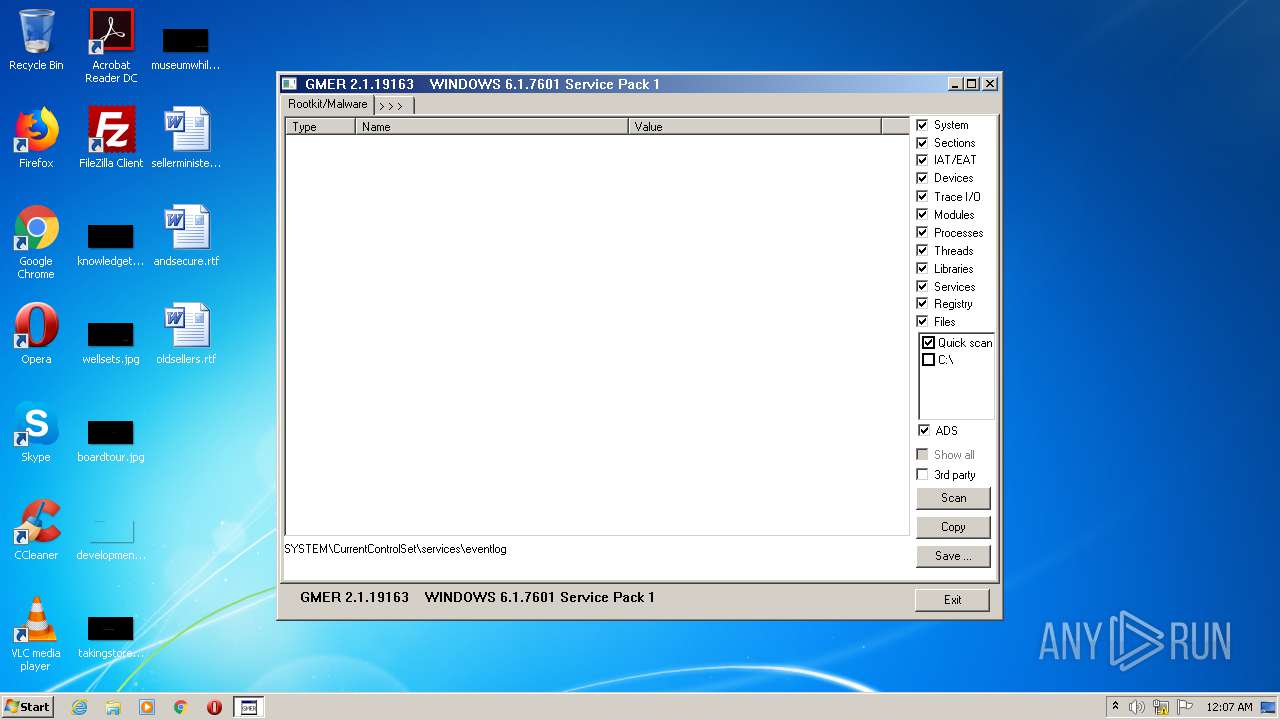
| File name: | gmer.exe |
| Full analysis: | https://app.any.run/tasks/80d1da98-1b12-4348-b5c0-3863a32a2582 |
| Verdict: | Malicious activity |
| Analysis date: | November 19, 2020, 00:07:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 60BF4AE8CC40B0E3E28613657ED2EED8 |
| SHA1: | C1BD4BC1E9408B95F5E63323A463A5DC84F76FBA |
| SHA256: | 4F61F20FA1EDFD0CE1DE2CA8110C725C9D9C16A9680748C12042A3302054FC72 |
| SSDEEP: | 6144:3/o8A/RhvlBjKfEiF4jPU7rp5daDOvFsvOAaWv+QT4rYBdLcFu+dE18b/RbA1i04:3/o8cXNkcigPw7dFvFsvNTCMauG01i01 |
MALICIOUS
Changes settings of System certificates
- gmer.exe (PID: 2580)
Loads dropped or rewritten executable
- gmer.exe (PID: 2580)
- host.exe (PID: 2076)
- explorer.exe (PID: 2332)
- AUDIODG.EXE (PID: 1428)
- DllHost.exe (PID: 3876)
- DllHost.exe (PID: 2156)
- SearchFilterHost.exe (PID: 2968)
- DllHost.exe (PID: 4088)
- SearchProtocolHost.exe (PID: 1328)
SUSPICIOUS
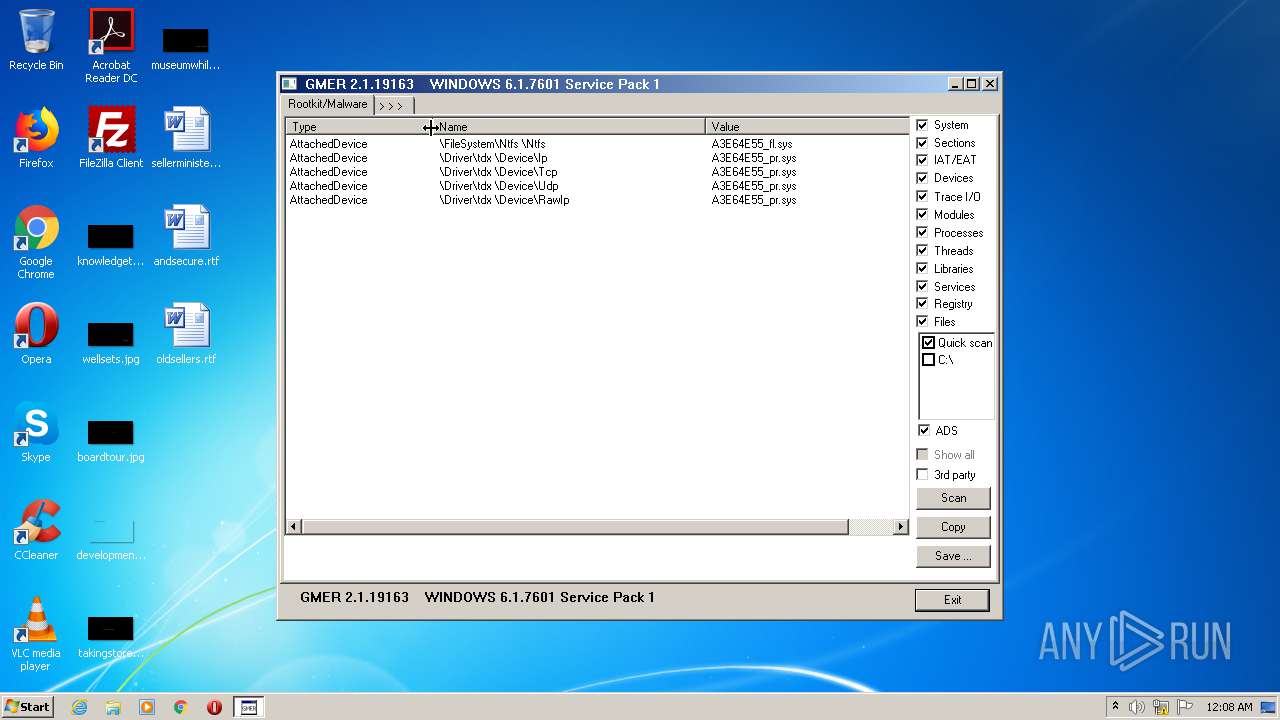
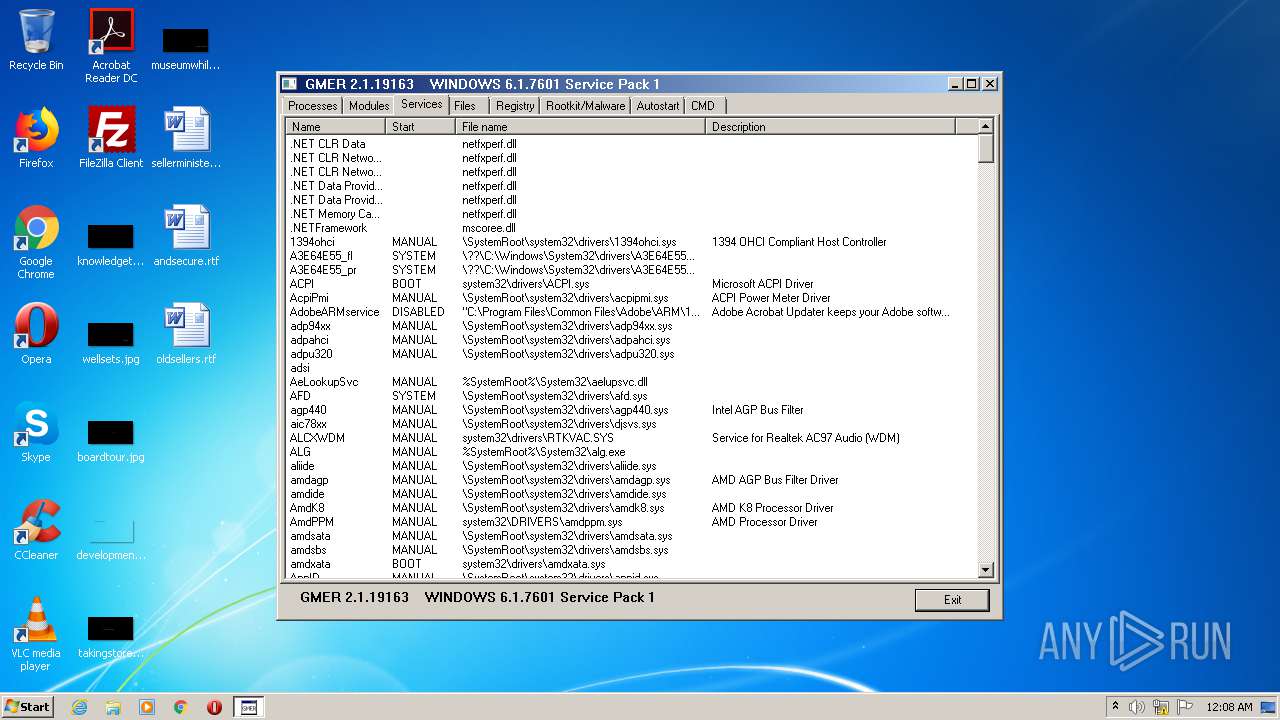
Creates or modifies windows services
- gmer.exe (PID: 2580)
Adds / modifies Windows certificates
- gmer.exe (PID: 2580)
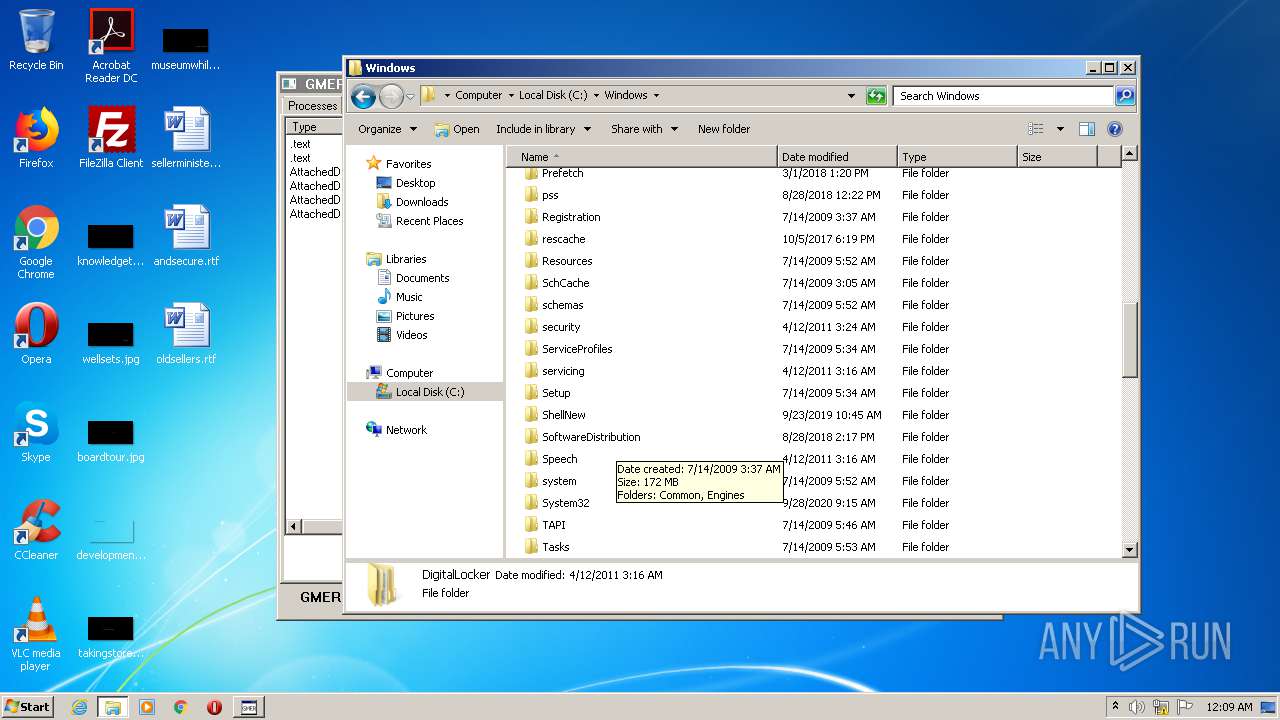
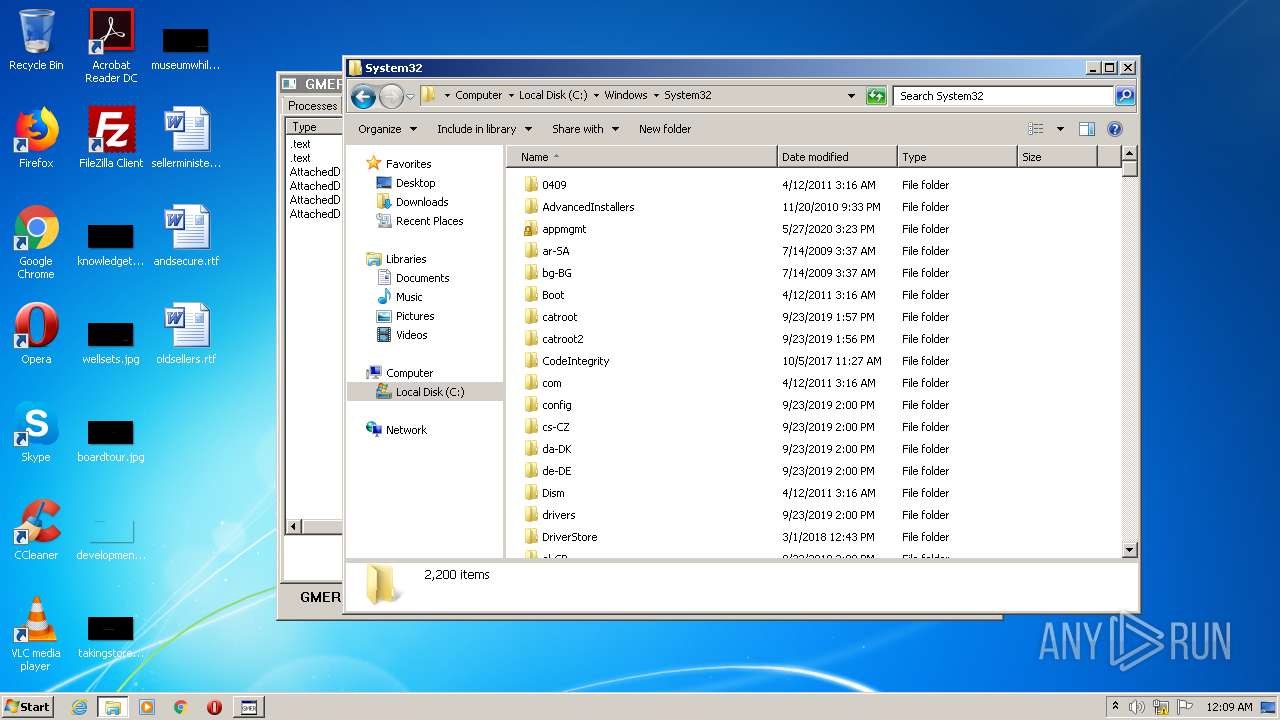
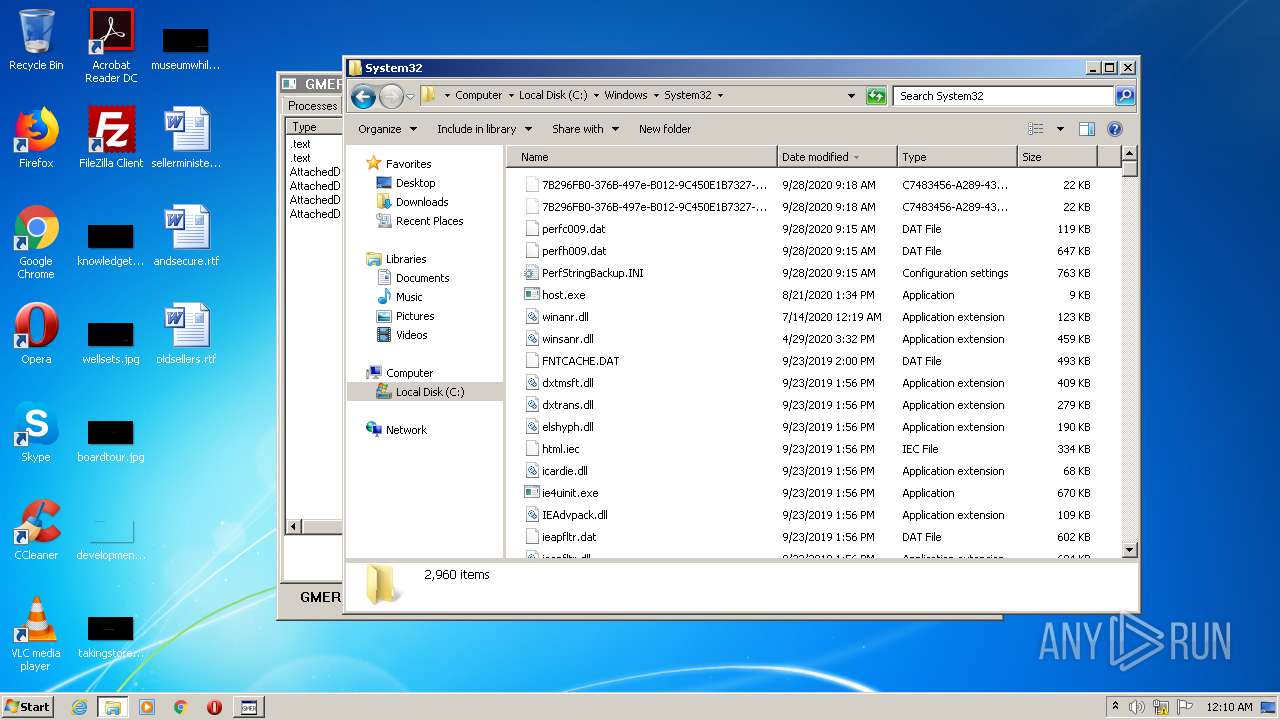
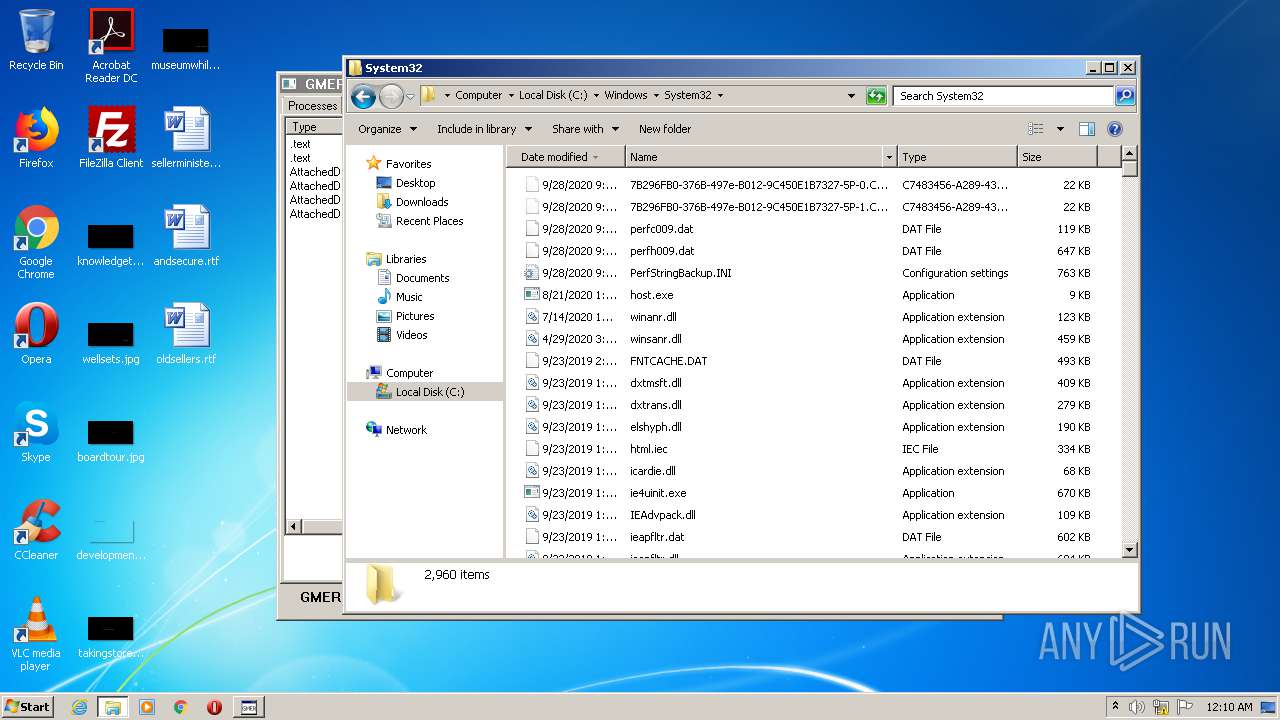
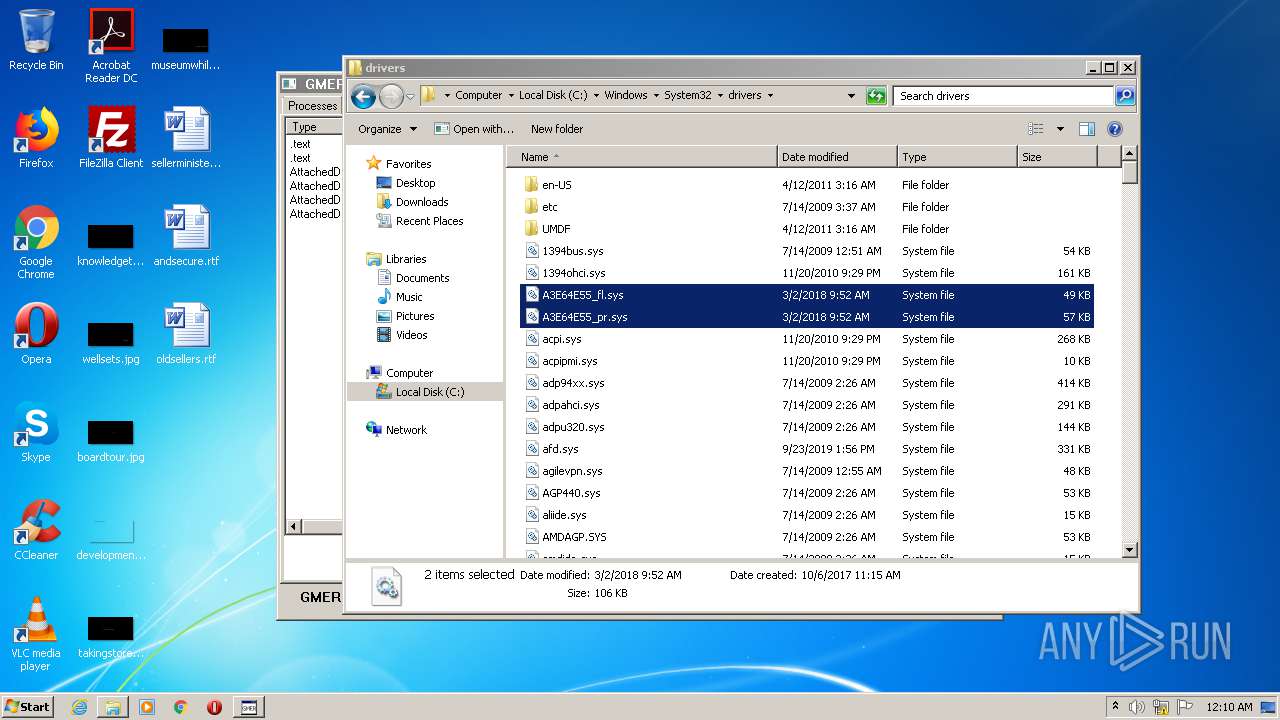
Executable content was dropped or overwritten
- gmer.exe (PID: 2580)
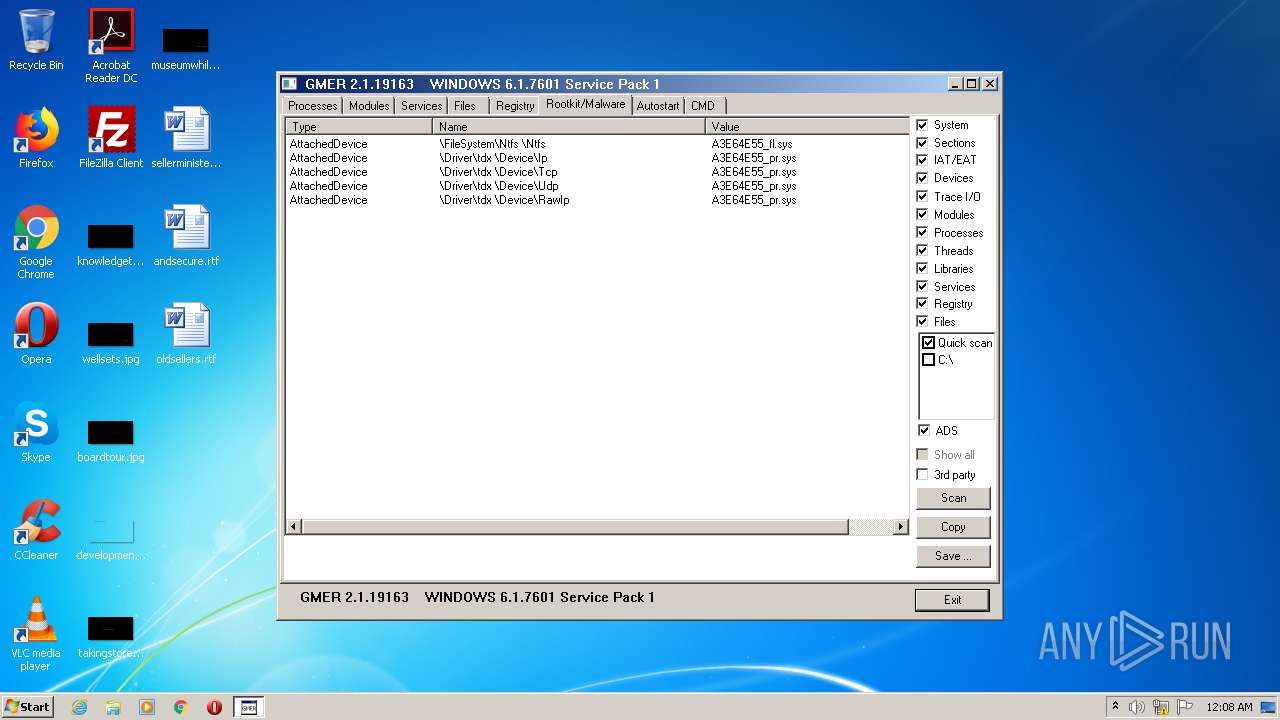
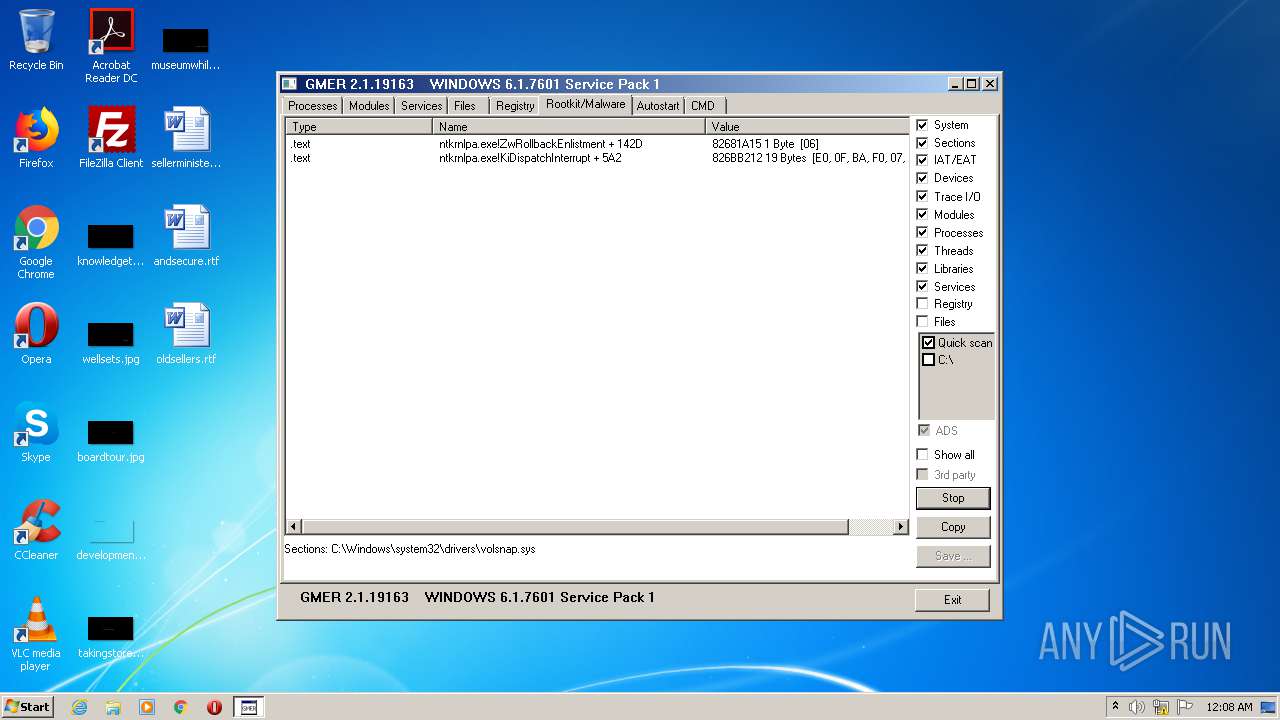
Low-level read access rights to disk partition
- gmer.exe (PID: 2580)
INFO
Reads settings of System Certificates
- gmer.exe (PID: 2580)
Manual execution by user
- explorer.exe (PID: 2332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:04:04 09:55:28+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 372736 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 520192 |
| EntryPoint: | 0xda9e0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.19163.0 |
| ProductVersionNumber: | 2.1.19163.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Polish |
| CharacterSet: | Unicode |
| FileVersion: | 2, 1, 19163 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Apr-2013 07:55:28 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 04-Apr-2013 07:55:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0007F000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00080000 | 0x0005B000 | 0x0005AC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92815 |
.rsrc | 0x000DB000 | 0x00002000 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.49192 |
Imports
KERNEL32.DLL |
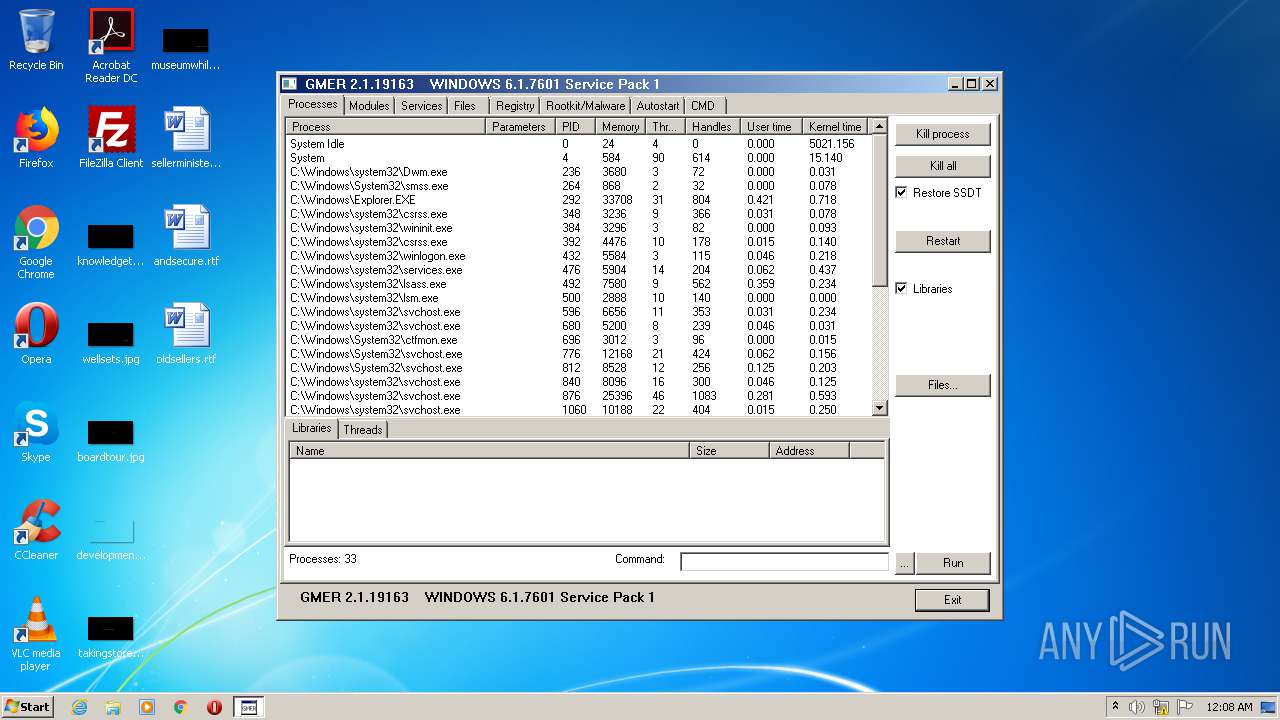
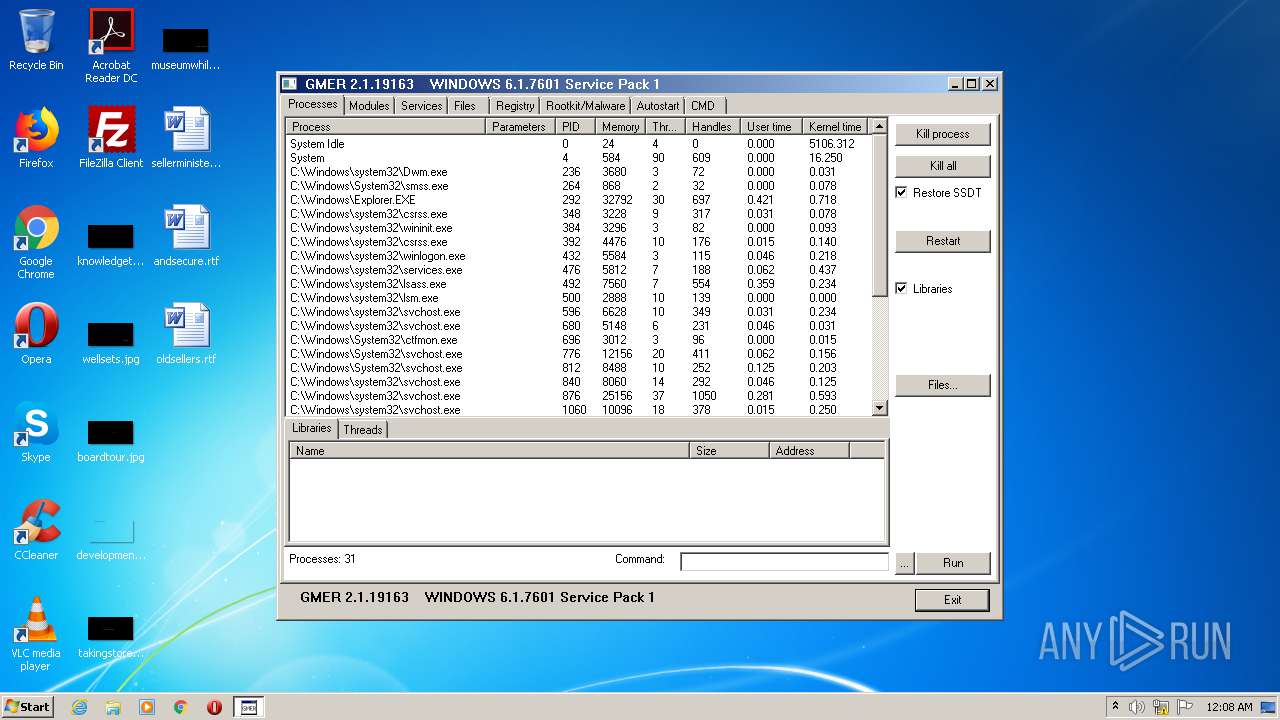
Total processes
44
Monitored processes
10
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1328 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1428 | C:\Windows\system32\AUDIODG.EXE 0x504 | C:\Windows\system32\AUDIODG.EXE | — | svchost.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Audio Device Graph Isolation Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2076 | "host.exe" | C:\Windows\system32\host.exe | — | srvpost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2096 | "C:\Users\admin\AppData\Local\Temp\gmer.exe" | C:\Users\admin\AppData\Local\Temp\gmer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 2, 1, 19163 Modules
| |||||||||||||||
| 2156 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2332 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2580 | "C:\Users\admin\AppData\Local\Temp\gmer.exe" | C:\Users\admin\AppData\Local\Temp\gmer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 2, 1, 19163 Modules
| |||||||||||||||
| 2968 | "C:\Windows\system32\SearchFilterHost.exe" 0 516 520 528 65536 524 | C:\Windows\system32\SearchFilterHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Filter Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3876 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4088 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
710
Read events
675
Write events
35
Delete events
0
Modification events
| (PID) Process: | (2076) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2076) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2076) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2076) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2076) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2076) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2076) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2076) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2076) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENESW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2076) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
19
Suspicious files
30
Text files
0
Unknown types
9
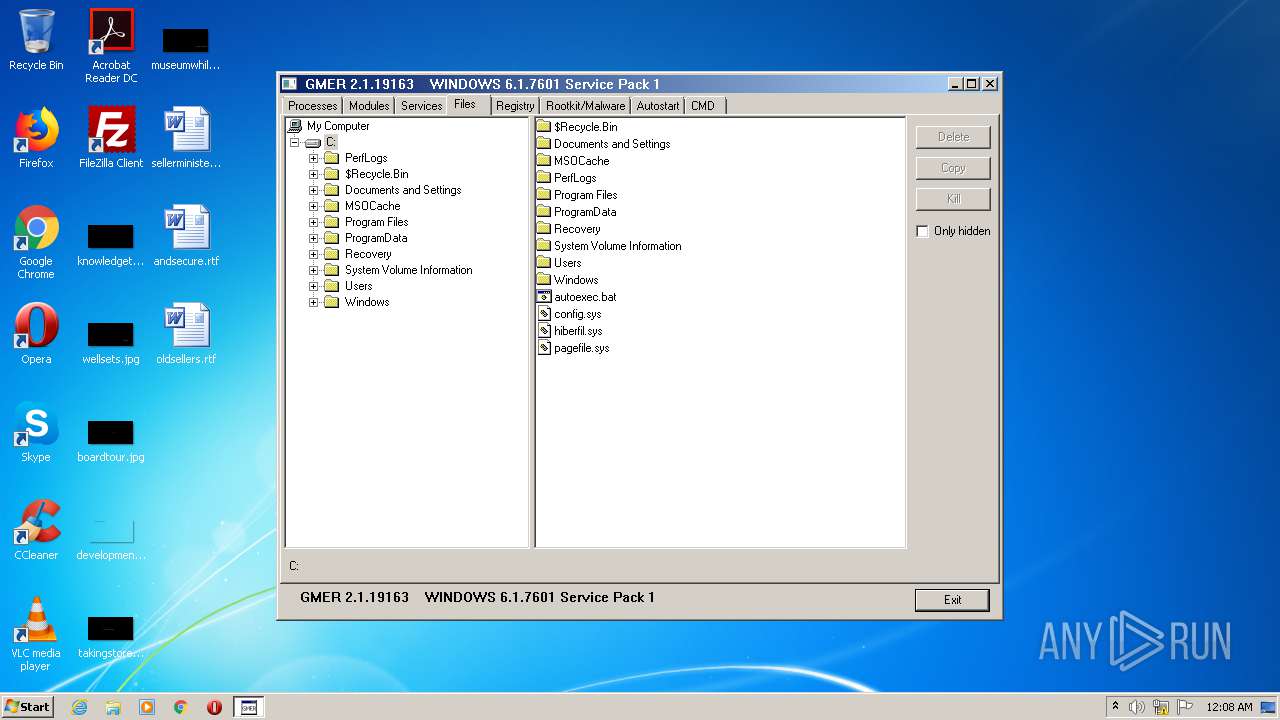
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | gmer.exe | C:\Users\admin\AppData\Local\Temp\CabB724.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | gmer.exe | C:\Users\admin\AppData\Local\Temp\TarB725.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmpB7B2.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmpB7E2.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmpB822.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmpB890.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmpB8DF.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmpB92E.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmpD185.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | gmer.exe | C:\Users\admin\AppData\Local\Temp\tmpD213.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
7
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2580 | gmer.exe | GET | 200 | 23.51.123.27:80 | http://sf.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTSqZMG5M8TA9rdzkbCnNwuMAd5VgQUz5mp6nsm9EvJjo%2FX8AUm7%2BPSp50CEFbG0met4H9y7rRgO7%2BEzqU%3D | NL | der | 1.62 Kb | whitelisted |
2580 | gmer.exe | GET | 200 | 23.51.123.27:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEFIA5aolVvwahu2WydRLM8c%3D | NL | der | 1.71 Kb | whitelisted |
2580 | gmer.exe | GET | 200 | 23.51.123.27:80 | http://ts-ocsp.ws.symantec.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRi82PVYYKWGJWdgVNyePy5kYTdqQQUX5r1blzMzHSa1N197z%2Fb7EyALt0CEA7P9DjI%2Fr81bgTYapgbGlA%3D | NL | der | 1.43 Kb | whitelisted |
2580 | gmer.exe | GET | 200 | 23.51.123.27:80 | http://ocsp.thawte.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQJ1TBLBrQ9OnPHXPVaWb87MxkNlgQUwu79F9f%2Btw%2FGciJ7fvbA4gIz7D4CEH6T6%2Ft8xk5Z6kuad9QG%2FDs%3D | NL | der | 1.30 Kb | whitelisted |
2580 | gmer.exe | GET | 200 | 23.51.123.27:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQJ1TBLBrQ9OnPHXPVaWb87MxkNlgQUwu79F9f%2Btw%2FGciJ7fvbA4gIz7D4CEEe%2FGZXfjVJGQ%2FfbbUgNMaQ%3D | NL | der | 1.30 Kb | whitelisted |
2580 | gmer.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
2580 | gmer.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
2580 | gmer.exe | GET | 200 | 93.184.220.29:80 | http://crl.verisign.com/tss-ca.crl | US | der | 413 b | whitelisted |
2580 | gmer.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
2580 | gmer.exe | GET | 200 | 23.51.123.27:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTO3jAJoCaQZUo7%2B2qJhdK4D6wpuQQUqkwAvoiA5mAvIL8uAwdOcMH2iFUCEDgl1%2Fr4Ya%2Be9JDnJrXWWtU%3D | NL | binary | 5 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2580 | gmer.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
2580 | gmer.exe | 93.184.220.29:80 | crl.verisign.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2580 | gmer.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
2580 | gmer.exe | 23.51.123.27:80 | ocsp.verisign.com | Akamai Technologies, Inc. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
ocsp.verisign.com |
| whitelisted |
sf.symcd.com |
| whitelisted |
ocsp.thawte.com |
| whitelisted |
ts-ocsp.ws.symantec.com |
| whitelisted |
crl.verisign.com |
| whitelisted |