| URL: | http://movimientoburofax.eastus.cloudapp.azure.com/ |
| Full analysis: | https://app.any.run/tasks/740122b9-e8ee-4aa4-8901-47b7daa4ad61 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 12:32:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8F54ADBE83C29EE2AD675F7F227537EA |
| SHA1: | E0F10A85CBAC8D75B70EF195BCCF4CD667C21D07 |
| SHA256: | 4FE8023DD60868DD27504F5AA33B9A54EEC3B9681B7436E9307E0E4B5E5D17BE |
| SSDEEP: | 3:N1KTOBlhaDESDLVU8h2Cc:C7DE75 |
MALICIOUS
Application was dropped or rewritten from another process
- 5ESvWhRg.exe (PID: 2804)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2840)
- msiexec.exe (PID: 2432)
- MsiExec.exe (PID: 2656)
Reads Internet Cache Settings
- MsiExec.exe (PID: 2656)
Changes the autorun value in the registry
- MsiExec.exe (PID: 2656)
Reads Environment values
- 5ESvWhRg.exe (PID: 2804)
INFO
Reads the hosts file
- chrome.exe (PID: 2964)
- chrome.exe (PID: 2468)
Reads Internet Cache Settings
- chrome.exe (PID: 2964)
- iexplore.exe (PID: 4088)
Manual execution by user
- iexplore.exe (PID: 4088)
- msiexec.exe (PID: 3840)
Application launched itself
- iexplore.exe (PID: 4088)
- msiexec.exe (PID: 2432)
- chrome.exe (PID: 2964)
Changes internet zones settings
- iexplore.exe (PID: 4088)
Reads internet explorer settings
- iexplore.exe (PID: 3556)
- iexplore.exe (PID: 3128)
Creates files in the program directory
- MsiExec.exe (PID: 2656)
Reads settings of System Certificates
- iexplore.exe (PID: 4088)
Changes settings of System certificates
- iexplore.exe (PID: 4088)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
22
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,7432634488394119122,2097699356686715774,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17554547277650685763 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,7432634488394119122,2097699356686715774,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15329104840013007610 --mojo-platform-channel-handle=3812 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2432 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,7432634488394119122,2097699356686715774,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3251889532167155826 --mojo-platform-channel-handle=1556 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2656 | C:\Windows\system32\MsiExec.exe -Embedding D9A8D7F4F3A7A4B65303CEDD4ED9AD49 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2804 | "C:\Programdata\mhedxmNVOimedi\5ESvWhRg.exe" "C:\Programdata\mhedxmNVOimedi\mE5Srfaf.jP" "C:\Programdata\mhedxmNVOimedi\gSbVRFGd.2f" | C:\Programdata\mhedxmNVOimedi\5ESvWhRg.exe | — | MsiExec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: AutoHotkey Unicode 32-bit Exit code: 0 Version: 1.1.33.02 Modules
| |||||||||||||||
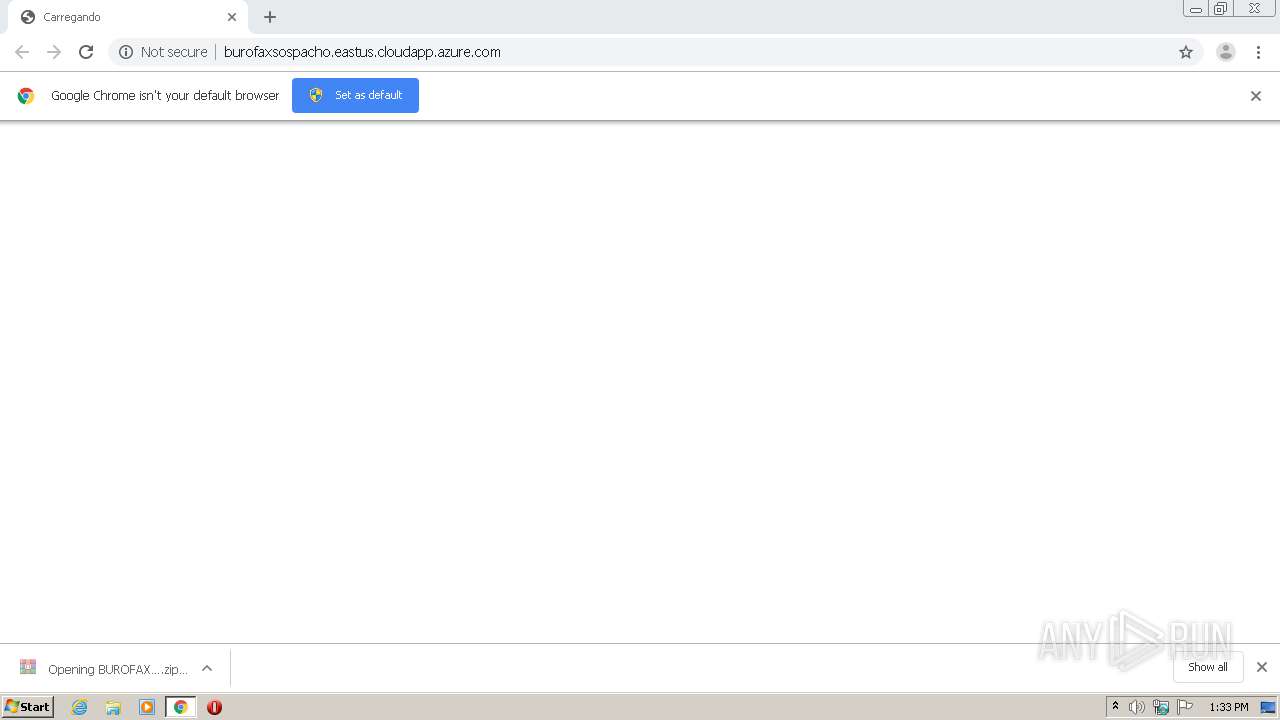
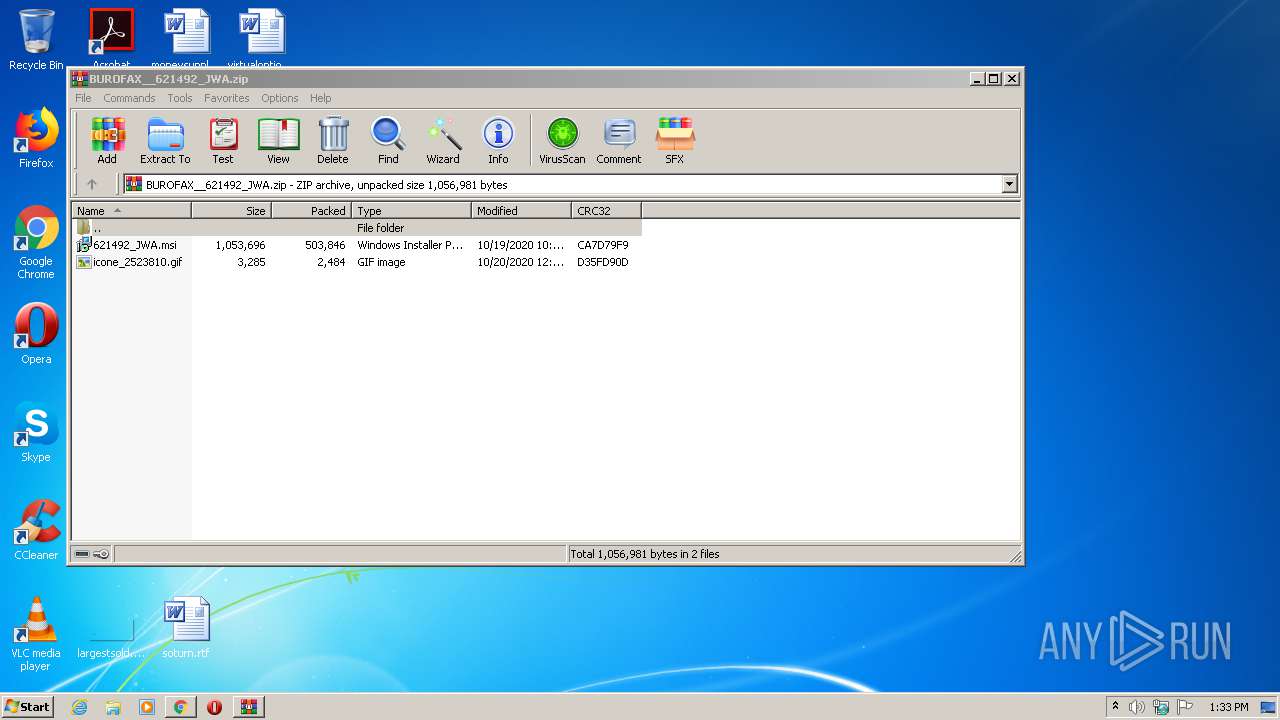
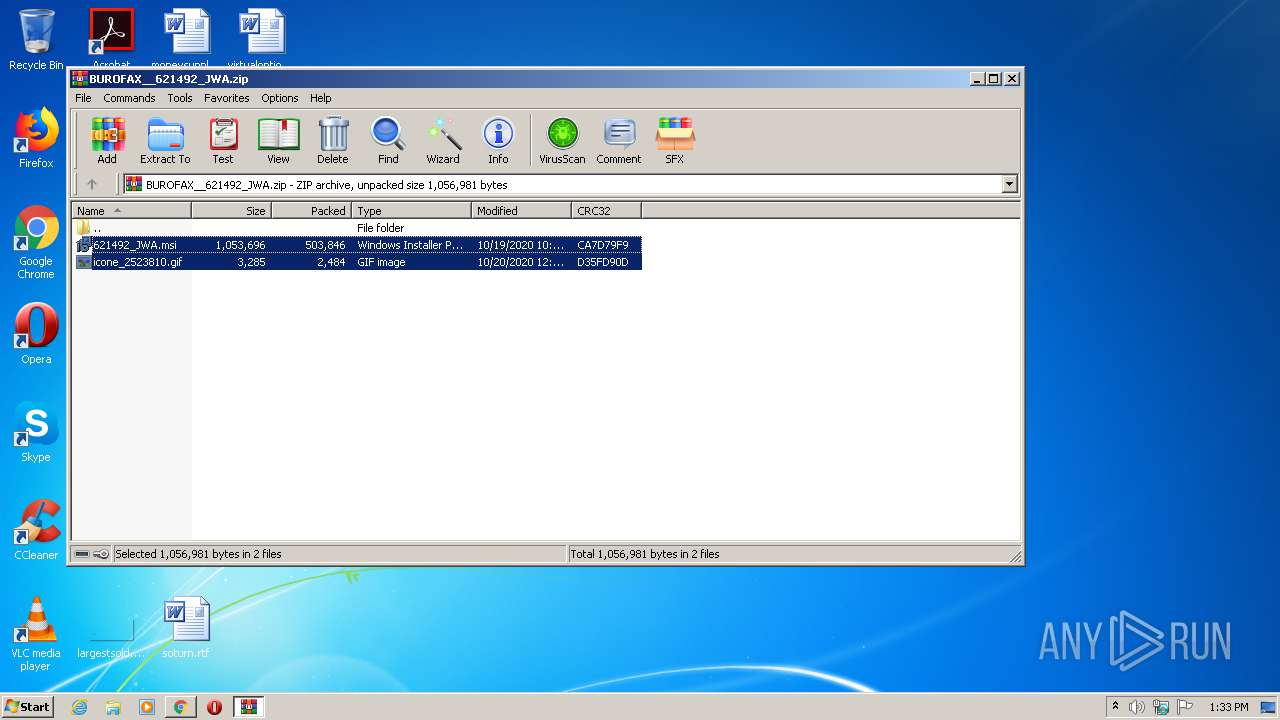
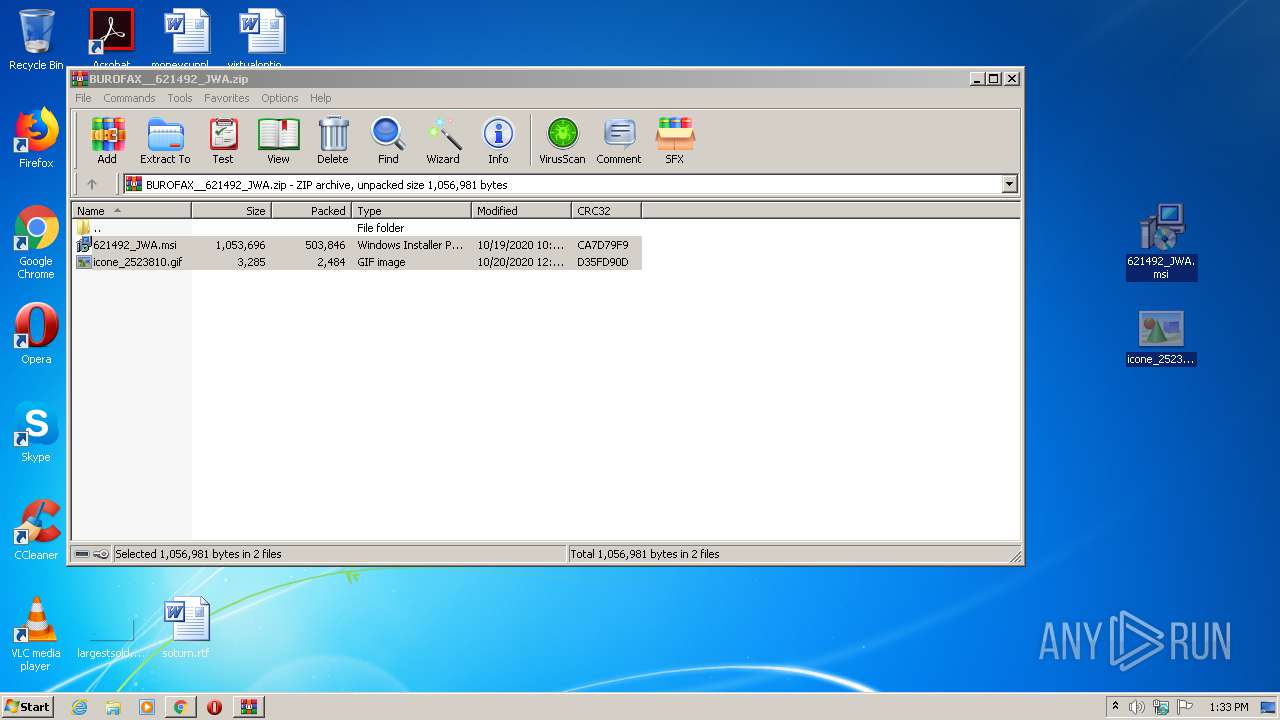
| 2840 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\BUROFAX__621492_JWA.zip" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,7432634488394119122,2097699356686715774,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16656760932666322462 --mojo-platform-channel-handle=972 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,7432634488394119122,2097699356686715774,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6117820725522548790 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,7432634488394119122,2097699356686715774,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12154057730546547586 --mojo-platform-channel-handle=3608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 796
Read events
2 568
Write events
210
Delete events
18
Modification events
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2964-13247670783250500 |
Value: 259 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
5
Suspicious files
18
Text files
73
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8ED900-B94.pma | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b57f21e9-d9b2-4f4d-acab-d1a82a64db6a.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF165132.TMP | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF165151.TMP | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF16518f.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
22
DNS requests
19
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2656 | MsiExec.exe | GET | 200 | 52.152.133.113:80 | http://sorprenderse.eastus.cloudapp.azure.com/ADERF32.zip | US | compressed | 7.82 Mb | malicious |
4088 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2468 | chrome.exe | GET | 404 | 52.146.13.17:80 | http://movimientoburofax.eastus.cloudapp.azure.com/favicon.ico | US | html | 305 b | unknown |
2468 | chrome.exe | GET | 200 | 52.146.13.17:80 | http://movimientoburofax.eastus.cloudapp.azure.com/ | US | html | 335 b | unknown |
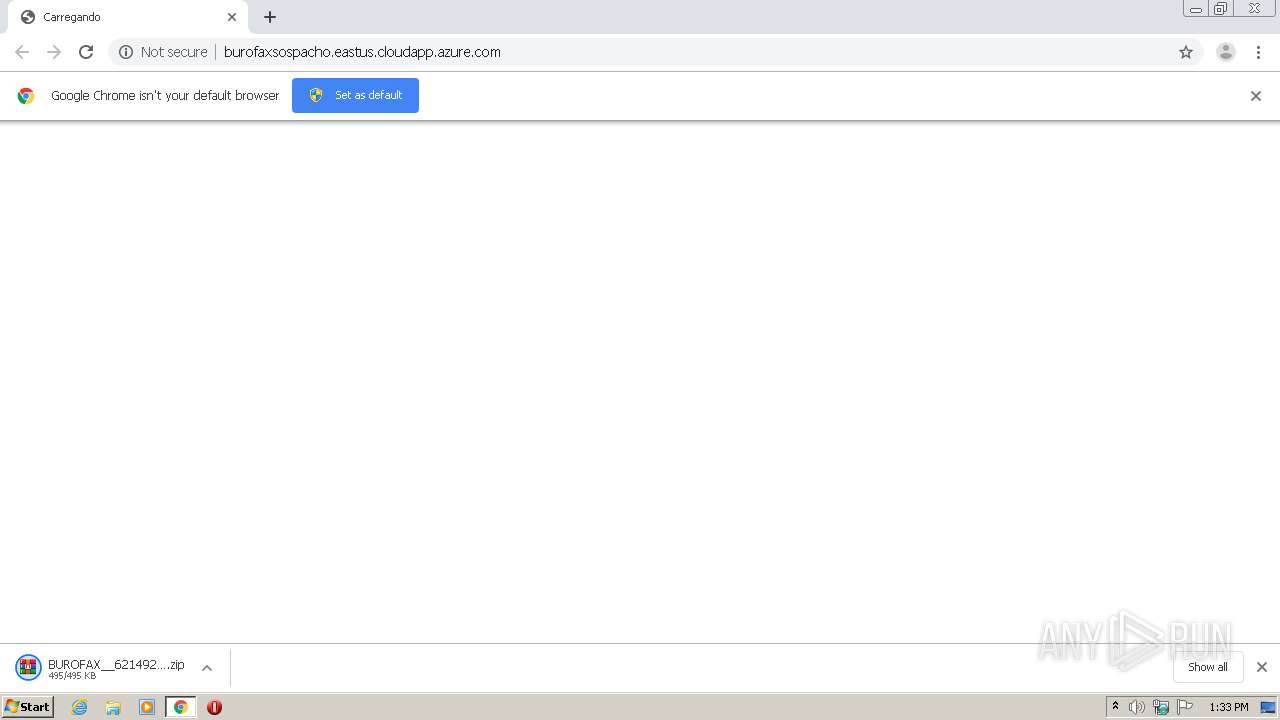
2468 | chrome.exe | GET | 404 | 138.91.116.40:80 | http://burofaxsospacho.eastus.cloudapp.azure.com/favicon.ico | US | html | 303 b | unknown |
2468 | chrome.exe | POST | 200 | 52.146.13.17:80 | http://movimientoburofax.eastus.cloudapp.azure.com/arquivo.php | US | html | 187 b | unknown |
2656 | MsiExec.exe | GET | 302 | 52.152.133.113:80 | http://sorprenderse.eastus.cloudapp.azure.com/32bits.php | US | html | 603 b | malicious |
4088 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
4088 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2468 | chrome.exe | POST | 200 | 138.91.116.40:80 | http://burofaxsospacho.eastus.cloudapp.azure.com/arquivo.php | US | compressed | 494 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 52.146.13.17:80 | movimientoburofax.eastus.cloudapp.azure.com | Microsoft Corporation | US | unknown |
2468 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2468 | chrome.exe | 52.146.13.17:80 | movimientoburofax.eastus.cloudapp.azure.com | Microsoft Corporation | US | unknown |
2468 | chrome.exe | 138.91.116.40:80 | burofaxsospacho.eastus.cloudapp.azure.com | Microsoft Corporation | US | unknown |
2468 | chrome.exe | 172.217.18.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
2468 | chrome.exe | 216.58.205.238:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2468 | chrome.exe | 172.217.23.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
4088 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2656 | MsiExec.exe | 52.152.133.113:80 | sorprenderse.eastus.cloudapp.azure.com | Microsoft Corporation | US | malicious |
2468 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
movimientoburofax.eastus.cloudapp.azure.com |
| unknown |
accounts.google.com |
| shared |
burofaxsospacho.eastus.cloudapp.azure.com |
| unknown |
clients2.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
sorprenderse.eastus.cloudapp.azure.com |
| malicious |
Threats
2 ETPRO signatures available at the full report