A7A475F469E5A017498B4EBE7DD7874583851E6A9FAD5CE | |||
| 5072 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DF4D32CA8A15CF82AF.TMP | binary | |
MD5:0A23364A9A41CA42E60125415524A048 | SHA256:51ED66449156C04AB7C3B59238C4014C5297C21C06DBC9F7855FA872243B3CE2 | |||
| 6980 | explorer.exe | C:\Windows\Resources\spoolsv.exe | executable | |
MD5:F71070193CF5A7234D137A6918E3A681 | SHA256:449D39F872025E41D9EC496F836D04D5491916E66CD3B4D3414E1BBB621A6AE4 | |||
| 5364 | wfc6setup.exe | C:\Program Files\Malwarebytes\Windows Firewall Control\Newtonsoft.Json.dll | executable | |
MD5:195FFB7167DB3219B217C4FD439EEDD6 | SHA256:E1E27AF7B07EEEDF5CE71A9255F0422816A6FC5849A483C6714E1B472044FA9D | |||
| 5476 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DF42693C78E25C2996.TMP | binary | |
MD5:5886122D4625424ECE9834CC1D0562A4 | SHA256:33F36C94151A1566343BE4ABFA3BB46BCBA8F4C4F7C33FC5F0DF704BFE402BC5 | |||
| 5364 | wfc6setup.exe | C:\Program Files\Malwarebytes\Windows Firewall Control\Google.Protobuf.dll | executable | |
MD5:D4FC377DF96077F4B38C4DF41535C610 | SHA256:44B0B144E10AB00469BC4C9B29F14E903430746B0B5DBA3E5F896F4EACD90277 | |||
| 5364 | wfc6setup.exe | C:\Program Files\Malwarebytes\Windows Firewall Control\System.Numerics.Vectors.dll | executable | |
MD5:AAA2CBF14E06E9D3586D8A4ED455DB33 | SHA256:1D3EF8698281E7CF7371D1554AFEF5872B39F96C26DA772210A33DA041BA1183 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
50
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5880 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
796 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
796 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1840 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6564 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4324 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6564 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5880 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5880 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |