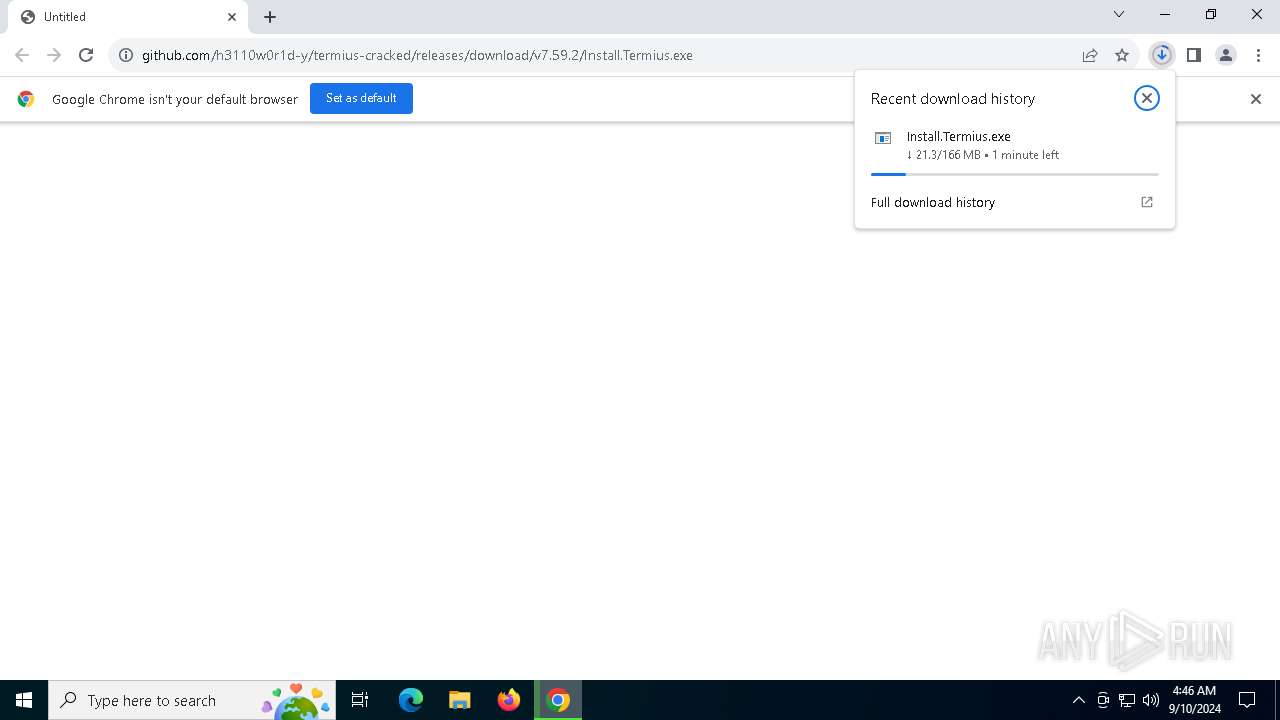
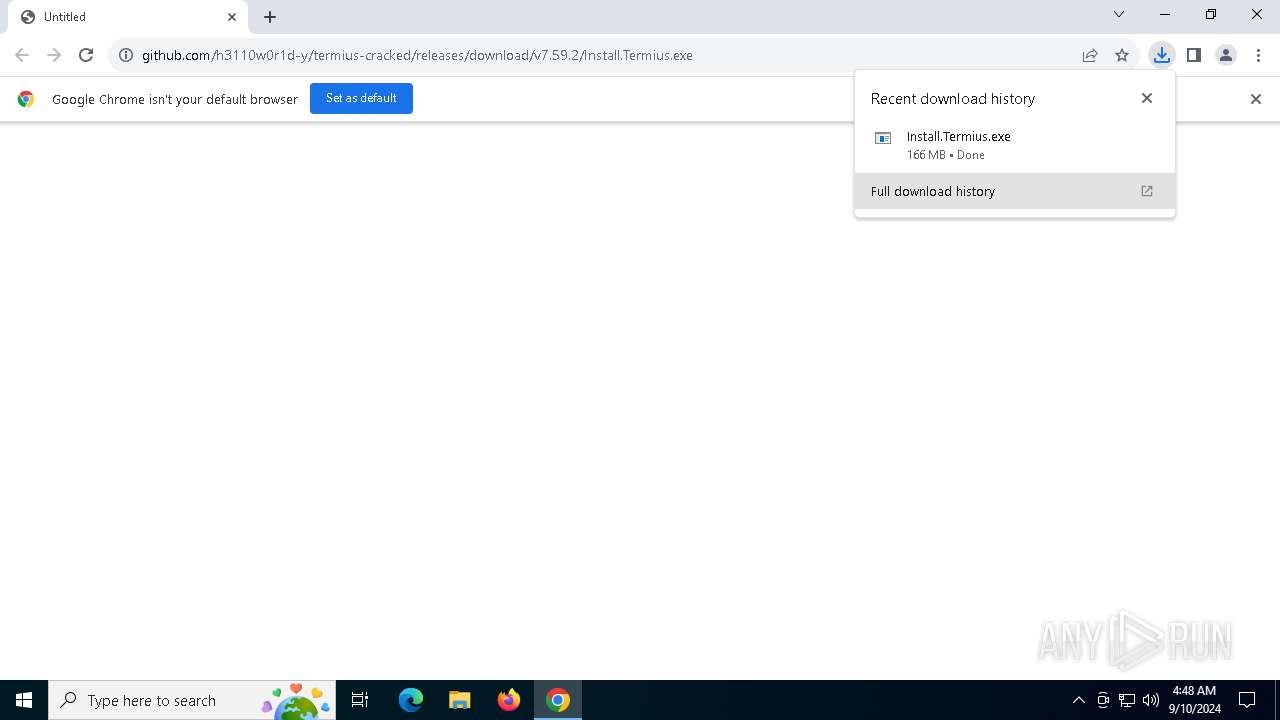
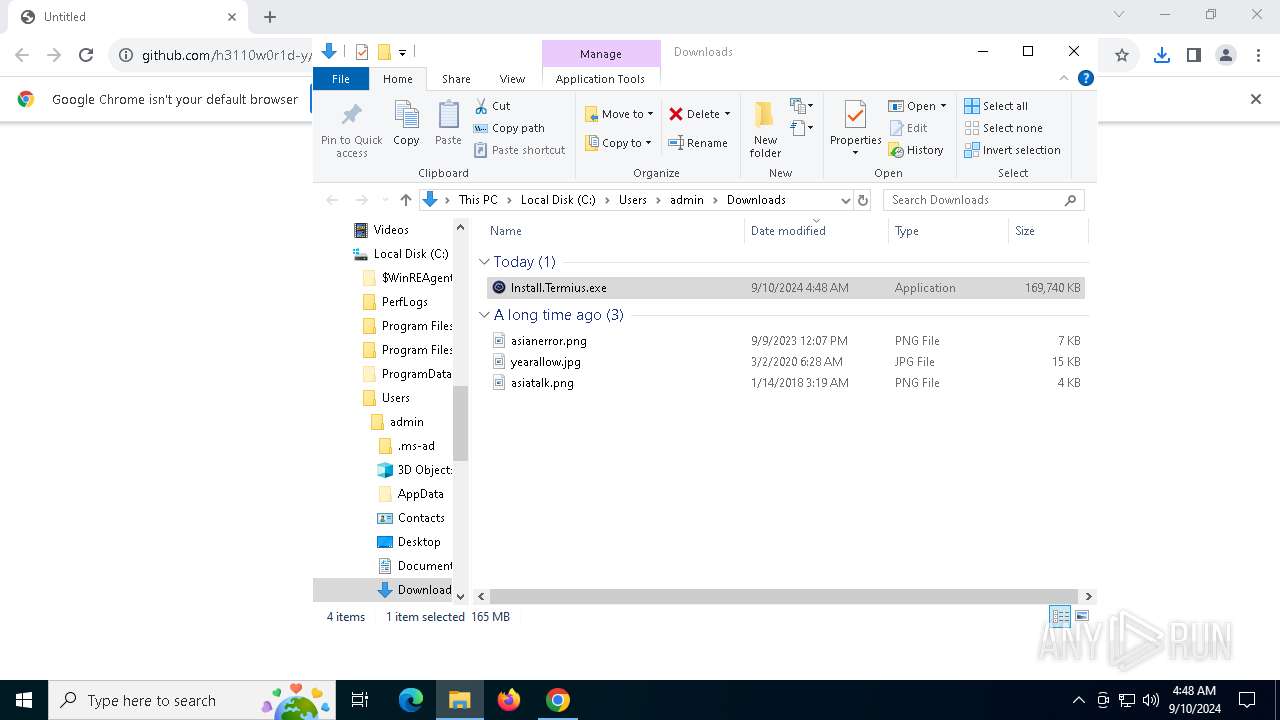
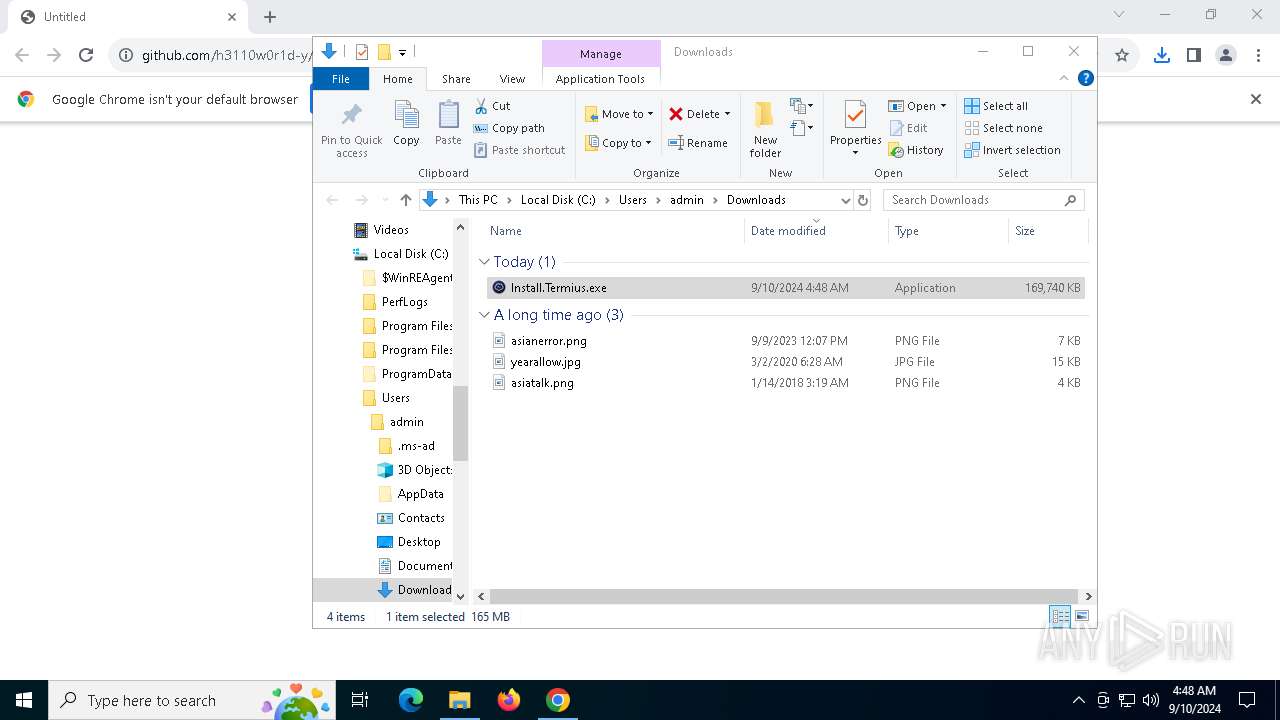
| URL: | https://github.com/h3110w0r1d-y/termius-cracked/releases/download/v7.59.2/Install.Termius.exe |
| Full analysis: | https://app.any.run/tasks/768feb03-5349-4491-a84f-5dd4b5427c2f |
| Verdict: | Malicious activity |
| Analysis date: | September 10, 2024, 04:46:21 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 095B9017887F20A81D5DAB71DA1BC2FC |
| SHA1: | DB6B3F9B1572E8A0AF74ACDAD7531F64F4296E22 |
| SHA256: | 4F8F86E623984D52844A08AEB7C2CECB942F6F263473518CCBE7B8CF4B7970AA |
| SSDEEP: | 3:N8tEd9WyVXYIcF/vOk52kCUJeYGXIMD0C:2uCGXYhlWJ++IMQC |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates file in the systems drive root
- explorer.exe (PID: 4552)
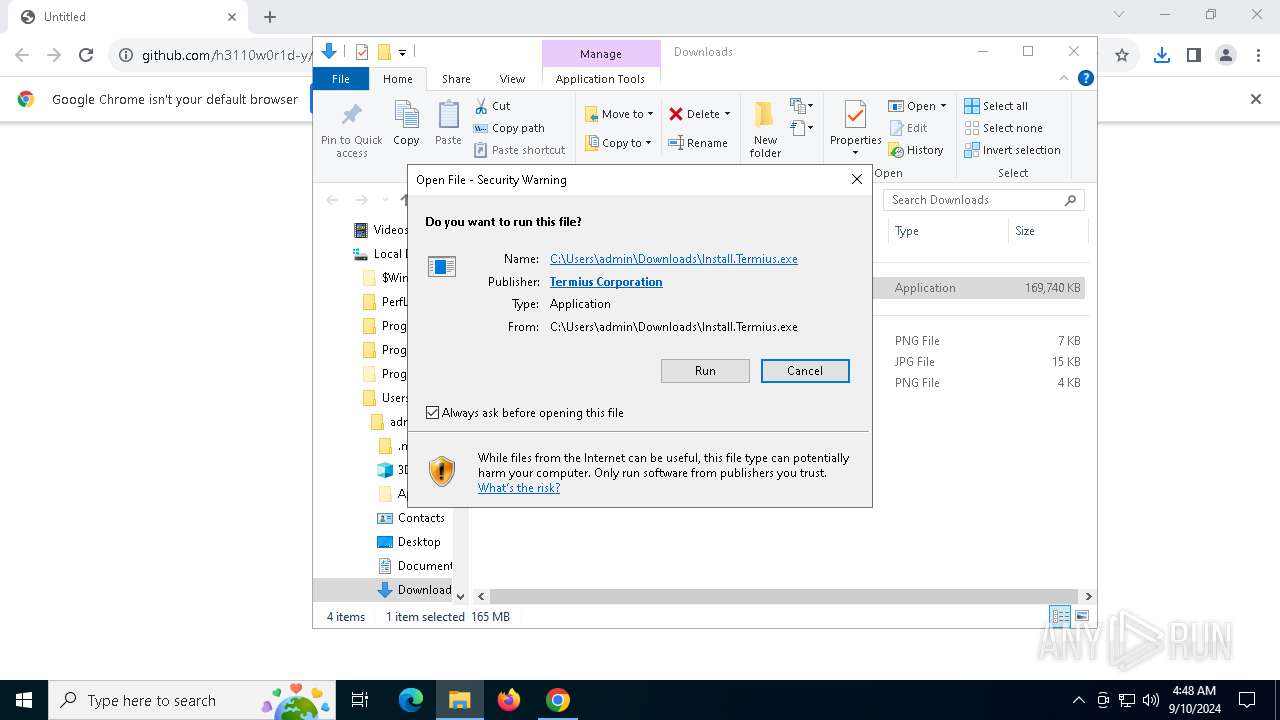
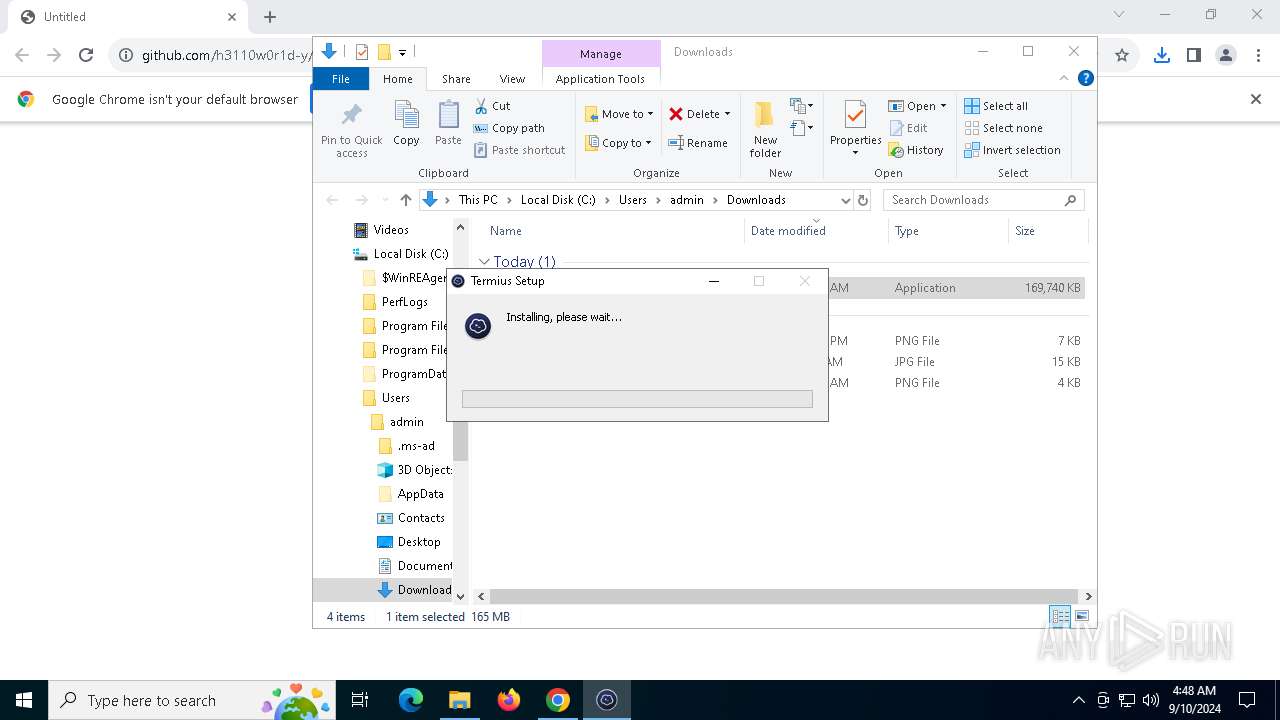
The process creates files with name similar to system file names
- Install.Termius.exe (PID: 4080)
Executable content was dropped or overwritten
- Install.Termius.exe (PID: 4080)
Malware-specific behavior (creating "System.dll" in Temp)
- Install.Termius.exe (PID: 4080)
Starts CMD.EXE for commands execution
- Install.Termius.exe (PID: 4080)
Get information on the list of running processes
- cmd.exe (PID: 3896)
- Install.Termius.exe (PID: 4080)
Drops 7-zip archiver for unpacking
- Install.Termius.exe (PID: 4080)
Process drops legitimate windows executable
- Install.Termius.exe (PID: 4080)
Creates a software uninstall entry
- Install.Termius.exe (PID: 4080)
Reads security settings of Internet Explorer
- Install.Termius.exe (PID: 4080)
- Termius.exe (PID: 5920)
Application launched itself
- Termius.exe (PID: 5920)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 6152)
Reads the software policy settings
- slui.exe (PID: 2684)
- explorer.exe (PID: 4552)
- Termius.exe (PID: 5920)
Application launched itself
- chrome.exe (PID: 6152)
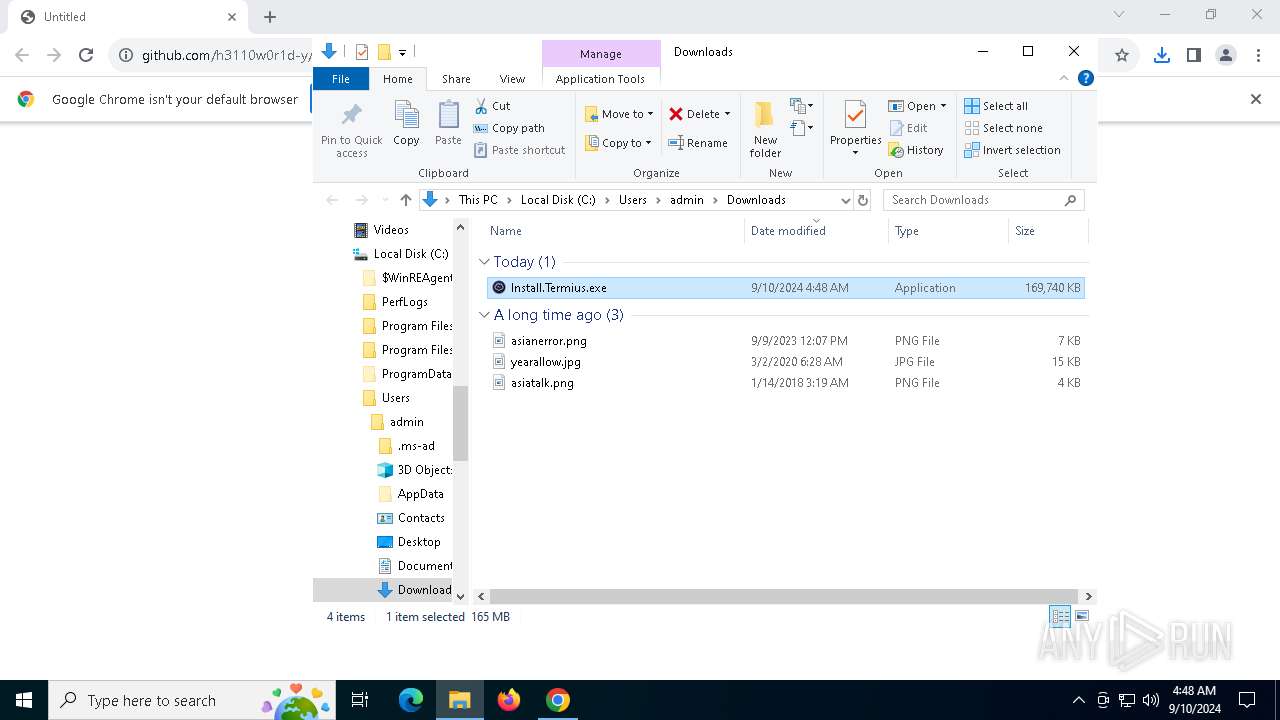
The process uses the downloaded file
- chrome.exe (PID: 2108)
- explorer.exe (PID: 4552)
- Install.Termius.exe (PID: 4080)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4552)
Checks proxy server information
- explorer.exe (PID: 4552)
- Termius.exe (PID: 5920)
Creates files or folders in the user directory
- explorer.exe (PID: 4552)
- Install.Termius.exe (PID: 4080)
- Termius.exe (PID: 3648)
- Termius.exe (PID: 5920)
- Termius.exe (PID: 736)
Checks supported languages
- Install.Termius.exe (PID: 4080)
- Termius.exe (PID: 5920)
- Termius.exe (PID: 3648)
- Termius.exe (PID: 4088)
- Termius.exe (PID: 736)
- Termius.exe (PID: 1060)
- Termius.exe (PID: 6212)
- Termius.exe (PID: 3424)
- Termius.exe (PID: 7204)
- Termius.exe (PID: 7216)
- Termius.exe (PID: 7392)
Create files in a temporary directory
- Install.Termius.exe (PID: 4080)
- Termius.exe (PID: 5920)
Reads the computer name
- Termius.exe (PID: 5920)
- Termius.exe (PID: 4088)
- Install.Termius.exe (PID: 4080)
- Termius.exe (PID: 736)
- Termius.exe (PID: 1060)
- Termius.exe (PID: 6212)
Reads Environment values
- Termius.exe (PID: 5920)
- Termius.exe (PID: 3424)
- Termius.exe (PID: 1060)
- Termius.exe (PID: 6212)
Reads product name
- Termius.exe (PID: 5920)
- Termius.exe (PID: 3424)
- Termius.exe (PID: 1060)
- Termius.exe (PID: 6212)
Process checks computer location settings
- Termius.exe (PID: 1060)
- Termius.exe (PID: 5920)
- Termius.exe (PID: 3424)
- Termius.exe (PID: 6212)
- Termius.exe (PID: 7392)
- Termius.exe (PID: 7216)
Reads the machine GUID from the registry
- Termius.exe (PID: 5920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
170
Monitored processes
33
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 736 | "C:\Users\admin\AppData\Local\Programs\Termius\Termius.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\Termius" --mojo-platform-channel-handle=2524 --field-trial-handle=1892,i,15147675837387517009,11249260504417802484,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Local\Programs\Termius\Termius.exe | Termius.exe | ||||||||||||
User: admin Company: Termius Corporation Integrity Level: MEDIUM Description: Termius Version: 7.59.2 Modules
| |||||||||||||||
| 1060 | "C:\Users\admin\AppData\Local\Programs\Termius\Termius.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\Termius" --app-user-model-id=electron.app.Termius --app-path="C:\Users\admin\AppData\Local\Programs\Termius\resources\app.asar" --no-sandbox --no-zygote --first-renderer-process --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2688 --field-trial-handle=1892,i,15147675837387517009,11249260504417802484,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Local\Programs\Termius\Termius.exe | — | Termius.exe | |||||||||||
User: admin Company: Termius Corporation Integrity Level: MEDIUM Description: Termius Version: 7.59.2 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5352 --field-trial-handle=2044,i,7335702980558211769,6144328924064864284,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5264 --field-trial-handle=2044,i,7335702980558211769,6144328924064864284,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4964 --field-trial-handle=2044,i,7335702980558211769,6144328924064864284,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3048 --field-trial-handle=2044,i,7335702980558211769,6144328924064864284,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2684 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3112 | C:\WINDOWS\System32\find.exe "Termius.exe" | C:\Windows\SysWOW64\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3424 | "C:\Users\admin\AppData\Local\Programs\Termius\Termius.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\Termius" --app-user-model-id=electron.app.Termius --app-path="C:\Users\admin\AppData\Local\Programs\Termius\resources\app.asar" --no-sandbox --no-zygote --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2888 --field-trial-handle=1892,i,15147675837387517009,11249260504417802484,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Local\Programs\Termius\Termius.exe | — | Termius.exe | |||||||||||
User: admin Company: Termius Corporation Integrity Level: MEDIUM Description: Termius Version: 7.59.2 Modules
| |||||||||||||||
| 3648 | C:\Users\admin\AppData\Local\Programs\Termius\Termius.exe --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Roaming\Termius /prefetch:7 --no-rate-limit --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Roaming\Termius\Crashpad --url=https://o76327.ingest.sentry.io/api/193727/minidump/?sentry_key=55af16af94074b88844cd7e16f535fa5 --annotation=_productName=Termius --annotation=_version=7.59.2 --annotation=plat=Win64 --annotation=prod=Electron --annotation=ver=21.4.4 --initial-client-data=0x4a4,0x4a8,0x4ac,0x4a0,0x4b0,0x7ff6a72606e0,0x7ff6a72606f0,0x7ff6a7260700 | C:\Users\admin\AppData\Local\Programs\Termius\Termius.exe | — | Termius.exe | |||||||||||
User: admin Company: Termius Corporation Integrity Level: MEDIUM Description: Termius Version: 7.59.2 Modules
| |||||||||||||||
Total events
41 297
Read events
41 160
Write events
110
Delete events
27
Modification events
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000702E8 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456033BCEE44DE41B4E8AEC331E84F566D2 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppBadgeUpdated |
| Operation: | write | Name: | Chrome |
Value: 5 | |||
| (PID) Process: | (6152) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6152) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6152) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6152) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6152) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppSwitched |
| Operation: | write | Name: | Chrome |
Value: 1 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | write | Name: | TraySearchBoxVisible |
Value: 1 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | write | Name: | TraySearchBoxVisibleOnAnyMonitor |
Value: 1 | |||
Executable files
58
Suspicious files
335
Text files
47
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF12afd0.TMP | — | |
MD5:— | SHA256:— | |||
| 6152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF12afdf.TMP | — | |
MD5:— | SHA256:— | |||
| 6152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 6152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF12b0d9.TMP | text | |
MD5:4320BE33704F77FF4DF4921358D2C50C | SHA256:8FDF7387C47EB272670EFF935D71492F03EAFAA55A8B22C05658BB0F1AC472EE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
71
DNS requests
43
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6364 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1932 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acottdsr4k6pgibdknx33vj64oxa_20240823.667410168.14/obedbbhbpmojnkanicioggnmelmoomoc_20240823.667410168.14_all_ENUS500000_ad46kswvnnyj2osjjnryykc7cc7q.crx3 | unknown | — | — | whitelisted |
2768 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acottdsr4k6pgibdknx33vj64oxa_20240823.667410168.14/obedbbhbpmojnkanicioggnmelmoomoc_20240823.667410168.14_all_ENUS500000_ad46kswvnnyj2osjjnryykc7cc7q.crx3 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acottdsr4k6pgibdknx33vj64oxa_20240823.667410168.14/obedbbhbpmojnkanicioggnmelmoomoc_20240823.667410168.14_all_ENUS500000_ad46kswvnnyj2osjjnryykc7cc7q.crx3 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acottdsr4k6pgibdknx33vj64oxa_20240823.667410168.14/obedbbhbpmojnkanicioggnmelmoomoc_20240823.667410168.14_all_ENUS500000_ad46kswvnnyj2osjjnryykc7cc7q.crx3 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acottdsr4k6pgibdknx33vj64oxa_20240823.667410168.14/obedbbhbpmojnkanicioggnmelmoomoc_20240823.667410168.14_all_ENUS500000_ad46kswvnnyj2osjjnryykc7cc7q.crx3 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acottdsr4k6pgibdknx33vj64oxa_20240823.667410168.14/obedbbhbpmojnkanicioggnmelmoomoc_20240823.667410168.14_all_ENUS500000_ad46kswvnnyj2osjjnryykc7cc7q.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6364 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6416 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6884 | chrome.exe | 140.82.121.3:443 | github.com | GITHUB | US | shared |
6152 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6884 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6884 | chrome.exe | 185.199.111.133:443 | objects.githubusercontent.com | FASTLY | US | shared |
6152 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
6364 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| shared |
accounts.google.com |
| whitelisted |
objects.githubusercontent.com |
| shared |
www.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |