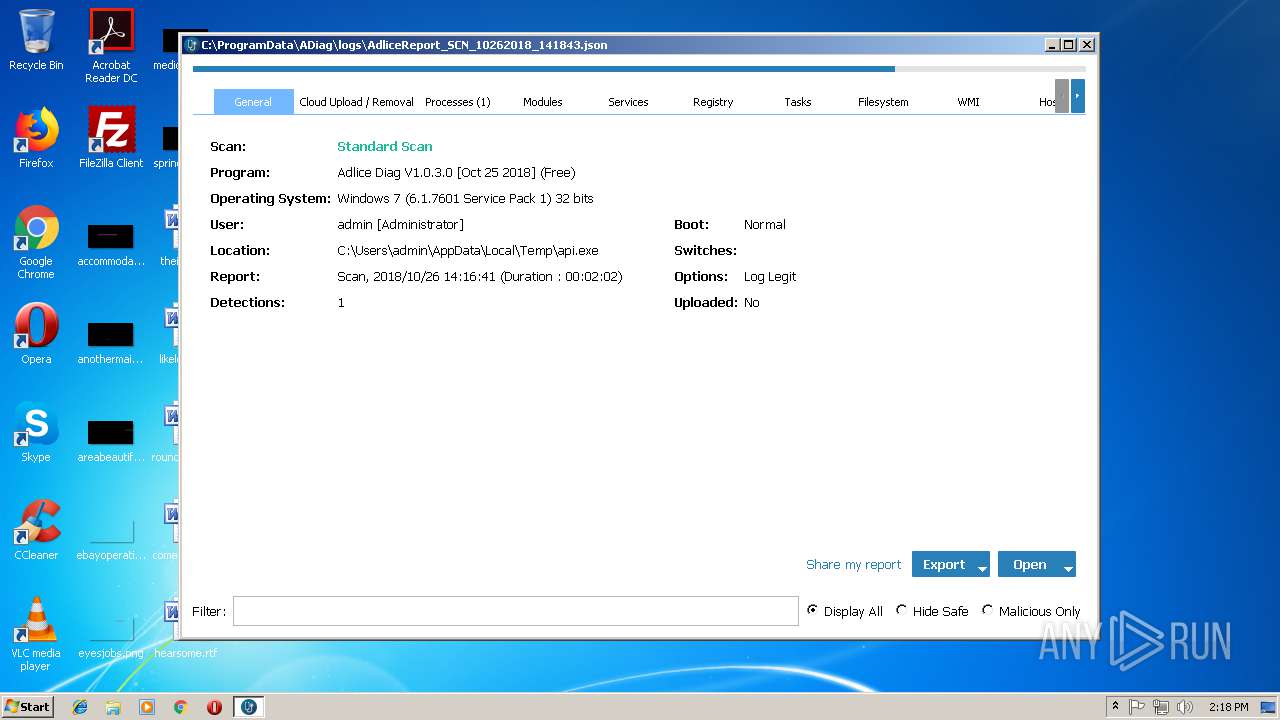
| download: | api |
| Full analysis: | https://app.any.run/tasks/dc799dbd-1c2b-466c-a976-22f67d1d3577 |
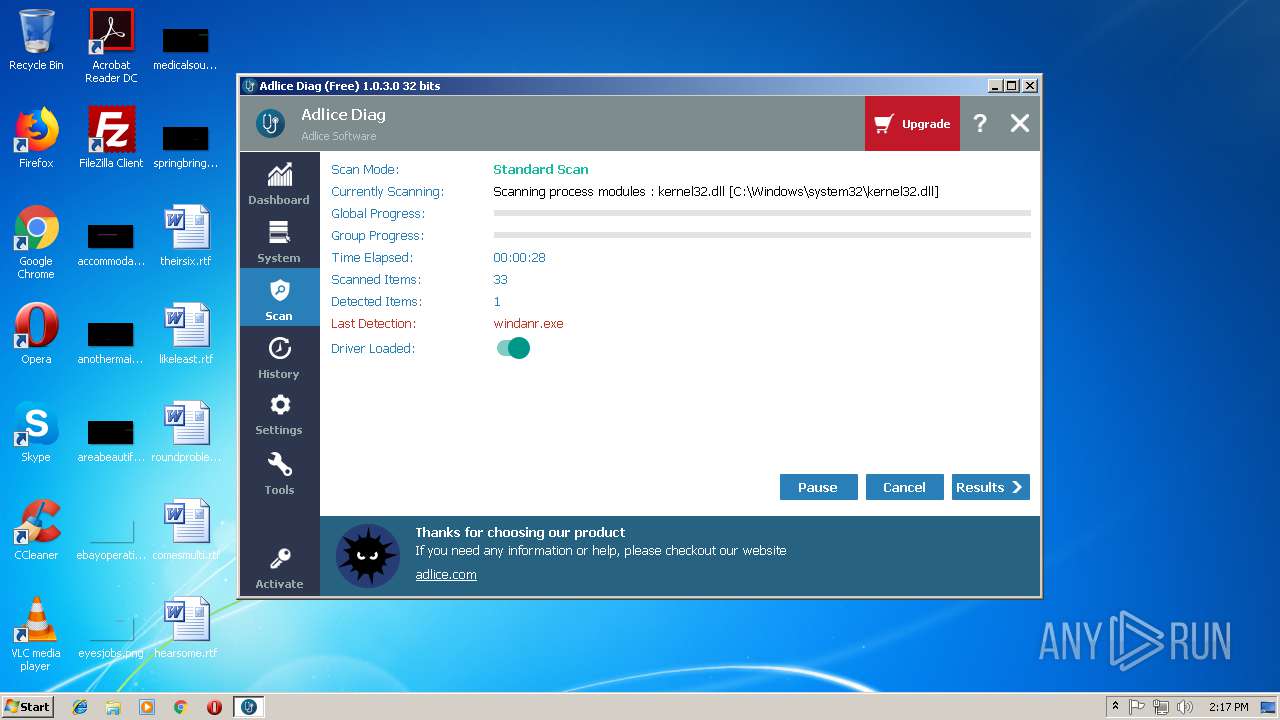
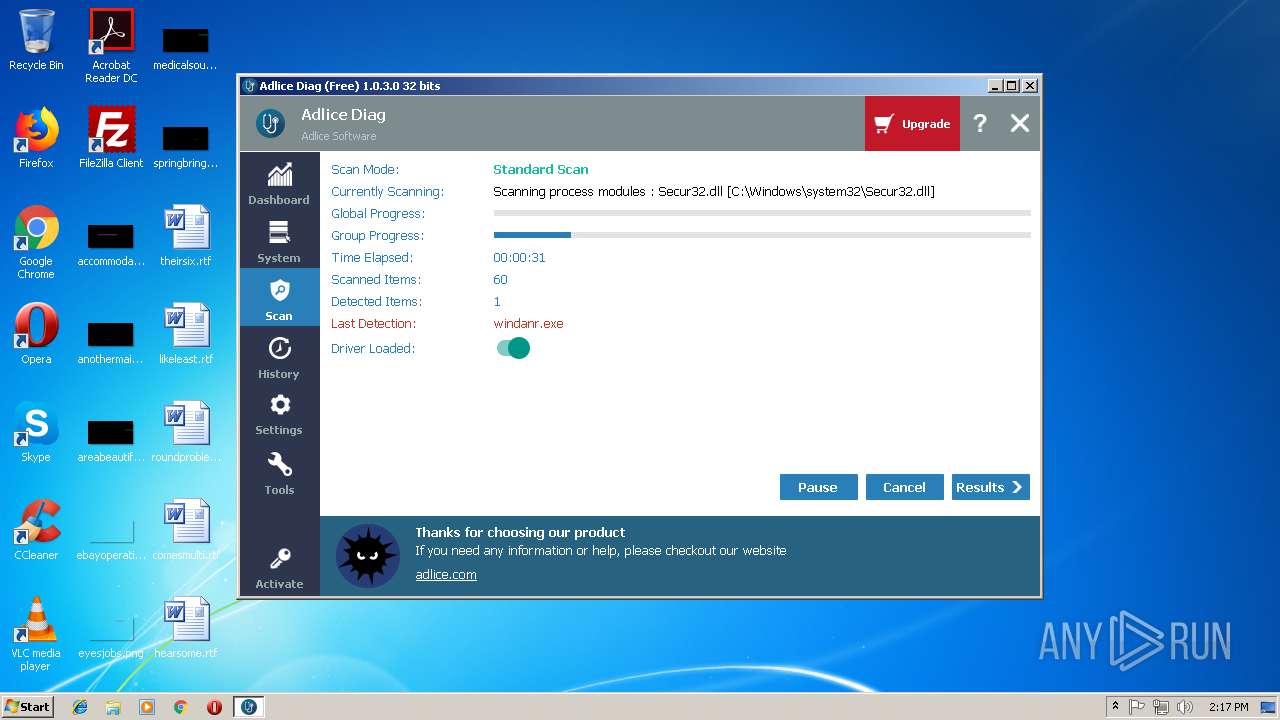
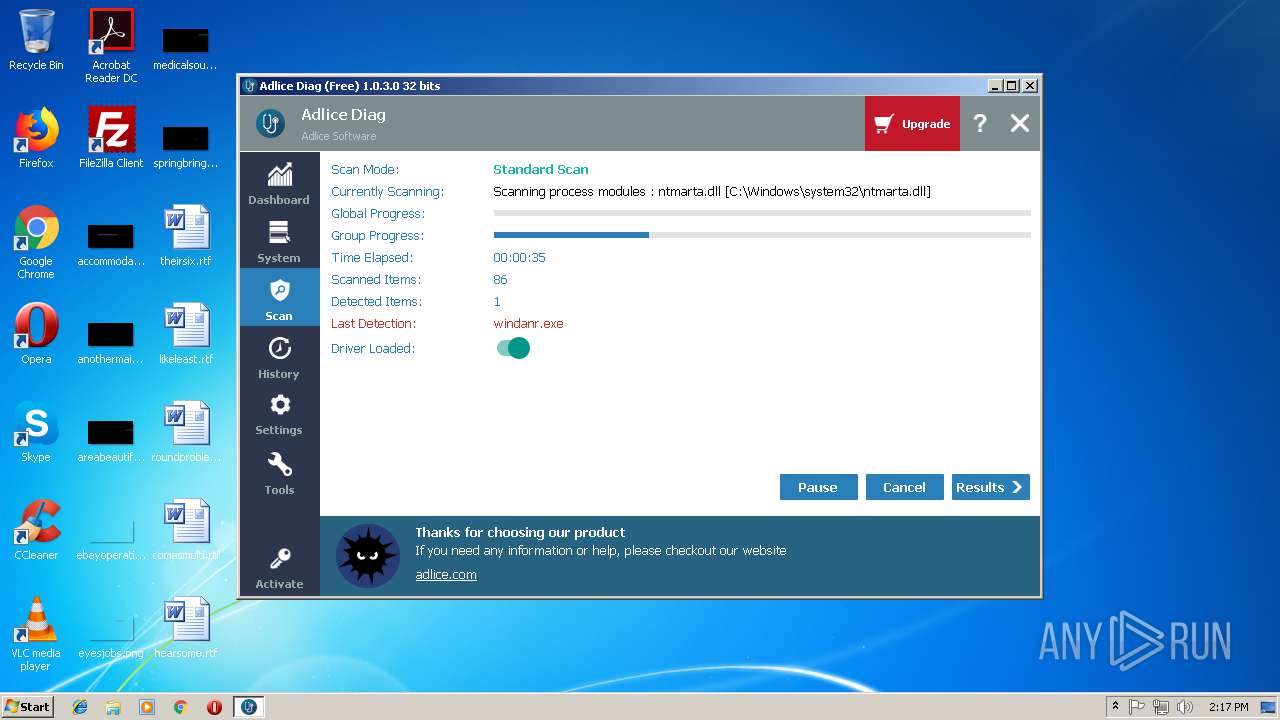
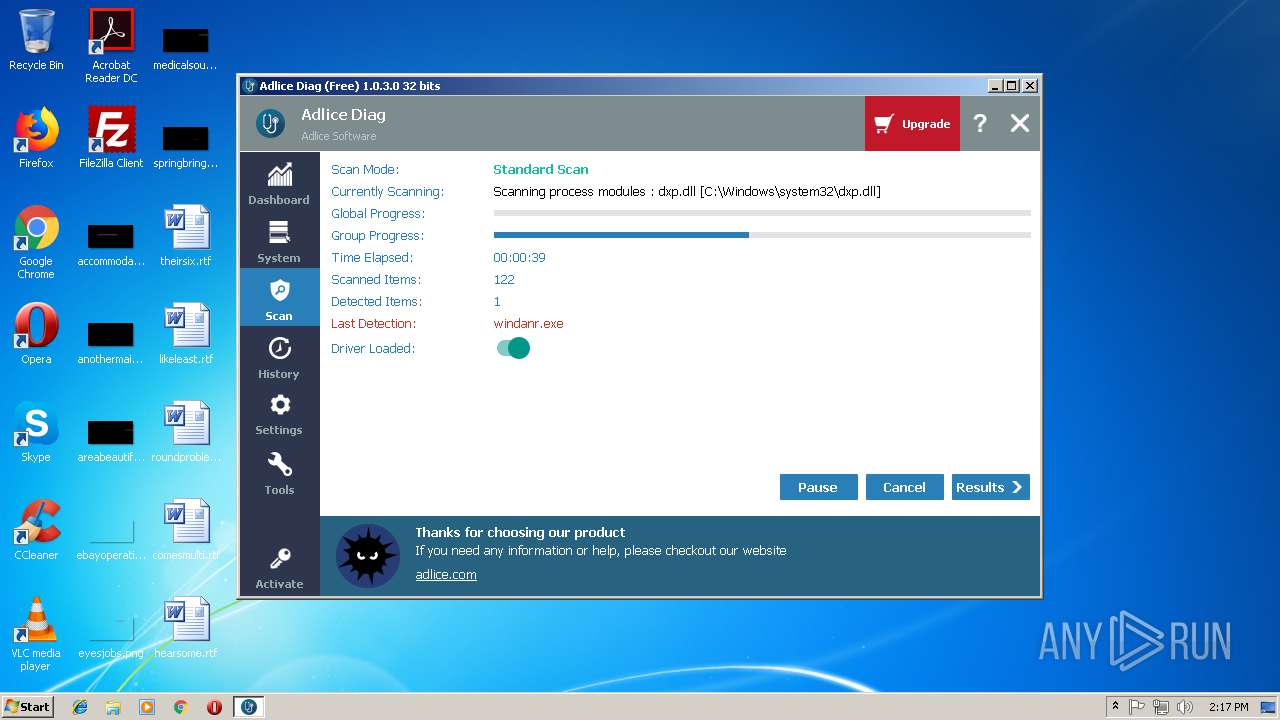
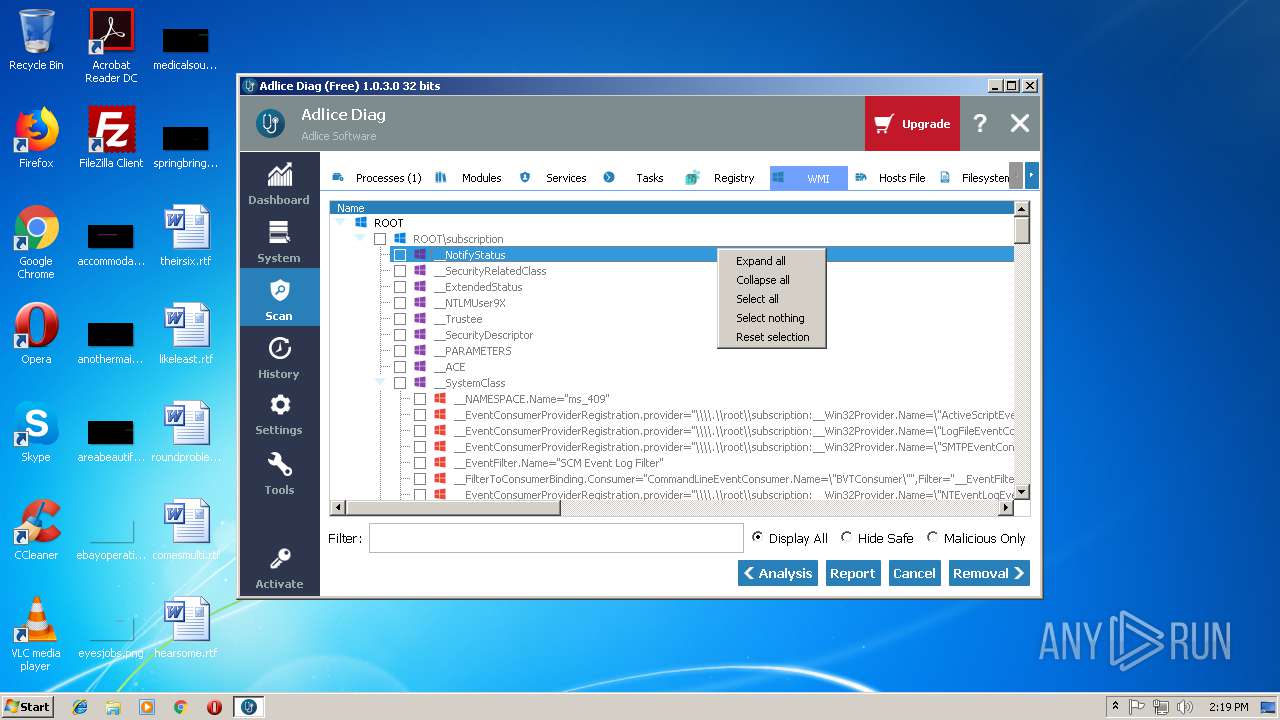
| Verdict: | Malicious activity |
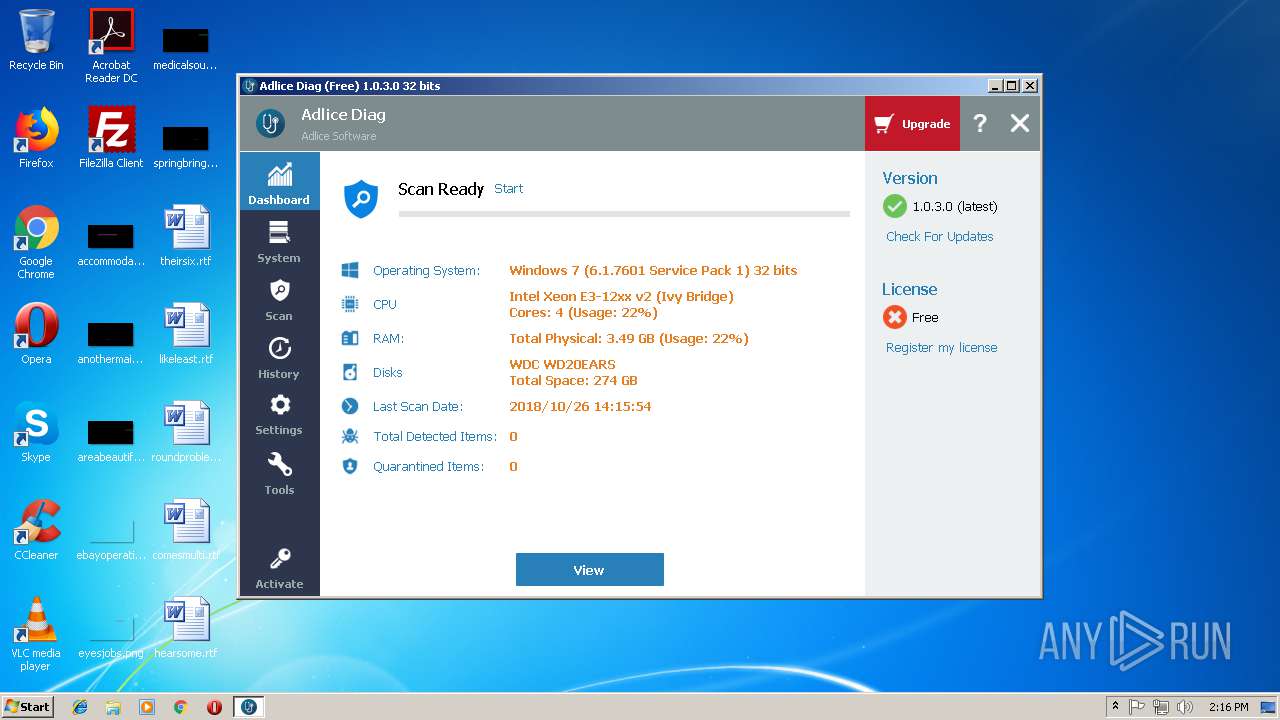
| Analysis date: | October 26, 2018, 13:14:43 |
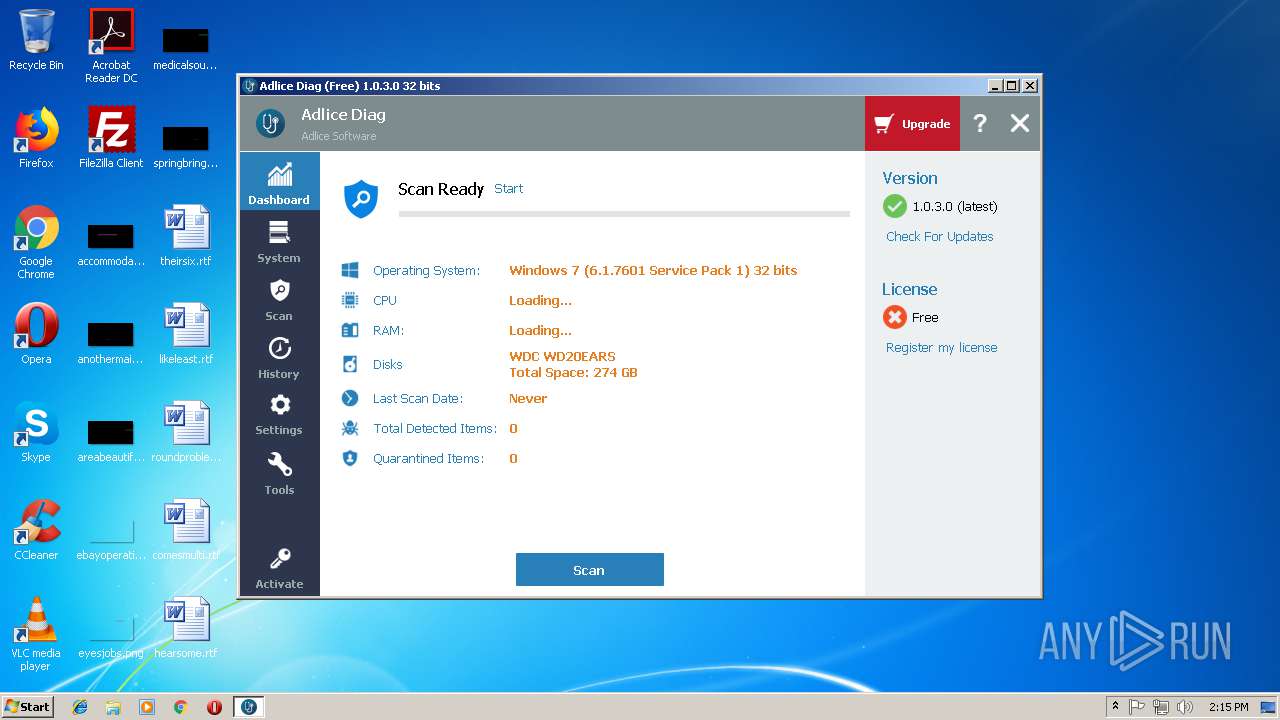
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D7A13D09AE40C01A8164BC76A5F9812D |
| SHA1: | 7D7BE18F2DBF4A72503EC4D561196F5C6C18AB68 |
| SHA256: | 4FC4384E0C72E64796A8DB0EE16E1DE956335570B3597540ED3964B4AF429C43 |
| SSDEEP: | 393216:4cyTfj9BTrixSa9LAiQds3Q5tL3UJsv6tWKFdu9Cg/GFO89/c:4cURB3a9LAbs3Q5N/J89/c |
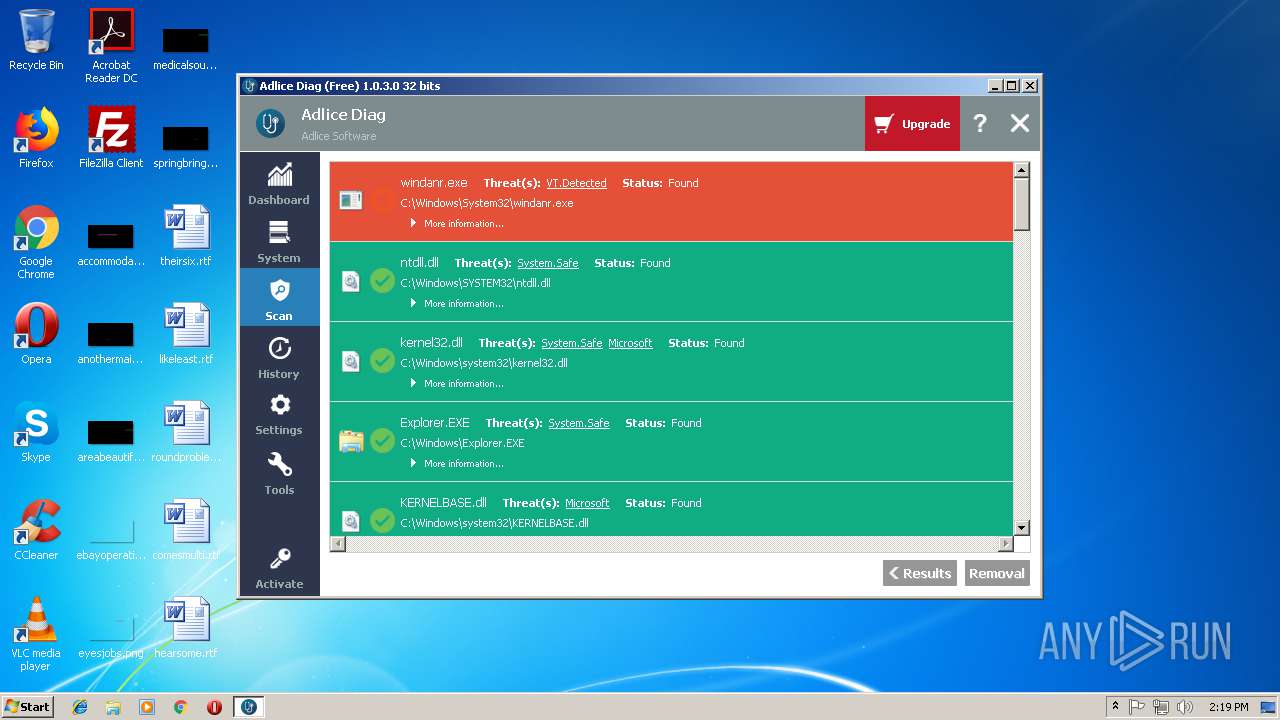
MALICIOUS
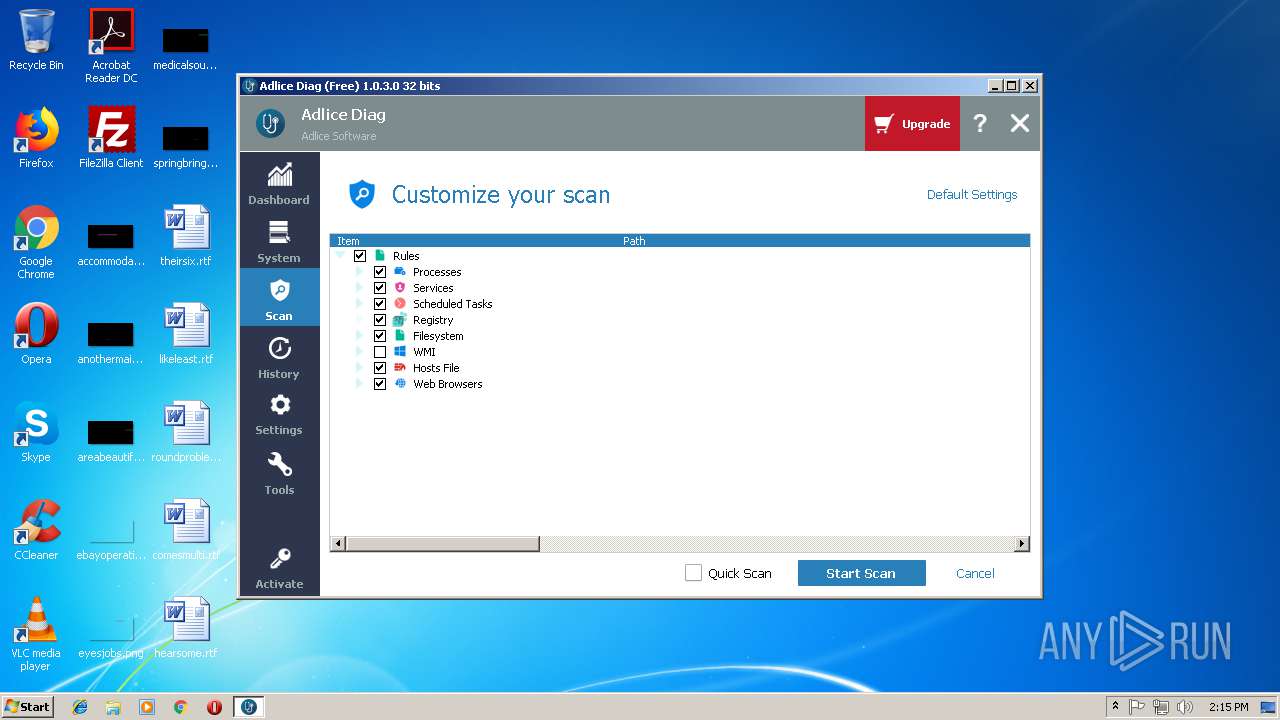
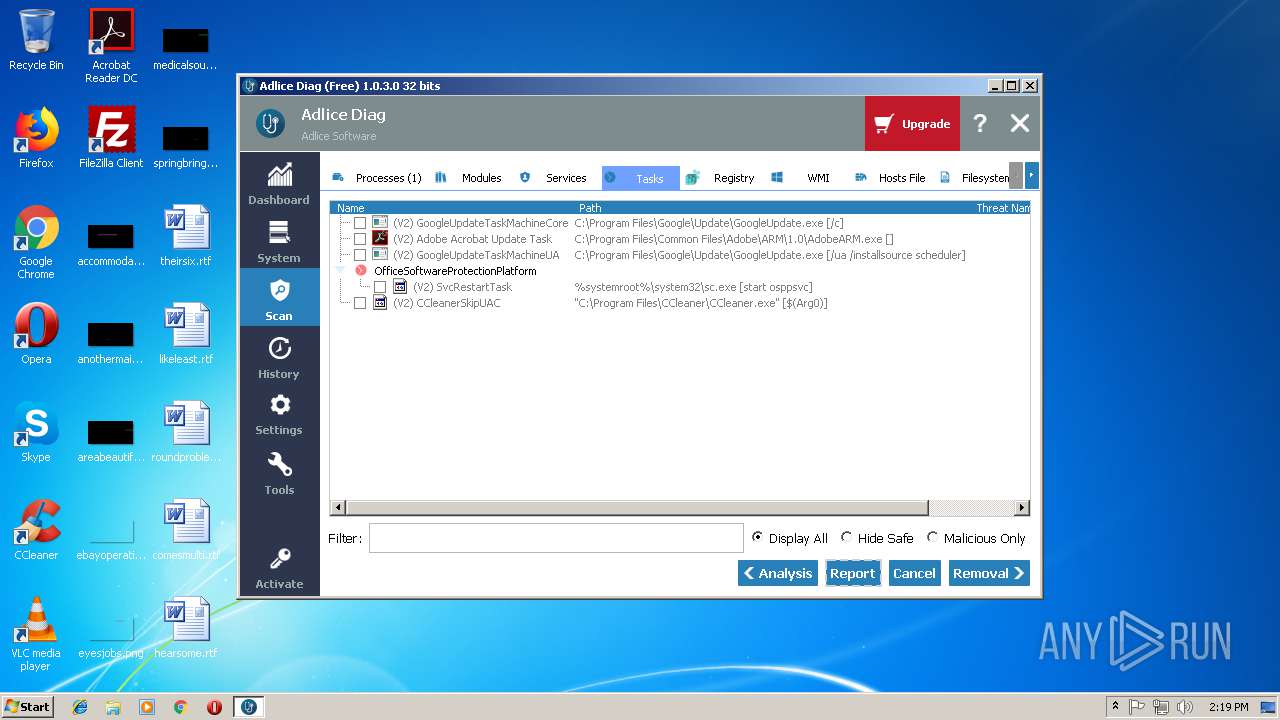
Loads the Task Scheduler DLL interface
- api.exe (PID: 3788)
Changes settings of System certificates
- api.exe (PID: 3788)
Loads the Task Scheduler COM API
- api.exe (PID: 3788)
SUSPICIOUS
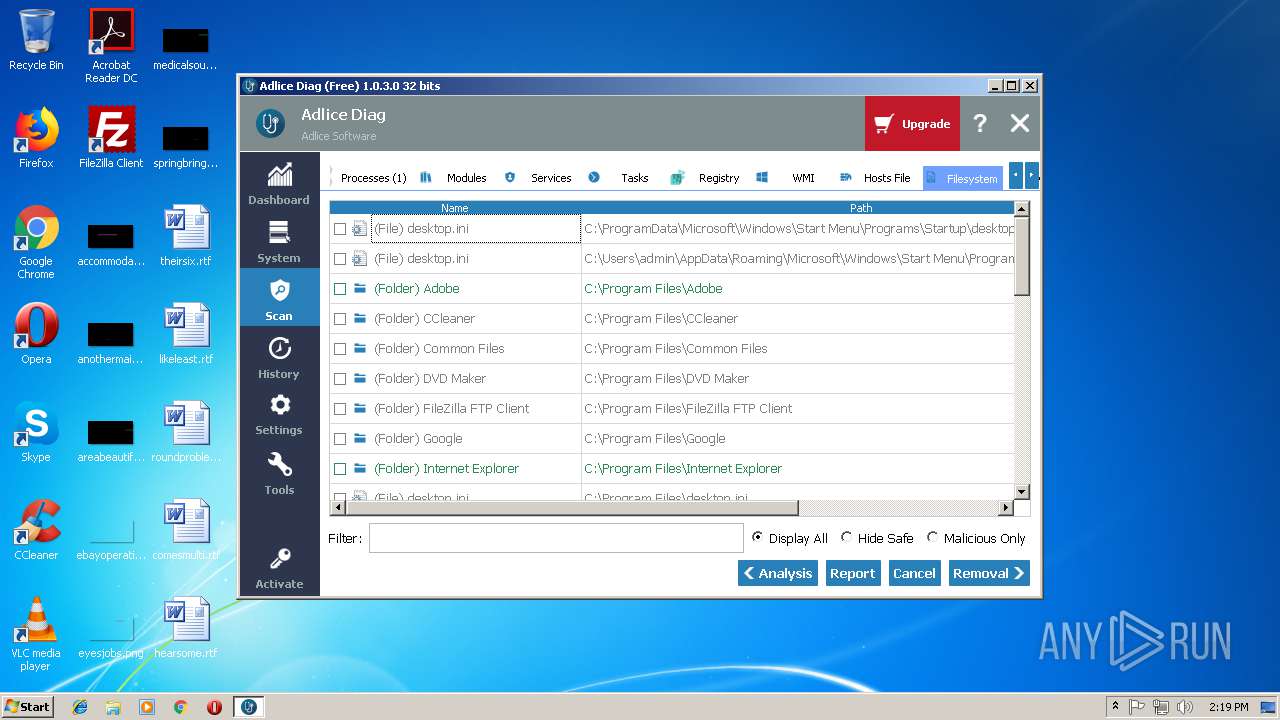
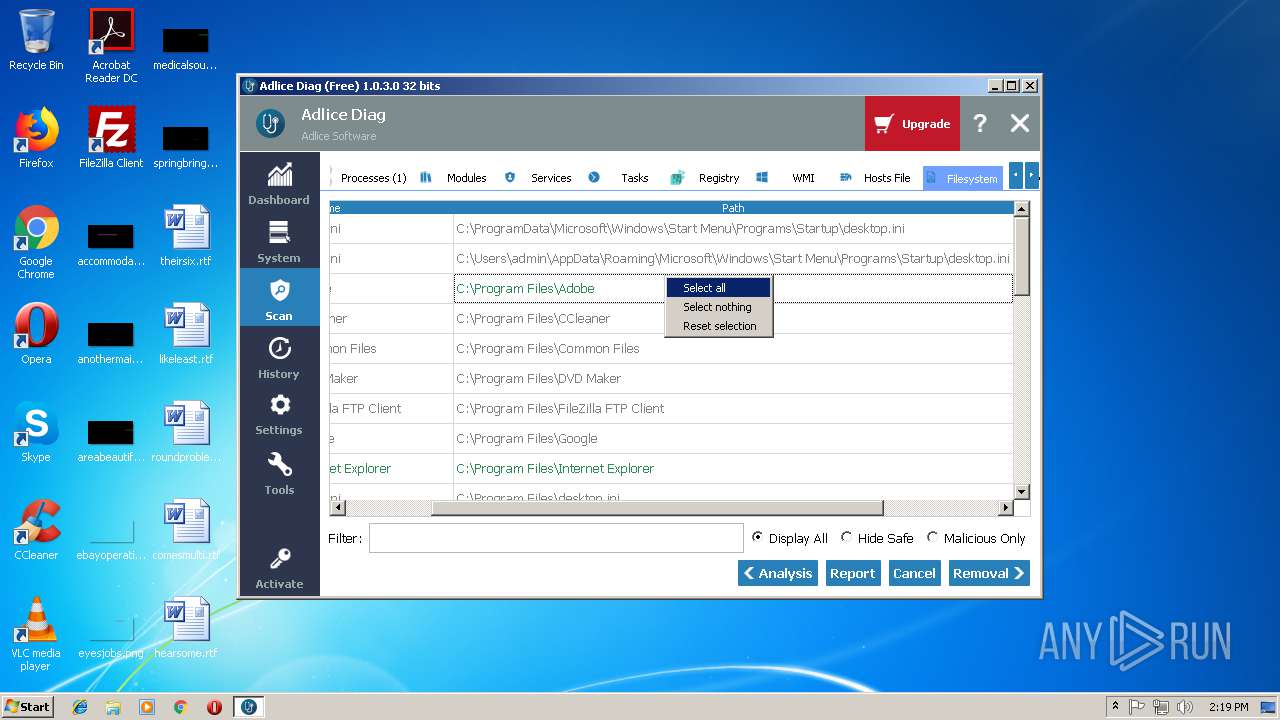
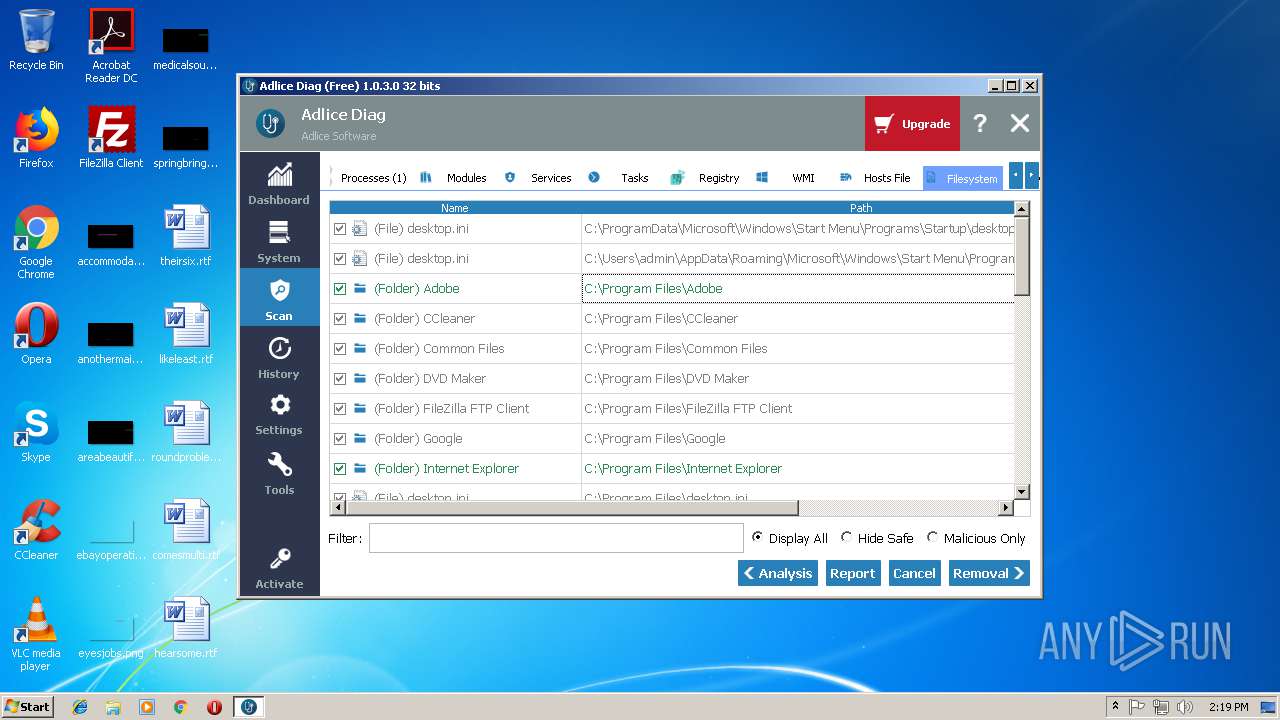
Creates files in the program directory
- api.exe (PID: 3788)
Low-level read access rights to disk partition
- api.exe (PID: 3788)
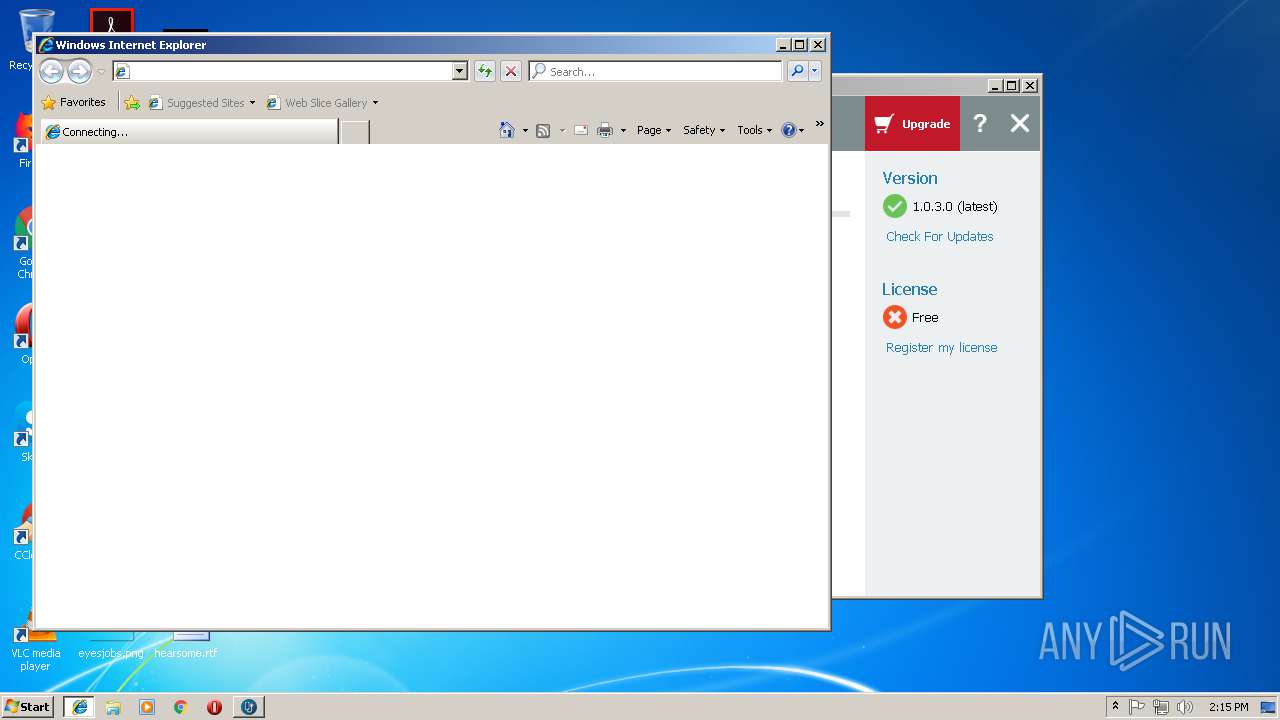
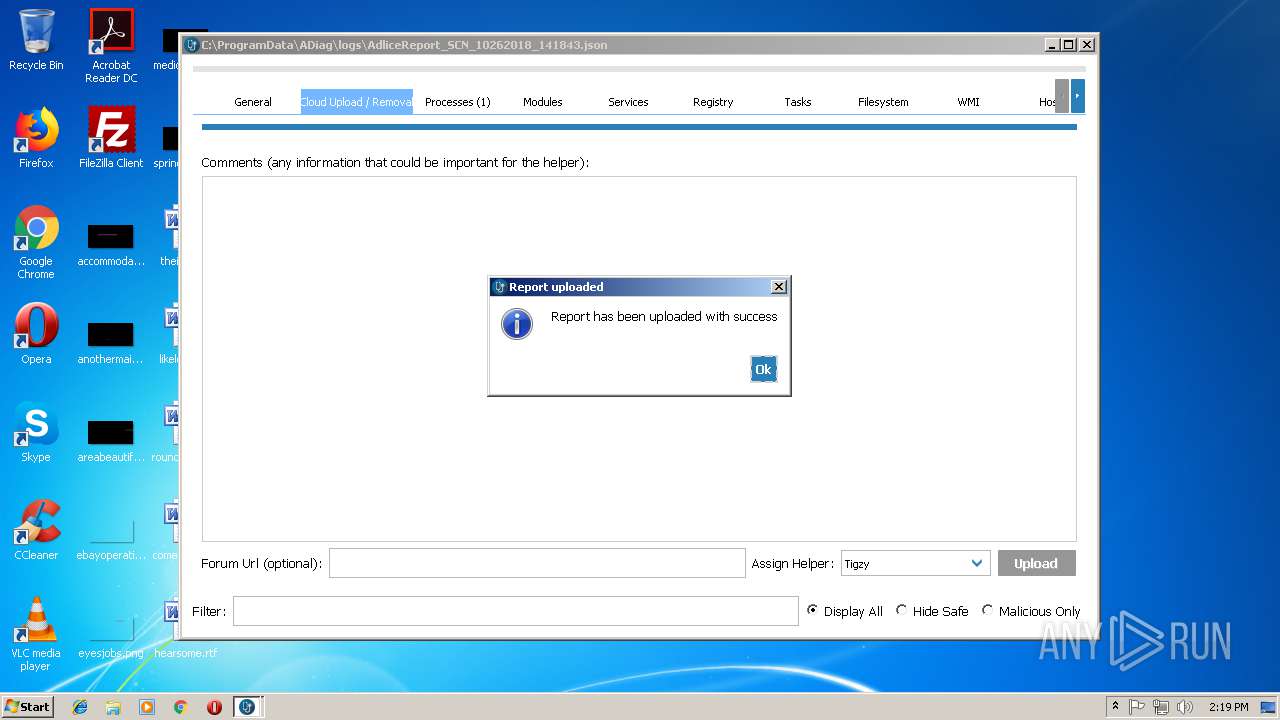
Starts Internet Explorer
- api.exe (PID: 3788)
Creates files in the Windows directory
- api.exe (PID: 3788)
Executable content was dropped or overwritten
- api.exe (PID: 3788)
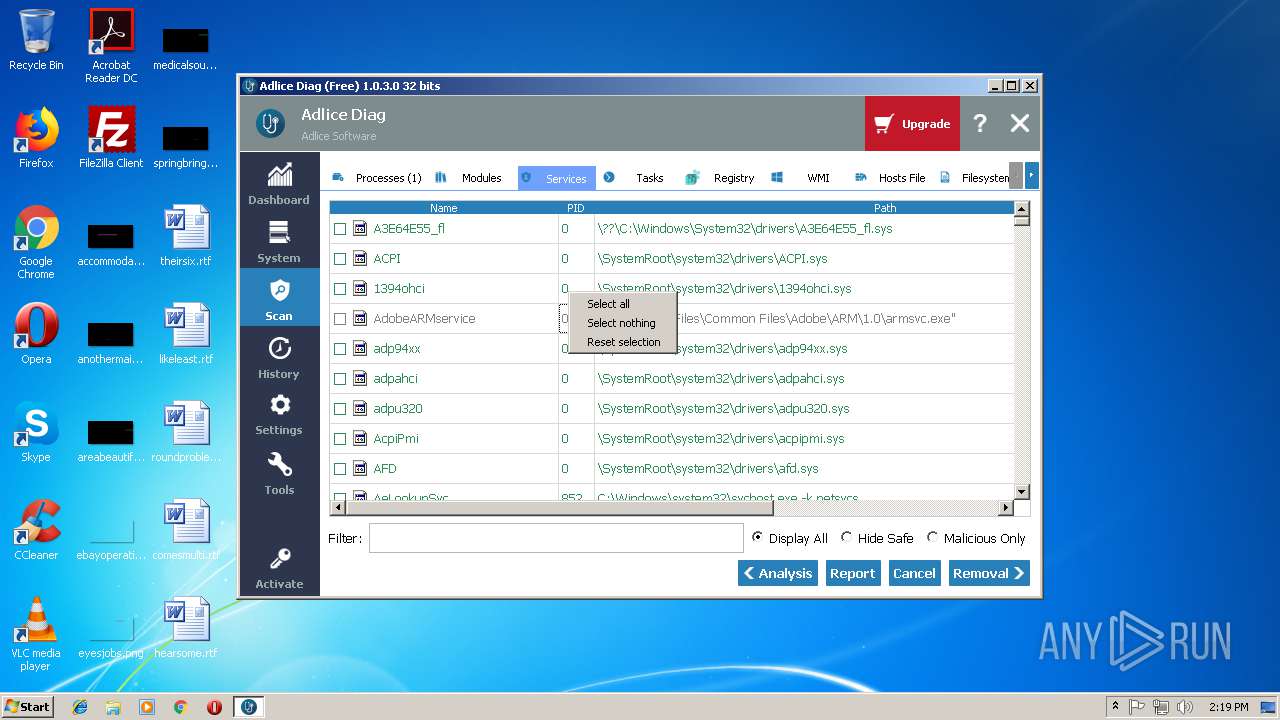
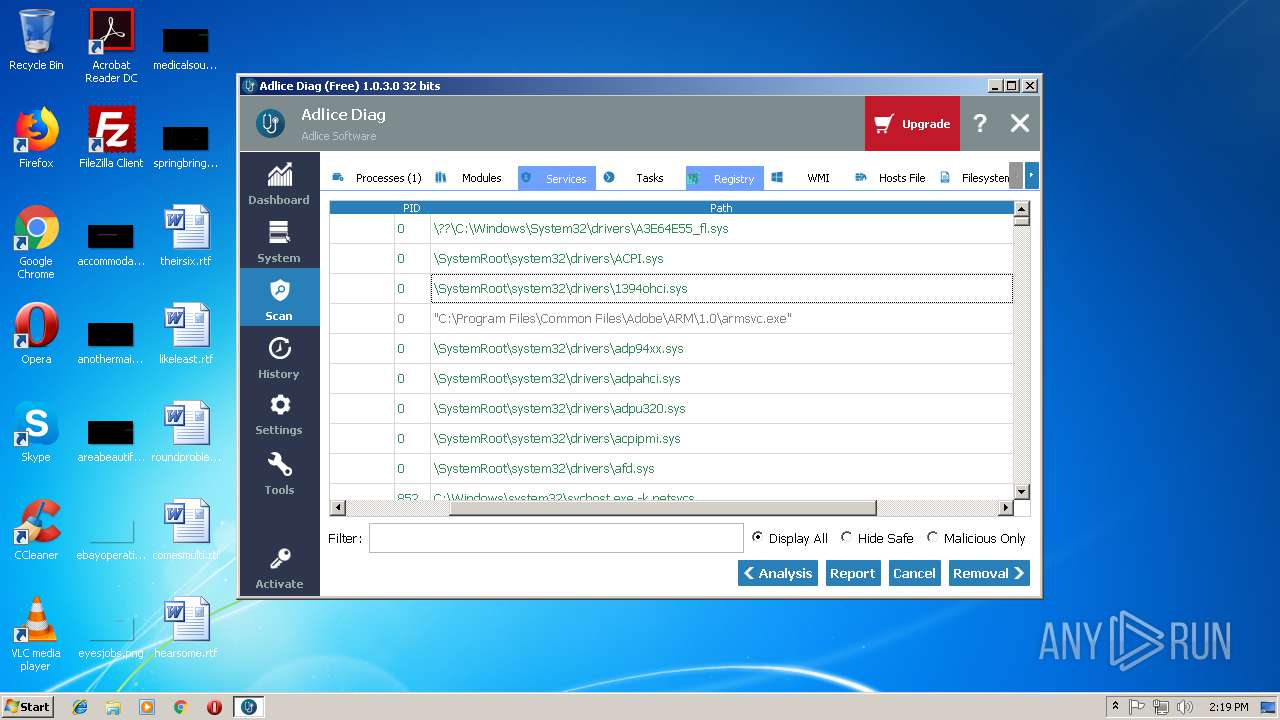
Creates or modifies windows services
- api.exe (PID: 3788)
Creates files in the driver directory
- api.exe (PID: 3788)
Removes files from Windows directory
- api.exe (PID: 3788)
Adds / modifies Windows certificates
- api.exe (PID: 3788)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1540)
- iexplore.exe (PID: 3280)
Reads Internet Cache Settings
- iexplore.exe (PID: 3028)
- iexplore.exe (PID: 2728)
Application launched itself
- iexplore.exe (PID: 1540)
Dropped object may contain Bitcoin addresses
- api.exe (PID: 3788)
Reads internet explorer settings
- iexplore.exe (PID: 2728)
Creates files in the user directory
- iexplore.exe (PID: 2728)
Changes settings of System certificates
- iexplore.exe (PID: 2728)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2728)
Reads settings of System Certificates
- api.exe (PID: 3788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:10:25 14:05:47+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 16007168 |
| InitializedDataSize: | 10700288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcb22c5 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
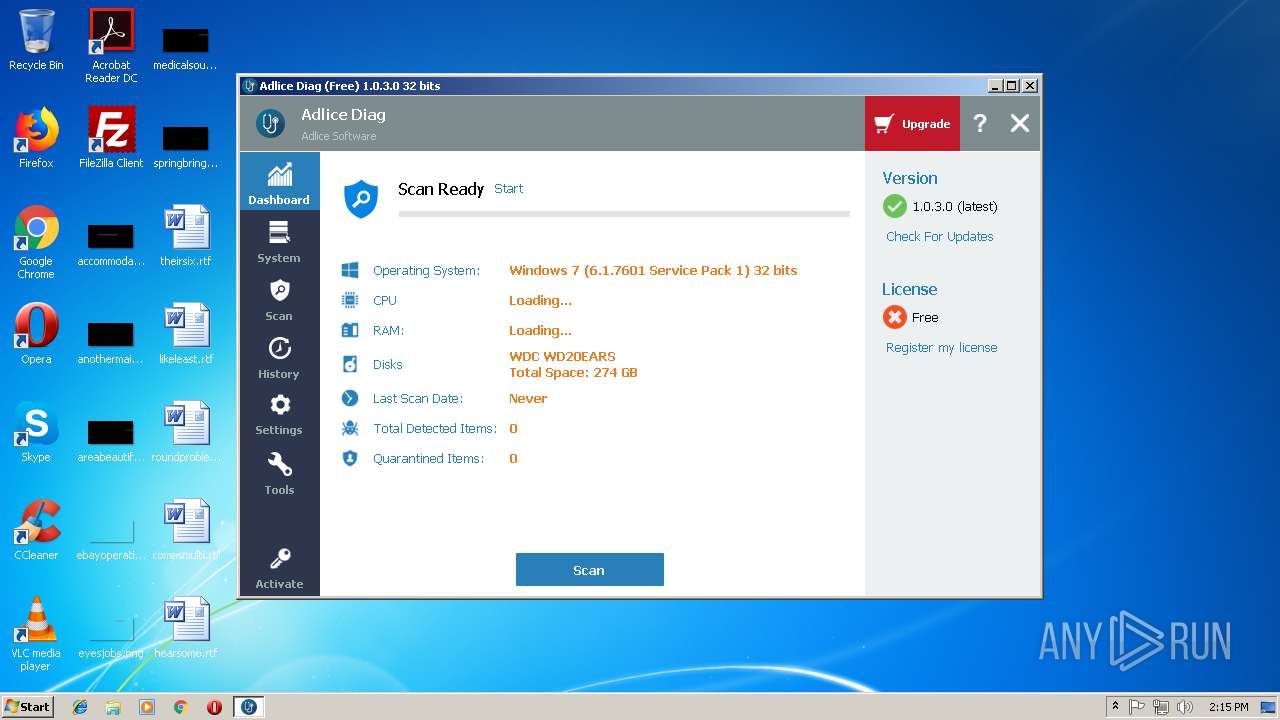
| FileVersionNumber: | 1.0.3.0 |
| ProductVersionNumber: | 1.0.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
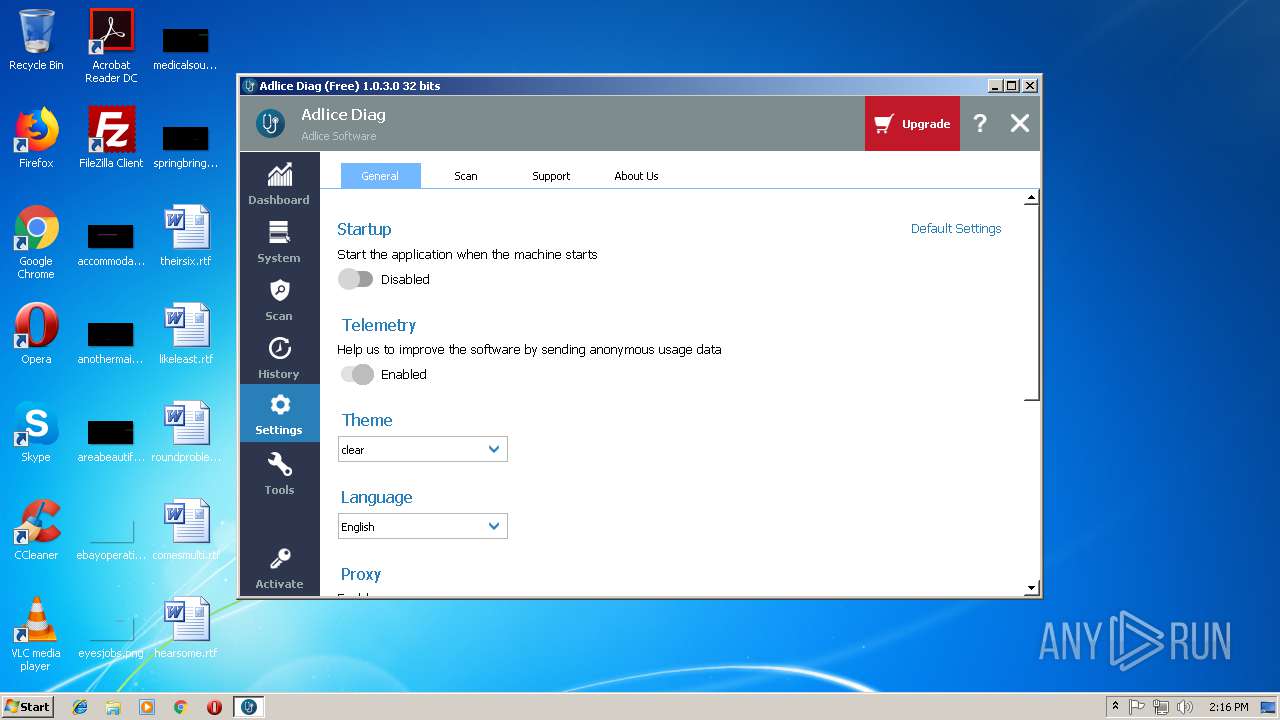
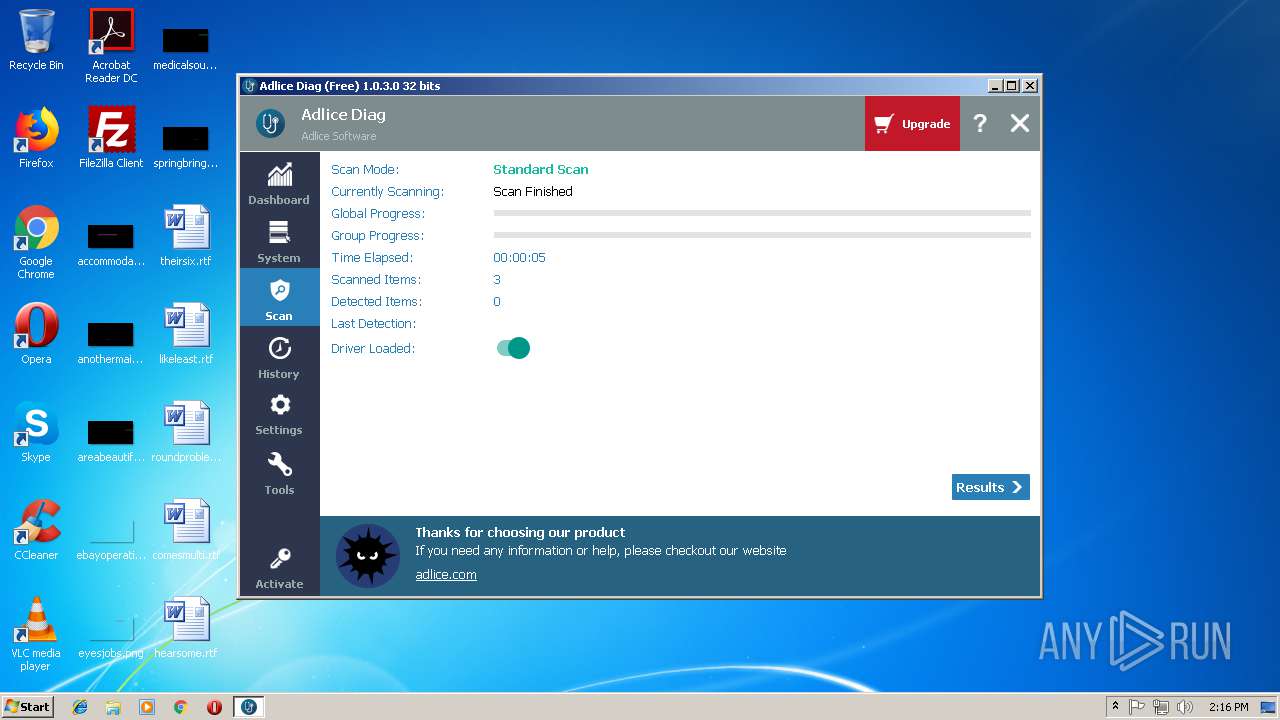
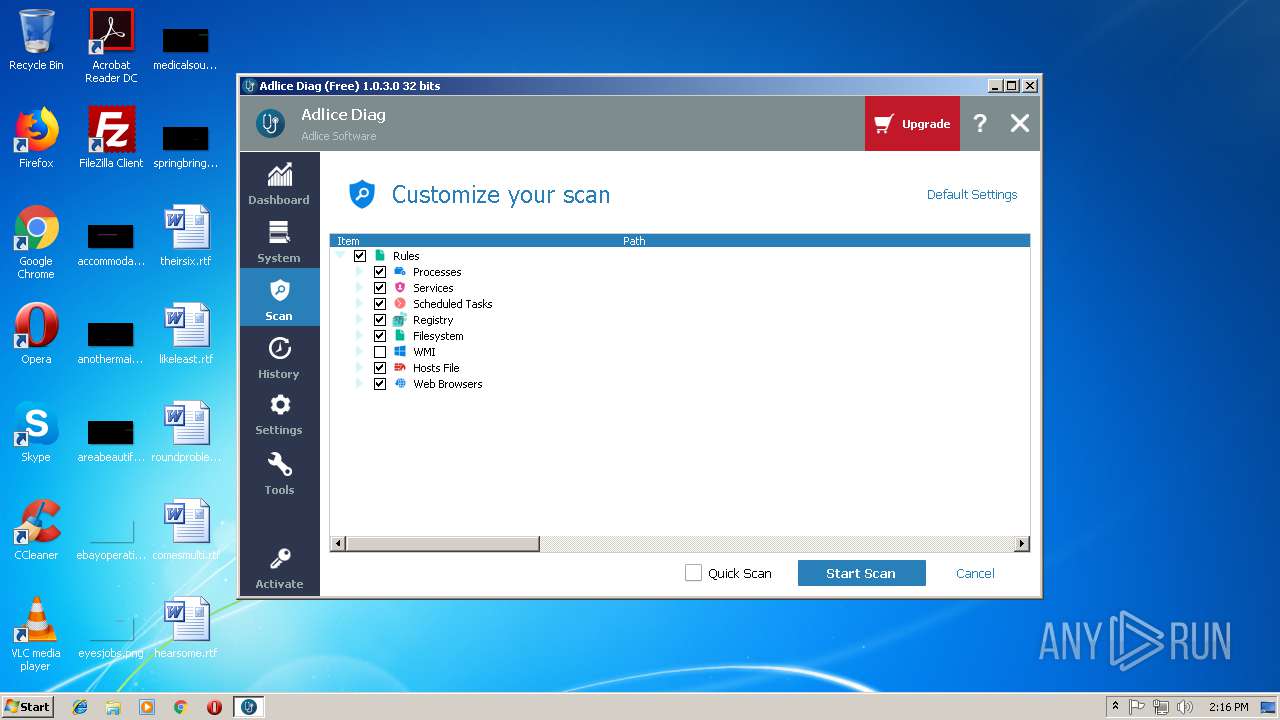
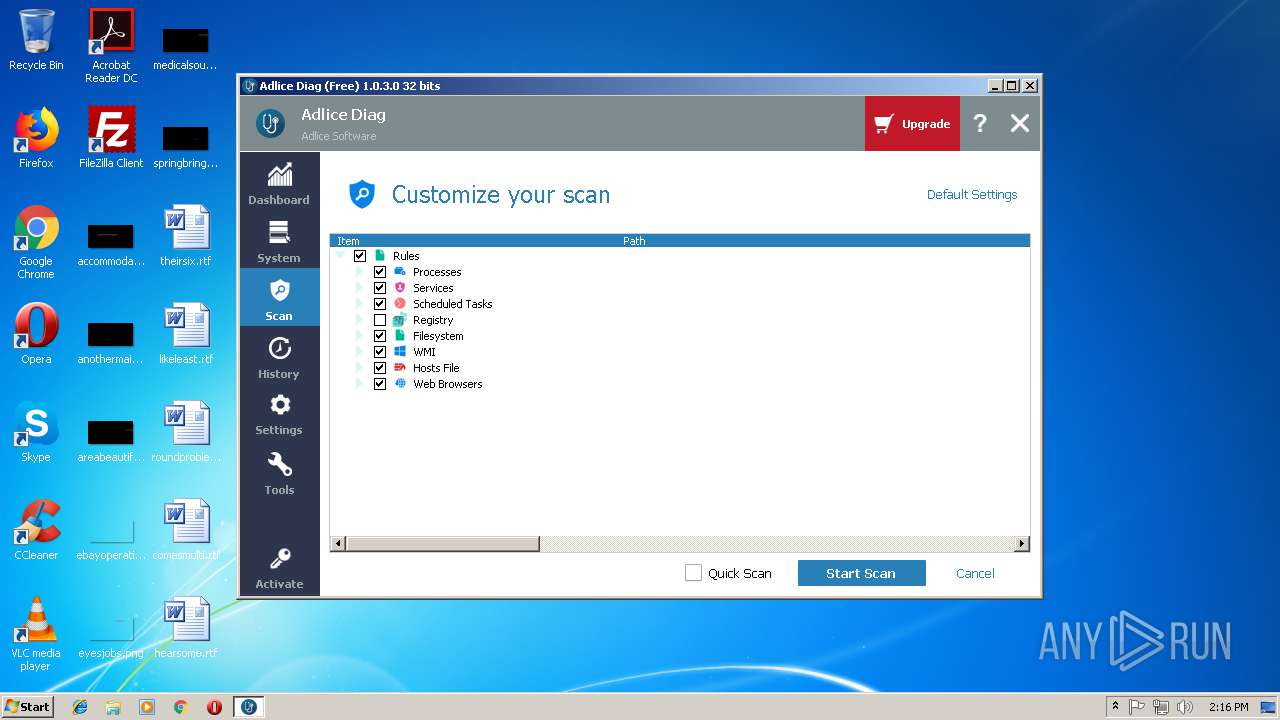
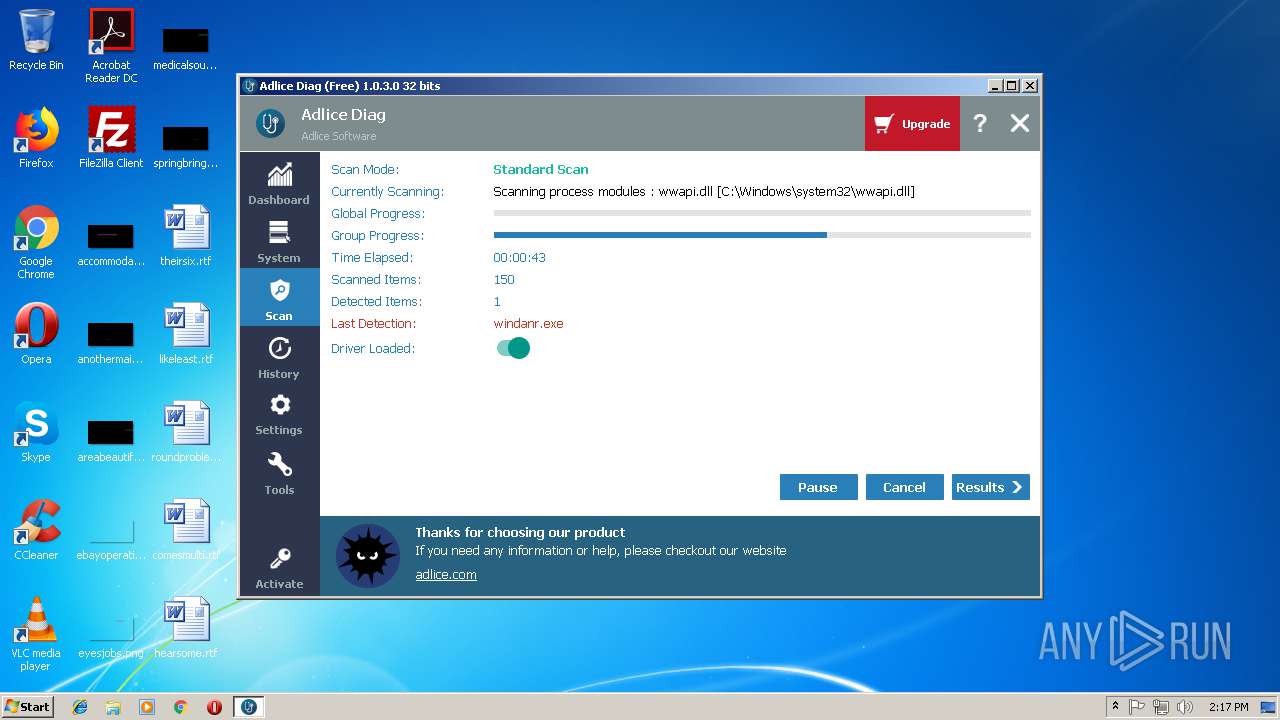
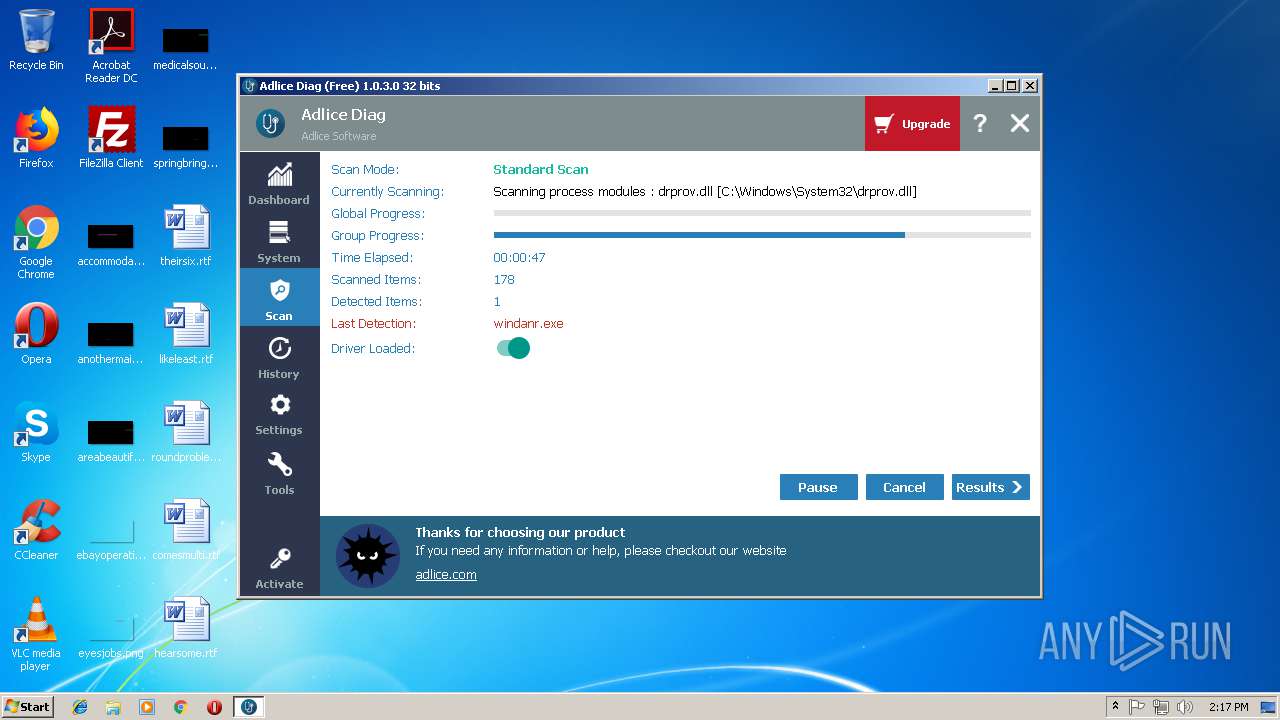
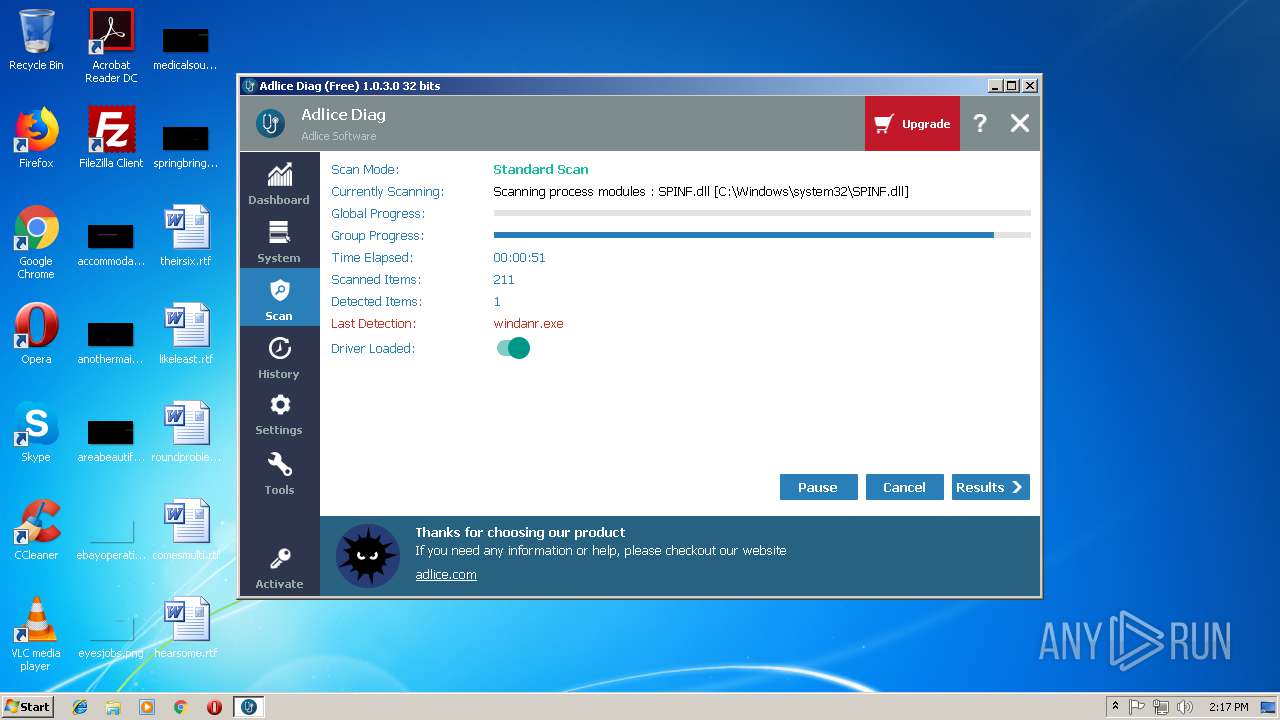
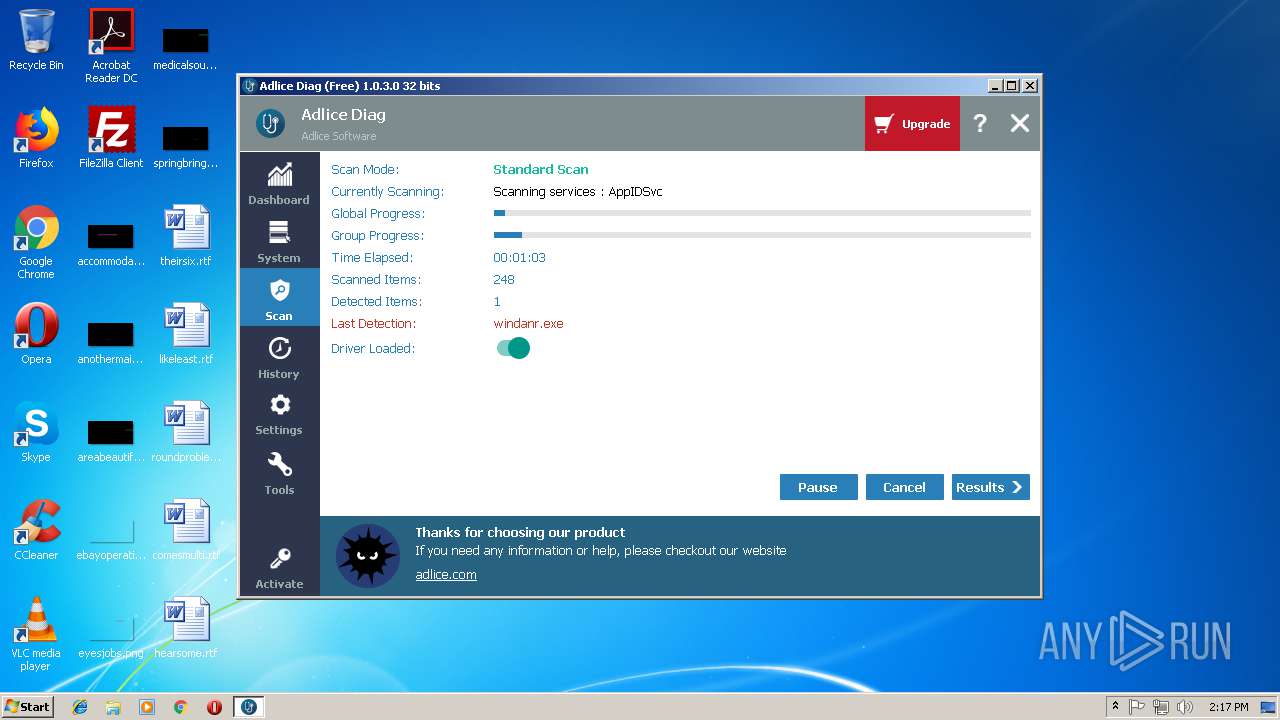
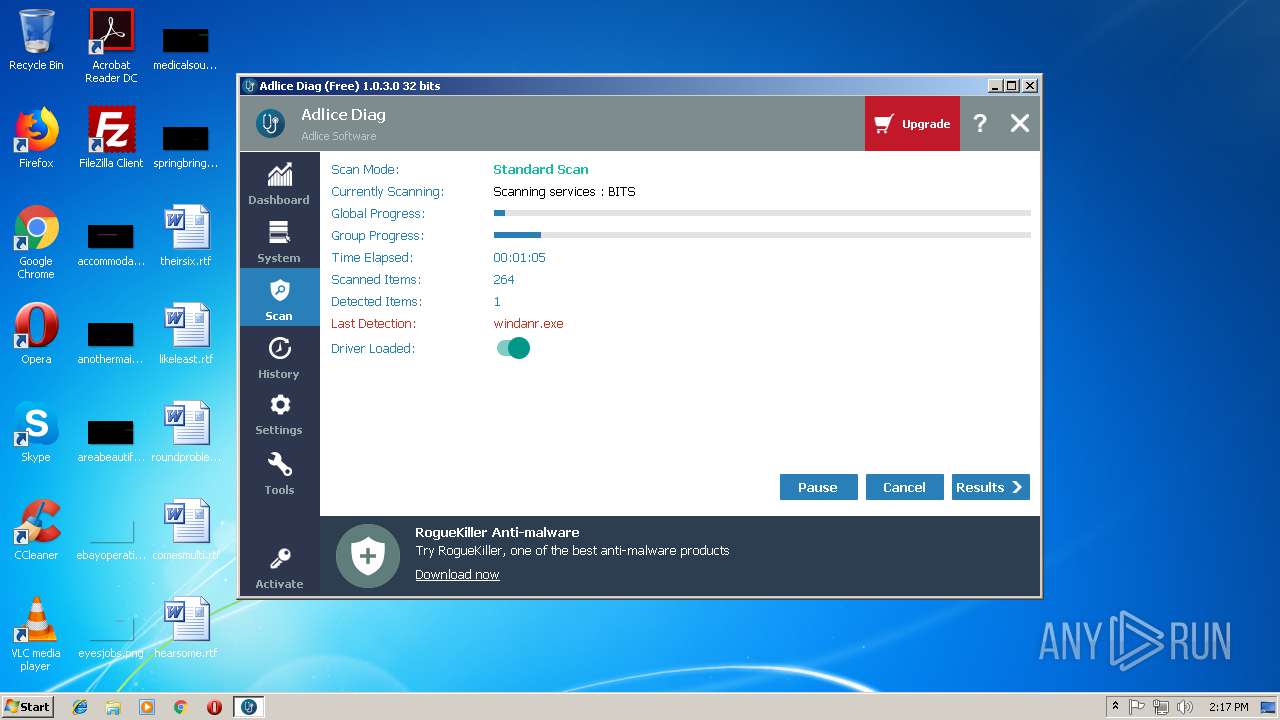
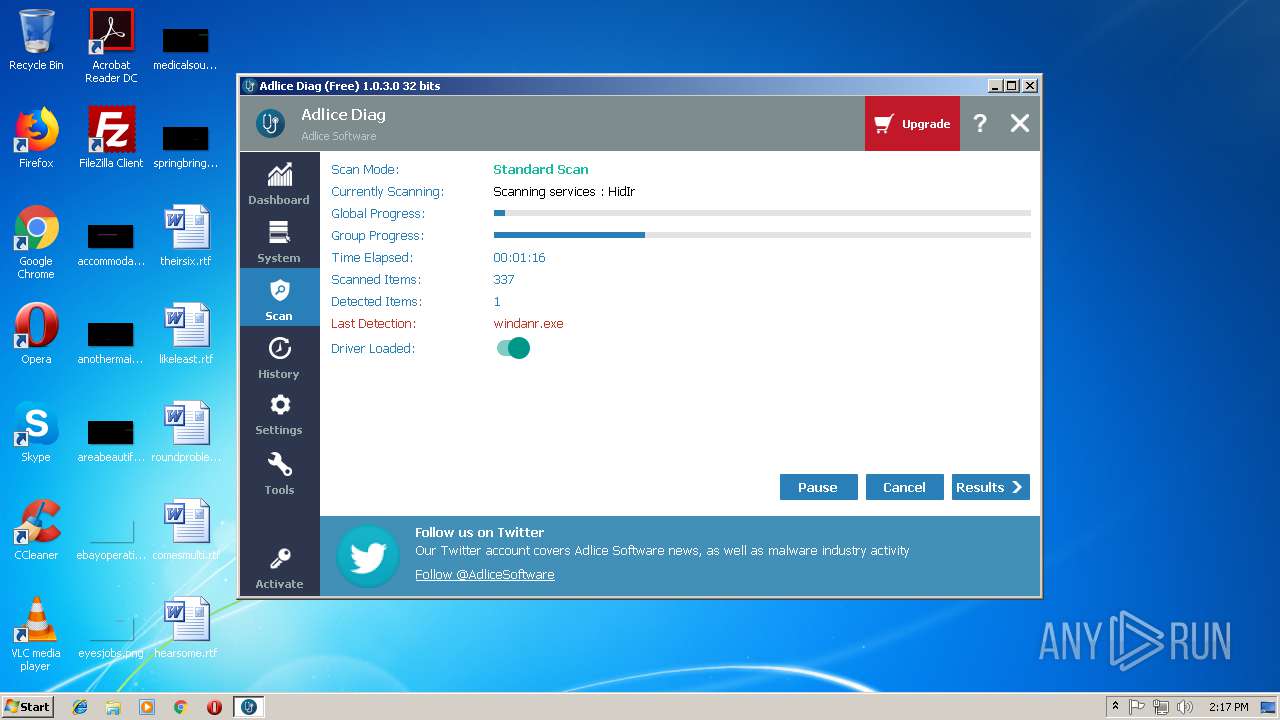
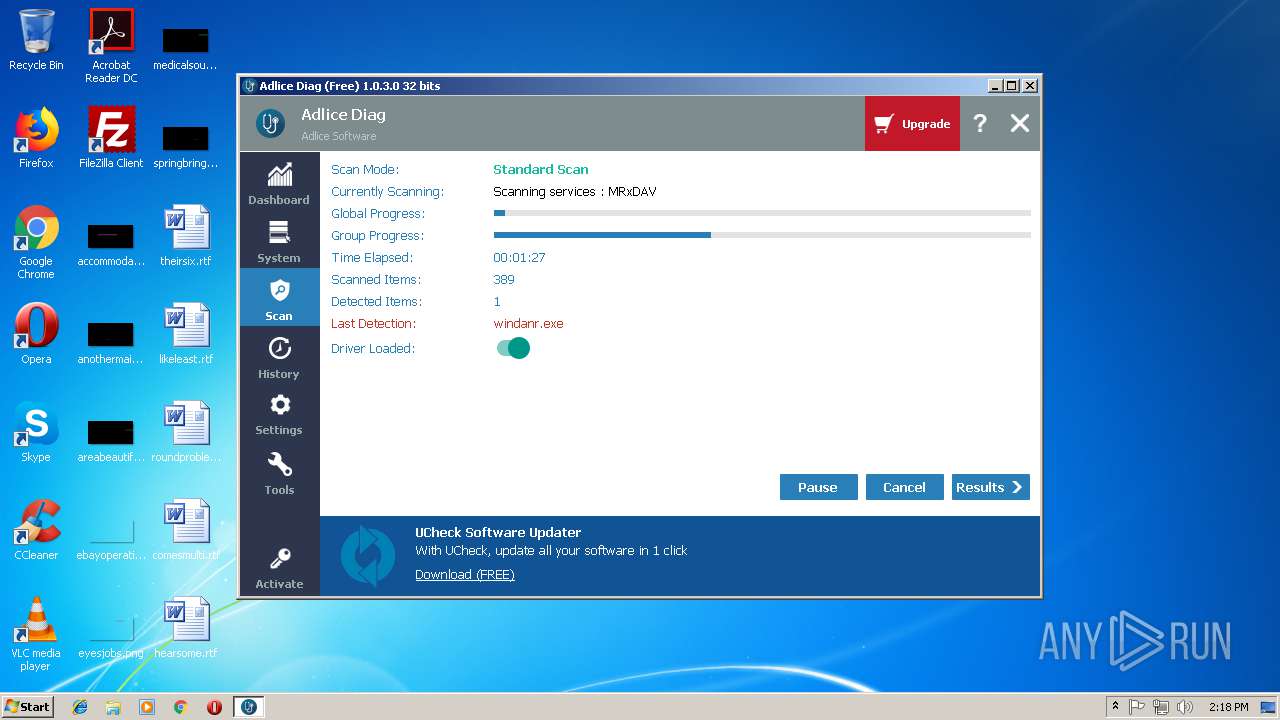
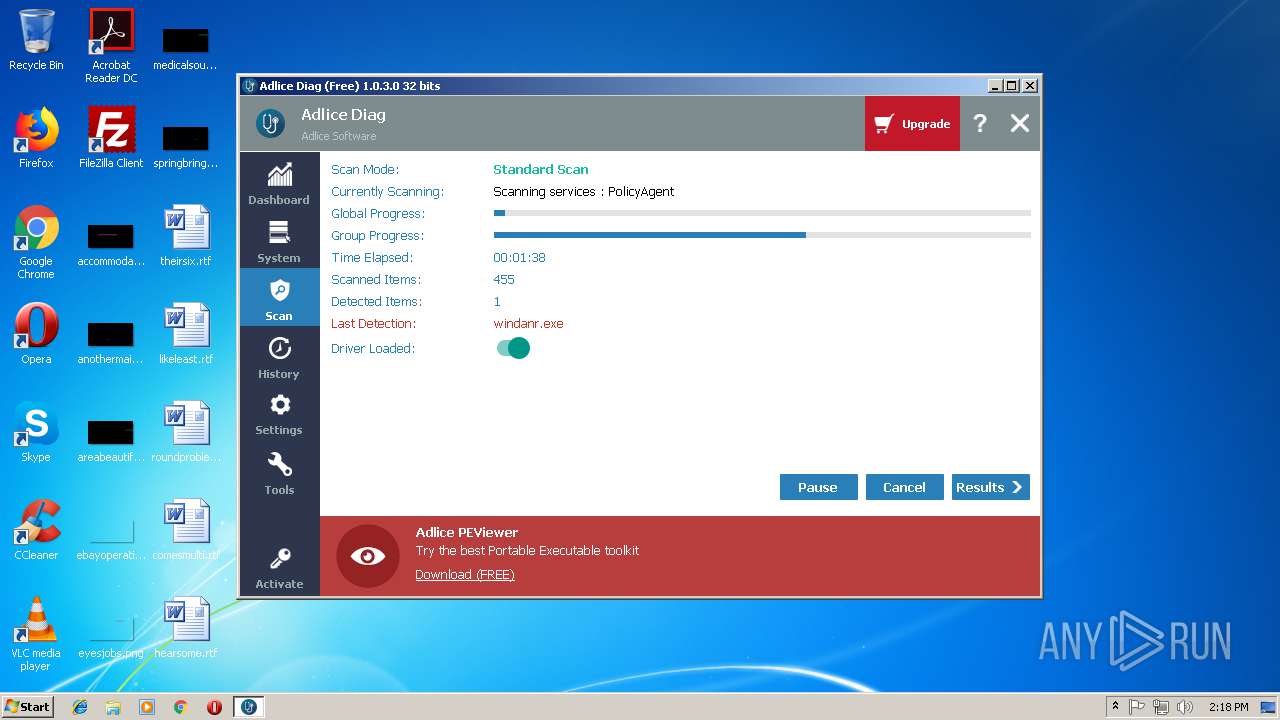
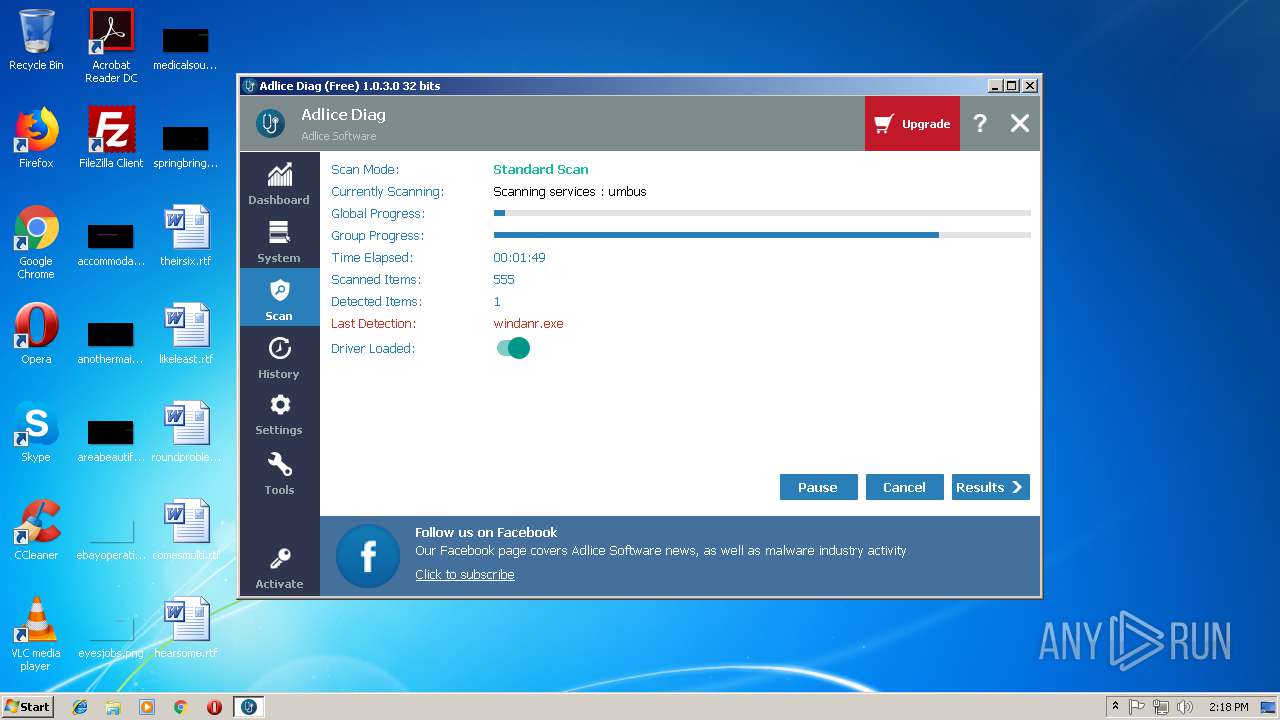
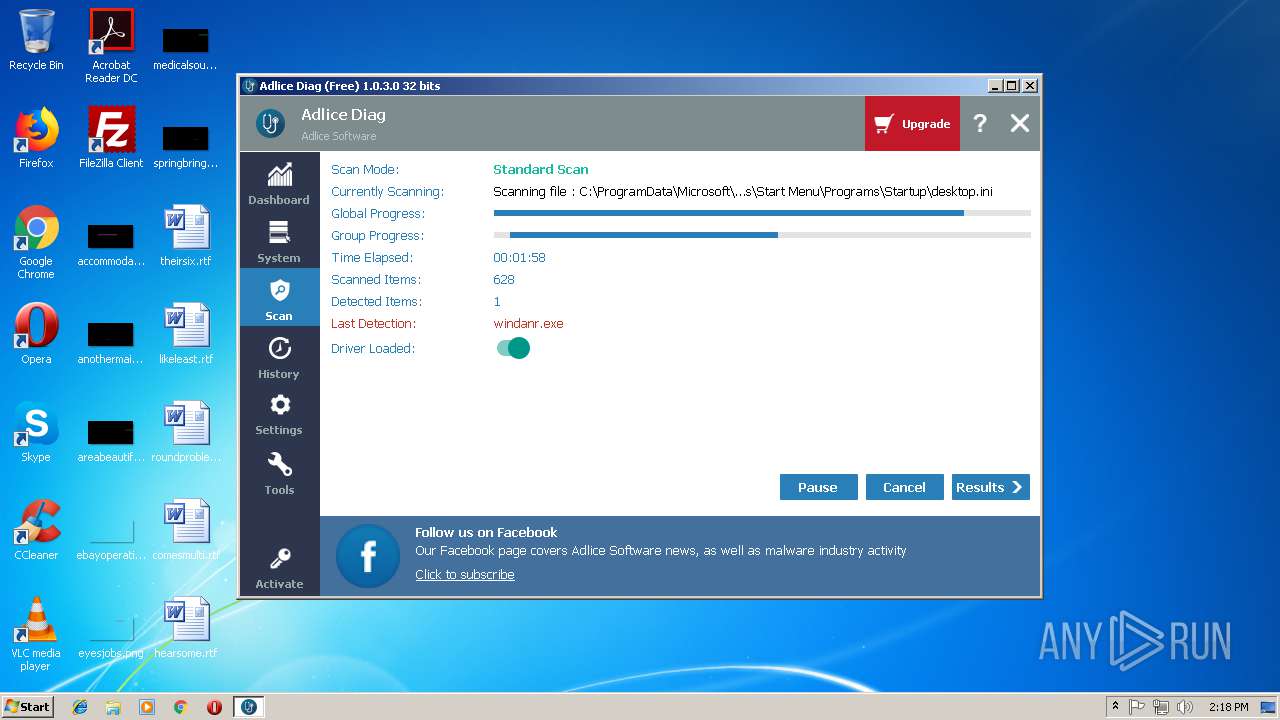
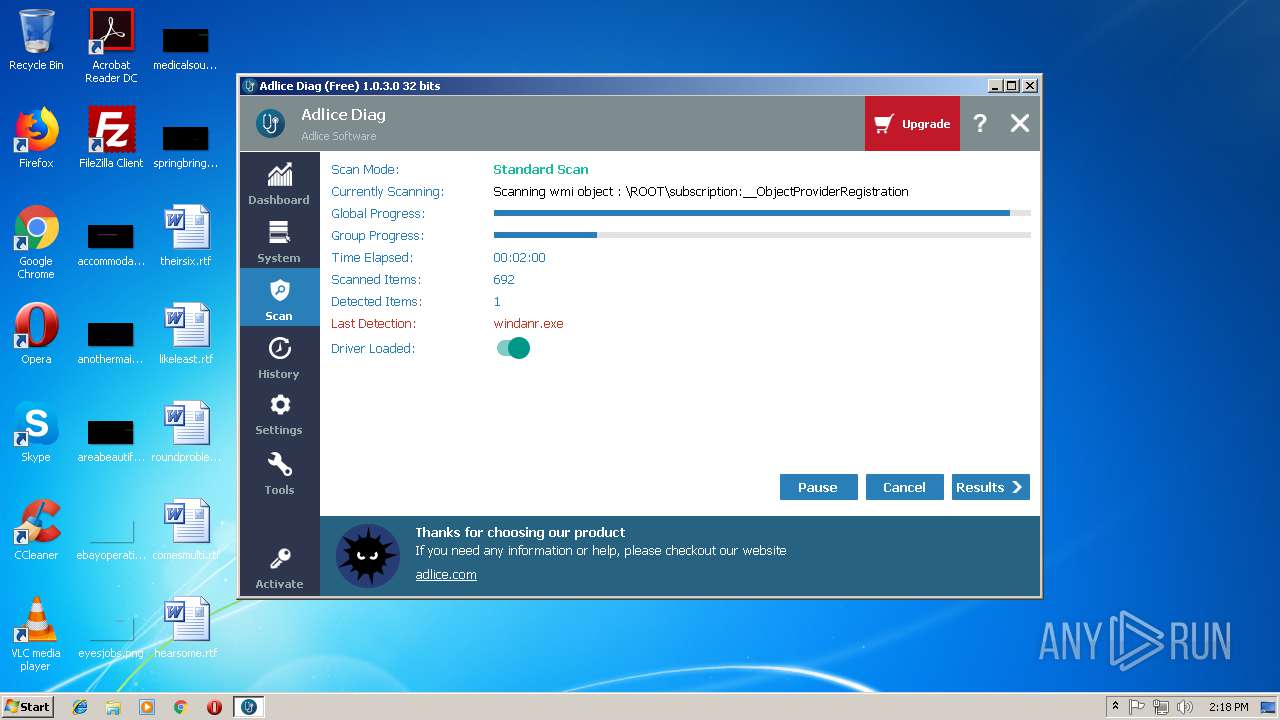
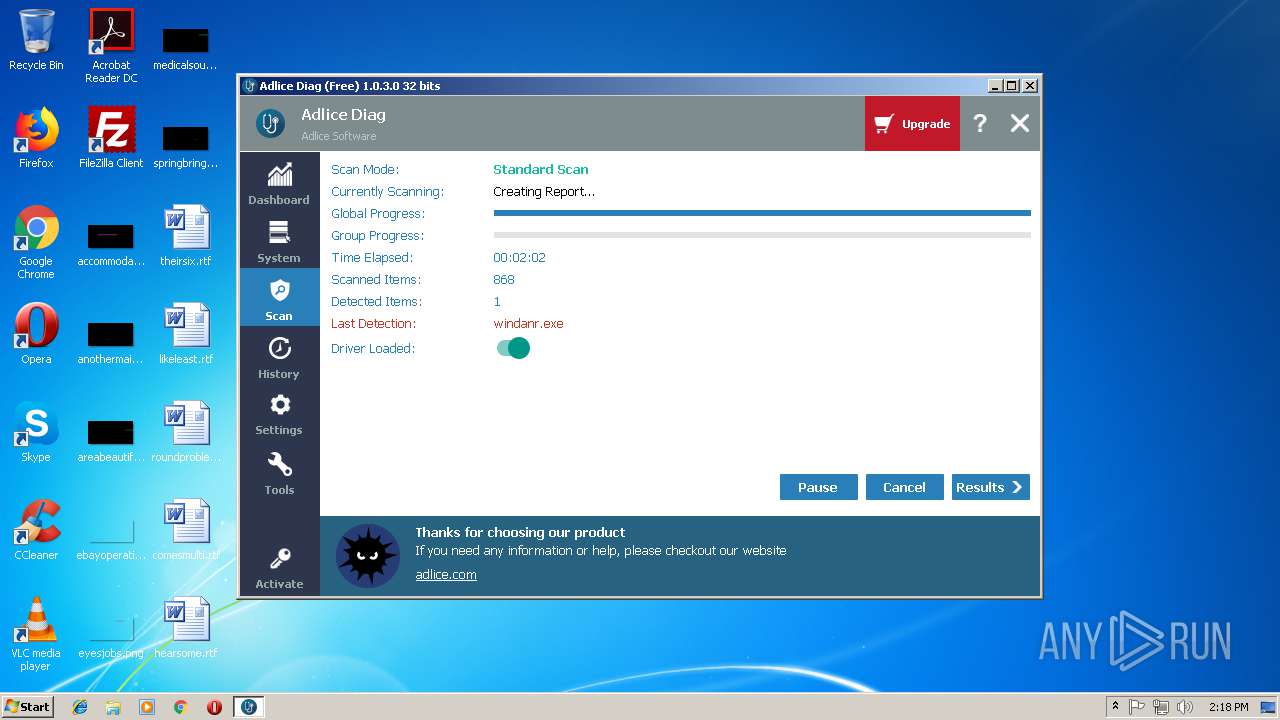
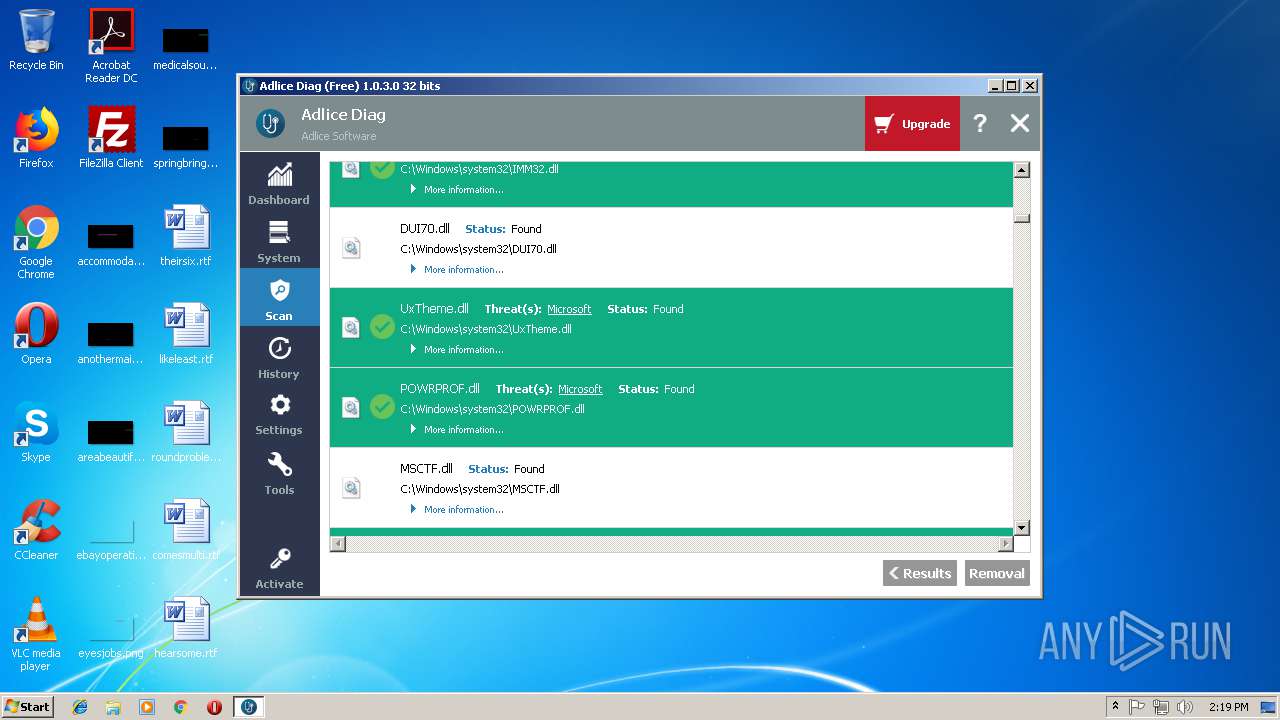
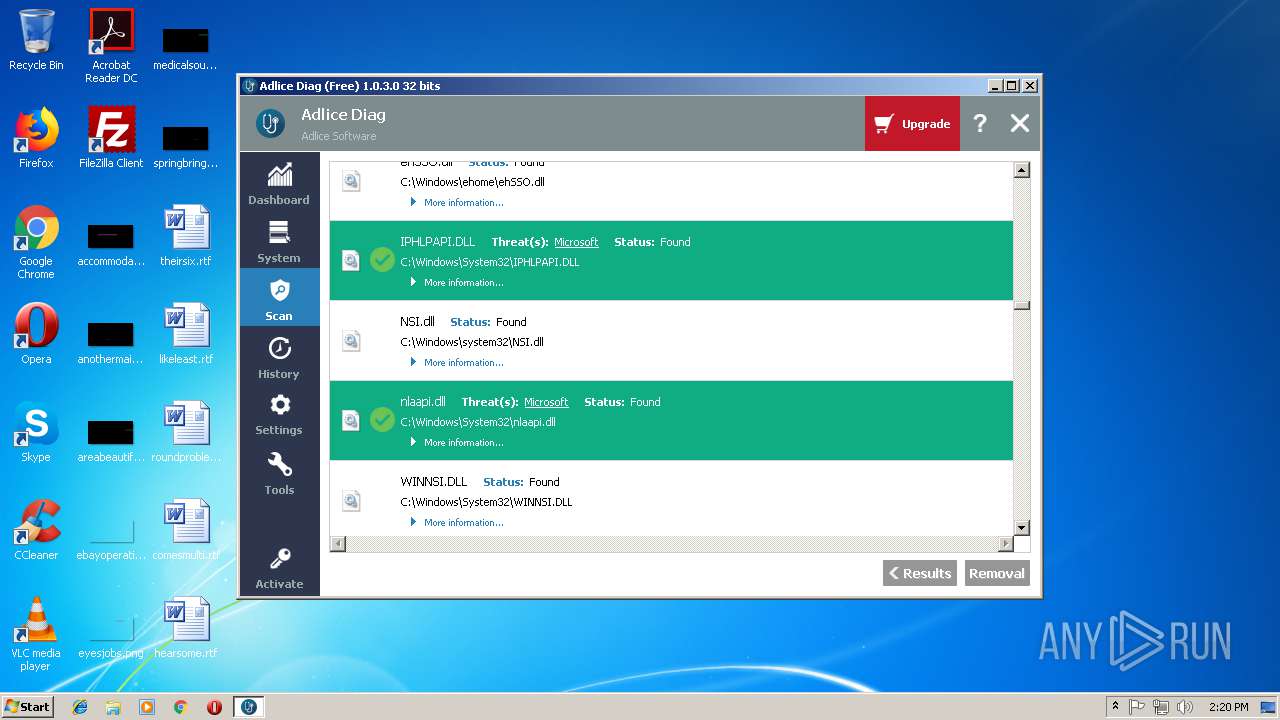
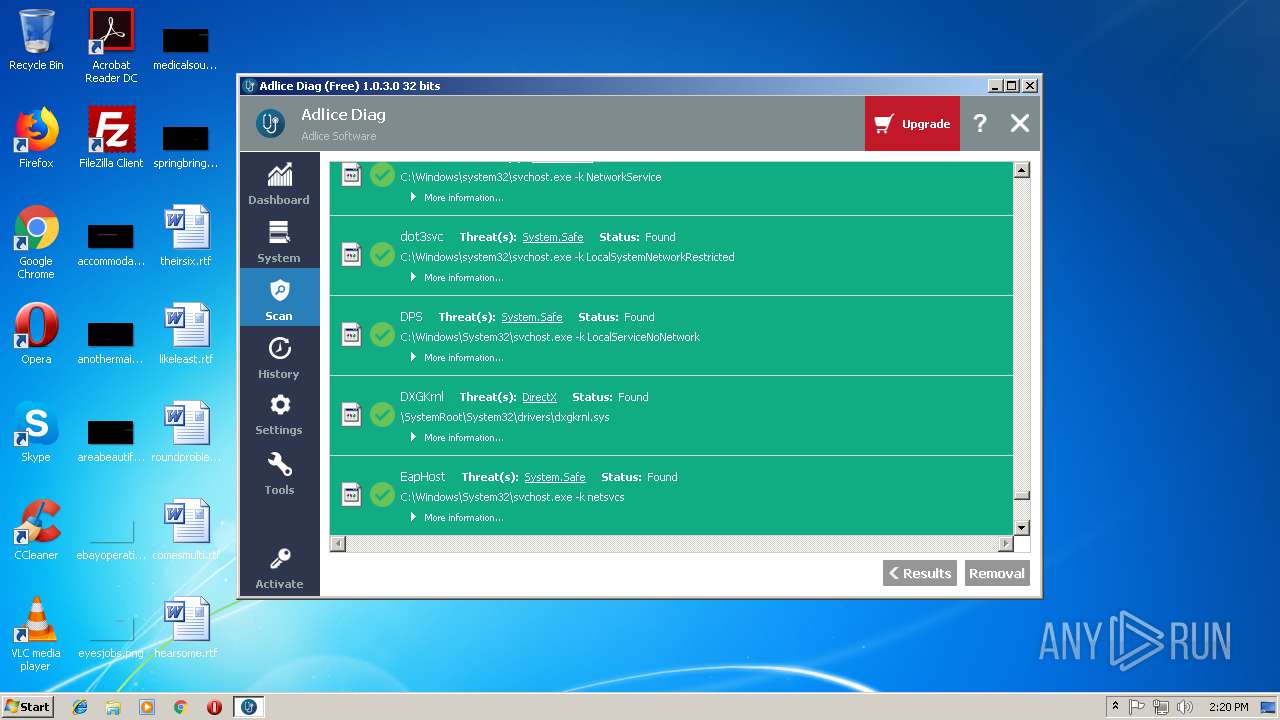
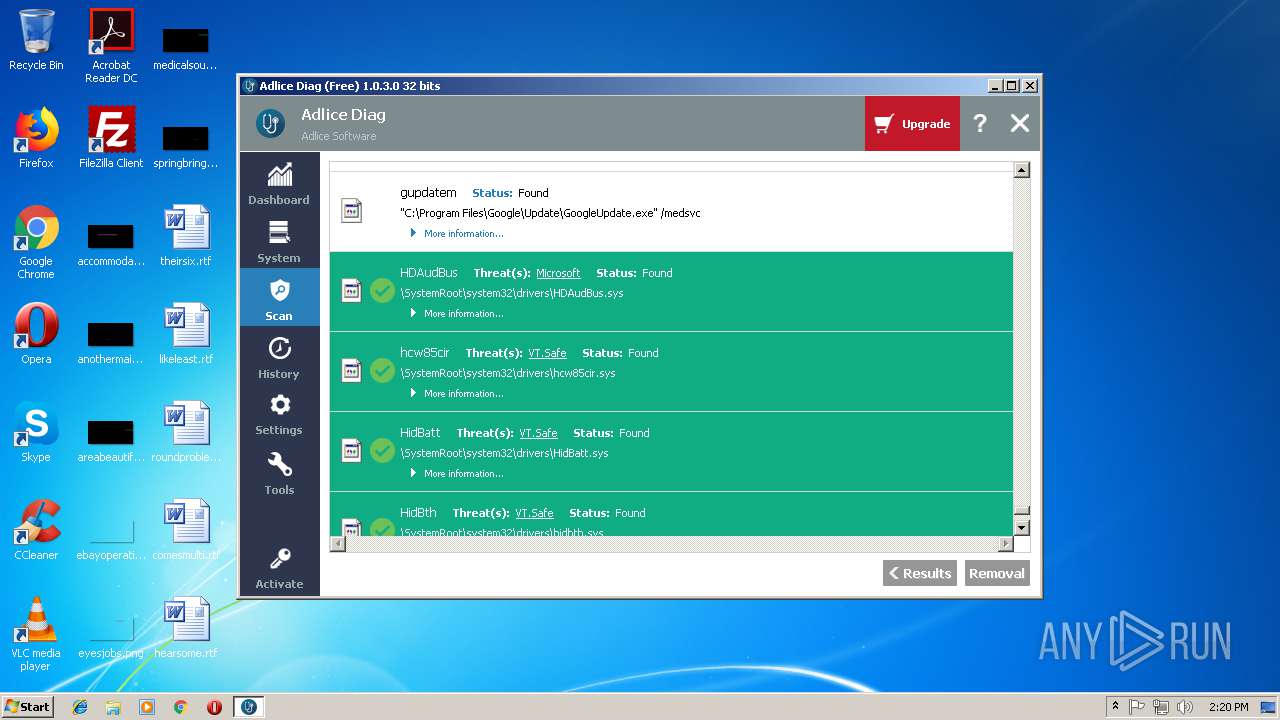
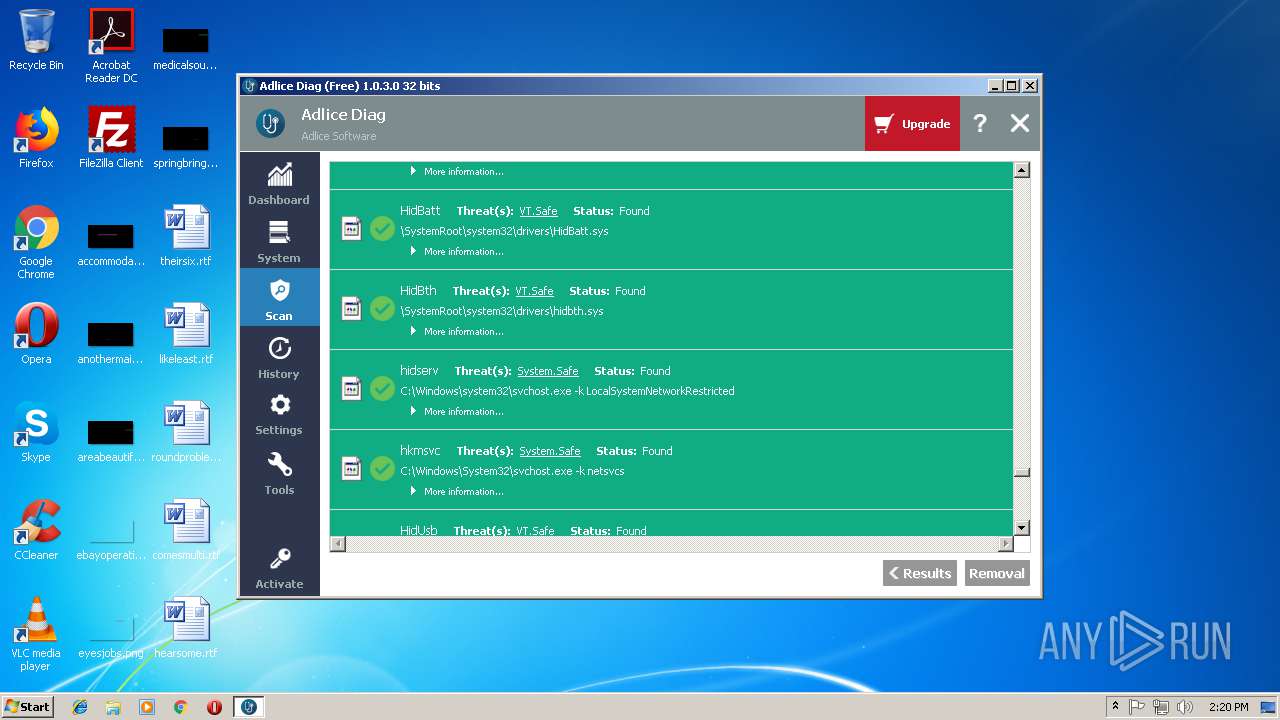
| CompanyName: | Adlice Software |
| FileDescription: | Anti-malware Diagnostic |
| FileVersion: | 1.0.3.0 |
| InternalName: | Adlice Diag |
| LegalCopyright: | Copyright Adlice Software(C) 2018 |
| LegalTrademarks1: | Adlice Software |
| LegalTrademarks2: | Adlice Software |
| OriginalFileName: | Adlice Diag |
| ProductName: | Adlice Diag |
| ProductVersion: | 1.0.3.0 |
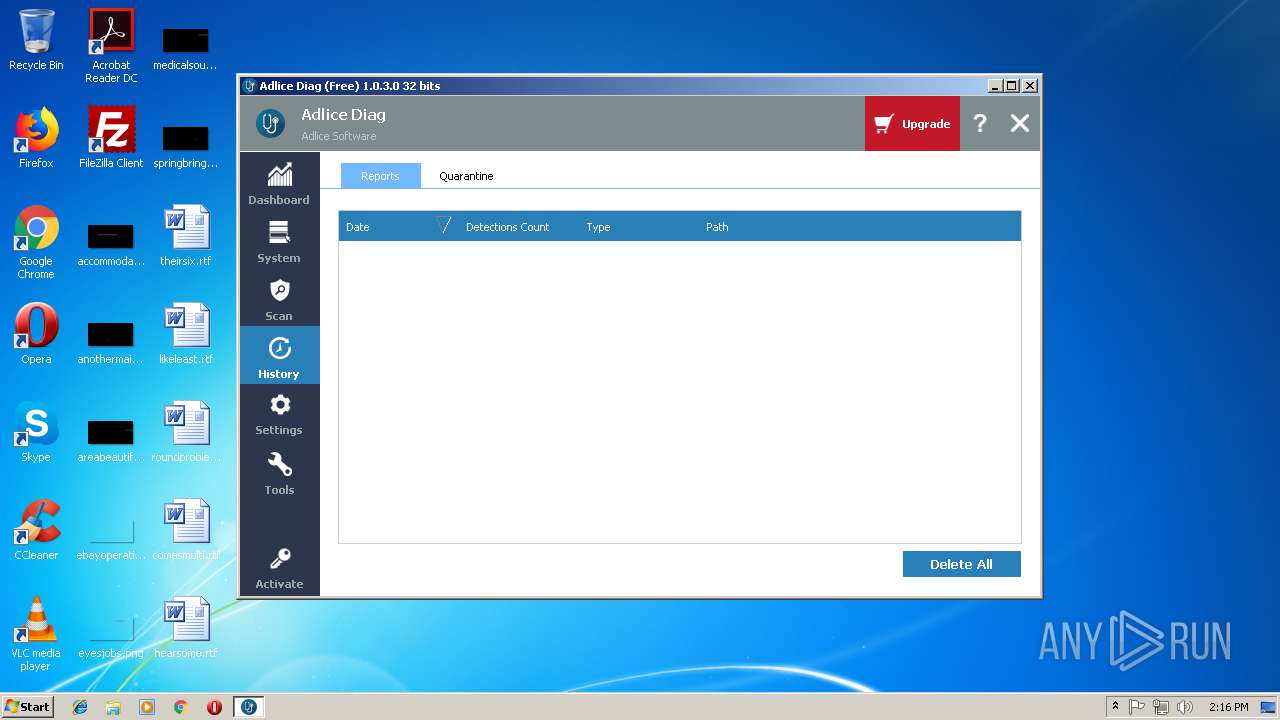
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Oct-2018 12:05:47 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Adlice Software |
| FileDescription: | Anti-malware Diagnostic |
| FileVersion: | 1.0.3.0 |
| InternalName: | Adlice Diag |
| LegalCopyright: | Copyright Adlice Software(C) 2018 |
| LegalTrademarks1: | Adlice Software |
| LegalTrademarks2: | Adlice Software |
| OriginalFilename: | Adlice Diag |
| ProductName: | Adlice Diag |
| ProductVersion: | 1.0.3.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000160 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 25-Oct-2018 12:05:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00F43E3E | 0x00F44000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59584 |
.rdata | 0x00F45000 | 0x004744D8 | 0x00474600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.23696 |
.data | 0x013BA000 | 0x00048C80 | 0x0002BC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.74204 |
.tls | 0x01403000 | 0x0000000D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.qtmetadL\x02 | 0x01404000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.15593 |
.gfids | 0x01405000 | 0x000007CC | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.10088 |
_RDATA | 0x01406000 | 0x00000124 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.51793 |
.rsrc | 0x01407000 | 0x004D66C0 | 0x004D6800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.88542 |
.reloc | 0x018DE000 | 0x0009F8C0 | 0x0009FA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64507 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21878 | 667 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.46968 | 296 | UNKNOWN | English - United States | RT_ICON |
3 | 6.0173 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 6.36951 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 5.70689 | 1384 | UNKNOWN | English - United States | RT_ICON |
6 | 7.94435 | 27916 | UNKNOWN | English - United States | RT_ICON |
7 | 6.31361 | 16936 | UNKNOWN | English - United States | RT_ICON |
8 | 6.3939 | 9640 | UNKNOWN | English - United States | RT_ICON |
9 | 6.36196 | 6760 | UNKNOWN | English - United States | RT_ICON |
10 | 6.49135 | 4264 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
CRYPT32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
OPENGL32.dll |
PSAPI.DLL |
Exports
Title | Ordinal | Address |
|---|---|---|
yr_compiler_add_fd | 1 | 0x00D45460 |
yr_compiler_add_file | 2 | 0x00D454F0 |
yr_compiler_add_string | 3 | 0x00D45580 |
yr_compiler_create | 4 | 0x00D45600 |
yr_compiler_define_boolean_variable | 5 | 0x00D45840 |
yr_compiler_define_float_variable | 6 | 0x00D458E0 |
yr_compiler_define_integer_variable | 7 | 0x00D45980 |
yr_compiler_define_string_variable | 8 | 0x00D45A20 |
yr_compiler_destroy | 9 | 0x00D45AF0 |
yr_compiler_get_current_file_name | 10 | 0x00D45BE0 |
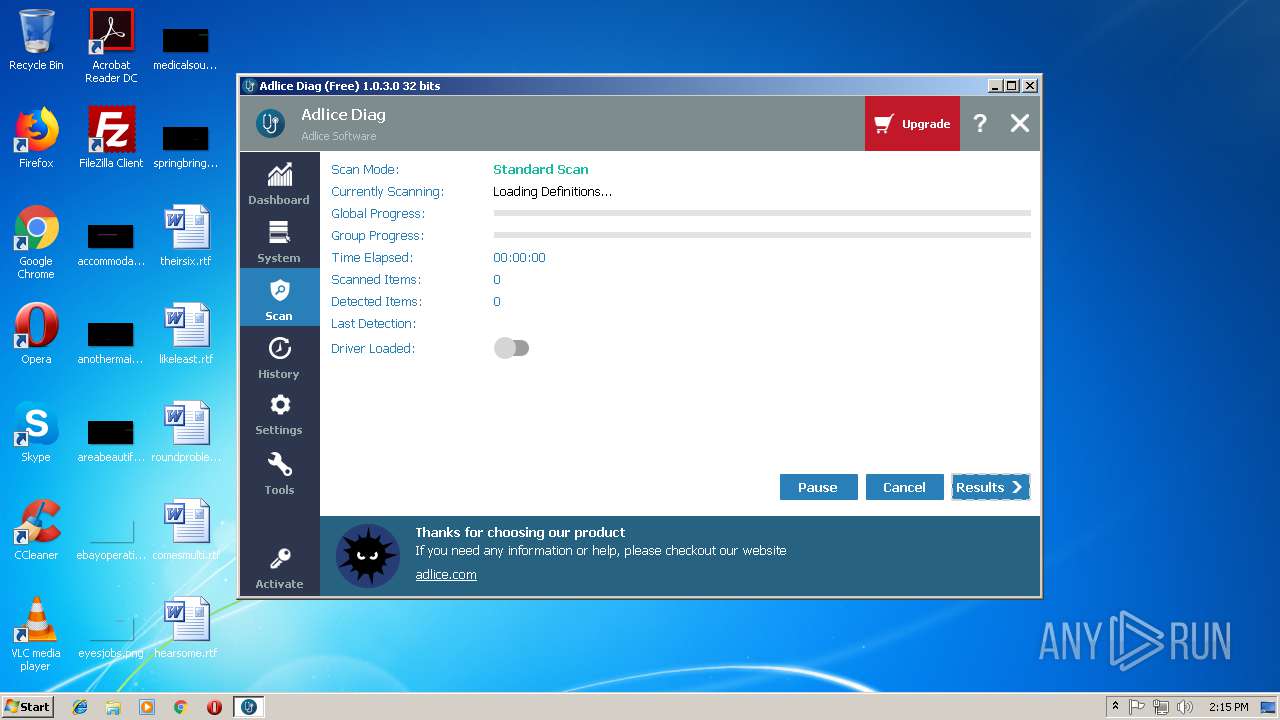
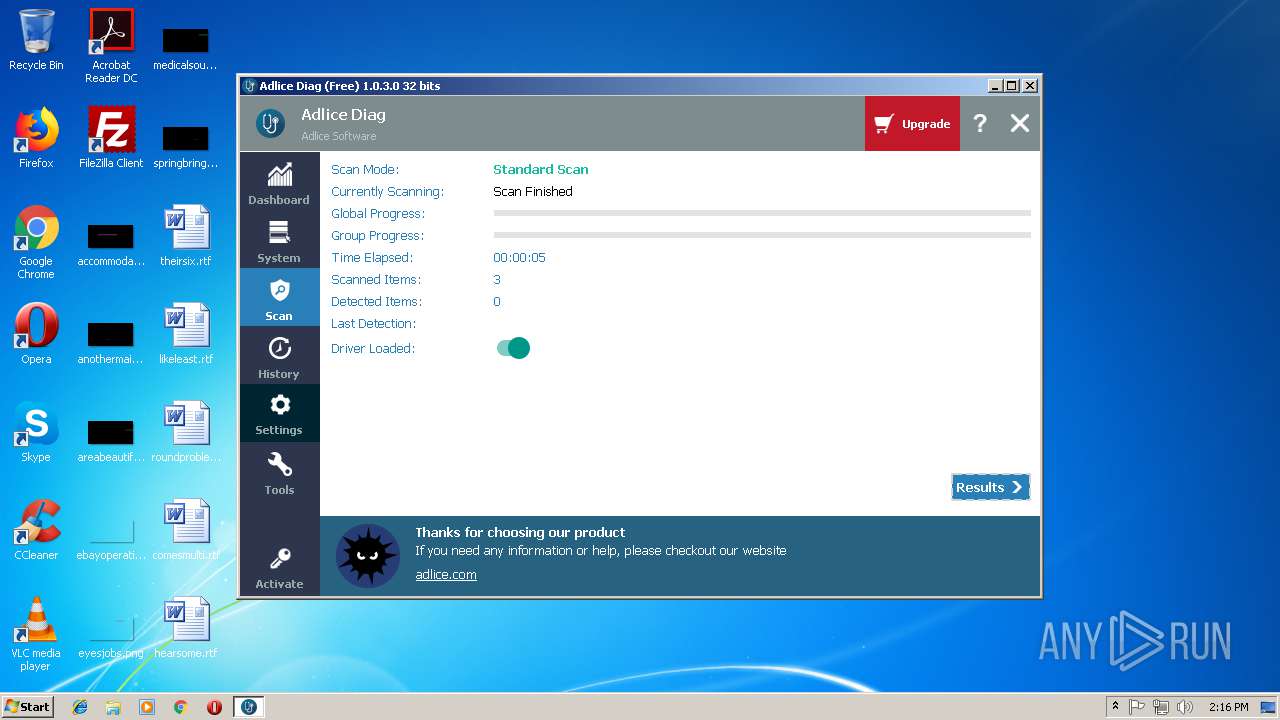
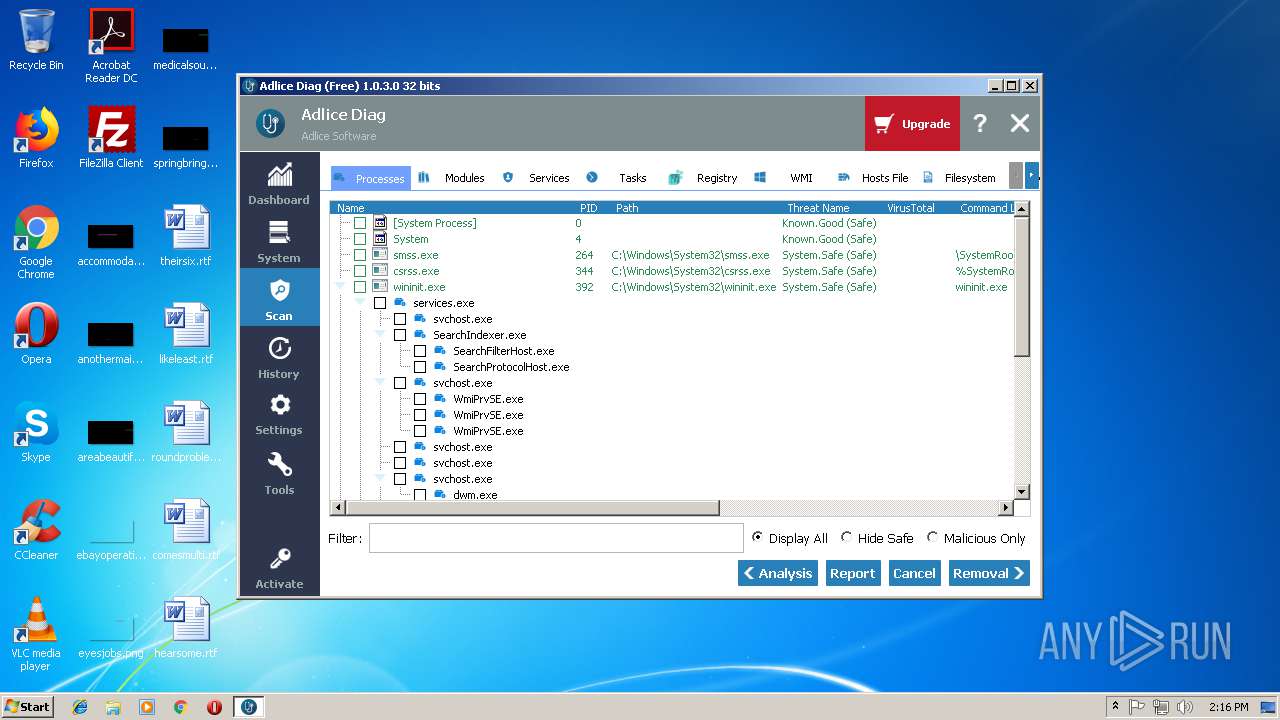
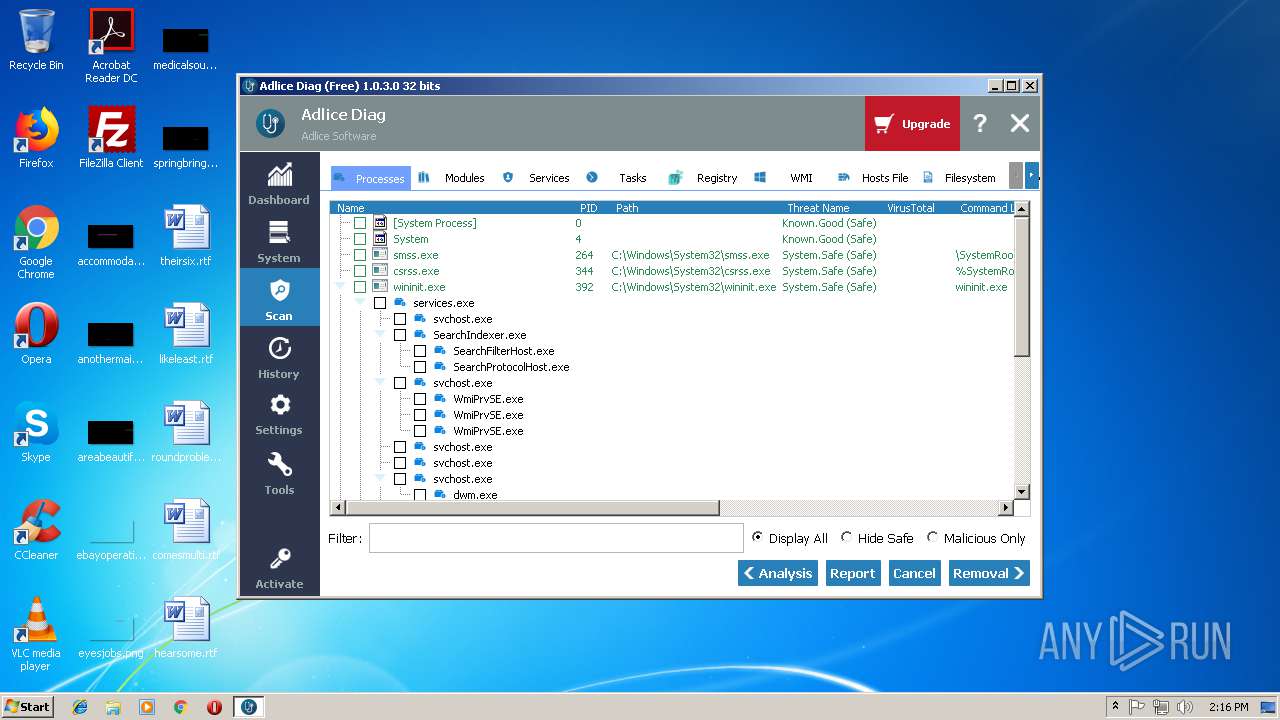
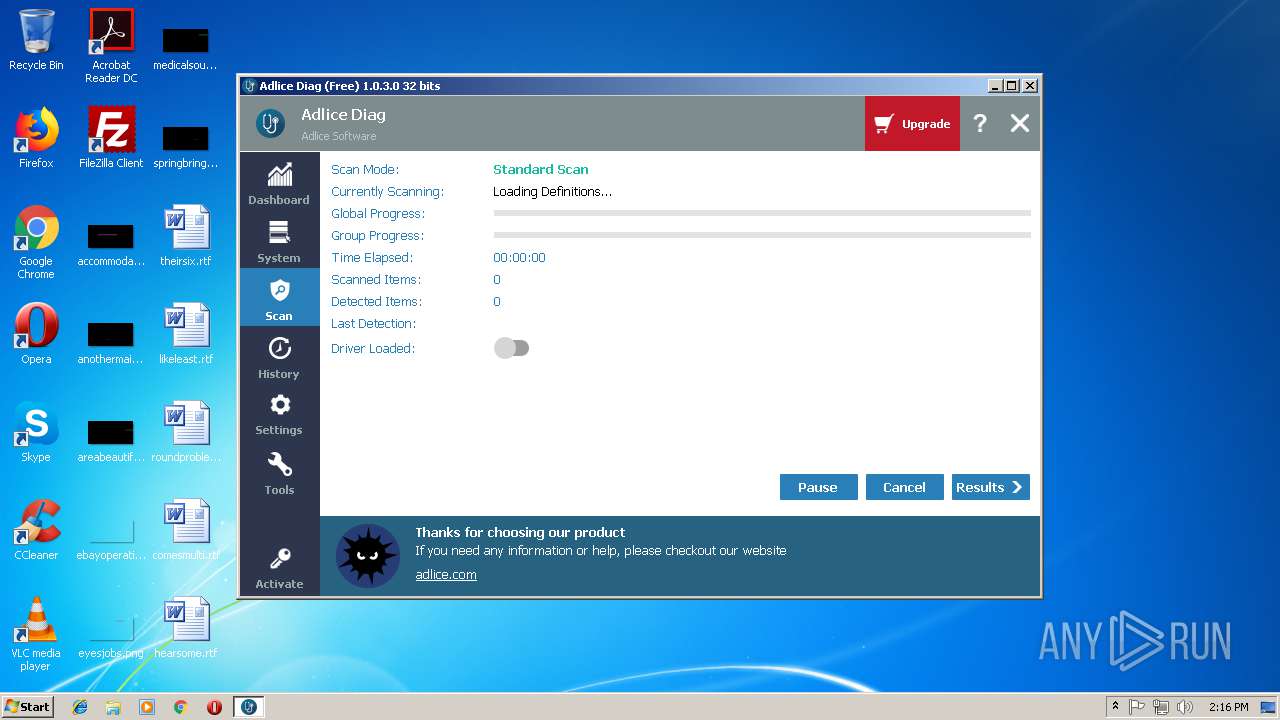
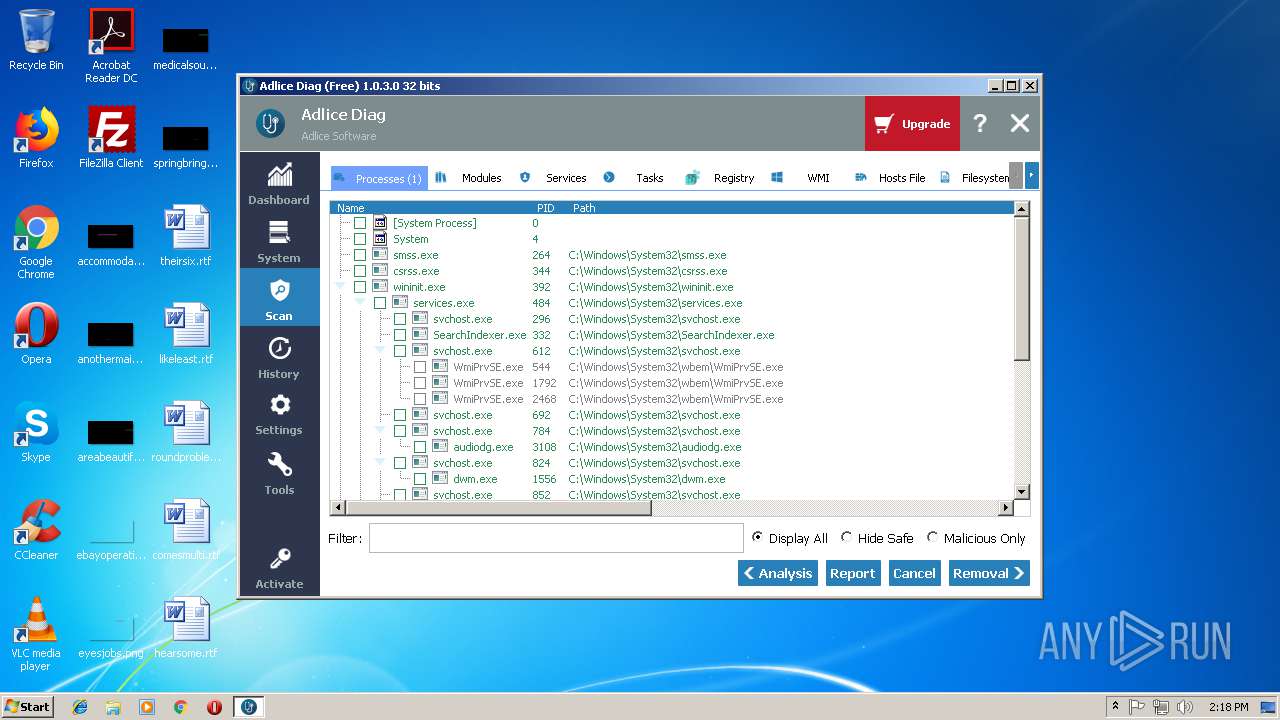
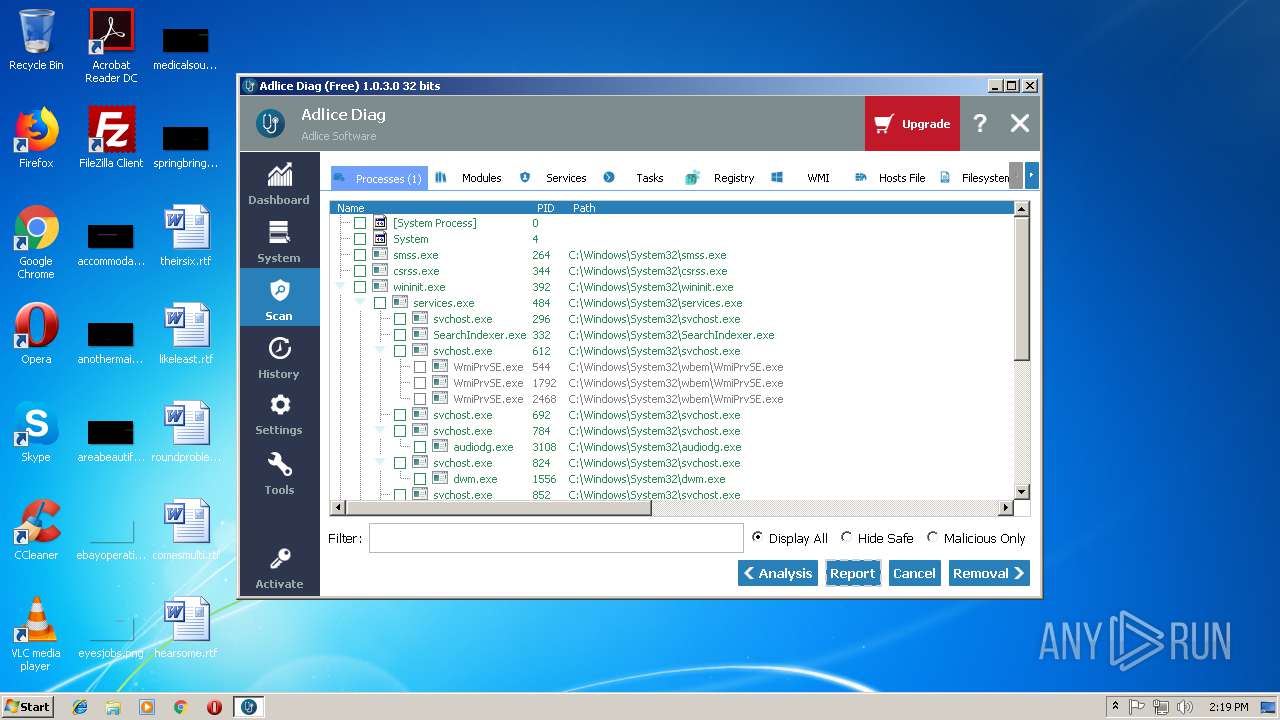
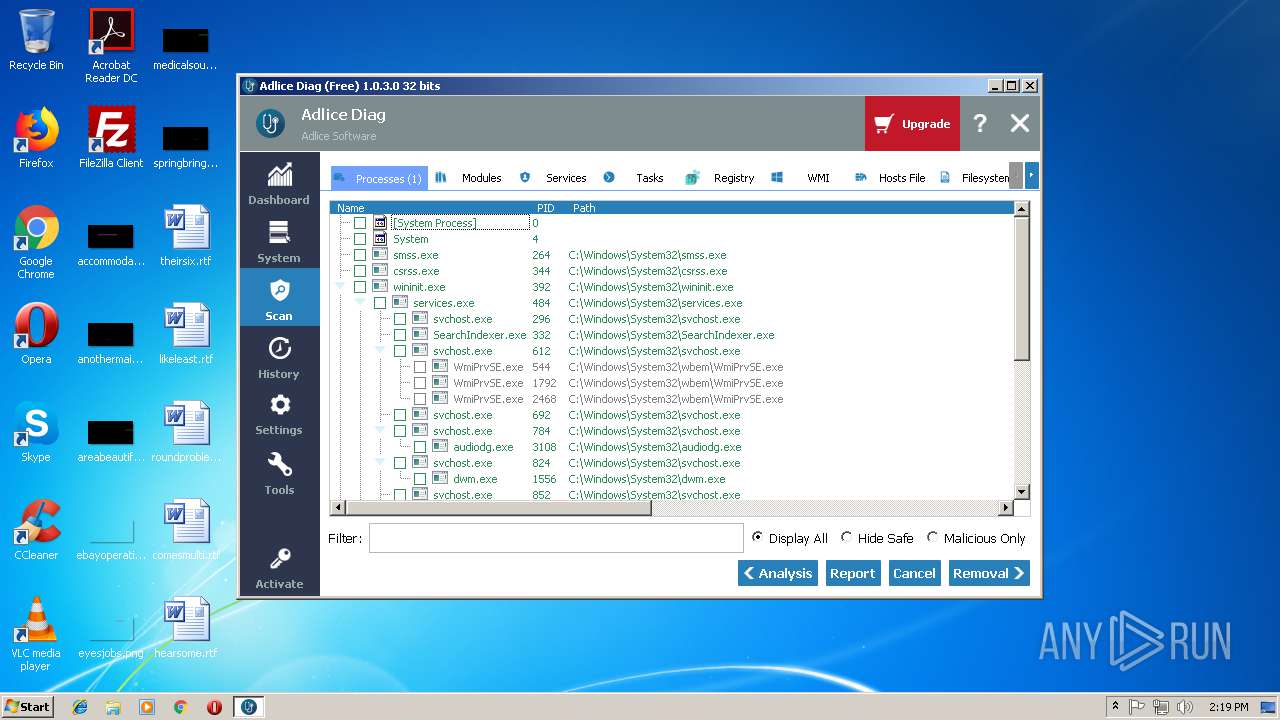
Total processes
46
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1540 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://adlice.com/thanks-downloading-diag/?utm_campaign=diag&utm_source=soft&utm_medium=btn" | C:\Program Files\Internet Explorer\iexplore.exe | api.exe | ||||||||||||
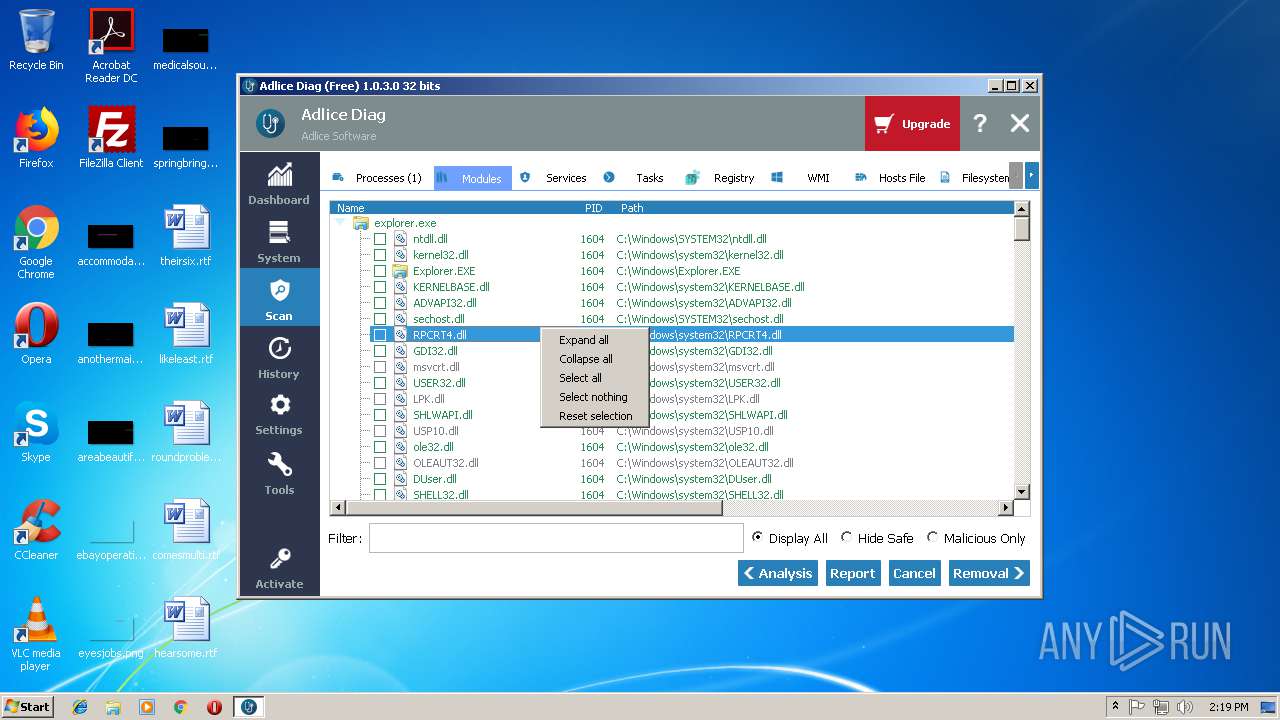
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3280 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3028 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1540 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
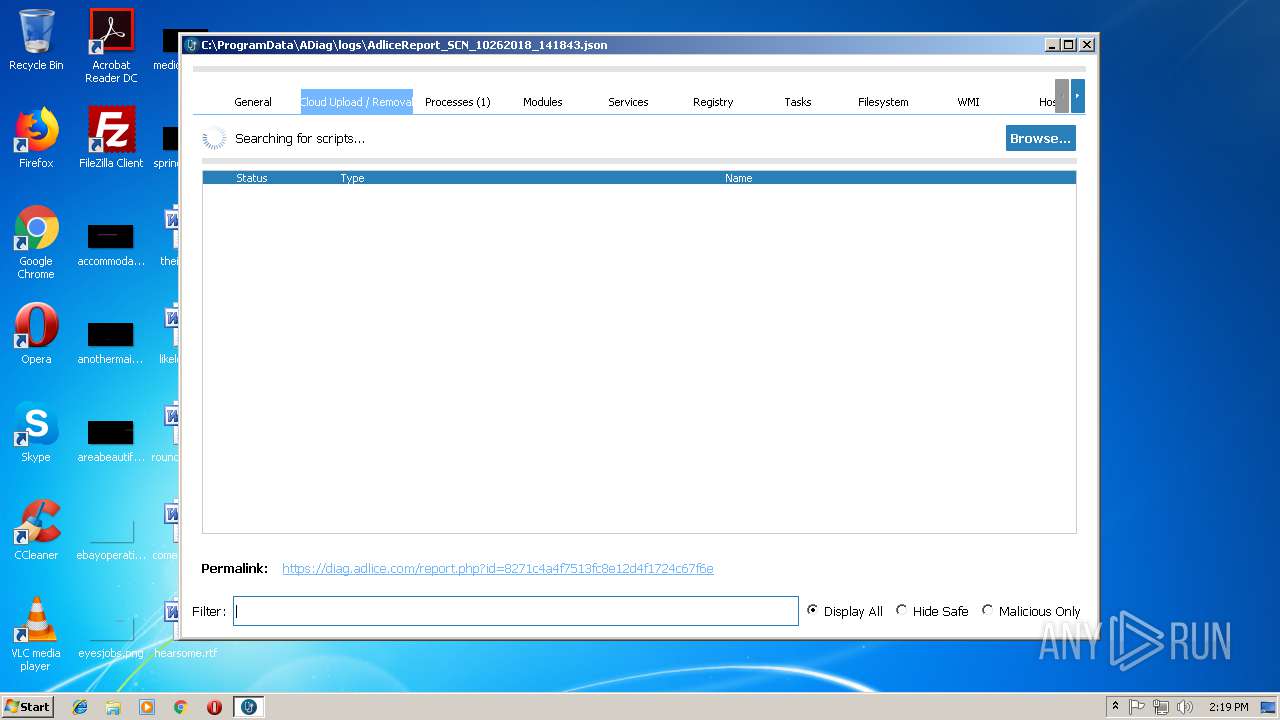
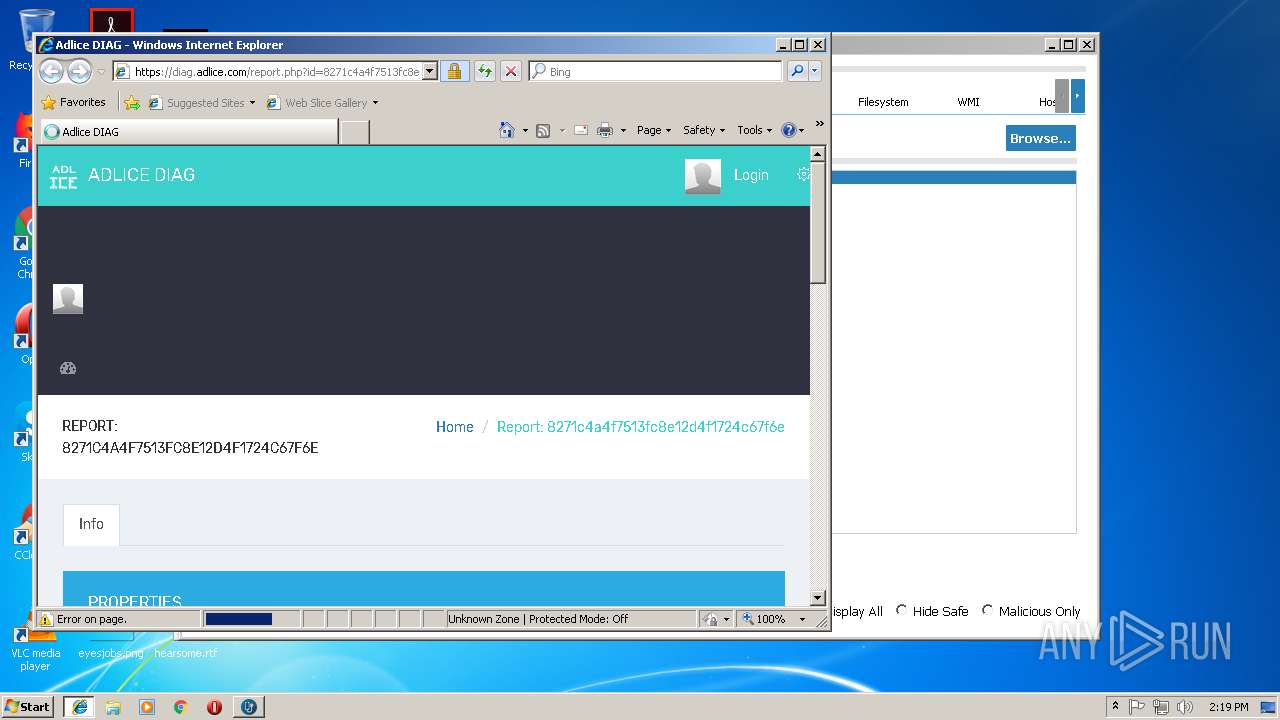
| 3280 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://diag.adlice.com/report.php?id=8271c4a4f7513fc8e12d4f1724c67f6e" | C:\Program Files\Internet Explorer\iexplore.exe | api.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
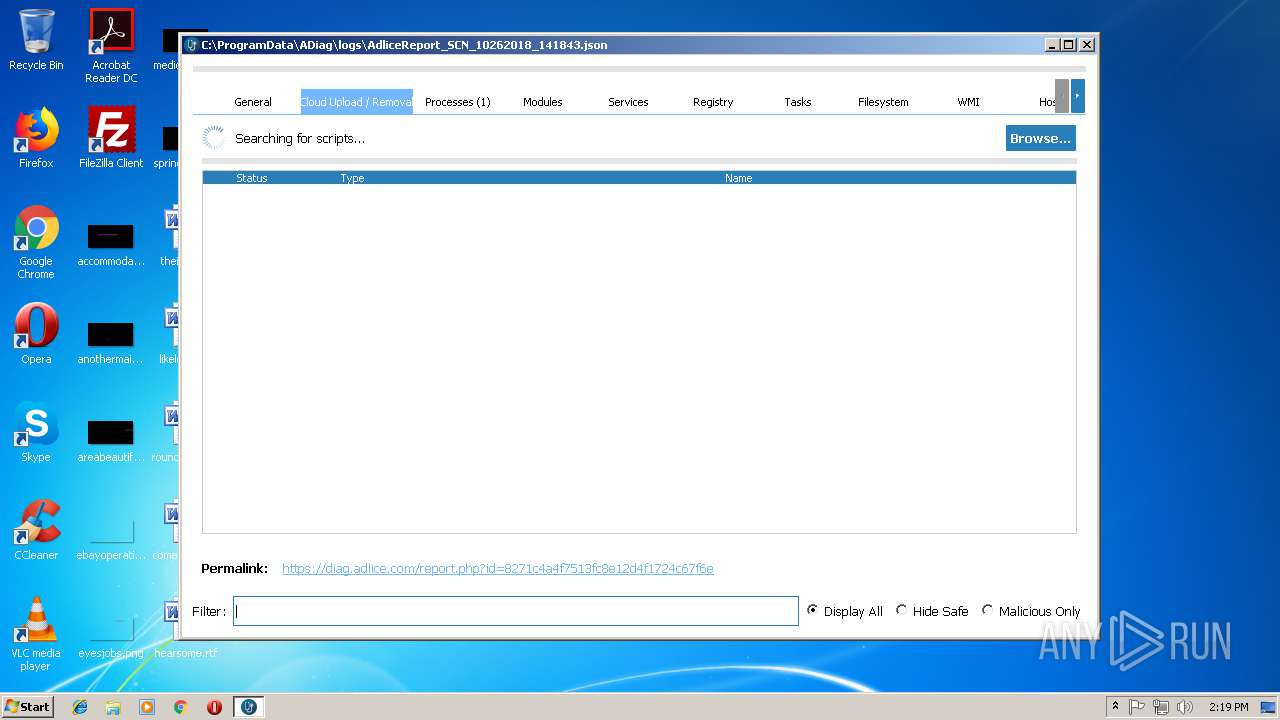
| 3784 | "C:\Users\admin\AppData\Local\Temp\api.exe" | C:\Users\admin\AppData\Local\Temp\api.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3788 | "C:\Users\admin\AppData\Local\Temp\api.exe" | C:\Users\admin\AppData\Local\Temp\api.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3916 | C:\Windows\system32\wbem\WmiApSrv.exe | C:\Windows\system32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4064 | C:\Windows\system32\wbem\WmiApSrv.exe | C:\Windows\system32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 150
Read events
1 003
Write events
145
Delete events
2
Modification events
| (PID) Process: | (3788) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3788) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3788) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3788) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3788) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3788) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3788) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3788) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3788) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3788) api.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\api_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
16
Text files
63
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1540 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF64F74B4DB54002AD.TMP | — | |
MD5:— | SHA256:— | |||
| 1540 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB920F0C97CD2EA7D.TMP | — | |
MD5:— | SHA256:— | |||
| 1540 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3DC254C53F55B2C0.TMP | — | |
MD5:— | SHA256:— | |||
| 1540 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA383535FE62FE8B9.TMP | — | |
MD5:— | SHA256:— | |||
| 1540 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\RecoveryStore.{3C68D3F5-D921-11E8-BFAB-5254004AAD11}.dat | — | |
MD5:— | SHA256:— | |||
| 3788 | api.exe | C:\Users\admin\AppData\Local\Temp\CabC308.tmp | — | |
MD5:— | SHA256:— | |||
| 3788 | api.exe | C:\Users\admin\AppData\Local\Temp\TarC309.tmp | — | |
MD5:— | SHA256:— | |||
| 3788 | api.exe | C:\Users\admin\AppData\Local\Temp\CabC3A6.tmp | — | |
MD5:— | SHA256:— | |||
| 3788 | api.exe | C:\Users\admin\AppData\Local\Temp\TarC3A7.tmp | — | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
197
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3788 | api.exe | GET | 200 | 104.16.90.188:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | US | der | 1.37 Kb | whitelisted |
3788 | api.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 54.2 Kb | whitelisted |
3280 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3788 | api.exe | 178.33.106.117:443 | download.adlice.com | OVH SAS | FR | suspicious |
1540 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3028 | iexplore.exe | 104.27.165.26:443 | adlice.com | Cloudflare Inc | US | shared |
3788 | api.exe | 104.16.90.188:80 | crt.comodoca.com | Cloudflare Inc | US | shared |
3788 | api.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3788 | api.exe | 74.125.34.46:443 | www.virustotal.com | Google Inc. | US | whitelisted |
3280 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2728 | iexplore.exe | 178.33.106.117:443 | download.adlice.com | OVH SAS | FR | suspicious |
2728 | iexplore.exe | 216.58.205.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2728 | iexplore.exe | 23.111.8.154:443 | oss.maxcdn.com | netDNA | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.adlice.com |
| whitelisted |
adlice.com |
| whitelisted |
www.bing.com |
| whitelisted |
adflux.adlice.com |
| whitelisted |
stats.adlice.com |
| whitelisted |
www.virustotal.com |
| whitelisted |
crt.comodoca.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
diag.adlice.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|
api.exe | libpng warning: iCCP: known incorrect sRGB profile
|
api.exe | QObject::connect: Cannot queue arguments of type 'QVector<int>'
(Make sure 'QVector<int>' is registered using qRegisterMetaType().)
|
api.exe | QObject::connect: Cannot queue arguments of type 'QVector<int>'
(Make sure 'QVector<int>' is registered using qRegisterMetaType().)
|
api.exe | QObject::connect: Cannot queue arguments of type 'QVector<int>'
(Make sure 'QVector<int>' is registered using qRegisterMetaType().)
|
api.exe | QObject::connect: Cannot queue arguments of type 'QVector<int>'
(Make sure 'QVector<int>' is registered using qRegisterMetaType().)
|