| File name: | 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop |
| Full analysis: | https://app.any.run/tasks/898d08fd-725d-472c-937b-6ea0fefab23c |
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2025, 02:33:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 4637DAAA37D9D3C70192A77D58989FF3 |
| SHA1: | B4D063E937A330D29D2843F81ABF9016A8E742BA |
| SHA256: | 4F85987BED604A4668F33A541BD26E39C4F15AD5AB6752FB2EFDC322375CF5D4 |
| SSDEEP: | 98304:eqLhckVIV3bj9ZUoRcgpLRcgqgptghfSqm4V45+Sl3bj9Z: |
MALICIOUS
Changes the autorun value in the registry
- 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe (PID: 7080)
SUSPICIOUS
Executable content was dropped or overwritten
- 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe (PID: 7080)
There is functionality for taking screenshot (YARA)
- 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe (PID: 7080)
Reads security settings of Internet Explorer
- 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe (PID: 7080)
Starts CMD.EXE for commands execution
- 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe (PID: 7080)
INFO
The sample compiled with english language support
- 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe (PID: 7080)
Checks supported languages
- 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe (PID: 7080)
Reads the computer name
- 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe (PID: 7080)
Create files in a temporary directory
- 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe (PID: 7080)
Failed to create an executable file in Windows directory
- 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe (PID: 7080)
Checks proxy server information
- slui.exe (PID: 684)
- 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe (PID: 7080)
Reads the software policy settings
- slui.exe (PID: 684)
Launching a file from a Registry key
- 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe (PID: 7080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (46.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (29.9) |
| .scr | | | Windows screen saver (14.1) |
| .exe | | | Win32 Executable (generic) (4.8) |
| .exe | | | Generic Win/DOS Executable (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:11:25 09:21:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 414208 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x53e3d |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | 3 |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Total processes
139
Monitored processes
8
Malicious processes
1
Suspicious processes
0
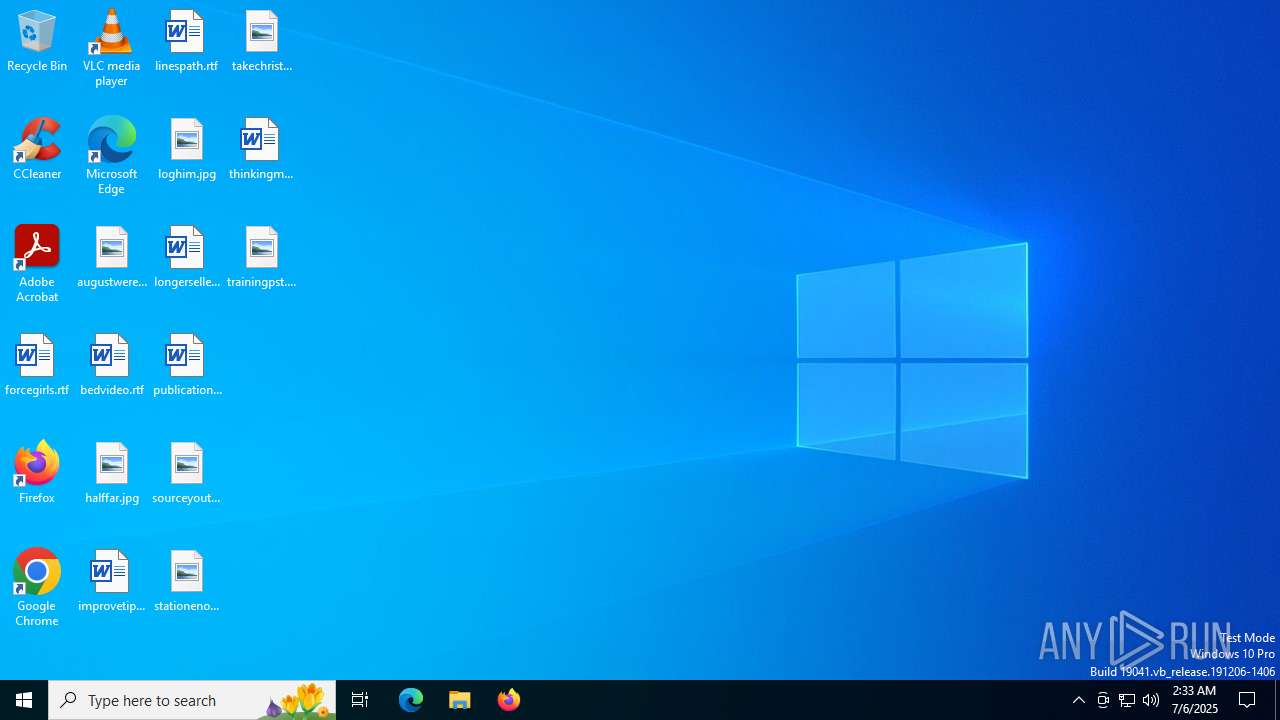
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 984 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1732 | C:\WINDOWS\system32\cmd.exe /C AT /delete /yes | C:\Windows\SysWOW64\cmd.exe | — | 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | AT 09:00 /interactive /EVERY:m,t,w,th,f,s,su C:\WINDOWS\system32\winhelp.exe | C:\Windows\SysWOW64\at.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Schedule service command line interface Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3704 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5496 | AT /delete /yes | C:\Windows\SysWOW64\at.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Schedule service command line interface Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7080 | "C:\Users\admin\Desktop\2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe" | C:\Users\admin\Desktop\2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7160 | C:\WINDOWS\system32\cmd.exe /C AT 09:00 /interactive /EVERY:m,t,w,th,f,s,su C:\WINDOWS\system32\winhelp.exe | C:\Windows\SysWOW64\cmd.exe | — | 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 043
Read events
4 041
Write events
2
Delete events
0
Modification events
| (PID) Process: | (7080) 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Yahoo Messengger |
Value: C:\WINDOWS\system32\regsvr.exe | |||
| (PID) Process: | (7080) 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\WorkgroupCrawler\Shares |
| Operation: | write | Name: | shared |
Value: \New Folder.exe | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7080 | 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | C:\Users\admin\AppData\Local\Temp\aut64B5.tmp | binary | |
MD5:95A563C56954CB237B0A2C754AE3CDC4 | SHA256:D3BDCF4FA517D471457F1679256BB4DE73E5A86857C64D2BFDA93FDE11D7C318 | |||
| 7080 | 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | C:\Users\admin\AppData\Local\Temp\aut64B6.tmp | executable | |
MD5:6FDEAC9EA041AFC28242533D8BB8A291 | SHA256:8E1B0FE0A291A0F2EAE532740100EF329E4AA1BDB353A77DF308E0B8212830C0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
25
DNS requests
8
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7064 | RUXIMICS.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
7064 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
7080 | 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | GET | — | 45.63.71.7:80 | http://www.crackspider.net/setting.doc | US | — | — | malicious |
7080 | 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | GET | — | 45.63.71.7:80 | http://www.crackspider.net/setting.xls | US | — | — | malicious |
7080 | 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | GET | — | 45.63.71.7:80 | http://www.crackspider.net/setting.doc | US | — | — | malicious |
7080 | 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | GET | — | 45.63.71.7:80 | http://www.crackspider.net/setting.xls | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7064 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7064 | RUXIMICS.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7064 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.crackspider.net |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7080 | 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | A Network Trojan was detected | ET MALWARE Possible Worm W32.Svich or Other Infection Request for setting.doc |
7080 | 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | A Network Trojan was detected | ET MALWARE Possible Worm W32.Svich or Other Infection Request for setting.xls |
7080 | 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | A Network Trojan was detected | ET MALWARE Possible Worm W32.Svich or Other Infection Request for setting.doc |
7080 | 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | A Network Trojan was detected | ET MALWARE Possible Worm W32.Svich or Other Infection Request for setting.xls |
7080 | 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | A Network Trojan was detected | ET MALWARE Possible Worm W32.Svich or Other Infection Request for setting.xls |
7080 | 2025-07-06_4637daaa37d9d3c70192a77d58989ff3_elex_stop.exe | A Network Trojan was detected | ET MALWARE Possible Worm W32.Svich or Other Infection Request for setting.doc |