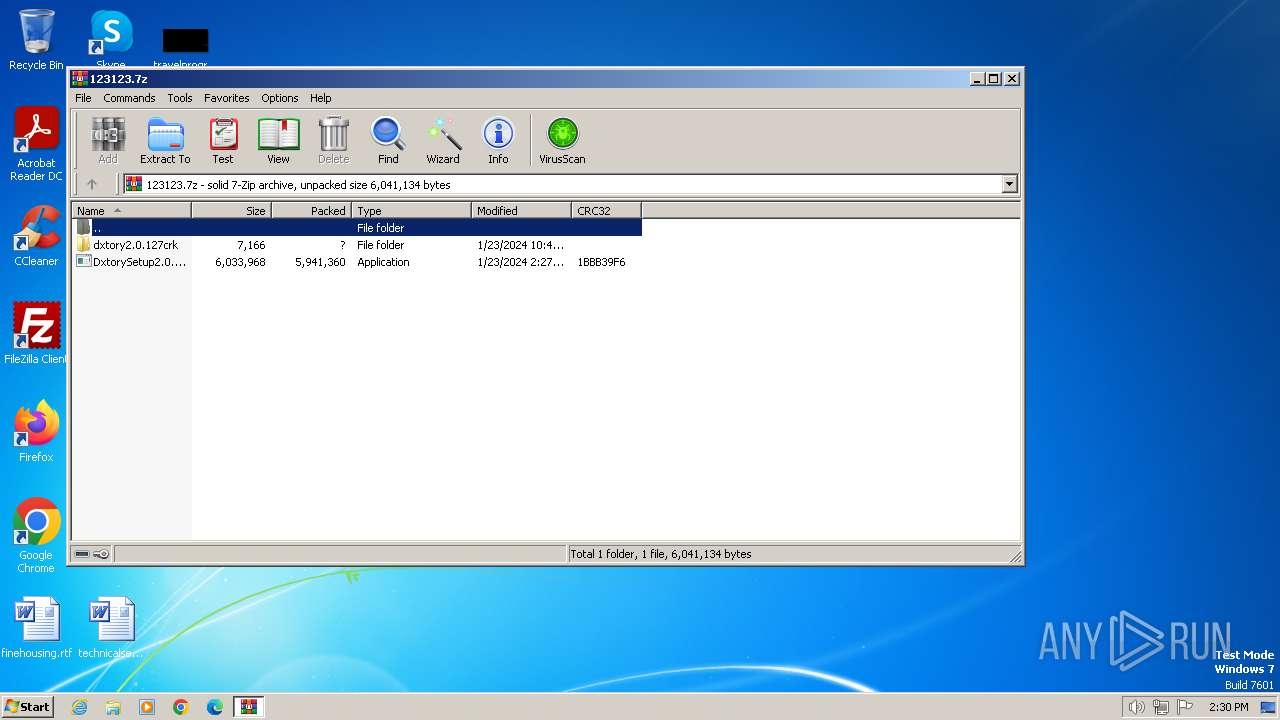
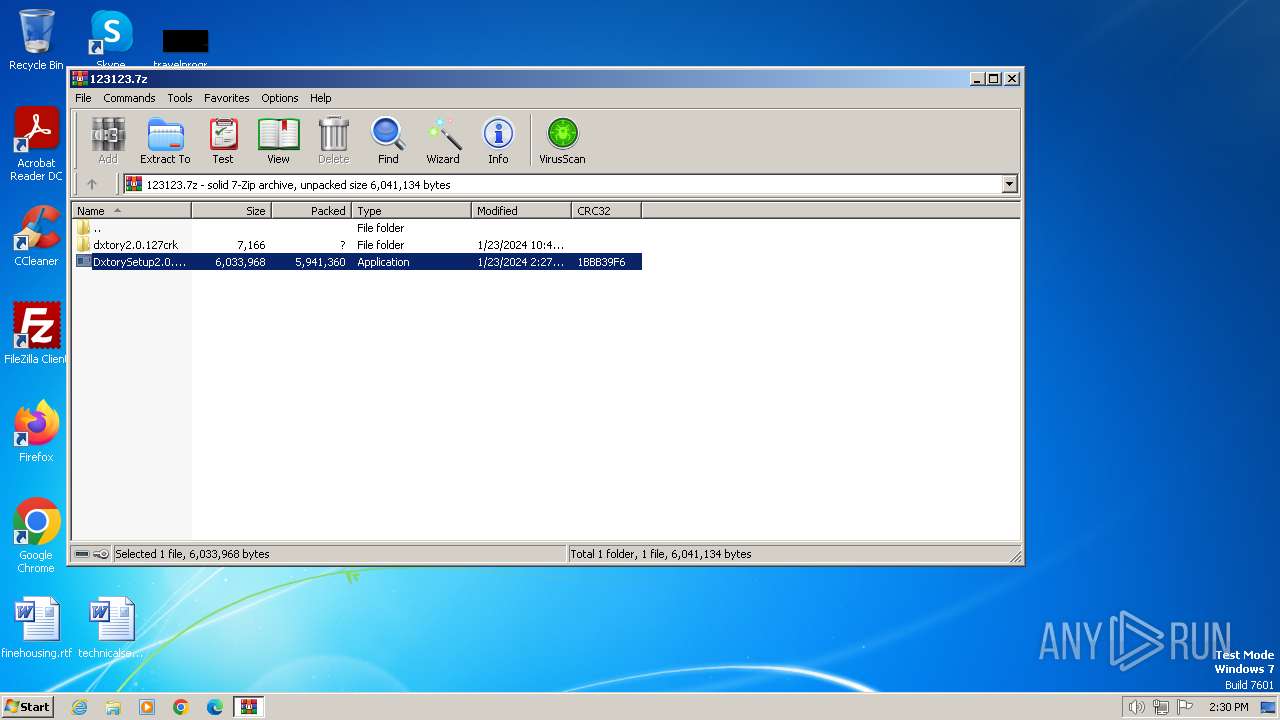
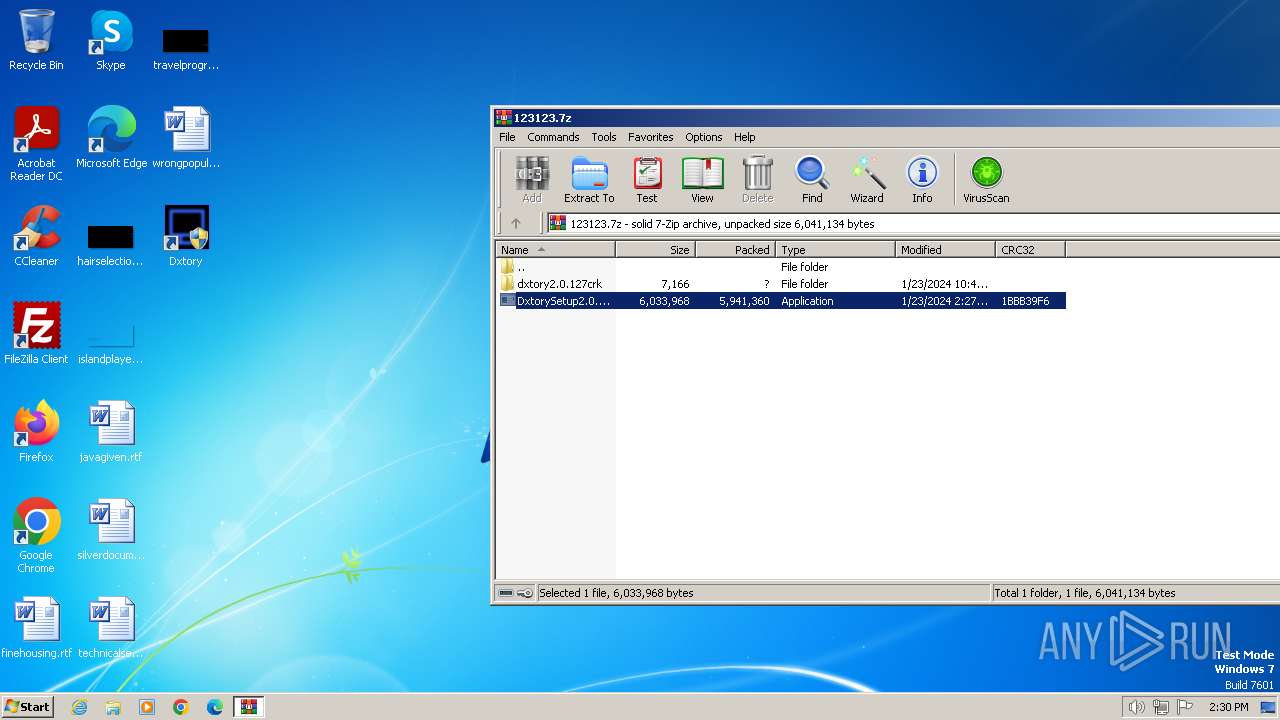
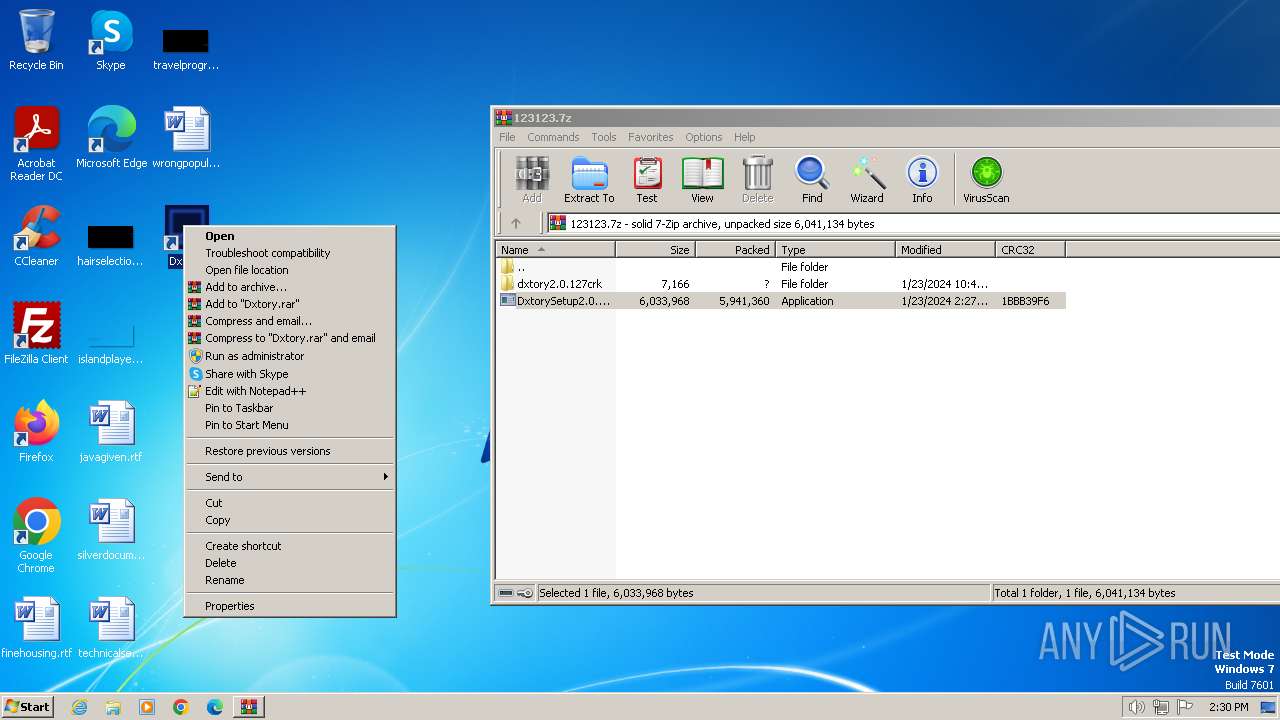
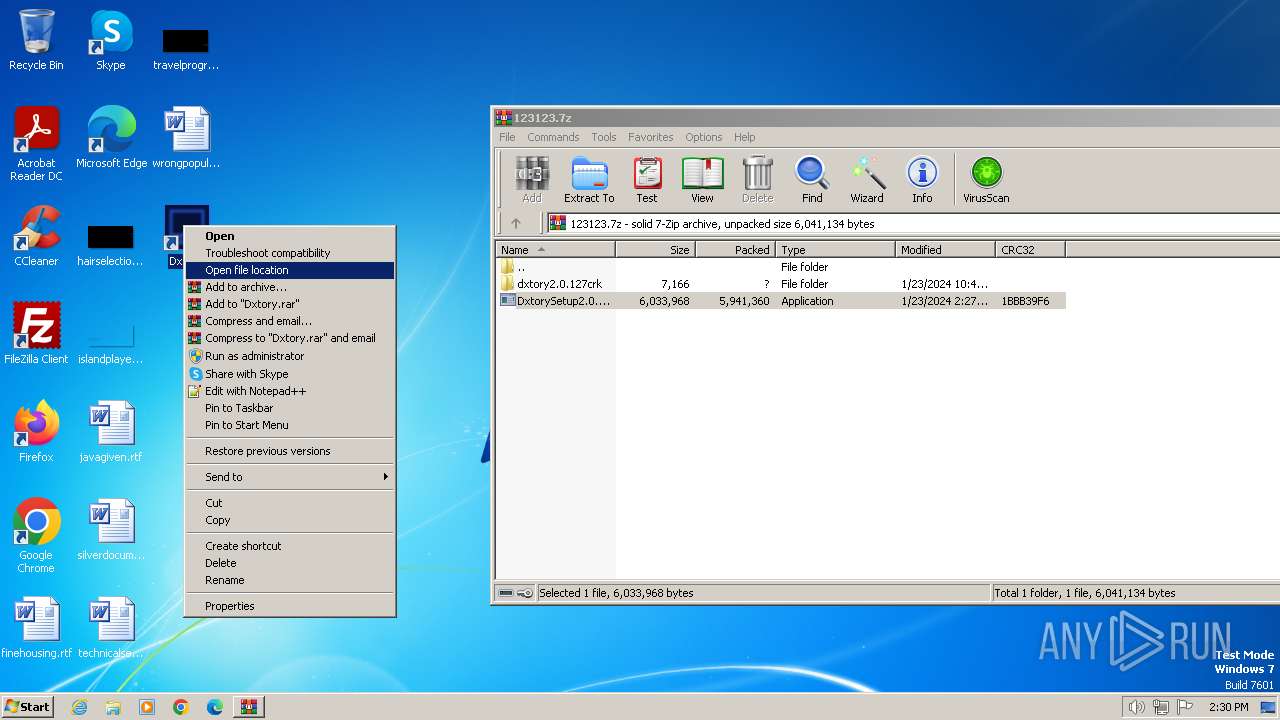
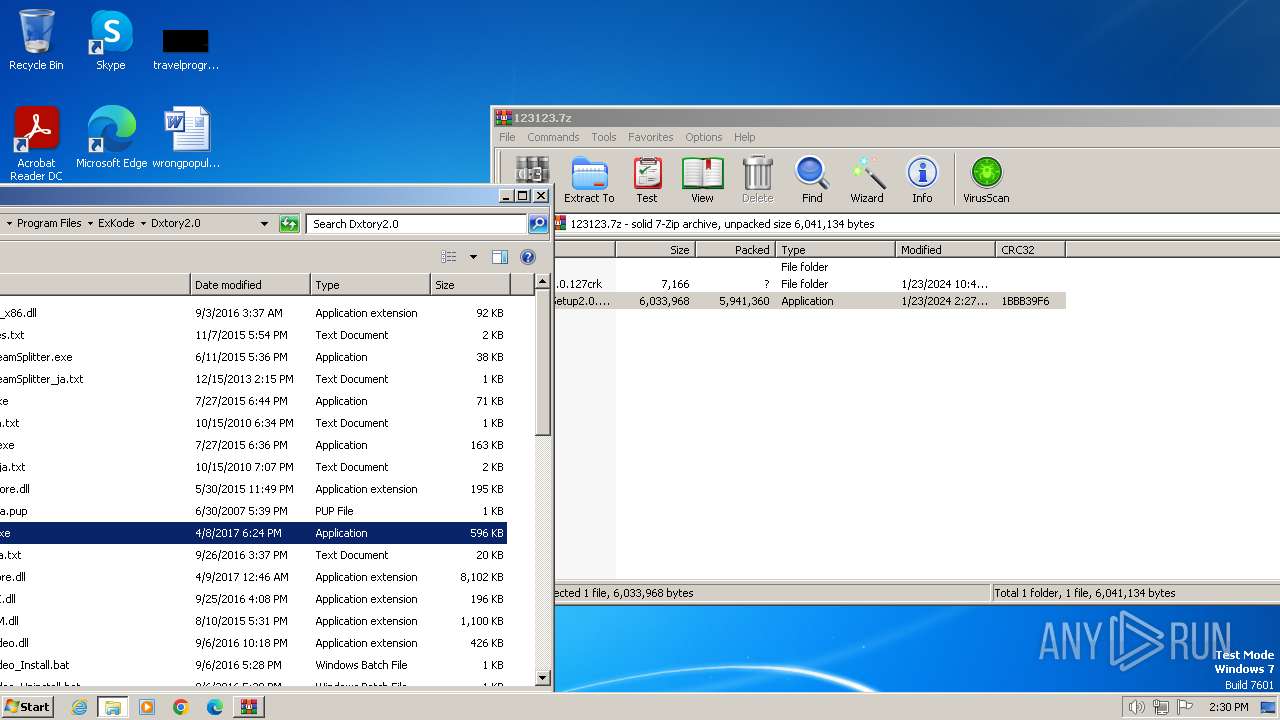
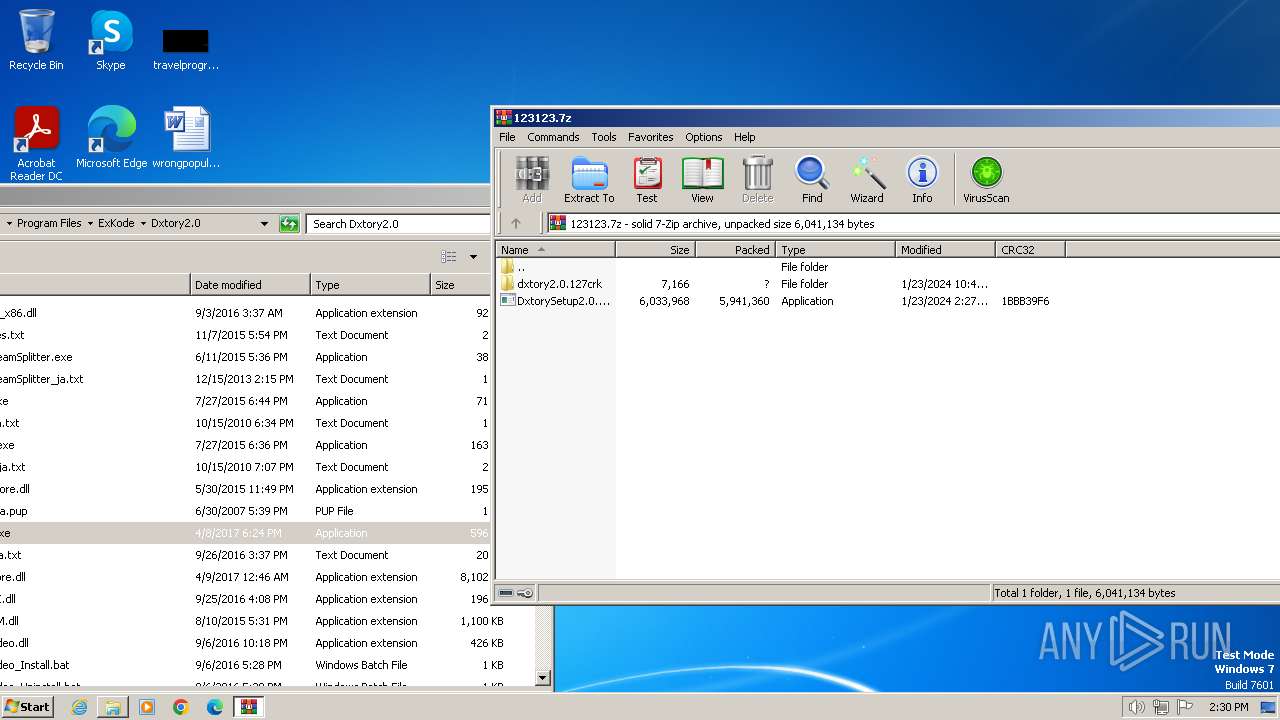
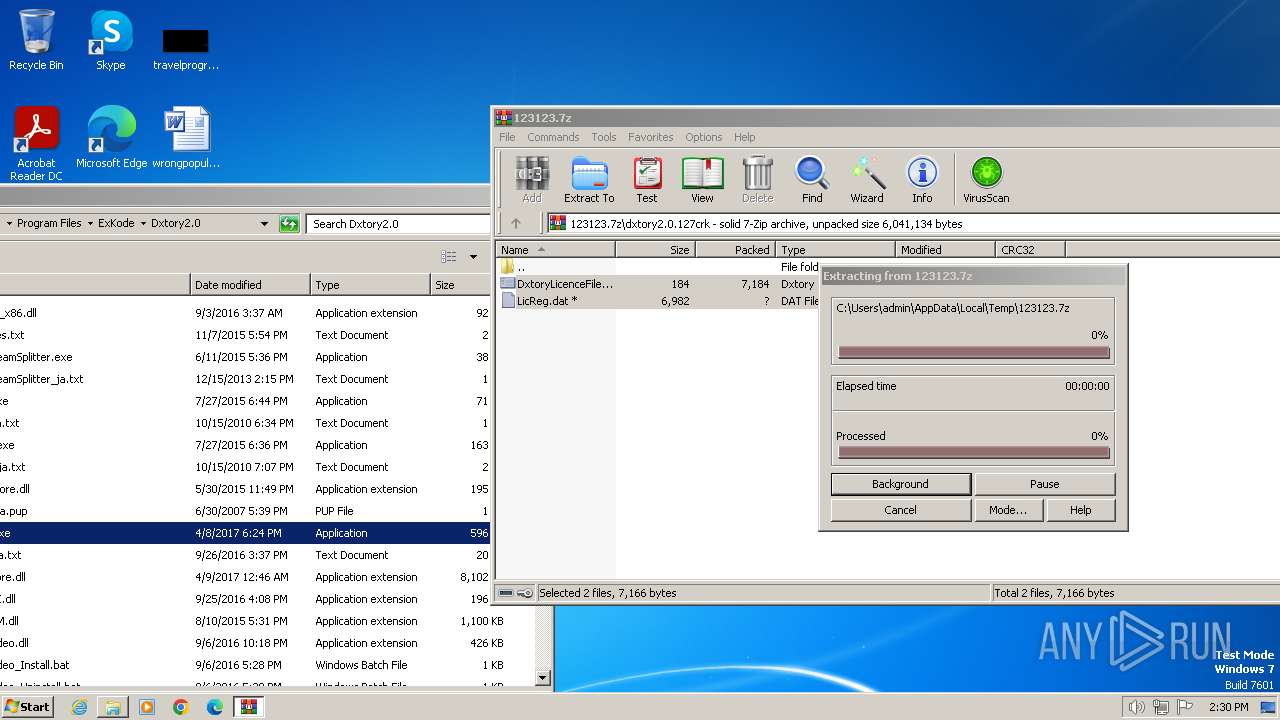
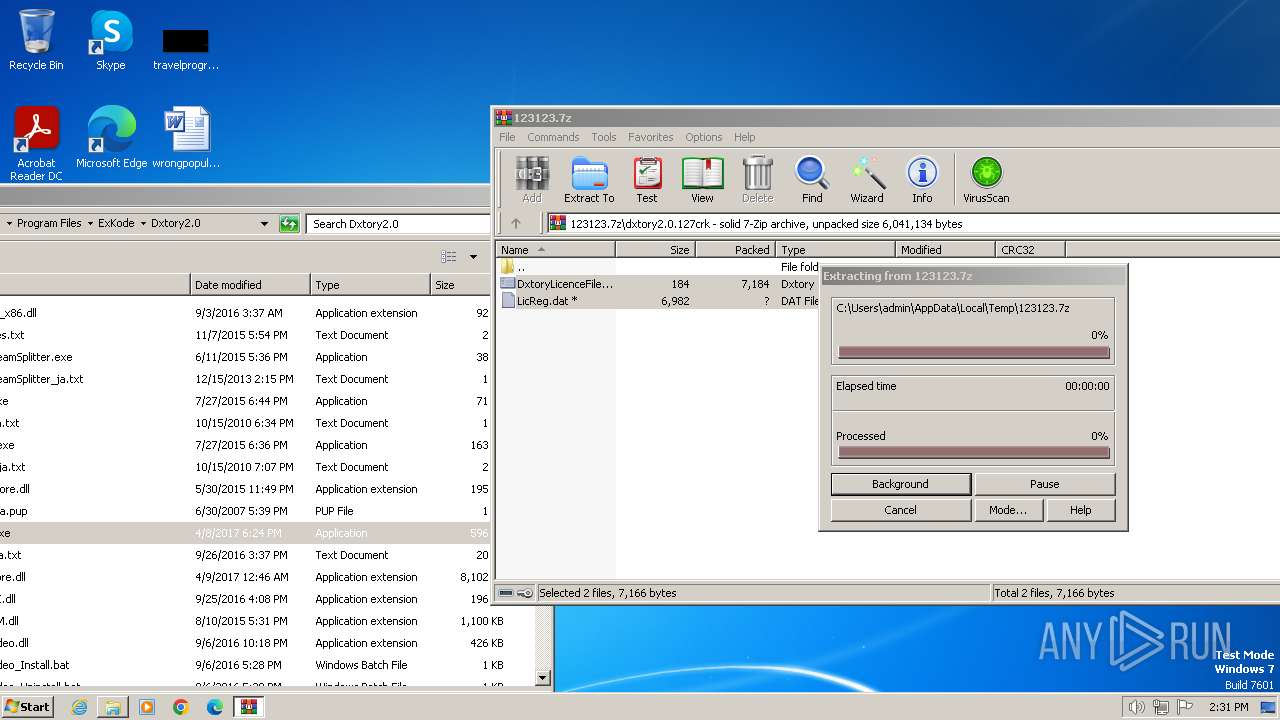
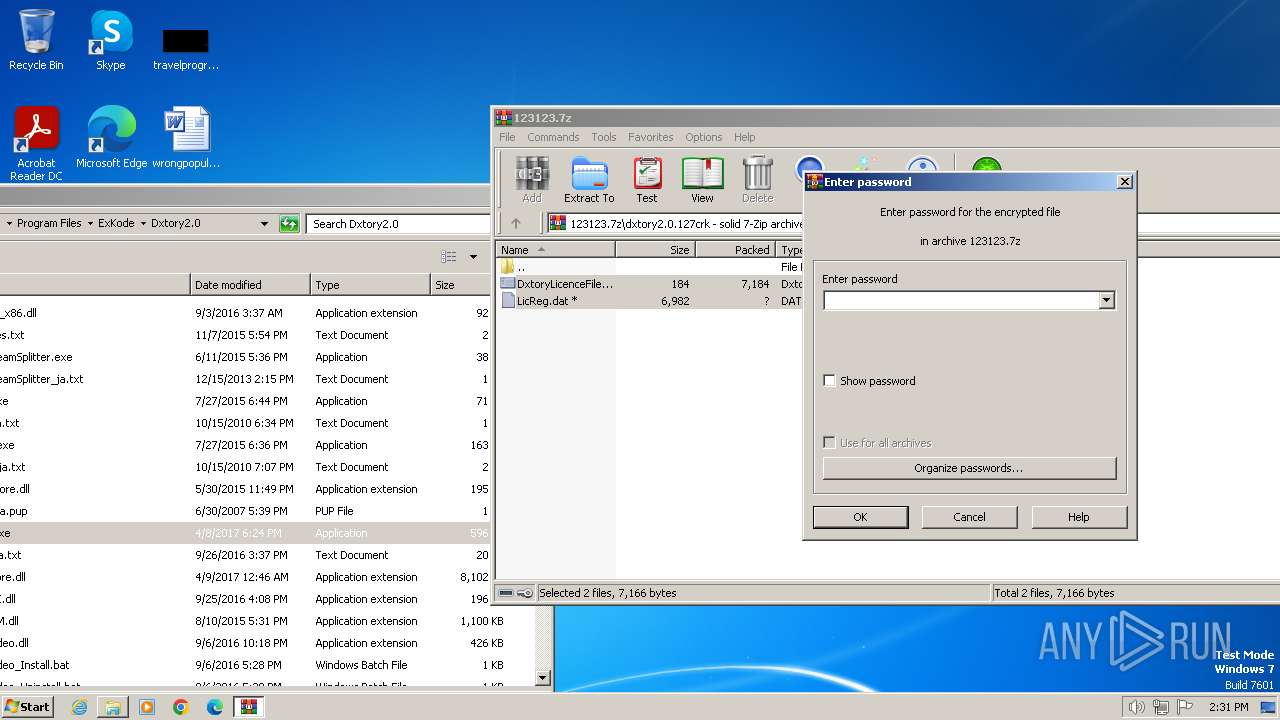
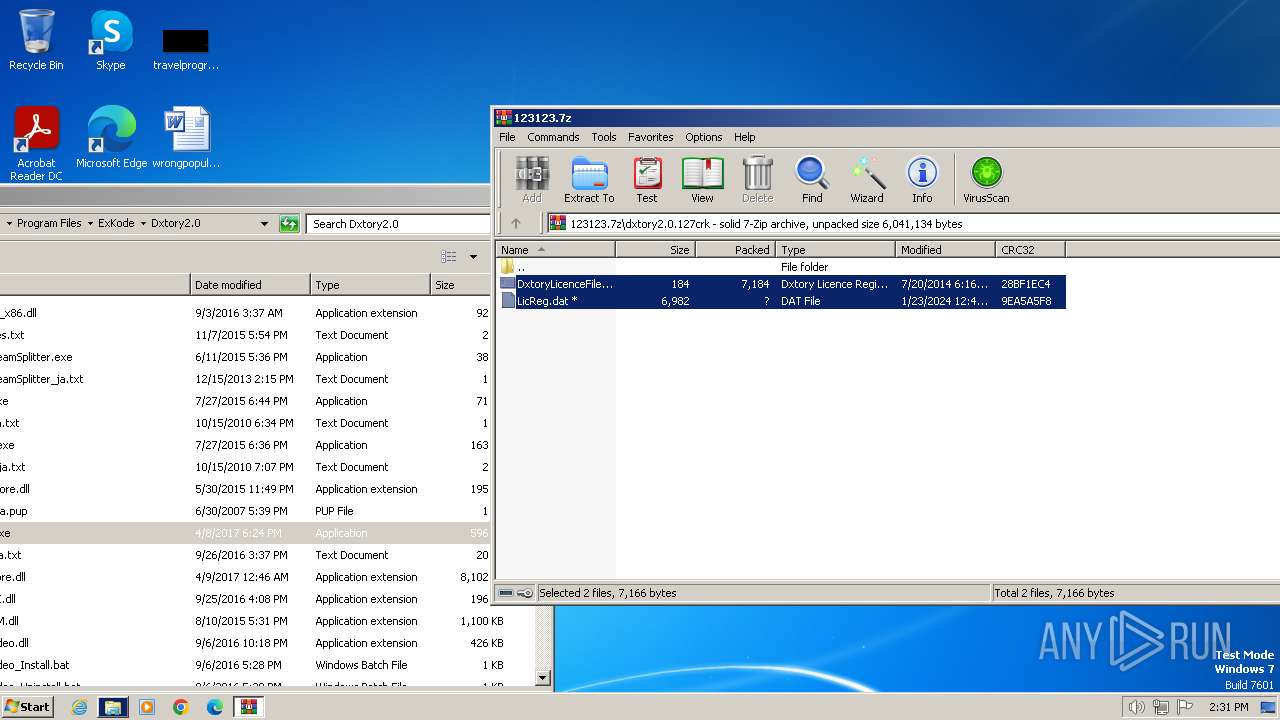
| File name: | 123123.7z |
| Full analysis: | https://app.any.run/tasks/10ee6ff0-494e-4b2b-8df8-3f9d270129fa |
| Verdict: | Malicious activity |
| Analysis date: | January 23, 2024, 14:29:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 4151644DDB47EB13DC1C16E7455FA397 |
| SHA1: | EFC39F623E47A6C6CC201FE36439F91B78AA856F |
| SHA256: | 4FC9322DAFEACFE5C2AECA541227BFD327A9863147D8E4EE4ADB0589B60DF017 |
| SSDEEP: | 98304:7RHs5Niy27xlki5GfftfAcCBqrHYBVVts2kMlRcv3Tcz5M+KriMH55OEfKnKmXuA:mi+cotdVQ2s |
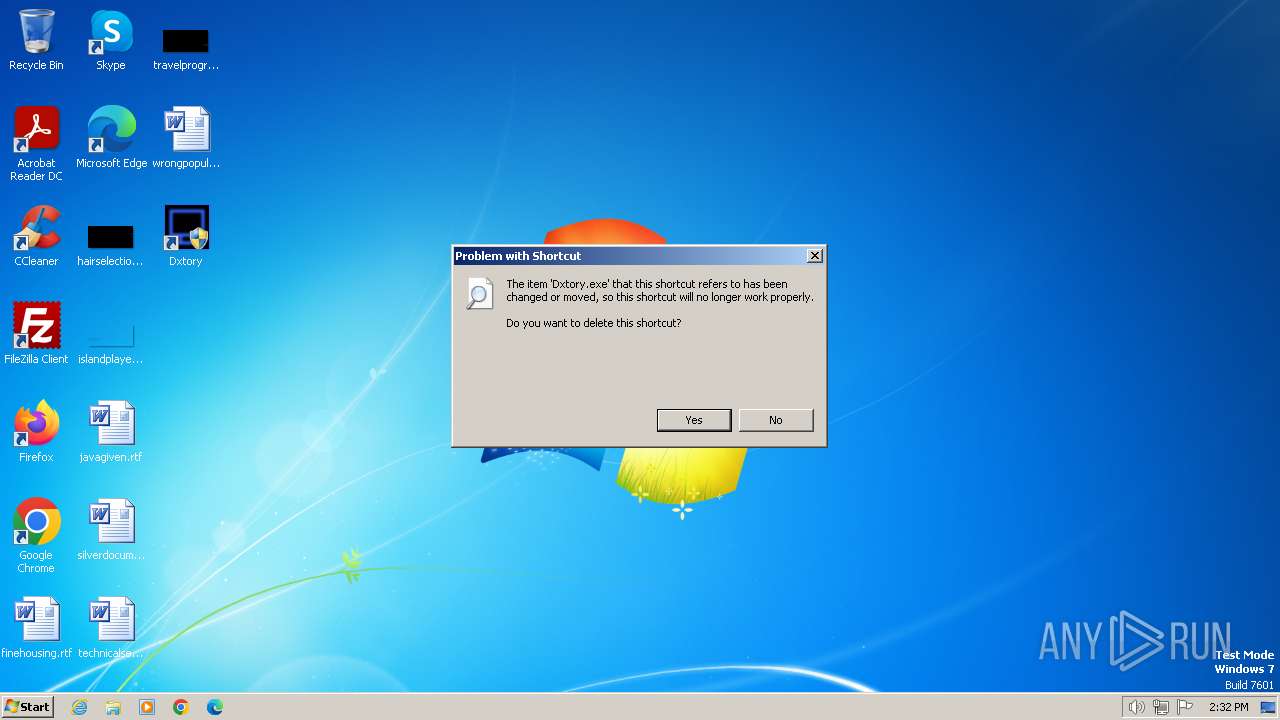
MALICIOUS
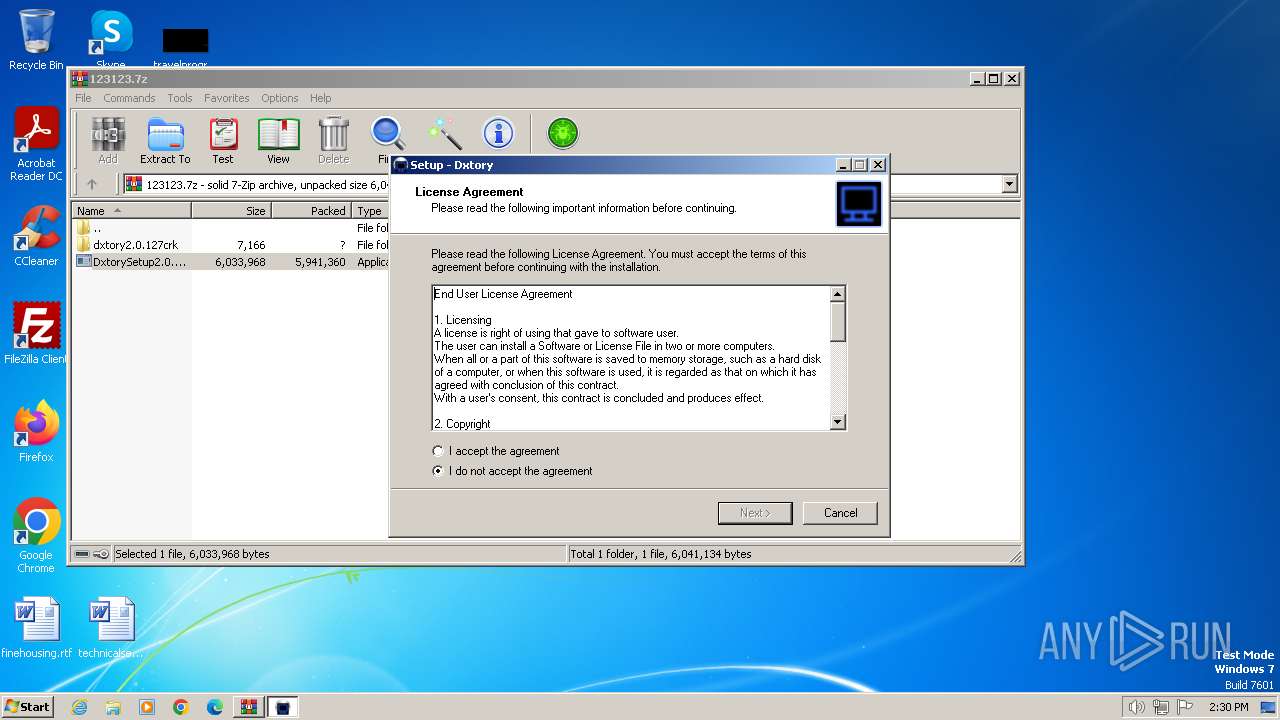
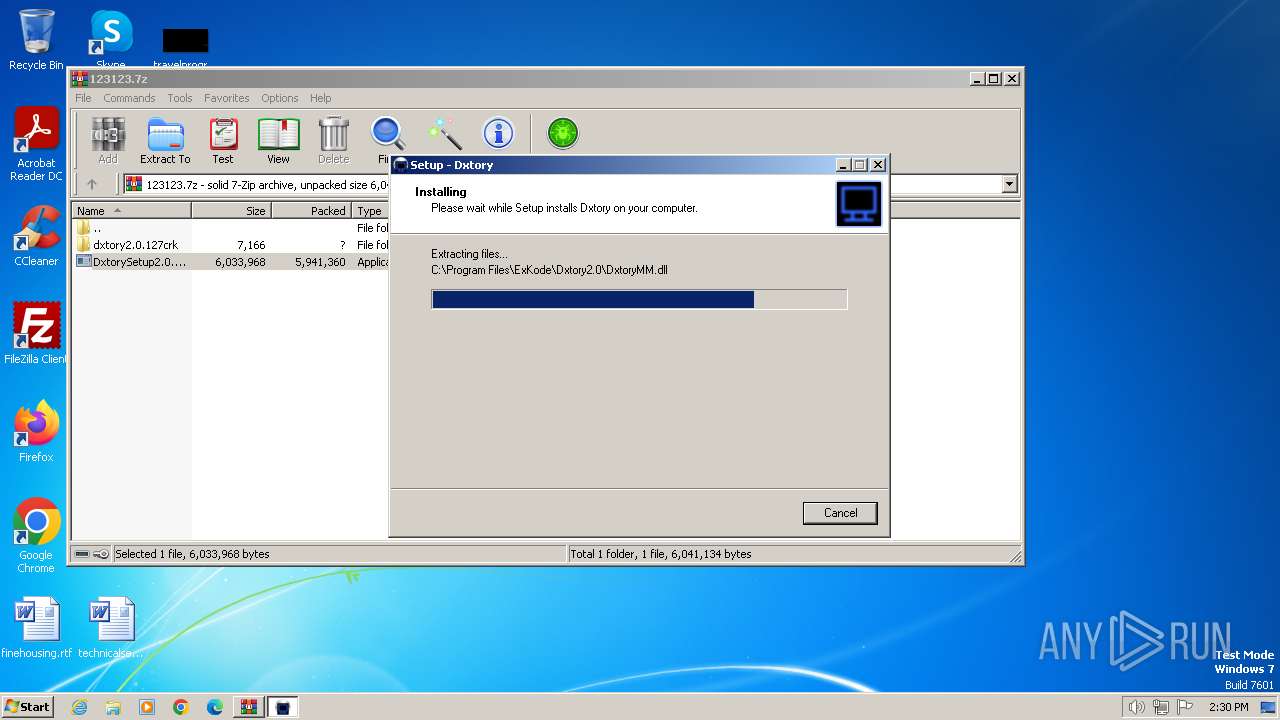
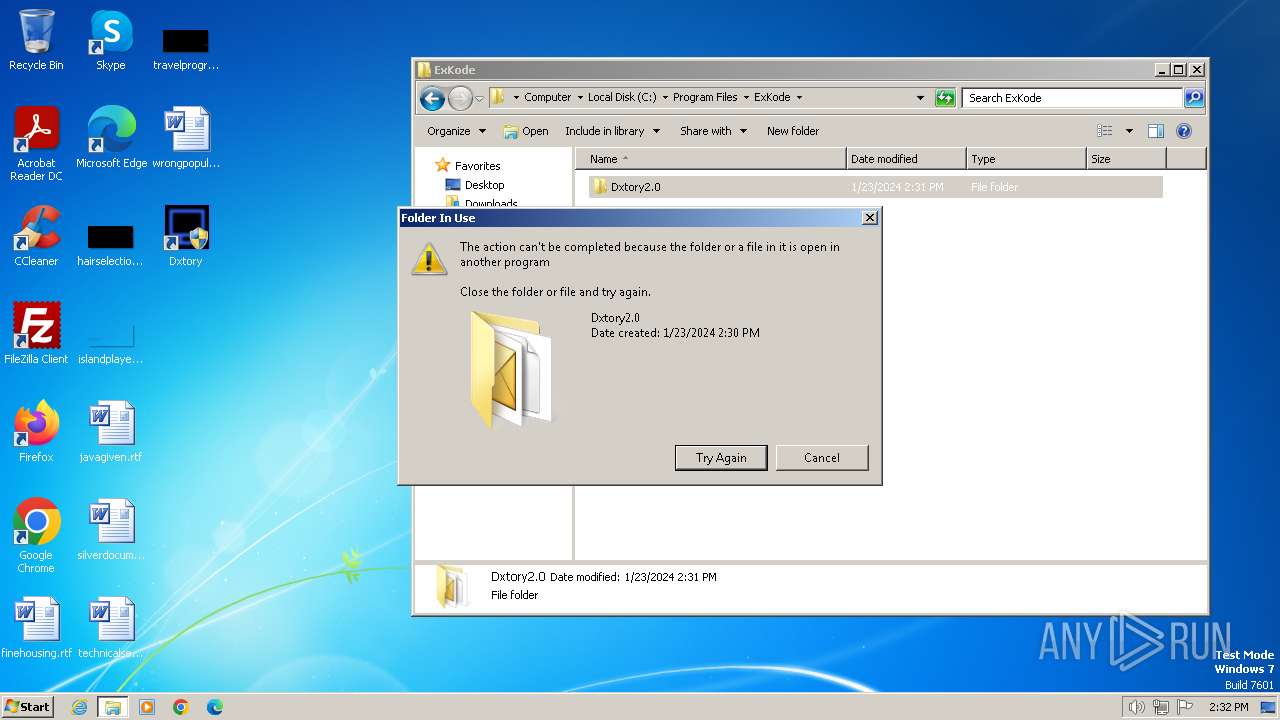
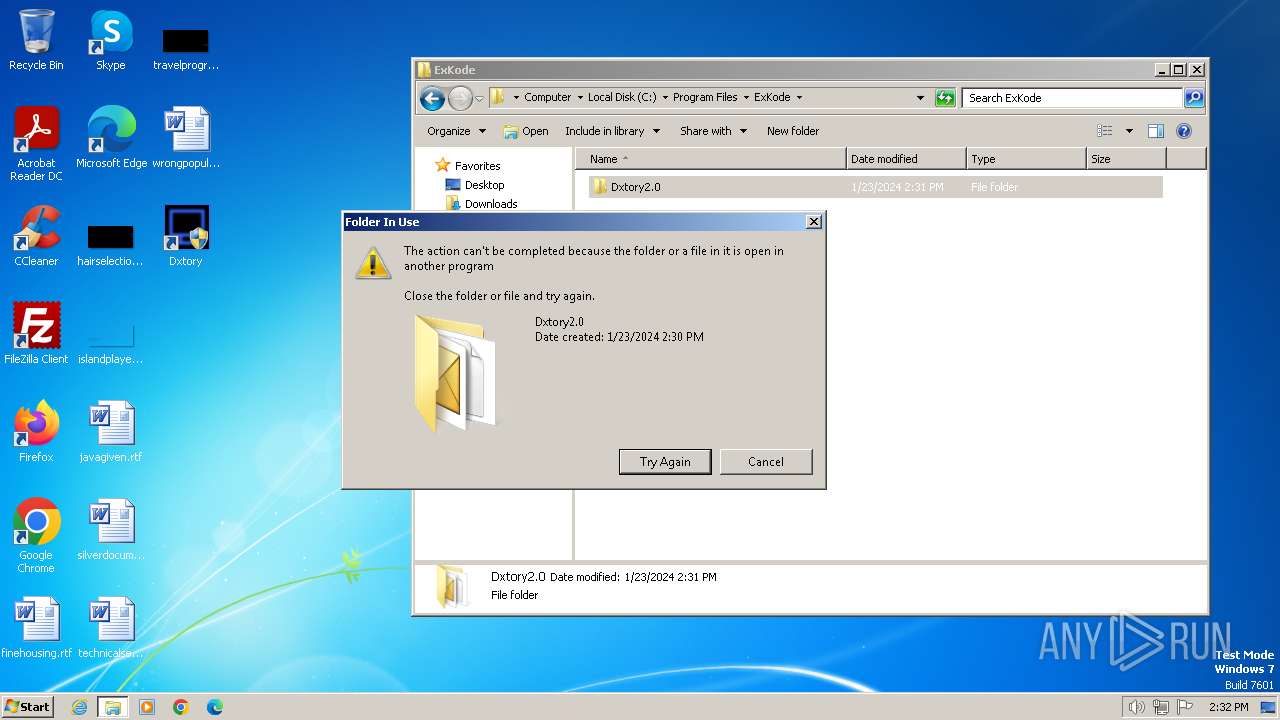
Drops the executable file immediately after the start
- DxtorySetup2.0.142.exe (PID: 2112)
- DxtorySetup2.0.142.exe (PID: 376)
- DxtorySetup2.0.142.tmp (PID: 2728)
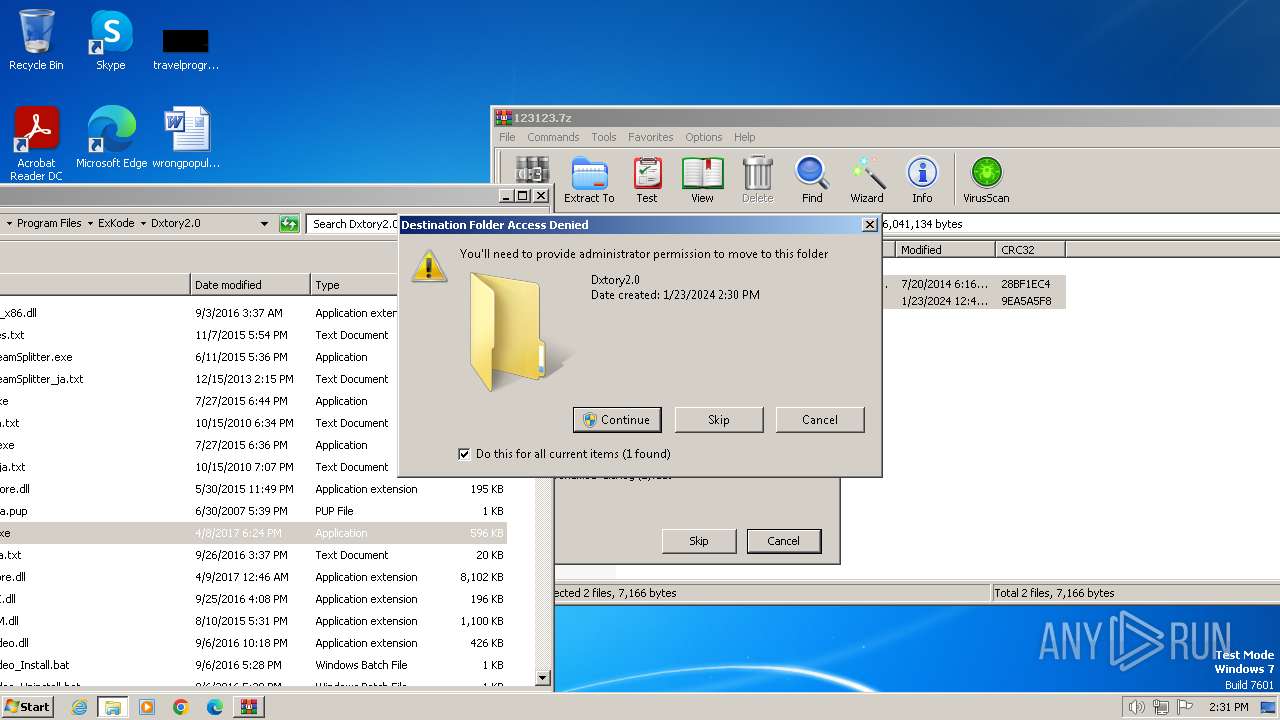
Creates a writable file in the system directory
- DxtorySetup2.0.142.tmp (PID: 2728)
Registers / Runs the DLL via REGSVR32.EXE
- DxtorySetup2.0.142.tmp (PID: 2728)
SUSPICIOUS
Executable content was dropped or overwritten
- DxtorySetup2.0.142.exe (PID: 376)
- DxtorySetup2.0.142.exe (PID: 2112)
- DxtorySetup2.0.142.tmp (PID: 2728)
Reads the Windows owner or organization settings
- DxtorySetup2.0.142.tmp (PID: 2728)
Uses RUNDLL32.EXE to load library
- DxtorySetup2.0.142.tmp (PID: 2728)
Reads the Internet Settings
- Dxtory.exe (PID: 3672)
- LicReg.exe (PID: 3584)
- LicReg.exe (PID: 3960)
- Dxtory.exe (PID: 3620)
Reads security settings of Internet Explorer
- Dxtory.exe (PID: 3672)
- Dxtory.exe (PID: 3620)
Reads settings of System Certificates
- Dxtory.exe (PID: 3672)
- Dxtory.exe (PID: 3620)
Checks Windows Trust Settings
- Dxtory.exe (PID: 3672)
- Dxtory.exe (PID: 3620)
Adds/modifies Windows certificates
- Dxtory.exe (PID: 3672)
INFO
Create files in a temporary directory
- DxtorySetup2.0.142.exe (PID: 376)
- DxtorySetup2.0.142.exe (PID: 2112)
- DxtorySetup2.0.142.tmp (PID: 2728)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2404)
Checks supported languages
- DxtorySetup2.0.142.exe (PID: 376)
- DxtorySetup2.0.142.tmp (PID: 452)
- DxtorySetup2.0.142.exe (PID: 2112)
- DxtorySetup2.0.142.tmp (PID: 2728)
- Dxtory.exe (PID: 448)
- LicReg.exe (PID: 3584)
- Dxtory.exe (PID: 3672)
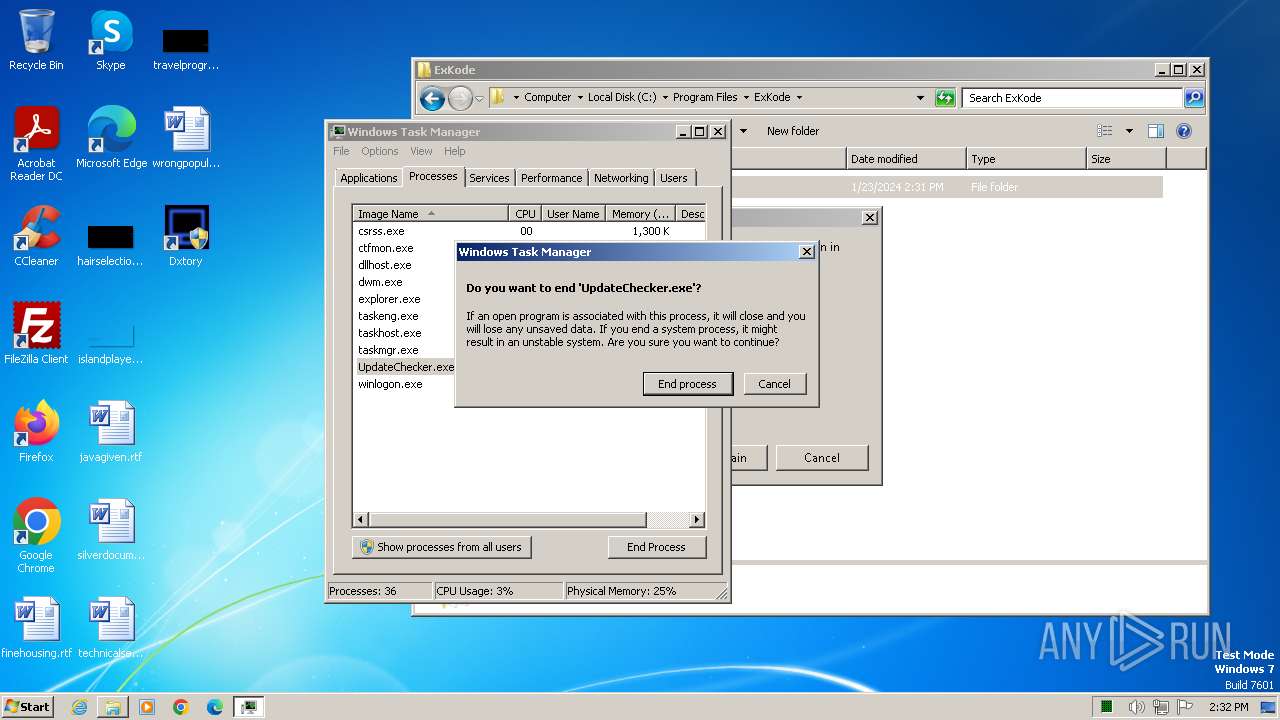
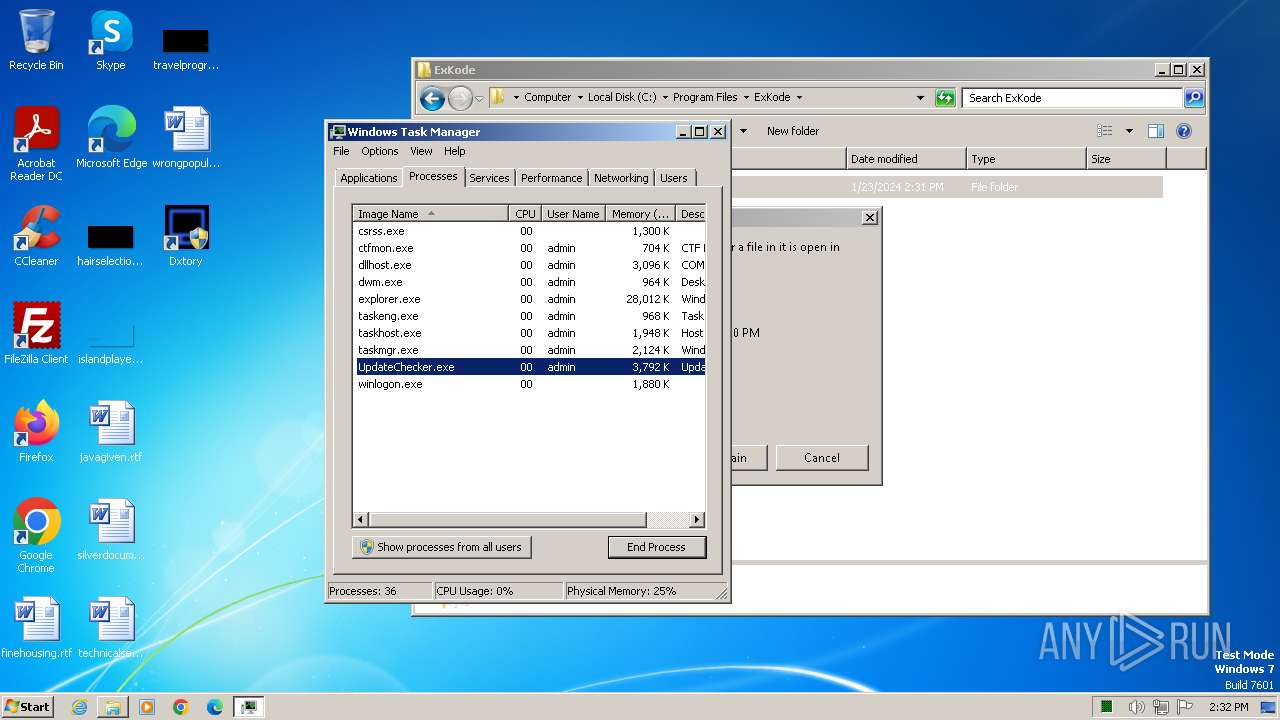
- UpdateChecker.exe (PID: 3652)
- Dxtory.exe (PID: 3896)
- Dxtory.exe (PID: 324)
- Dxtory.exe (PID: 3620)
- UpdateChecker.exe (PID: 992)
- LicReg.exe (PID: 3960)
- wmpnscfg.exe (PID: 3460)
Reads the computer name
- DxtorySetup2.0.142.tmp (PID: 452)
- Dxtory.exe (PID: 448)
- LicReg.exe (PID: 3584)
- DxtorySetup2.0.142.tmp (PID: 2728)
- Dxtory.exe (PID: 3896)
- Dxtory.exe (PID: 3672)
- UpdateChecker.exe (PID: 3652)
- LicReg.exe (PID: 3960)
- Dxtory.exe (PID: 324)
- Dxtory.exe (PID: 3620)
- UpdateChecker.exe (PID: 992)
- wmpnscfg.exe (PID: 3460)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2404)
Reads the machine GUID from the registry
- Dxtory.exe (PID: 448)
- LicReg.exe (PID: 3584)
- Dxtory.exe (PID: 3672)
- UpdateChecker.exe (PID: 3652)
- Dxtory.exe (PID: 3896)
- LicReg.exe (PID: 3960)
- Dxtory.exe (PID: 3620)
- Dxtory.exe (PID: 324)
- UpdateChecker.exe (PID: 992)
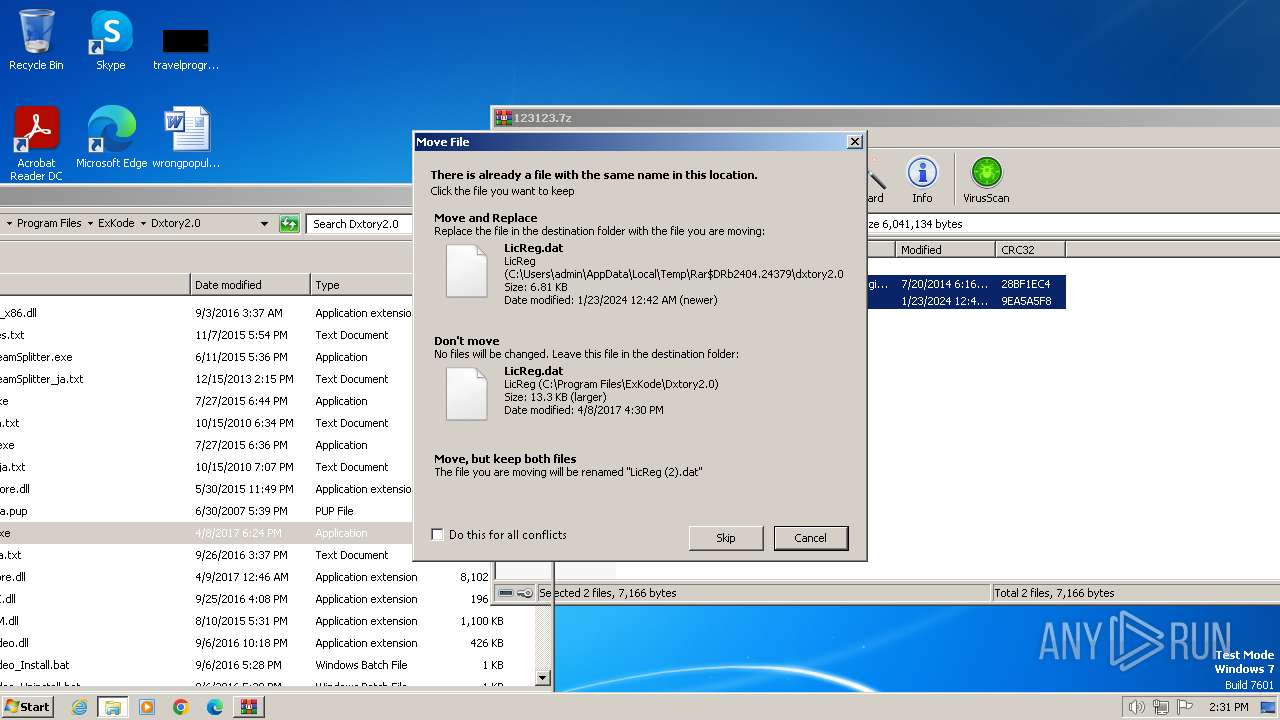
Creates files or folders in the user directory
- rundll32.exe (PID: 3616)
- Dxtory.exe (PID: 3672)
- LicReg.exe (PID: 3584)
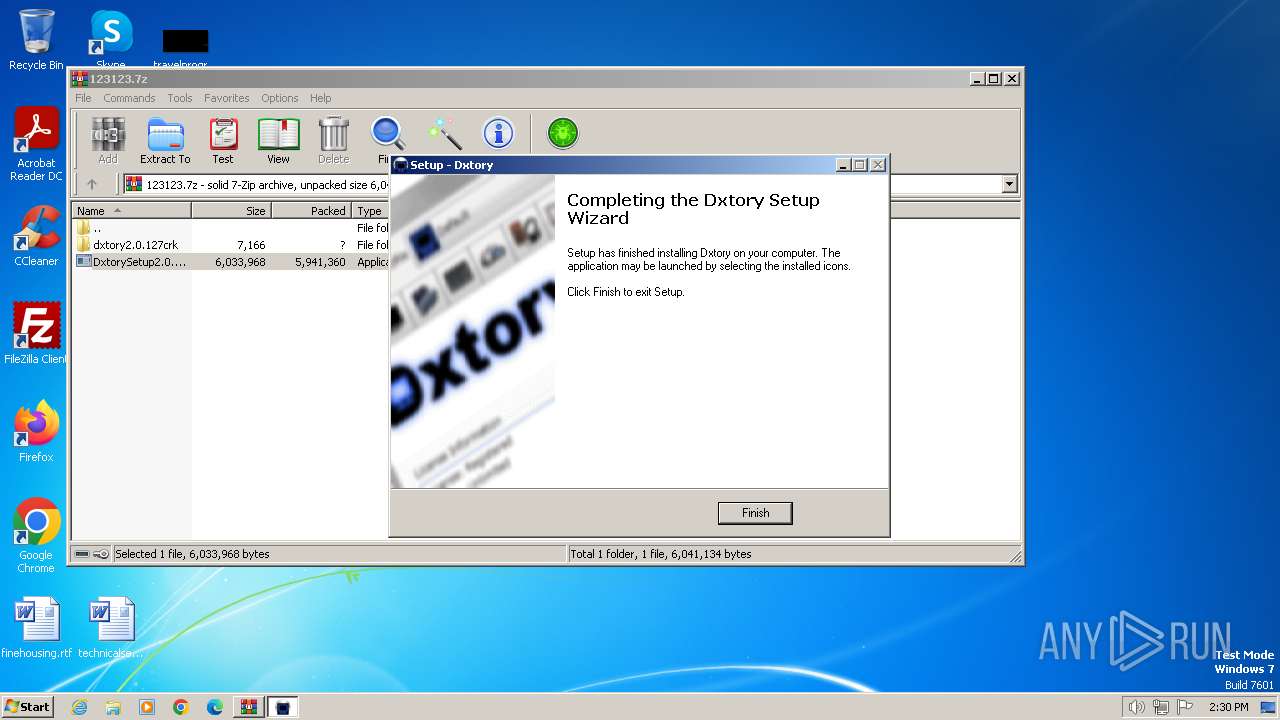
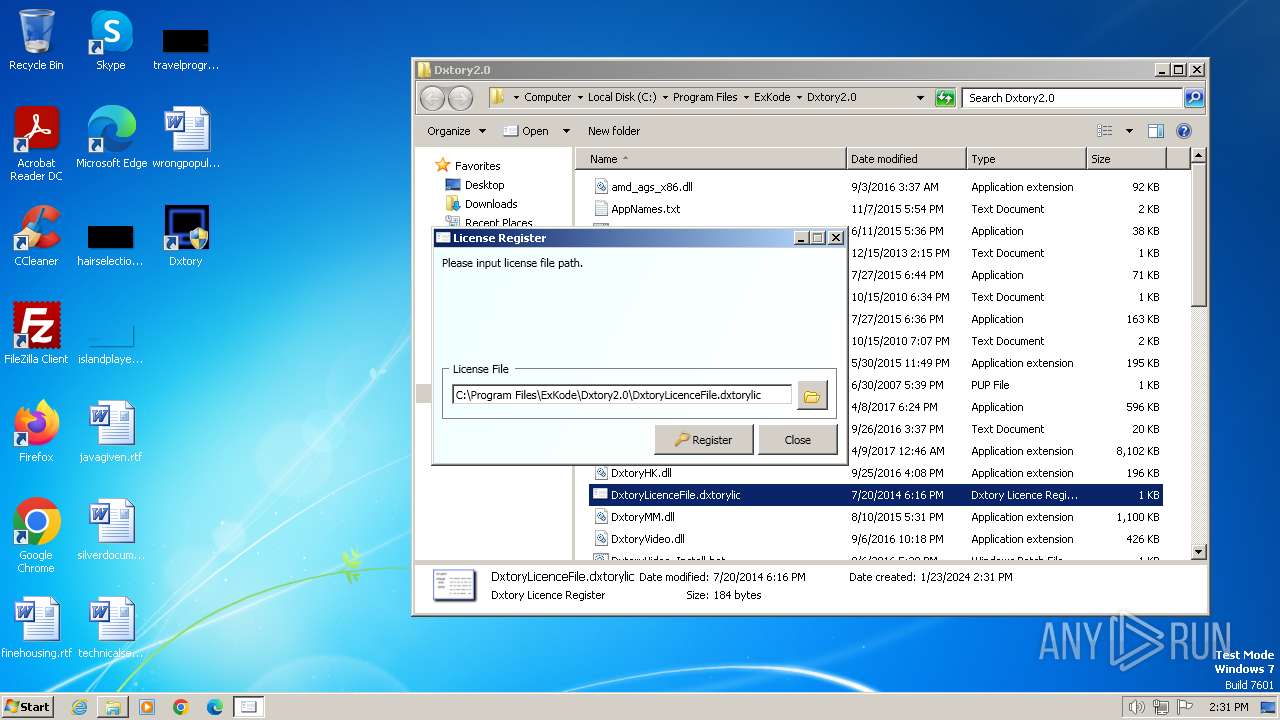
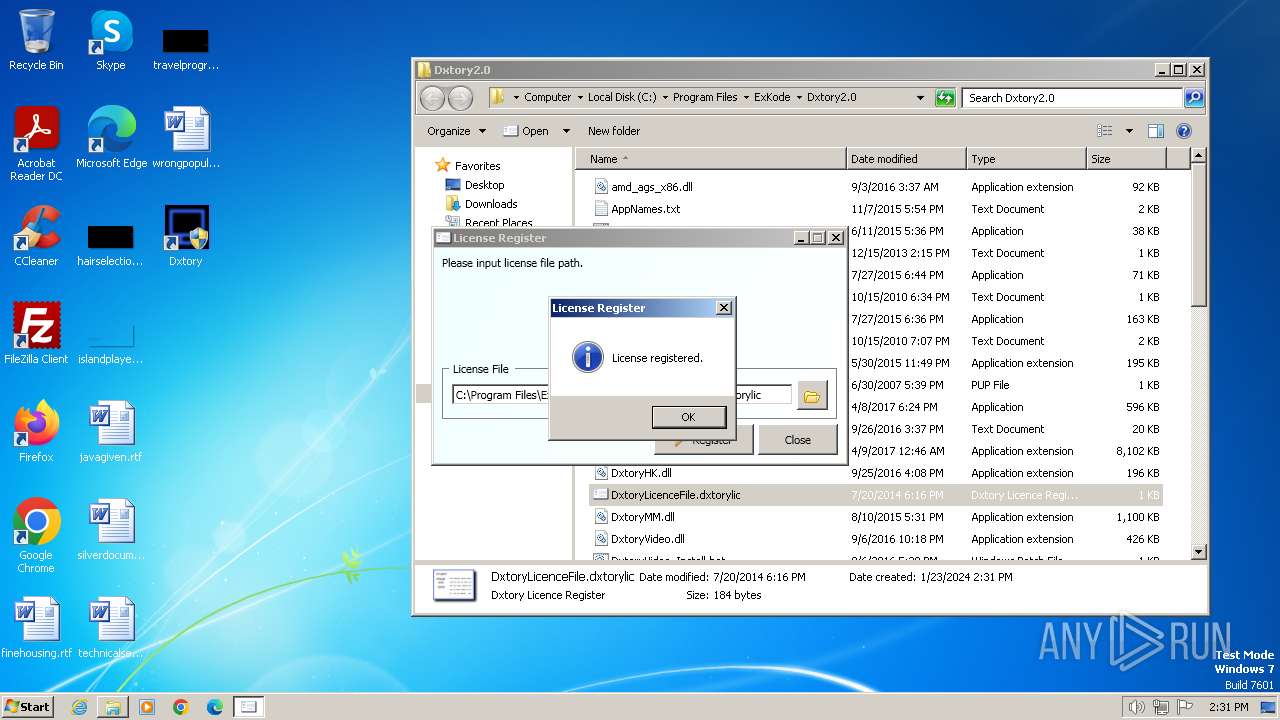
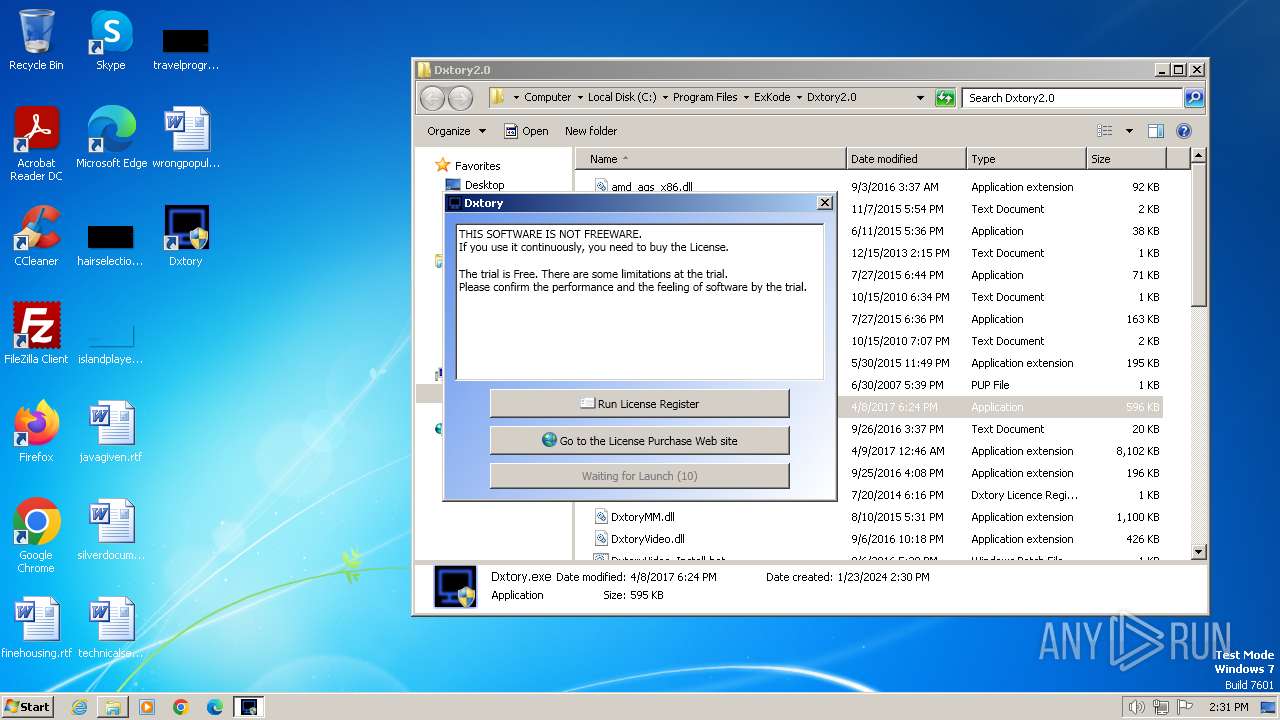
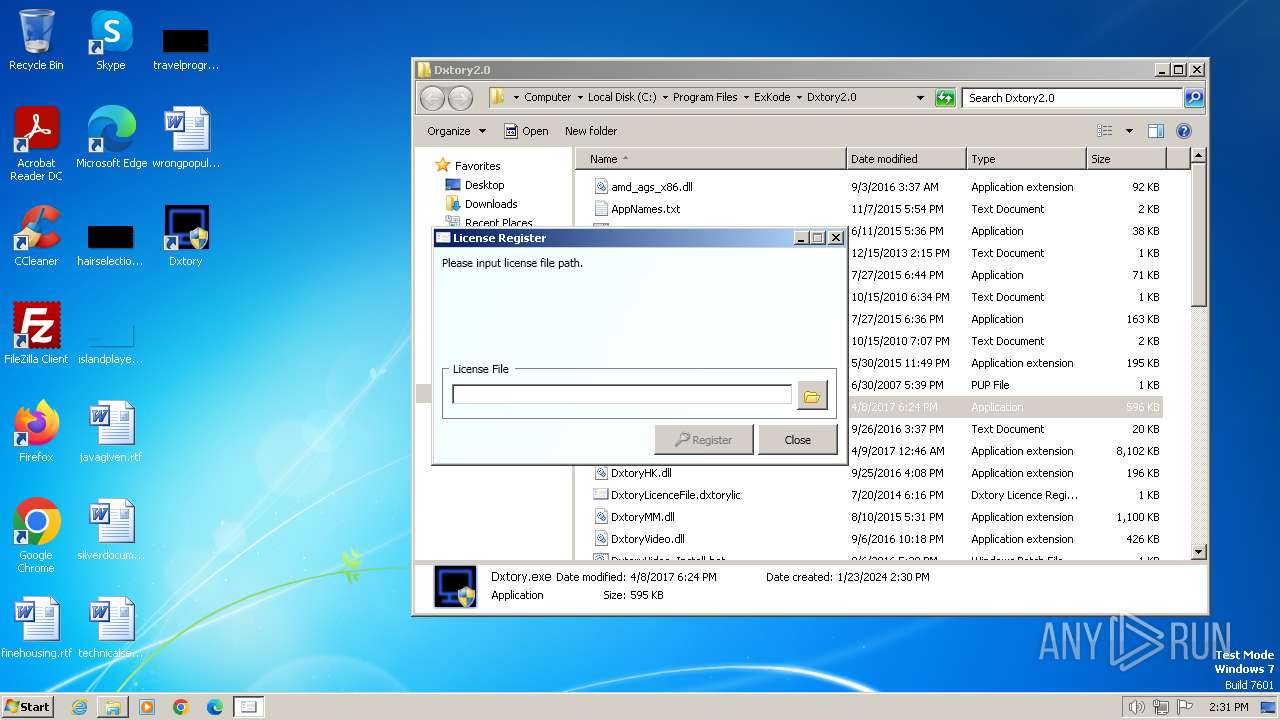
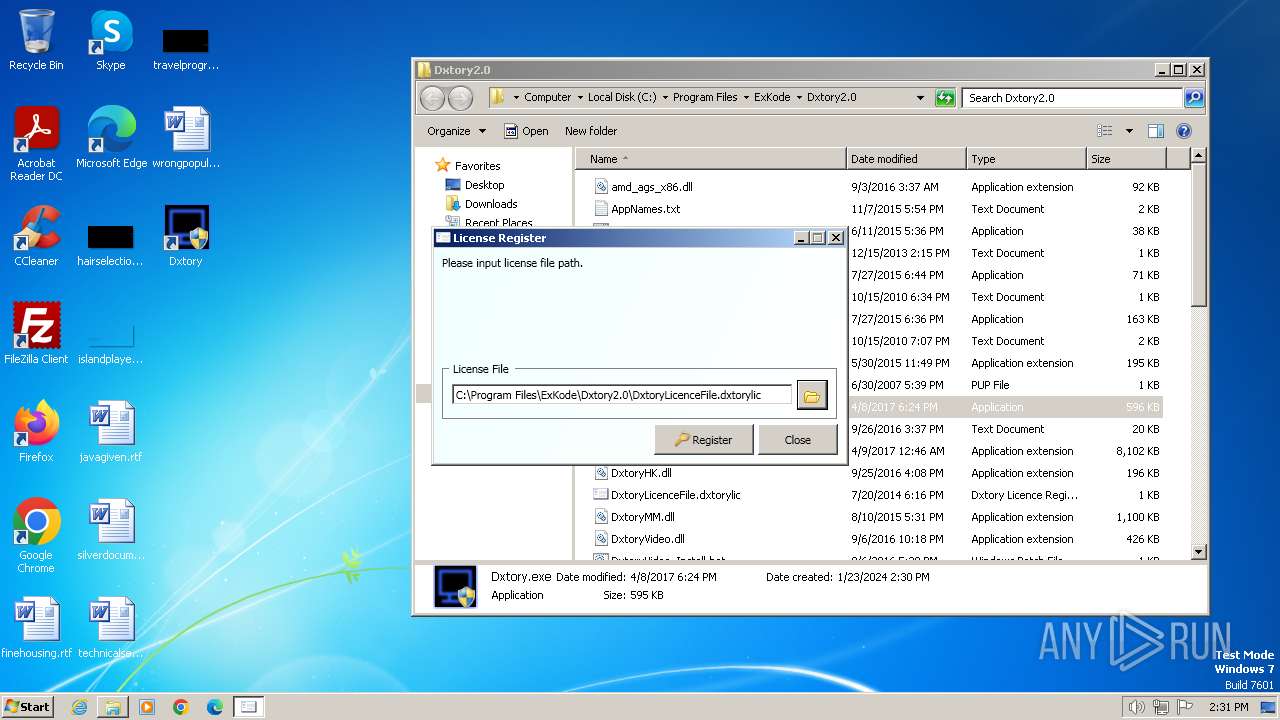
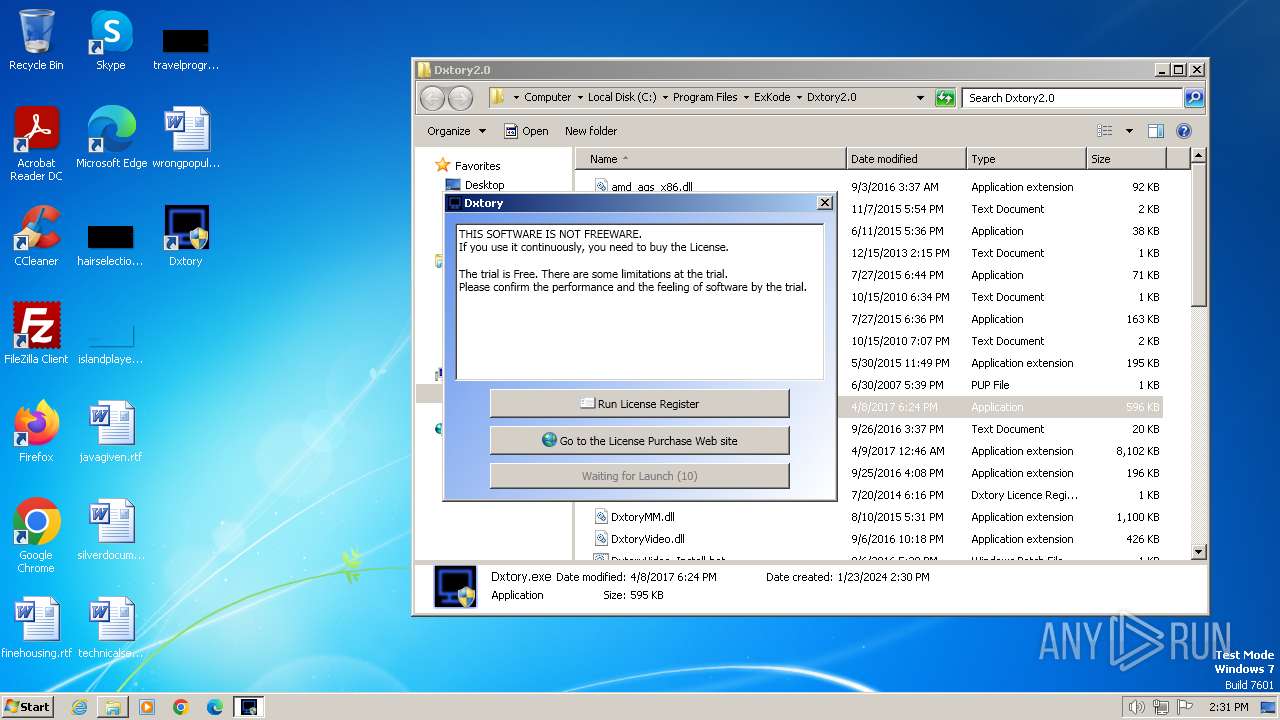
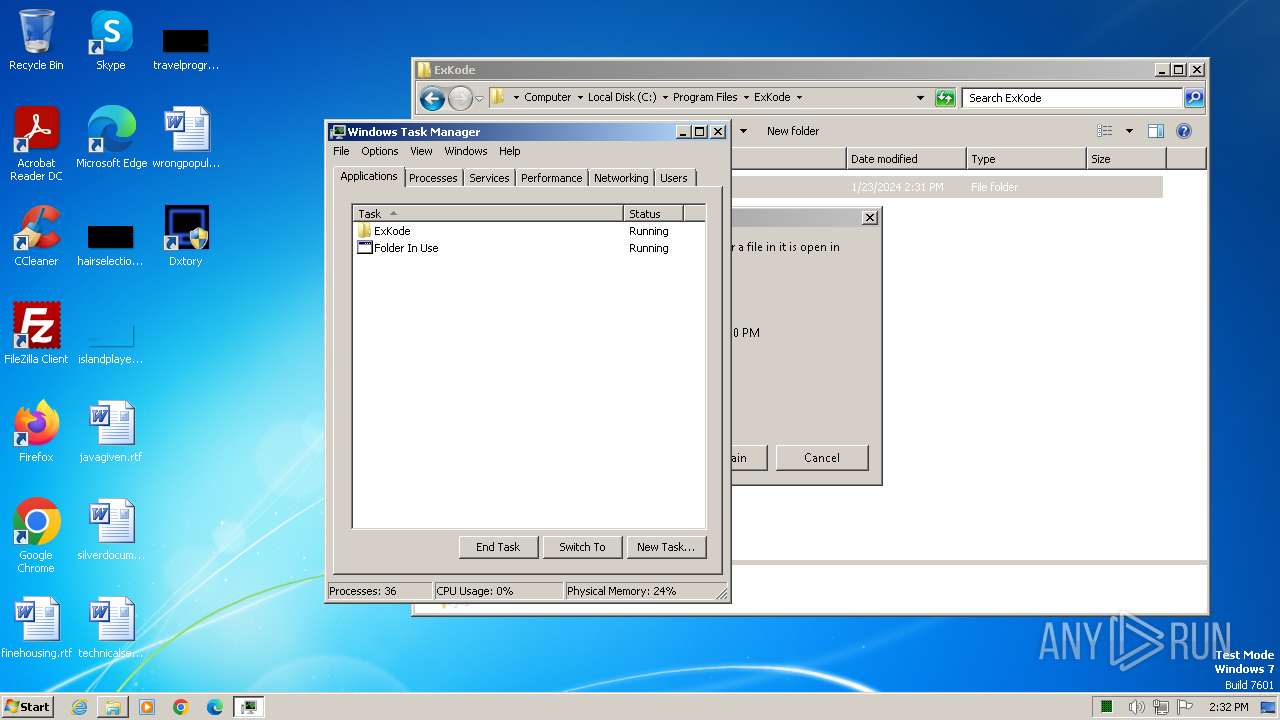
Manual execution by a user
- LicReg.exe (PID: 3584)
- Dxtory.exe (PID: 3924)
- Dxtory.exe (PID: 3672)
- Dxtory.exe (PID: 784)
- Dxtory.exe (PID: 3620)
- wmpnscfg.exe (PID: 3460)
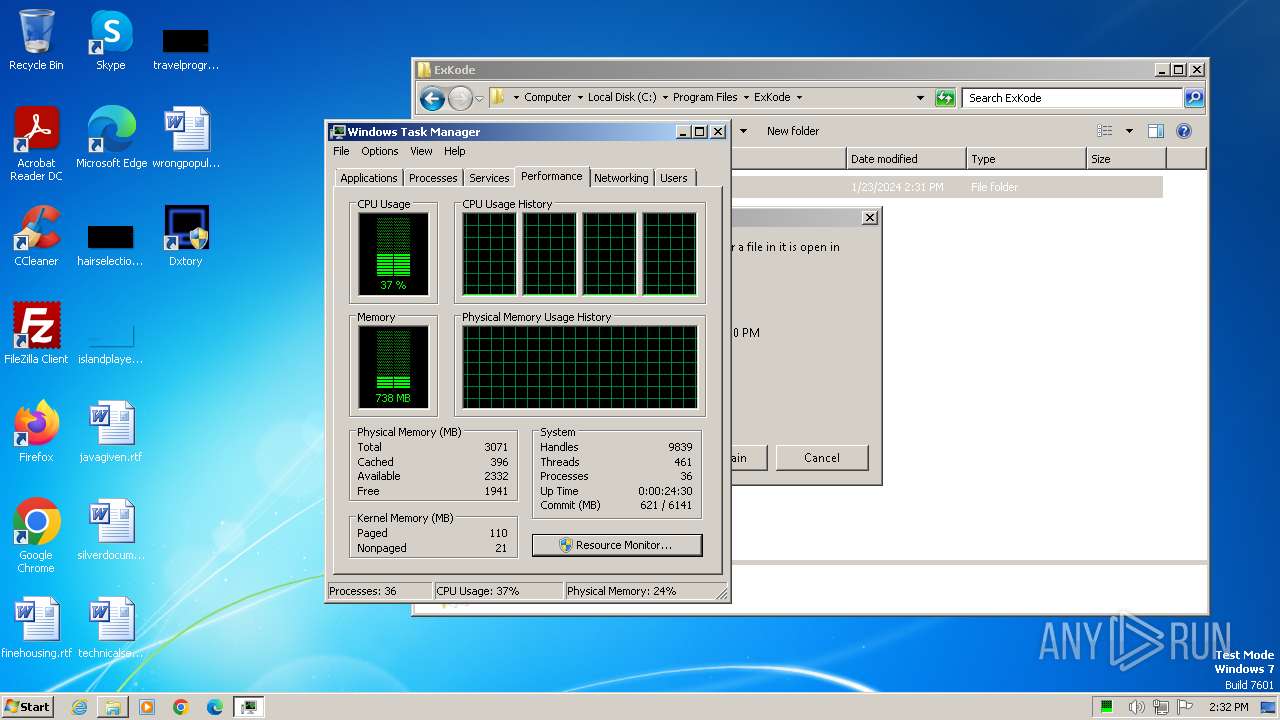
- taskmgr.exe (PID: 2732)
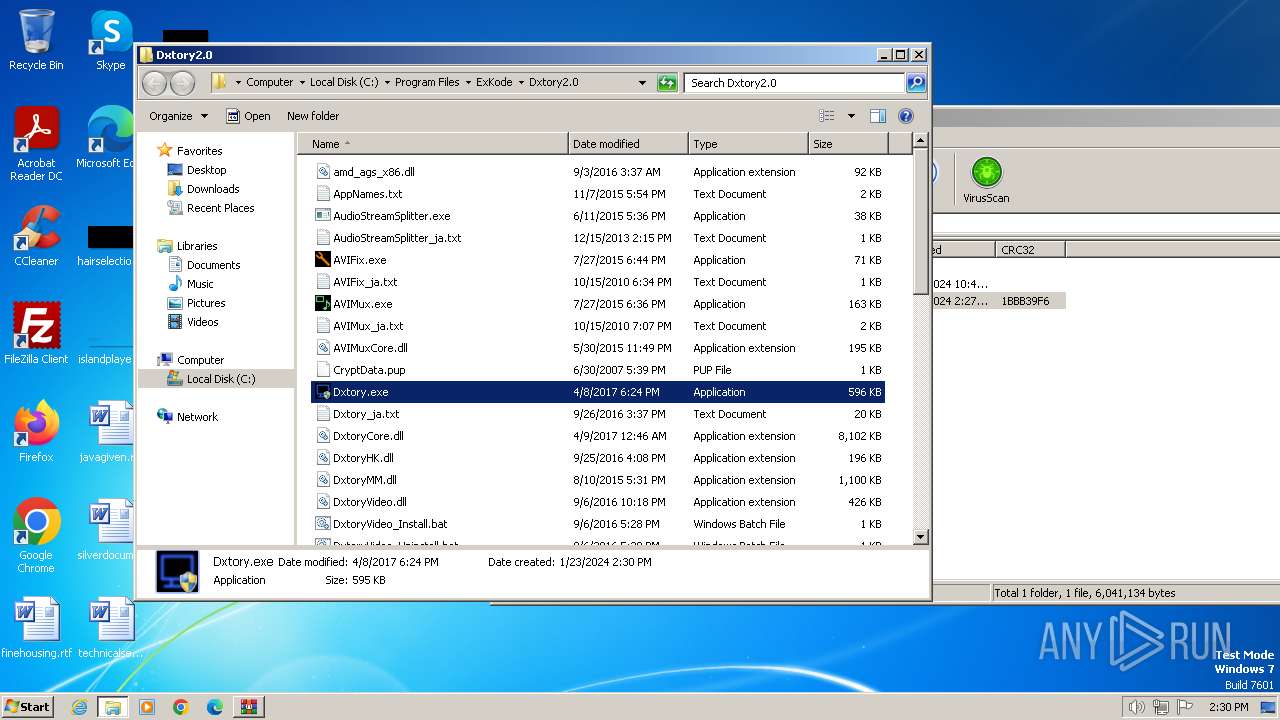
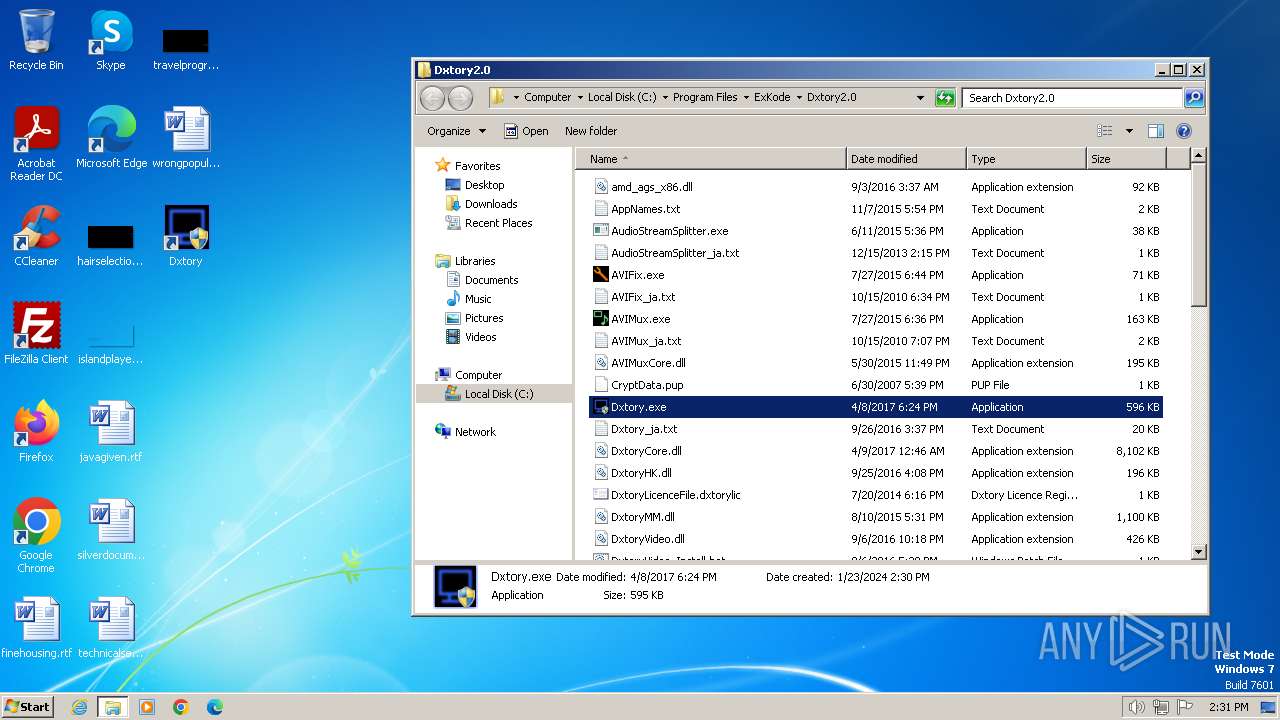
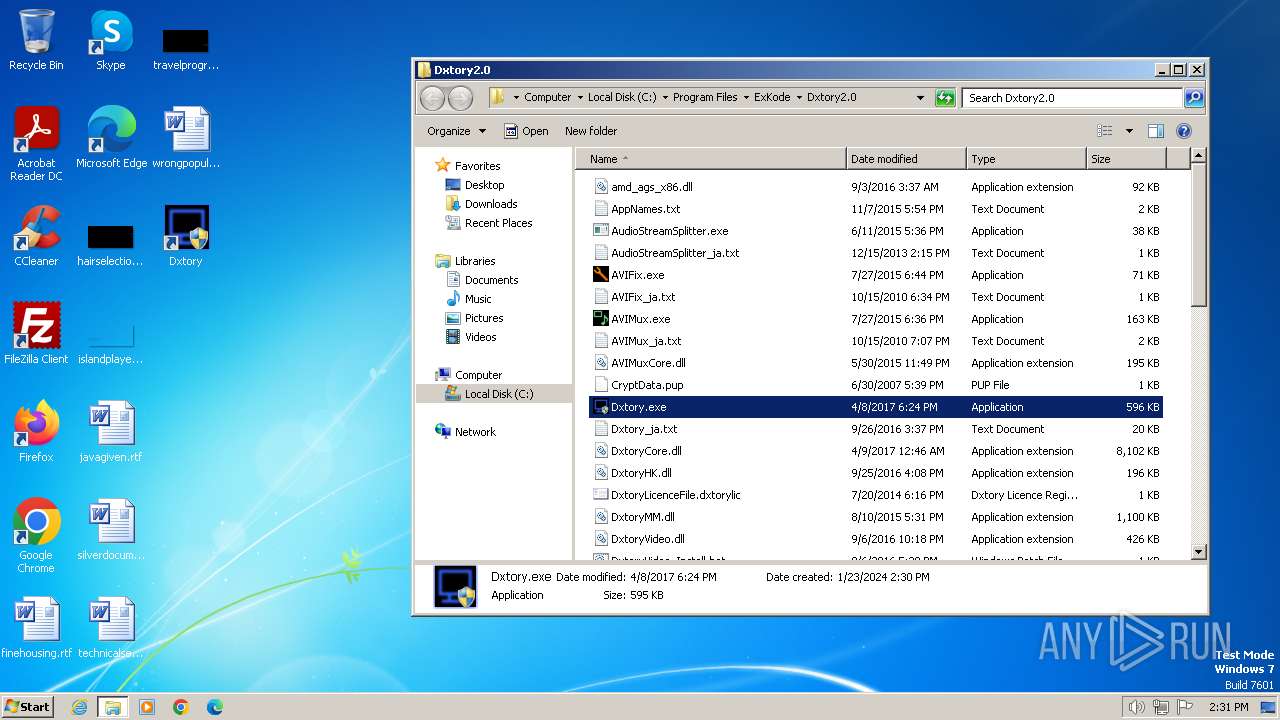
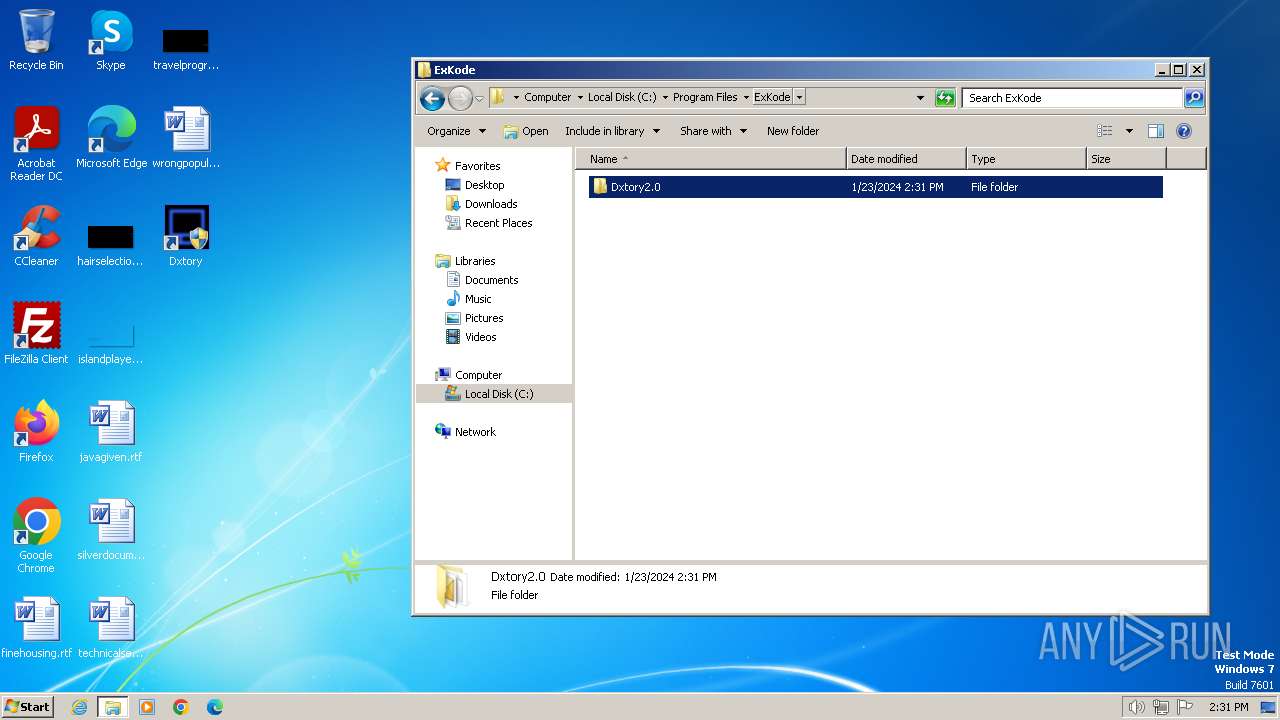
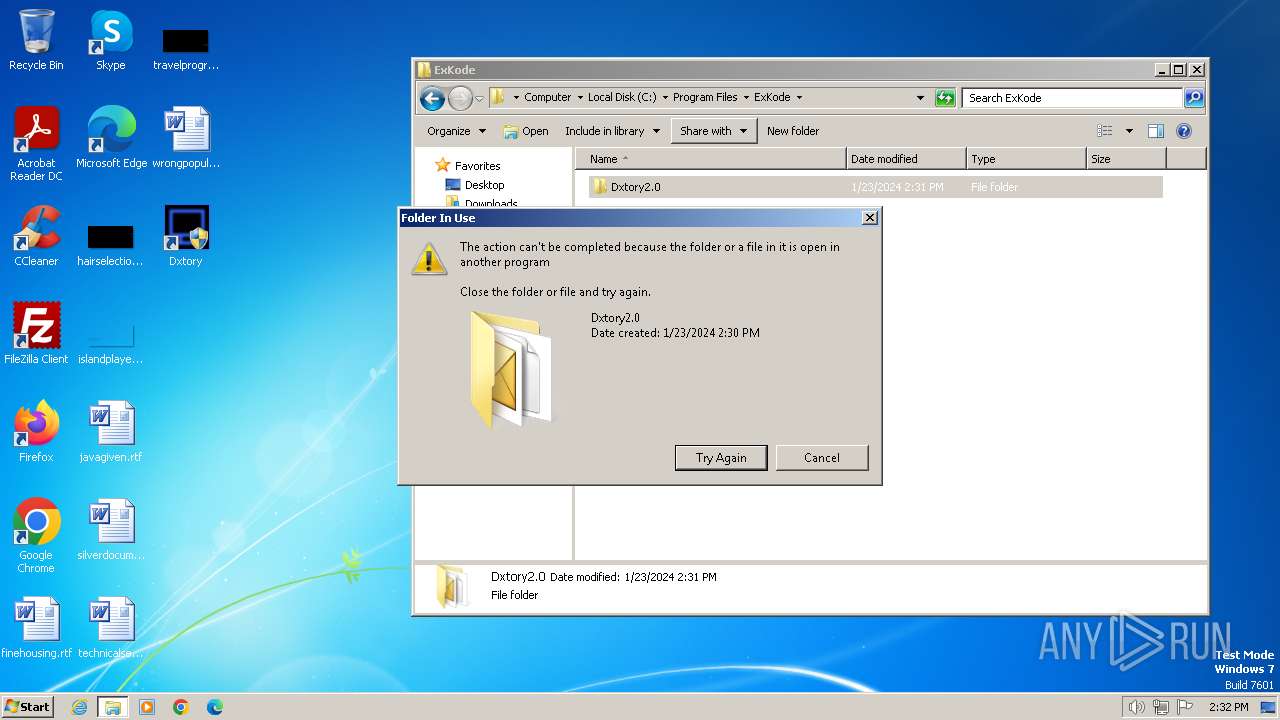
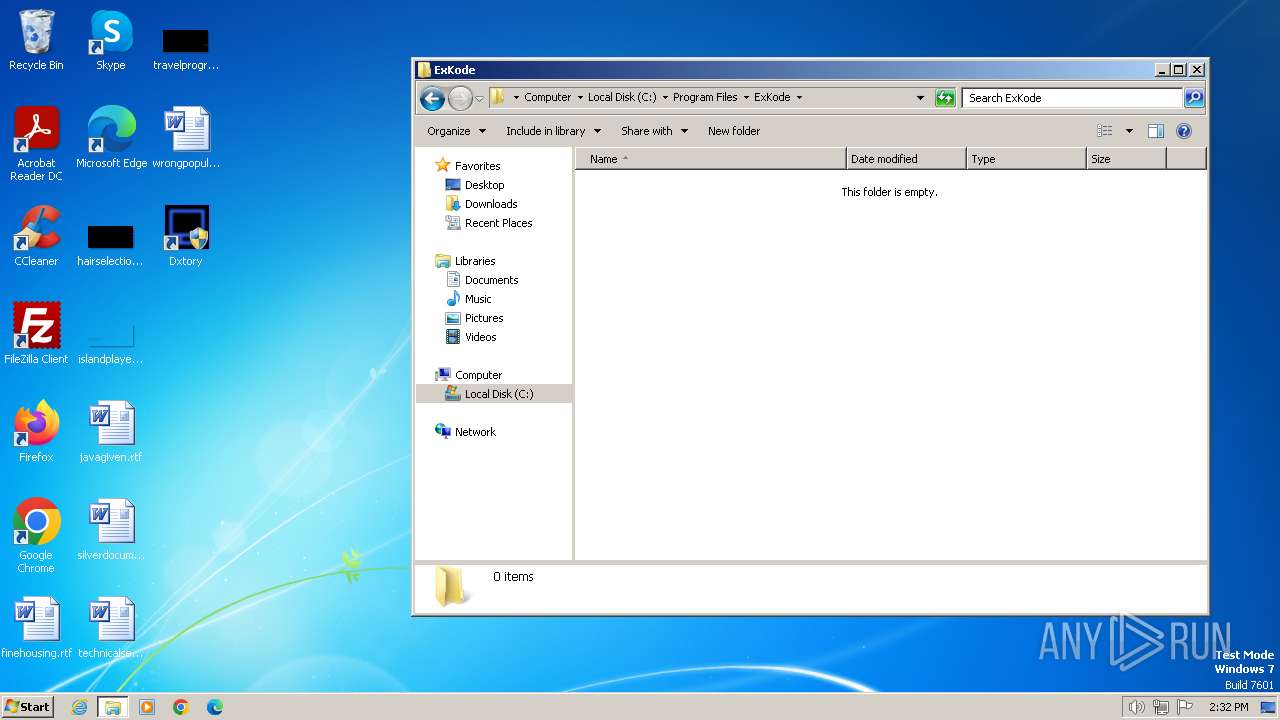
Creates files in the program directory
- DxtorySetup2.0.142.tmp (PID: 2728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
82
Monitored processes
26
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\ExKode\Dxtory2.0\Dxtory.exe" /BUILD_JUMPLIST | C:\Program Files\ExKode\Dxtory2.0\Dxtory.exe | — | LicReg.exe | |||||||||||
User: admin Company: ExKode Co. Ltd. Integrity Level: HIGH Description: Dxtory Exit code: 0 Version: 2.0.0.142 Modules
| |||||||||||||||
| 376 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2404.19200\DxtorySetup2.0.142.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2404.19200\DxtorySetup2.0.142.exe | WinRAR.exe | ||||||||||||
User: admin Company: ExKode Co. Ltd. Integrity Level: MEDIUM Description: Dxtory Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 448 | "C:\Program Files\ExKode\Dxtory2.0\Dxtory.exe" /BUILD_JUMPLIST | C:\Program Files\ExKode\Dxtory2.0\Dxtory.exe | — | DxtorySetup2.0.142.tmp | |||||||||||
User: admin Company: ExKode Co. Ltd. Integrity Level: HIGH Description: Dxtory Exit code: 0 Version: 2.0.0.142 Modules
| |||||||||||||||
| 452 | "C:\Users\admin\AppData\Local\Temp\is-4OK9V.tmp\DxtorySetup2.0.142.tmp" /SL5="$C013E,5604284,139264,C:\Users\admin\AppData\Local\Temp\Rar$EXb2404.19200\DxtorySetup2.0.142.exe" | C:\Users\admin\AppData\Local\Temp\is-4OK9V.tmp\DxtorySetup2.0.142.tmp | — | DxtorySetup2.0.142.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 784 | "C:\Program Files\ExKode\Dxtory2.0\Dxtory.exe" | C:\Program Files\ExKode\Dxtory2.0\Dxtory.exe | — | explorer.exe | |||||||||||
User: admin Company: ExKode Co. Ltd. Integrity Level: MEDIUM Description: Dxtory Exit code: 3221226540 Version: 2.0.0.142 Modules
| |||||||||||||||
| 992 | "C:\Program Files\ExKode\Dxtory2.0\UpdateChecker.exe" | C:\Program Files\ExKode\Dxtory2.0\UpdateChecker.exe | — | Dxtory.exe | |||||||||||
User: admin Company: Dxtory Software Integrity Level: HIGH Description: Update Checker Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 1112 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1236 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\ExKode\Dxtory2.0\DxtoryVideo.dll" | C:\Windows\System32\regsvr32.exe | — | DxtorySetup2.0.142.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1376 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2112 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2404.19200\DxtorySetup2.0.142.exe" /SPAWNWND=$B016C /NOTIFYWND=$C013E | C:\Users\admin\AppData\Local\Temp\Rar$EXb2404.19200\DxtorySetup2.0.142.exe | DxtorySetup2.0.142.tmp | ||||||||||||
User: admin Company: ExKode Co. Ltd. Integrity Level: HIGH Description: Dxtory Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
22 254
Read events
21 907
Write events
328
Delete events
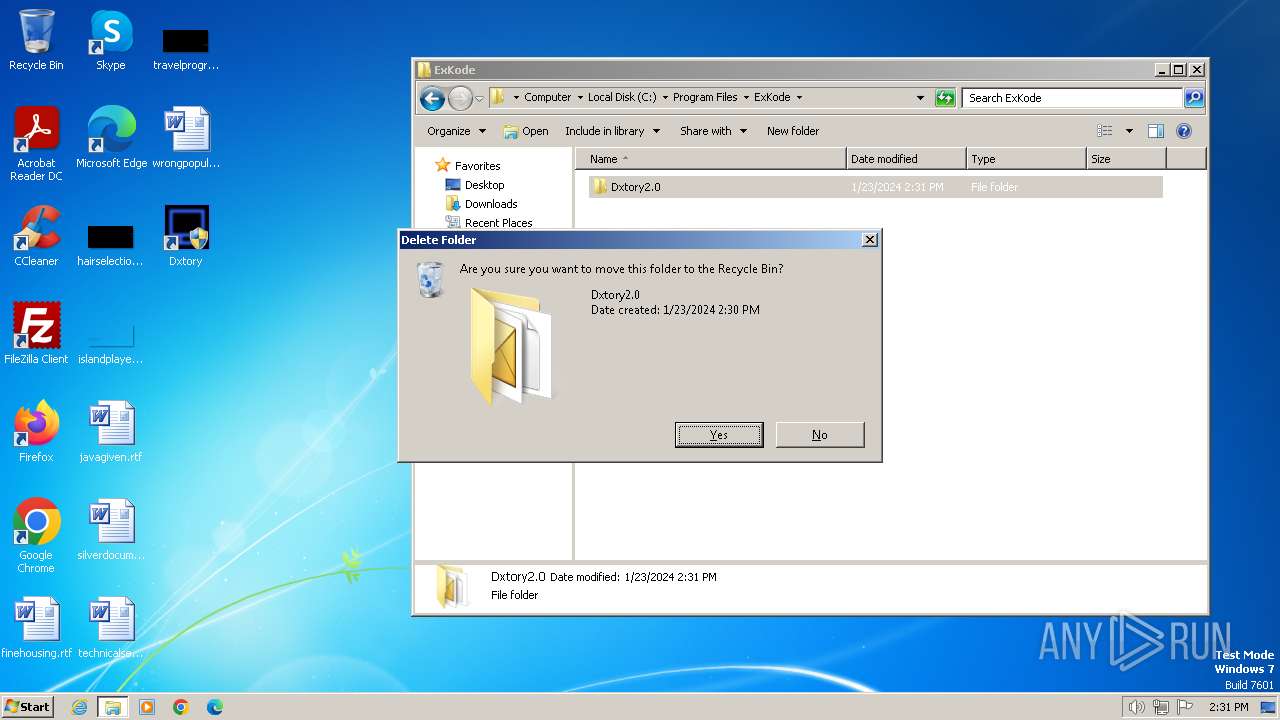
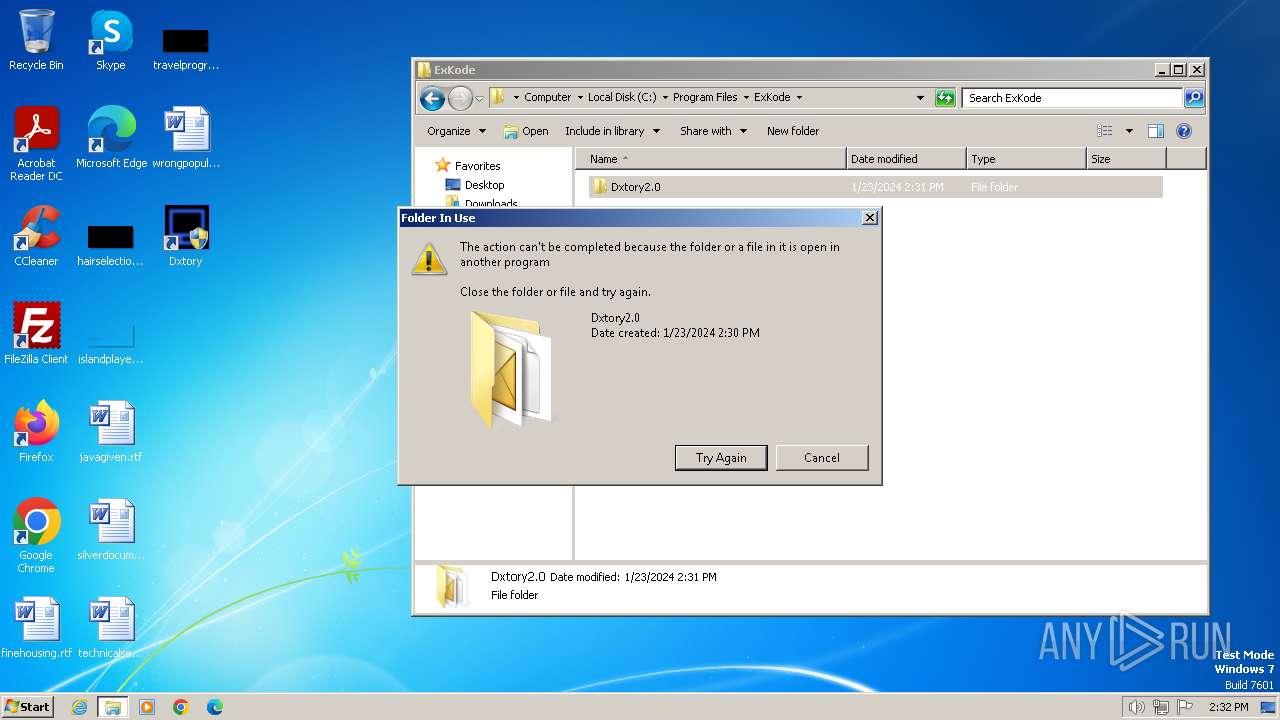
19
Modification events
| (PID) Process: | (2404) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
44
Suspicious files
37
Text files
41
Unknown types
0
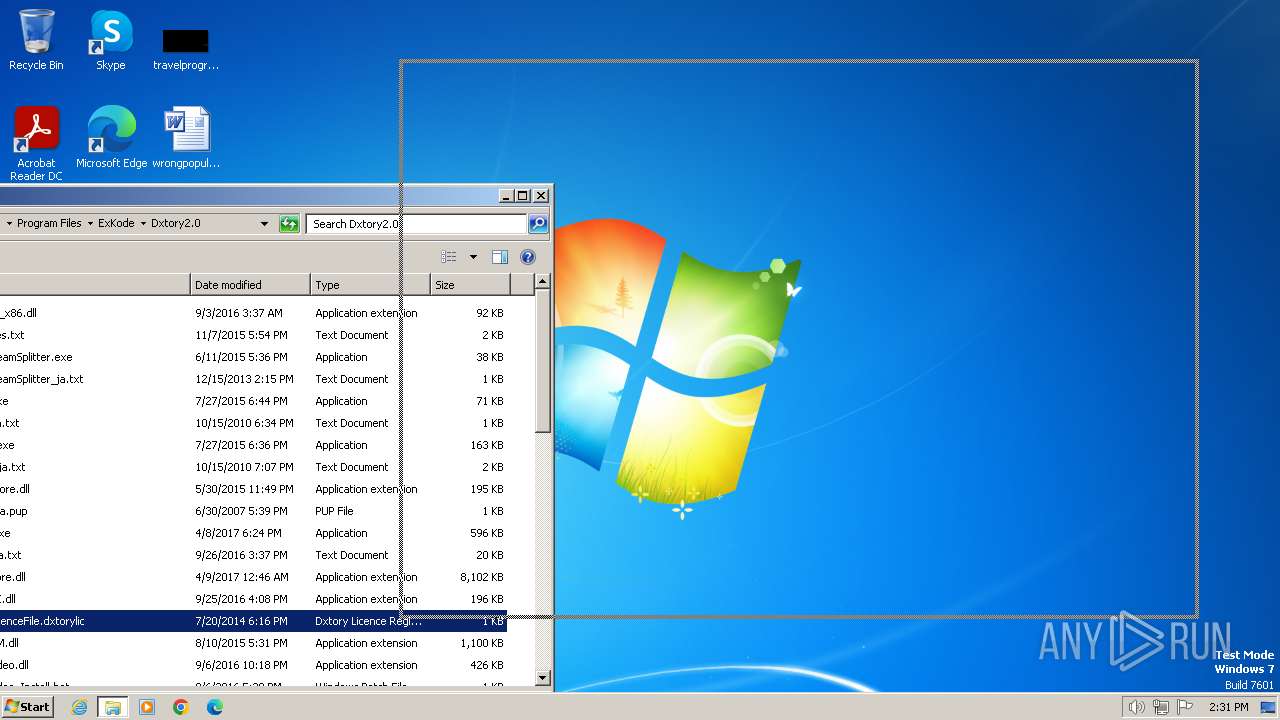
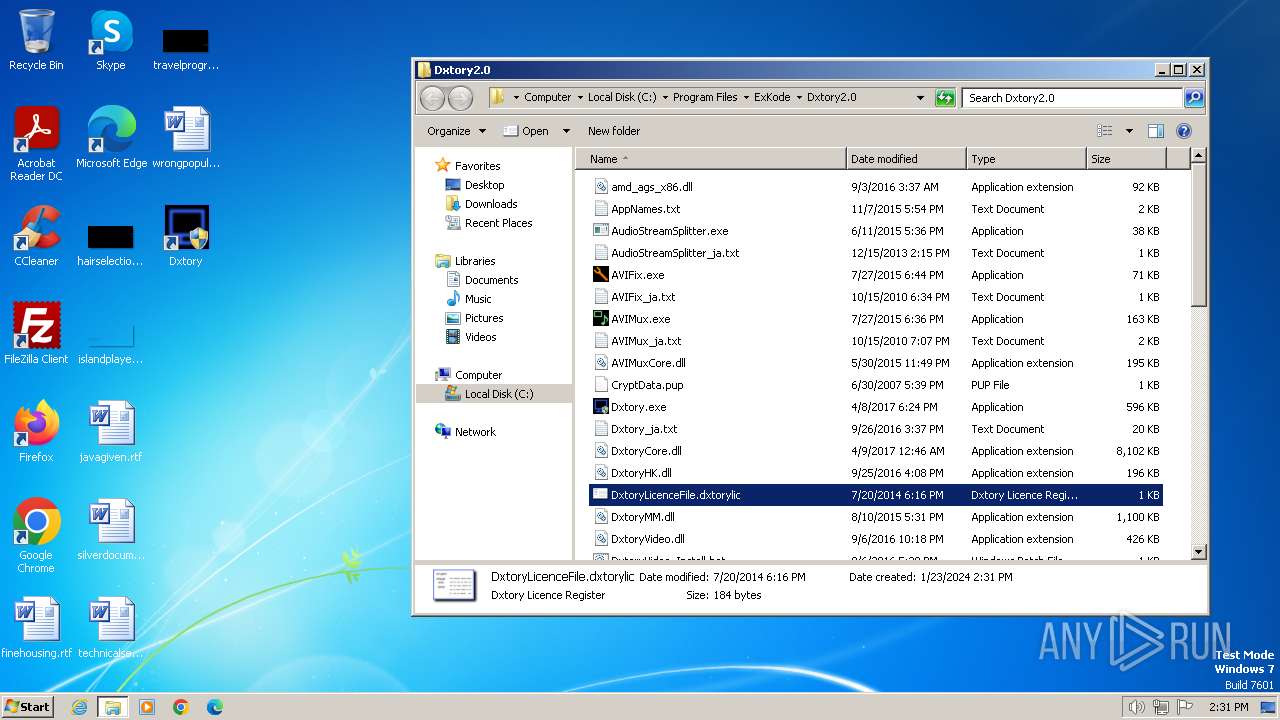
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
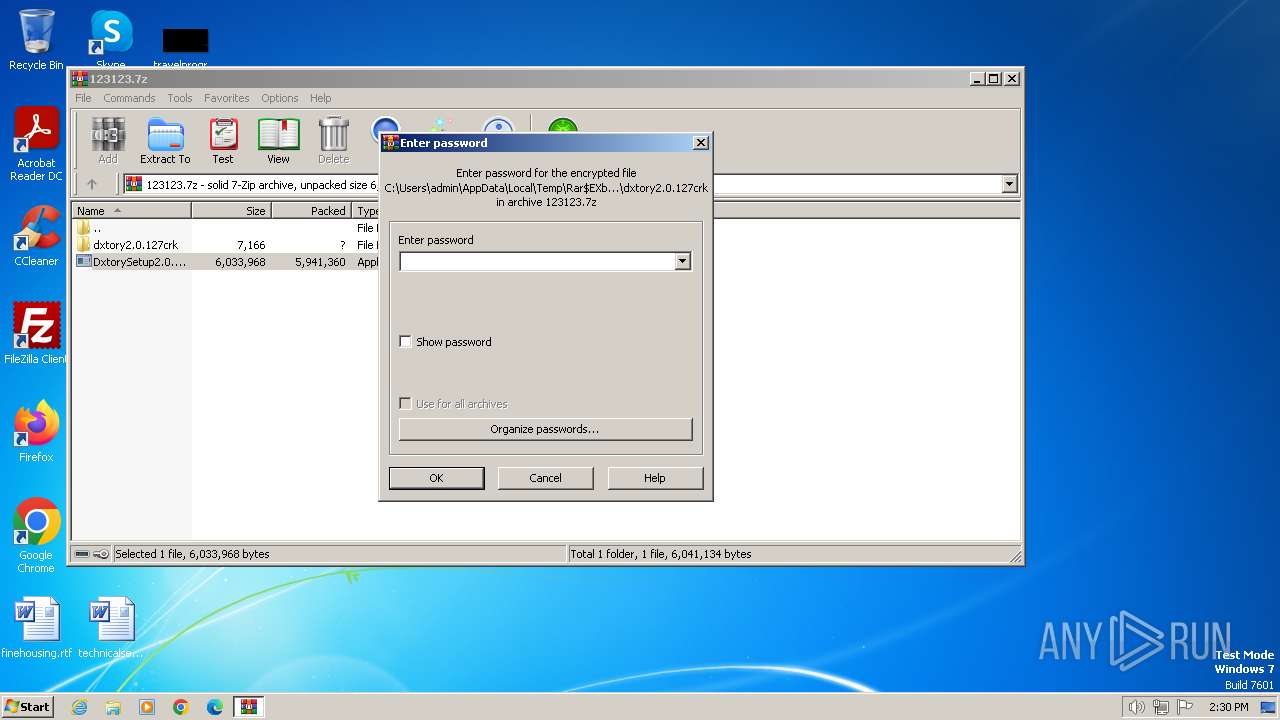
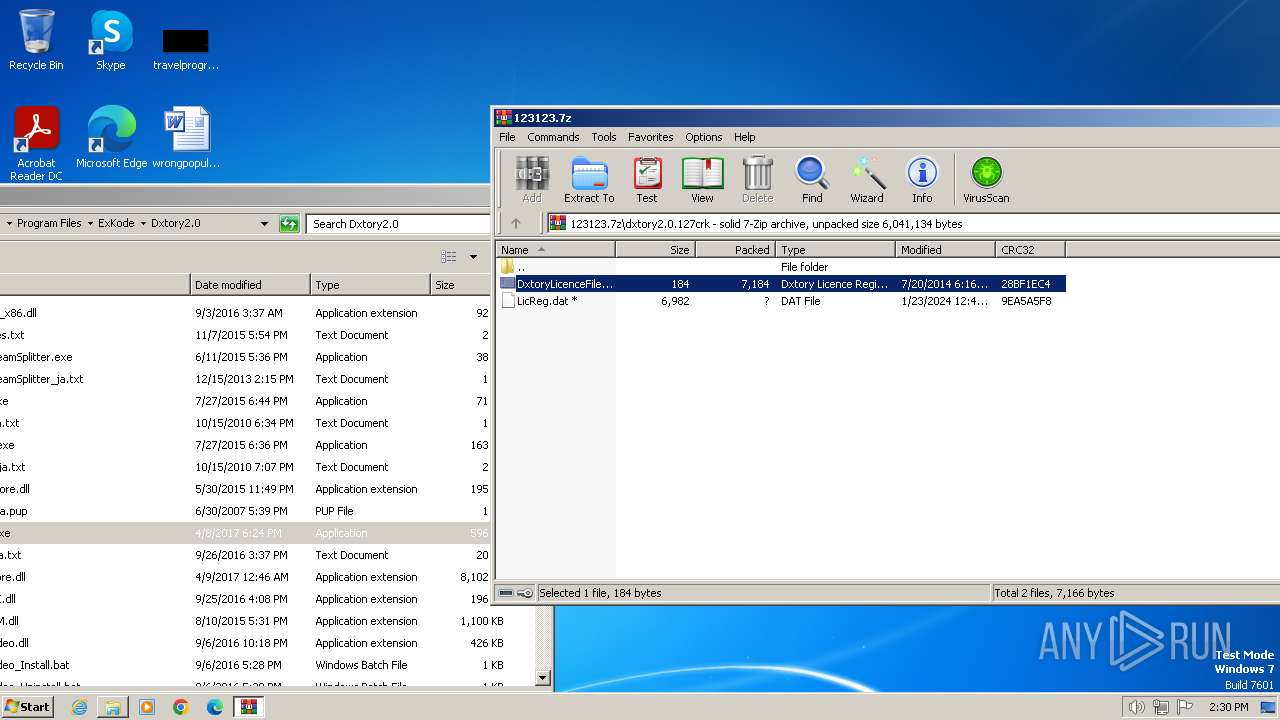
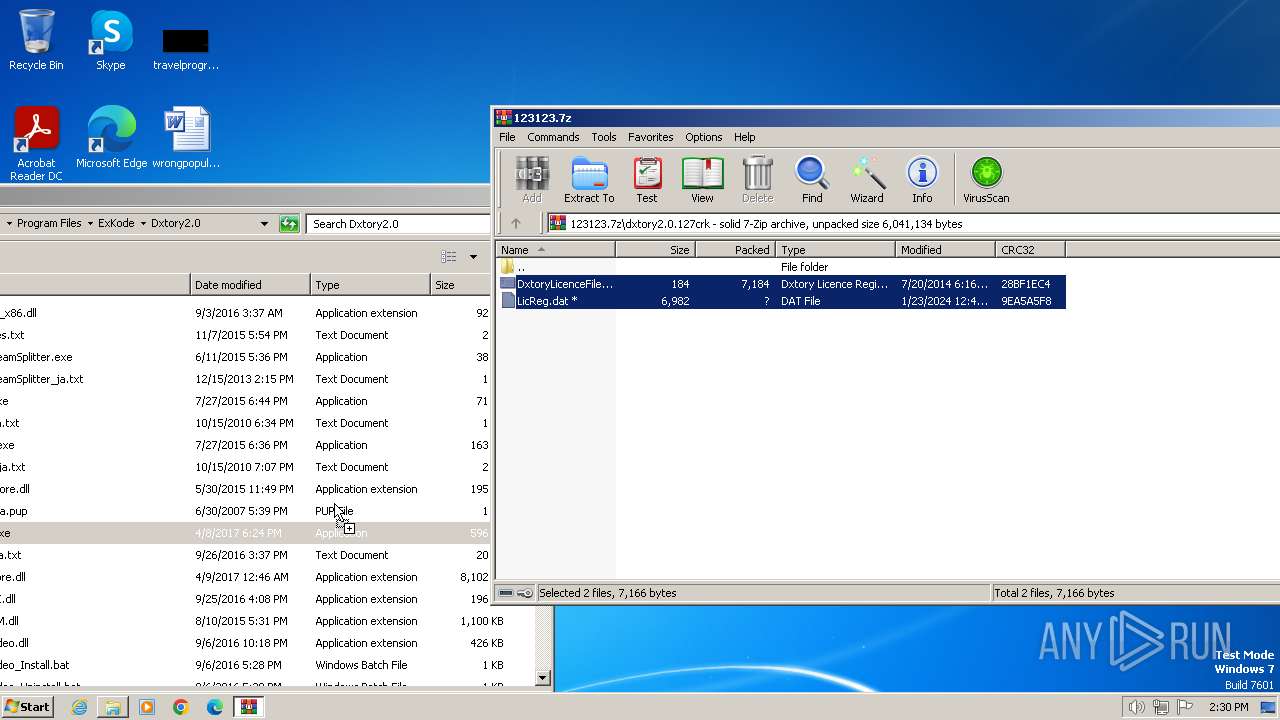
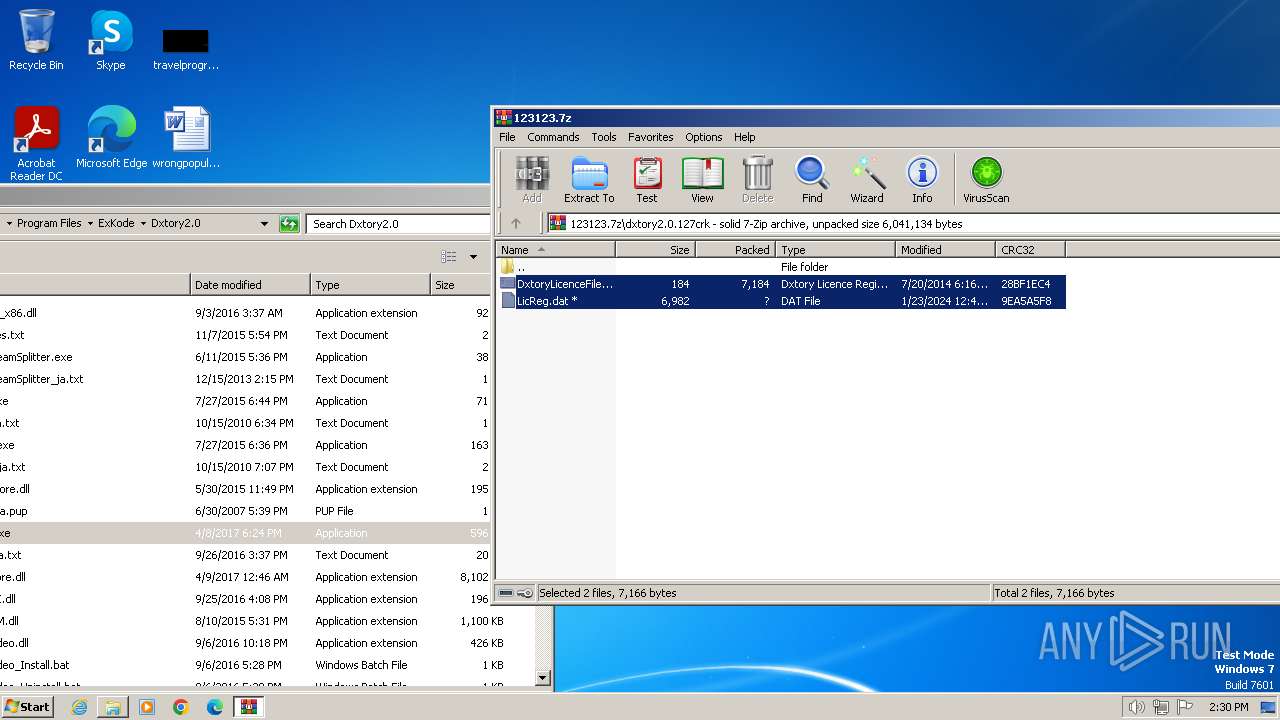
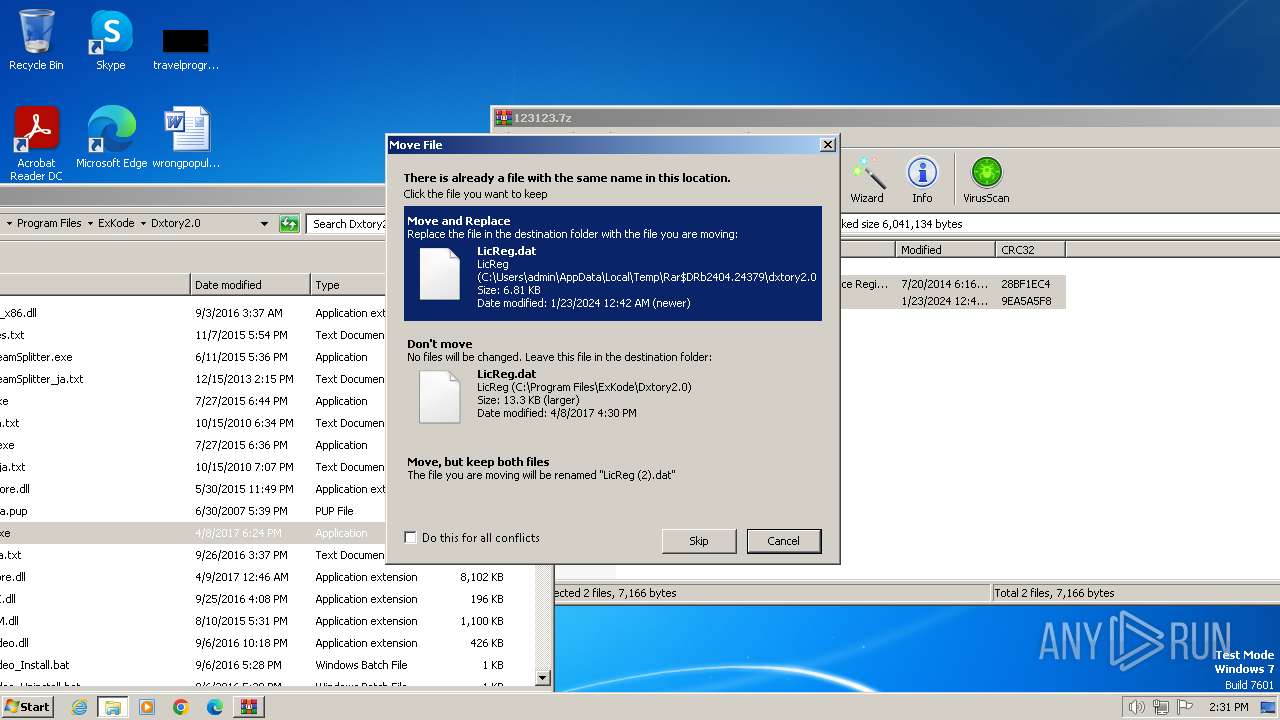
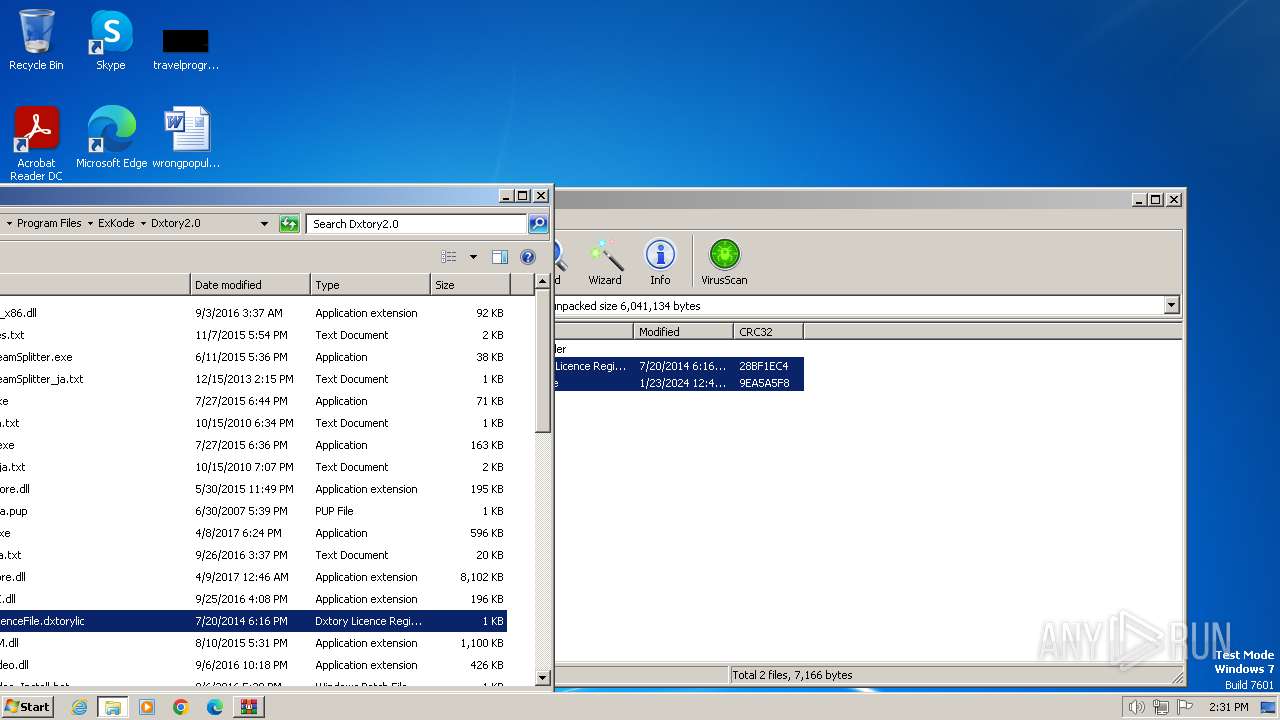
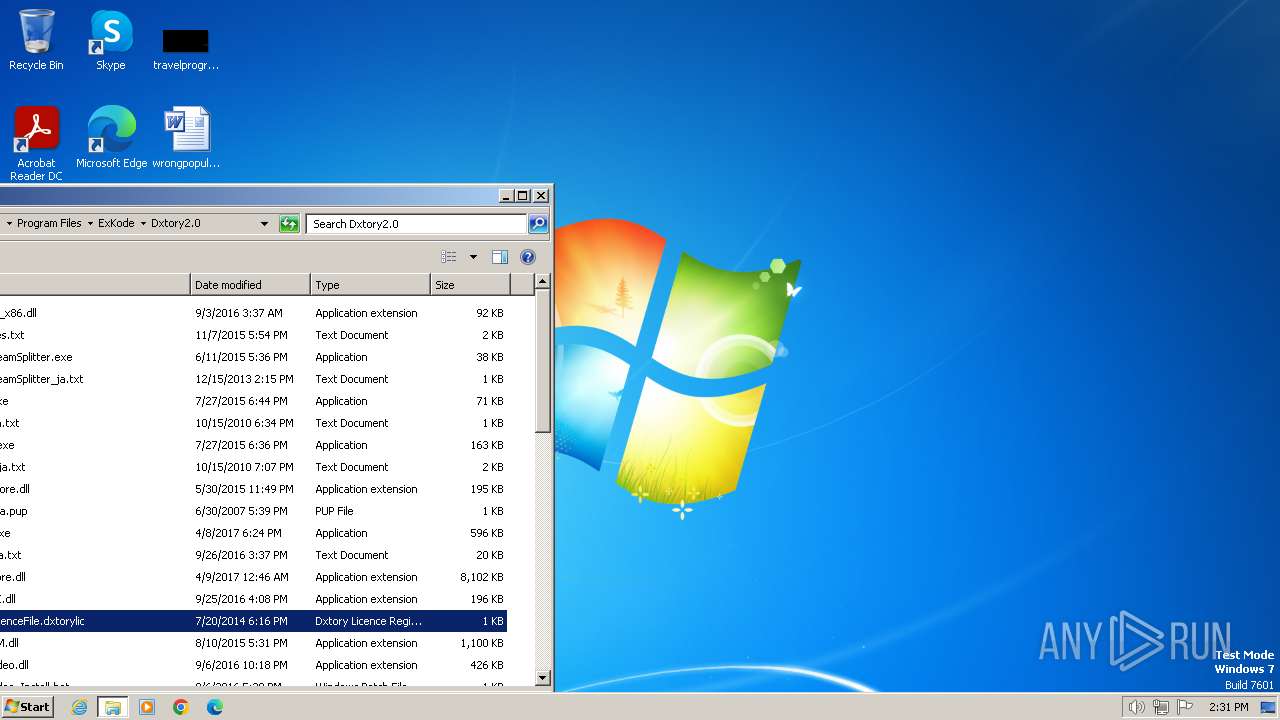
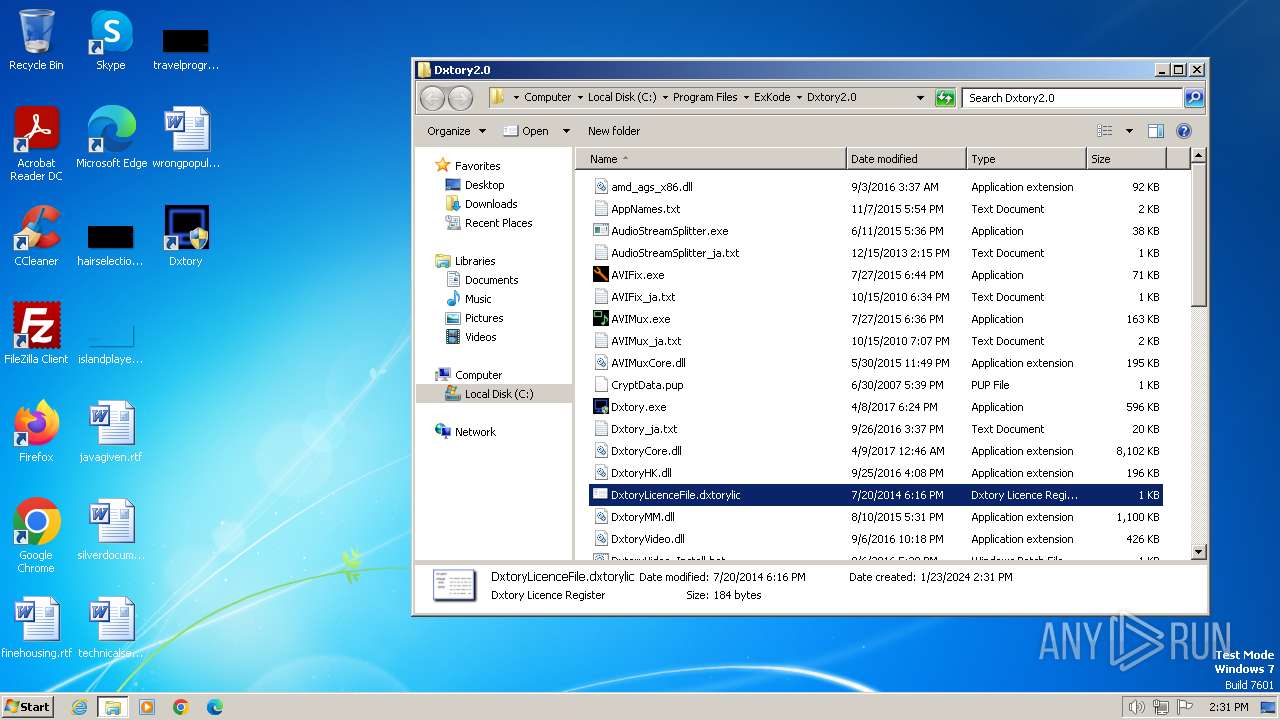
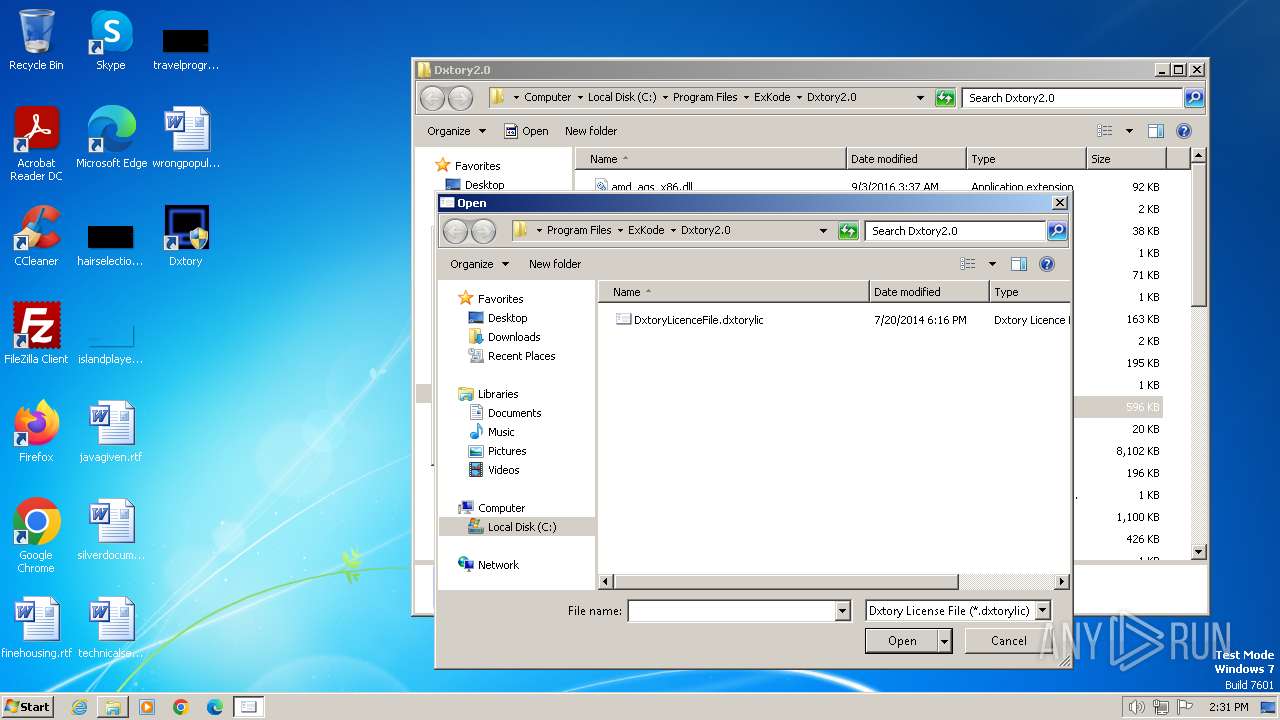
| 2404 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2404.19200\dxtory2.0.127crk\DxtoryLicenceFile.dxtorylic | binary | |
MD5:D615B3865F9148906208BAC07249A504 | SHA256:FE7FBA4DE836CA13B02D00ED2E10FC04A2EE6DF50DC2BDD2BF9AECA98DFB73D2 | |||
| 2728 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\is-KHVLH.tmp | text | |
MD5:3119E45A4338D49B1C4B74761EA5795E | SHA256:33F9F7D352488A8B52E2AC23A56D9E0B8F7E44C3A745865C41F2D1A4E7C9F951 | |||
| 2728 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\is-4JT9U.tmp | executable | |
MD5:90FC14379DAD173AB5A76001F57E39C9 | SHA256:C5108CE31C85C1C5D953D3F632E2728DB973EAE72A453AE5C8D218474D3F4E18 | |||
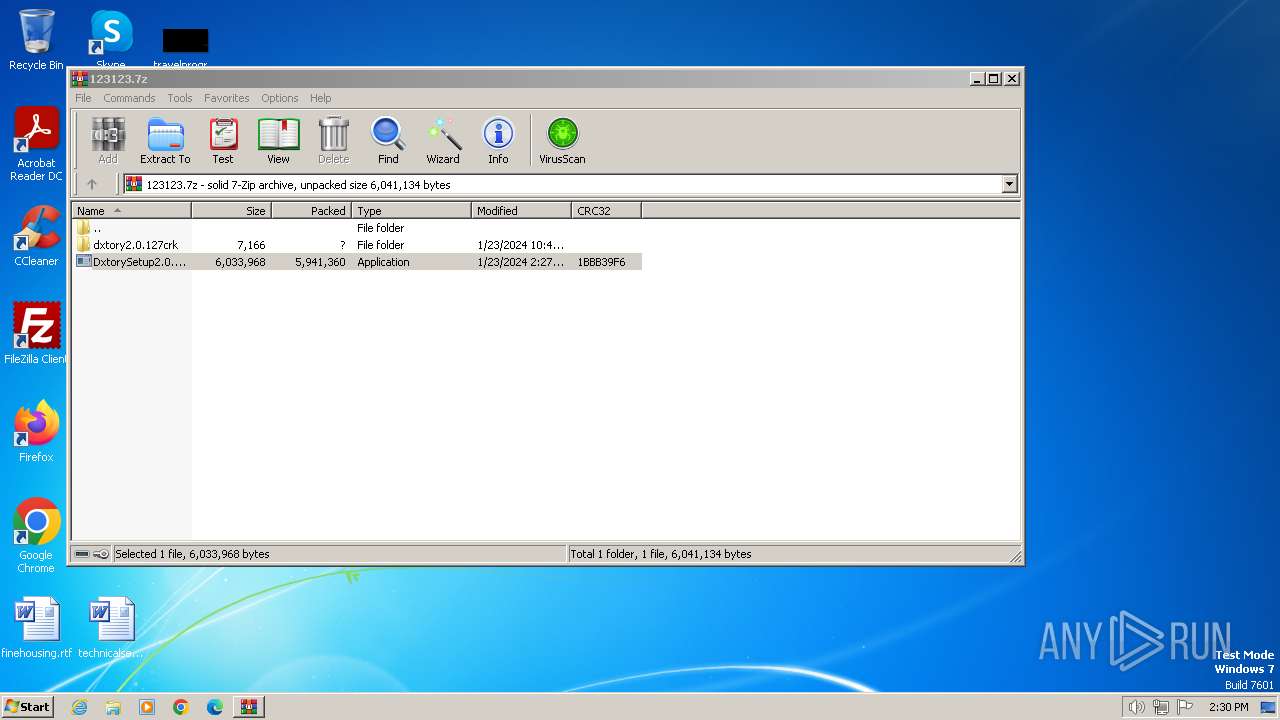
| 2404 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2404.19200\DxtorySetup2.0.142.exe | executable | |
MD5:33D8DA8B8B324E00F0FAEC75958B71AA | SHA256:8001D0A7B431EC1AD539526521871765A72F313178F6B7D3E2F9DAAB595A3F95 | |||
| 2728 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\AVIMuxCore.dll | executable | |
MD5:90FC14379DAD173AB5A76001F57E39C9 | SHA256:C5108CE31C85C1C5D953D3F632E2728DB973EAE72A453AE5C8D218474D3F4E18 | |||
| 2112 | DxtorySetup2.0.142.exe | C:\Users\admin\AppData\Local\Temp\is-9GT07.tmp\DxtorySetup2.0.142.tmp | executable | |
MD5:B4182D49FE9ECF068312B8CB93077D9B | SHA256:8C15EDDD22511474F48660FAC4422796D2D01DD99845C49A30B8953434077709 | |||
| 2728 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\is-V7GQ5.tmp | executable | |
MD5:720FC1464F05AC2E691CB4C2BE93ABDC | SHA256:84661ACCEDCFC804A5747A347BED5E07A64BFFC27D8C940C1D7D0E848AA1DB27 | |||
| 2728 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\is-GJUFR.tmp | executable | |
MD5:F2AE8FB4DDF3F8062353A0998487F458 | SHA256:FAA34944CCCA53266567D1A4C93AAA80392124AD353DD32BEF5189E53C492B9F | |||
| 2728 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\AVIMux.exe | executable | |
MD5:F2AE8FB4DDF3F8062353A0998487F458 | SHA256:FAA34944CCCA53266567D1A4C93AAA80392124AD353DD32BEF5189E53C492B9F | |||
| 2728 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\is-LJT81.tmp | executable | |
MD5:B4182D49FE9ECF068312B8CB93077D9B | SHA256:8C15EDDD22511474F48660FAC4422796D2D01DD99845C49A30B8953434077709 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |