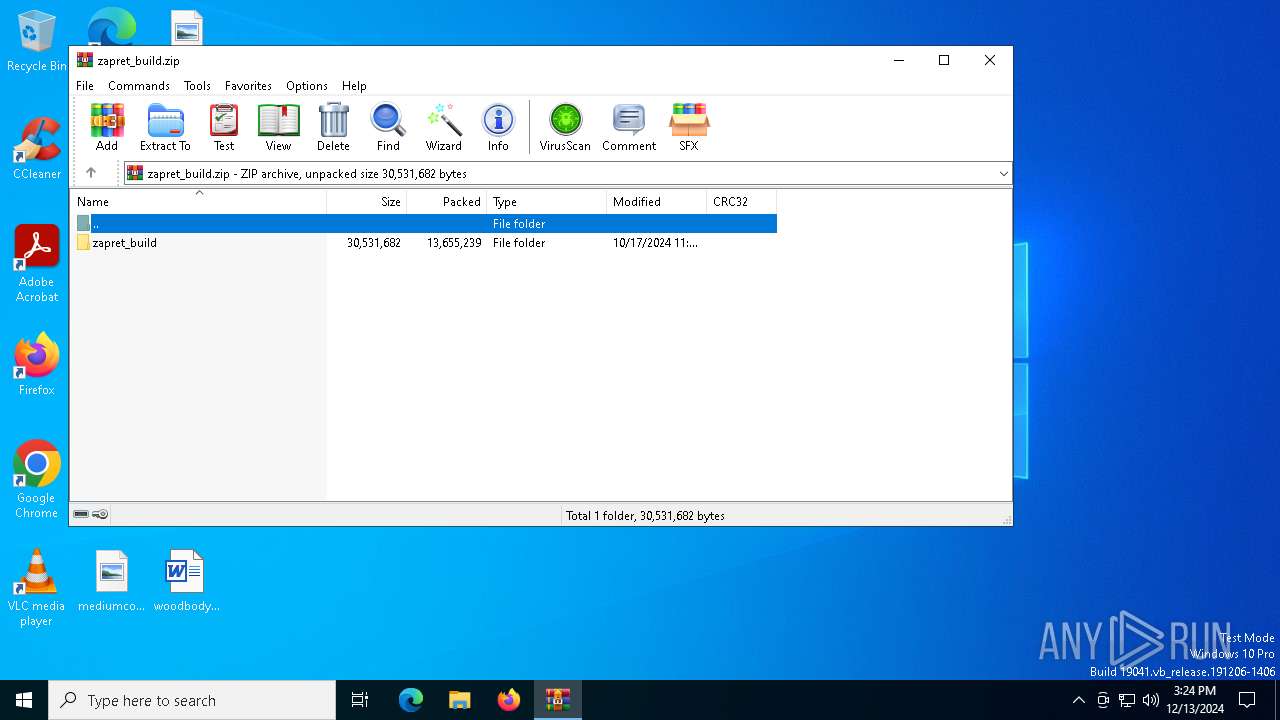
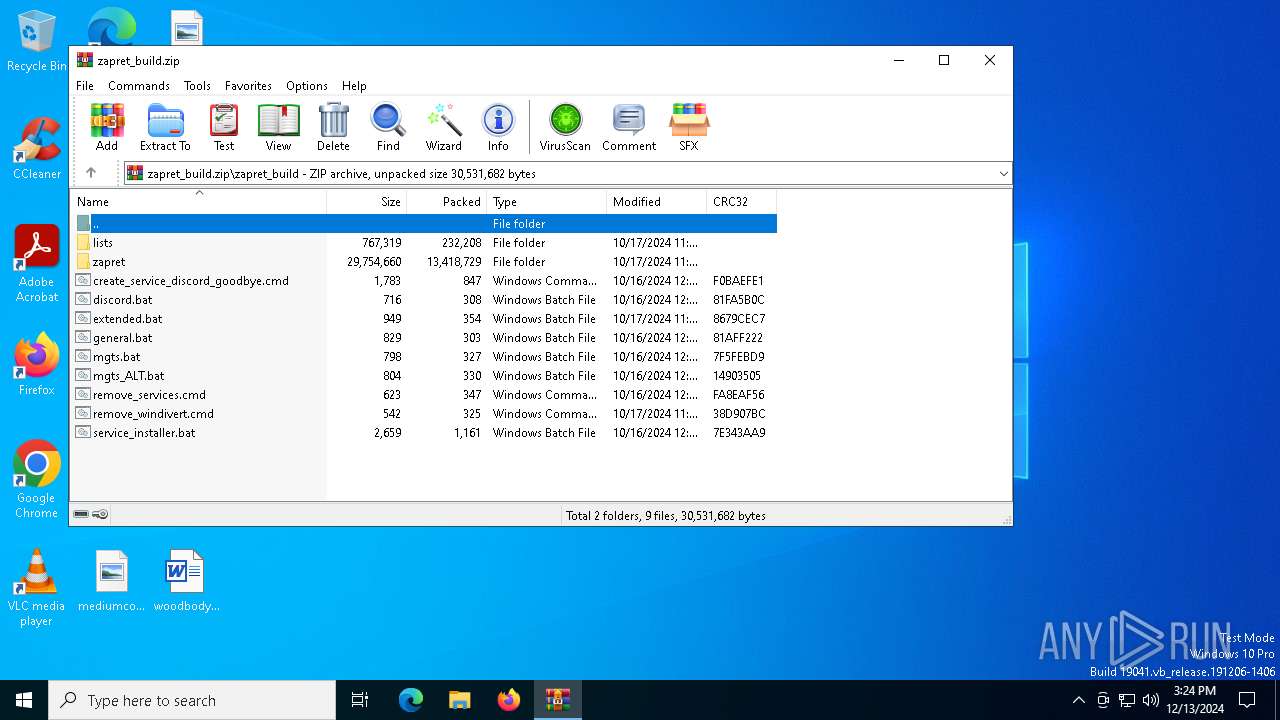
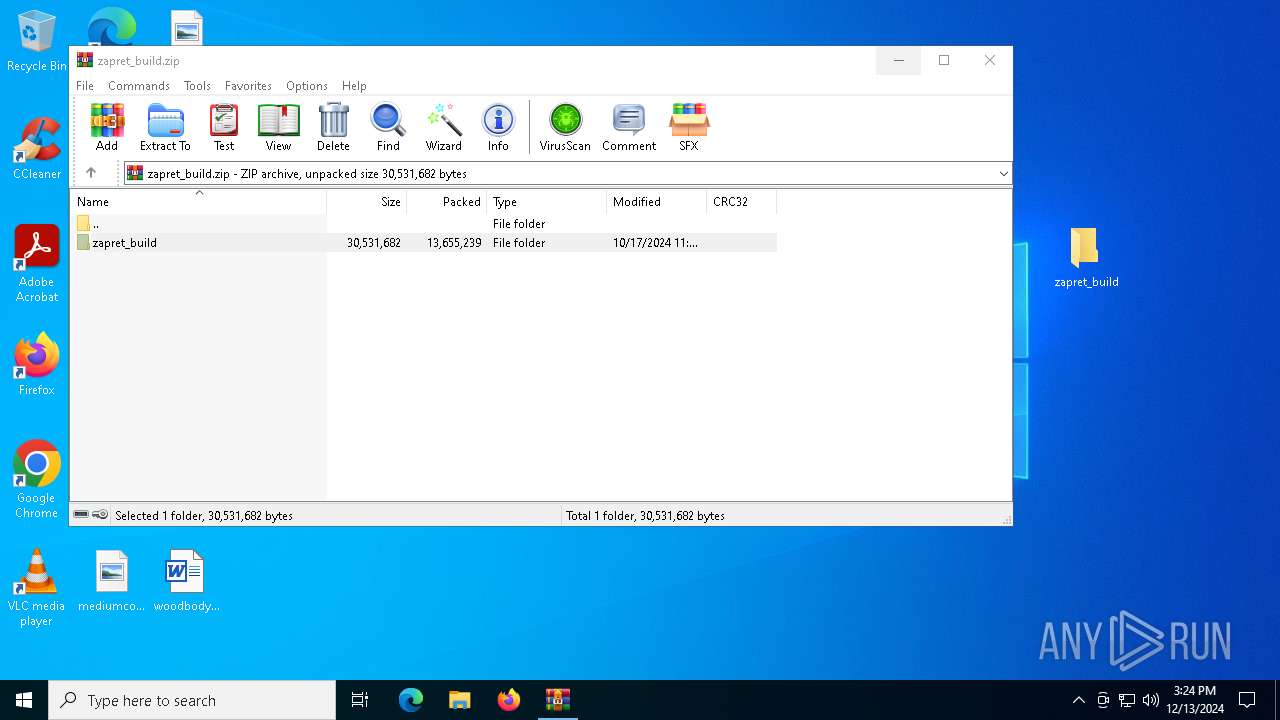
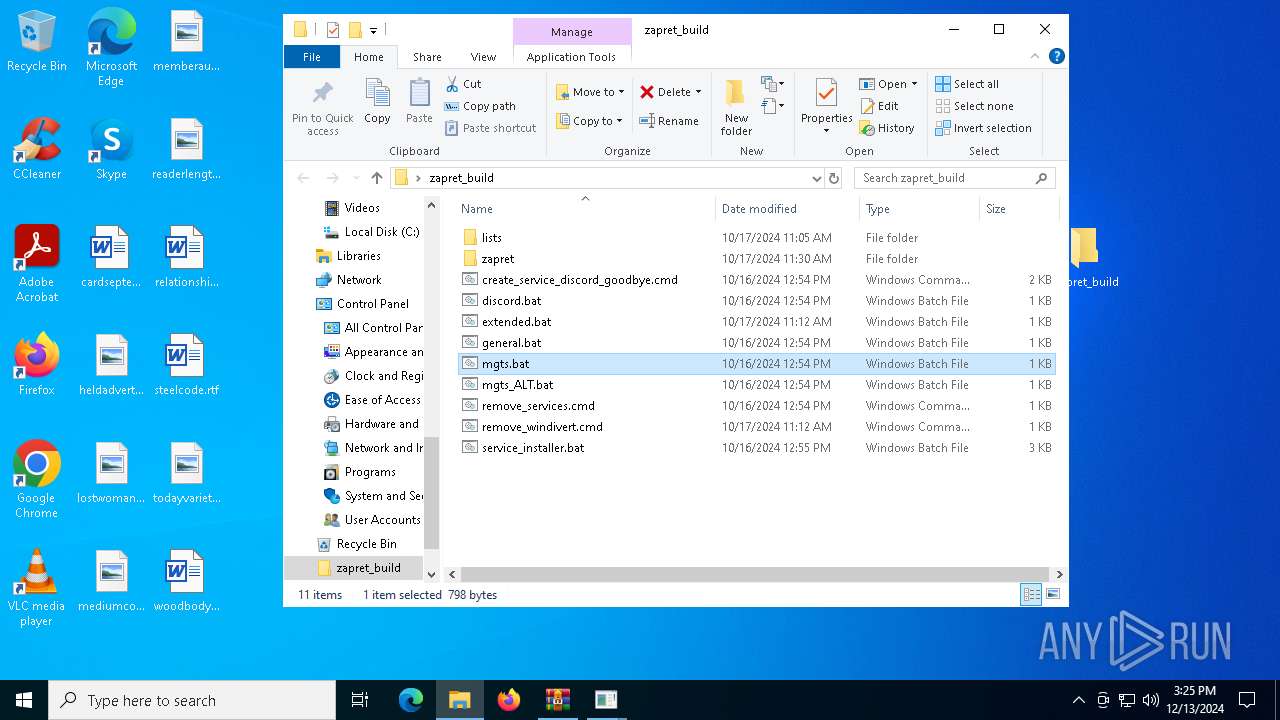
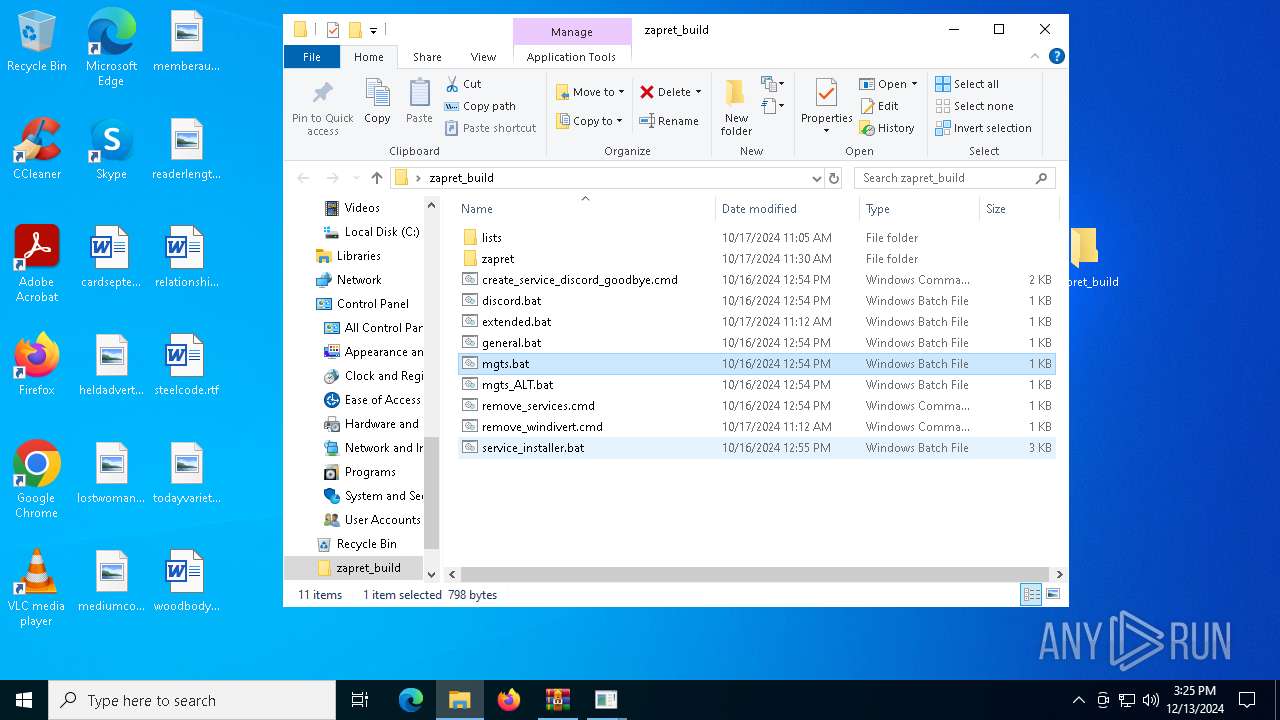
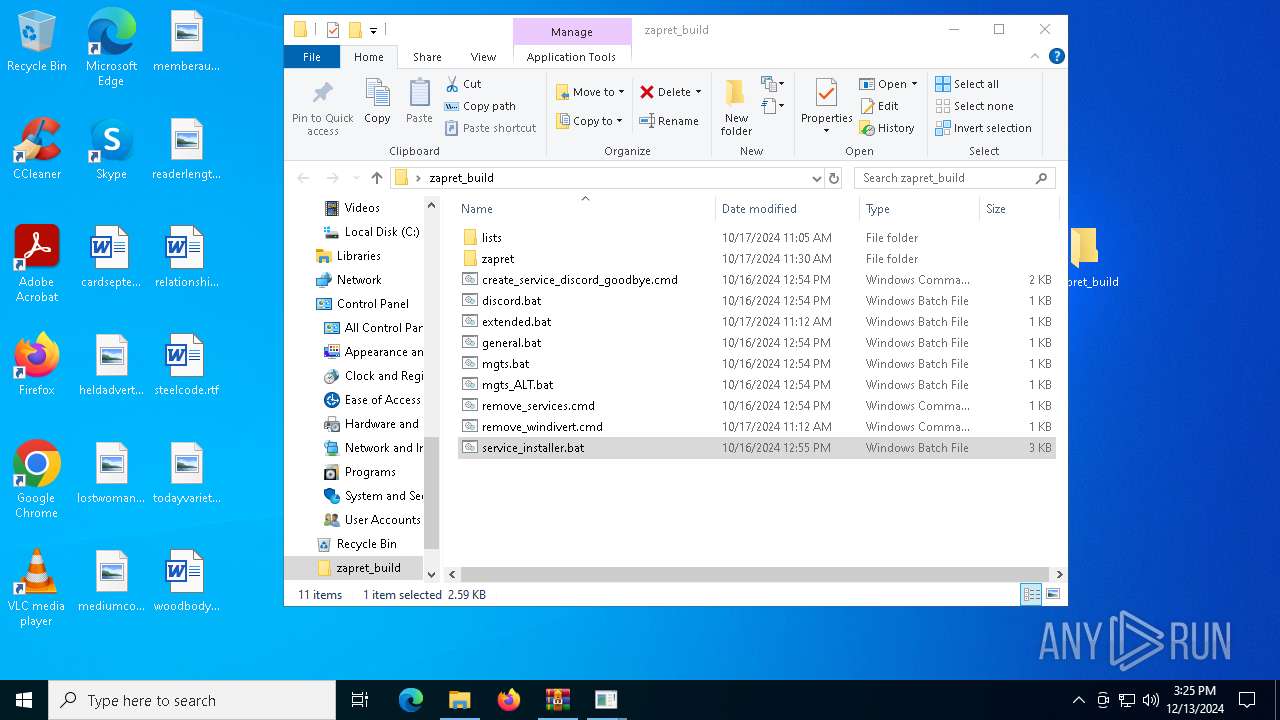
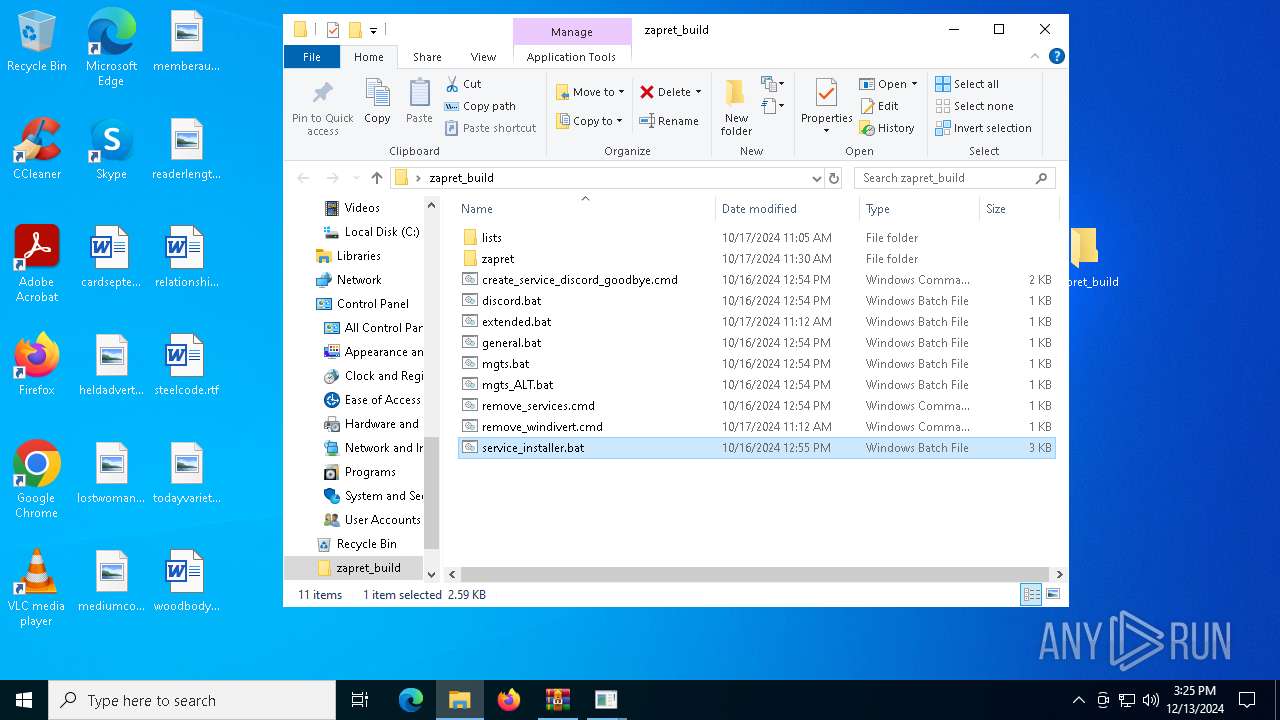
| File name: | zapret_build.zip |
| Full analysis: | https://app.any.run/tasks/513f3710-f1b2-4095-adfc-f5ad9a887540 |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 15:24:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | E9CAF5D3B51C2E7AA2FD6B9E84362A0C |
| SHA1: | 932FC5785D1D49050B9DFE0323F99815A5ED69C0 |
| SHA256: | 4FC3E517B7855FDC966FDFCA0431317D5B4A22D46C757045B5070112B39F4FF4 |
| SSDEEP: | 98304:H6UYPkxljOp5lZ3BVJh/8fiuhpeFEP6th02KcUD6etsfNZPZQ2+i+4sHSXGRpljv:OPbSkdiDOYZnTUOKTPqZad4cMp |
MALICIOUS
Detects Cygwin installation
- WinRAR.exe (PID: 6536)
Generic archive extractor
- WinRAR.exe (PID: 6536)
Starts NET.EXE for service management
- cmd.exe (PID: 2972)
- net.exe (PID: 5748)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 6536)
Starts SC.EXE for service management
- cmd.exe (PID: 2972)
INFO
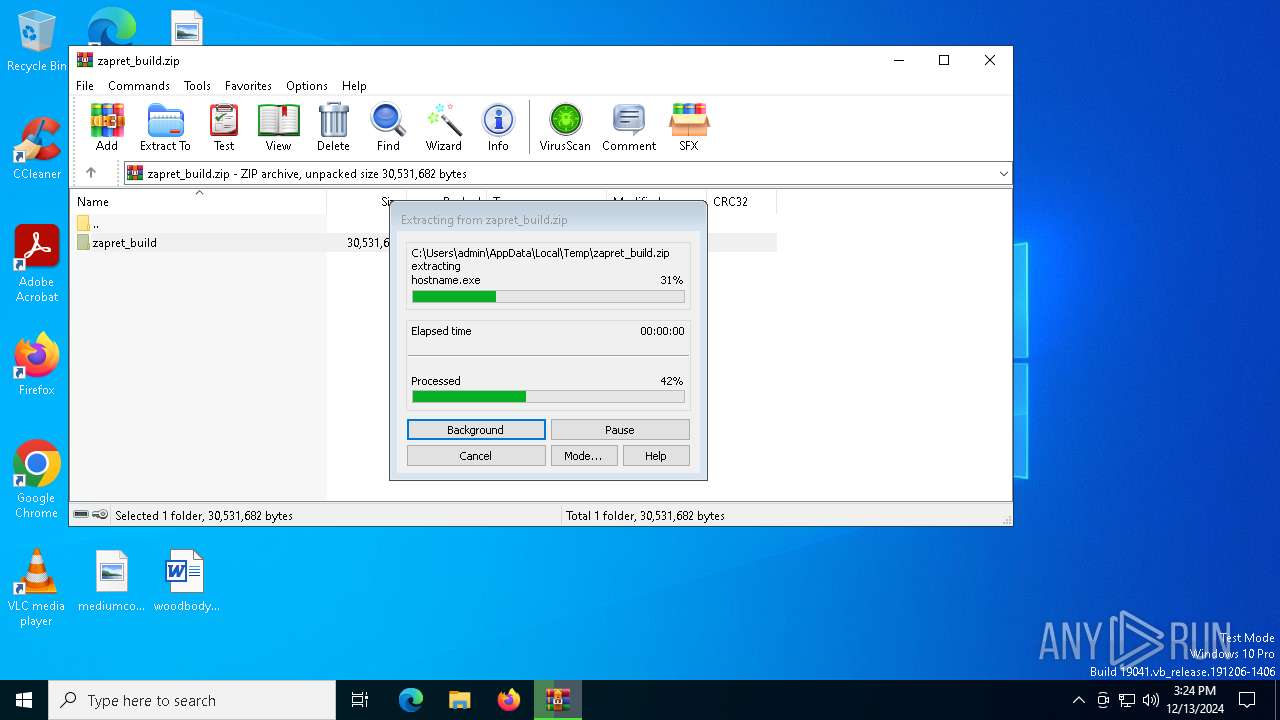
The process uses the downloaded file
- WinRAR.exe (PID: 6536)
- cmd.exe (PID: 4596)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6536)
The sample compiled with english language support
- WinRAR.exe (PID: 6536)
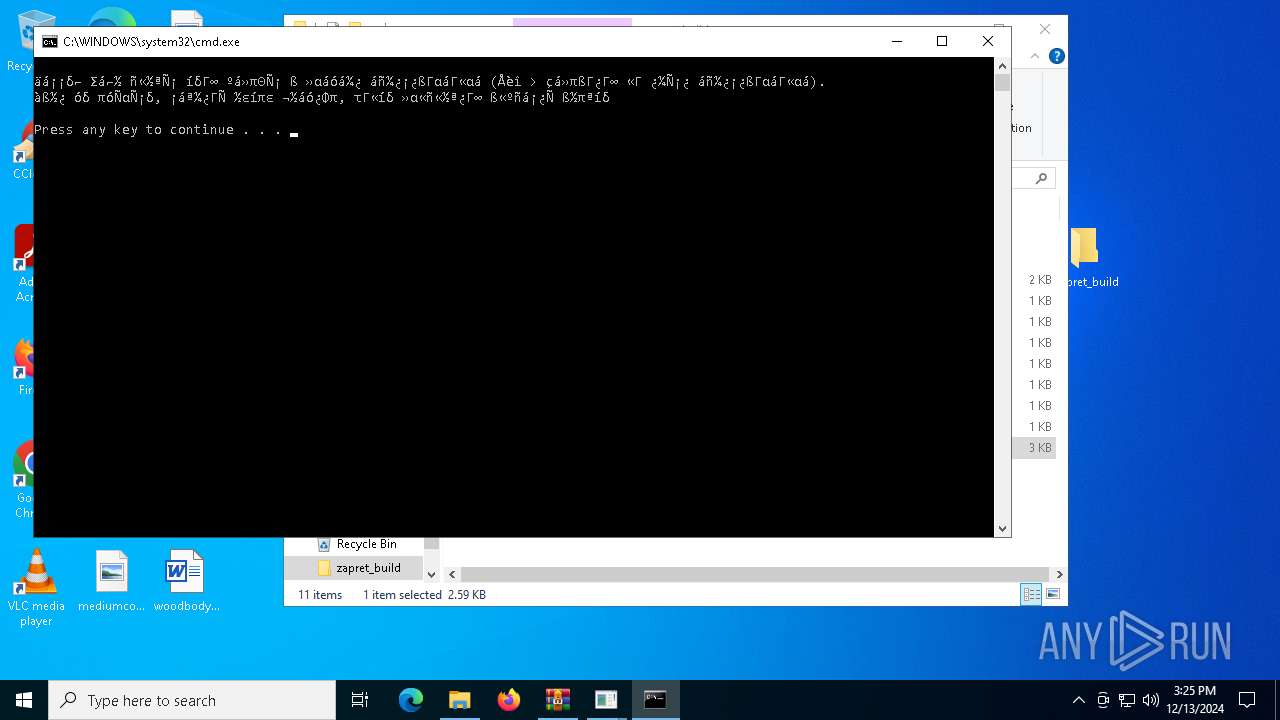
Manual execution by a user
- cmd.exe (PID: 6856)
- cmd.exe (PID: 2972)
- cmd.exe (PID: 4596)
- cmd.exe (PID: 6372)
UPX packer has been detected
- winws.exe (PID: 7000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:10:17 16:12:24 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | zapret_build/ |
Total processes
144
Monitored processes
24
Malicious processes
2
Suspicious processes
0
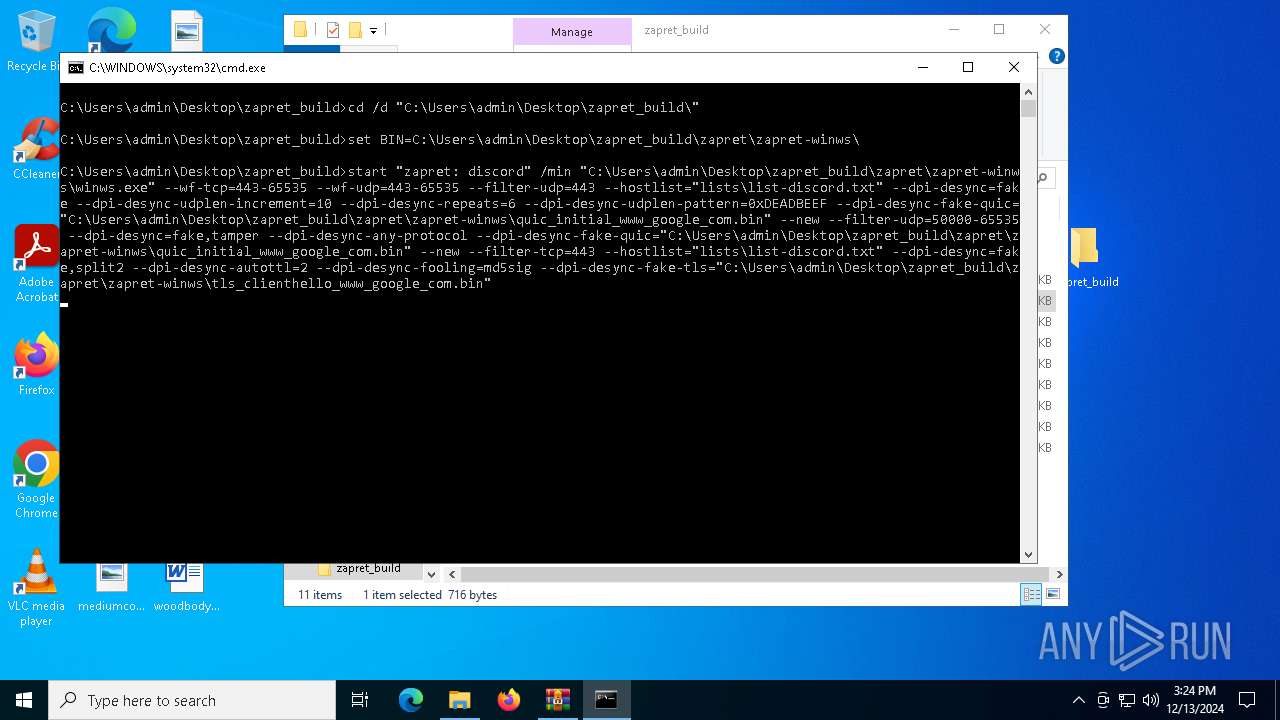
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
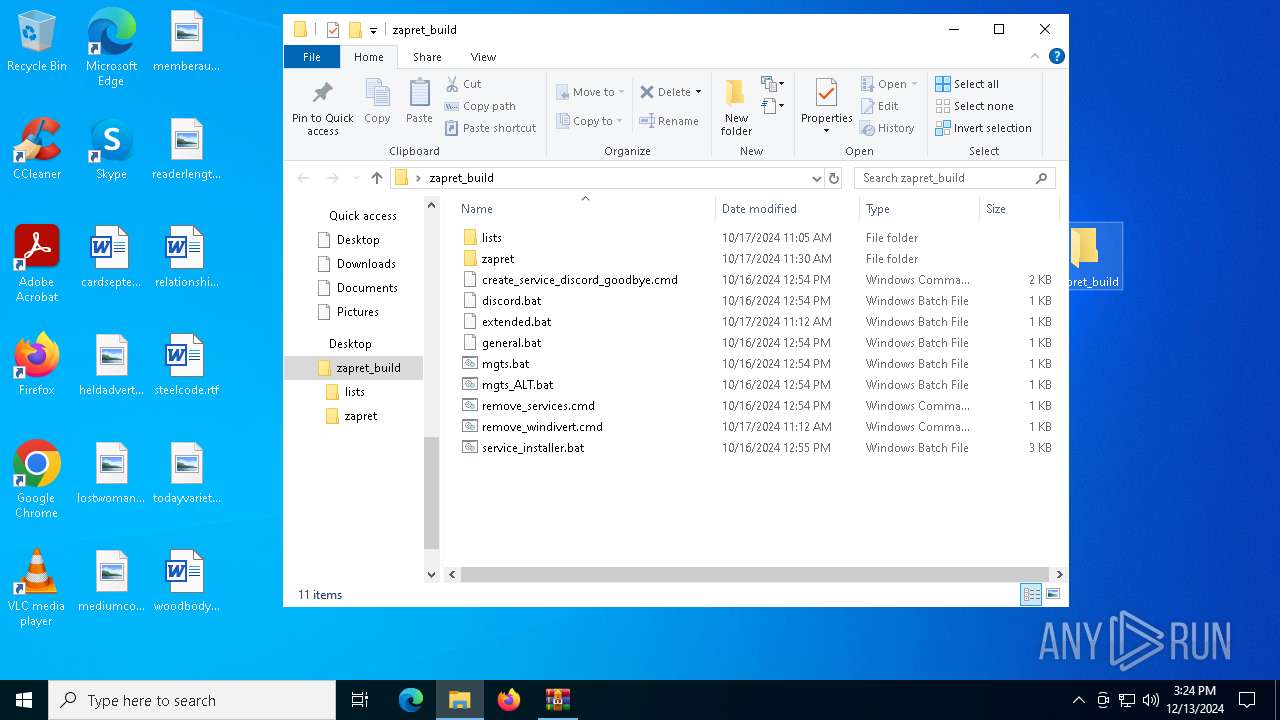
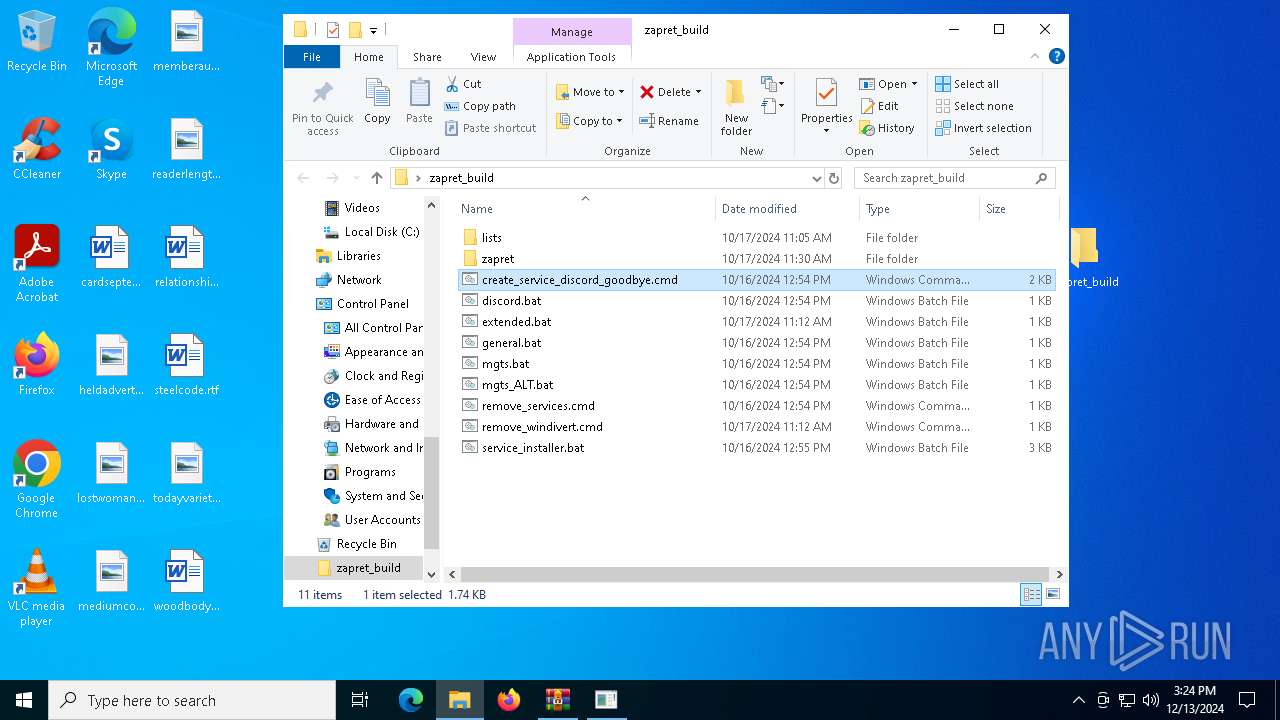
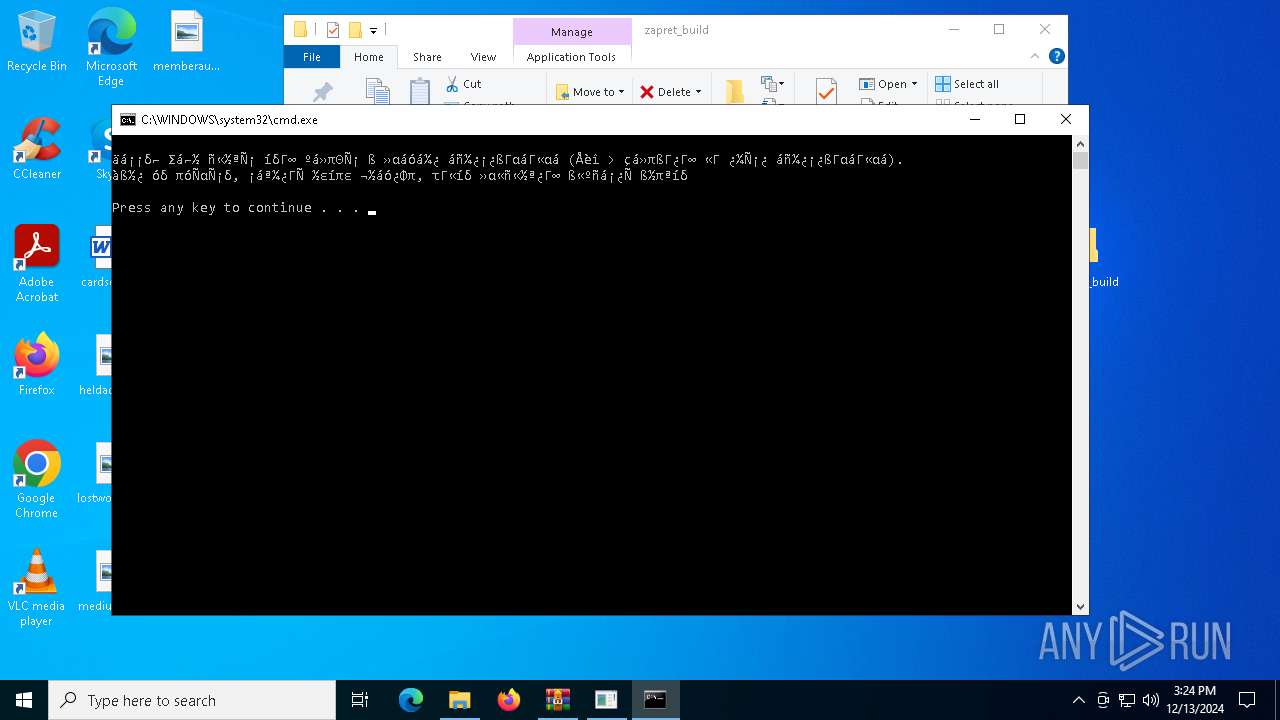
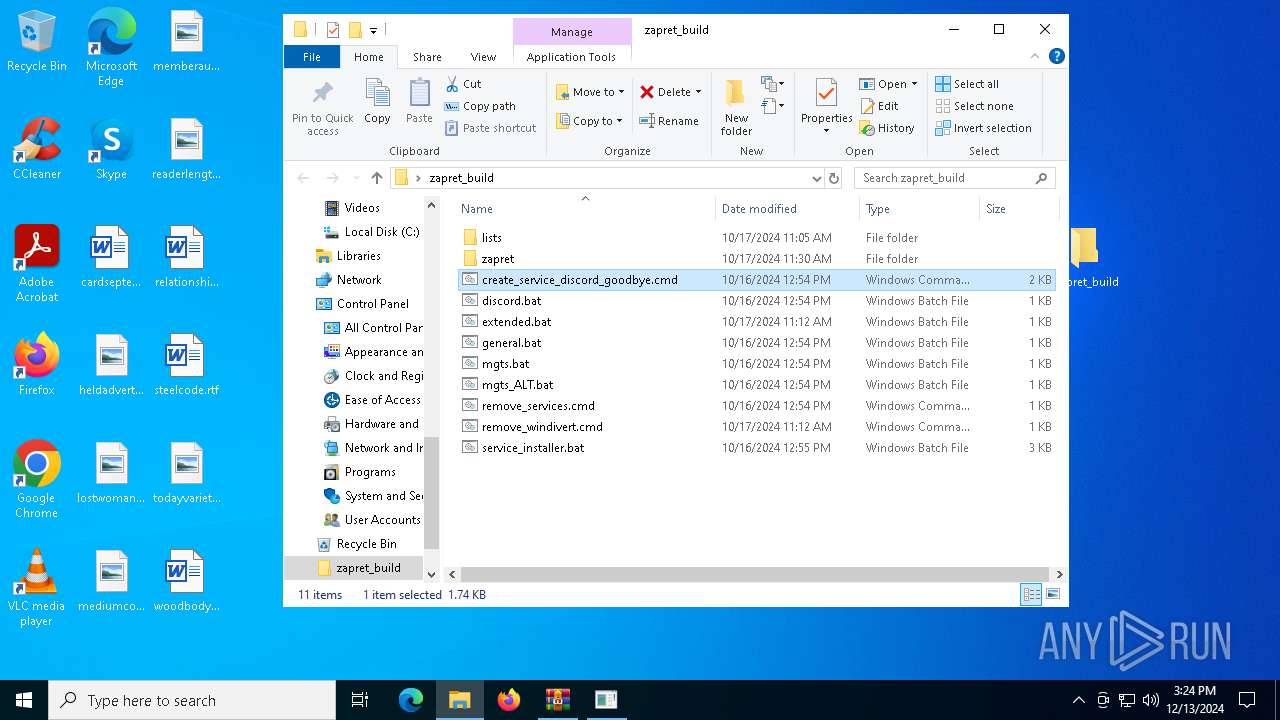
| 2972 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\zapret_build\create_service_discord_goodbye.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3260 | "C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\winws.exe" --wf-raw="@lists\rules.txt" --filter-udp=443 --hostlist="lists\list-general.txt" --dpi-desync=fake --dpi-desync-udplen-increment=10 --dpi-desync-repeats=6 --dpi-desync-udplen-pattern=0xDEADBEEF --dpi-desync-fake-quic="C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\quic_initial_www_google_com.bin" --new --filter-udp=50000-65535 --dpi-desync=fake,tamper --dpi-desync-any-protocol --dpi-desync-fake-quic="C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\quic_initial_www_google_com.bin" --new --filter-tcp=80 --dpi-desync=split --dpi-desync-ttl=4 --dpi-desync-fooling=md5sig --new --filter-tcp=443 --hostlist="lists\list-general.txt" --dpi-desync=fake,split2 --dpi-desync-ttl=2 --dpi-desync-split-pos=1 --dpi-desync=fake,disorder2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig | C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\winws.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3420 | sc description "zapret" "zapret DPI bypass software" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3772 | "C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\winws.exe" --wf-raw="@lists\rules.txt" --filter-udp=443 --hostlist="lists\list-general.txt" --dpi-desync=fake --dpi-desync-udplen-increment=10 --dpi-desync-repeats=6 --dpi-desync-udplen-pattern=0xDEADBEEF --dpi-desync-fake-quic="C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\quic_initial_www_google_com.bin" --new --filter-udp=50000-65535 --dpi-desync=fake,tamper --dpi-desync-any-protocol --dpi-desync-fake-quic="C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\quic_initial_www_google_com.bin" --new --filter-tcp=80 --dpi-desync=split --dpi-desync-ttl=4 --dpi-desync-fooling=md5sig --new --filter-tcp=443 --hostlist="lists\list-general.txt" --dpi-desync=fake,split2 --dpi-desync-ttl=2 --dpi-desync-split-pos=1 --dpi-desync=fake,disorder2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig | C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\winws.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4076 | C:\WINDOWS\system32\net1 stop "zapret" | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4516 | "C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\winws.exe" --wf-raw="@lists\rules.txt" --filter-udp=443 --hostlist="lists\list-general.txt" --dpi-desync=fake --dpi-desync-udplen-increment=10 --dpi-desync-repeats=6 --dpi-desync-udplen-pattern=0xDEADBEEF --dpi-desync-fake-quic="C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\quic_initial_www_google_com.bin" --new --filter-udp=50000-65535 --dpi-desync=fake,tamper --dpi-desync-any-protocol --dpi-desync-fake-quic="C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\quic_initial_www_google_com.bin" --new --filter-tcp=80 --dpi-desync=split --dpi-desync-ttl=4 --dpi-desync-fooling=md5sig --new --filter-tcp=443 --hostlist="lists\list-general.txt" --dpi-desync=fake,split2 --dpi-desync-ttl=2 --dpi-desync-split-pos=1 --dpi-desync=fake,disorder2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig | C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\winws.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
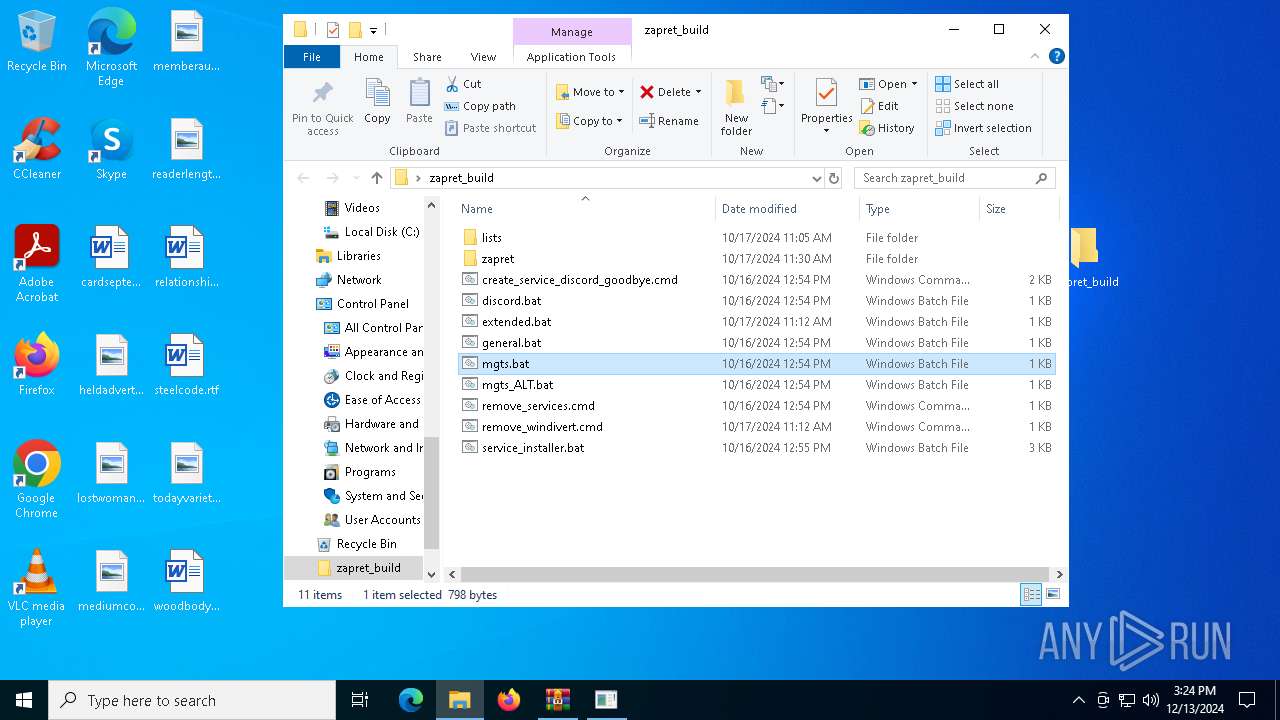
| 4596 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\zapret_build\mgts.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4672 | sc create "zapret" binPath="\"C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\winws.exe\" --wf-raw=\"@C:\Users\admin\Desktop\zapret_build\lists\rules.txt\" --filter-udp=443 --hostlist=\"C:\Users\admin\Desktop\zapret_build\lists\list-discord.txt\" --dpi-desync=fake --dpi-desync-repeats=6 --dpi-desync-fake-quic=\"C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\quic_initial_www_google_com.bin\" --new --filter-udp=50000-65535 --dpi-desync=fake --dpi-desync-any-protocol --dpi-desync-cutoff=d3 --dpi-desync-repeats=6 --dpi-desync-fake-quic=\"C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\quic_initial_www_google_com.bin\" --new --filter-tcp=443 --hostlist=\"C:\Users\admin\Desktop\zapret_build\lists\list-discord.txt\" --dpi-desync=fake,split --dpi-desync-autottl=2 --dpi-desync-repeats=6 --dpi-desync-fooling=badseq --dpi-desync-fake-tls=\"C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\tls_clienthello_www_google_com.bin\"" DisplayName="zapret DPI bypass: Discord (GoodbyeDPI)" start=auto depend="GoodbyeDPI" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5000 | sc delete "zapret" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5548 | sc start "zapret" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 868
Read events
2 856
Write events
12
Delete events
0
Modification events
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\zapret_build.zip | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7000) winws.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\System\WinDivert |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Users\admin\Desktop\zapret_build\zapret\zapret-winws\WinDivert64.sys | |||
| (PID) Process: | (7000) winws.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\System\WinDivert |
| Operation: | write | Name: | TypesSupported |
Value: 7 | |||
Executable files
143
Suspicious files
190
Text files
73
Unknown types
3
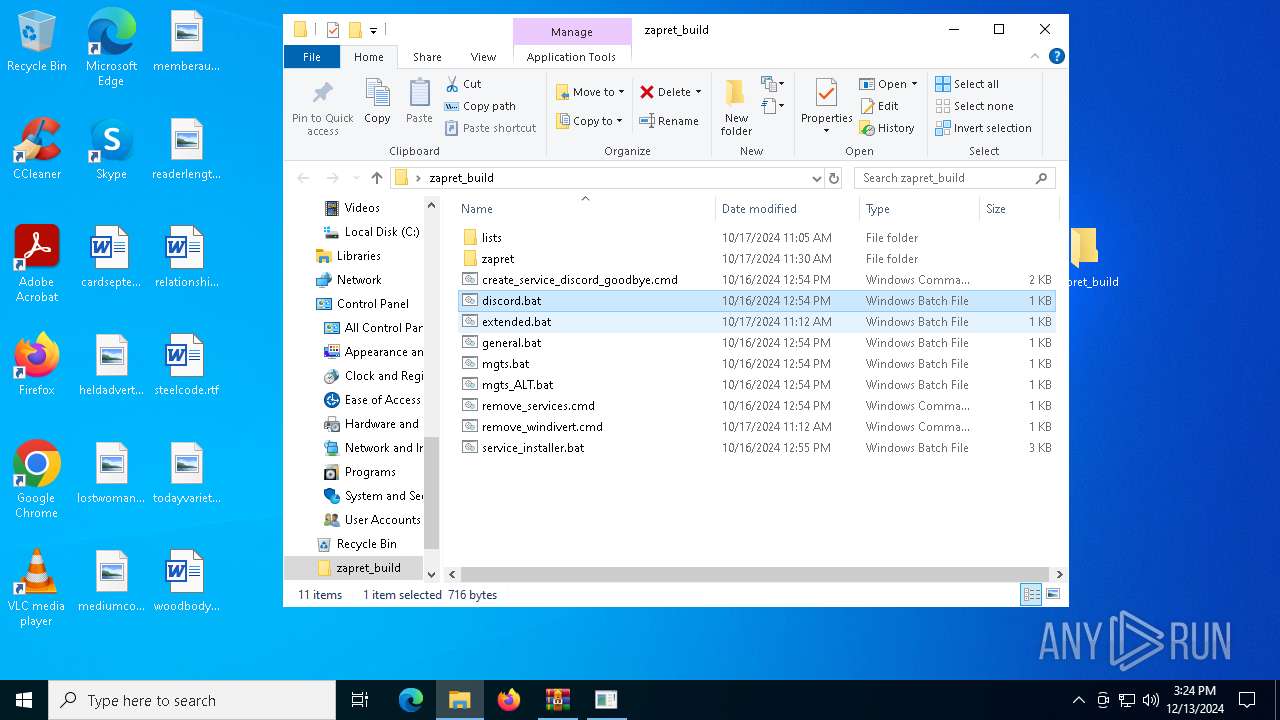
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6536 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6536.27568\zapret_build\zapret\blockcheck\cygwin\bin\arch.exe | executable | |
MD5:BB5A8CD42155A3E7974C9EF8F2ADB32A | SHA256:69A92F9ED499E6451759A1809537C1662C3F1CD2AFFE0A7D9DD555F6B73539FE | |||
| 6536 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6536.27568\zapret_build\create_service_discord_goodbye.cmd | text | |
MD5:7BFDCECD62053A57AD095E1D35527354 | SHA256:C58D6DA183C32BD012303A98D60434F059C7A211E31CA07210F25D1BDA8039FD | |||
| 6536 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6536.27568\zapret_build\mgts_ALT.bat | text | |
MD5:72917D9C4B175C2BFA16BCD2D6F6BEF6 | SHA256:DA968350FE924E9B2DF2F0685308AA46FF63219B00A1D948DD725AF46FD90BFB | |||
| 6536 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6536.27568\zapret_build\service_installer.bat | text | |
MD5:CA37C8E89A8B7F9E64FFF263F8DA31EA | SHA256:841AE034E2BFA92BEFB162DE7C93F7A66E5CCD2C7D806D2E6508C13B77185845 | |||
| 6536 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6536.27568\zapret_build\remove_services.cmd | text | |
MD5:ABA7EE2B3CBFBD0E1C676A9A2B9A5C8E | SHA256:916CE8F038BA41224EA09C217B3589D7CE1F5BD5B8B8FF272EF4D946AB9FD405 | |||
| 6536 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6536.27568\zapret_build\lists\list-general.txt | text | |
MD5:A03D2C9945CD2C801C3CE17519513BE9 | SHA256:0D1ABA287A4DBE47A4F077E527C34FACC459DFA715CD89E990C8C5FC4C9C672F | |||
| 6536 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6536.27568\zapret_build\zapret\blockcheck\cygwin\bin\basename.exe | executable | |
MD5:88910994D984FE1EC33239D4AA91CCEF | SHA256:1D36AF5EF59CF397DE184E23B4C9A32C2FBD4D0AA8E33309578E400976E42244 | |||
| 6536 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6536.27568\zapret_build\remove_windivert.cmd | text | |
MD5:99281FA177A93F3D930A13598D348851 | SHA256:3059B74B12E5731DFA2D725AD6E77D3AF983BAF93DA2F8CB7D2F1076D4E74F6B | |||
| 6536 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6536.27568\zapret_build\zapret\blockcheck\cygwin\bin\bash.exe | executable | |
MD5:4ABEFC48E21AB1D2E805994119183A51 | SHA256:DF601377E3C85F60DF06A5A1B3BE87EC2B1892580BE86BD39D51E42C03BEE2B1 | |||
| 6536 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6536.27568\zapret_build\zapret\blockcheck\blockcheck.cmd | text | |
MD5:63728C8F6BA352B98189B00ABB568518 | SHA256:2F3BCDD441689BA6FE7D08D2DD715B2B25EC16D0BDD4DC2A405ED11D6C2FB9D2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
34
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4 | System | GET | 200 | 23.48.23.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4 | System | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
132 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7144 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 92.123.104.43:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.138:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 23.48.23.138:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |