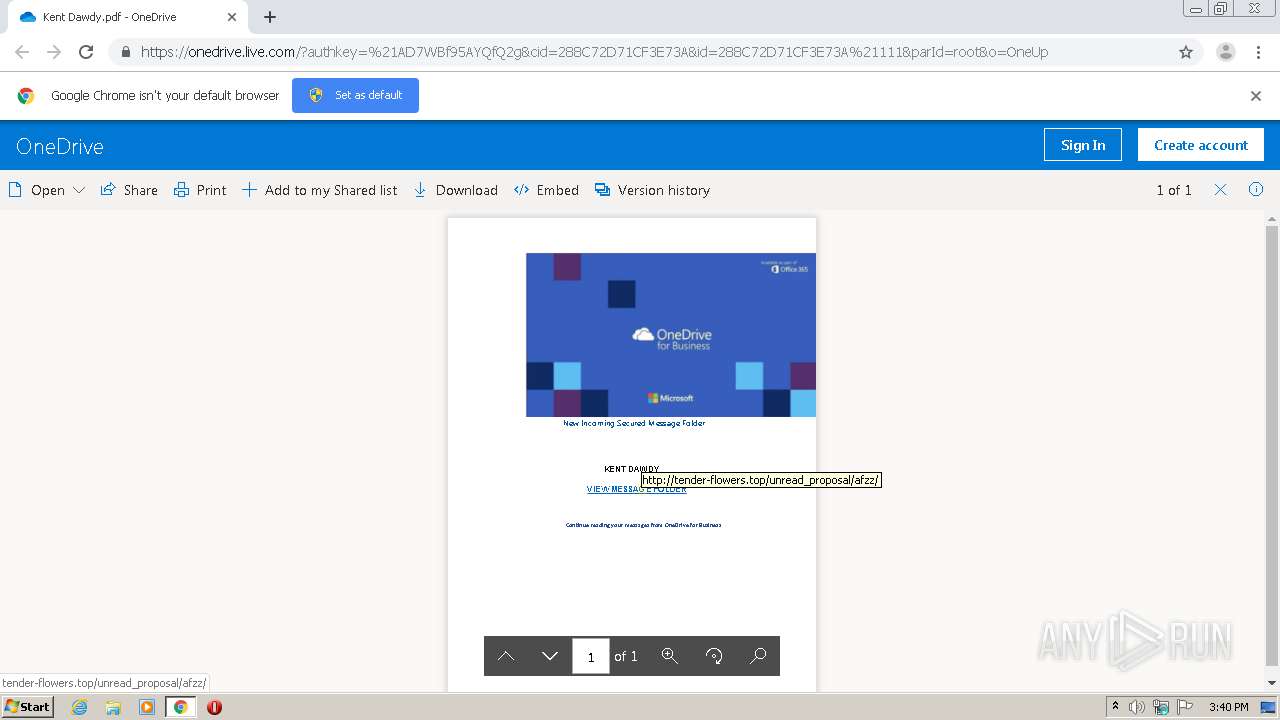
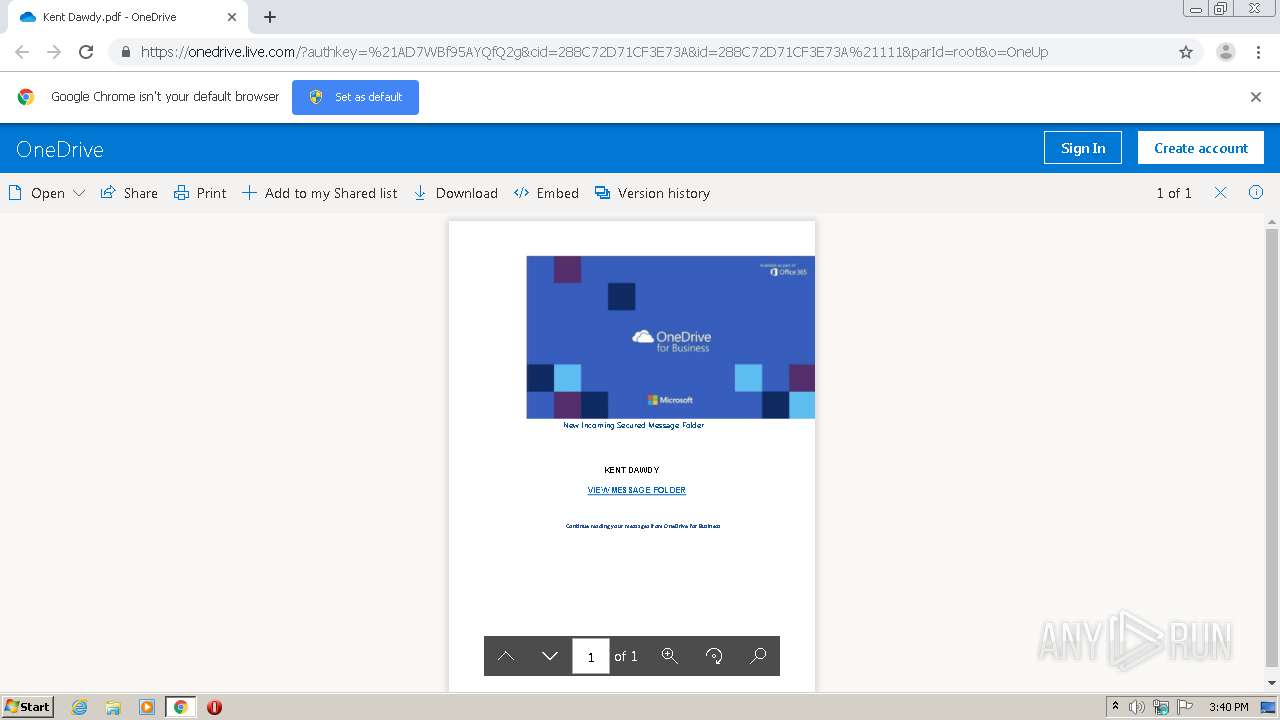
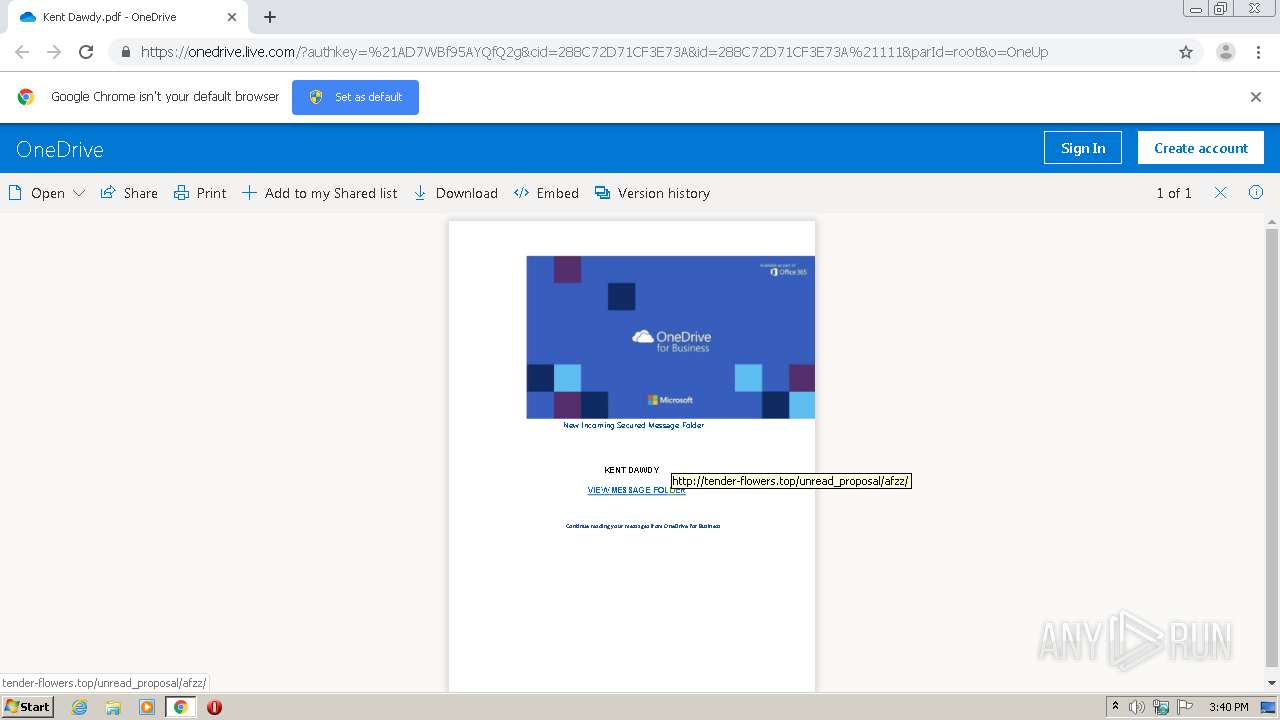
| URL: | https://onedrive.live.com/?authkey=%21AD7WBf95AYQfQ2g&cid=288C72D71CF3E73A&id=288C72D71CF3E73A%21111&parId=root&o=OneUp |
| Full analysis: | https://app.any.run/tasks/7e55fdf2-da5d-43f4-9791-7244870ecd0b |
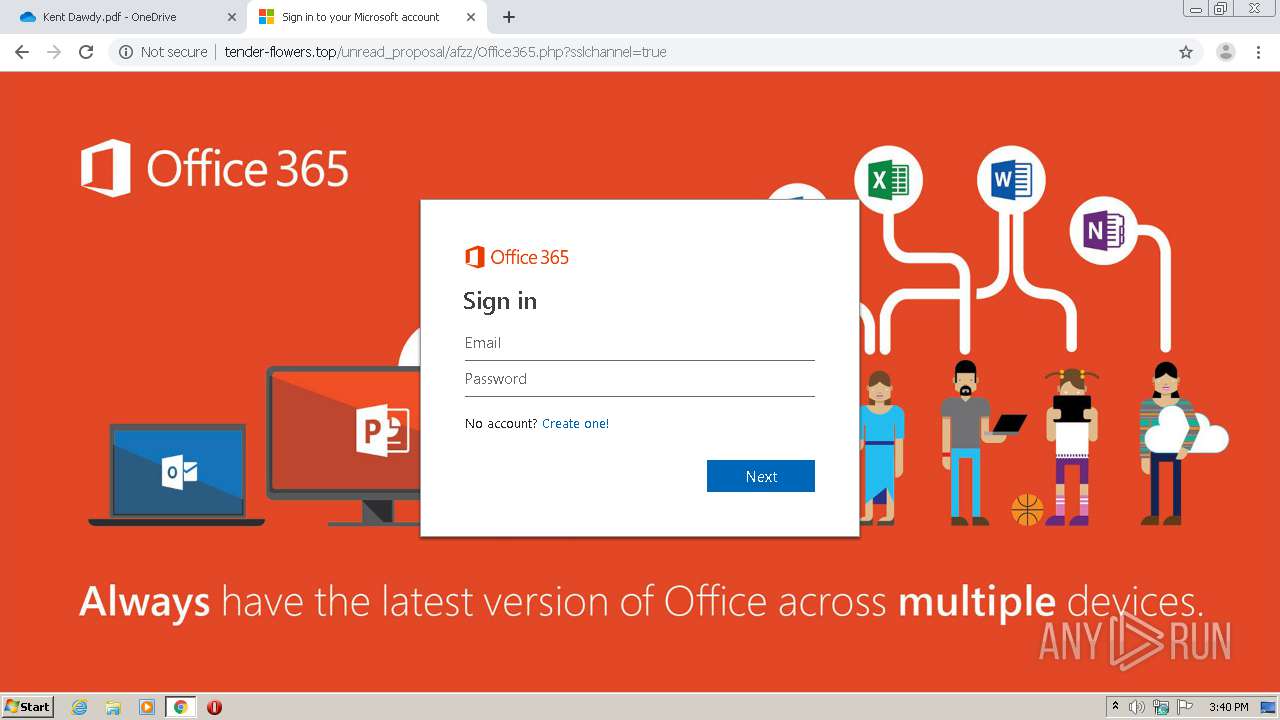
| Verdict: | Malicious activity |
| Analysis date: | June 10, 2020, 14:39:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7537D92987B6B461DEE2AB8931B14E2D |
| SHA1: | C9A329CFCA81120E477F9BA2FC75AC784505E22B |
| SHA256: | 4FE87EAA53F131A1B0AEC5B6377C81D86BC060CE93FF29BB76506A16D648B94D |
| SSDEEP: | 3:N8Ck3CTZxAXDEZ0wfomjnSFmomjnSDNzVzKHJV:2CkSTfAXIZ0wfom2com2DNxyb |
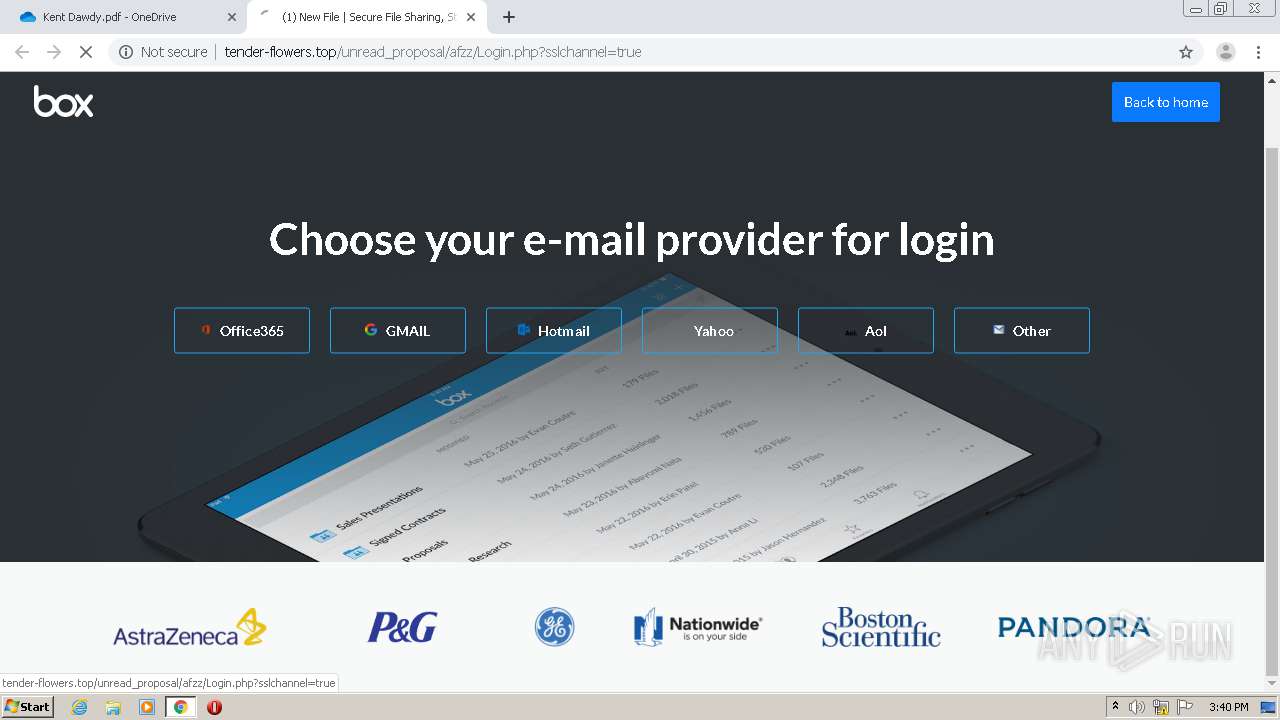
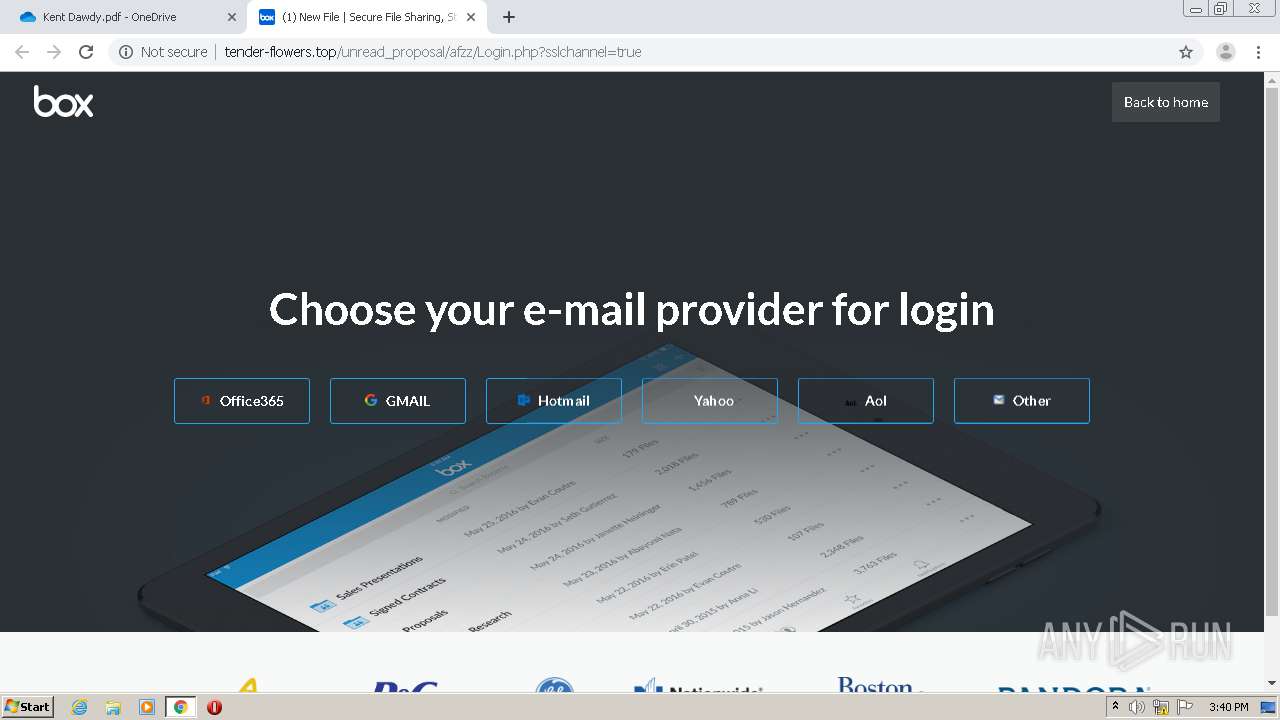
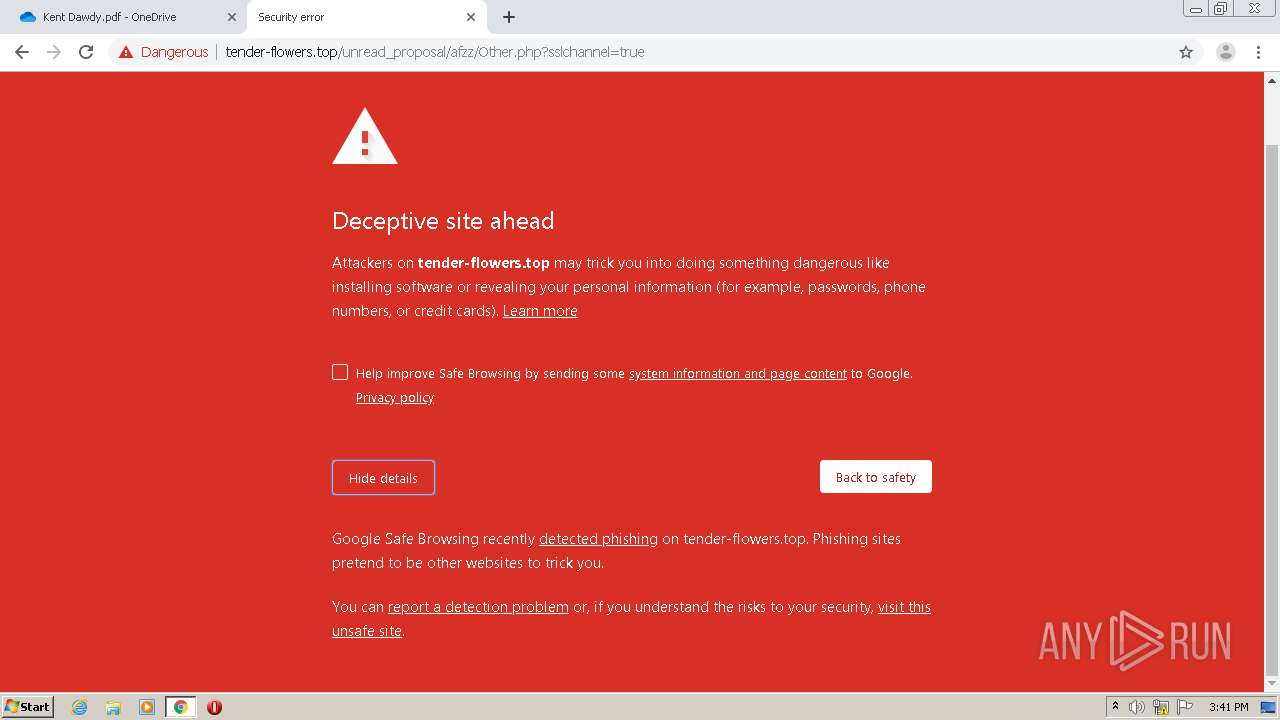
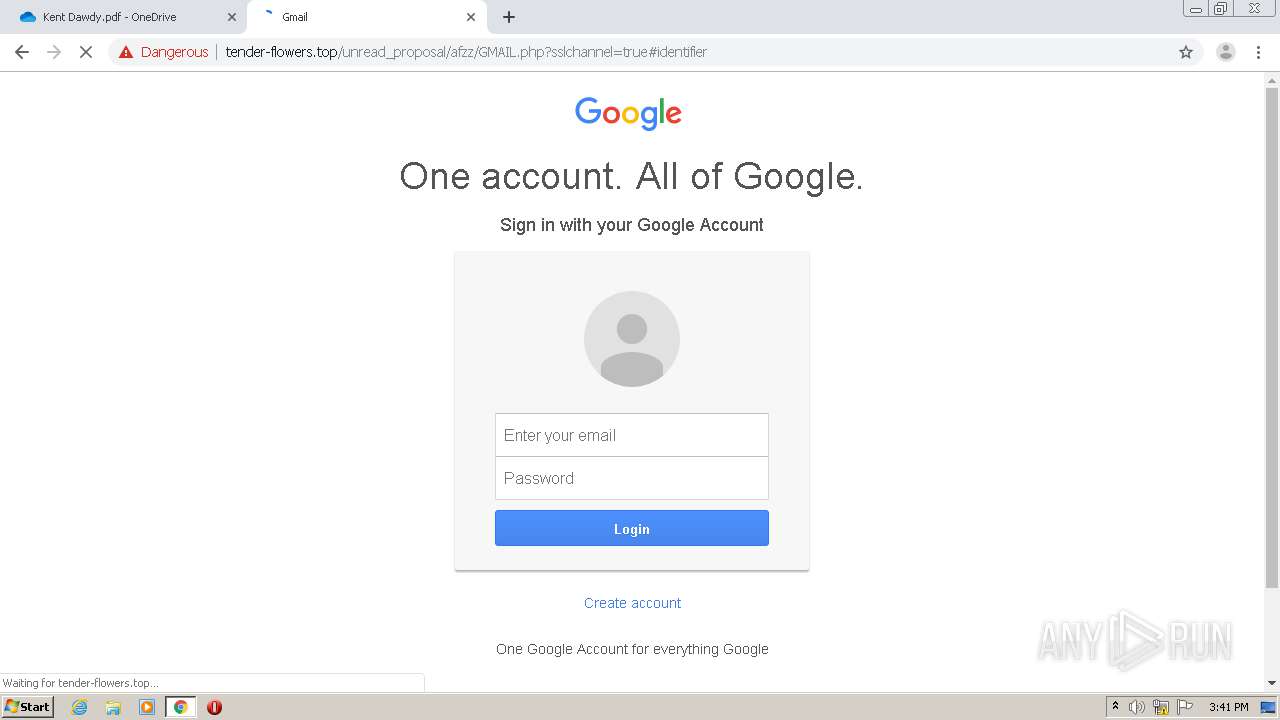
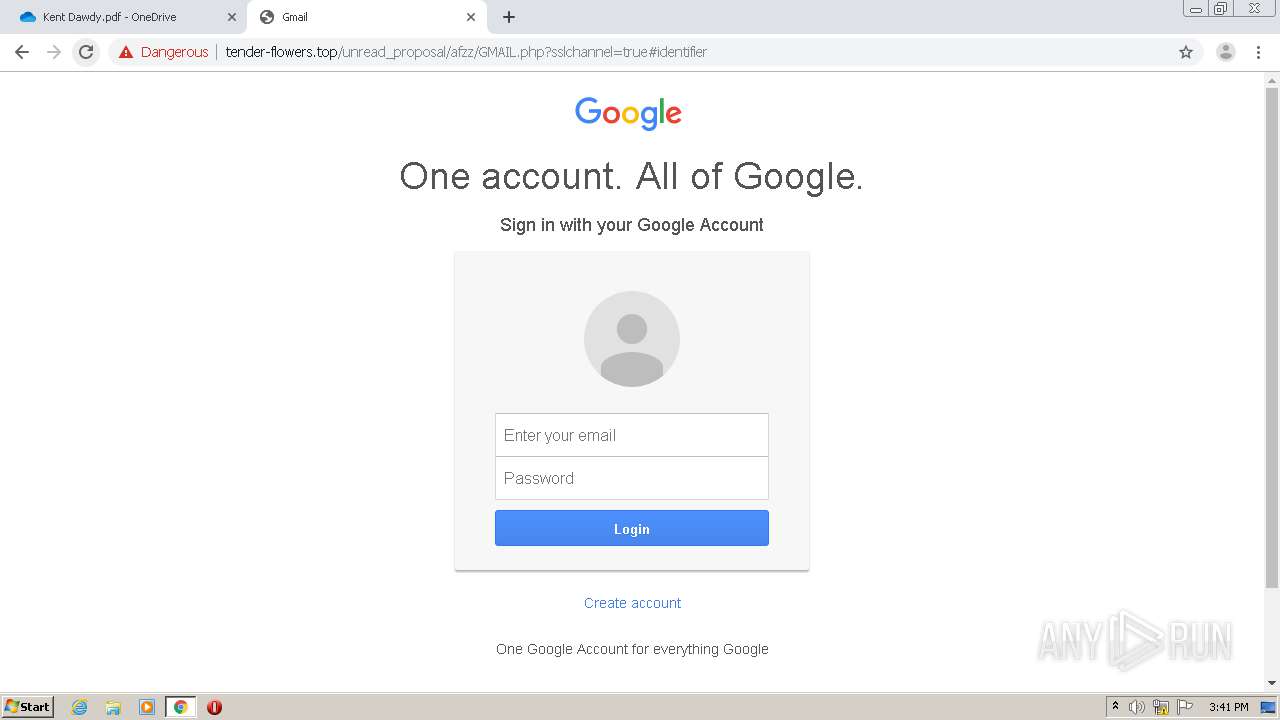
MALICIOUS
Loads Microsoft favicon from HTTP
- chrome.exe (PID: 1520)
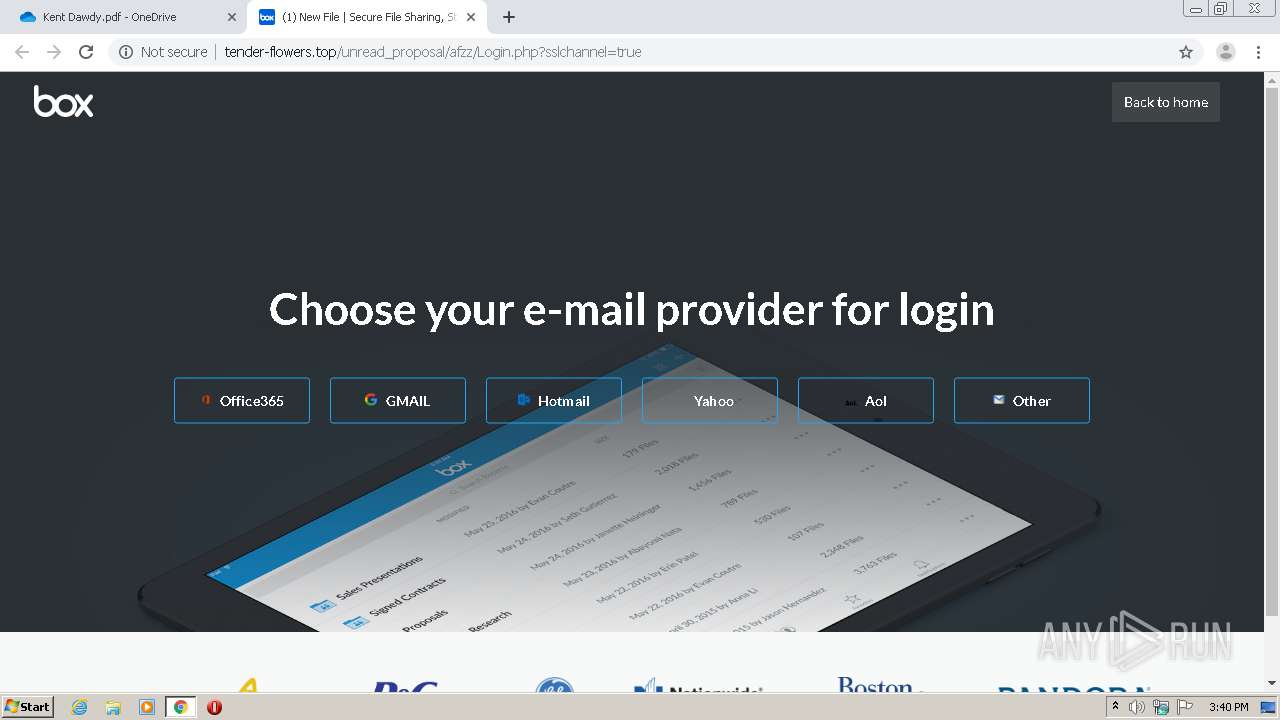
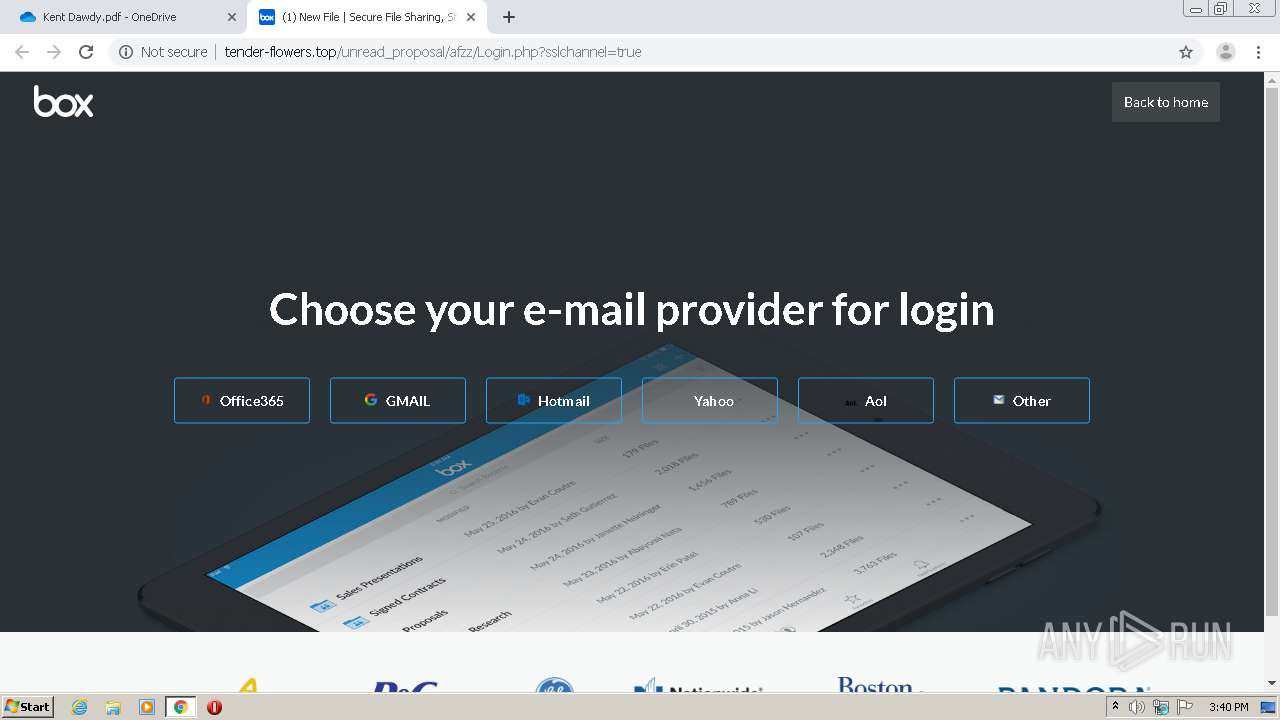
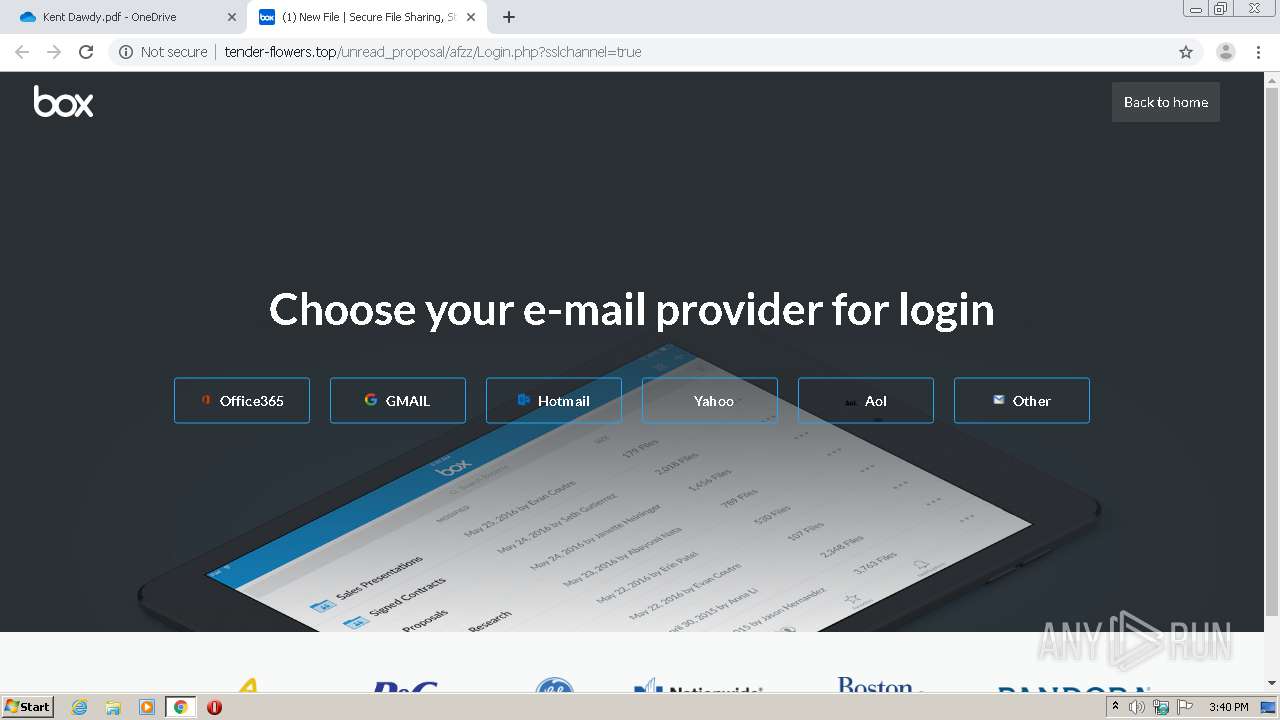
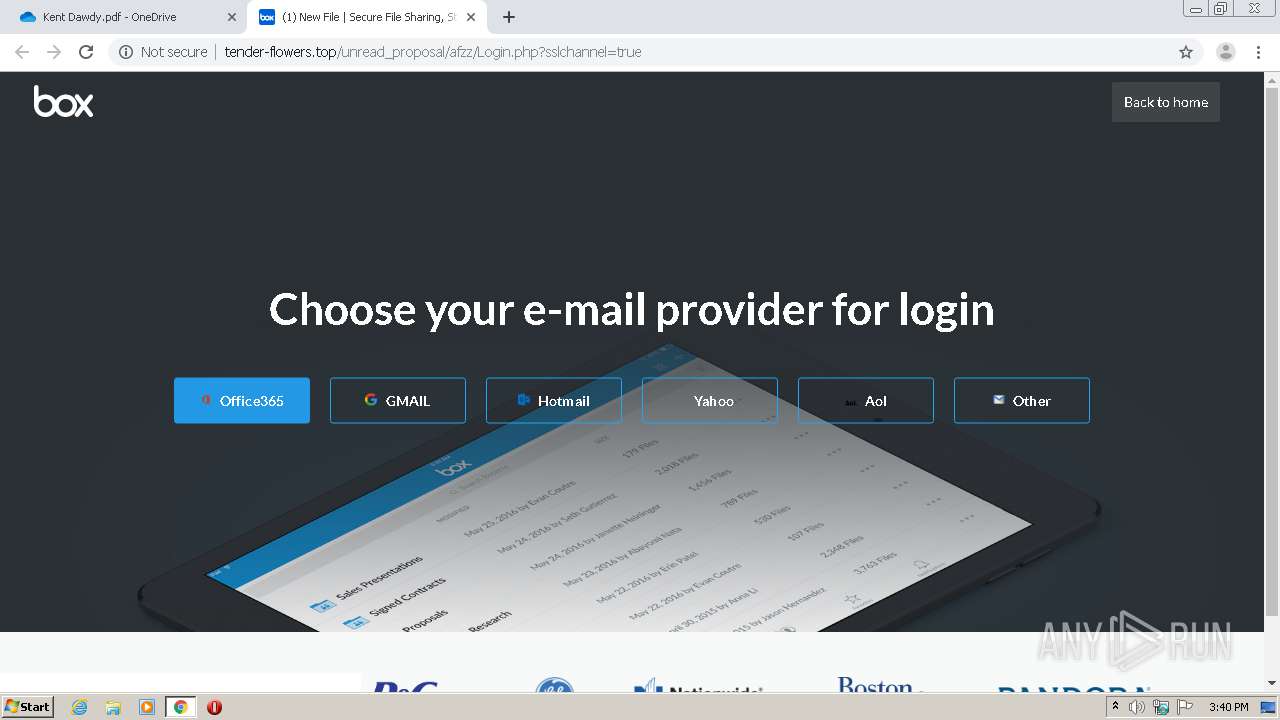
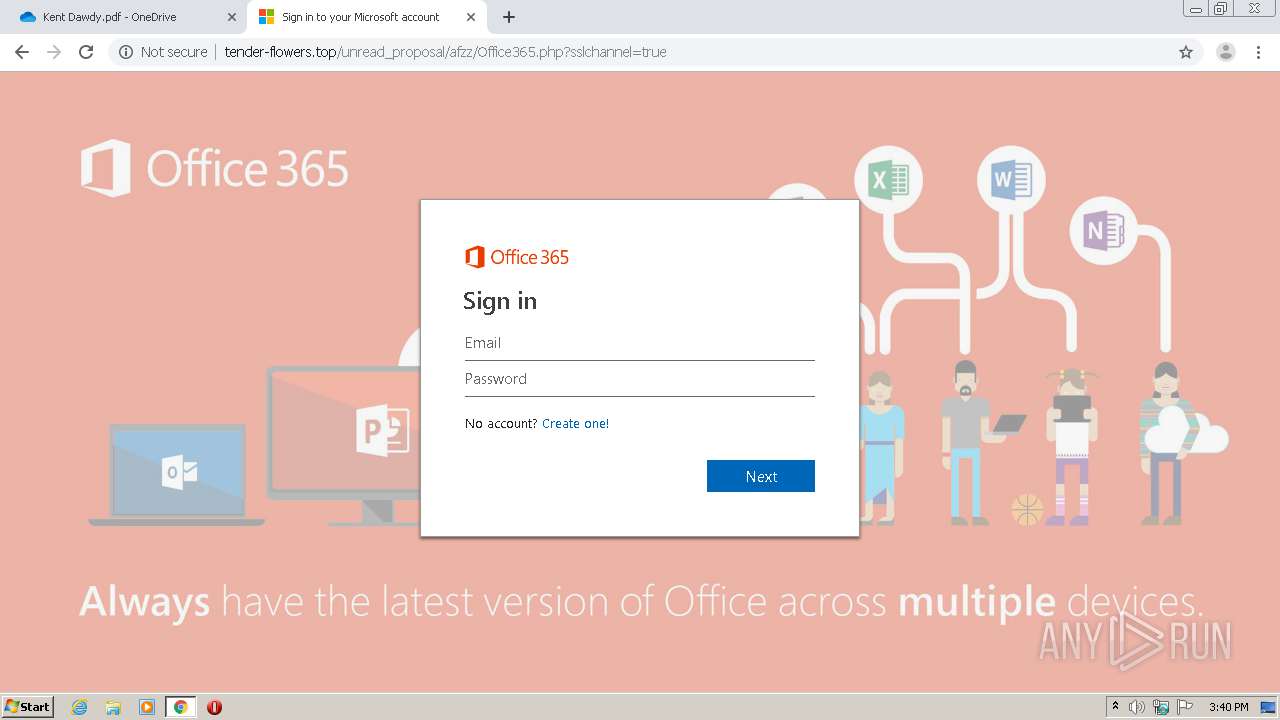
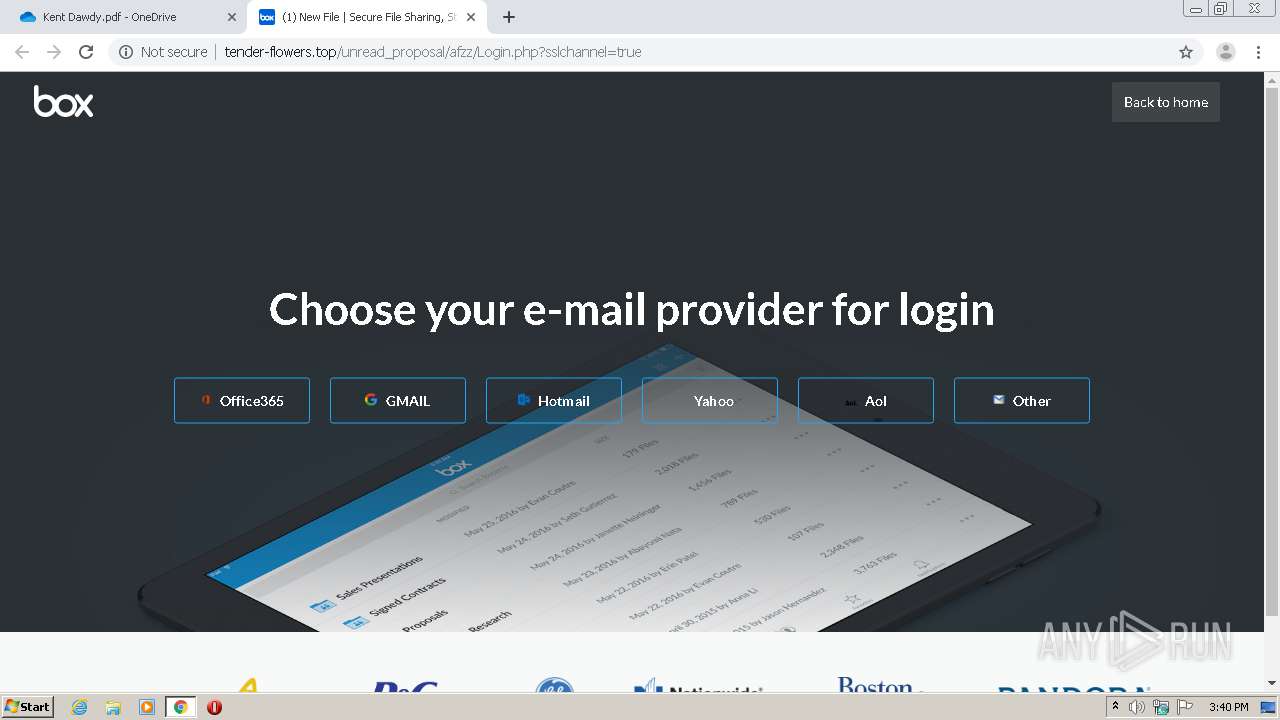
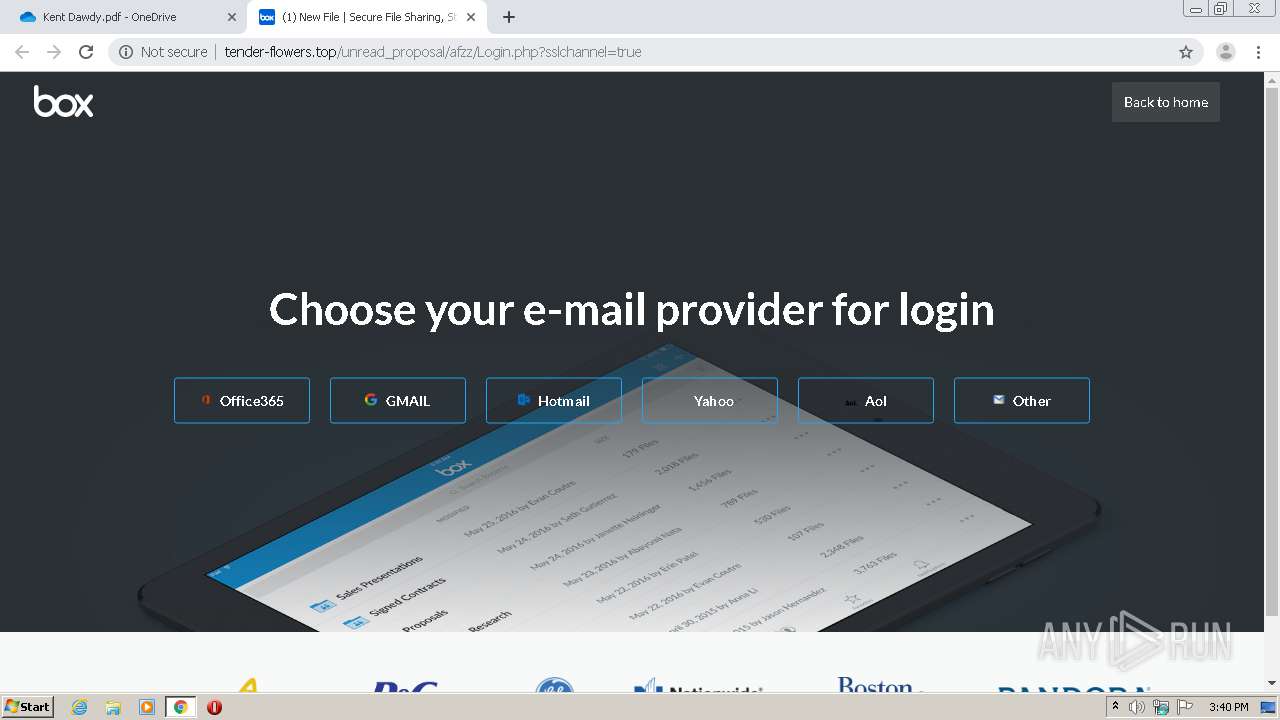
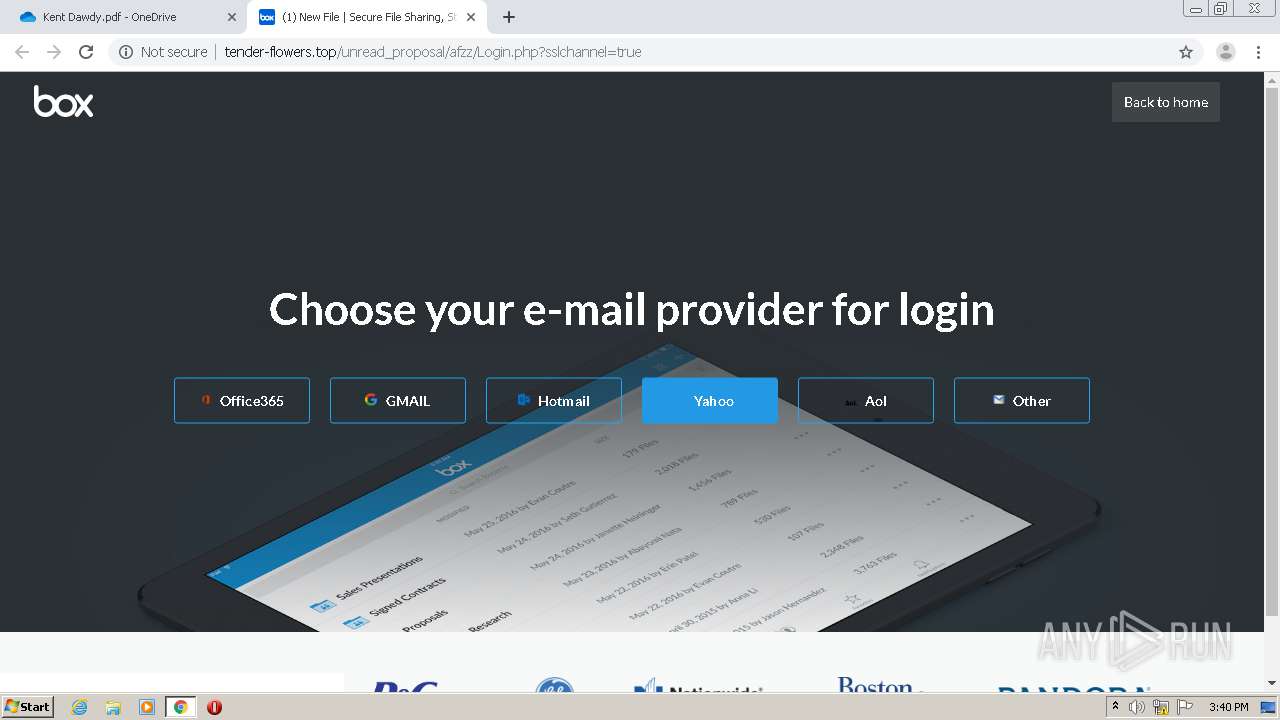
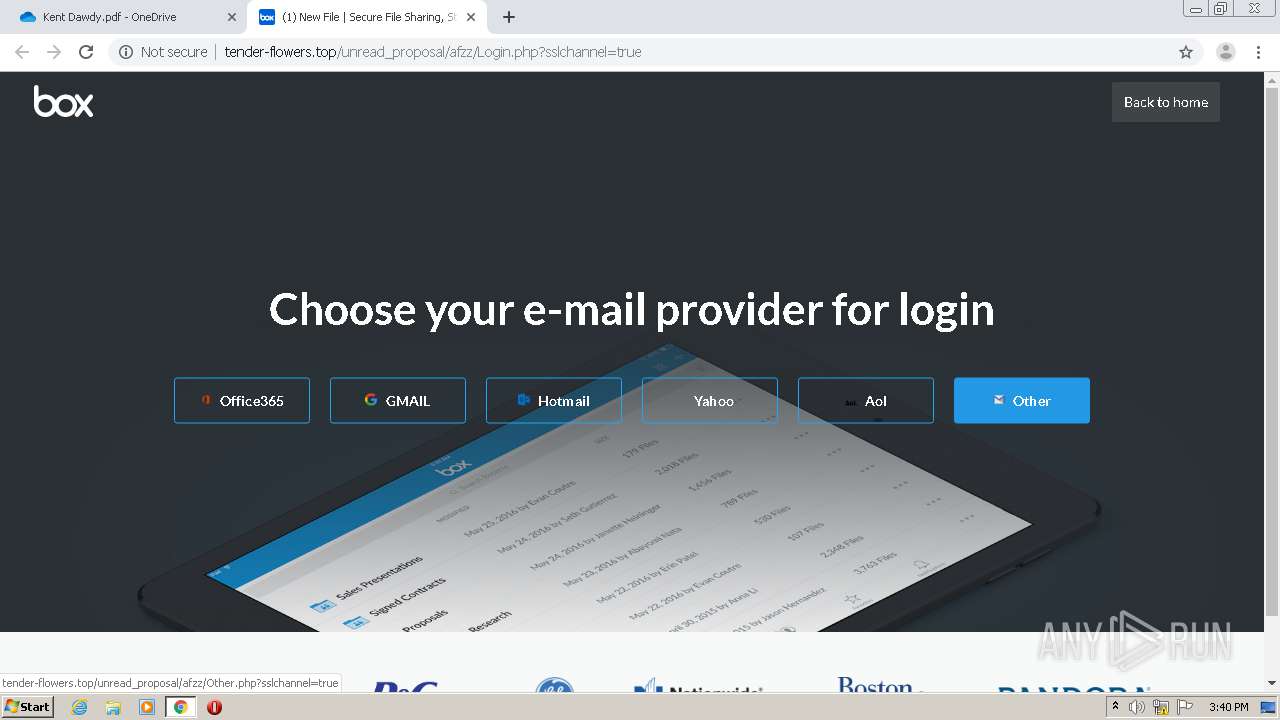
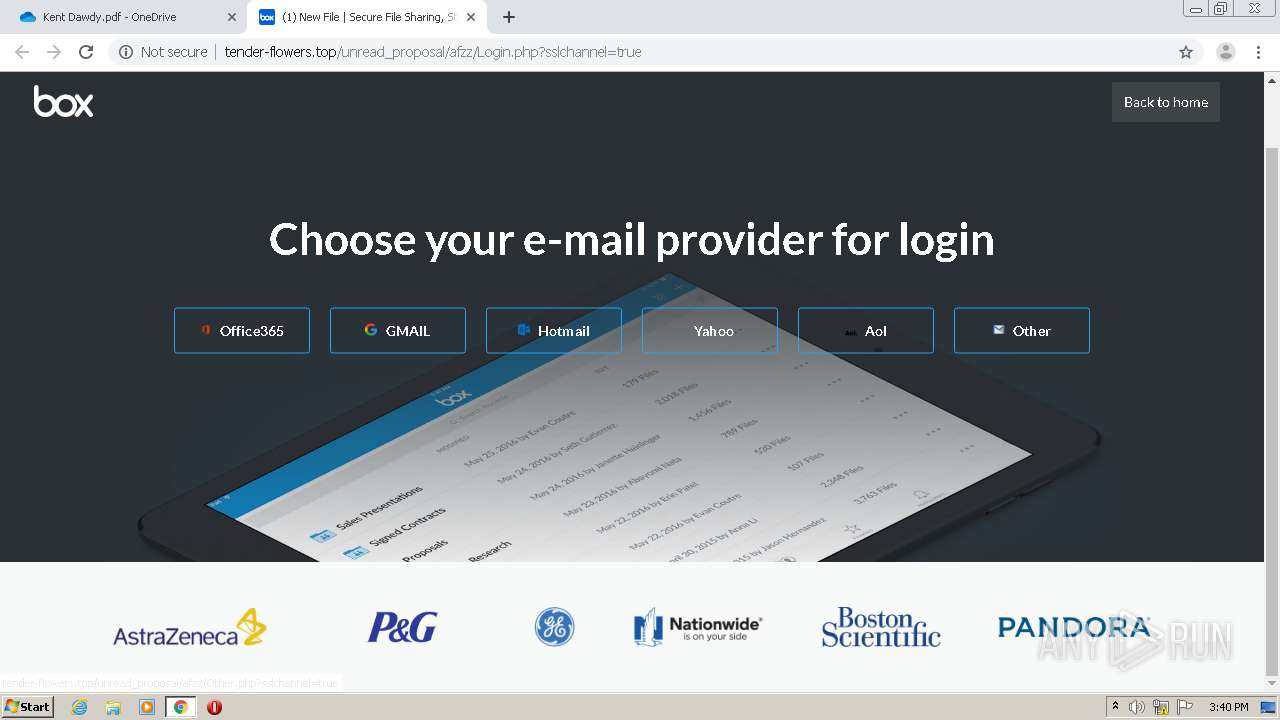
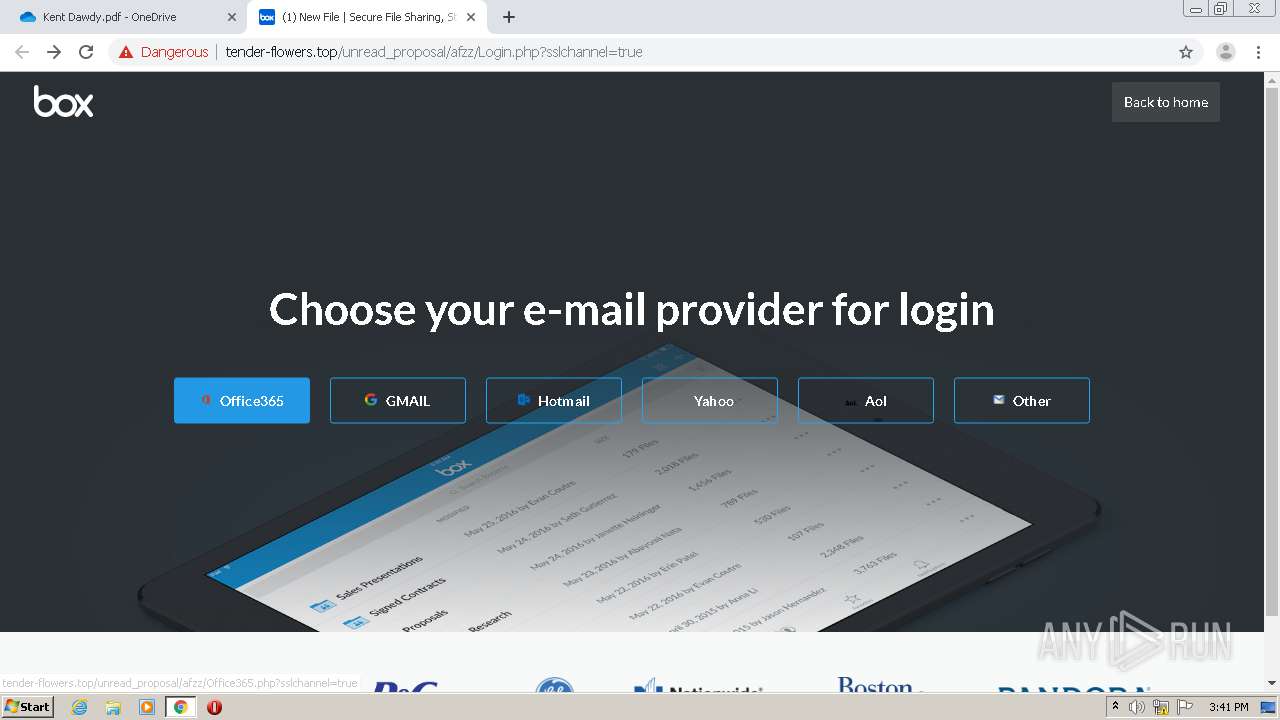
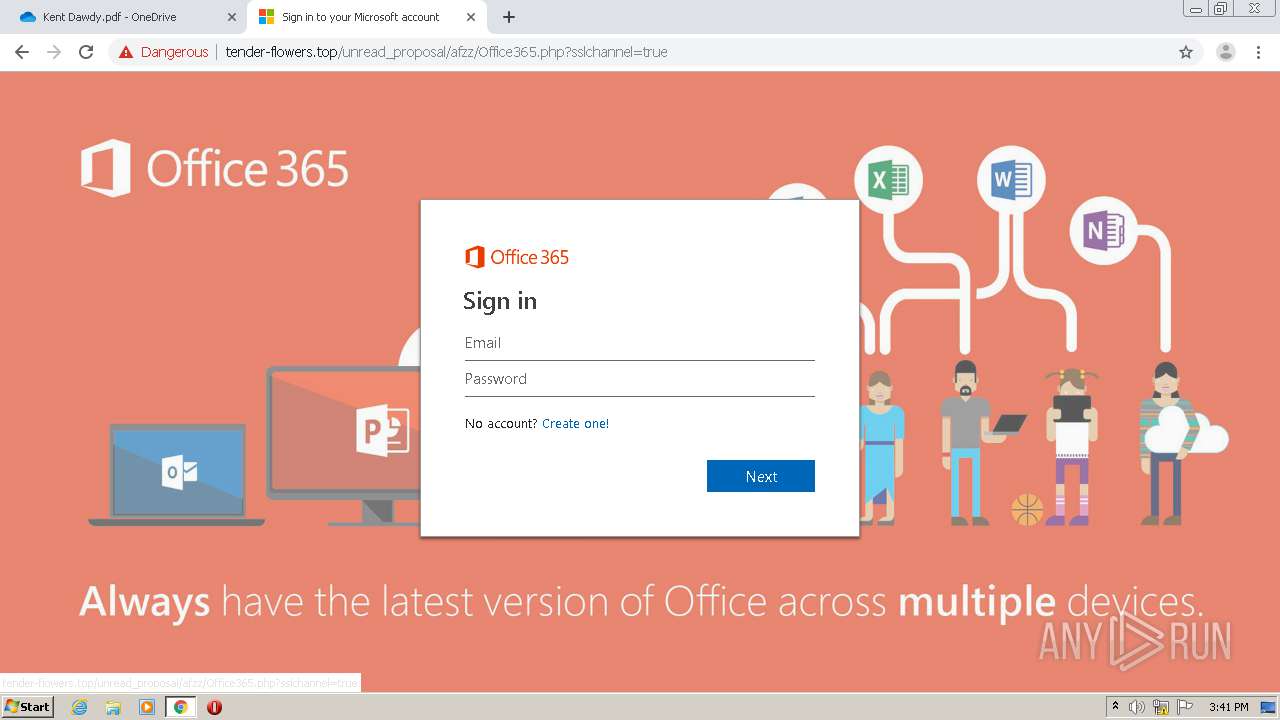
Office365 phishing was detected
- chrome.exe (PID: 1520)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1032)
INFO
Reads the hosts file
- chrome.exe (PID: 1032)
- chrome.exe (PID: 1520)
Application launched itself
- chrome.exe (PID: 1032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
29
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,1357781164822454679,6199341300167539216,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8522402171506923227 --mojo-platform-channel-handle=4016 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,1357781164822454679,6199341300167539216,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9598489698212629850 --mojo-platform-channel-handle=4092 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,1357781164822454679,6199341300167539216,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6595707205219747955 --mojo-platform-channel-handle=2544 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://onedrive.live.com/?authkey=%21AD7WBf95AYQfQ2g&cid=288C72D71CF3E73A&id=288C72D71CF3E73A%21111&parId=root&o=OneUp" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,1357781164822454679,6199341300167539216,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11586136503421569008 --mojo-platform-channel-handle=1532 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,1357781164822454679,6199341300167539216,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=720941986617924193 --mojo-platform-channel-handle=3512 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1357781164822454679,6199341300167539216,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12625647633571300618 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,1357781164822454679,6199341300167539216,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5394508056700637474 --mojo-platform-channel-handle=4516 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=984 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1357781164822454679,6199341300167539216,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2824014834247247816 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
614
Read events
519
Write events
90
Delete events
5
Modification events
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1032-13236273579793625 |
Value: 259 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1032-13236273579793625 |
Value: 259 | |||
Executable files
0
Suspicious files
133
Text files
316
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EE0F0AC-408.pma | — | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d735e558-5e25-48d5-9e24-c65ec312ed87.tmp | — | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF15cadb.TMP | text | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF15caeb.TMP | text | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1032 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15cd0e.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
126
DNS requests
54
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1520 | chrome.exe | GET | 200 | 173.194.160.218:80 | http://r4---sn-hpa7zn7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=185.128.27.133&mm=28&mn=sn-hpa7zn7d&ms=nvh&mt=1591799897&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 823 Kb | whitelisted |
1520 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
1520 | chrome.exe | GET | 200 | 104.26.5.108:80 | http://pngimg.com/uploads/email/email_PNG20.png | US | image | 32.0 Kb | whitelisted |
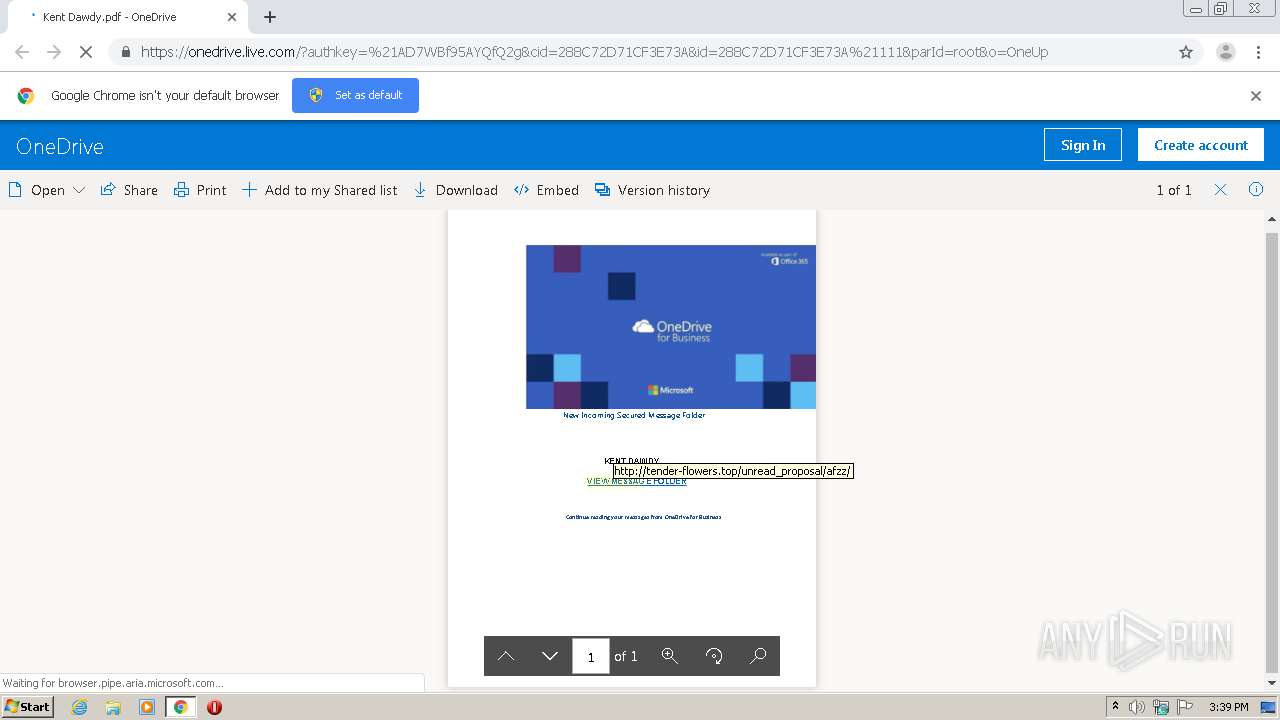
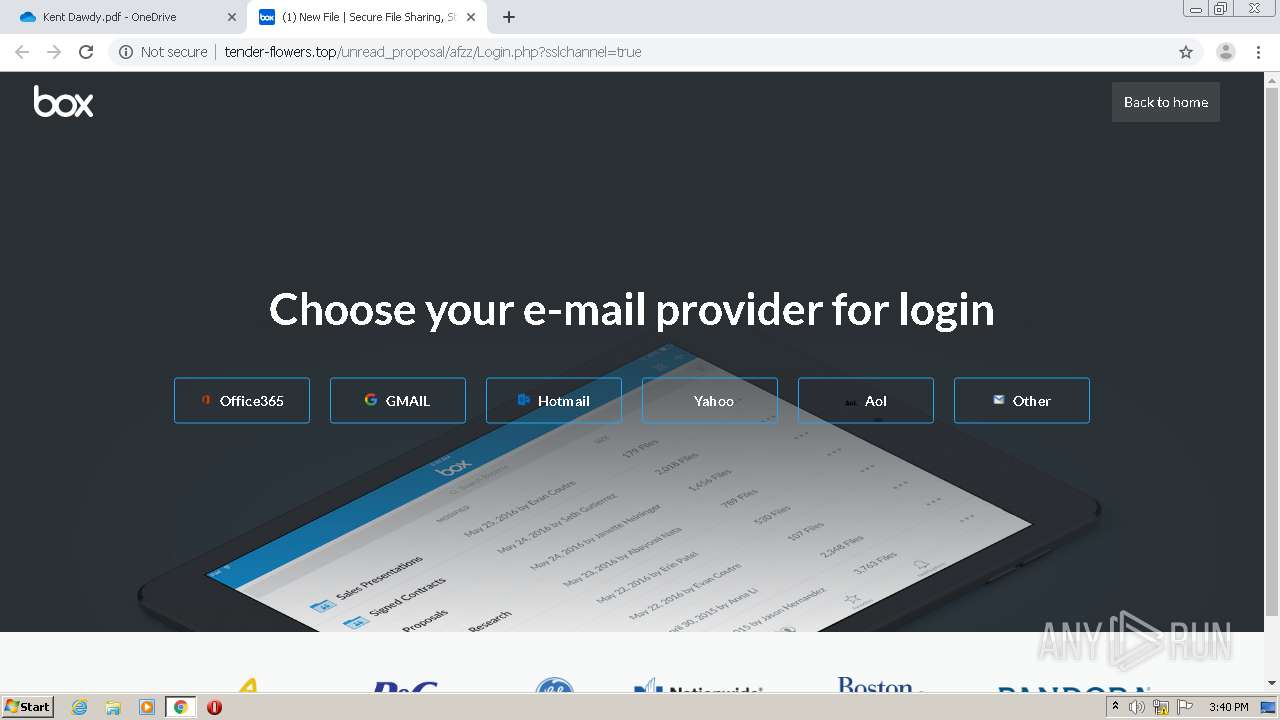
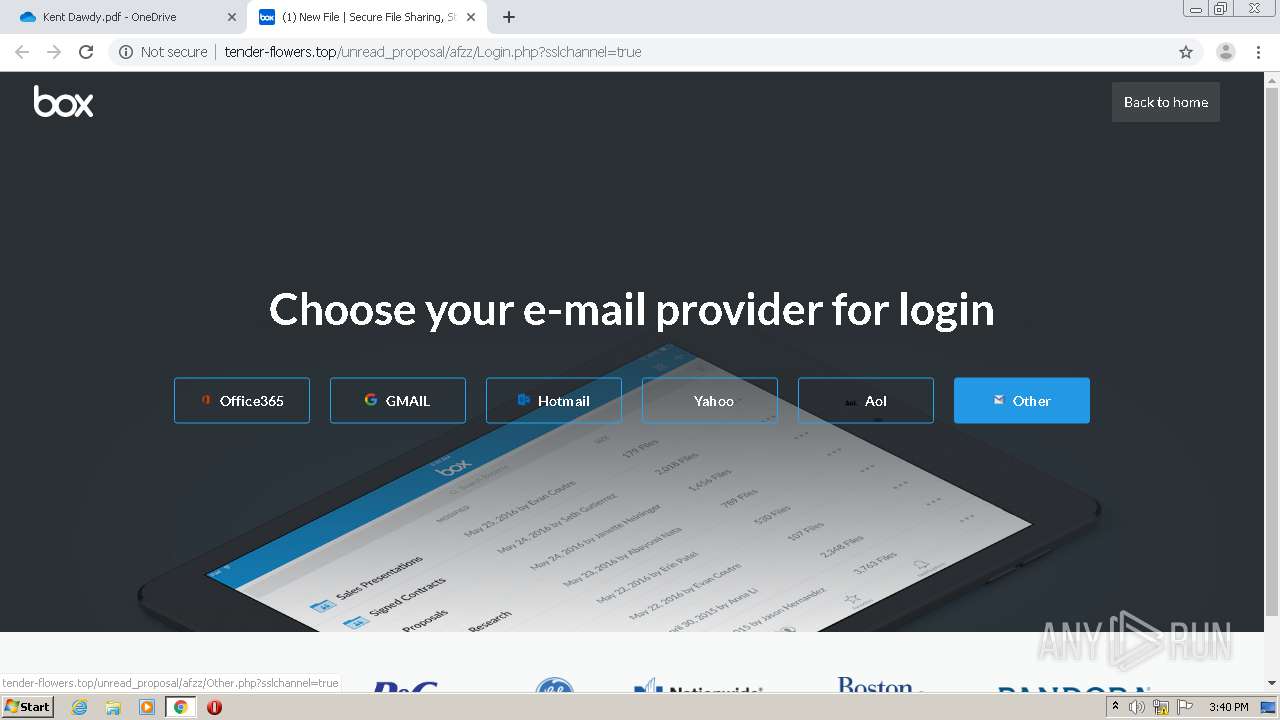
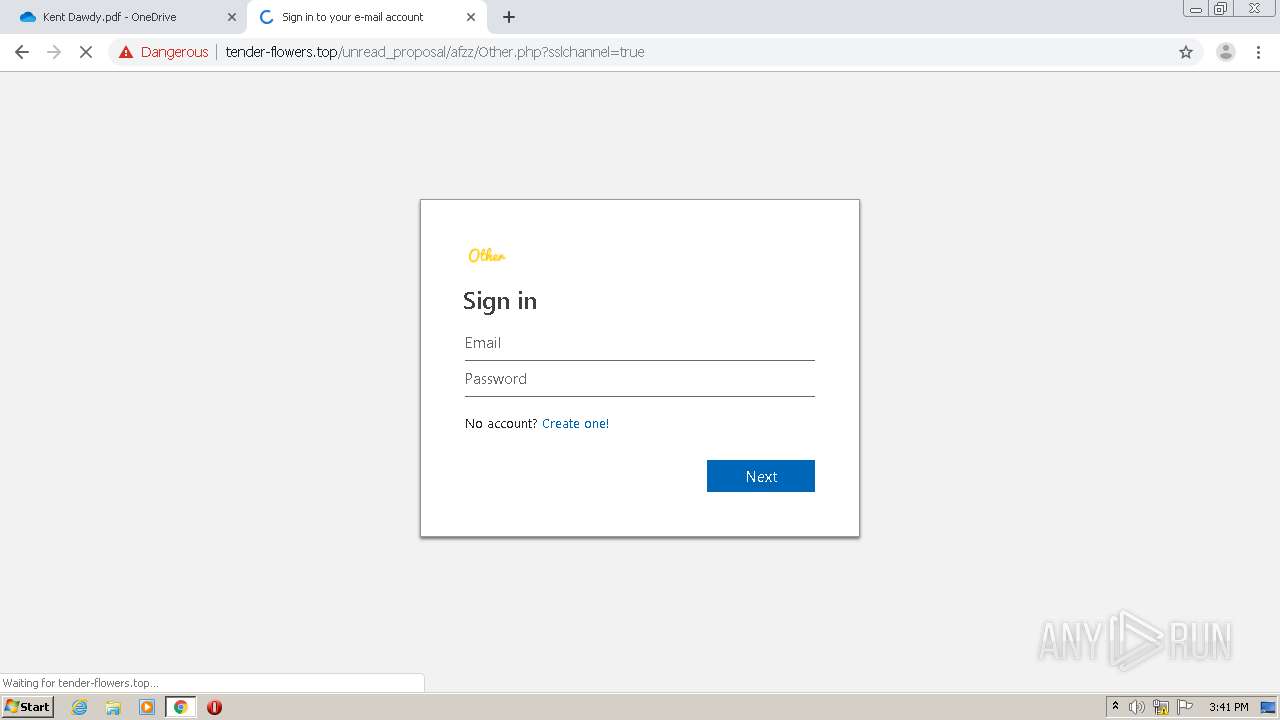
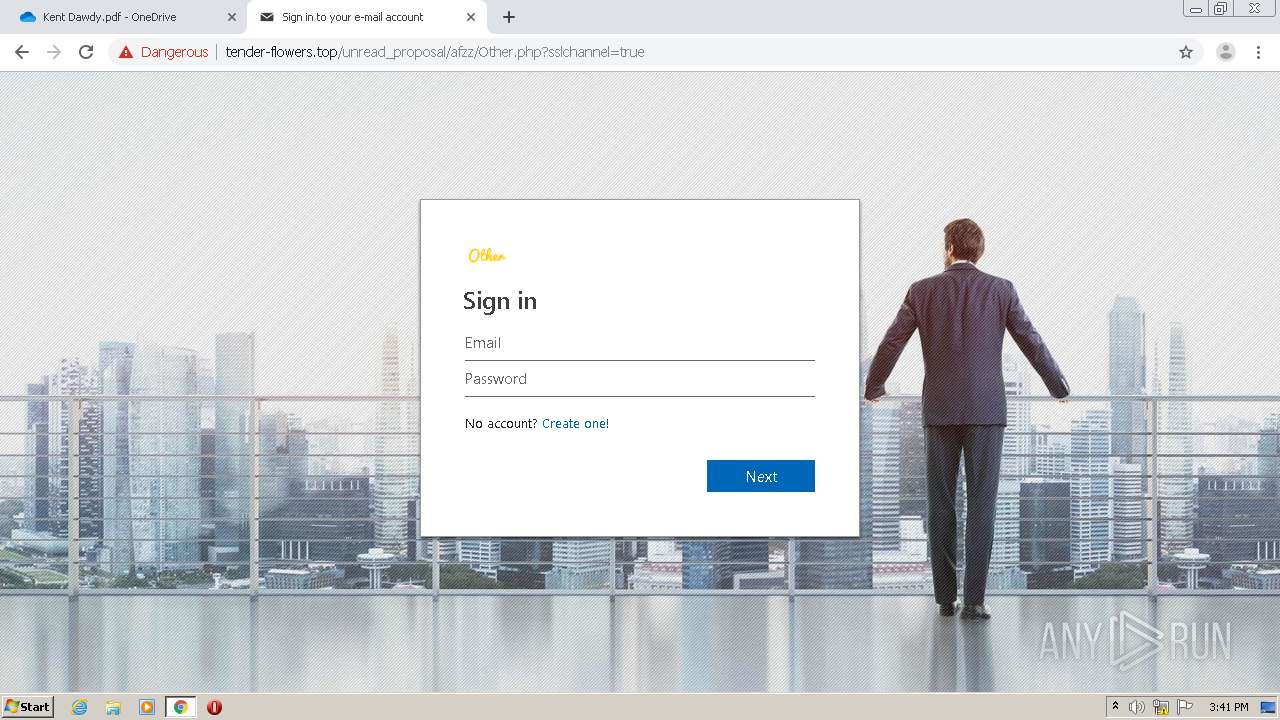
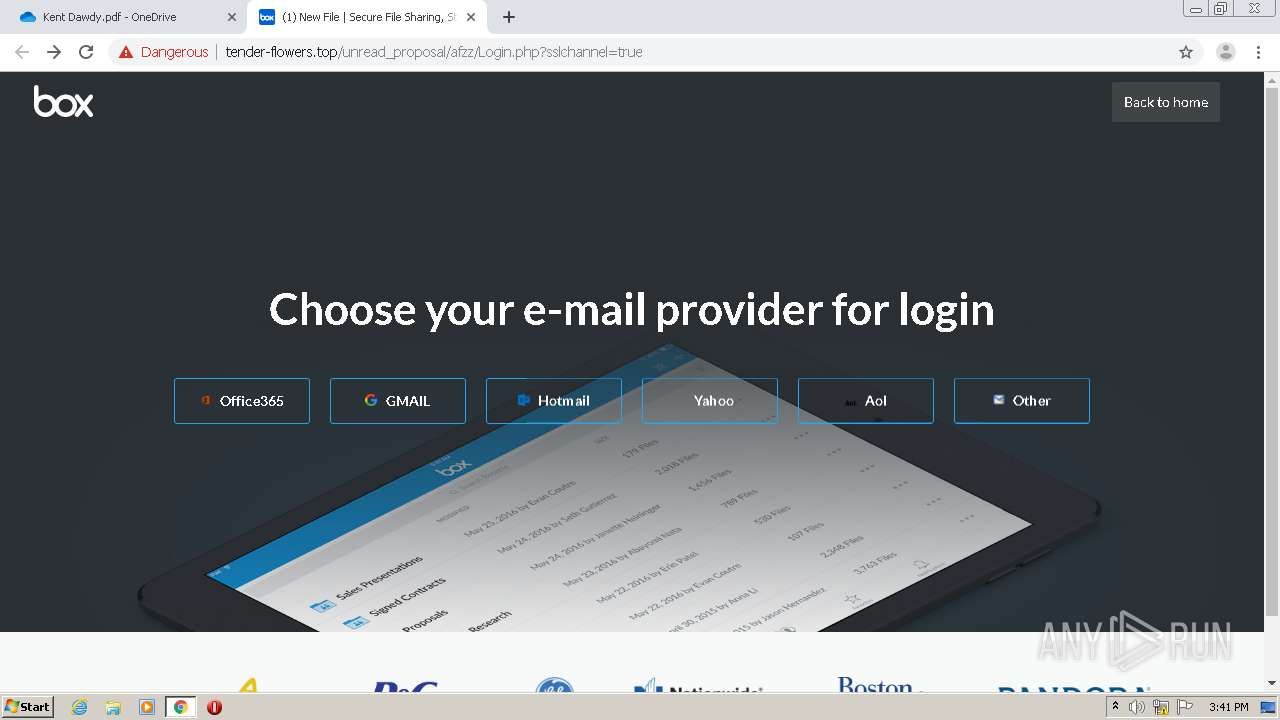
1520 | chrome.exe | GET | 200 | 91.234.99.105:80 | http://tender-flowers.top/unread_proposal/afzz/Office365.php?sslchannel=true | NL | html | 19.4 Kb | suspicious |
1520 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
1520 | chrome.exe | GET | 200 | 91.234.99.105:80 | http://tender-flowers.top/unread_proposal/afzz/assets/css/css.css | NL | text | 4.48 Kb | suspicious |
1520 | chrome.exe | GET | 200 | 91.234.99.105:80 | http://tender-flowers.top/unread_proposal/afzz/assets/css/css_yXMMnLSSpPunfPzrxqTY5Fxi0thyZrjewLEjqduzimc.css | NL | text | 7.06 Kb | suspicious |
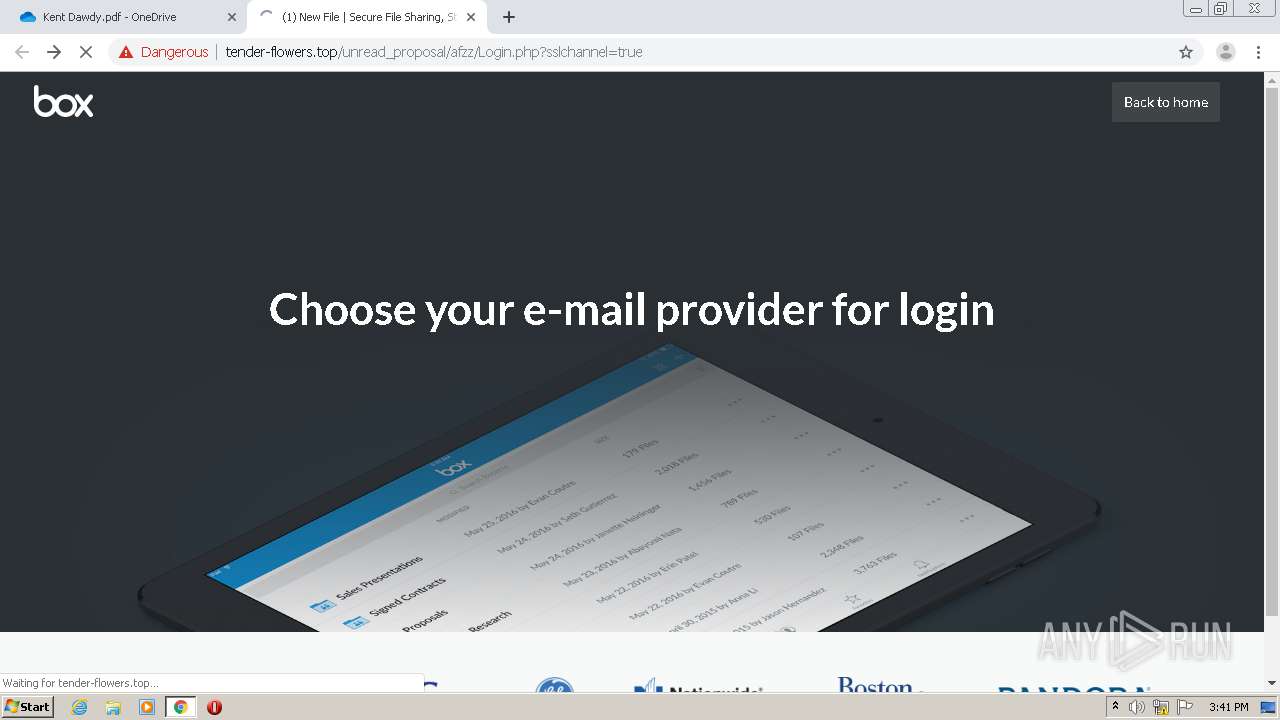
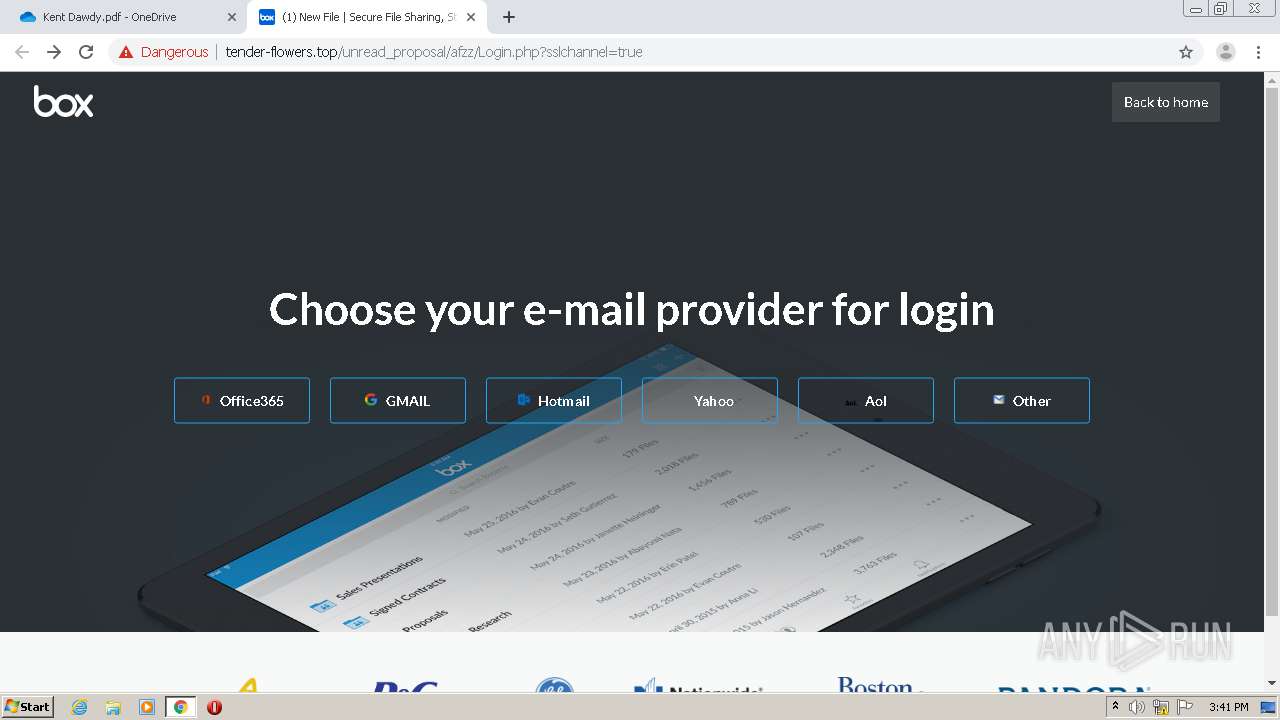
1520 | chrome.exe | GET | 200 | 91.234.99.105:80 | http://tender-flowers.top/unread_proposal/afzz/Login.php?sslchannel=true | NL | html | 8.22 Kb | suspicious |
1520 | chrome.exe | GET | 200 | 91.234.99.105:80 | http://tender-flowers.top/unread_proposal/afzz/assets/img/GE.png | NL | image | 5.02 Kb | suspicious |
1520 | chrome.exe | GET | 200 | 91.234.99.105:80 | http://tender-flowers.top/unread_proposal/afzz/ | NL | html | 113 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1520 | chrome.exe | 216.58.212.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1520 | chrome.exe | 13.107.42.13:443 | onedrive.live.com | Microsoft Corporation | US | malicious |
1520 | chrome.exe | 172.217.16.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1520 | chrome.exe | 40.90.136.180:443 | skyapi.onedrive.live.com | Microsoft Corporation | US | whitelisted |
1520 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
1520 | chrome.exe | 40.77.226.250:443 | web.vortex.data.microsoft.com | Microsoft Corporation | IE | whitelisted |
1520 | chrome.exe | 13.107.42.12:443 | api.onedrive.com | Microsoft Corporation | US | suspicious |
1520 | chrome.exe | 54.76.175.152:443 | dpm.demdex.net | Amazon.com, Inc. | IE | unknown |
1520 | chrome.exe | 172.217.18.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
1520 | chrome.exe | 216.58.207.38:443 | ad.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
onedrive.live.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
static2.sharepointonline.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
spoprod-a.akamaihd.net |
| whitelisted |
skyapi.onedrive.live.com |
| shared |
browser.pipe.aria.microsoft.com |
| whitelisted |
shellprod.msocdn.com |
| whitelisted |
shell.cdn.office.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
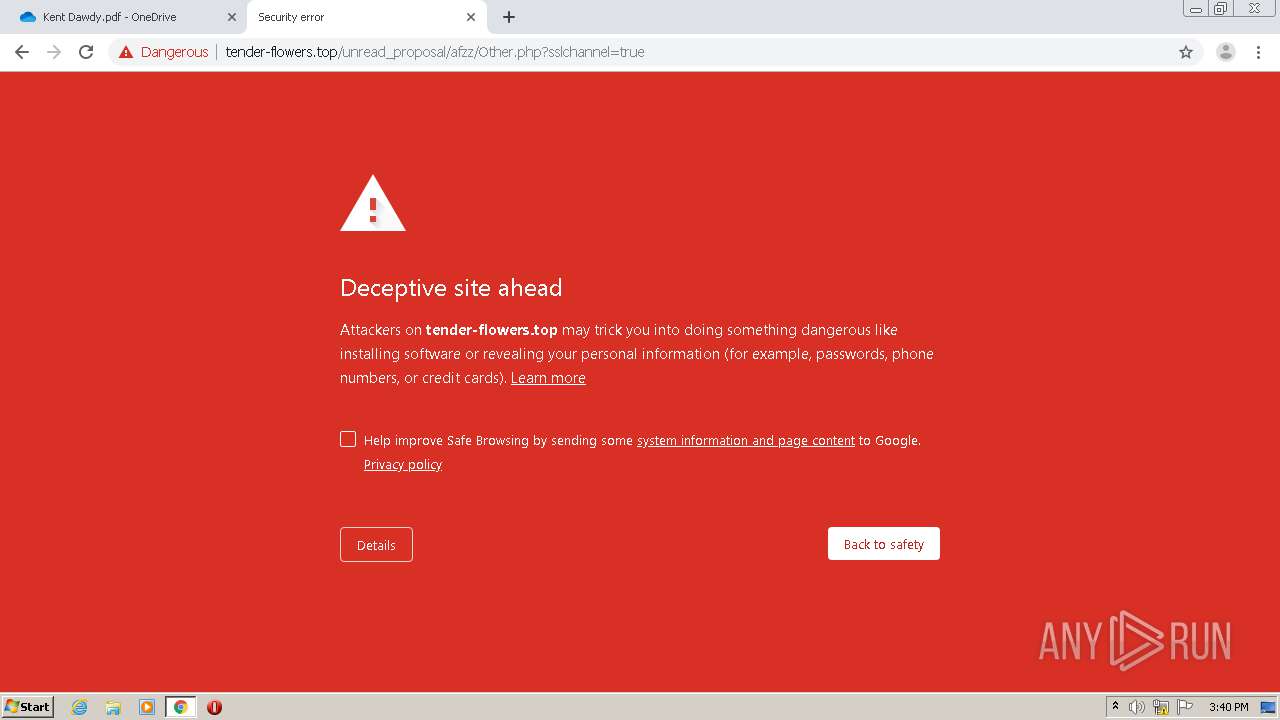
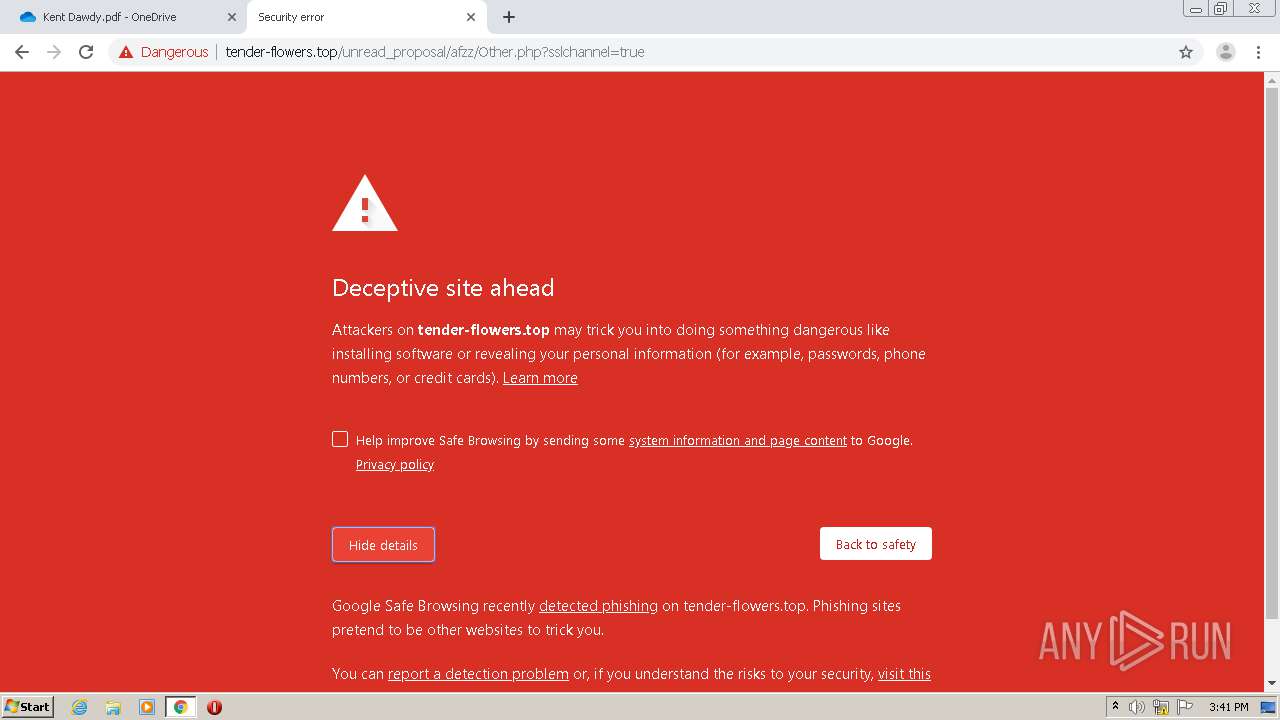
1040 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
1520 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
1520 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Microsoft Live Phishing Landing |
1520 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Microsoft Account Phishing Landing M1 2018-04-19 |
1520 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Microsoft Account Phishing Landing 2018-08-07 |
1520 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
1520 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
1520 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Microsoft Live Phishing Landing |
1520 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Microsoft Account Phishing Landing M1 2018-04-19 |
1520 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Microsoft Account Phishing Landing 2018-08-07 |