| File name: | Roblox.exe |
| Full analysis: | https://app.any.run/tasks/bc32b43c-61a7-44a9-9f17-7439236f76a2 |
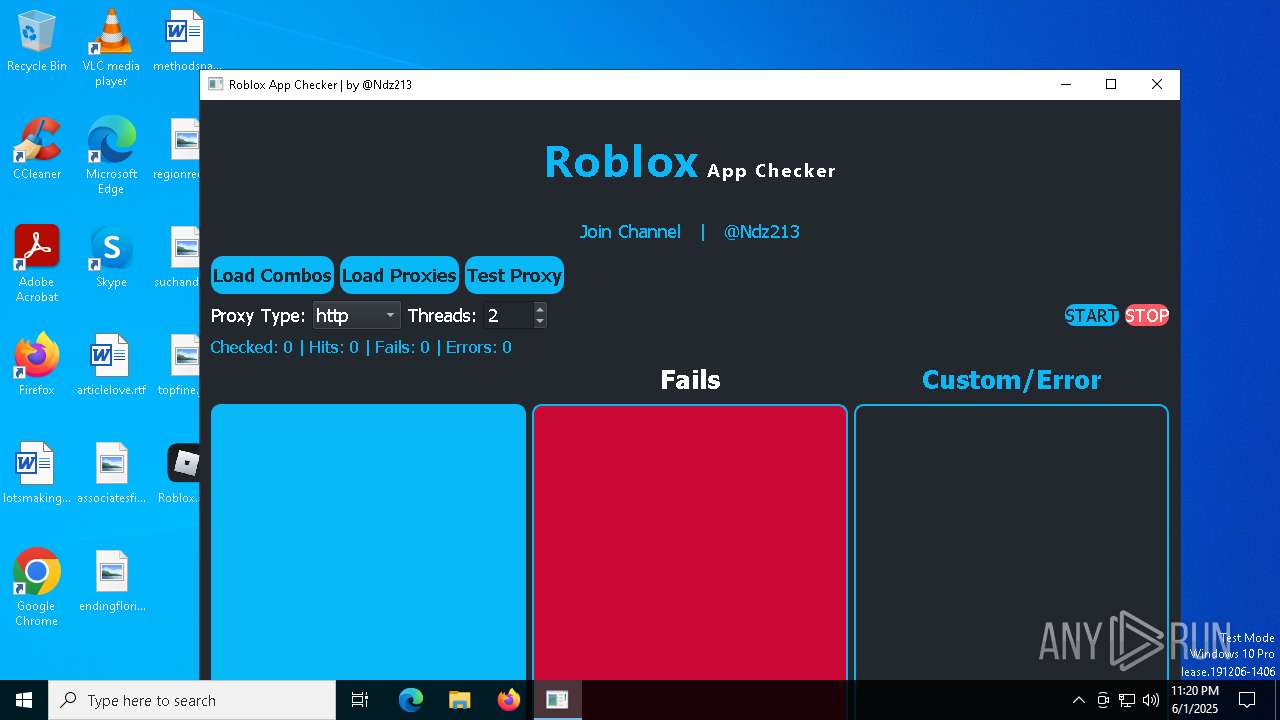
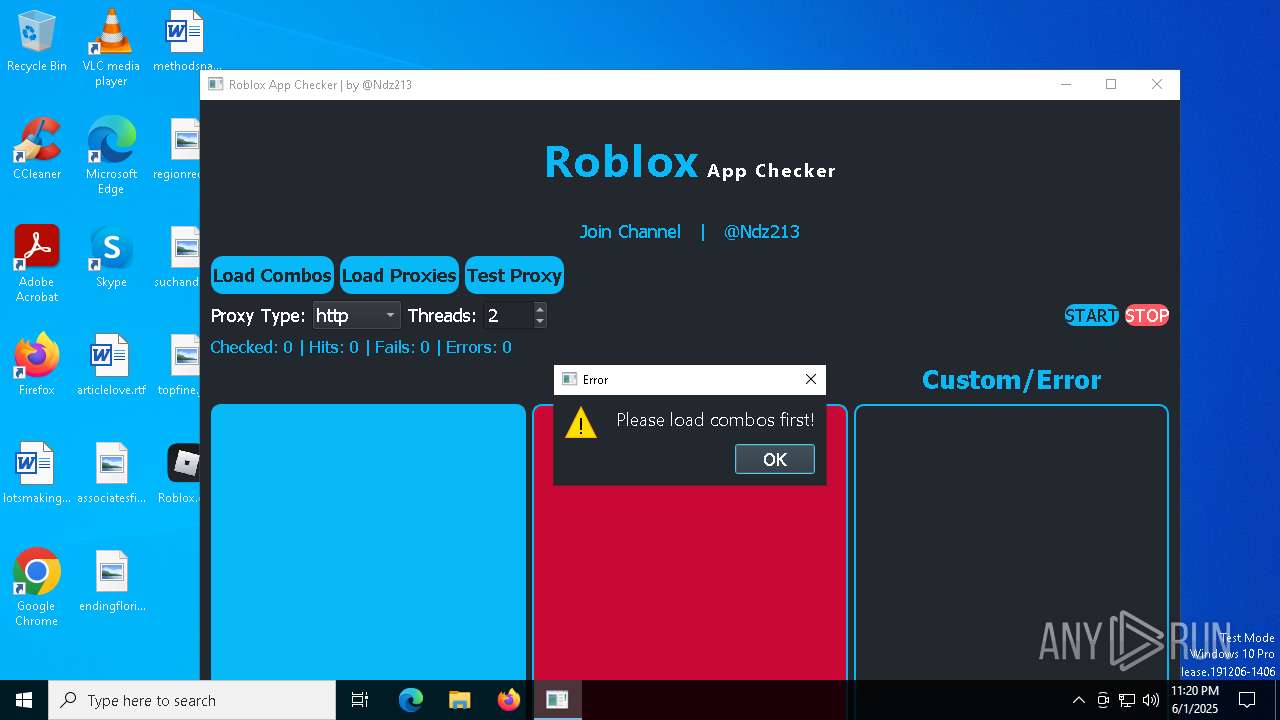
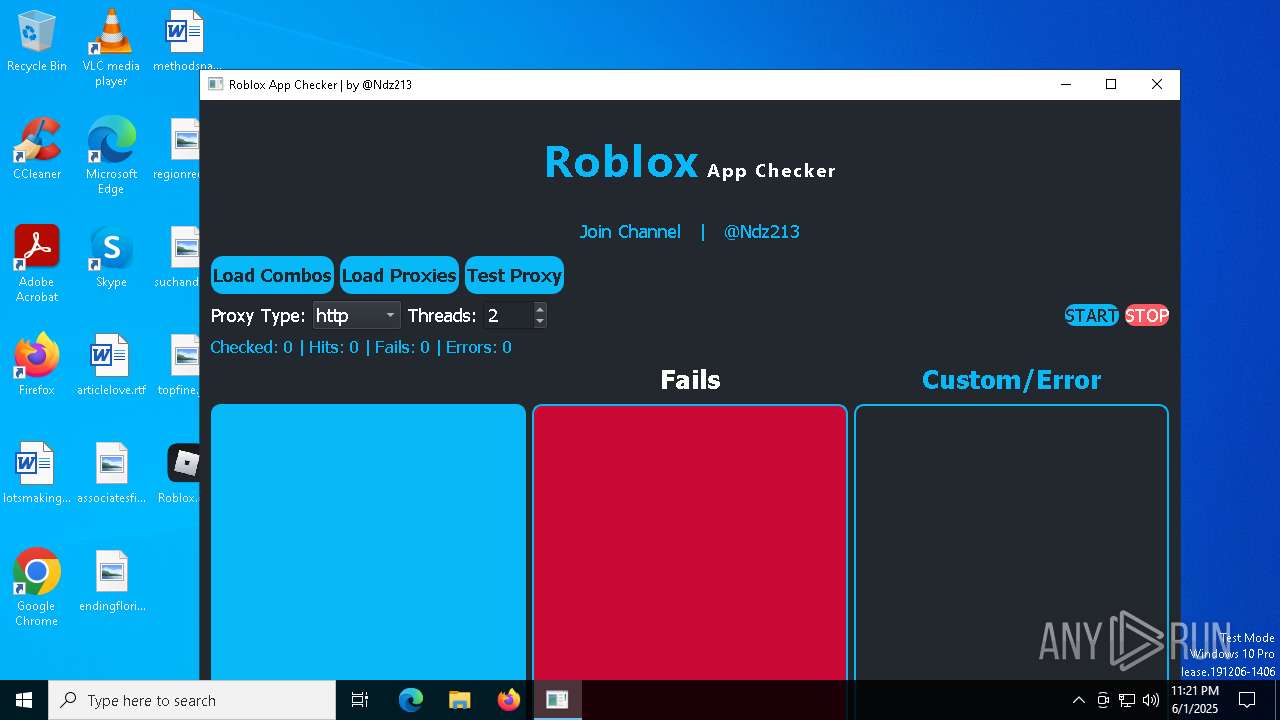
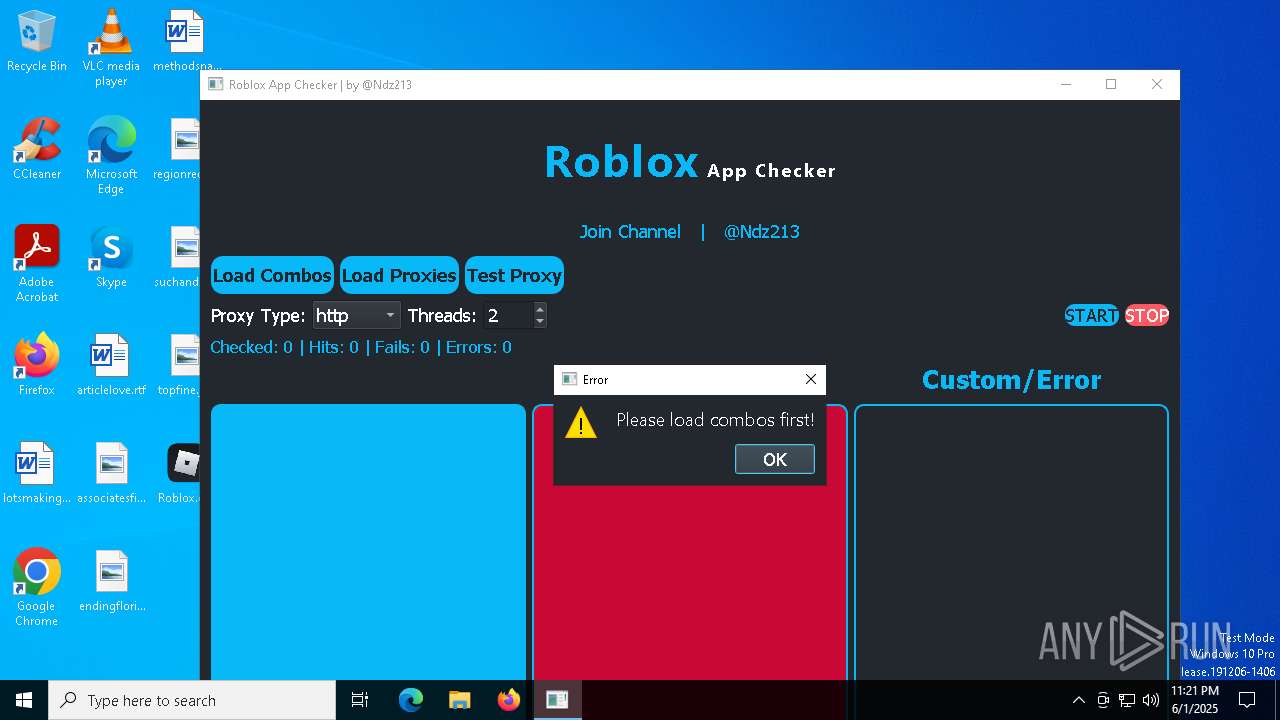
| Verdict: | Malicious activity |
| Analysis date: | June 01, 2025, 23:19:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 0F63E729994BCF8E54D164A57B1CE3C7 |
| SHA1: | 81640E0EBE5C9C5024236691DF2797103EA61A14 |
| SHA256: | 4F7E1355C7C450341A7EB1A12FD12AF2D1A9A12CDBC4C4E5DD5653B97689EE01 |
| SSDEEP: | 393216:RIu8VNkPEqrlDHGVEfv7mKxgYVfaW+3OfhAfk+tiN6wU/j1VG:Ry4PEqBDrn7mgllaPefhaCCj1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process drops C-runtime libraries
- Roblox.exe (PID: 7500)
Process drops legitimate windows executable
- Roblox.exe (PID: 7500)
Process drops python dynamic module
- Roblox.exe (PID: 7500)
Loads Python modules
- Roblox.exe (PID: 6240)
Executable content was dropped or overwritten
- Roblox.exe (PID: 7500)
Application launched itself
- Roblox.exe (PID: 7500)
There is functionality for taking screenshot (YARA)
- Roblox.exe (PID: 7500)
- Roblox.exe (PID: 6240)
INFO
Reads the computer name
- Roblox.exe (PID: 7500)
- Roblox.exe (PID: 6240)
Checks supported languages
- Roblox.exe (PID: 7500)
- Roblox.exe (PID: 6240)
The sample compiled with english language support
- Roblox.exe (PID: 7500)
Create files in a temporary directory
- Roblox.exe (PID: 7500)
PyInstaller has been detected (YARA)
- Roblox.exe (PID: 7500)
- Roblox.exe (PID: 6240)
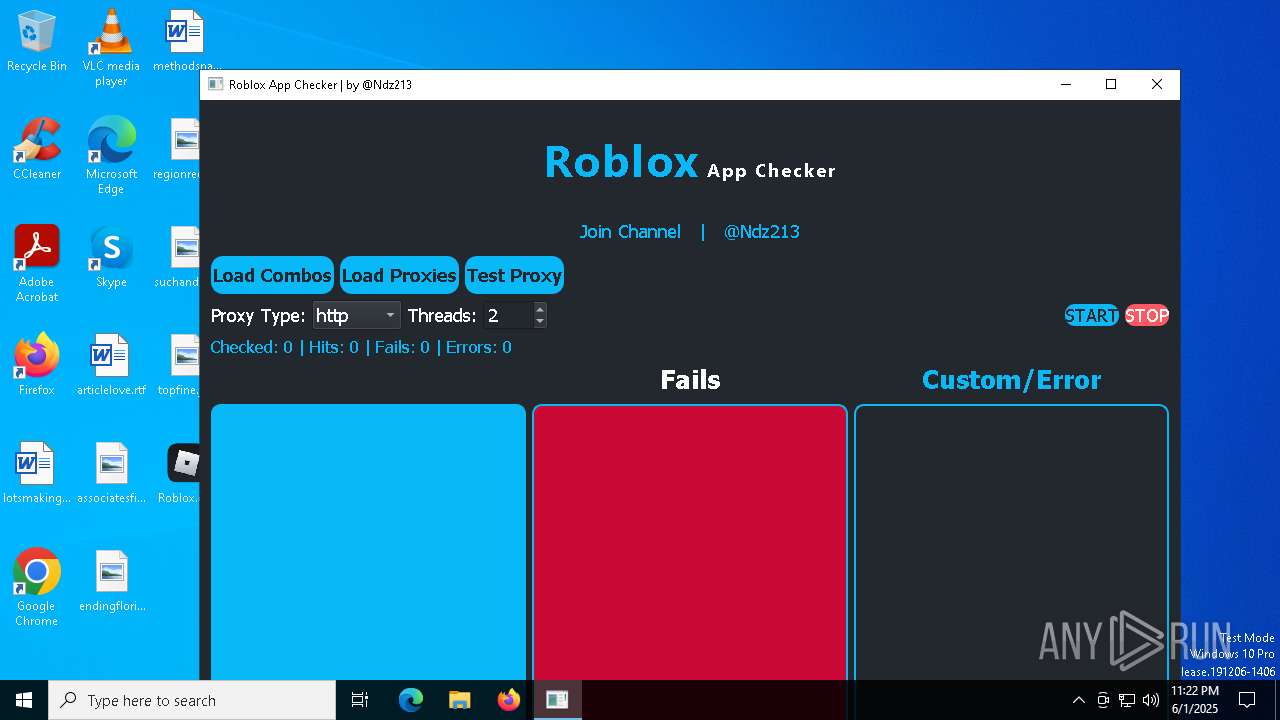
Checks proxy server information
- slui.exe (PID: 6132)
Reads the software policy settings
- slui.exe (PID: 6132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:01 21:22:55+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 173568 |
| InitializedDataSize: | 162304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce30 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
119
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6132 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6240 | "C:\Users\admin\Desktop\Roblox.exe" | C:\Users\admin\Desktop\Roblox.exe | — | Roblox.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7500 | "C:\Users\admin\Desktop\Roblox.exe" | C:\Users\admin\Desktop\Roblox.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
3 849
Read events
3 849
Write events
0
Delete events
0
Modification events
Executable files
107
Suspicious files
76
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7500 | Roblox.exe | C:\Users\admin\AppData\Local\Temp\_MEI75002\PyQt5\Qt5\bin\Qt5Gui.dll | executable | |
MD5:47307A1E2E9987AB422F09771D590FF1 | SHA256:5E7D2D41B8B92A880E83B8CC0CA173F5DA61218604186196787EE1600956BE1E | |||
| 7500 | Roblox.exe | C:\Users\admin\AppData\Local\Temp\_MEI75002\PyQt5\Qt5\bin\VCRUNTIME140.dll | executable | |
MD5:971DBBE854FC6AB78C095607DFAD7B5C | SHA256:5E197A086B6A7711BAA09AFE4EA7C68F0E777B2FF33F1DF25A21F375B7D9693A | |||
| 7500 | Roblox.exe | C:\Users\admin\AppData\Local\Temp\_MEI75002\PyQt5\Qt5\bin\Qt5Qml.dll | executable | |
MD5:D055566B5168D7B1D4E307C41CE47C4B | SHA256:30035484C81590976627F8FACE9507CAA8581A7DC7630CCCF6A8D6DE65CAB707 | |||
| 7500 | Roblox.exe | C:\Users\admin\AppData\Local\Temp\_MEI75002\PyQt5\Qt5\bin\Qt5Svg.dll | executable | |
MD5:03761F923E52A7269A6E3A7452F6BE93 | SHA256:7348CFC6444438B8845FB3F59381227325D40CA2187D463E82FC7B8E93E38DB5 | |||
| 7500 | Roblox.exe | C:\Users\admin\AppData\Local\Temp\_MEI75002\PyQt5\Qt5\bin\Qt5Core.dll | executable | |
MD5:817520432A42EFA345B2D97F5C24510E | SHA256:8D2FF4CE9096DDCCC4F4CD62C2E41FC854CFD1B0D6E8D296645A7F5FD4AE565A | |||
| 7500 | Roblox.exe | C:\Users\admin\AppData\Local\Temp\_MEI75002\PyQt5\Qt5\bin\Qt5DBus.dll | executable | |
MD5:0E8FF02D971B61B5D2DD1AC4DF01AE4A | SHA256:1AA70B106A10C86946E23CAA9FC752DC16E29FBE803BBA1F1AB30D1C63EE852A | |||
| 7500 | Roblox.exe | C:\Users\admin\AppData\Local\Temp\_MEI75002\PyQt5\Qt5\bin\opengl32sw.dll | executable | |
MD5:7DBC97BFEE0C7AC89DA8D0C770C977B6 | SHA256:963641A718F9CAE2705D5299EAE9B7444E84E72AB3BEF96A691510DD05FA1DA4 | |||
| 7500 | Roblox.exe | C:\Users\admin\AppData\Local\Temp\_MEI75002\PyQt5\Qt5\bin\Qt5QmlModels.dll | executable | |
MD5:2030C4177B499E6118BE5B9E5761FCE1 | SHA256:51E4E5A5E91F78774C44F69B599FAE4735277EF2918F7061778615CB5C4F6E81 | |||
| 7500 | Roblox.exe | C:\Users\admin\AppData\Local\Temp\_MEI75002\PyQt5\Qt5\plugins\generic\qtuiotouchplugin.dll | executable | |
MD5:750A31DE7840B5EED8BA14C1BD84D348 | SHA256:A9BFFB0F3CD69CD775C328C916E46440FE80D99119FAEBC350C7EC51E3E57C41 | |||
| 7500 | Roblox.exe | C:\Users\admin\AppData\Local\Temp\_MEI75002\PyQt5\Qt5\bin\Qt5WebSockets.dll | executable | |
MD5:A016545F963548E0F37885E07EF945C7 | SHA256:6B56F77DA6F17880A42D2F9D2EC8B426248F7AB2196A0F55D37ADE39E3878BC6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
47
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 40.126.31.73:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.0:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.31.0:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.73:443 | https://login.live.com/RST2.srf | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 20.109.210.53:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 304 | 20.109.210.53:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 13.85.23.206:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5988 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |