| File name: | 3f17b75eeee9de388f51ef821ed30f15 |
| Full analysis: | https://app.any.run/tasks/b913df89-031c-4f70-905f-2282ef0c9a1b |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2022, 06:17:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3F17B75EEEE9DE388F51EF821ED30F15 |
| SHA1: | 937B032589EB76EB685FB19A02CD5952C89DAB8C |
| SHA256: | 4FB79897FD57AC7D1724C92EF26E493E15D974F83C2C7F6E72AF4F6E8084FF20 |
| SSDEEP: | 3072:D/s8DI8Sa/p0b2q6wU1tDULG2WZbfqzI/P51Xmfk1M/h3:Dk8M8fY/VmtGDgp1 |
MALICIOUS
Application was dropped or rewritten from another process
- offgduqm.exe (PID: 1044)
TOFSEE detected by memory dumps
- svchost.exe (PID: 1596)
Modifies exclusions in Windows Defender
- svchost.exe (PID: 1596)
Creates a writable file the system directory
- svchost.exe (PID: 1596)
SUSPICIOUS
Reads the Internet Settings
- 3f17b75eeee9de388f51ef821ed30f15.exe (PID: 1756)
Executes as Windows Service
- offgduqm.exe (PID: 1044)
Detected use of alternative data streams (AltDS)
- svchost.exe (PID: 1596)
Creates or modifies Windows services
- svchost.exe (PID: 1596)
Connects to SMTP port
- svchost.exe (PID: 1596)
Connects to unusual port
- svchost.exe (PID: 1596)
- svchost.exe (PID: 3828)
Application launched itself
- svchost.exe (PID: 1596)
INFO
Checks supported languages
- 3f17b75eeee9de388f51ef821ed30f15.exe (PID: 1756)
- offgduqm.exe (PID: 1044)
Reads the computer name
- 3f17b75eeee9de388f51ef821ed30f15.exe (PID: 1756)
- offgduqm.exe (PID: 1044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Tofsee
(PID) Process(1596) svchost.exe
C2 (2)patmushta.info
ovicrush.cn
Encrypted Strings (59)c:\Windows
\system32\
ImagePath
.exe
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
MSConfig
/r
.exe
cmd /C move /Y "%s" %s
sc config %s binPath= "%s%s /d\"%s\""
sc start %s
svchost.exe
SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
ConsentPromptBehaviorAdmin
PromptOnSecureDesktop
MSConfig
:.repos
USERPROFILE
\Local Settings:.repos
USERPROFILE
\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat.repos
USERPROFILE
\wincookie.repos
TMP
Config
Control Panel\Buses
Config
SOFTWARE\Microsoft\Buses
Config
Control Panel\Buses
Config
SOFTWARE\Microsoft\Buses
SYSTEM\CurrentControlSet\services
ImagePath
SYSTEM\CurrentControlSet\services
SYSTEM\CurrentControlSet\services
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
.exe
qazwsxed
%s%i%i%i%i.bat
@echo off
:next_try
del "%s">nul
if exist "%s" (
ping 127.0.0.1 >nul
goto next_try
)
del %%0
svchost.exe
.exe
/u
USERPROFILE
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
/d
/e
/d
/e
.exe
"%s" /u"%s"
USERPROFILE
.exe
USERPROFILE
USERPROFILE
ver=%d lid=%d
win=%X/%d sid=%s
rep=%s
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2021-Feb-22 23:09:13 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 232 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 4 |
| TimeDateStamp: | 2021-Feb-22 23:09:13 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 4096 | 73461 | 73728 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67293 |
.rdata | 77824 | 124744 | 124928 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.94686 |
.data | 204800 | 53628 | 35328 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.719982 |
.rsrc | 262144 | 58696 | 58880 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.24425 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.75223 | 3752 | UNKNOWN | French - Belgium | RT_ICON |
2 | 5.75898 | 2216 | UNKNOWN | French - Belgium | RT_ICON |
3 | 6.05029 | 1384 | UNKNOWN | French - Belgium | RT_ICON |
4 | 5.99528 | 9640 | UNKNOWN | French - Belgium | RT_ICON |
5 | 6.08006 | 4264 | UNKNOWN | French - Belgium | RT_ICON |
6 | 6.01363 | 2440 | UNKNOWN | French - Belgium | RT_ICON |
7 | 6.09734 | 1128 | UNKNOWN | French - Belgium | RT_ICON |
8 | 5.68611 | 3752 | UNKNOWN | French - Belgium | RT_ICON |
9 | 5.76937 | 2216 | UNKNOWN | French - Belgium | RT_ICON |
10 | 5.56158 | 1736 | UNKNOWN | French - Belgium | RT_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
WINHTTP.dll |
Total processes
55
Monitored processes
12
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | sc description cuifczot "wifi internet conection" | C:\Windows\system32\sc.exe | 3f17b75eeee9de388f51ef821ed30f15.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
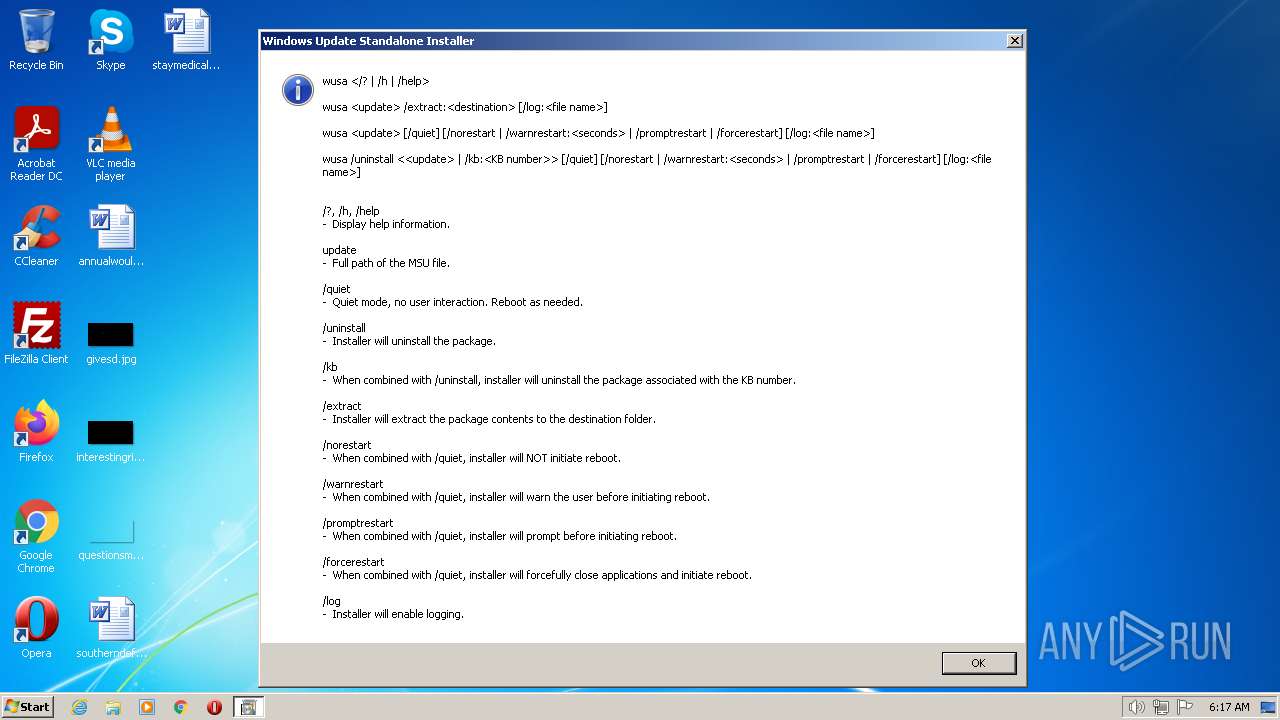
| 568 | "C:\Windows\System32\wusa.exe" | C:\Windows\System32\wusa.exe | — | 3f17b75eeee9de388f51ef821ed30f15.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1044 | C:\Windows\system32\cuifczot\offgduqm.exe /d"C:\Users\admin\AppData\Local\Temp\3f17b75eeee9de388f51ef821ed30f15.exe" | C:\Windows\system32\cuifczot\offgduqm.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1404 | "C:\Windows\System32\wusa.exe" | C:\Windows\System32\wusa.exe | 3f17b75eeee9de388f51ef821ed30f15.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1596 | svchost.exe | C:\Windows\system32\svchost.exe | offgduqm.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
Tofsee(PID) Process(1596) svchost.exe C2 (2)patmushta.info ovicrush.cn Encrypted Strings (59)c:\Windows \system32\ ImagePath .exe SOFTWARE\Microsoft\Windows\CurrentVersion\Run SOFTWARE\Microsoft\Windows\CurrentVersion\Run MSConfig /r .exe cmd /C move /Y "%s" %s
sc config %s binPath= "%s%s /d\"%s\""
sc start %s svchost.exe SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System ConsentPromptBehaviorAdmin PromptOnSecureDesktop MSConfig :.repos USERPROFILE \Local Settings:.repos USERPROFILE \Local Settings\Application Data\Microsoft\Windows\UsrClass.dat.repos USERPROFILE \wincookie.repos TMP Config Control Panel\Buses Config SOFTWARE\Microsoft\Buses Config Control Panel\Buses Config SOFTWARE\Microsoft\Buses SYSTEM\CurrentControlSet\services ImagePath SYSTEM\CurrentControlSet\services SYSTEM\CurrentControlSet\services SOFTWARE\Microsoft\Windows\CurrentVersion\Run SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths SOFTWARE\Microsoft\Windows\CurrentVersion\Run SOFTWARE\Microsoft\Windows\CurrentVersion\Run .exe qazwsxed %s%i%i%i%i.bat @echo off
:next_try
del "%s">nul
if exist "%s" (
ping 127.0.0.1 >nul
goto next_try
)
del %%0 svchost.exe .exe /u USERPROFILE SOFTWARE\Microsoft\Windows\CurrentVersion\Run /d /e /d /e .exe "%s" /u"%s" USERPROFILE .exe USERPROFILE USERPROFILE ver=%d lid=%d
win=%X/%d sid=%s
rep=%s | |||||||||||||||
| 1660 | netsh advfirewall firewall add rule name="Host-process for services of Windows" dir=in action=allow program="C:\Windows\system32\svchost.exe" enable=yes>nul | C:\Windows\system32\netsh.exe | 3f17b75eeee9de388f51ef821ed30f15.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1756 | "C:\Users\admin\AppData\Local\Temp\3f17b75eeee9de388f51ef821ed30f15.exe" | C:\Users\admin\AppData\Local\Temp\3f17b75eeee9de388f51ef821ed30f15.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2572 | sc start cuifczot | C:\Windows\system32\sc.exe | 3f17b75eeee9de388f51ef821ed30f15.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2936 | sc create cuifczot binPath= "C:\Windows\system32\cuifczot\offgduqm.exe /d\"C:\Users\admin\AppData\Local\Temp\3f17b75eeee9de388f51ef821ed30f15.exe\"" type= own start= auto DisplayName= "wifi support" | C:\Windows\system32\sc.exe | 3f17b75eeee9de388f51ef821ed30f15.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3708 | cmd /C mkdir C:\Windows\system32\cuifczot\ | C:\Windows\system32\cmd.exe | 3f17b75eeee9de388f51ef821ed30f15.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 178
Read events
1 104
Write events
74
Delete events
0
Modification events
| (PID) Process: | (1756) 3f17b75eeee9de388f51ef821ed30f15.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1756) 3f17b75eeee9de388f51ef821ed30f15.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1756) 3f17b75eeee9de388f51ef821ed30f15.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1756) 3f17b75eeee9de388f51ef821ed30f15.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1660) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1660) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (1660) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (1660) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (1660) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (1660) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
Executable files
2
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3816 | cmd.exe | C:\Windows\System32\cuifczot\offgduqm.exe | executable | |
MD5:— | SHA256:— | |||
| 1596 | svchost.exe | C:\Windows\system32\config\systemprofile:.repos | binary | |
MD5:— | SHA256:— | |||
| 1756 | 3f17b75eeee9de388f51ef821ed30f15.exe | C:\Users\admin\AppData\Local\Temp\offgduqm.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
19
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 142.250.186.164:80 | http://www.google.com/ | US | html | 2.24 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1596 | svchost.exe | 20.112.52.29:80 | microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | malicious |
1596 | svchost.exe | 67.195.228.106:25 | mta6.am0.yahoodns.net | YAHOO-GQ1 | US | unknown |
1596 | svchost.exe | 185.246.220.218:443 | patmushta.info | Delis LLC | BG | unknown |
1596 | svchost.exe | 94.100.180.31:25 | mxs.mail.ru | LLC VK | RU | unknown |
1596 | svchost.exe | 64.233.184.26:25 | smtp.google.com | GOOGLE | US | whitelisted |
3828 | svchost.exe | 213.91.128.133:10060 | fastpool.xyz | Vivacom | BG | malicious |
1596 | svchost.exe | 176.113.115.158:487 | — | Red Bytes LLC | RU | unknown |
1596 | svchost.exe | 176.113.115.155:423 | — | Red Bytes LLC | RU | suspicious |
1596 | svchost.exe | 176.113.115.157:423 | — | Red Bytes LLC | RU | unknown |
1596 | svchost.exe | 176.113.115.156:423 | — | Red Bytes LLC | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
microsoft.com |
| whitelisted |
patmushta.info |
| malicious |
microsoft-com.mail.protection.outlook.com |
| whitelisted |
yahoo.com |
| whitelisted |
mta6.am0.yahoodns.net |
| whitelisted |
dns.msftncsi.com |
| shared |
google.com |
| malicious |
smtp.google.com |
| whitelisted |
mail.ru |
| whitelisted |
mxs.mail.ru |
| shared |