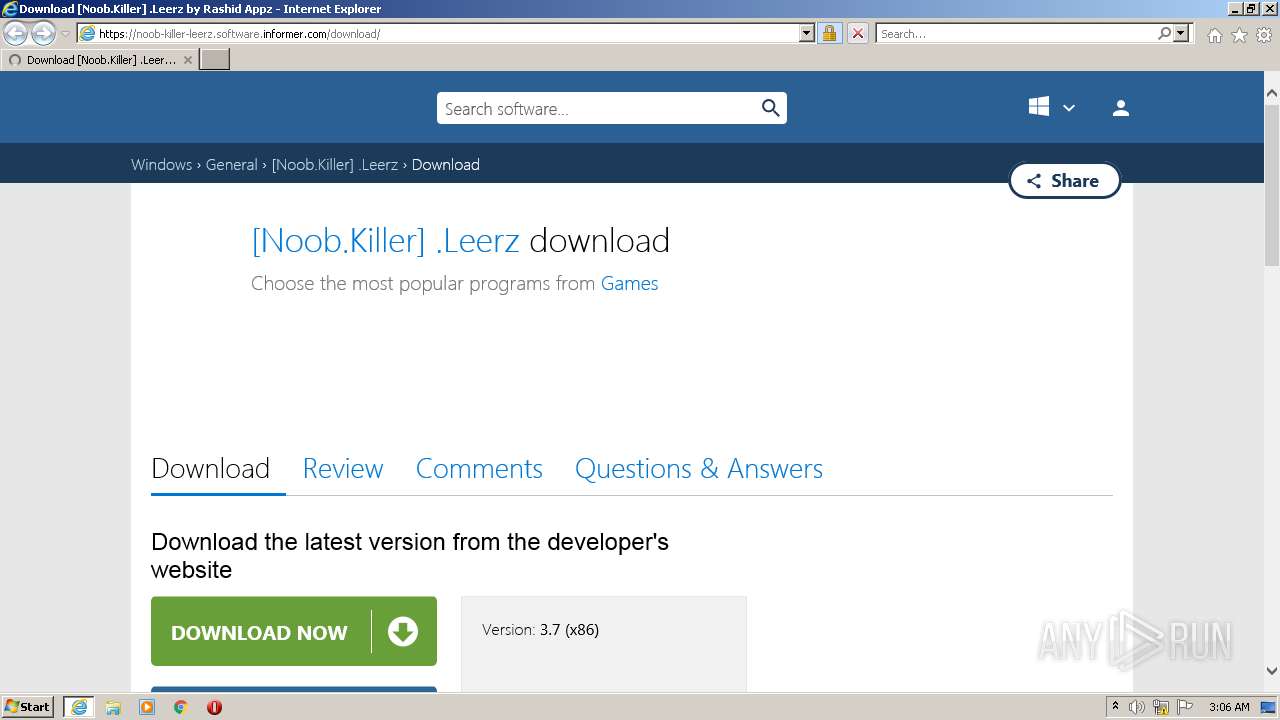
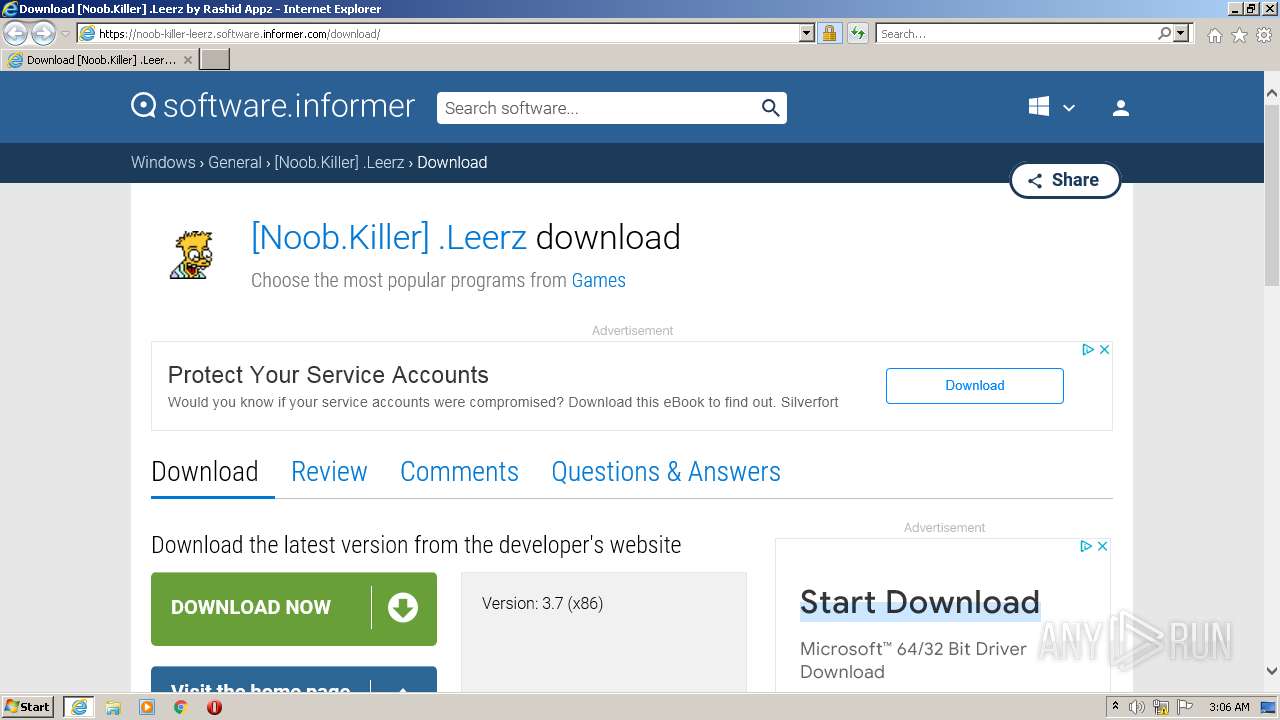
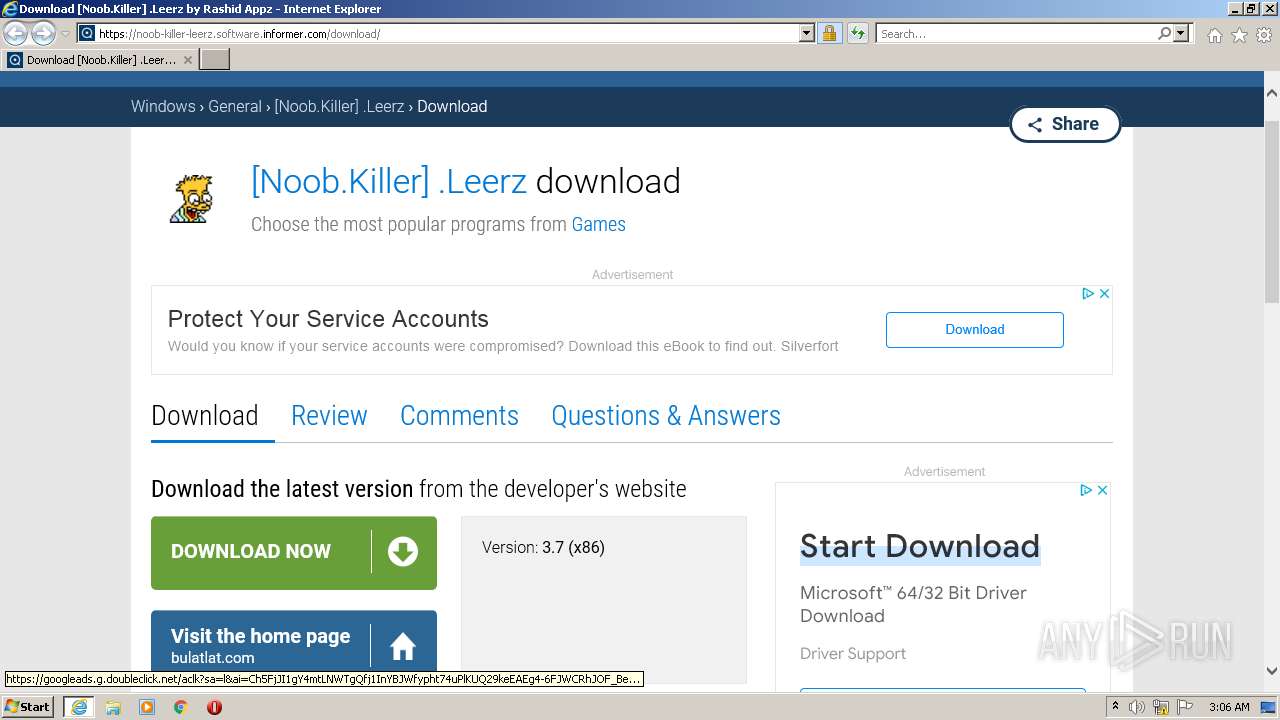
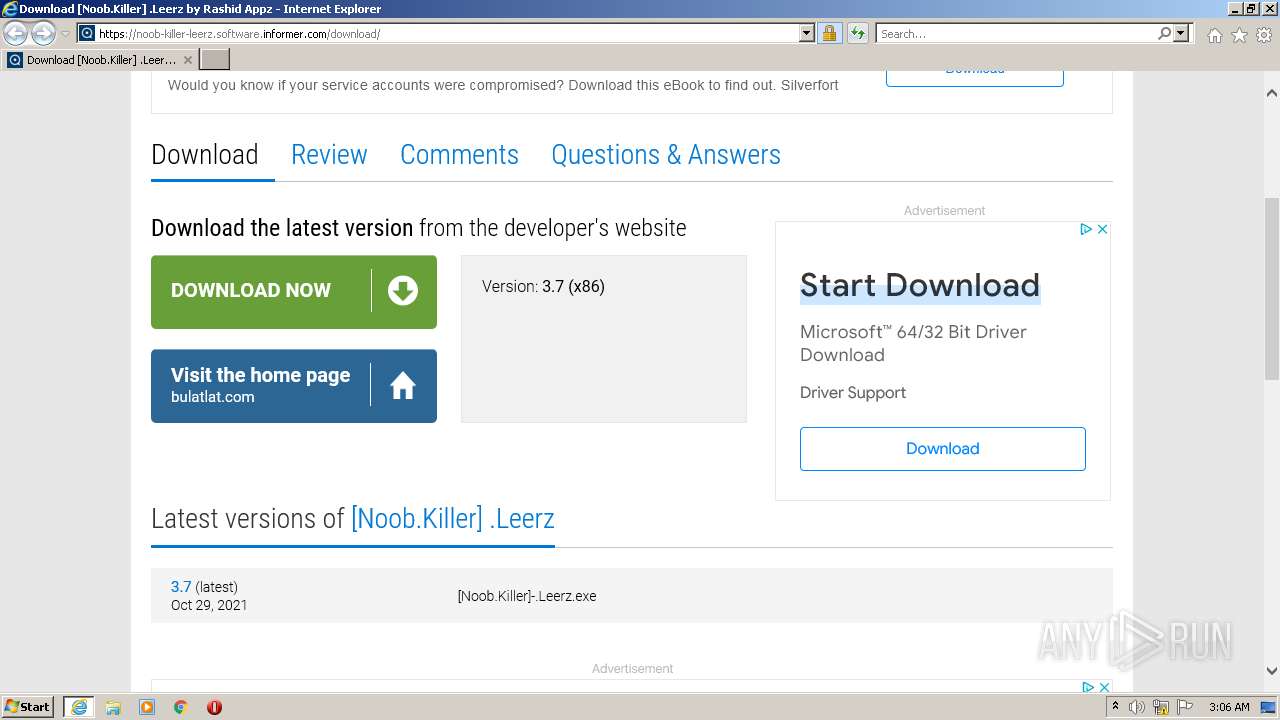
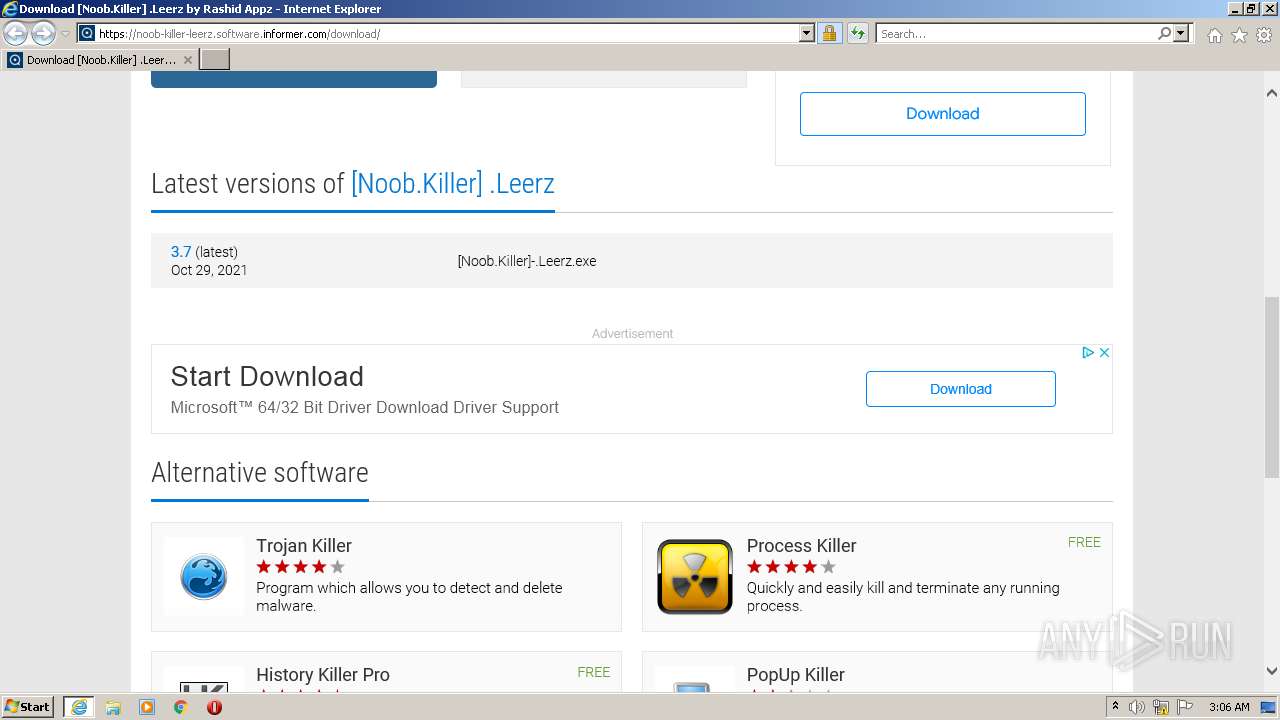
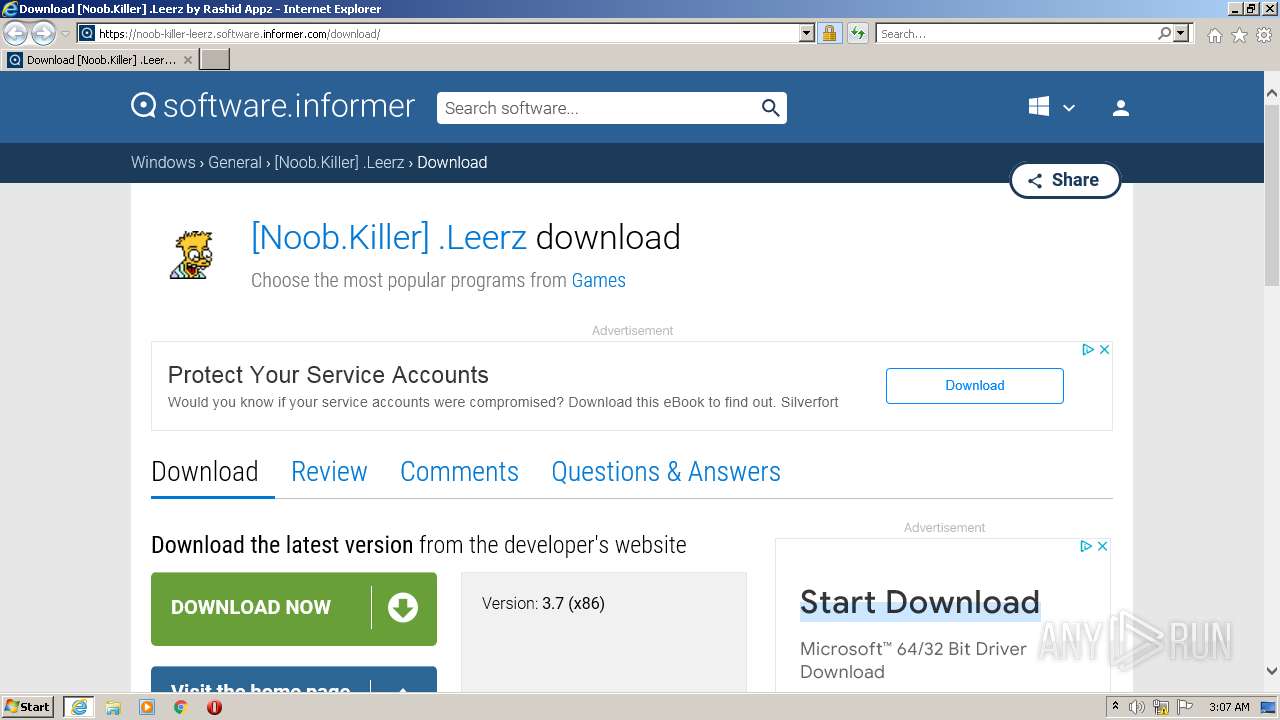
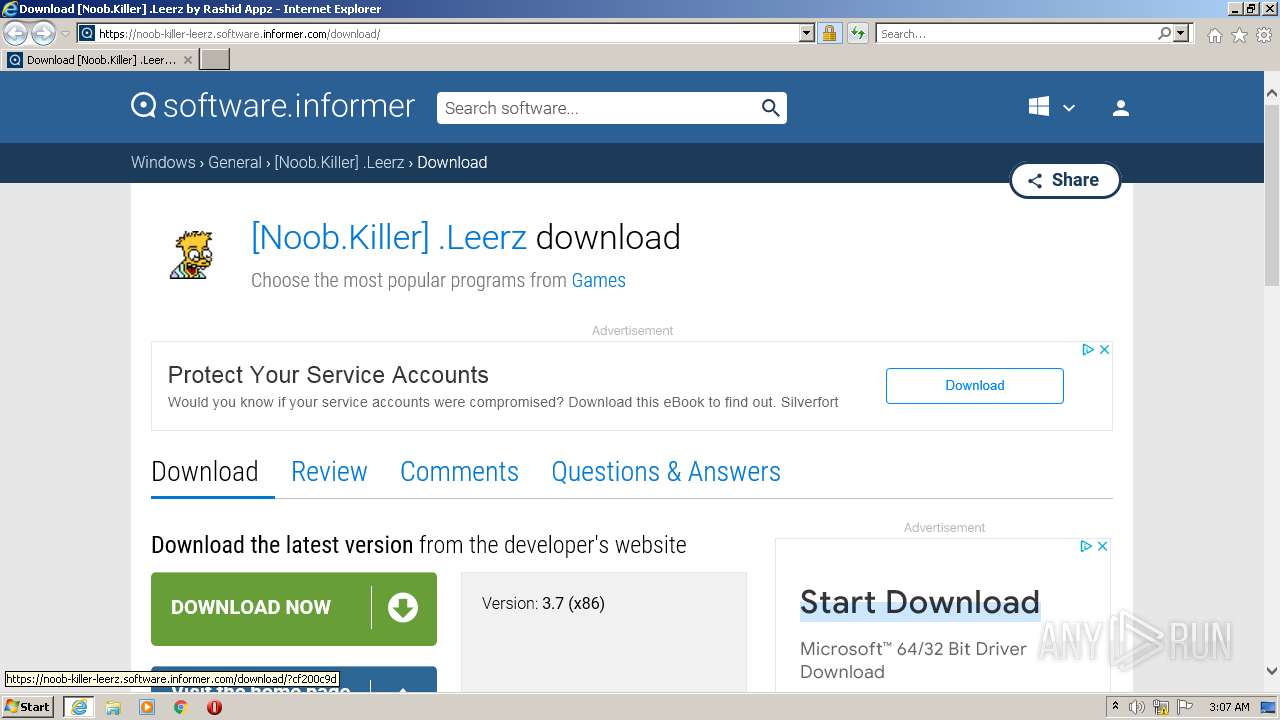
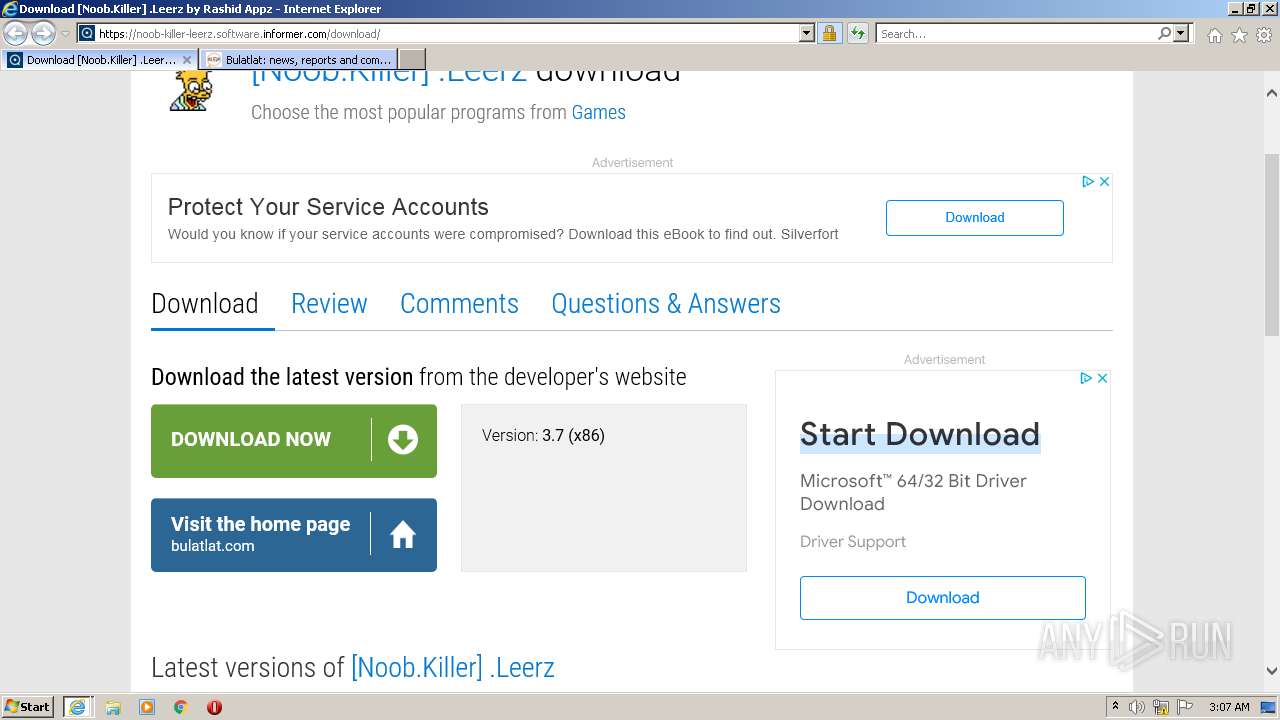
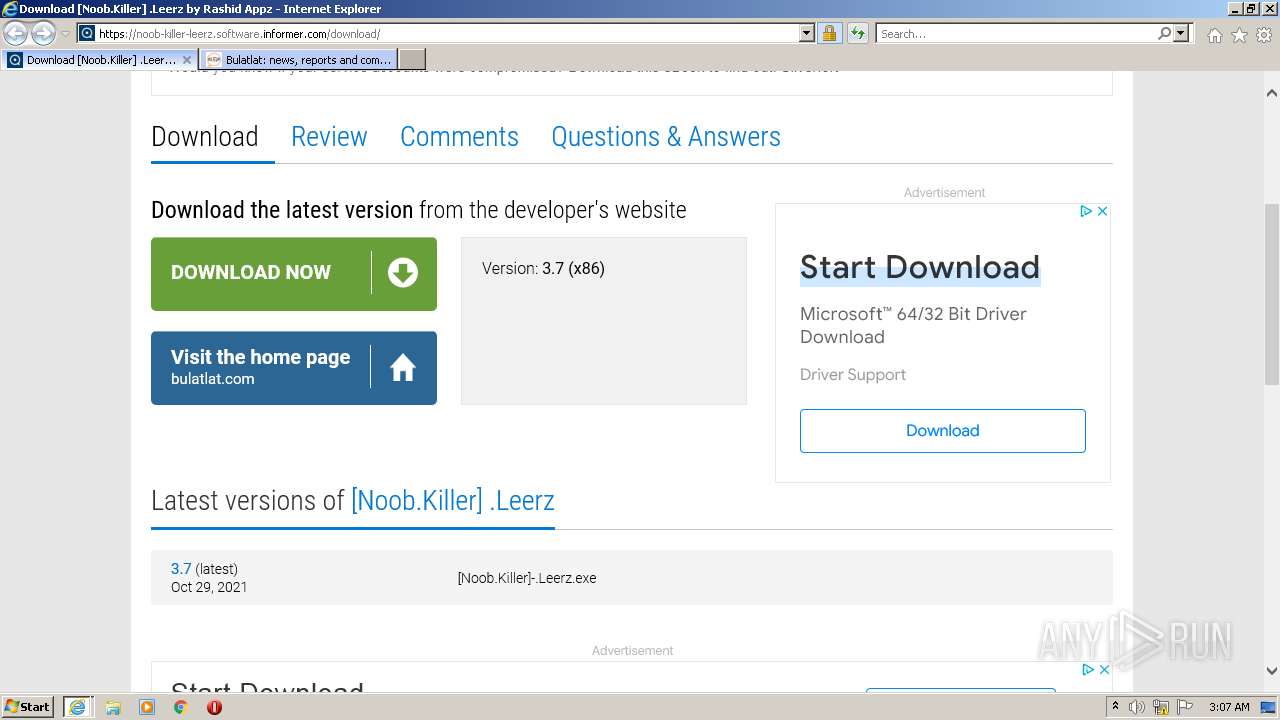
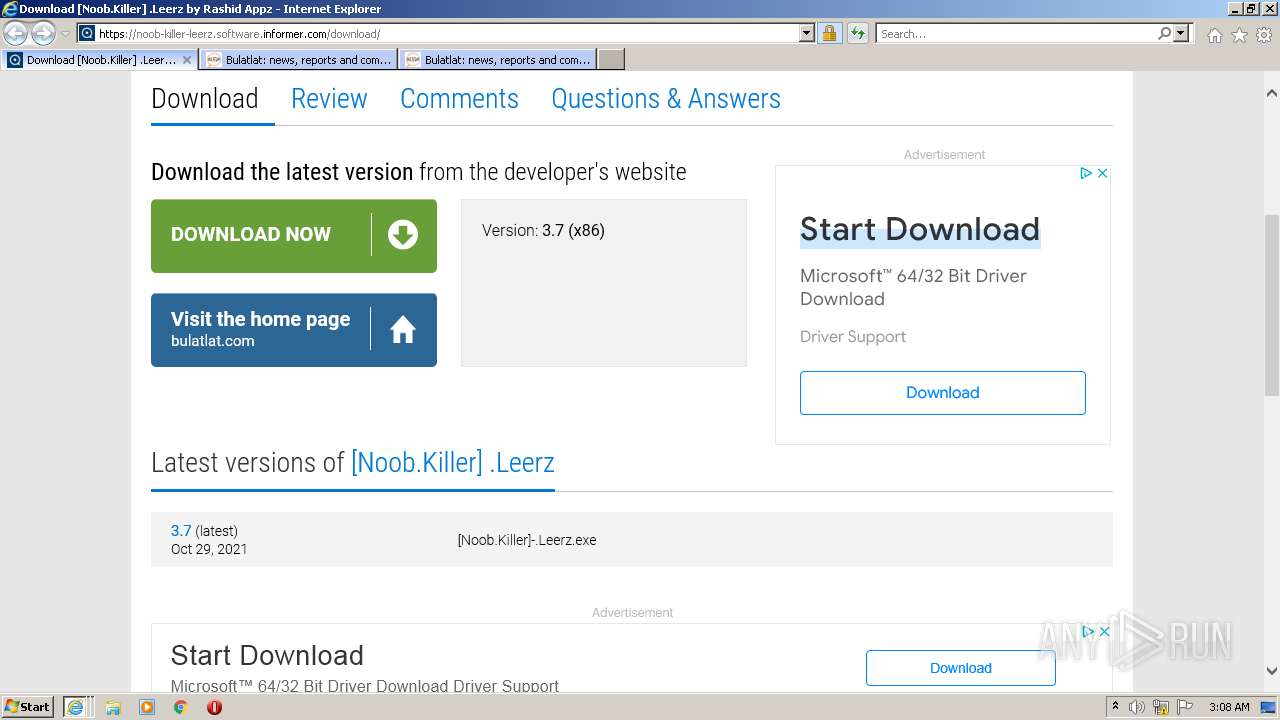
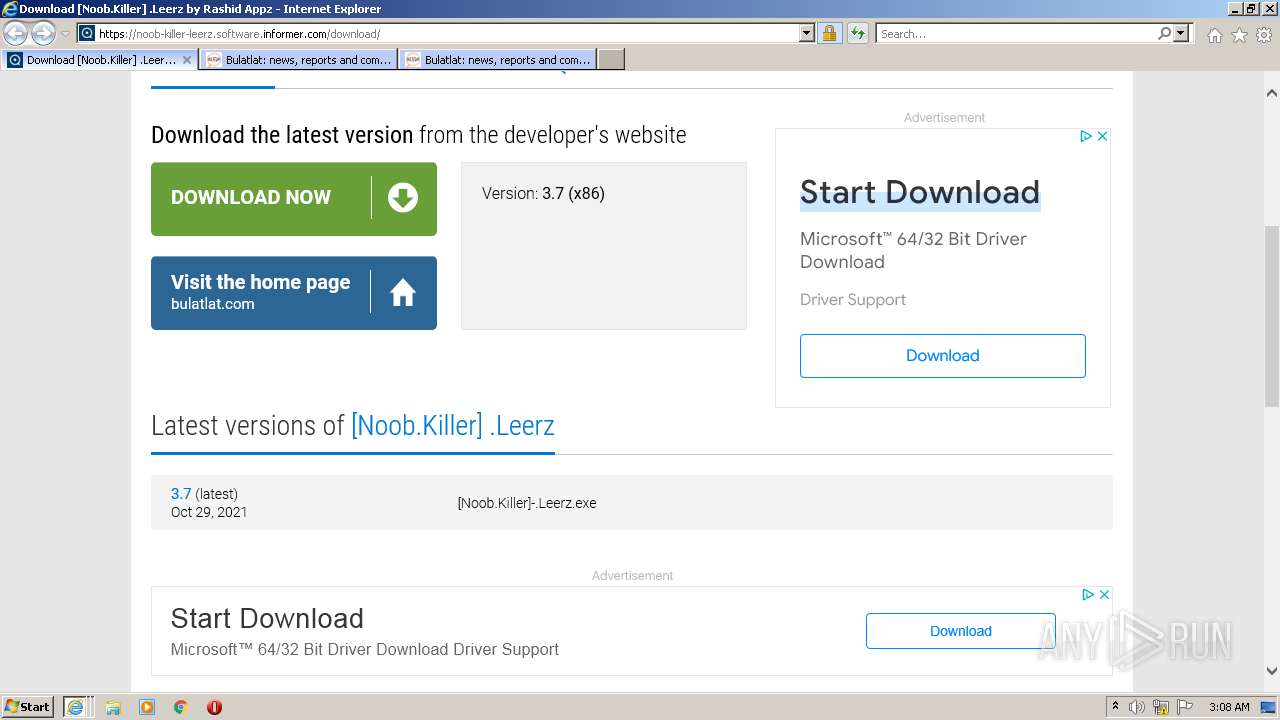
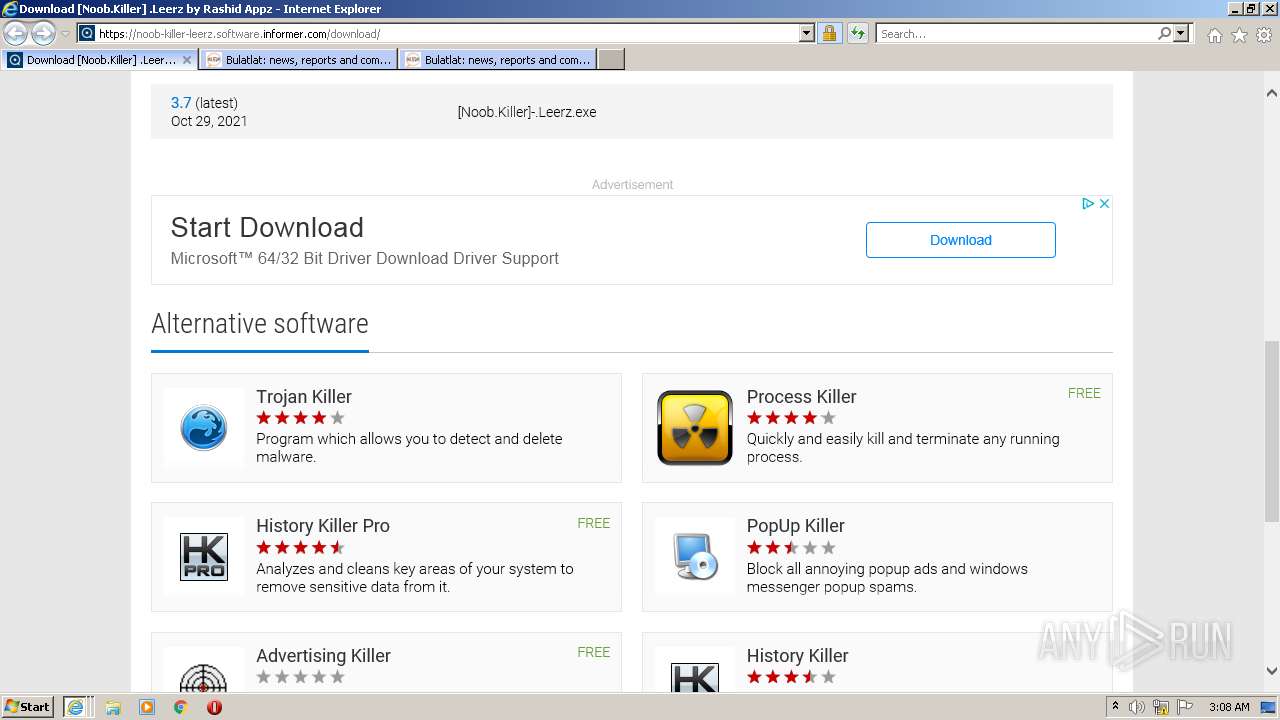
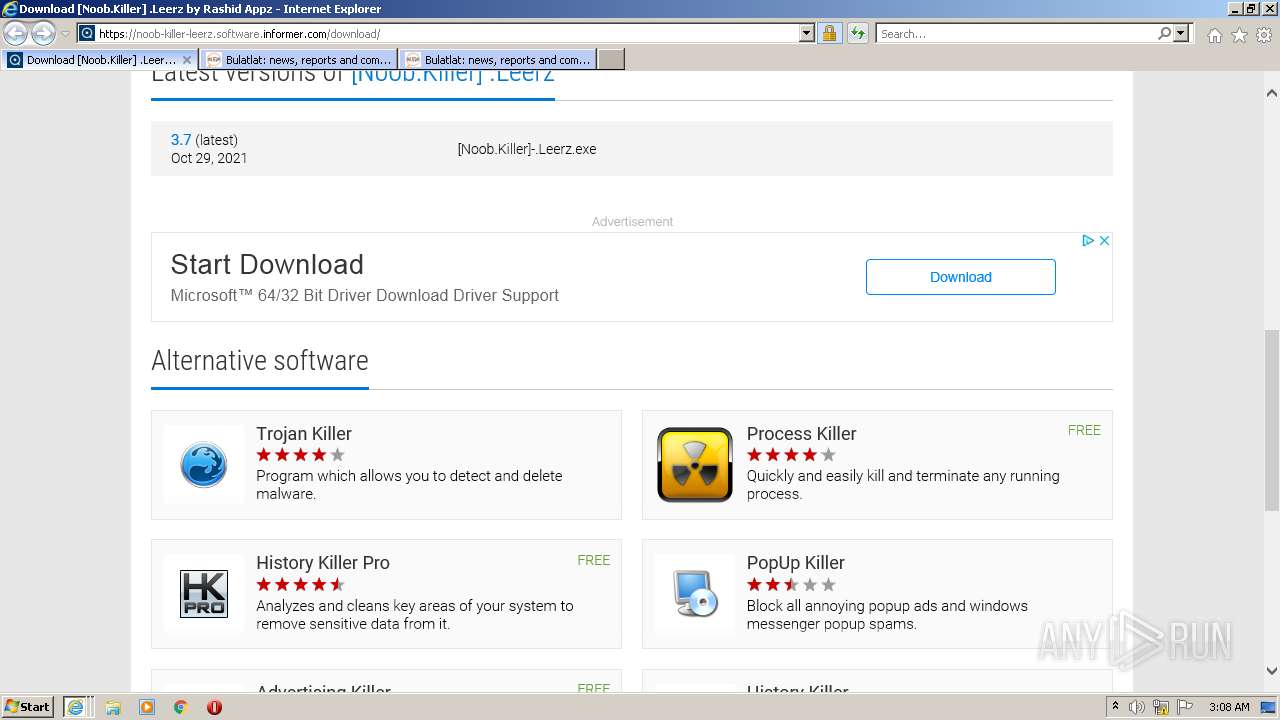
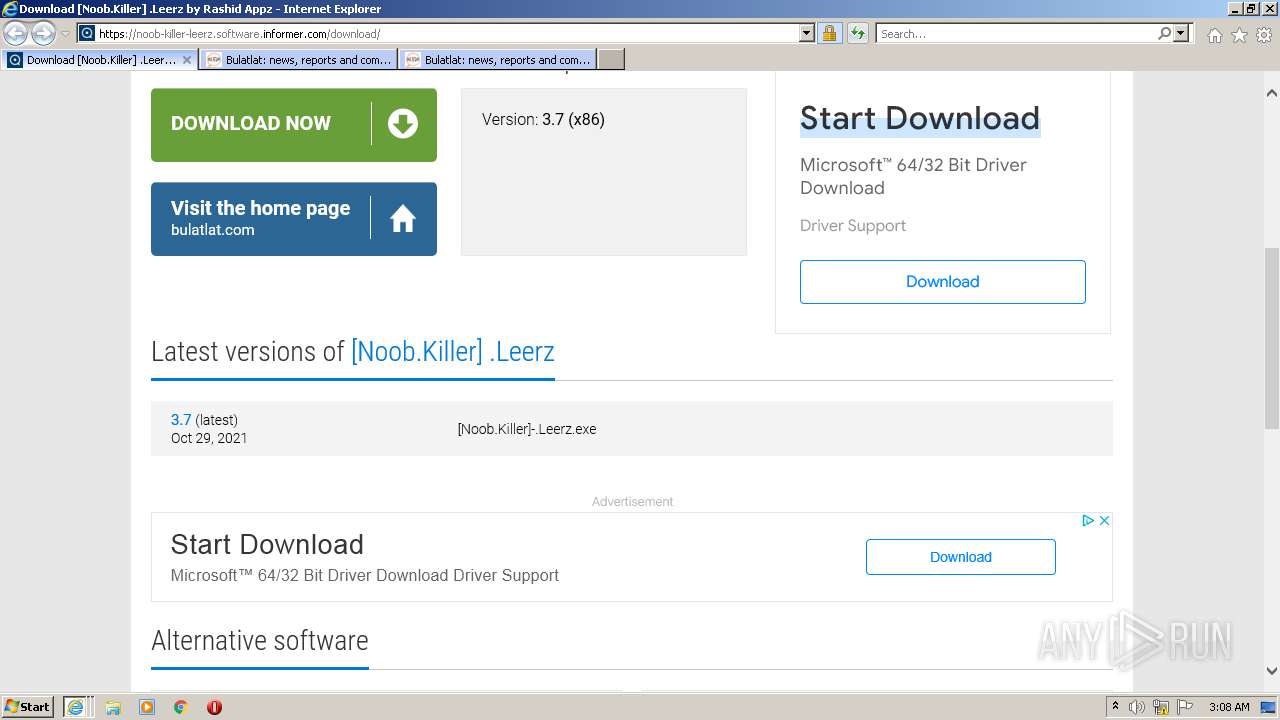
| URL: | https://noob-killer-leerz.software.informer.com/download/ |
| Full analysis: | https://app.any.run/tasks/7ac93479-13ed-45f4-877e-c5c21235ad59 |
| Verdict: | No threats detected |
| Analysis date: | November 01, 2022, 03:05:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 785907976F37227A7F80750CC96E14C9 |
| SHA1: | ECBDF8FF71CEF9C7EAE2F0324163E041ED05EFA2 |
| SHA256: | 4F838947C7D23CE6B8F893FB847B02AC190991A6FDB3CD7EDDE59A377E694F9E |
| SSDEEP: | 3:N8vgHAkTR3j4mLn:2oHAMR30mL |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3052 CREDAT:3413274 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3052 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3052 CREDAT:2954516 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3052 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://noob-killer-leerz.software.informer.com/download/" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3492 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3052 CREDAT:2561304 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
41 753
Read events
41 404
Write events
343
Delete events
6
Modification events
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30993822 | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30993822 | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
52
Text files
227
Unknown types
56
Dropped files
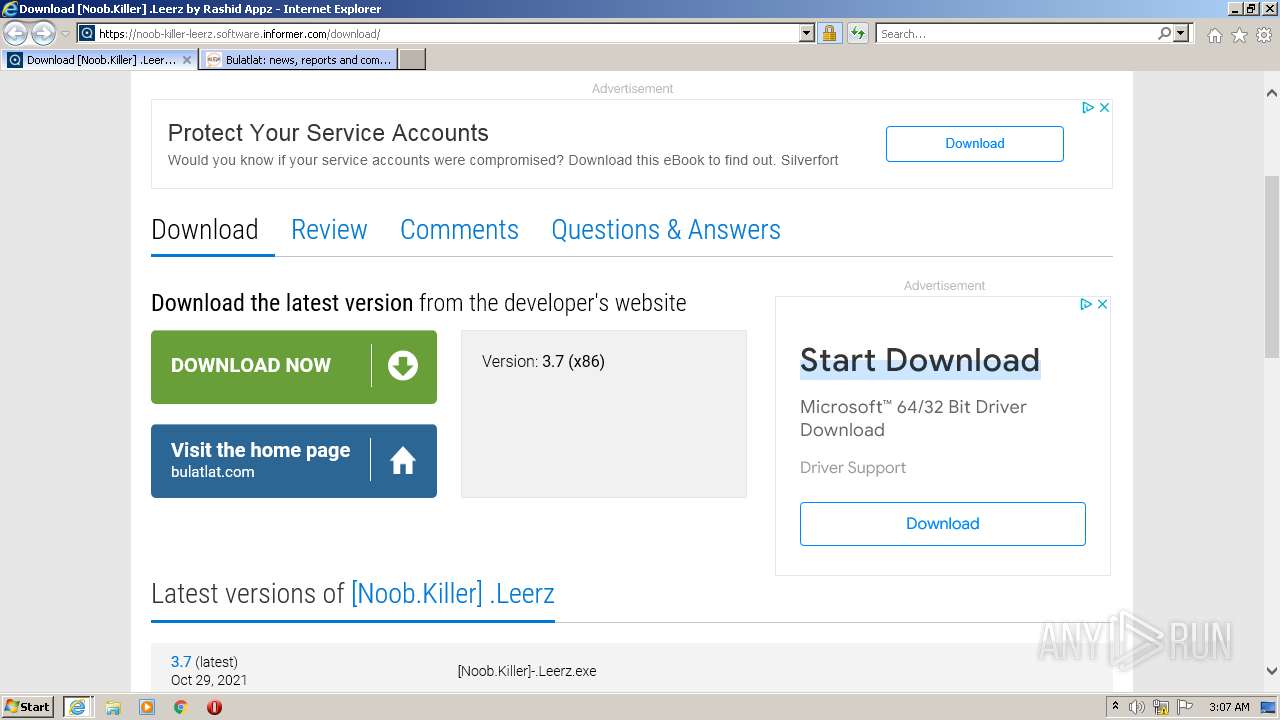
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2564 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7DDEB965A66AA4EB770E17C40767B418 | der | |
MD5:73E2990ABBE731253B63BCC91561B4BA | SHA256:5FC2352851853904642398C0ECFC713EF60F9E39E68C0A9C4482E6B4D2A226CD | |||
| 2564 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarAB64.tmp | cat | |
MD5:49BF6095F16B1924B2FCEF4AB961503B | SHA256:B305AA3836DF8734E2FC0C99664558A869C6AC9CB23DE24262FE34A3BF367DE7 | |||
| 2564 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\EHPLLYM8.txt | text | |
MD5:437B6398C0C4B0D100C41939BB83E3AF | SHA256:4638333E0EADD21FEAF44DE63BEA35DCBE76BDF9F4E09000D41BB5357E4BE055 | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:DC270B65961A5C197832B86153A5F5E5 | SHA256:3DAA66F7132532B1FA01F77BD4B88FEA21537F417968A8D604D5AD5768AB814D | |||
| 2564 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\G51B7AJI.txt | text | |
MD5:0E4E8D5D02F48ED3049B0DE5044928DD | SHA256:5A0C7FDD0432667BF74CF4A645A6D6500CB4CEC7C2342B9CC11572082143C8C7 | |||
| 2564 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:EFD322ECED2242C007C3F9745053E5F8 | SHA256:63BD3B5F83EF69C92E8C9202C9B55103FCAF0824B158C25B01784DE24AB75222 | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:0A252572B19C815ECFD75FFEC577EBEA | SHA256:A908428E25B4D120D6B36B700D1B82CF6E45DB0E9290362E71B467846B57B9EF | |||
| 2564 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:2CDF3BD3F4B345E364A84840A75A8267 | SHA256:BFEF36842BDA6B42F9C217FA536791898C94D964A0D89594EECA67250857DDF8 | |||
| 2564 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\download[1].htm | html | |
MD5:38A0DE4124D16356D5BF39DBF0EF34DD | SHA256:FA5B7081D77DD0DADAF5E106D7FEEDB7B34079C015C48A948F7BEDD913387980 | |||
| 2564 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:ADD29268A94FFB7D2315A52806A142BD | SHA256:35F863FEA4C896E6822BAF4039E38778F96BC7EC9DE47C7078307E8E94030EE7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
236
DNS requests
65
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2564 | iexplore.exe | GET | 200 | 41.63.96.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9eae438d1ab9dc75 | ZA | compressed | 4.70 Kb | whitelisted |
2564 | iexplore.exe | GET | 200 | 96.16.145.230:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
3052 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2564 | iexplore.exe | GET | 200 | 2.16.186.8:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgRZLSnaLQ9MIgIdzHYxxZV9vA%3D%3D | unknown | der | 503 b | shared |
2564 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2564 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFgp%2FItoW8aCEpZyb6sCgtg%3D | US | der | 471 b | whitelisted |
2564 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDbkGTmNqggqhJdBntfn8NX | US | der | 472 b | whitelisted |
2564 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2564 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 1.42 Kb | whitelisted |
2564 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEPkIO1Fut3ZEn%2Fhuq7tiKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3052 | iexplore.exe | 2.16.186.232:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
2564 | iexplore.exe | 96.16.145.230:80 | x1.c.lencr.org | AKAMAI-AS | DE | suspicious |
3052 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
2564 | iexplore.exe | 2.16.186.8:80 | r3.o.lencr.org | Akamai International B.V. | DE | whitelisted |
2564 | iexplore.exe | 142.250.74.200:443 | www.googletagmanager.com | GOOGLE | US | suspicious |
2564 | iexplore.exe | 142.250.184.226:443 | pagead2.googlesyndication.com | GOOGLE | US | whitelisted |
2564 | iexplore.exe | 208.88.224.98:443 | i.informer.com | WZCOM | US | unknown |
2564 | iexplore.exe | 74.117.179.70:443 | img.informer.com | WZCOM | US | suspicious |
2564 | iexplore.exe | 142.250.181.226:443 | googleads.g.doubleclick.net | GOOGLE | US | whitelisted |
2564 | iexplore.exe | 142.250.186.35:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
noob-killer-leerz.software.informer.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r3.o.lencr.org |
| shared |
img.informer.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
i.informer.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3492 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |