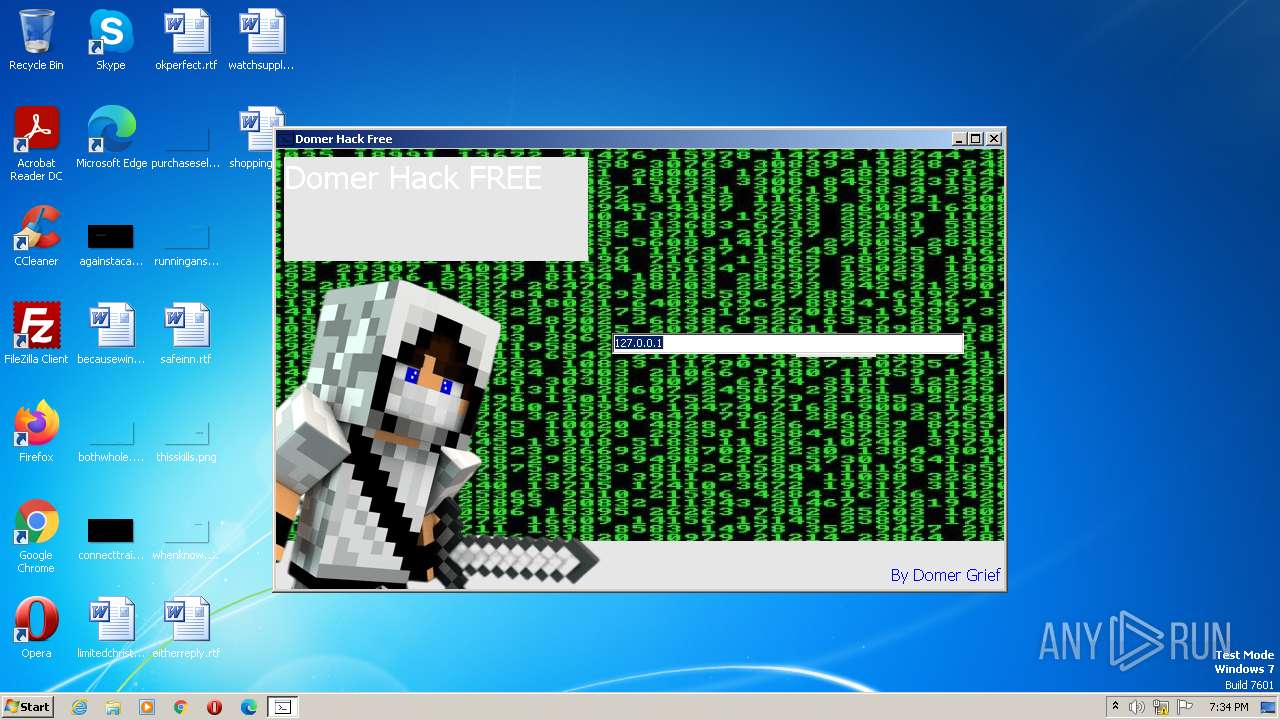
| File name: | Domer Hack.exe |
| Full analysis: | https://app.any.run/tasks/2189daa4-6200-414b-9708-4553d2bd7c83 |
| Verdict: | Malicious activity |
| Analysis date: | July 14, 2023, 18:33:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AB9616F7F7F4960BDA05B862039B2C72 |
| SHA1: | F891BEFA16F777A05CE7CE0618EF1342BD211952 |
| SHA256: | 4F76903B0E86C2CB8249EC5858F957527CC4E89D5CE2A46154AF3D40FCE05704 |
| SSDEEP: | 393216:g8HMqQhccc7Xg0qhooNRtILfP+Zv1uzKHWFWqZ:5H+hcc2gfILfE1uiLI |
MALICIOUS
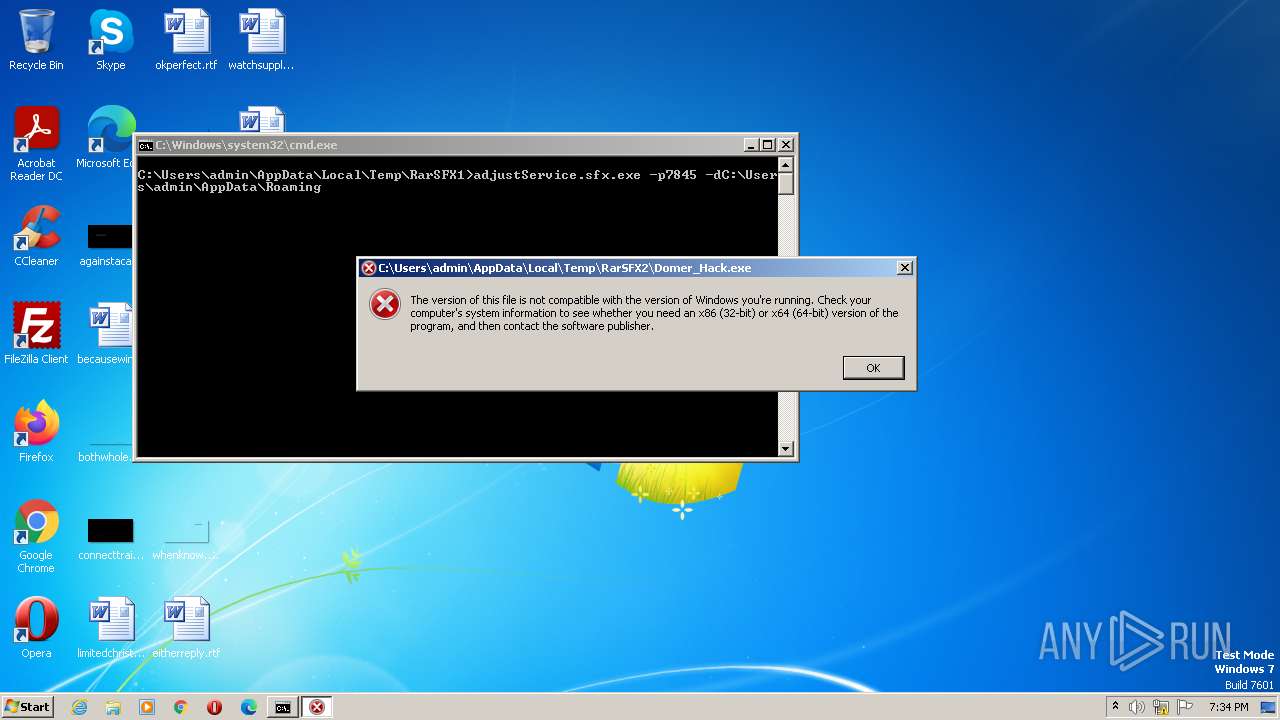
Application was dropped or rewritten from another process
- adjustService.exe (PID: 1780)
- аdjustService.exe (PID: 3060)
- Domer_Hack.exe (PID: 2860)
Loads dropped or rewritten executable
- Domer_Hack.exe (PID: 2860)
SUSPICIOUS
Executable content was dropped or overwritten
- Domer Hack.exe (PID: 3396)
- adjustService.exe (PID: 3660)
- adjustService.sfx.exe (PID: 1076)
Starts itself from another location
- Domer Hack.exe (PID: 3396)
Reads the Internet Settings
- Domer Hack.exe (PID: 3396)
- adjustService.exe (PID: 3660)
- adjustService.sfx.exe (PID: 1076)
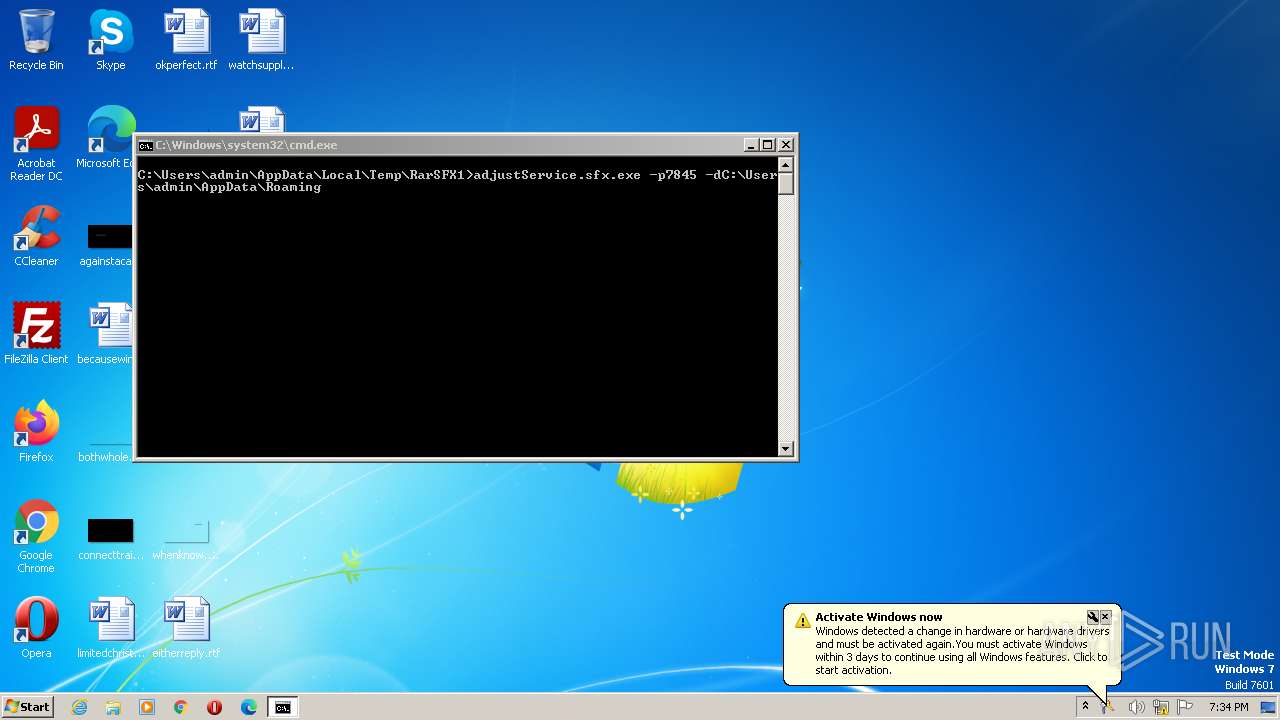
Starts CMD.EXE for commands execution
- adjustService.exe (PID: 3660)
Executing commands from a ".bat" file
- adjustService.exe (PID: 3660)
INFO
The process checks LSA protection
- Domer Hack.exe (PID: 3396)
- adjustService.exe (PID: 3660)
- adjustService.sfx.exe (PID: 1076)
- adjustService.exe (PID: 1780)
- аdjustService.exe (PID: 3060)
- Domer_Hack.exe (PID: 2860)
Checks supported languages
- Domer Hack.exe (PID: 3396)
- adjustService.exe (PID: 3660)
- adjustService.sfx.exe (PID: 1076)
- adjustService.exe (PID: 1780)
- аdjustService.exe (PID: 3060)
- Domer_Hack.exe (PID: 2860)
Reads the computer name
- Domer Hack.exe (PID: 3396)
- adjustService.exe (PID: 3660)
- adjustService.sfx.exe (PID: 1076)
- аdjustService.exe (PID: 3060)
- adjustService.exe (PID: 1780)
- Domer_Hack.exe (PID: 2860)
Create files in a temporary directory
- Domer Hack.exe (PID: 3396)
- adjustService.exe (PID: 3660)
- adjustService.sfx.exe (PID: 1076)
- adjustService.exe (PID: 1780)
- Domer_Hack.exe (PID: 2860)
The executable file from the user directory is run by the CMD process
- adjustService.sfx.exe (PID: 1076)
Reads the machine GUID from the registry
- adjustService.exe (PID: 1780)
- аdjustService.exe (PID: 3060)
Creates files or folders in the user directory
- adjustService.exe (PID: 1780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x20780 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 117760 |
| CodeSize: | 208384 |
| LinkerVersion: | 14.33 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2023:05:29 16:03:32+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-May-2023 16:03:32 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 29-May-2023 16:03:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00032DBC | 0x00032E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70538 |
.rdata | 0x00034000 | 0x0000B1D0 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.27064 |
.data | 0x00040000 | 0x00024750 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.08355 |
.didat | 0x00065000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.50336 |
.rsrc | 0x00066000 | 0x0000E044 | 0x0000E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.80238 |
.reloc | 0x00075000 | 0x000023DC | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.67862 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 5.10026 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.25868 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.02609 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.18109 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.04307 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.66634 | 508 | Latin 1 / Western European | UNKNOWN | RT_STRING |
8 | 3.71728 | 582 | Latin 1 / Western European | UNKNOWN | RT_STRING |
9 | 3.73856 | 422 | Latin 1 / Western European | UNKNOWN | RT_STRING |
10 | 3.55807 | 220 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
KERNEL32.dll |
OLEAUT32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
44
Monitored processes
7
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1076 | adjustService.sfx.exe -p7845 -dC:\Users\admin\AppData\Roaming | C:\Users\admin\AppData\Local\Temp\RarSFX1\adjustService.sfx.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1780 | "C:\Users\admin\AppData\Local\Temp\RarSFX2\adjustService.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX2\adjustService.exe | — | adjustService.sfx.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2860 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\Domer_Hack.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\Domer_Hack.exe | — | Domer Hack.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3060 | "C:\Users\admin\AppData\Local\Temp\RarSFX2\аdjustService.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX2\аdjustService.exe | — | adjustService.sfx.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3396 | "C:\Users\admin\AppData\Local\Temp\Domer Hack.exe" | C:\Users\admin\AppData\Local\Temp\Domer Hack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3660 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\adjustService.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\adjustService.exe | Domer Hack.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3992 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\RarSFX1\adjustService.bat" " | C:\Windows\System32\cmd.exe | — | adjustService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 798
Read events
2 774
Write events
24
Delete events
0
Modification events
| (PID) Process: | (3396) Domer Hack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3396) Domer Hack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3396) Domer Hack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3396) Domer Hack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3660) adjustService.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3660) adjustService.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3660) adjustService.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3660) adjustService.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1076) adjustService.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1076) adjustService.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
8
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3660 | adjustService.exe | C:\Users\admin\AppData\Local\Temp\RarSFX1\adjustService.bat | text | |
MD5:9467FDC3EA693B0827748707EE023016 | SHA256:21B7E4A31876568CD3716AD9A7BCB3A260B2124282DA0D58BF9BCE3F028754B8 | |||
| 1076 | adjustService.sfx.exe | C:\Users\admin\AppData\Local\Temp\RarSFX2\adjustService.exe | executable | |
MD5:C2BE6BB25335D4BFC3E880EF79BF8003 | SHA256:62D4F6C2EF8AA2D1A8B4B7710B39934A2A328DEFC5A00C5F1E0D05EF6A4B8768 | |||
| 3396 | Domer Hack.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\adjustService.exe | executable | |
MD5:3D364E4547AC77054FD2376DF3092D62 | SHA256:EDD7FF7014E25B0DF8654F5064BB62DF39A6667E62FD3A30B9B0E106BDA6CA3B | |||
| 1076 | adjustService.sfx.exe | C:\Users\admin\AppData\Local\Temp\RarSFX2\аdjustService.exe | executable | |
MD5:8296383BA1CAE4F27D7FFD2A6519F67E | SHA256:5656A69925BA13C97C9C789C87E5945193D374A86525641751C22AE06296A4F1 | |||
| 1076 | adjustService.sfx.exe | C:\Users\admin\AppData\Local\Temp\RarSFX2\Domer_Haсk.exe | executable | |
MD5:145FCC98B2A116BB9AE8A31DE0206BA8 | SHA256:9D817FC7E72B9B8790956745185DFFFF4F4724EB5F5B75E57DC1E6C7A1767AF2 | |||
| 3396 | Domer Hack.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Domer_Hack.exe | executable | |
MD5:1A312C06BCA80B3AC48CF77BD3472F28 | SHA256:E40F9EAD95D2A7A64416151EEE05D71C9A9EB3760C2CAC5E119465452274F4EB | |||
| 1780 | adjustService.exe | C:\Users\admin\AppData\Roaming\app | text | |
MD5:8F11404A507CFB98455F89A534077F73 | SHA256:F7C301F3FCCE1C2444B540090E5024F0CEA1806AB8AE1D81901ECC3B63334CBB | |||
| 2860 | Domer_Hack.exe | C:\Users\admin\AppData\Local\Temp\PSE20\1a312c06bca80b3ac48cf77bd3472f28\php.ini | text | |
MD5:6A40C247FBCD22D14261FA55F6A16858 | SHA256:A337F139CF6AA502AFF68E7A948A62D2BCE9CCEF3E2709B603BA6528BFD23C87 | |||
| 3396 | Domer Hack.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\php5ts.dll | executable | |
MD5:C9AFF68F6673FAE7580527E8C76805B6 | SHA256:9B2C8B8C4CEC301C4303F58CA4E8B261D516F10FEB24573B092DFCCC263BAEA4 | |||
| 3660 | adjustService.exe | C:\Users\admin\AppData\Local\Temp\RarSFX1\adjustService.sfx.exe | executable | |
MD5:FB2F119370D2A8FCC765F2D193AA245E | SHA256:BCA32F70ECDBD4CEC7DDE53512CF1E28F7E036877253A935D1FA9DFD0F405E37 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1068 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |