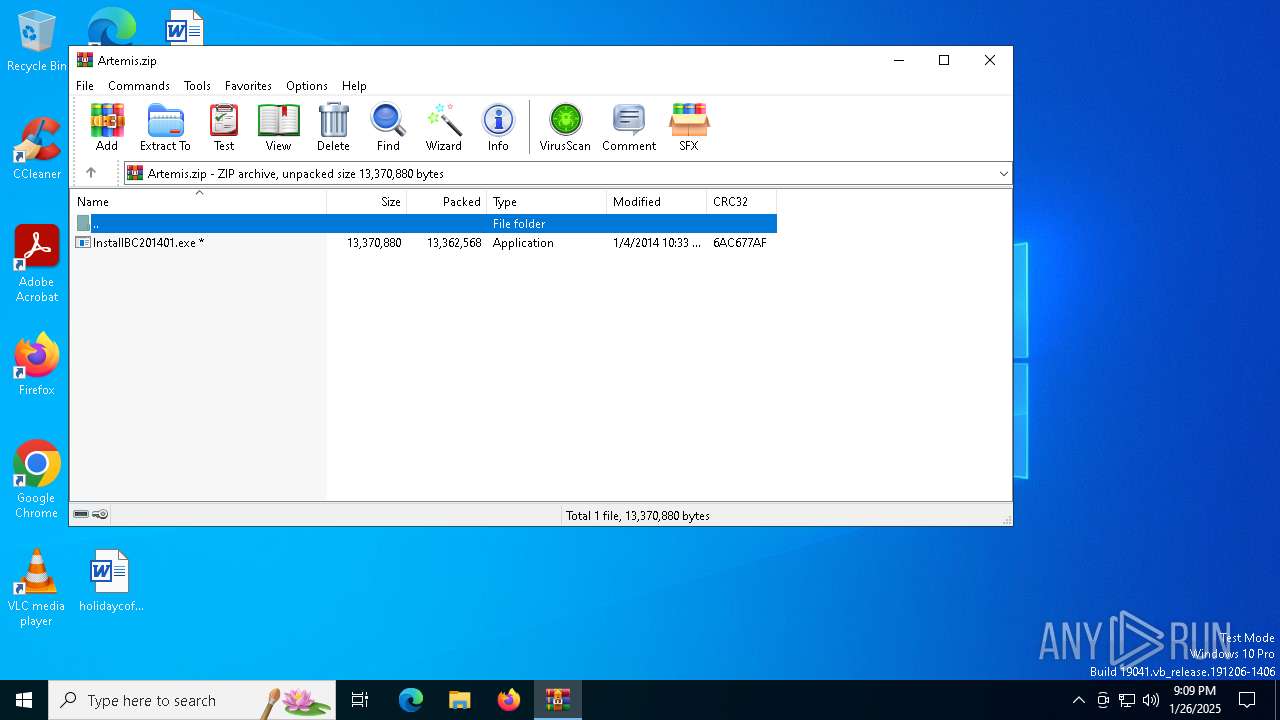
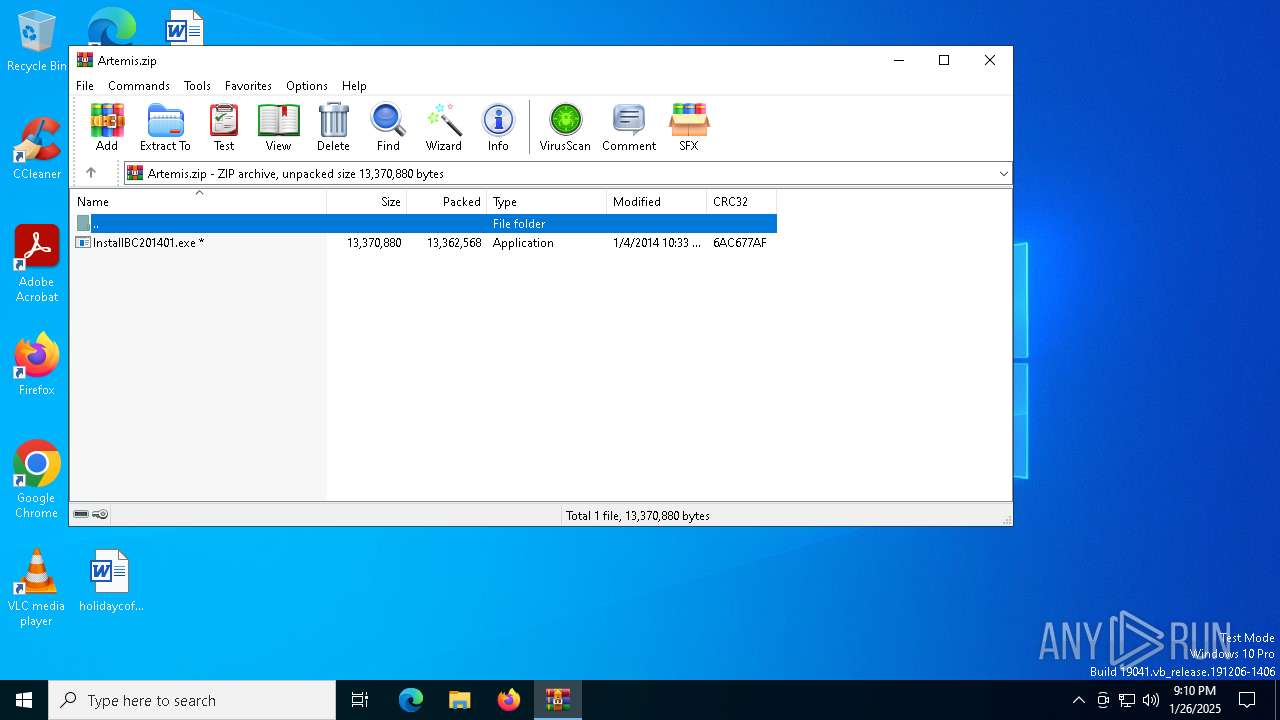
| File name: | Artemis.zip |
| Full analysis: | https://app.any.run/tasks/04dc7baf-6ca6-4ef3-a648-c6e46373ca57 |
| Verdict: | Malicious activity |
| Analysis date: | January 26, 2025, 21:09:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 2599847A7535908F7C0DB0A6B16DBF0E |
| SHA1: | 702EFBA00D45134BF229D352280F7BA6274D7282 |
| SHA256: | 4FCE8D0D64CCEA6E75440354FB309D72E9C91C4D9F344B543952FB18FDD18C4F |
| SSDEEP: | 393216:6rGzQvxdnEOSvGon7f527yj/yuvCGR3O3v:WGMvx9EpvGAdZjxv53O3v |
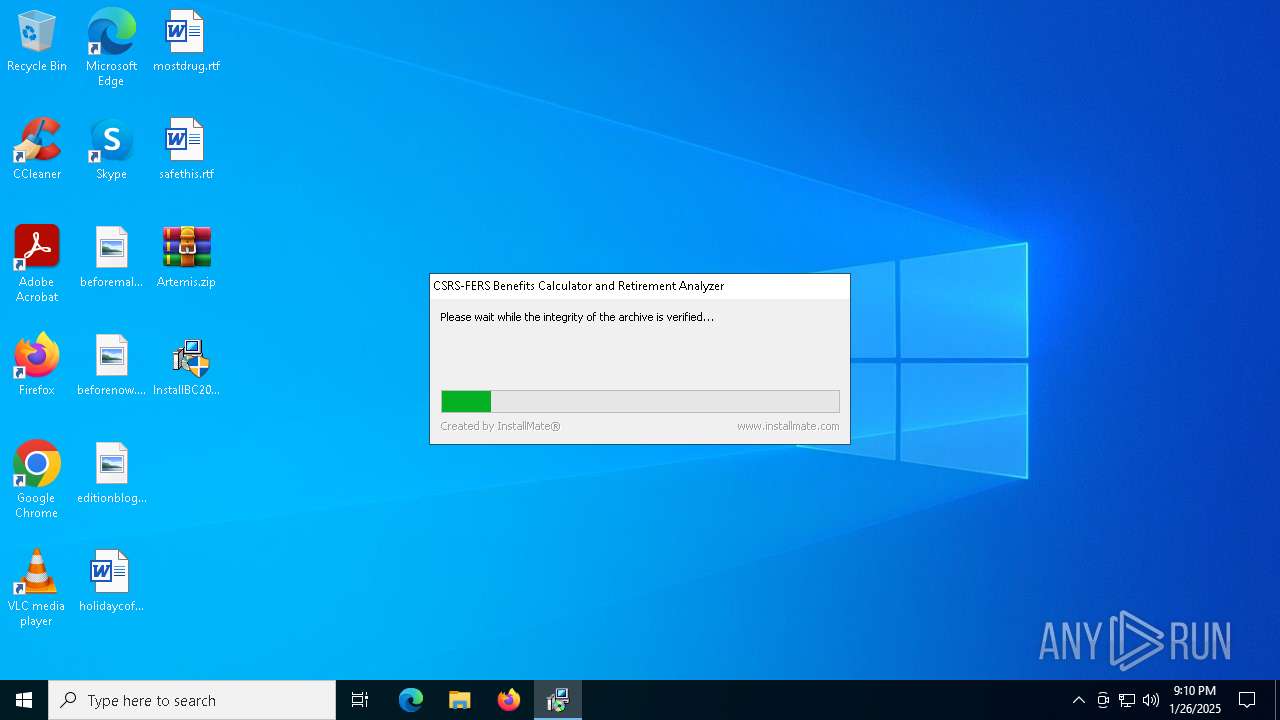
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2800)
SUSPICIOUS
Executable content was dropped or overwritten
- InstallBC201401.exe (PID: 4968)
The process creates files with name similar to system file names
- InstallBC201401.exe (PID: 4968)
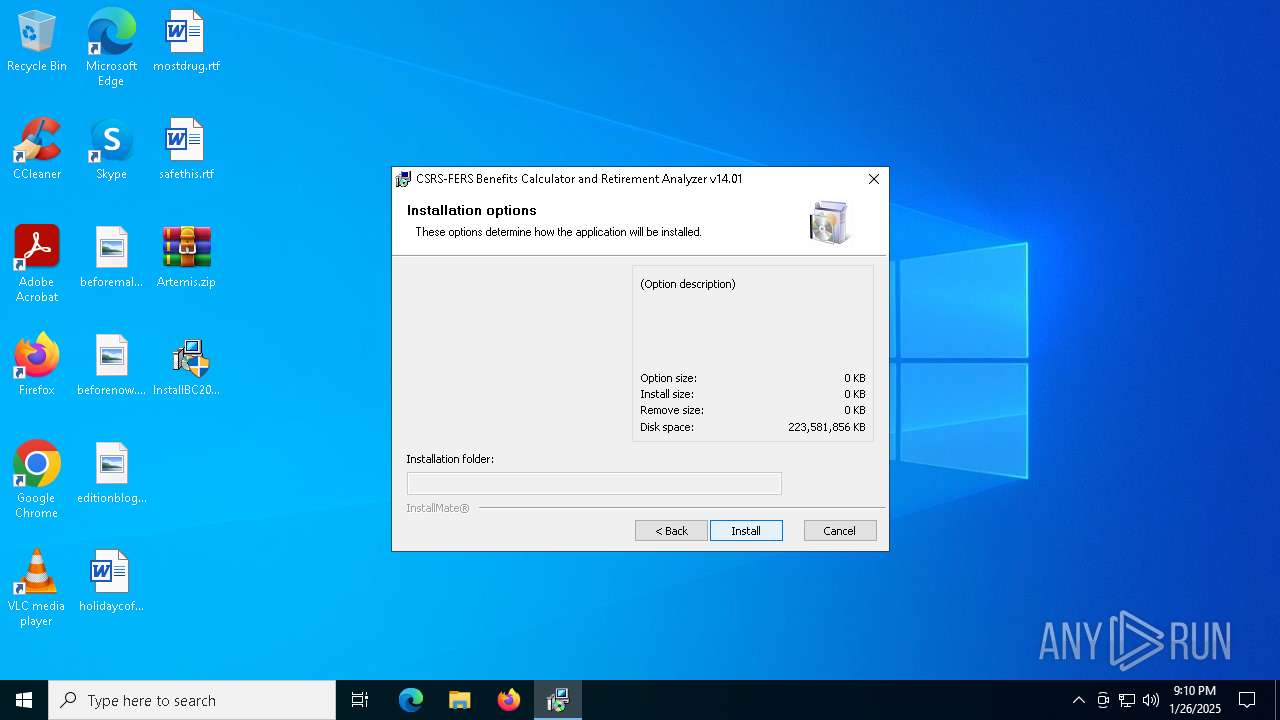
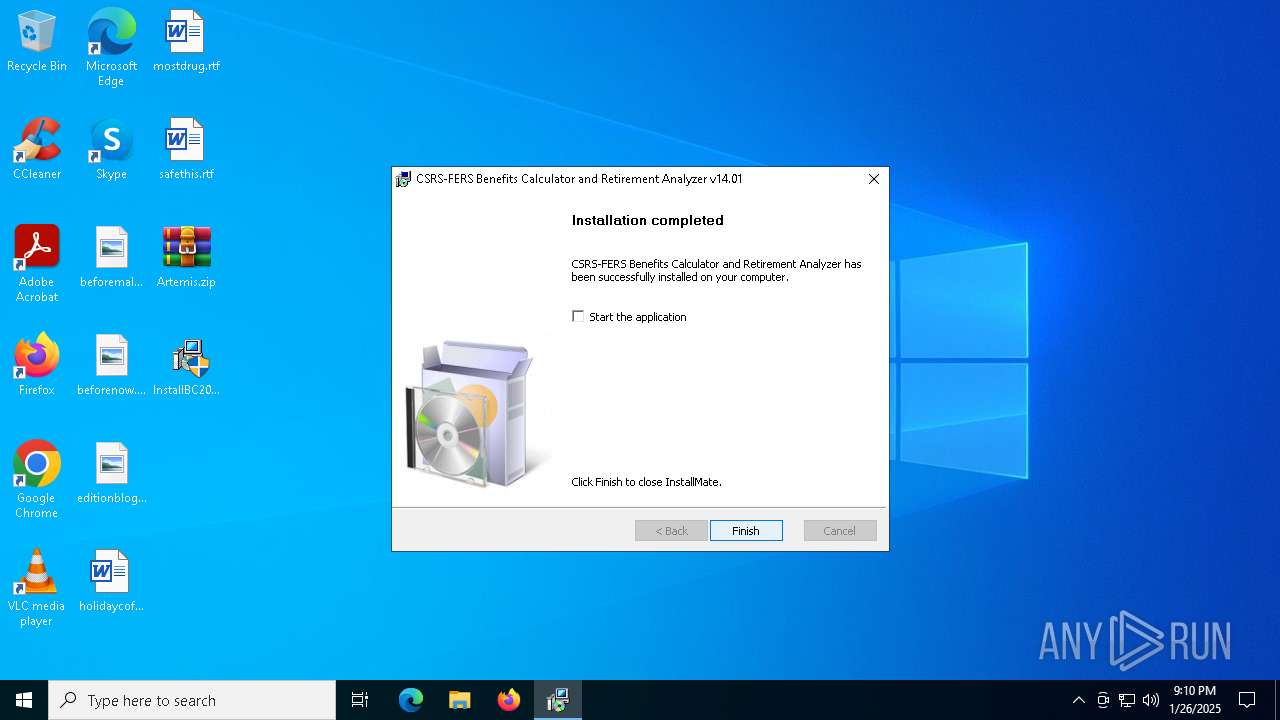
Creates a software uninstall entry
- InstallBC201401.exe (PID: 4968)
Process drops legitimate windows executable
- InstallBC201401.exe (PID: 4968)
INFO
Create files in a temporary directory
- InstallBC201401.exe (PID: 4968)
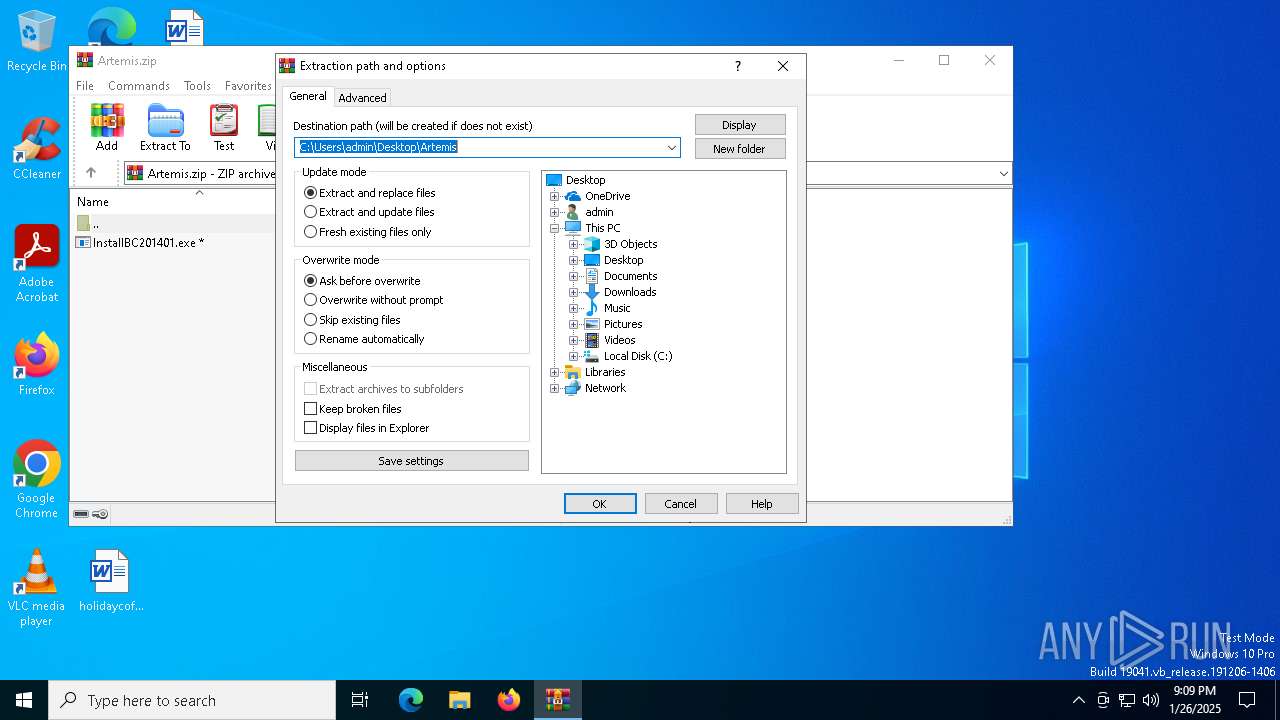
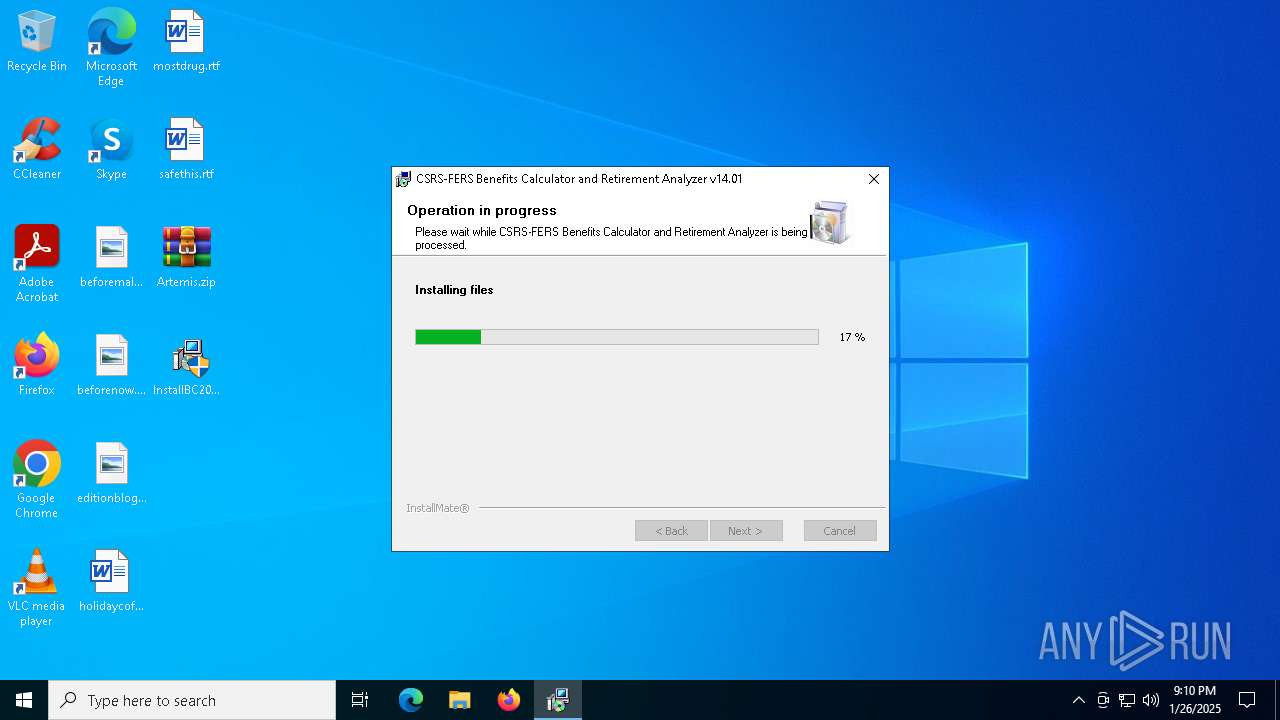
Manual execution by a user
- InstallBC201401.exe (PID: 2756)
- InstallBC201401.exe (PID: 4968)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2800)
Reads Environment values
- InstallBC201401.exe (PID: 4968)
Reads the computer name
- InstallBC201401.exe (PID: 4968)
Creates files in the program directory
- InstallBC201401.exe (PID: 4968)
Checks supported languages
- InstallBC201401.exe (PID: 4968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2014:01:04 22:33:38 |
| ZipCRC: | 0x6ac677af |
| ZipCompressedSize: | 13362568 |
| ZipUncompressedSize: | 13370880 |
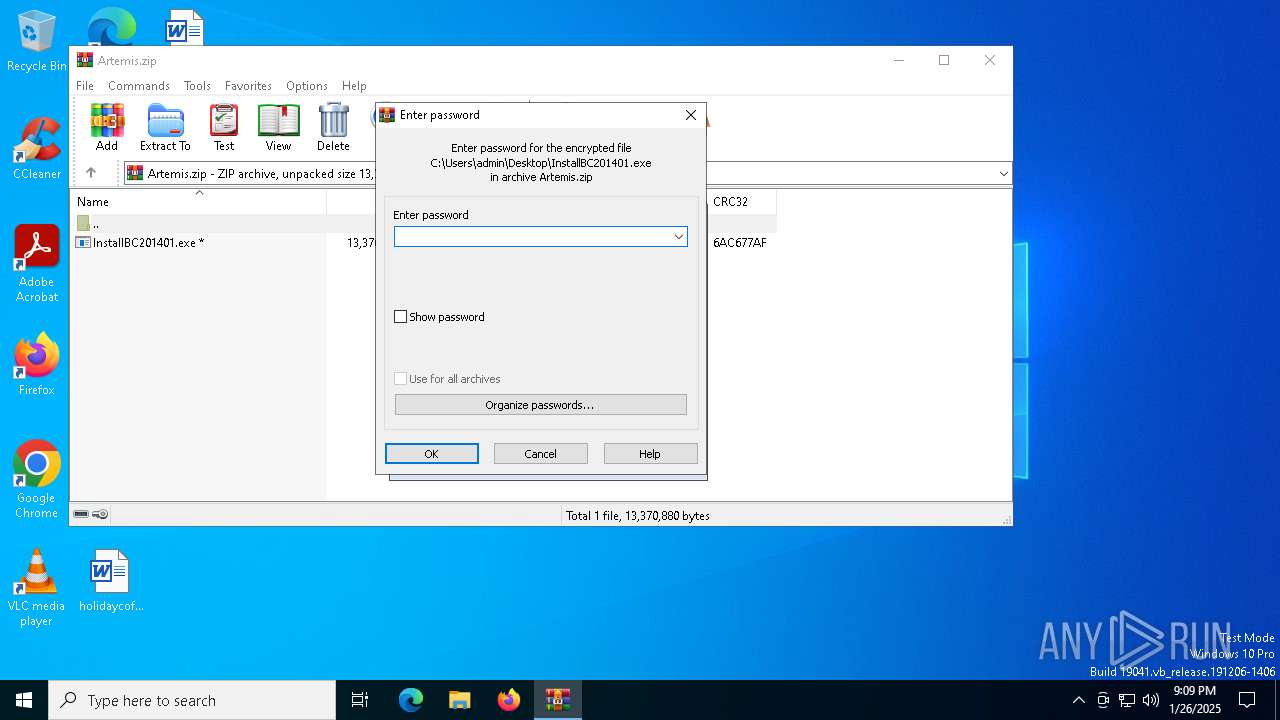
| ZipFileName: | InstallBC201401.exe |
Total processes
125
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
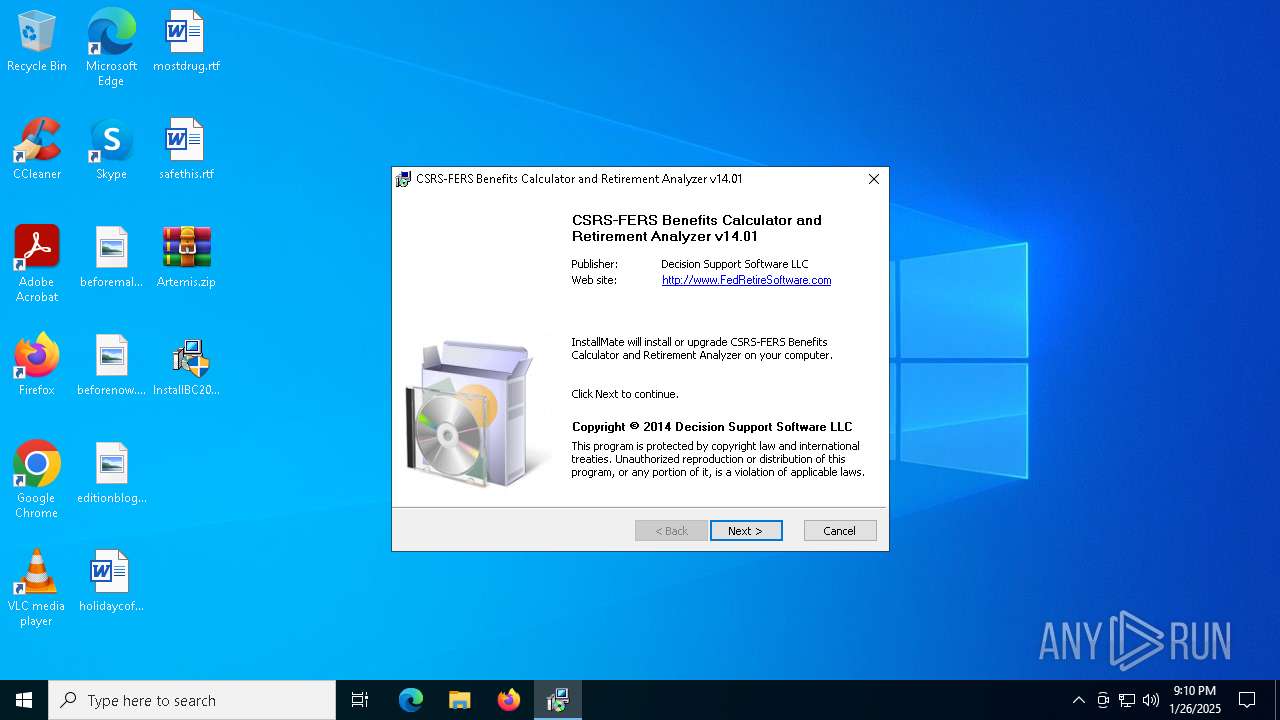
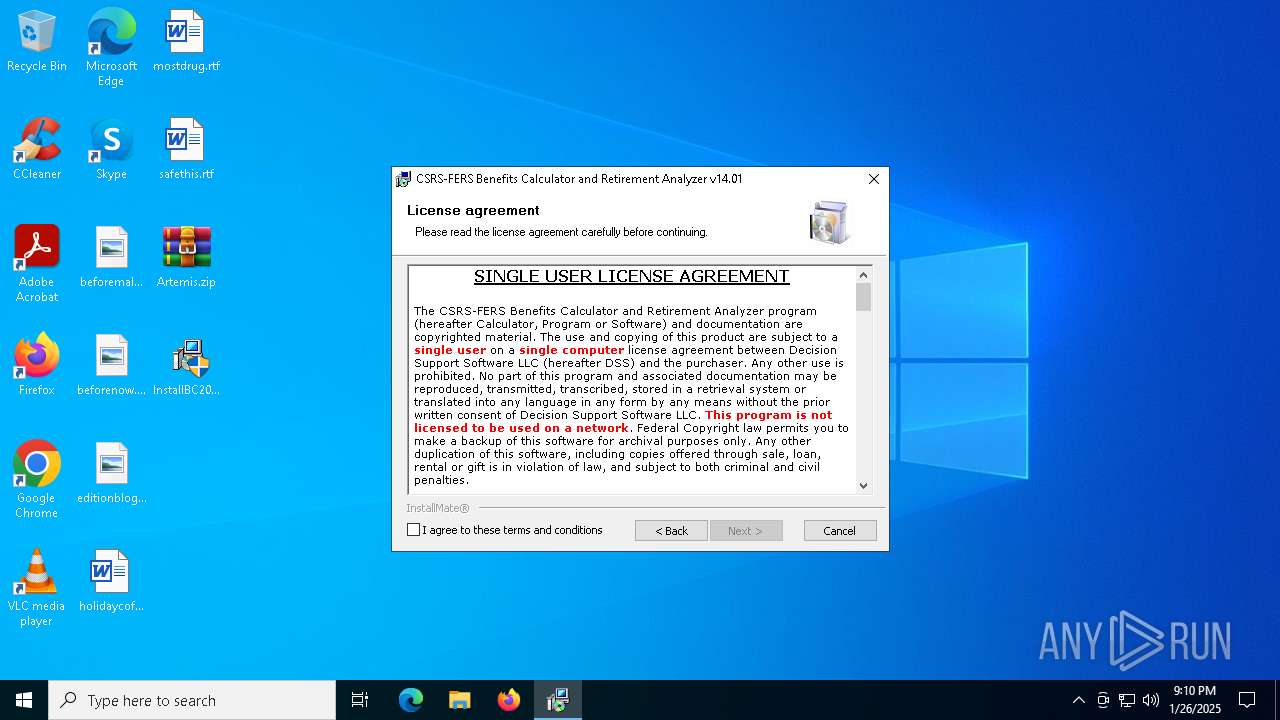
| 2756 | "C:\Users\admin\Desktop\InstallBC201401.exe" | C:\Users\admin\Desktop\InstallBC201401.exe | — | explorer.exe | |||||||||||
User: admin Company: Decision Support Software LLC Integrity Level: MEDIUM Description: Installer for CSRS-FERS Benefits Calculator and Retirement Analy Exit code: 3221226540 Version: 2014.1.4.1230 Modules
| |||||||||||||||
| 2800 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Artemis.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4968 | "C:\Users\admin\Desktop\InstallBC201401.exe" | C:\Users\admin\Desktop\InstallBC201401.exe | explorer.exe | ||||||||||||
User: admin Company: Decision Support Software LLC Integrity Level: HIGH Description: Installer for CSRS-FERS Benefits Calculator and Retirement Analy Exit code: 0 Version: 2014.1.4.1230 Modules
| |||||||||||||||
Total events
2 001
Read events
1 939
Write events
44
Delete events
18
Modification events
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Artemis.zip | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (2800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
9
Suspicious files
2
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4968 | InstallBC201401.exe | C:\Users\admin\AppData\Local\Temp\Tsu524A9B4C.dll | executable | |
MD5:BE4559AB30CA2957A49209F0E786CCC7 | SHA256:F4B52618DB95A41819D623D44995BB7A3F9ACBCB406447CA8ECDDEE8859B94C1 | |||
| 4968 | InstallBC201401.exe | C:\ProgramData\InstallMate\{1E453EA8-BB42-419D-8067-D2477A36B761}\Setup.ico | image | |
MD5:C3926CEF276C0940DADBC8142153CEC9 | SHA256:0EC48E3C1886BC0169A4BC262F012E9B7914E3B440BB0ECC4D8123924ABC9B93 | |||
| 4968 | InstallBC201401.exe | C:\ProgramData\InstallMate\{1E453EA8-BB42-419D-8067-D2477A36B761}\x64\regsvr32.exe | executable | |
MD5:BDD30A19308CB40BACECE6C4636526B6 | SHA256:C5AB5B4C61EAB3D810FD22D9B3CCBC86BDB2ED4D375CCE8488754C917B002986 | |||
| 4968 | InstallBC201401.exe | C:\ProgramData\InstallMate\{1E453EA8-BB42-419D-8067-D2477A36B761}\_Setup.dll | executable | |
MD5:76DDA4C8CE17DF4591C5B9A7363854CE | SHA256:735A433ADE90EAF829FD9C11C4BF6A33DCF712F5451BBAB0B6B9435EDE7B6259 | |||
| 4968 | InstallBC201401.exe | C:\ProgramData\InstallMate\{1E453EA8-BB42-419D-8067-D2477A36B761}\Setup.exe | executable | |
MD5:39C78ACD07821DF6F706F695B5E566AB | SHA256:6C70D20E43651F4F40A39F0F5B9346157C17A9BBB0E2C738C713F545550FE58F | |||
| 4968 | InstallBC201401.exe | C:\Users\admin\AppData\Local\Temp\601D42D0.dat | binary | |
MD5:B0A7109B74113B1A5A532D4BAD90A8B5 | SHA256:77098FBEB11A37C5AAF858B4255BE416FE0847CEBD99331641FAF01038D838C9 | |||
| 4968 | InstallBC201401.exe | C:\Users\admin\AppData\Local\Temp\601D42D0\_Setup.dll | executable | |
MD5:76DDA4C8CE17DF4591C5B9A7363854CE | SHA256:735A433ADE90EAF829FD9C11C4BF6A33DCF712F5451BBAB0B6B9435EDE7B6259 | |||
| 2800 | WinRAR.exe | C:\Users\admin\Desktop\InstallBC201401.exe | executable | |
MD5:CAFF801A280D42DBD1AD6B1266D3C43A | SHA256:834D1DBFAB8330EA5F1844F6E905ED0AC19D1033EE9A9F1122AD2051C56783DC | |||
| 4968 | InstallBC201401.exe | C:\ProgramData\InstallMate\{1E453EA8-BB42-419D-8067-D2477A36B761}\Tsu.dll | executable | |
MD5:BE4559AB30CA2957A49209F0E786CCC7 | SHA256:F4B52618DB95A41819D623D44995BB7A3F9ACBCB406447CA8ECDDEE8859B94C1 | |||
| 4968 | InstallBC201401.exe | C:\ProgramData\InstallMate\{1E453EA8-BB42-419D-8067-D2477A36B761}\Setup.dat | binary | |
MD5:6042C3CF15CB3BBF3582E4FECA7F77C1 | SHA256:34AA49B0CB90247EA2D72B2DC130E82BDBB92FB6221B5FEF7F2ACE861F30F51A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
30
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3296 | svchost.exe | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3296 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4640 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4640 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5684 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3296 | svchost.exe | 23.48.23.177:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3296 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
1176 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |