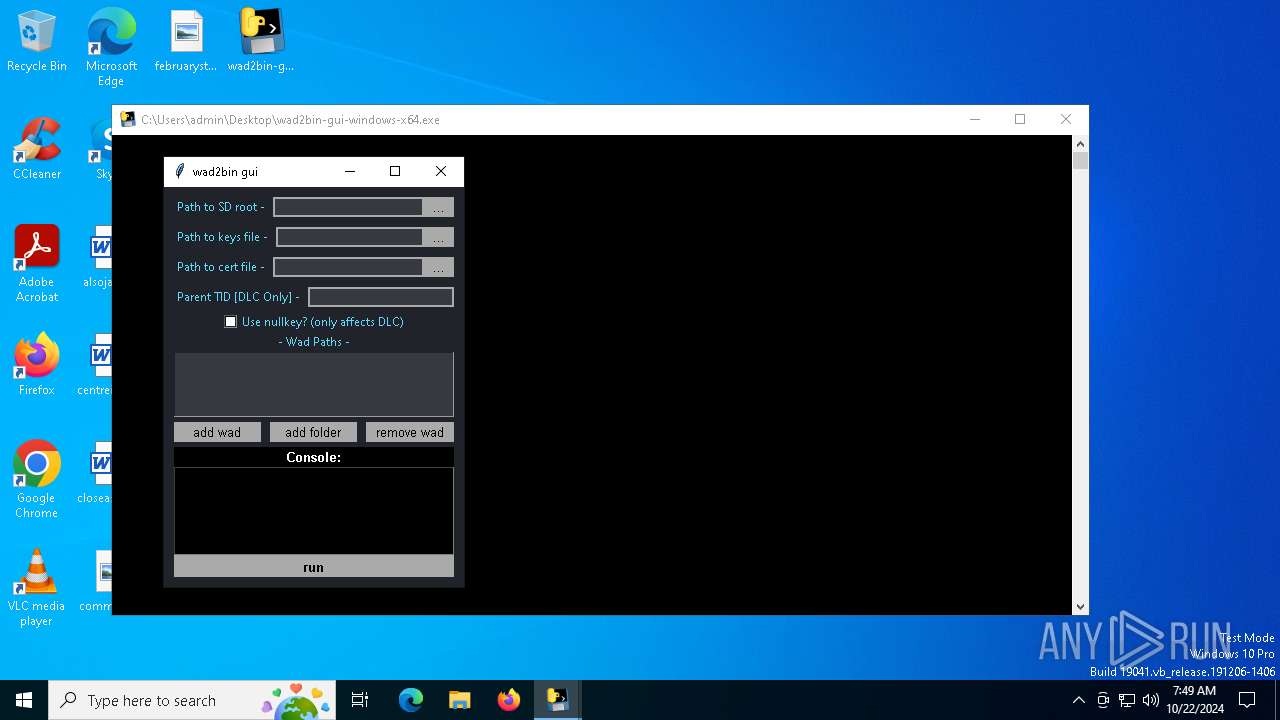
| File name: | wad2bin-gui-windows-x64.exe |
| Full analysis: | https://app.any.run/tasks/41012272-480b-4853-bdd5-16b06177bb7c |
| Verdict: | Malicious activity |
| Analysis date: | October 22, 2024, 07:48:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | CE5A8DF978ADBAA3F25969E07BE57ED5 |
| SHA1: | 713912C191930C09676767B12318E9A1426A1DA8 |
| SHA256: | 4FCFB0F3529AC95C8B82370B05AEE6EE1035D0925502C69D9614E2B1D18BAEAA |
| SSDEEP: | 98304:4tO4kJbR+NMHsHQPuCGrHWqzVSwtGLLjoMiuyTreRplC9O4qQWUdfKaeMwQ3y8lO:e+b3EcaAP9BcMXD7N |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process drops C-runtime libraries
- wad2bin-gui-windows-x64.exe (PID: 5284)
Process drops python dynamic module
- wad2bin-gui-windows-x64.exe (PID: 5284)
Executable content was dropped or overwritten
- wad2bin-gui-windows-x64.exe (PID: 5284)
Process drops legitimate windows executable
- wad2bin-gui-windows-x64.exe (PID: 5284)
Application launched itself
- wad2bin-gui-windows-x64.exe (PID: 5284)
INFO
Checks supported languages
- wad2bin-gui-windows-x64.exe (PID: 5284)
Reads the computer name
- wad2bin-gui-windows-x64.exe (PID: 5284)
Create files in a temporary directory
- wad2bin-gui-windows-x64.exe (PID: 5284)
PyInstaller has been detected (YARA)
- wad2bin-gui-windows-x64.exe (PID: 5284)
- wad2bin-gui-windows-x64.exe (PID: 7148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2021:04:15 05:29:45+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.28 |
| CodeSize: | 137728 |
| InitializedDataSize: | 141312 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8864 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
125
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5284 | "C:\Users\admin\Desktop\wad2bin-gui-windows-x64.exe" | C:\Users\admin\Desktop\wad2bin-gui-windows-x64.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6736 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | wad2bin-gui-windows-x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7148 | "C:\Users\admin\Desktop\wad2bin-gui-windows-x64.exe" | C:\Users\admin\Desktop\wad2bin-gui-windows-x64.exe | wad2bin-gui-windows-x64.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
218
Read events
218
Write events
0
Delete events
0
Modification events
Executable files
62
Suspicious files
3
Text files
916
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5284 | wad2bin-gui-windows-x64.exe | C:\Users\admin\AppData\Local\Temp\_MEI52842\_socket.pyd | executable | |
MD5:4827652DE133C83FA1CAE839B361856C | SHA256:87832A3B89E2ADA8F704A8F066013660D591D9CE01CE901CC57A3B973F0858BA | |||
| 5284 | wad2bin-gui-windows-x64.exe | C:\Users\admin\AppData\Local\Temp\_MEI52842\_asyncio.pyd | executable | |
MD5:0400B1958D0F7AA0D2AD409EA12FFEC7 | SHA256:6E25AA5931F175B971DFD05AAB7A24CEF29EDD8F4B524341C414D0577C07A200 | |||
| 5284 | wad2bin-gui-windows-x64.exe | C:\Users\admin\AppData\Local\Temp\_MEI52842\_decimal.pyd | executable | |
MD5:A2B554D61E6CF63C6E5BBAFB20AE3359 | SHA256:30EEA56A4D1DD78F9D65FCB6168AB189CFA8098C38AAD47EE770756A056749CA | |||
| 5284 | wad2bin-gui-windows-x64.exe | C:\Users\admin\AppData\Local\Temp\_MEI52842\_bz2.pyd | executable | |
MD5:A49C5F406456B79254EB65D015B81088 | SHA256:CE4EF8ED1E72C1D3A6082D500A17A009EB6E8ED15022BF3B68A22291858FECED | |||
| 5284 | wad2bin-gui-windows-x64.exe | C:\Users\admin\AppData\Local\Temp\_MEI52842\_overlapped.pyd | executable | |
MD5:7D5BB2A3E4FBCEADDFEEF929A21E610C | SHA256:5F92C163B9FE6ABB0F8B106A972F6A86F84271B2E32C67F95737387C85719837 | |||
| 5284 | wad2bin-gui-windows-x64.exe | C:\Users\admin\AppData\Local\Temp\_MEI52842\_hashlib.pyd | executable | |
MD5:5E5AF52F42EAF007E3AC73FD2211F048 | SHA256:A30CF1A40E0B09610E34BE187F1396AC5A44DCFB27BC7FF9B450D1318B694C1B | |||
| 5284 | wad2bin-gui-windows-x64.exe | C:\Users\admin\AppData\Local\Temp\_MEI52842\_lzma.pyd | executable | |
MD5:CF9FD17B1706F3044A8F74F6D398D5F1 | SHA256:9209CCC60115727B192BF7771551040CA6FDD50F9BF8C3D2EACBFD424E8245E4 | |||
| 5284 | wad2bin-gui-windows-x64.exe | C:\Users\admin\AppData\Local\Temp\_MEI52842\_ctypes.pyd | executable | |
MD5:291A0A9B63BAE00A4222A6DF71A22023 | SHA256:820E840759EED12E19F3C485FD819B065B49D9DC704AE3599A63077416D63324 | |||
| 5284 | wad2bin-gui-windows-x64.exe | C:\Users\admin\AppData\Local\Temp\_MEI52842\VCRUNTIME140.dll | executable | |
MD5:4A365FFDBDE27954E768358F4A4CE82E | SHA256:6A0850419432735A98E56857D5CFCE97E9D58A947A9863CA6AFADD1C7BCAB27C | |||
| 5284 | wad2bin-gui-windows-x64.exe | C:\Users\admin\AppData\Local\Temp\_MEI52842\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:32E55AFF4D5256219823A53F82B83FEC | SHA256:81641164DC5B8C264C4C71602895957E196708D20D86EC6C92906AC4908EA904 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
27
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3952 | RUXIMICS.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3952 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3952 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.209.158:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
3952 | RUXIMICS.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |