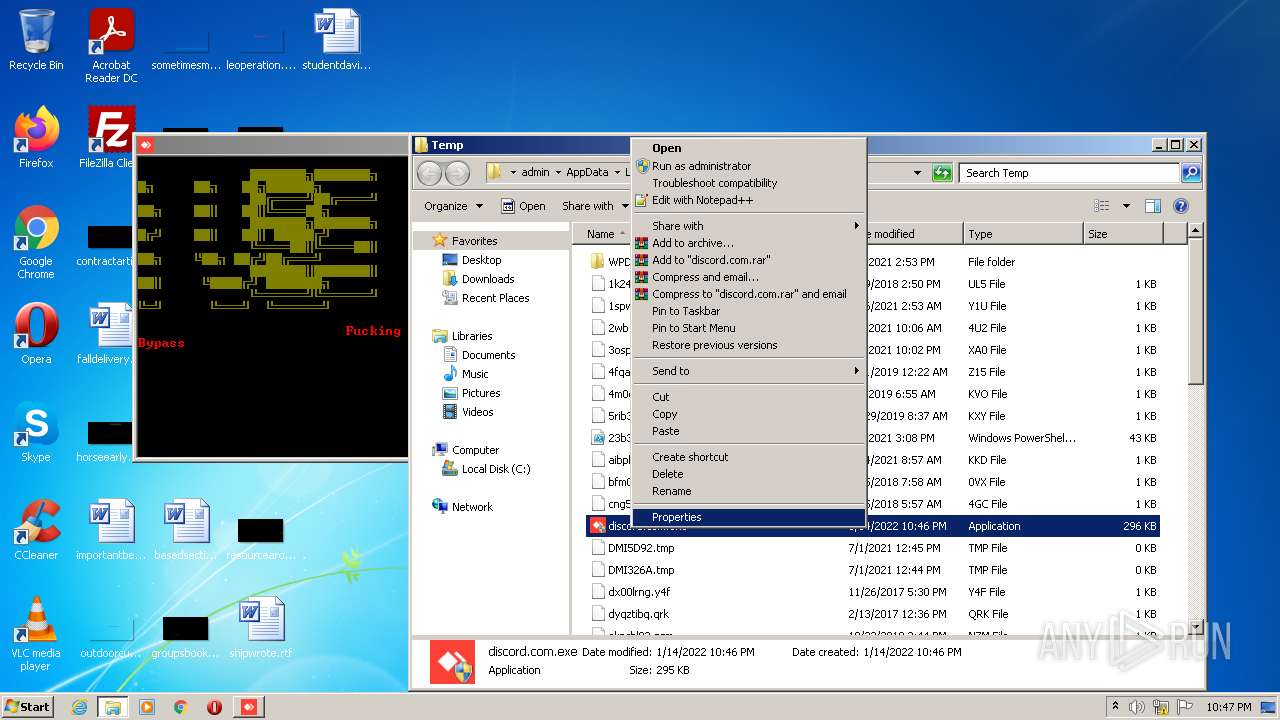
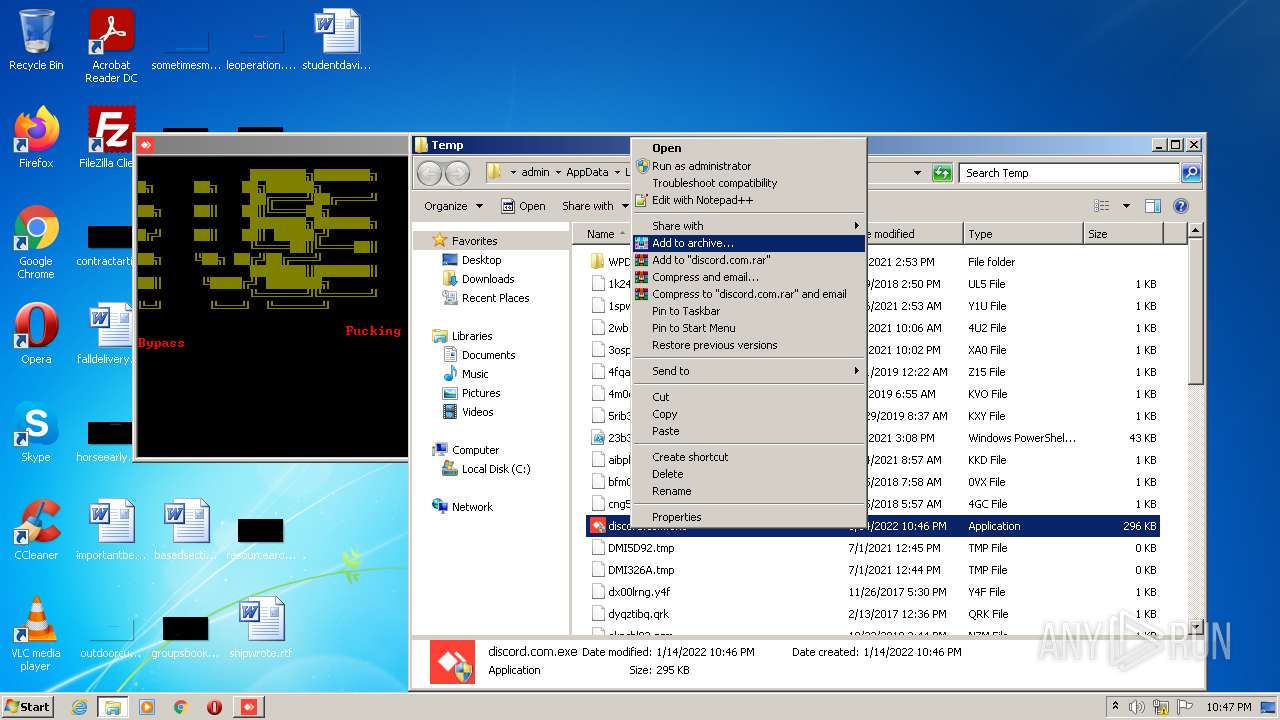
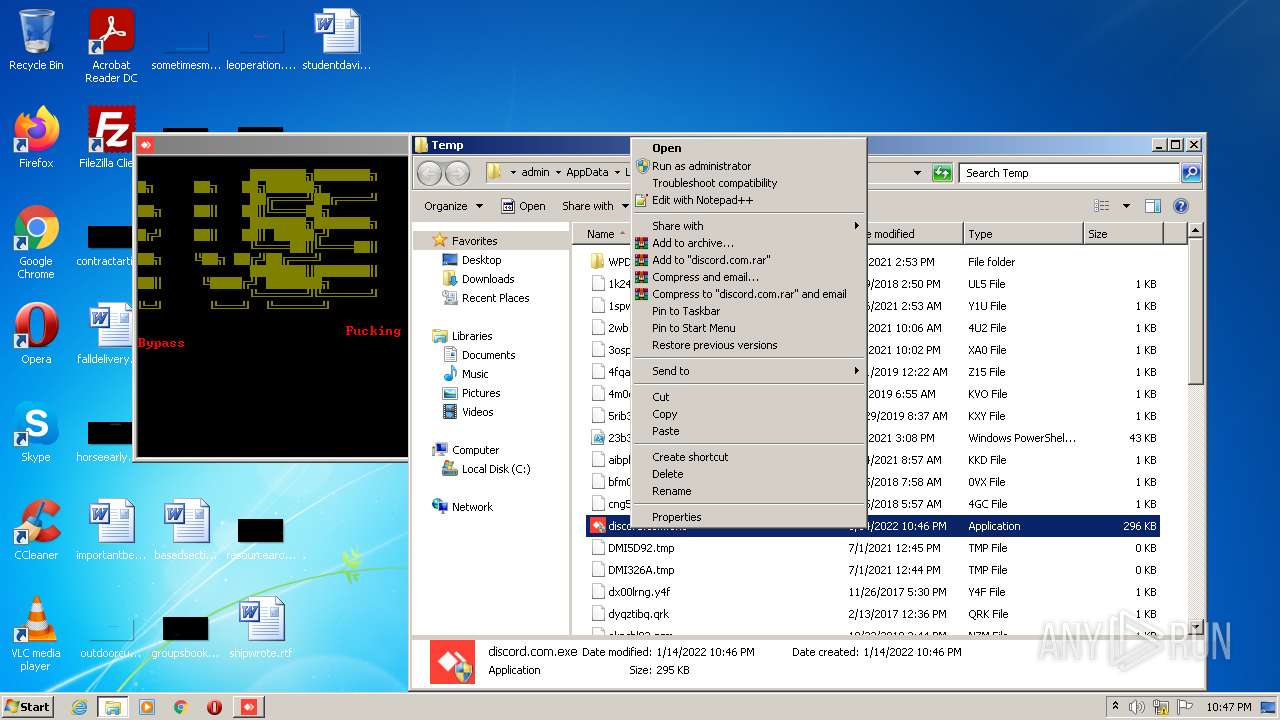
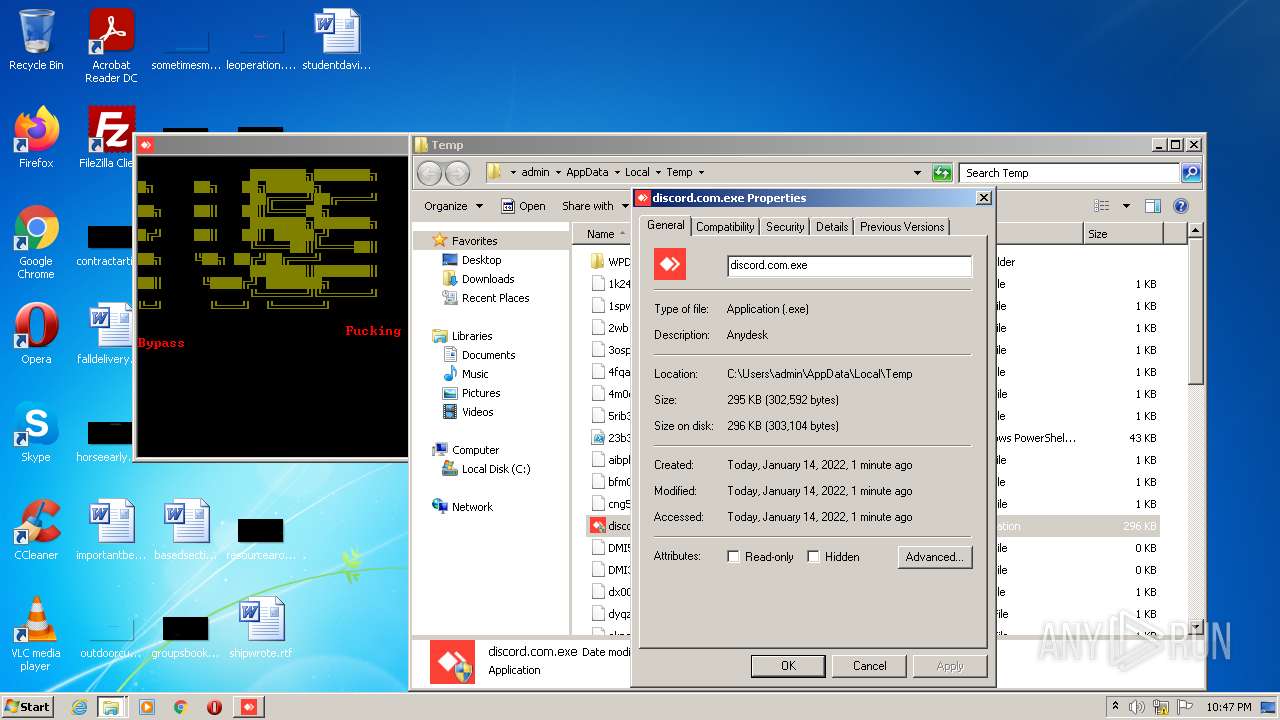
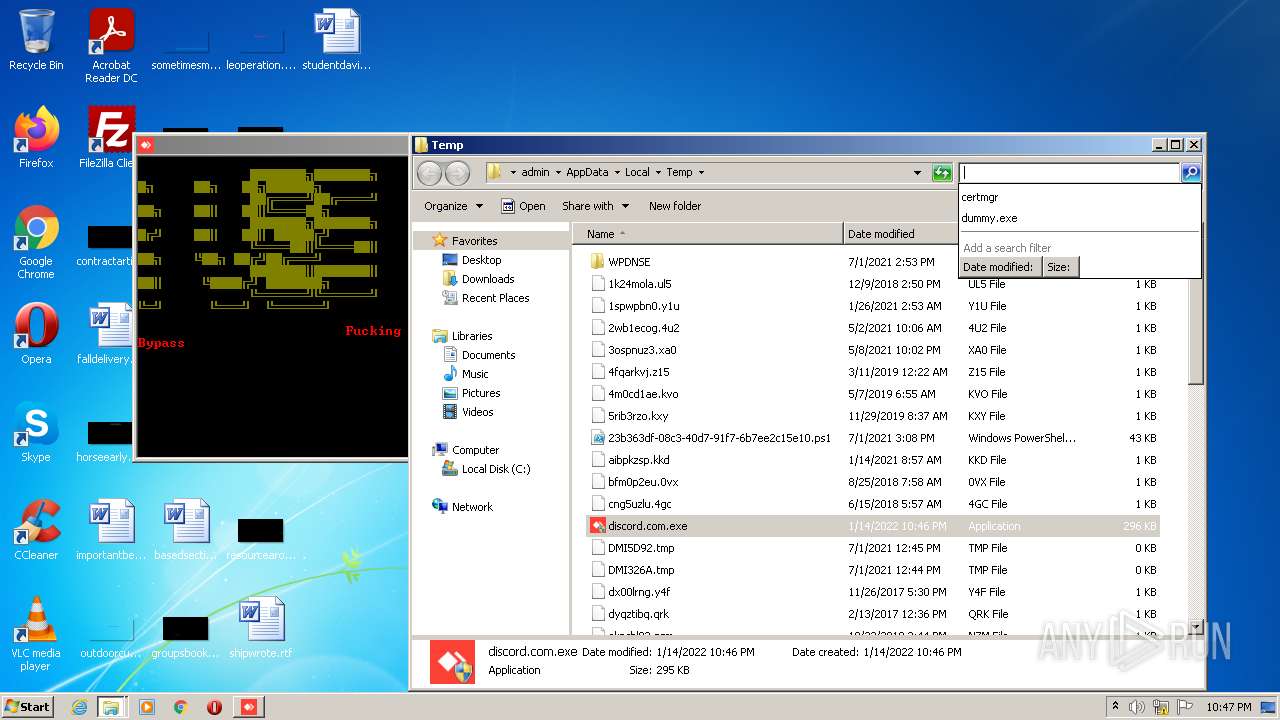
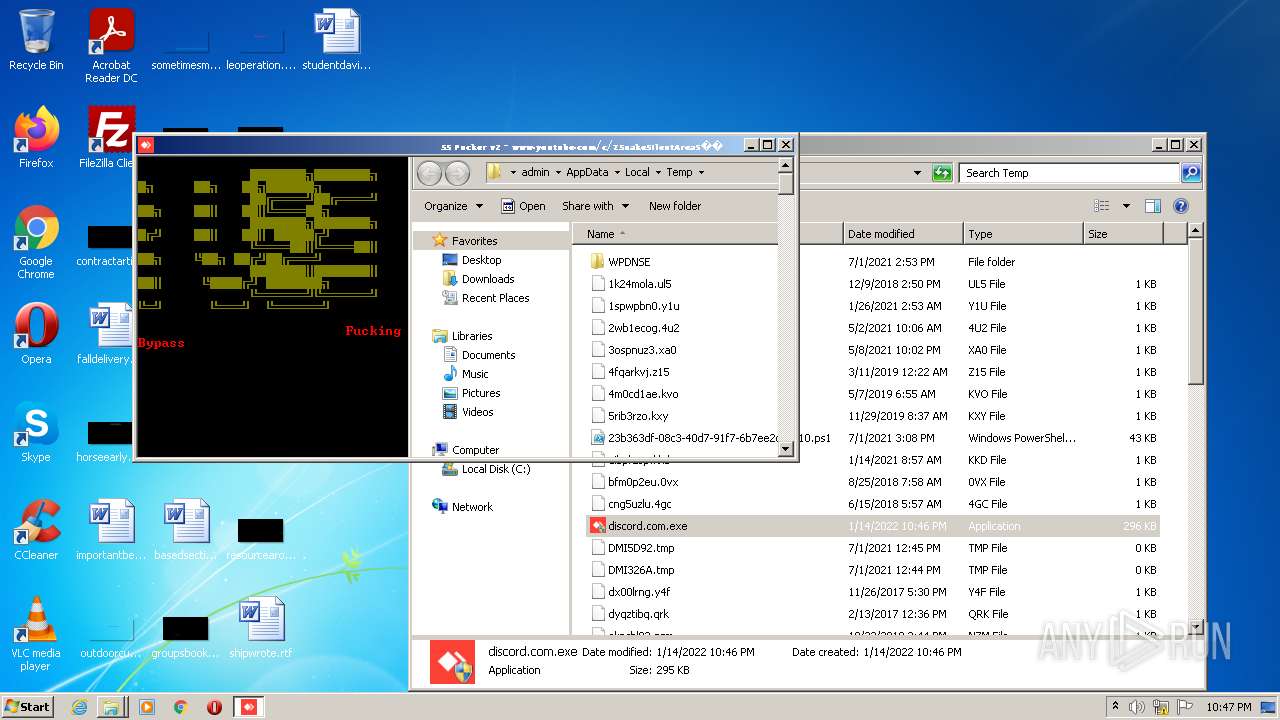
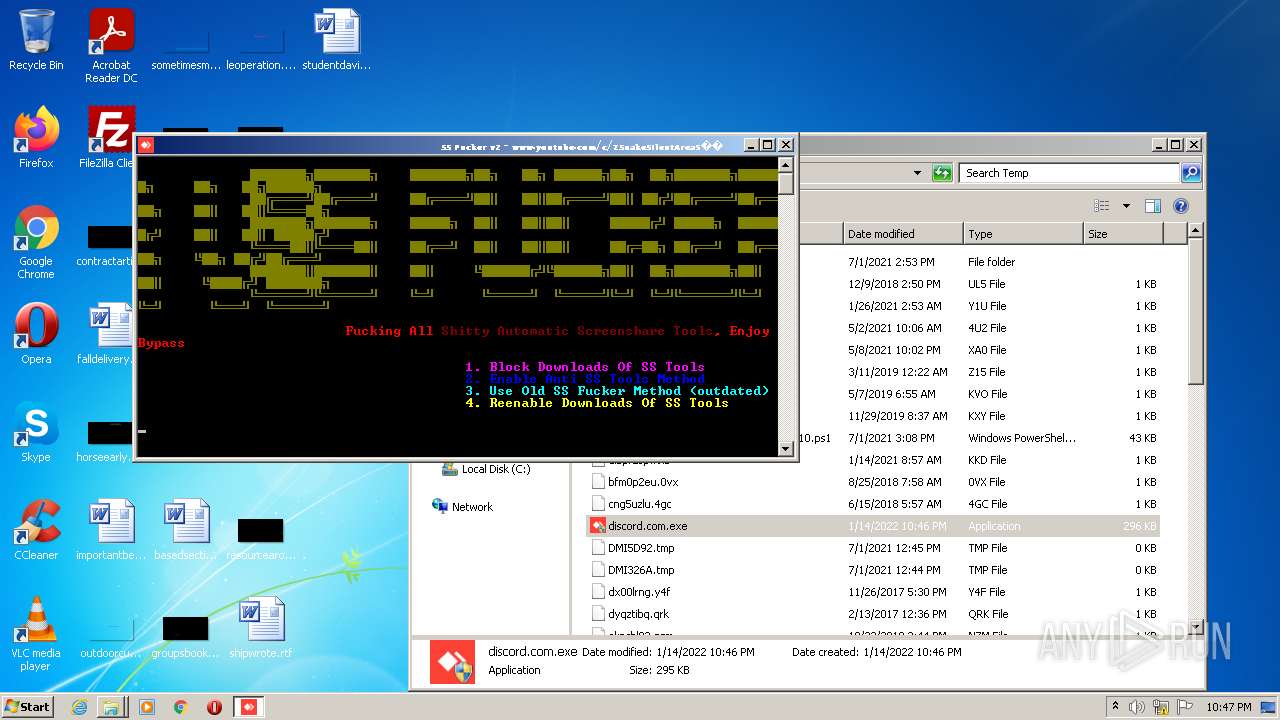
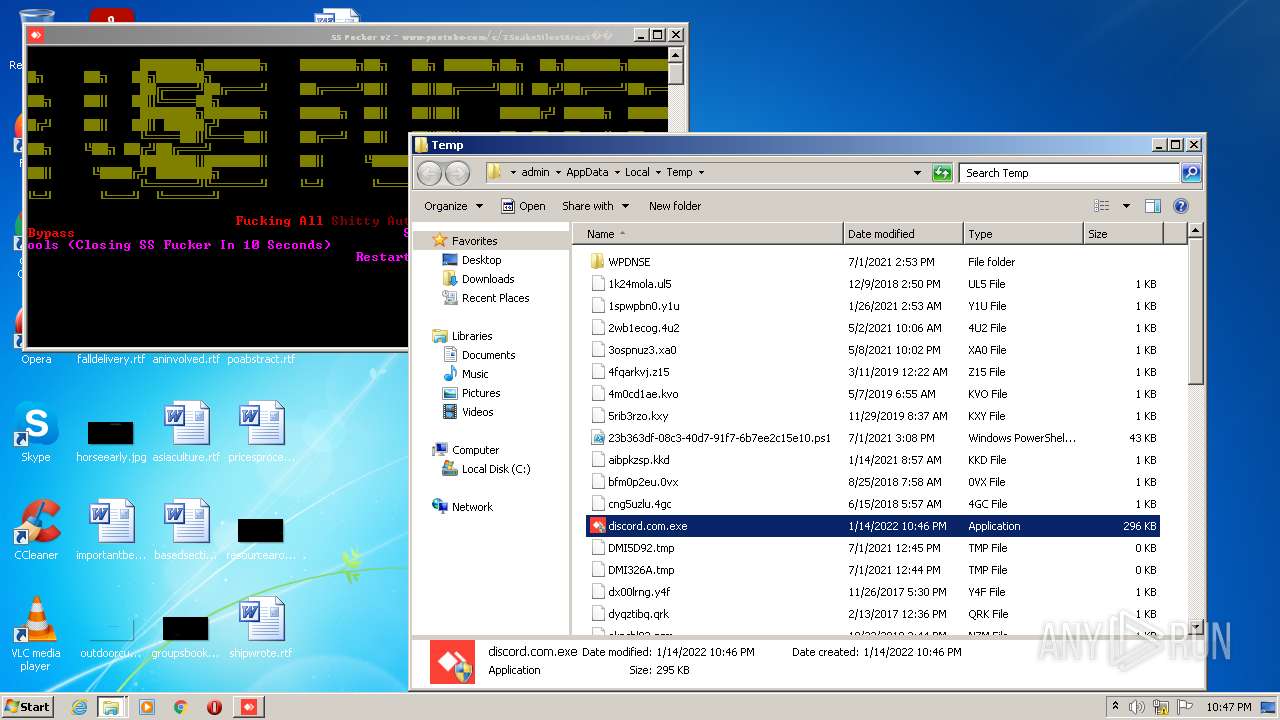
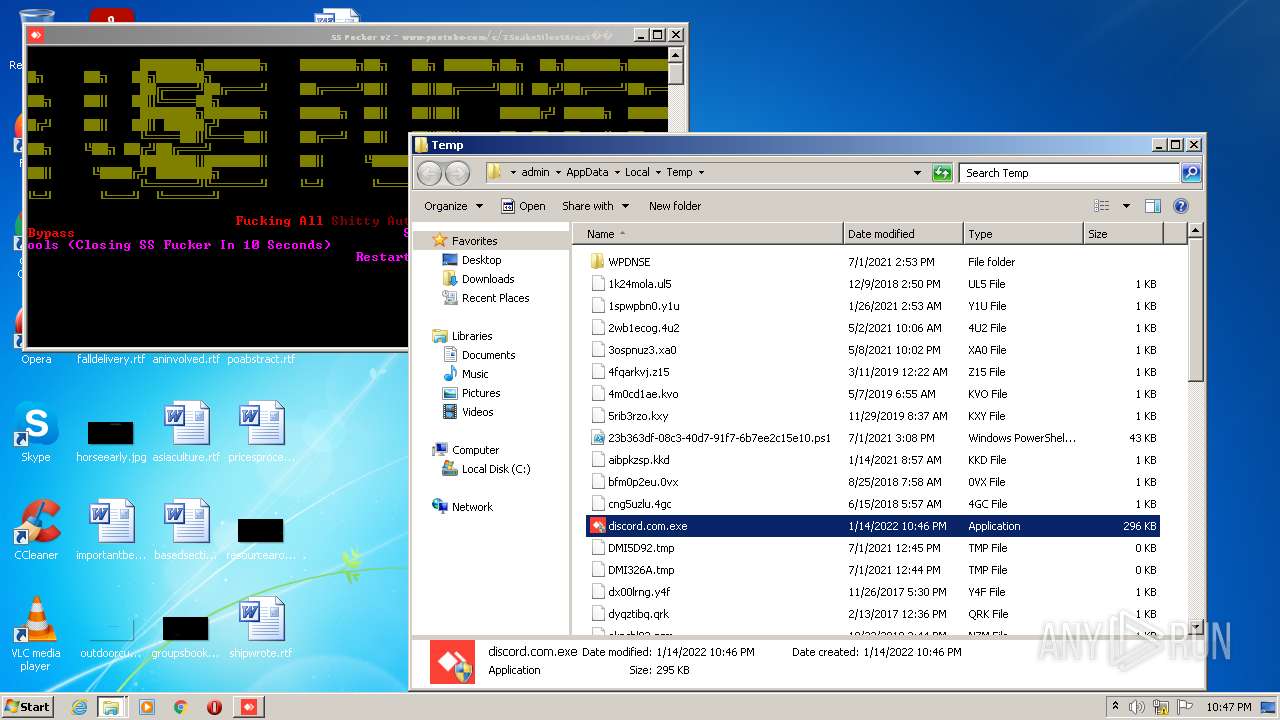
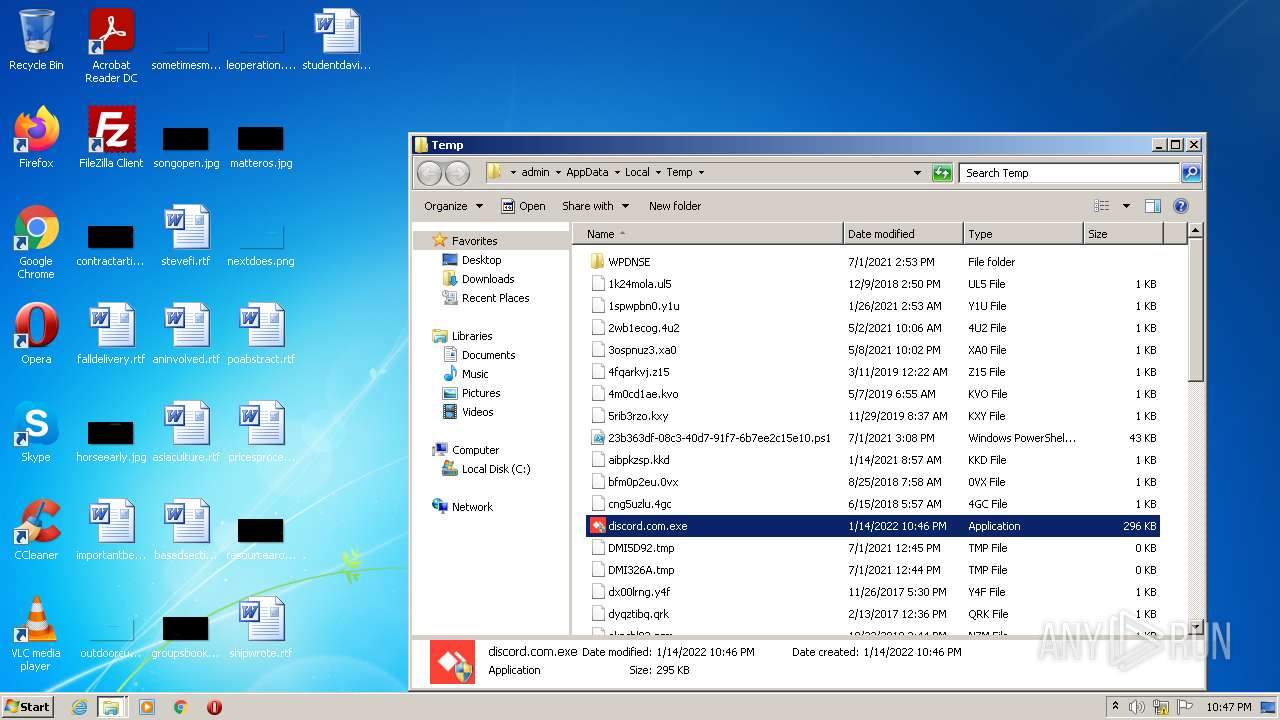
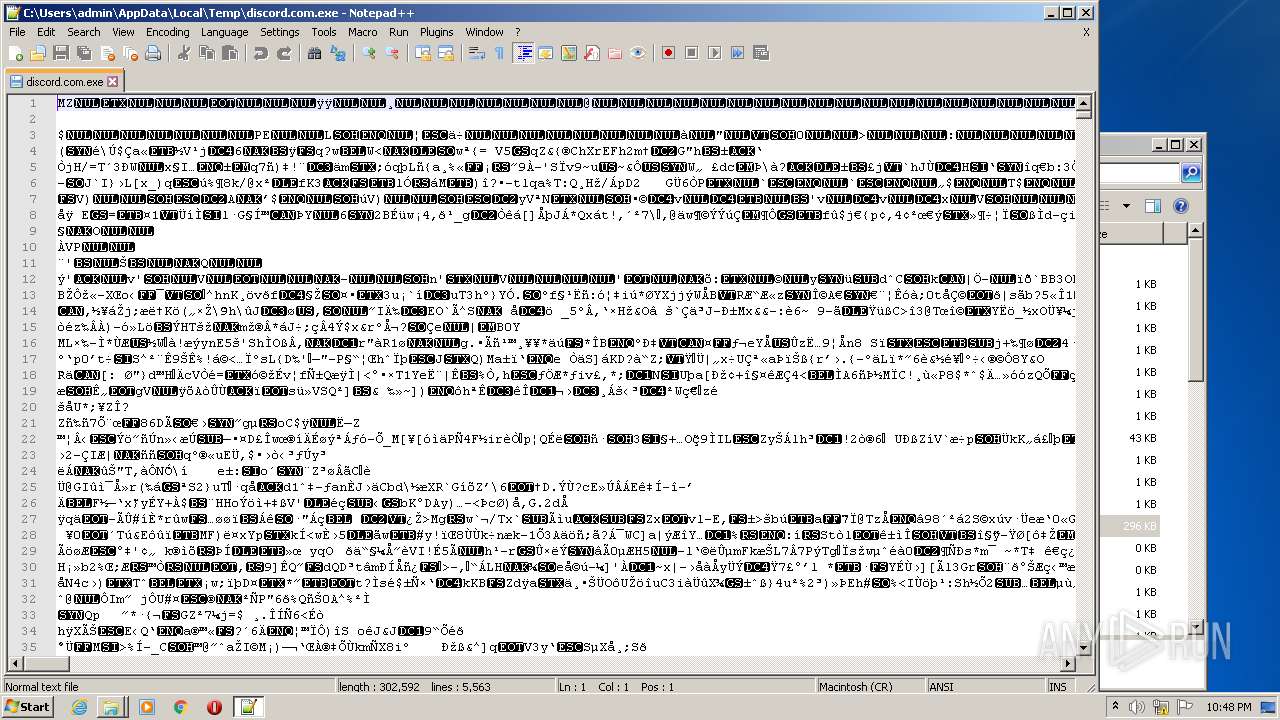
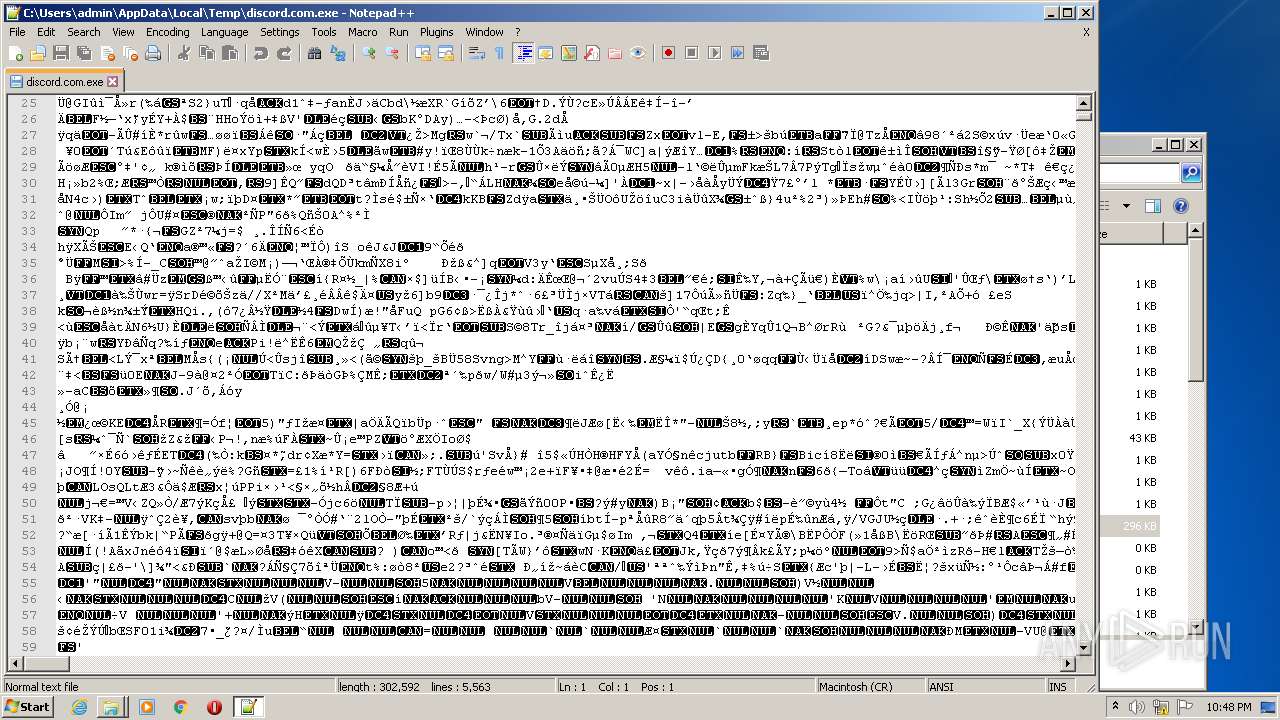
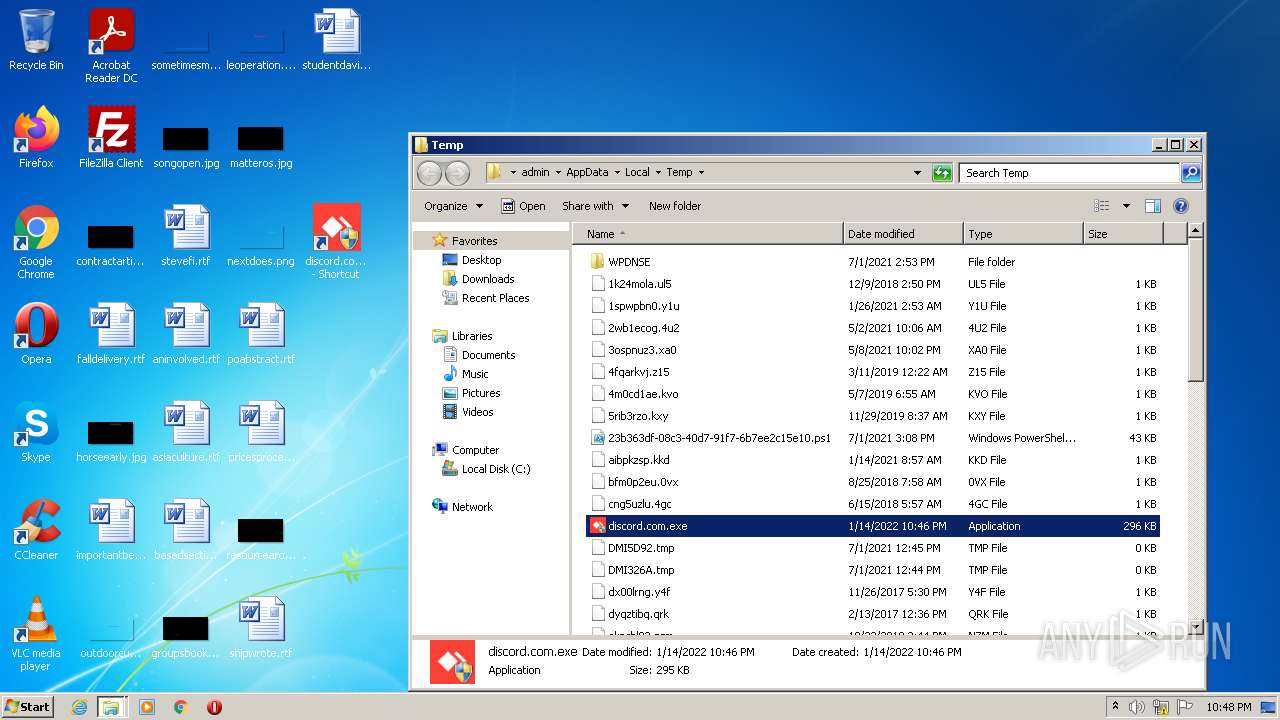
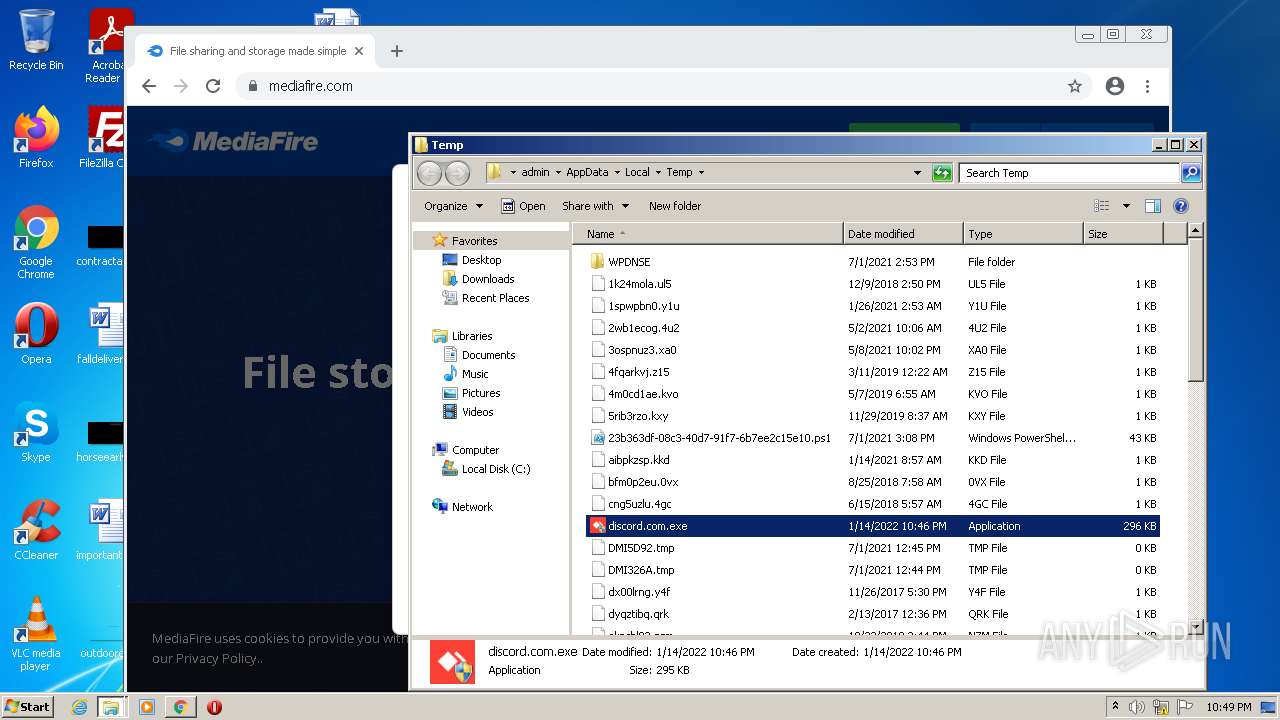
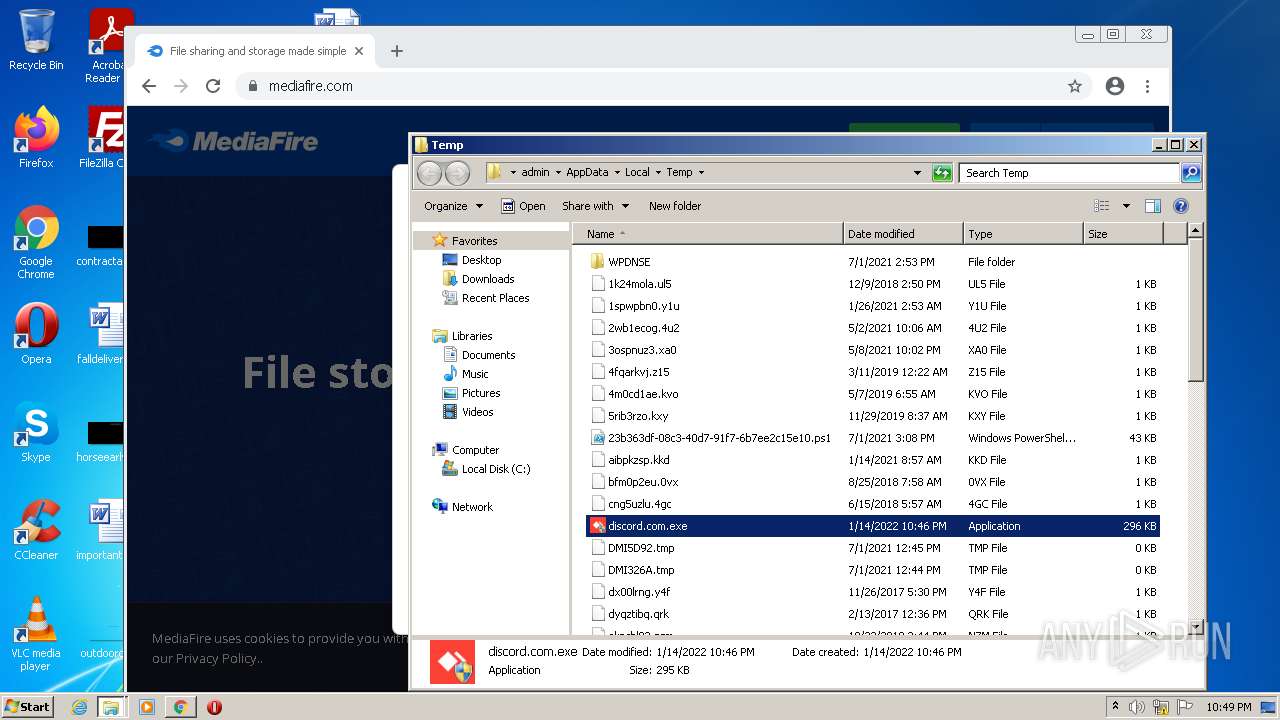
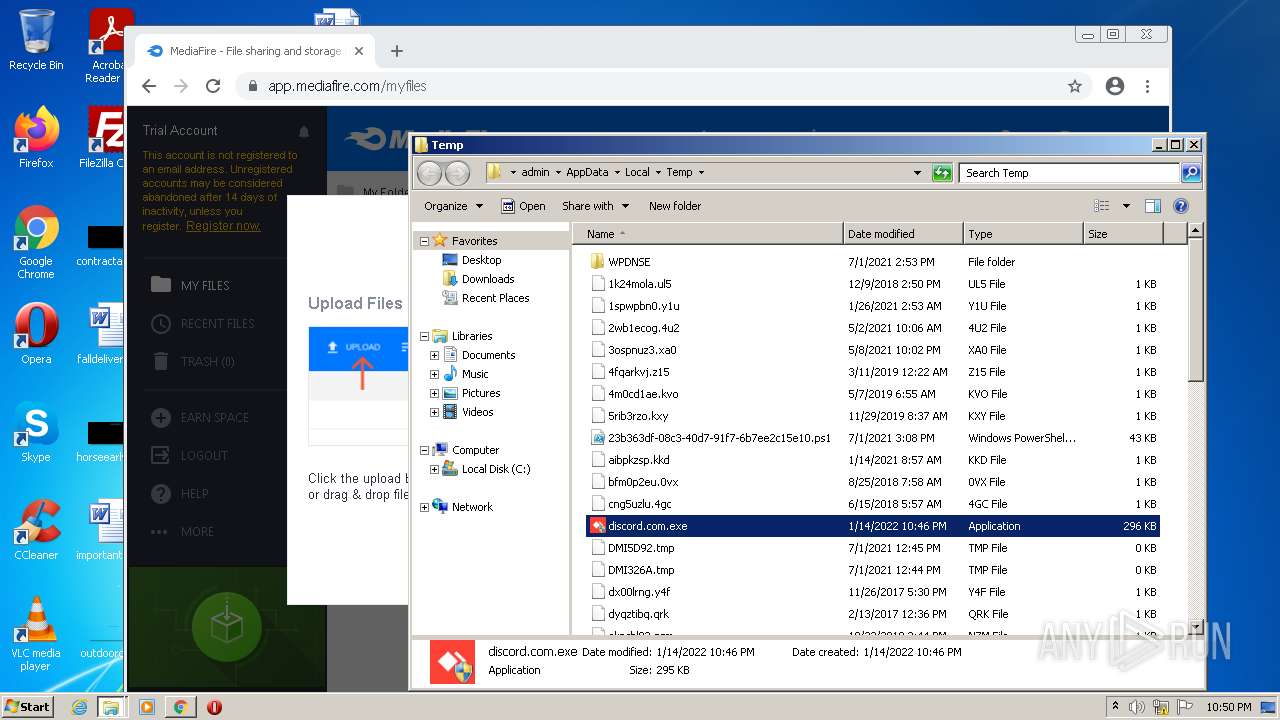
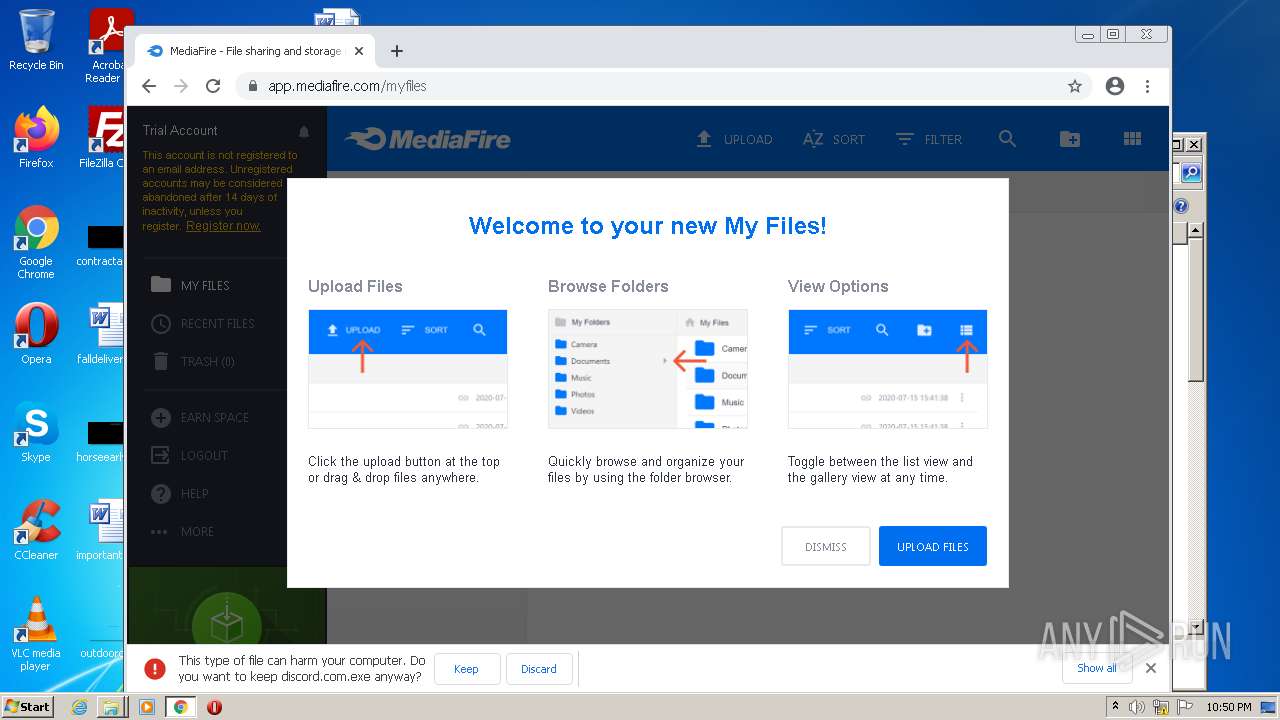
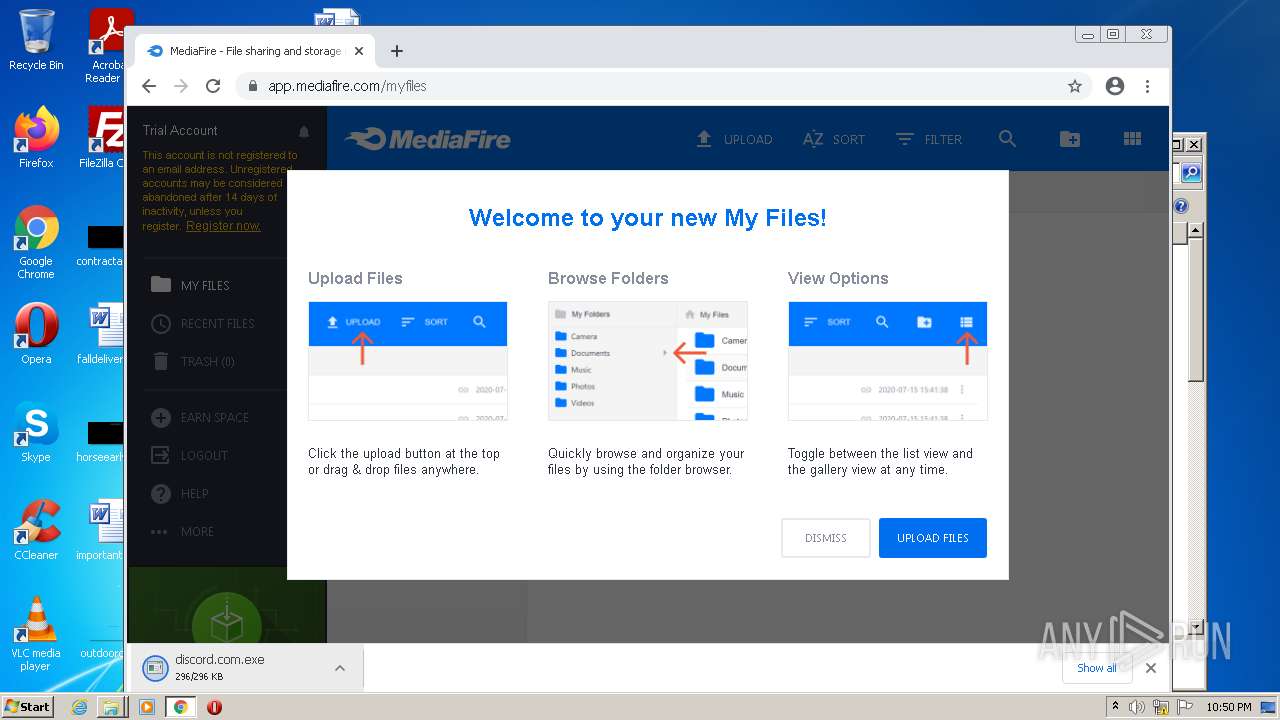
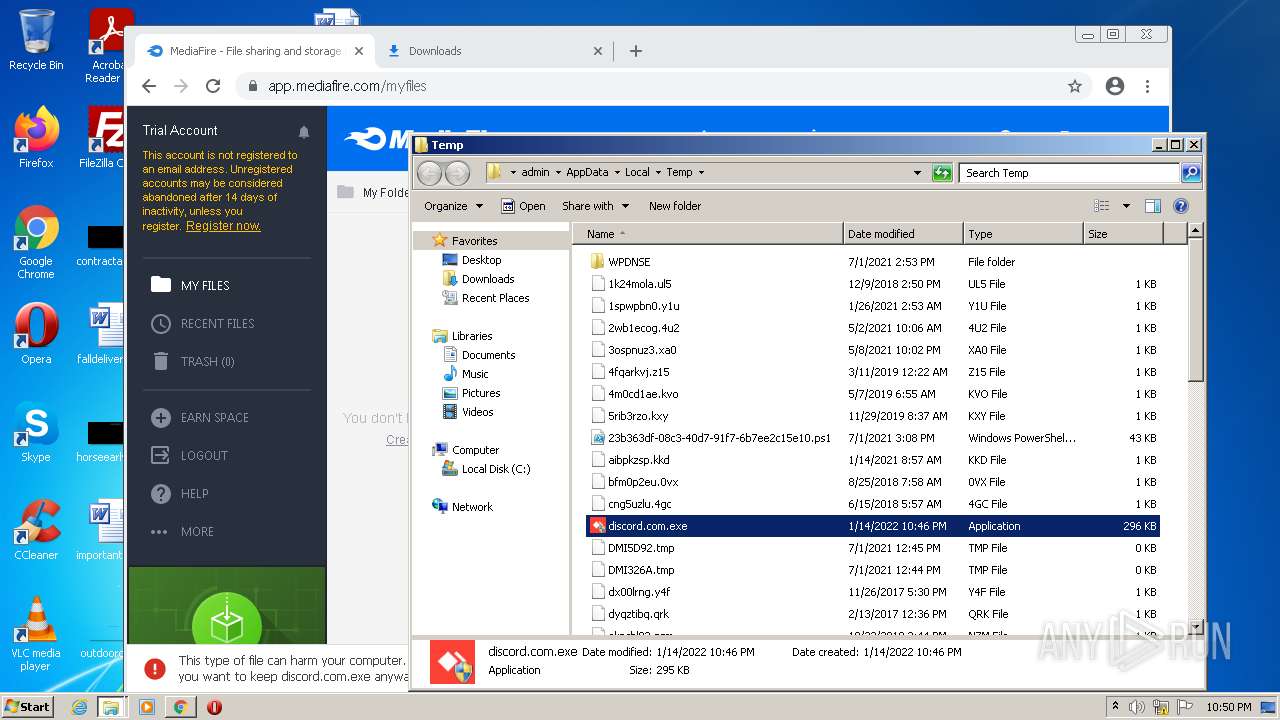
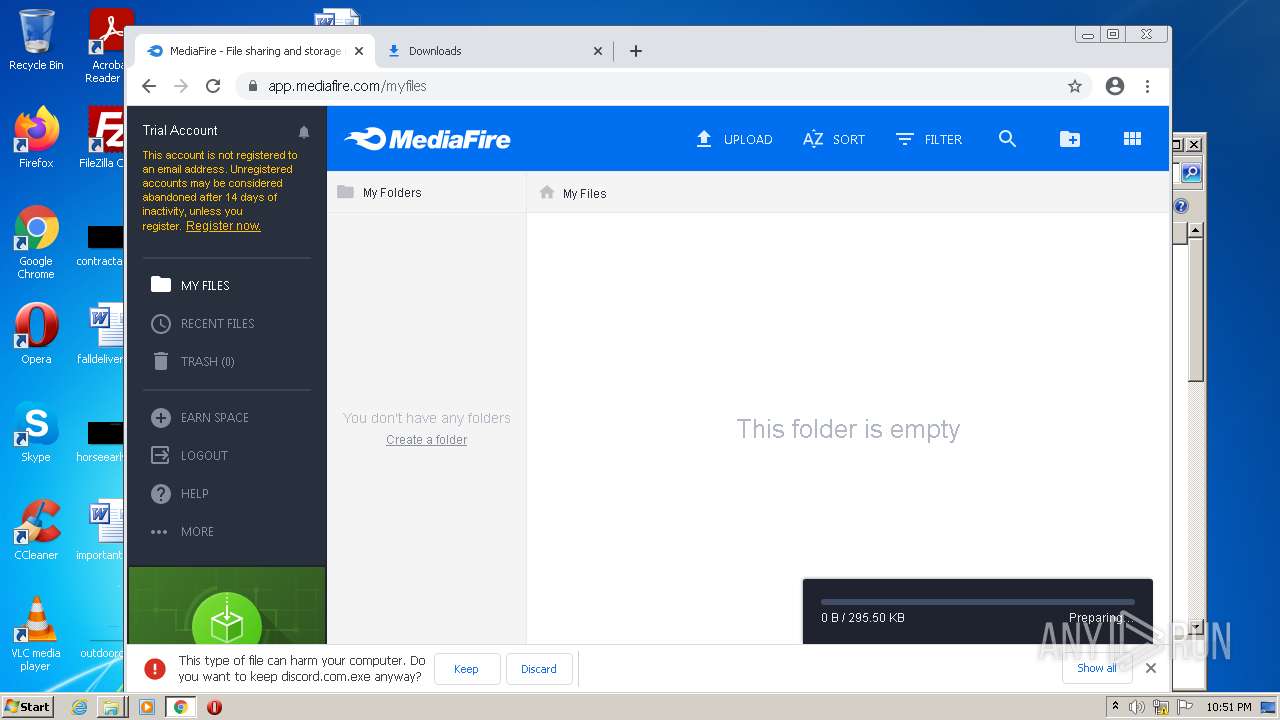
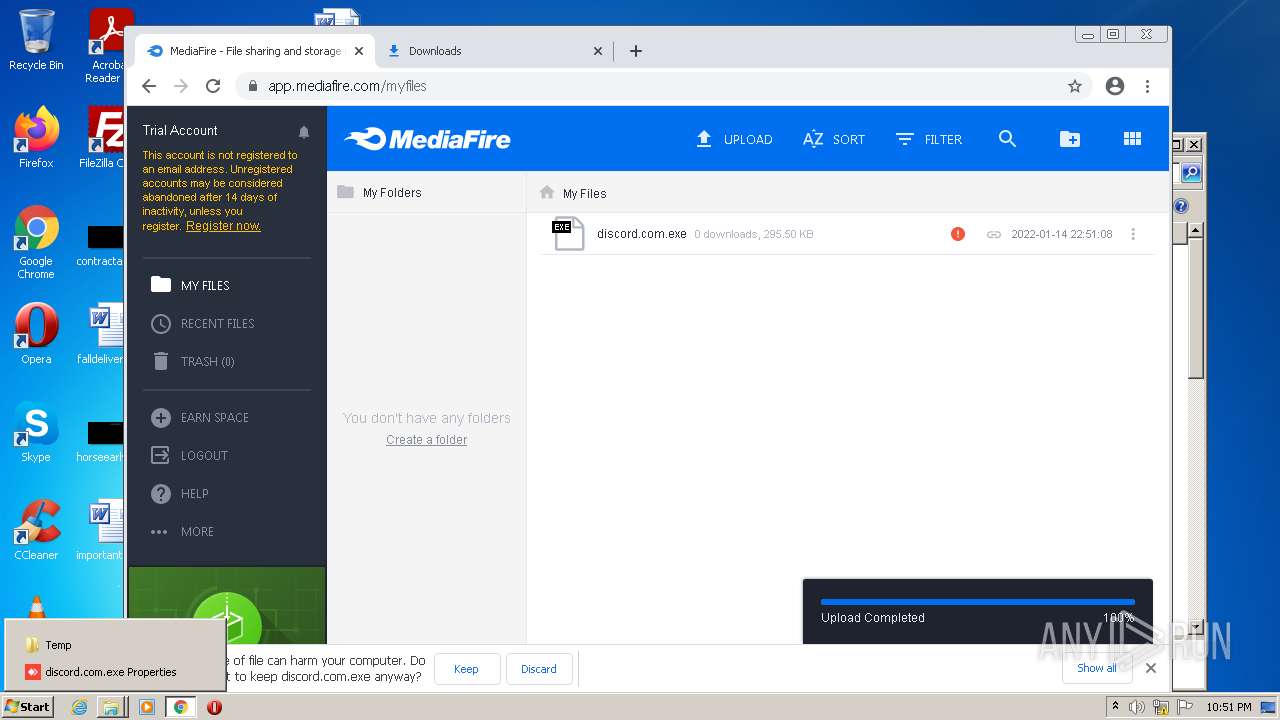
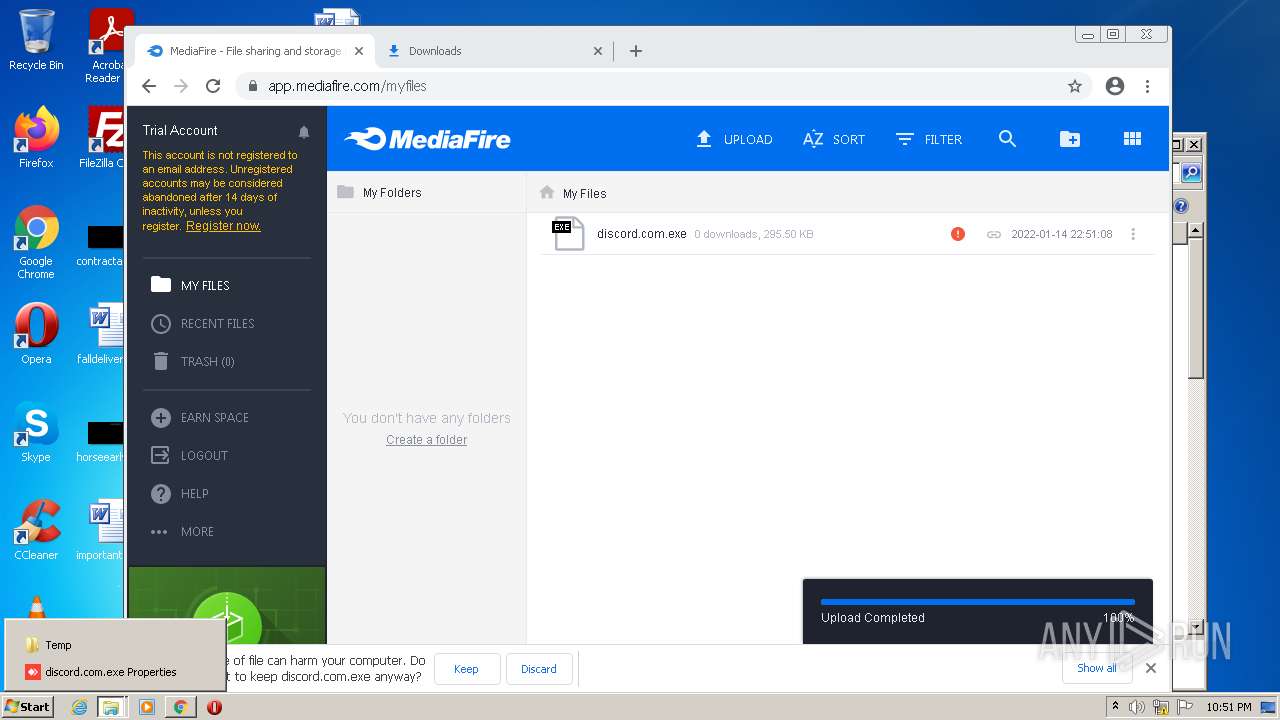
| File name: | discord.com |
| Full analysis: | https://app.any.run/tasks/45f65d4e-f6e6-4c76-b625-6529526c8982 |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2022, 22:46:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | E125688A2B58ACE841909B7F677D9B4A |
| SHA1: | 0102D0334DF047AB902C3621B4477F735A945C79 |
| SHA256: | 4F5CD89D62D08959C1A0AF30B2658DCA3D8FA462397E5260F6A62522EA9B6F33 |
| SSDEEP: | 6144:6LoXJ4Dc8zcpMxkhg/YMoEqbGb/waIwkJ/3+1PZTIKBBd:6Lrc6mIYQzIwkJ/CTd |
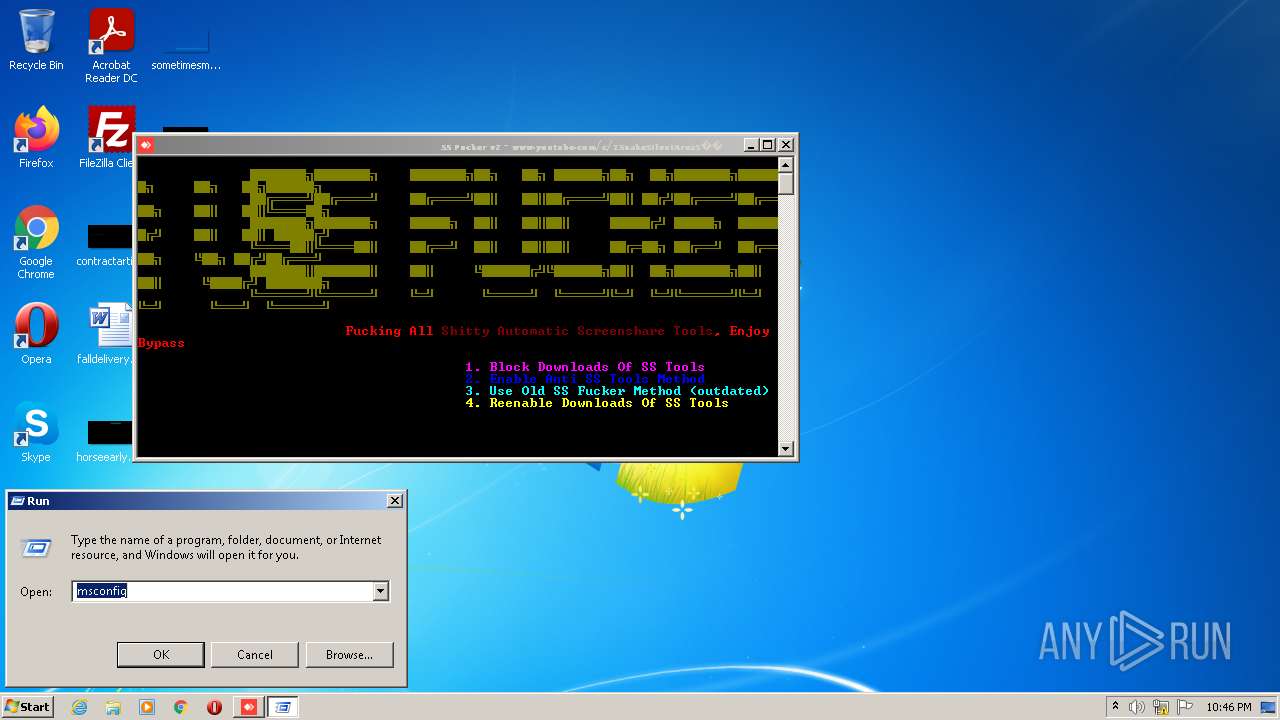
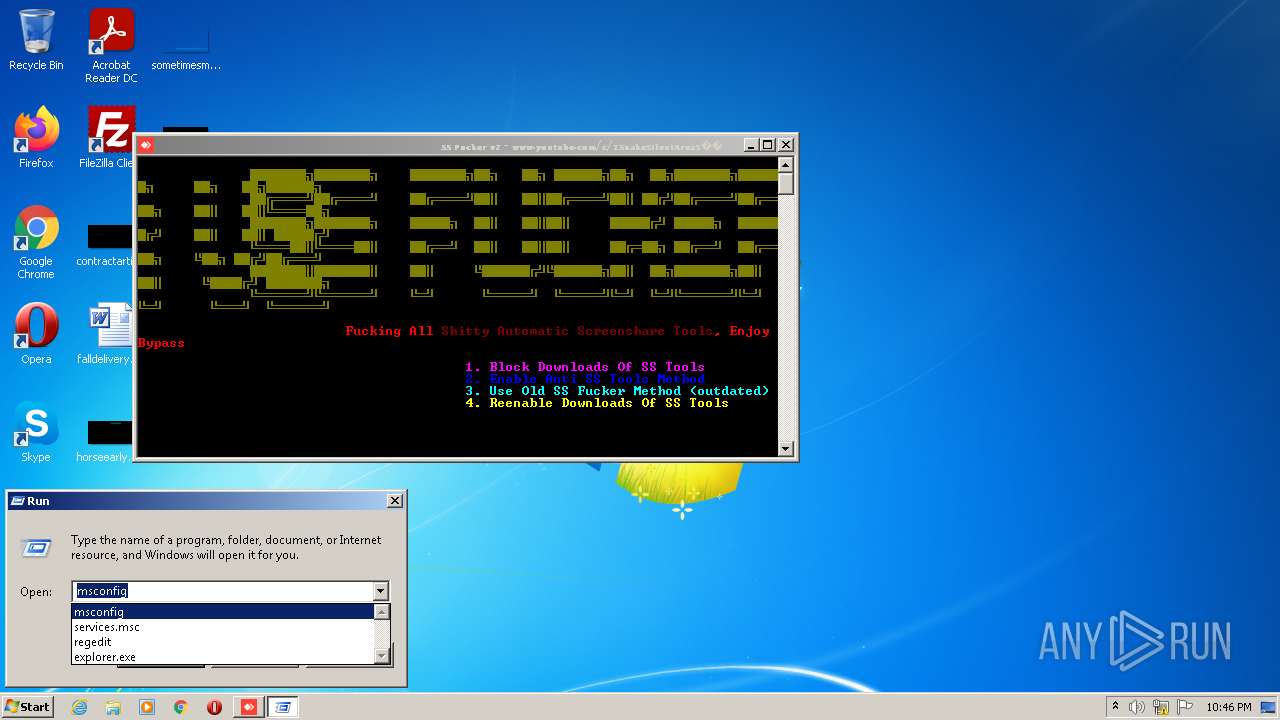
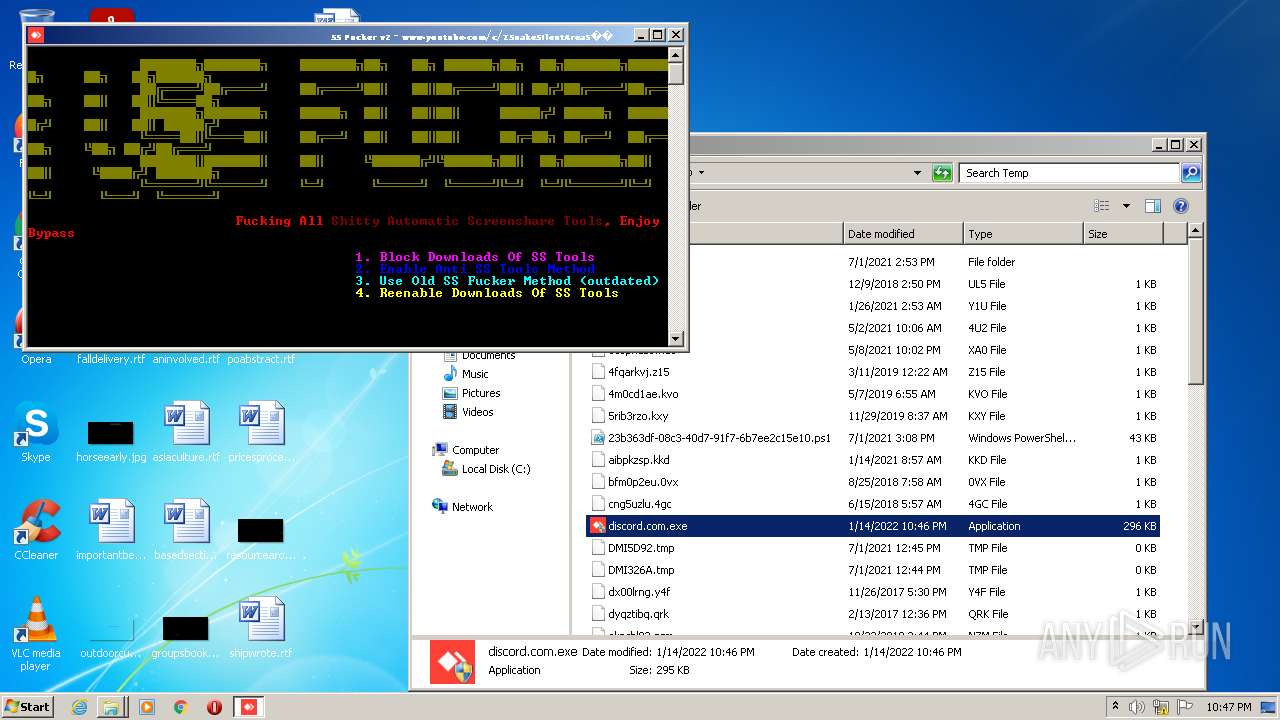
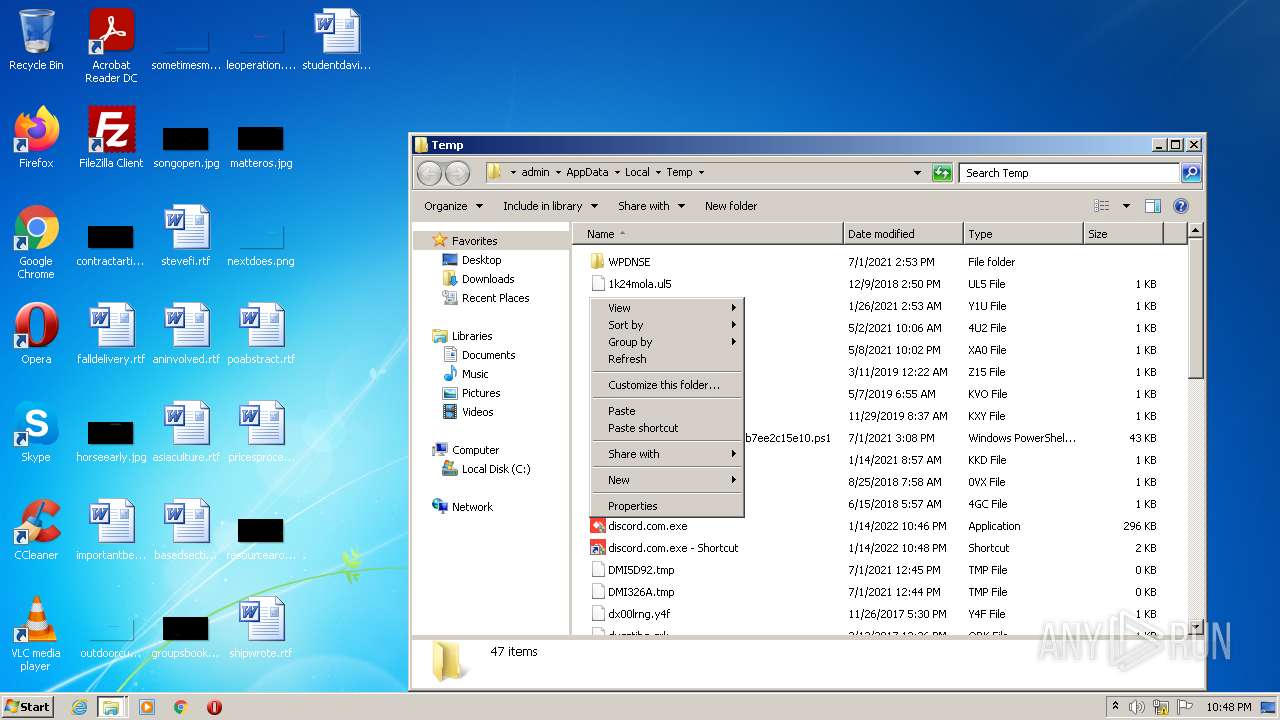
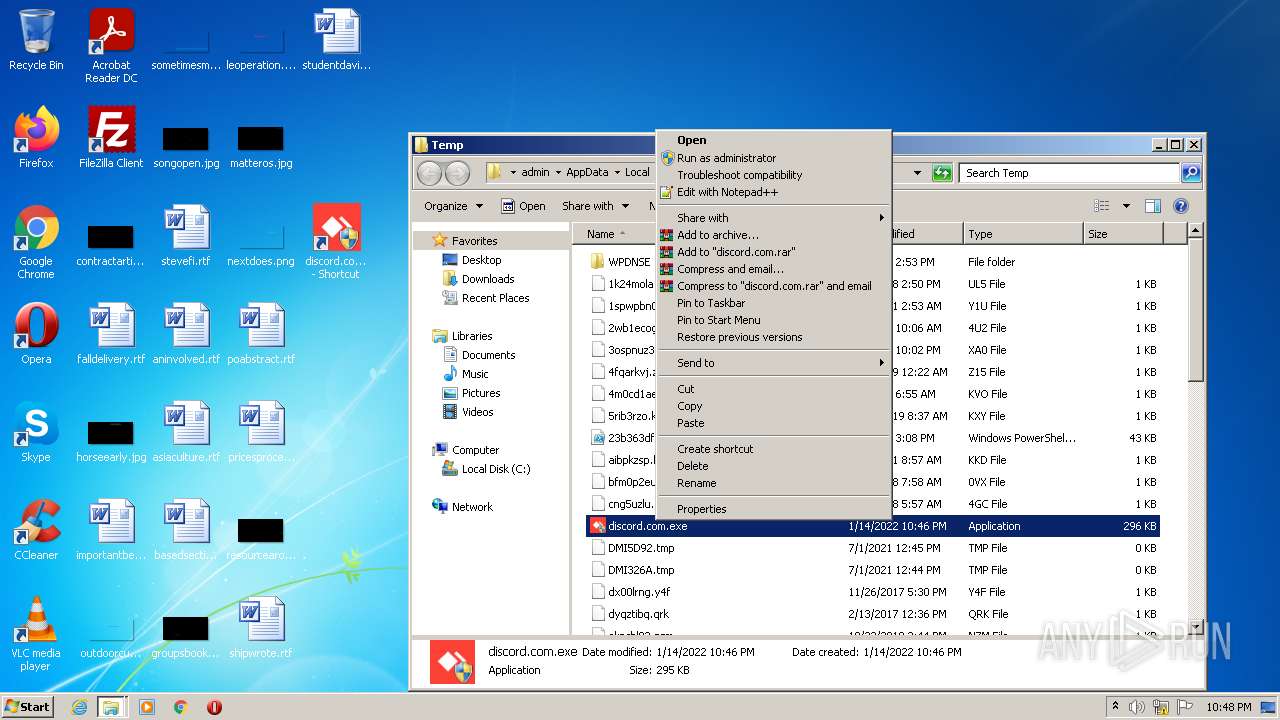
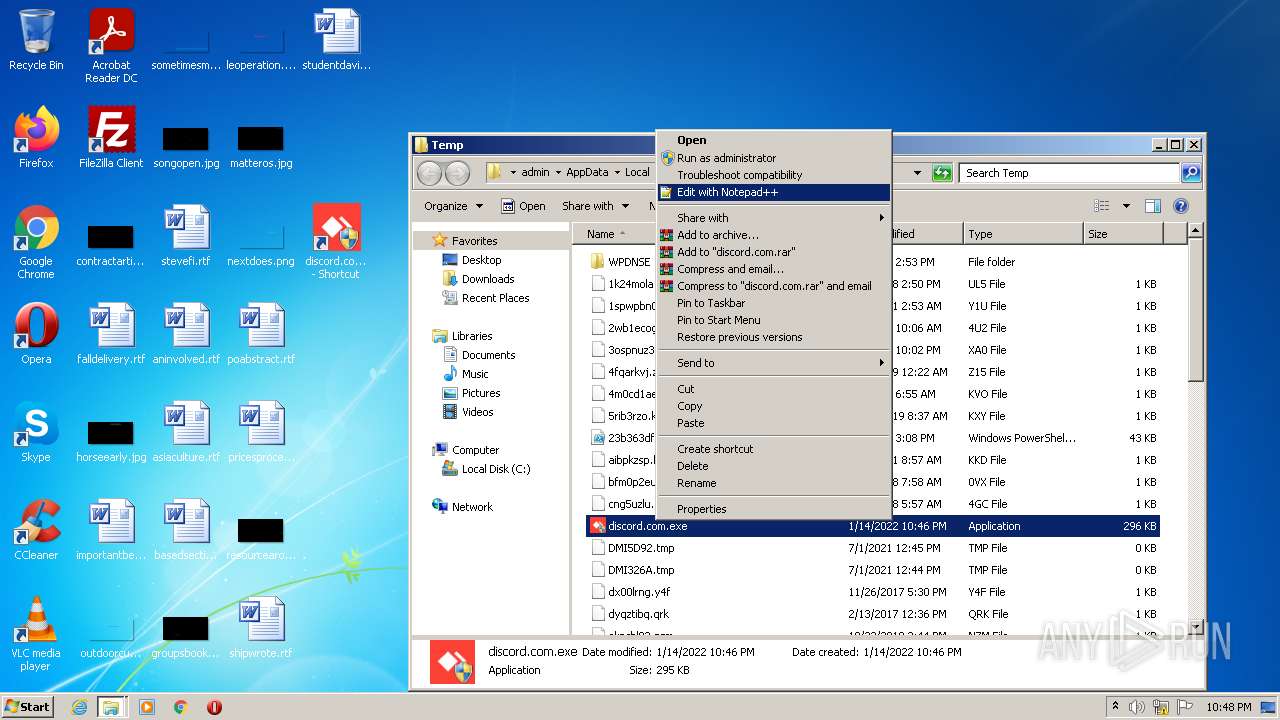
MALICIOUS
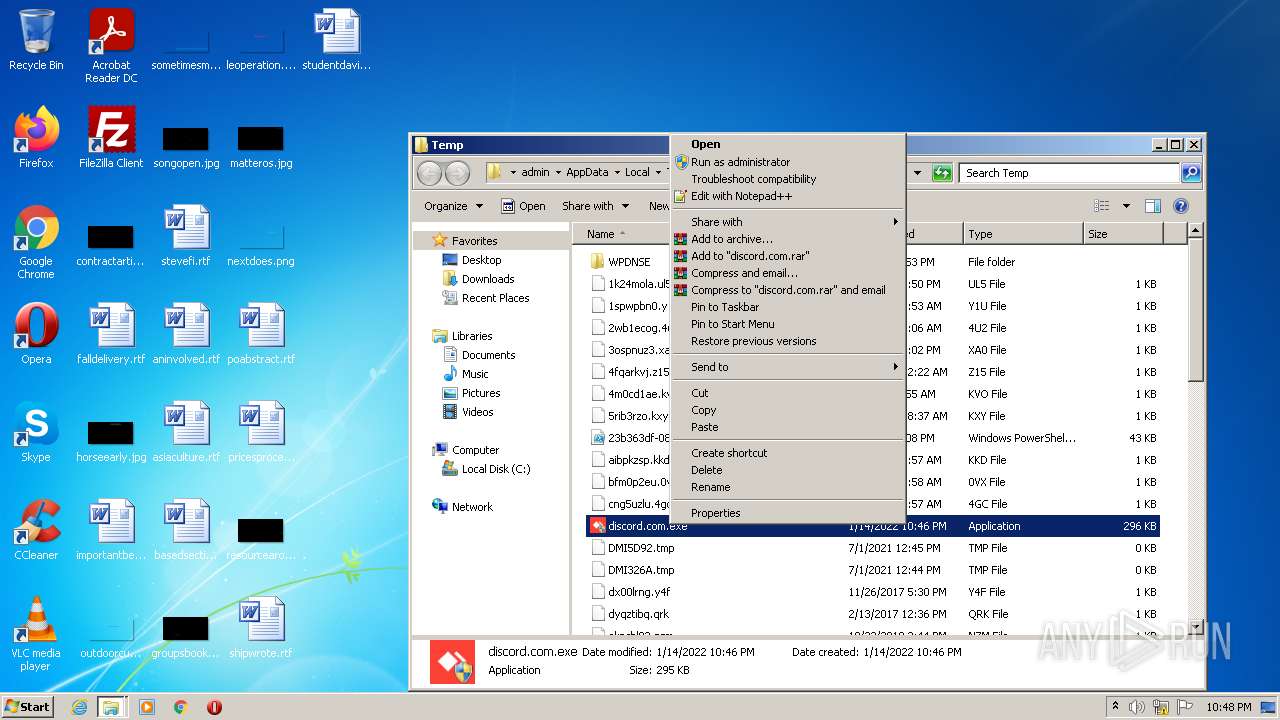
Runs app for hidden code execution
- discord.com.exe (PID: 276)
Starts NET.EXE for service management
- cmd.exe (PID: 1364)
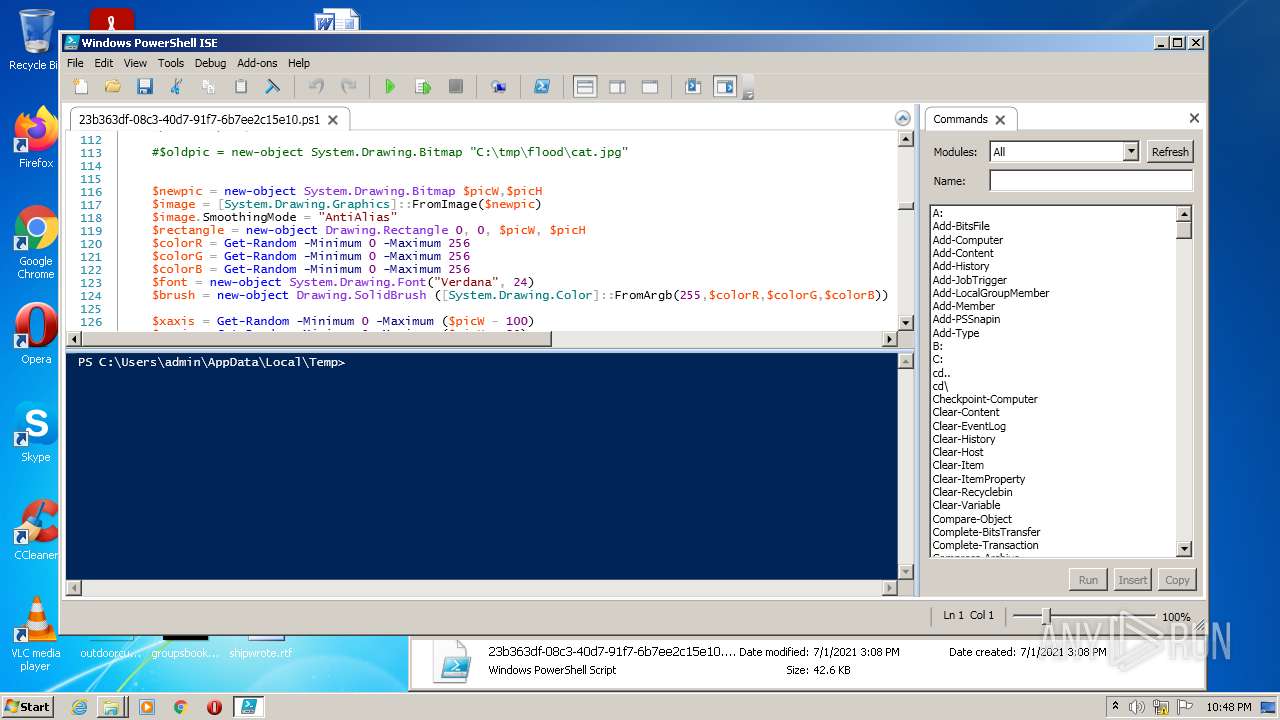
SUSPICIOUS
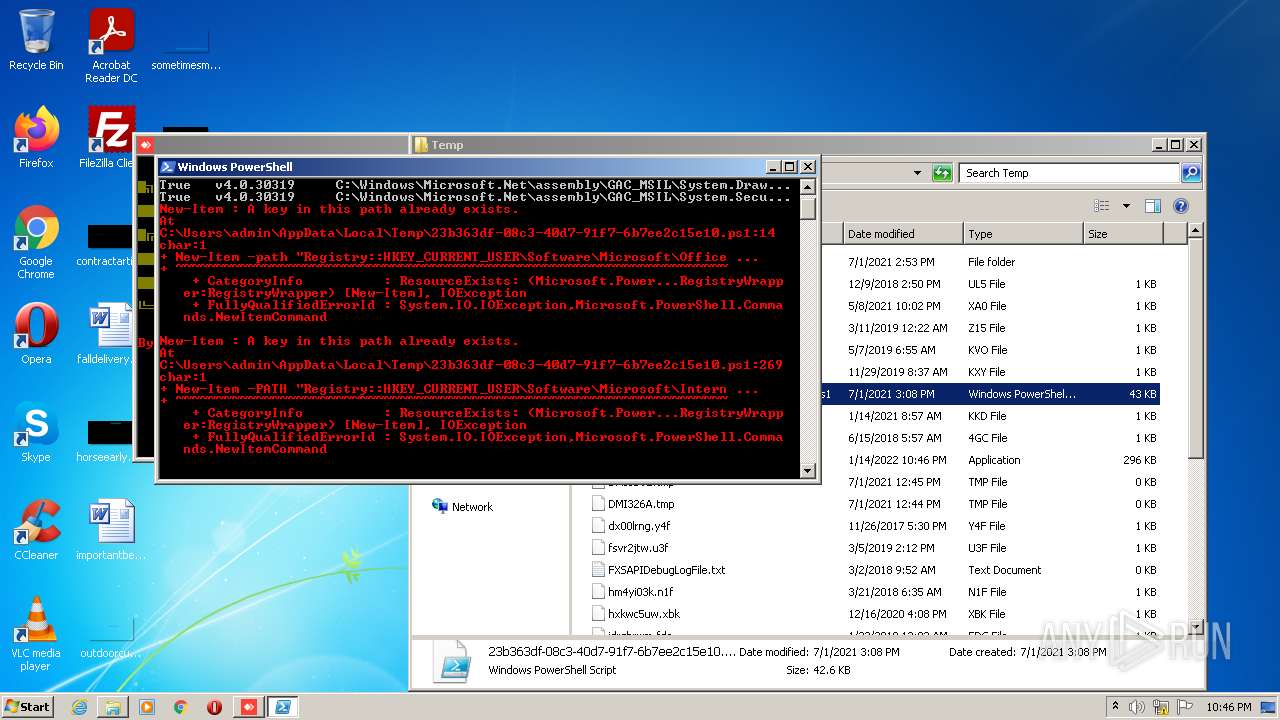
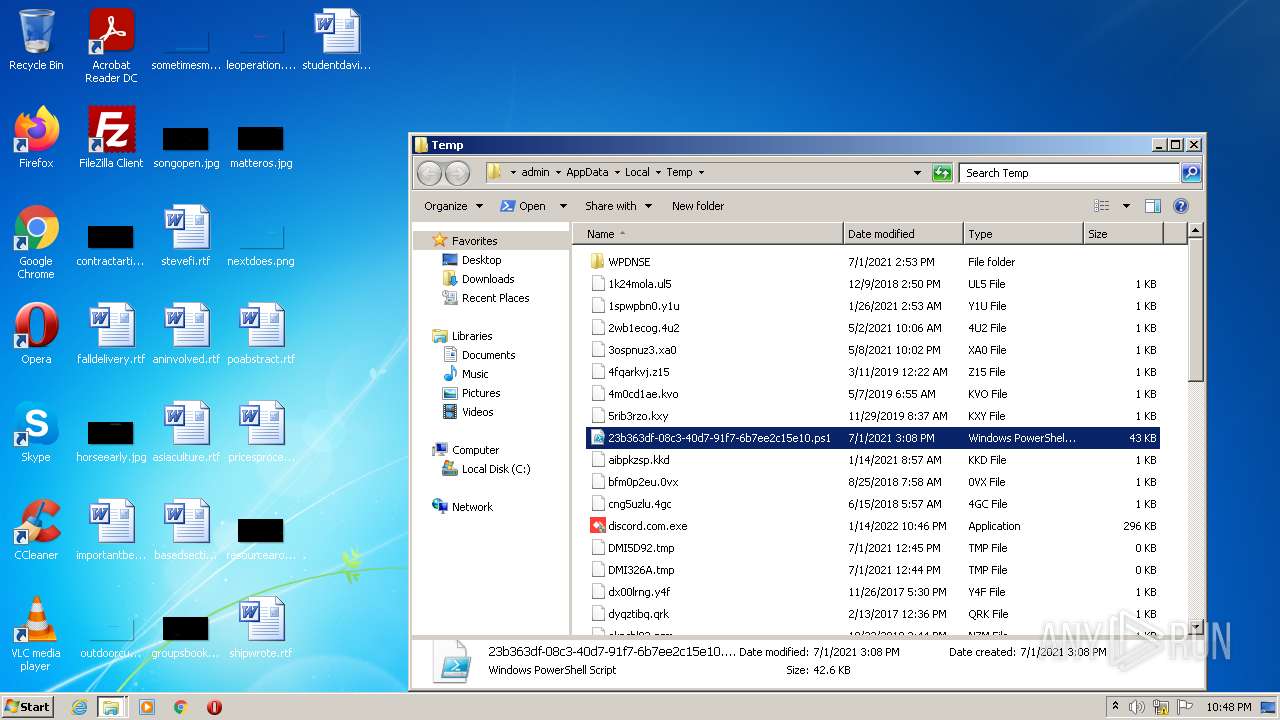
PowerShell script executed
- powershell.exe (PID: 3688)
Reads the computer name
- discord.com.exe (PID: 3340)
- powershell.exe (PID: 3688)
- discord.com.exe (PID: 276)
- powershell_ise.exe (PID: 3648)
Checks supported languages
- discord.com.exe (PID: 3340)
- powershell.exe (PID: 3688)
- cmd.exe (PID: 1364)
- discord.com.exe (PID: 276)
- powershell_ise.exe (PID: 3648)
- notepad++.exe (PID: 3044)
Reads the date of Windows installation
- powershell.exe (PID: 3688)
Starts CMD.EXE for commands execution
- discord.com.exe (PID: 276)
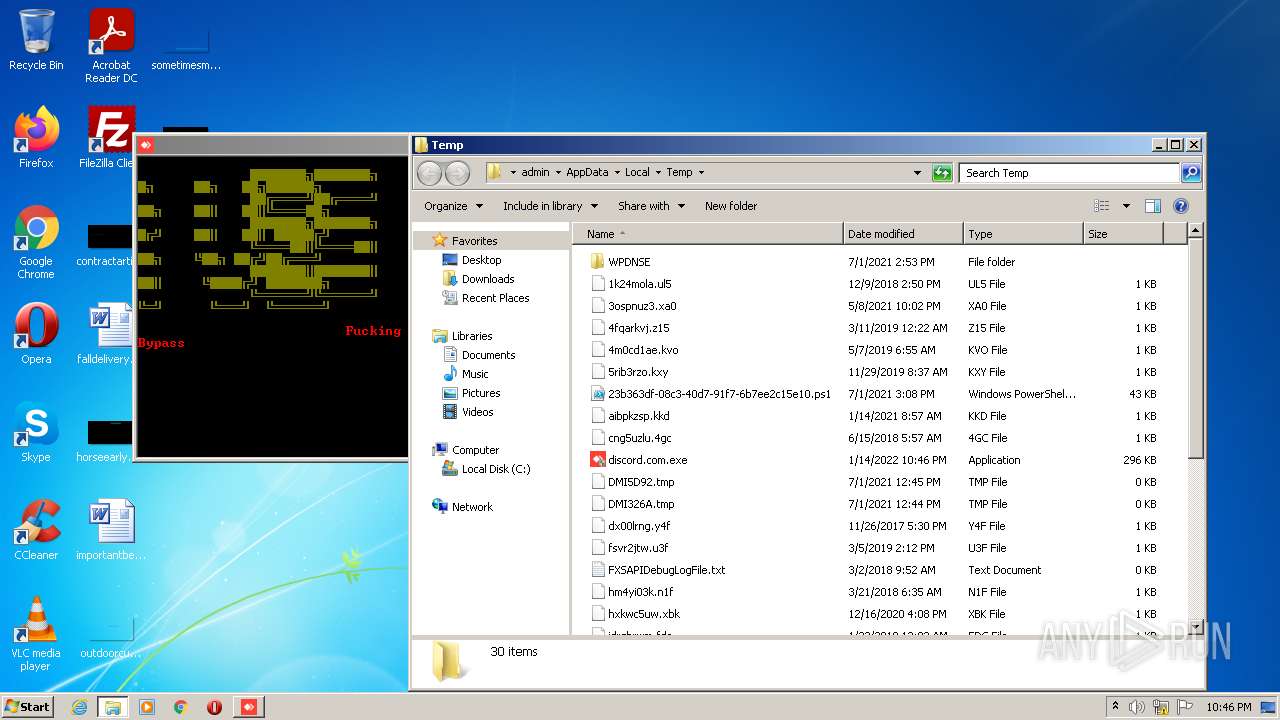
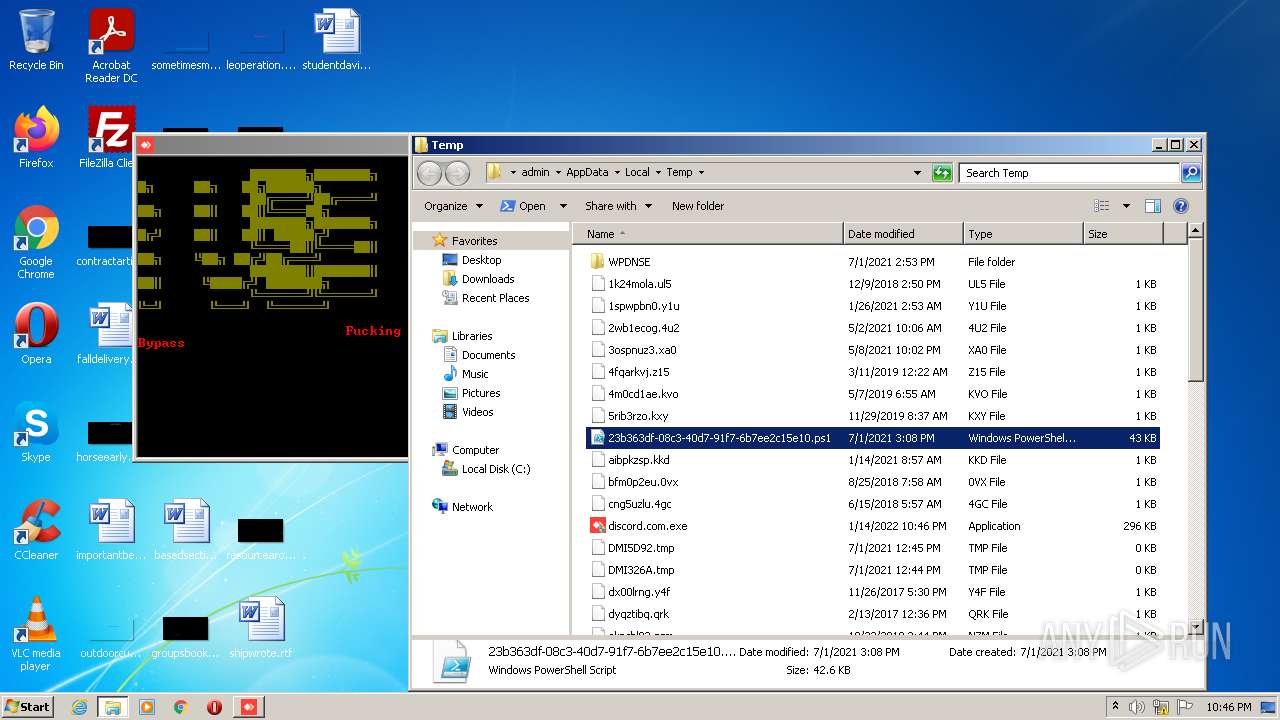
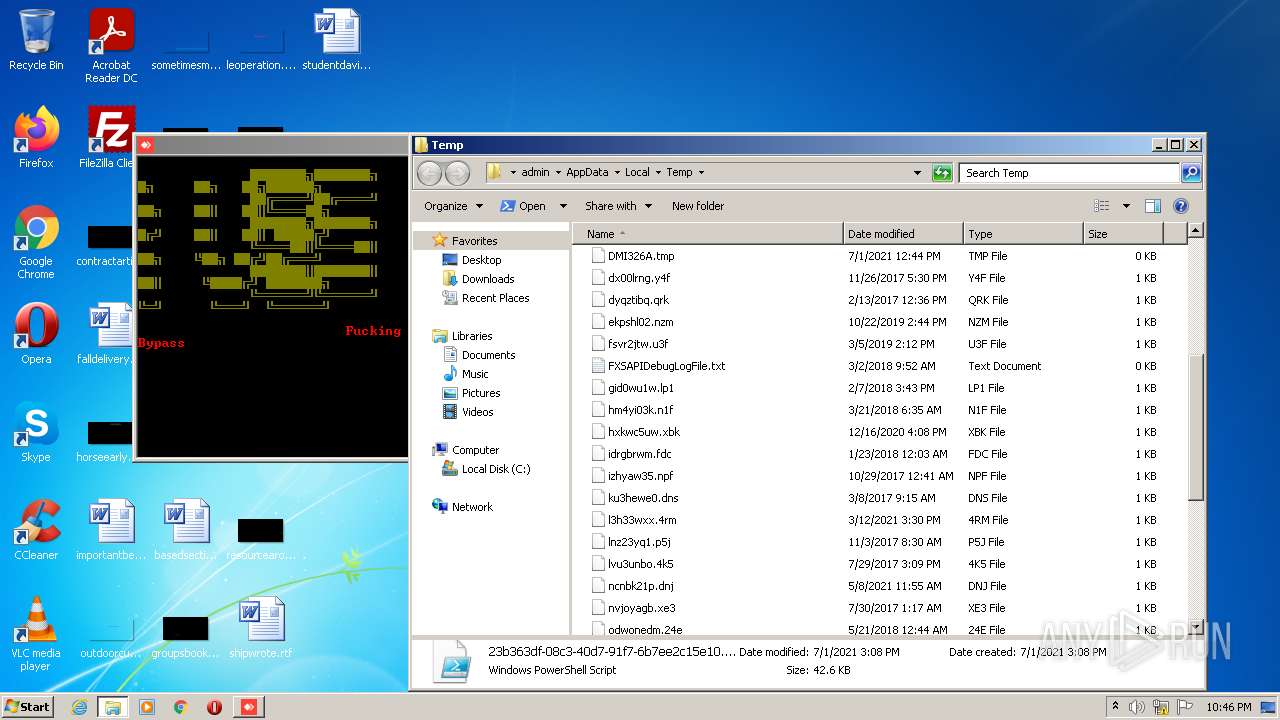
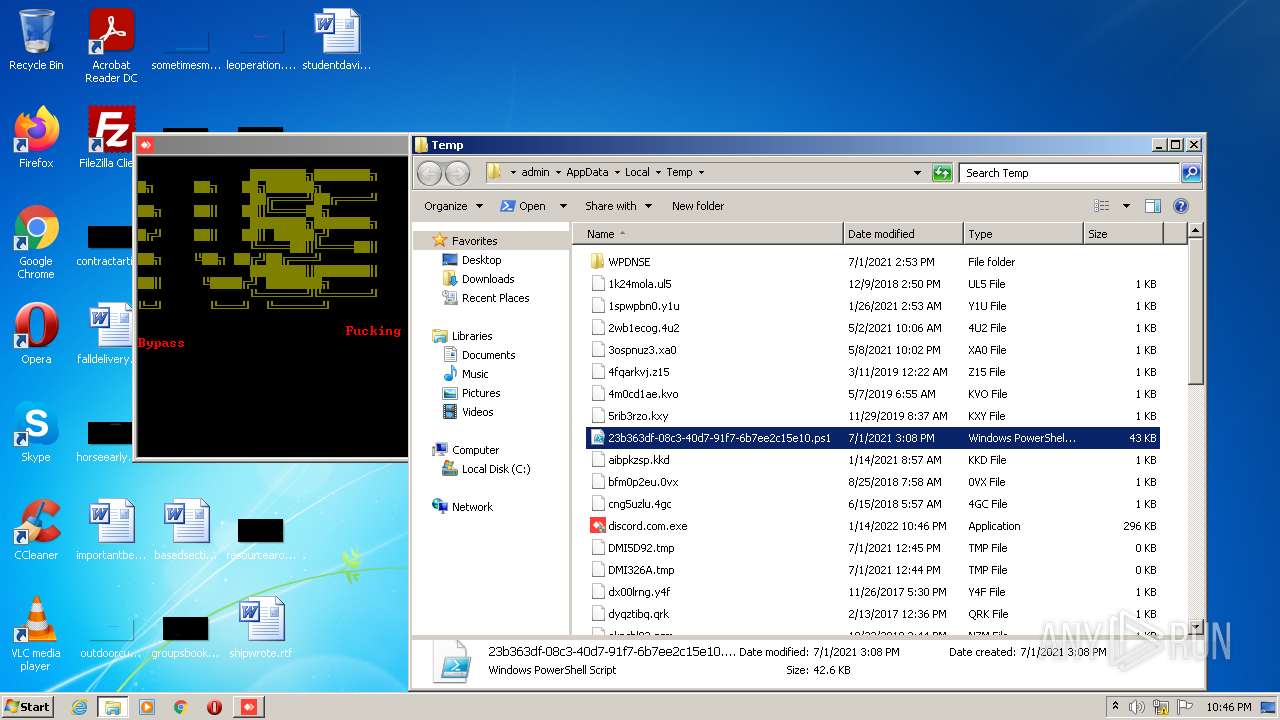
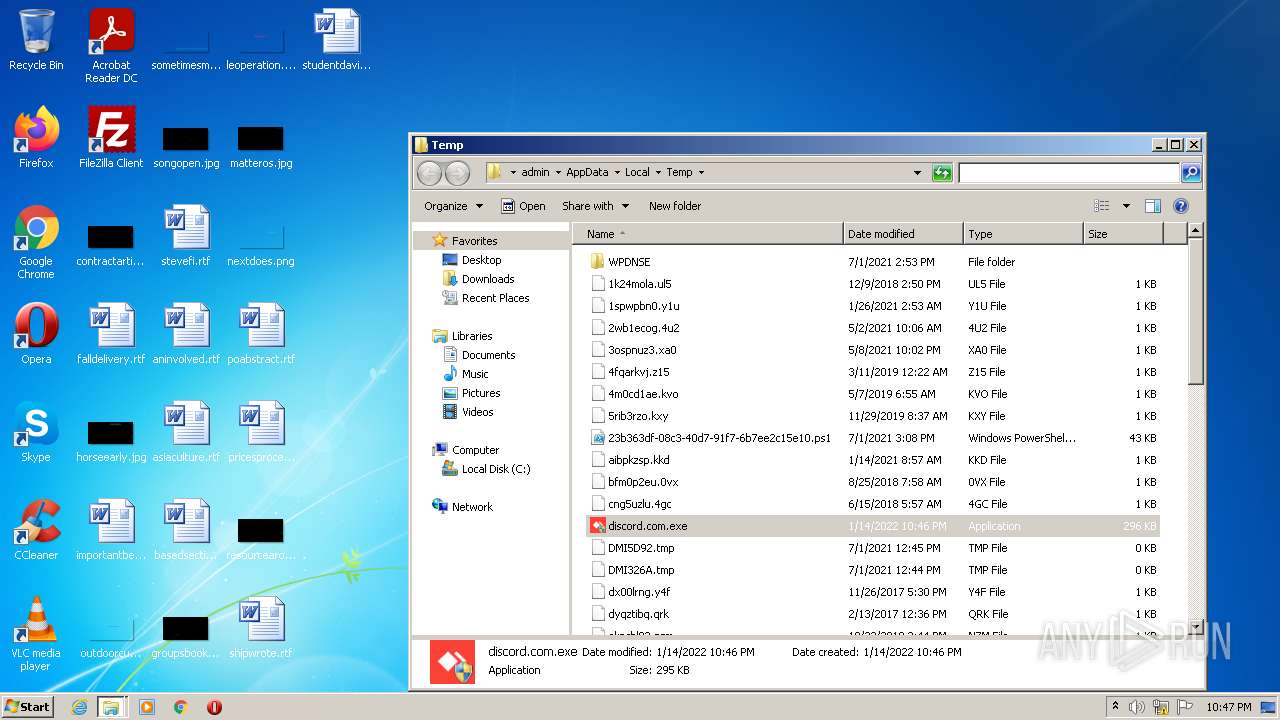
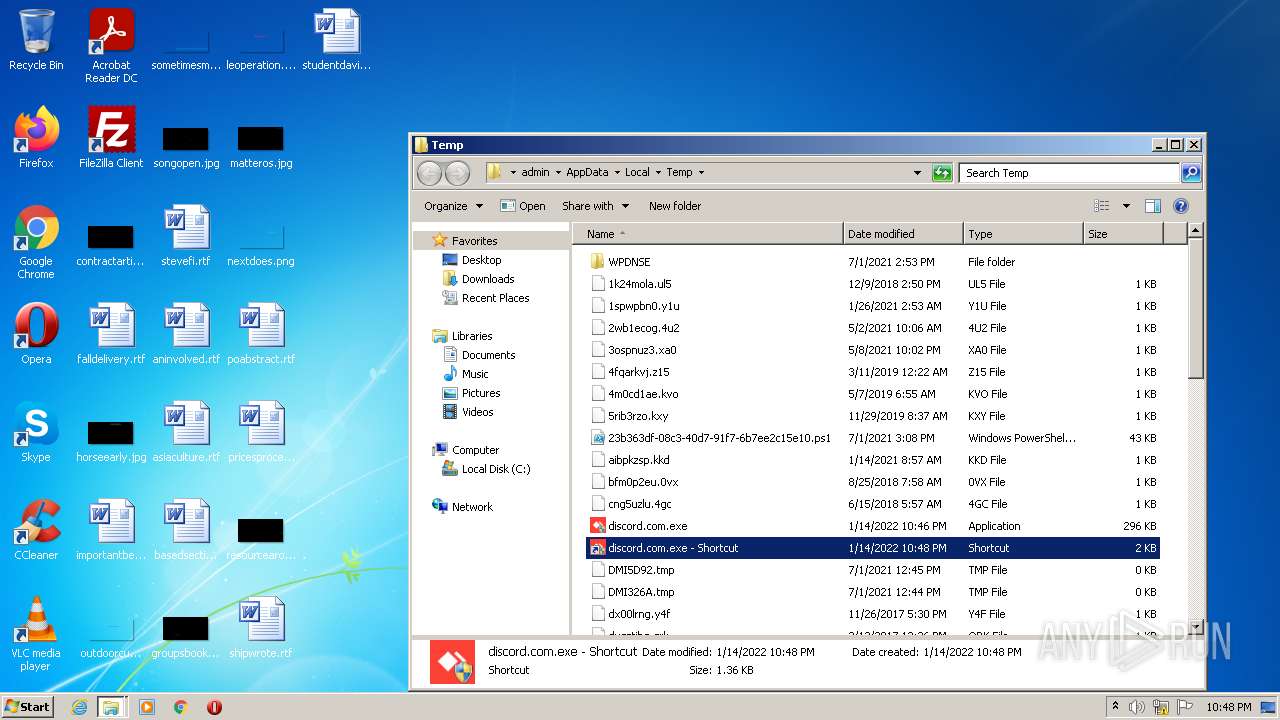
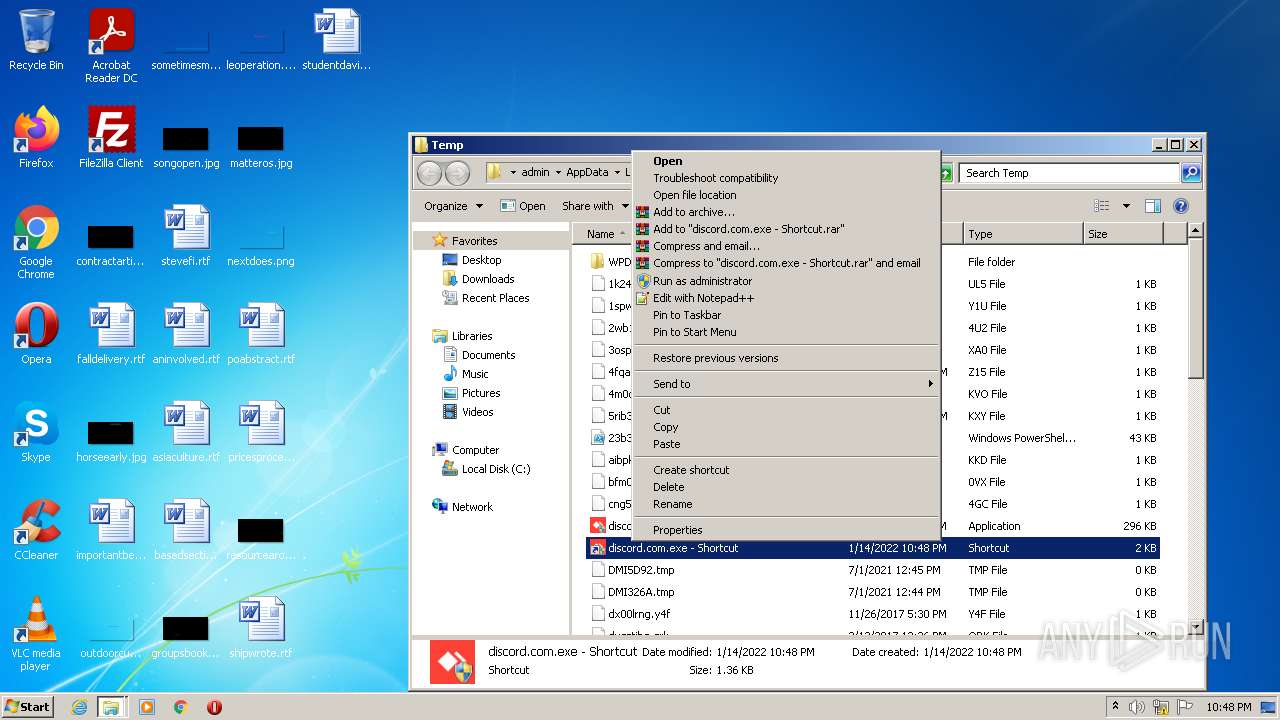
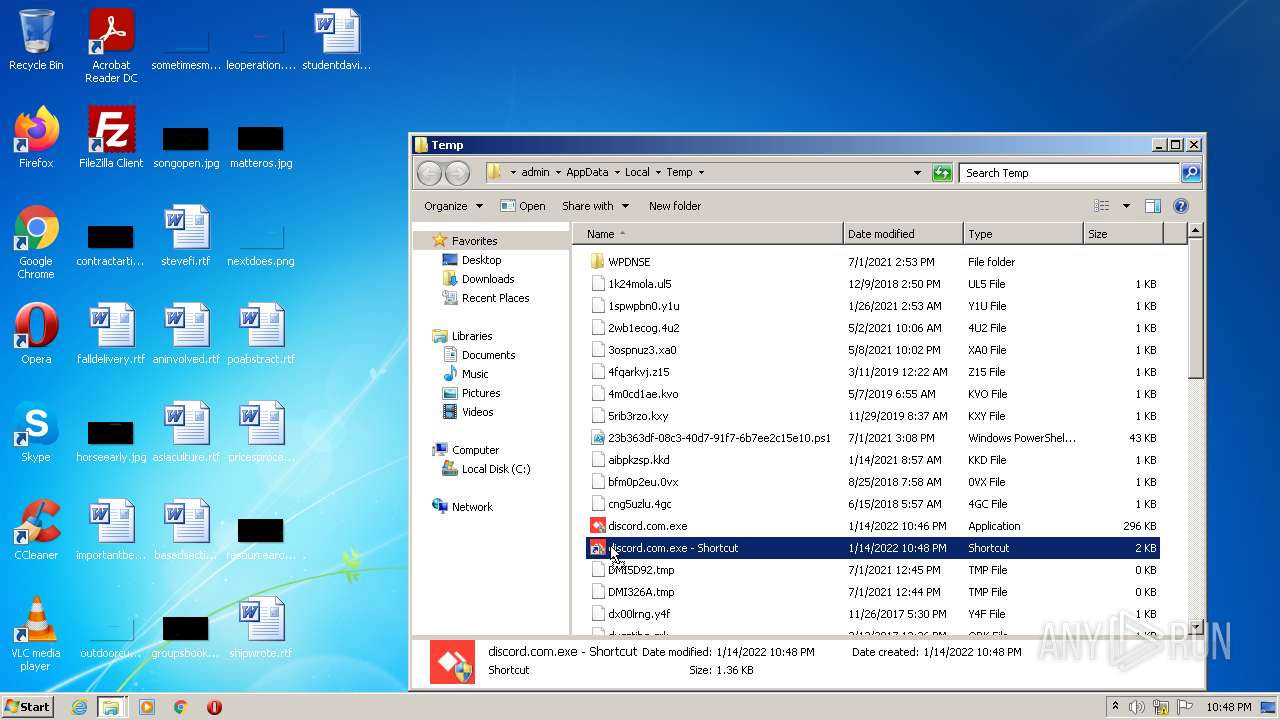
Creates files in the user directory
- powershell.exe (PID: 3688)
Modifies files in Chrome extension folder
- chrome.exe (PID: 484)
Drops a file with a compile date too recent
- chrome.exe (PID: 484)
Executable content was dropped or overwritten
- chrome.exe (PID: 484)
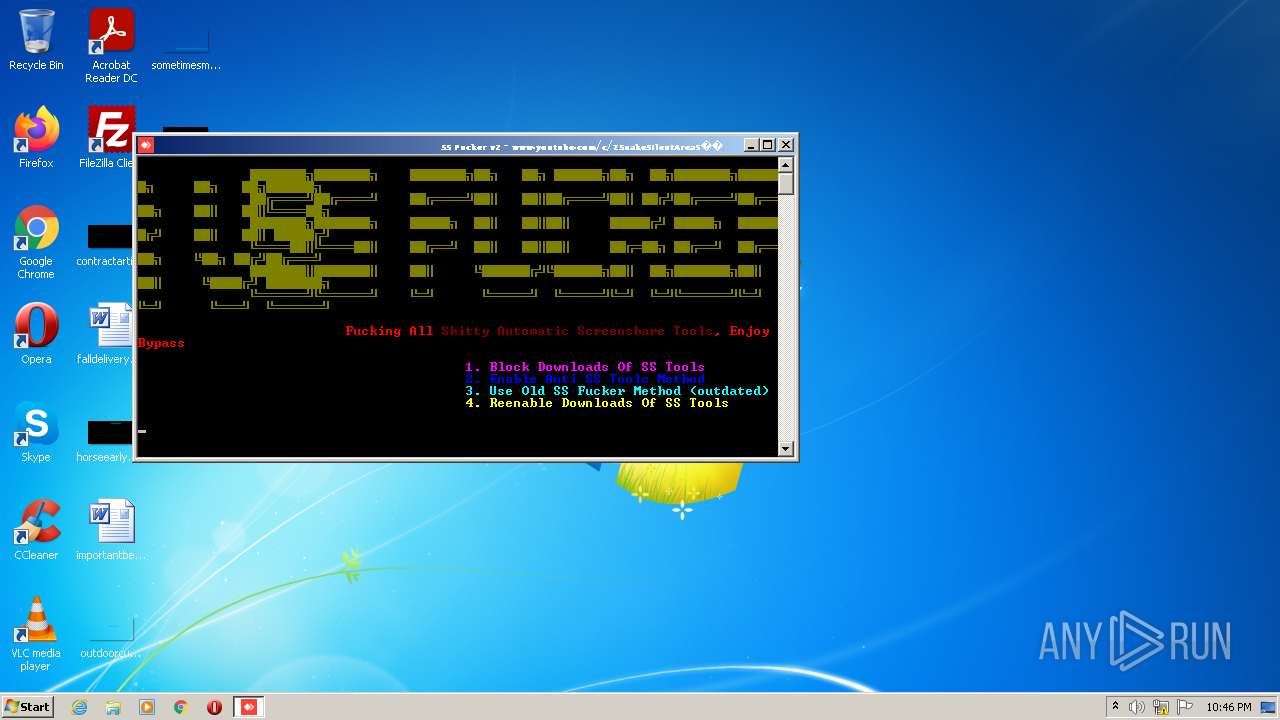
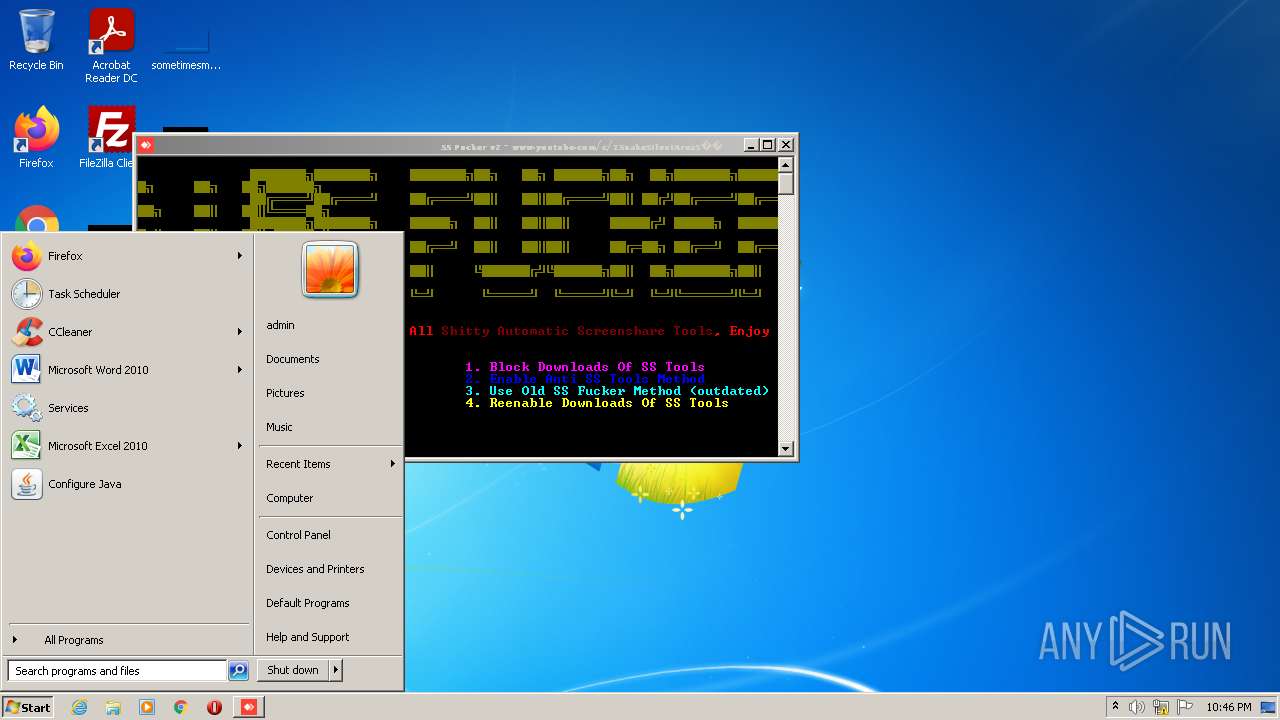
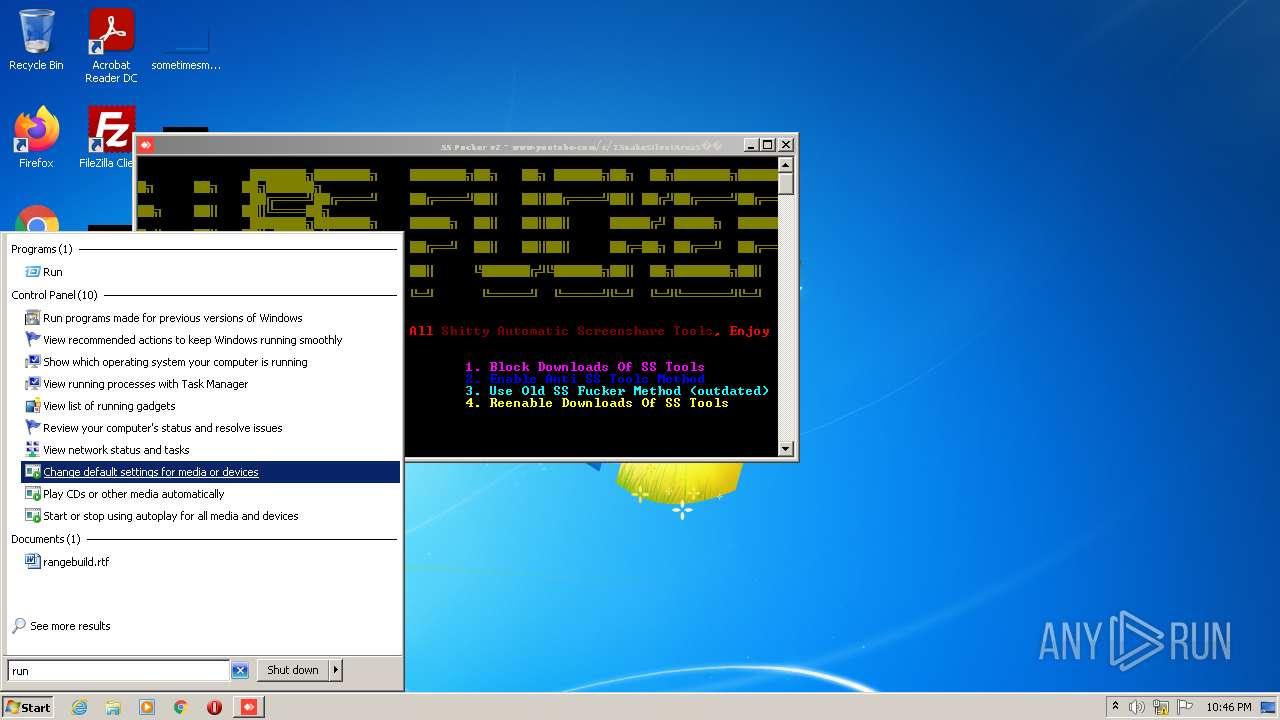
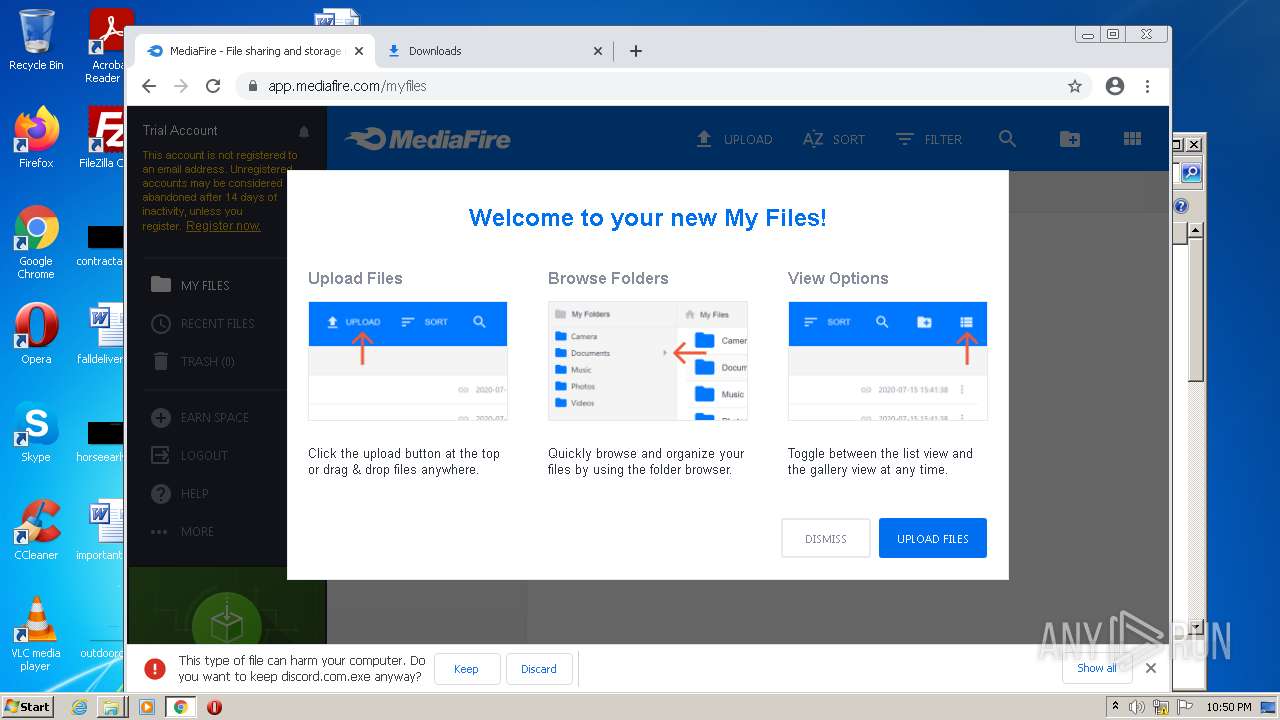
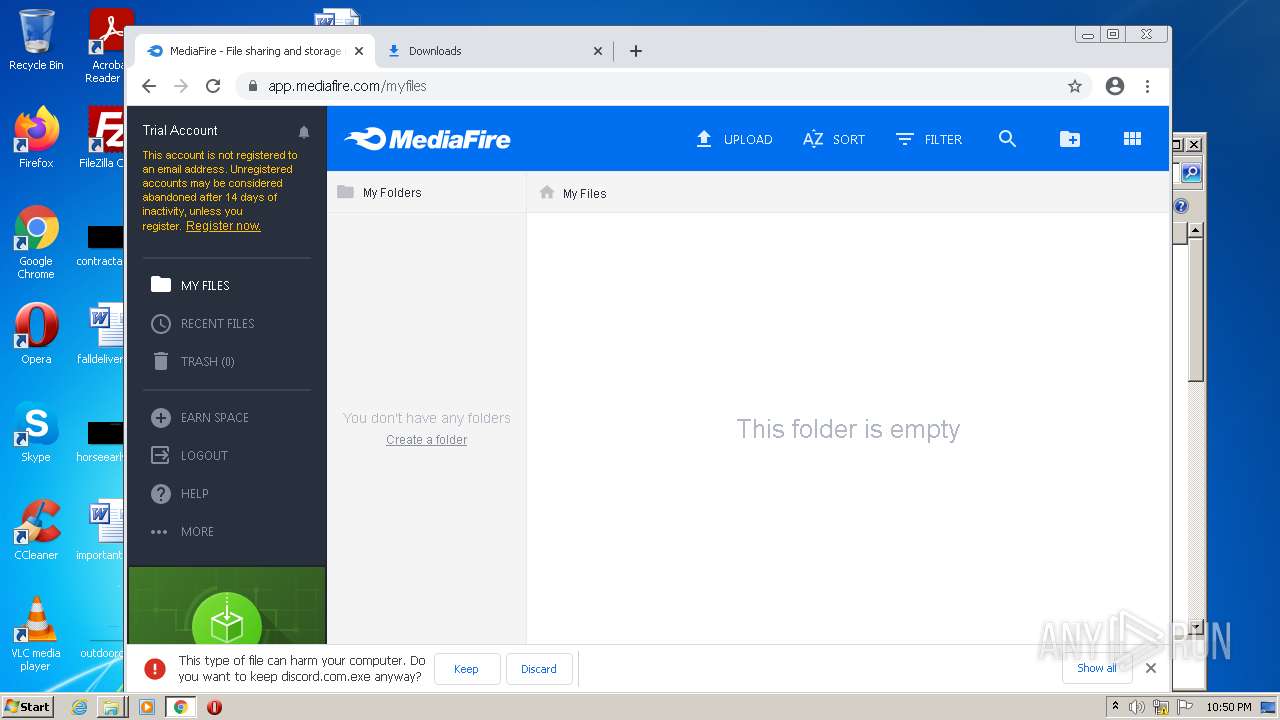
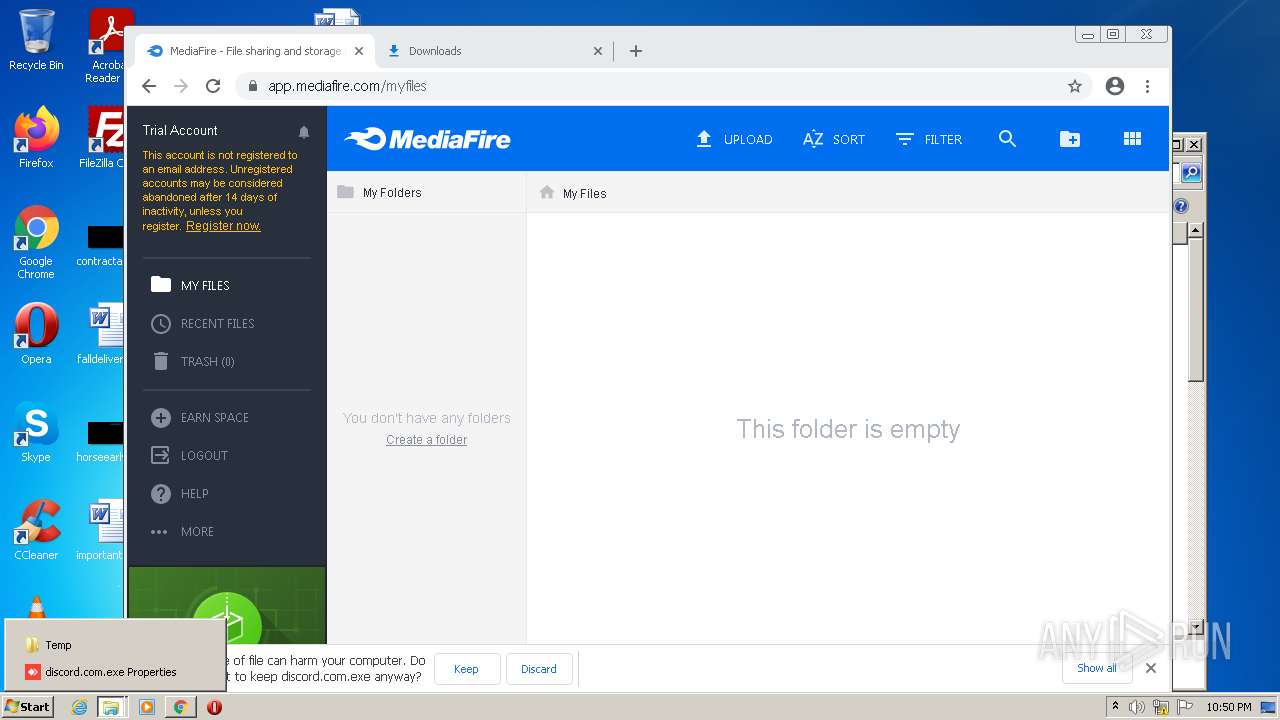
INFO
Manual execution by user
- powershell.exe (PID: 3688)
- discord.com.exe (PID: 736)
- discord.com.exe (PID: 276)
- powershell_ise.exe (PID: 3648)
- rundll32.exe (PID: 3188)
- notepad++.exe (PID: 3044)
- chrome.exe (PID: 484)
Checks Windows Trust Settings
- powershell.exe (PID: 3688)
- powershell_ise.exe (PID: 3648)
Checks supported languages
- net1.exe (PID: 1608)
- net.exe (PID: 2876)
- rundll32.exe (PID: 3188)
- chrome.exe (PID: 484)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 2164)
- chrome.exe (PID: 2824)
- chrome.exe (PID: 3808)
- chrome.exe (PID: 3100)
- chrome.exe (PID: 1680)
- chrome.exe (PID: 4044)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 736)
- chrome.exe (PID: 2064)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 3072)
- chrome.exe (PID: 3604)
- chrome.exe (PID: 460)
- chrome.exe (PID: 924)
- chrome.exe (PID: 2484)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 3468)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 2432)
- chrome.exe (PID: 1448)
- chrome.exe (PID: 2176)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 4056)
- chrome.exe (PID: 1264)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 4008)
- chrome.exe (PID: 2300)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 3040)
- chrome.exe (PID: 1488)
- chrome.exe (PID: 3744)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 2784)
- chrome.exe (PID: 3588)
- chrome.exe (PID: 676)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 2904)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 2580)
- chrome.exe (PID: 3368)
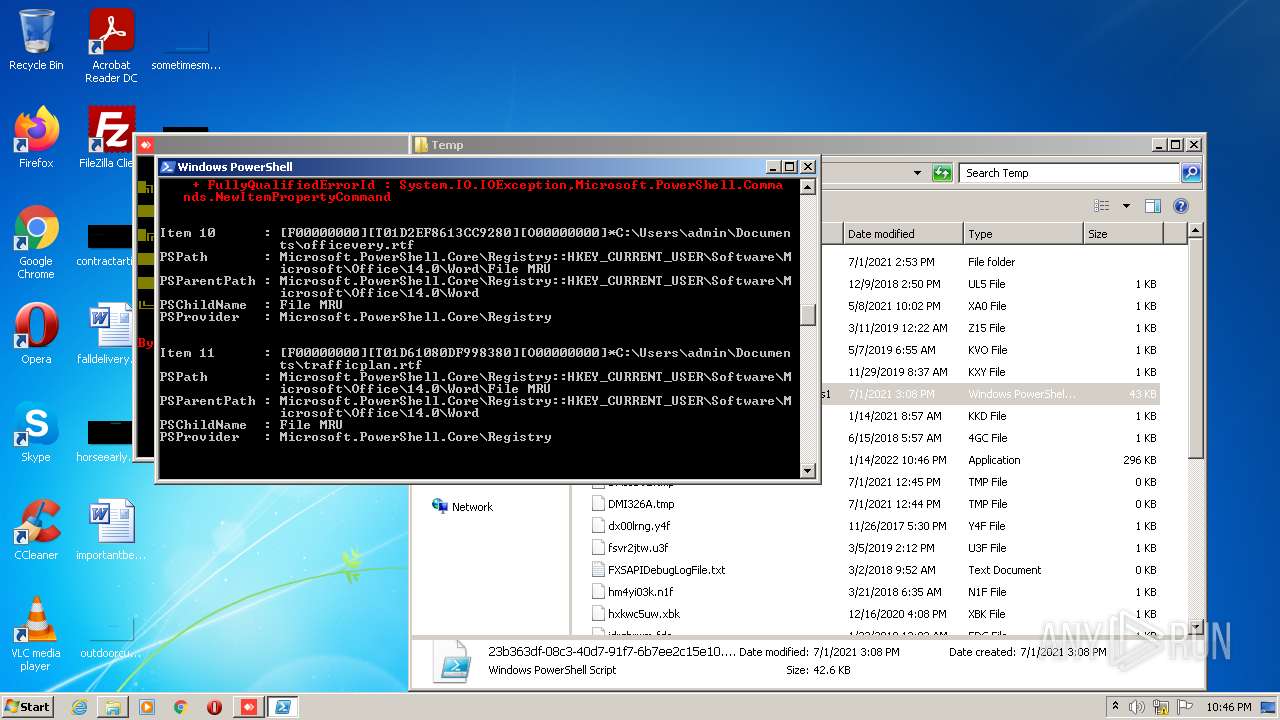
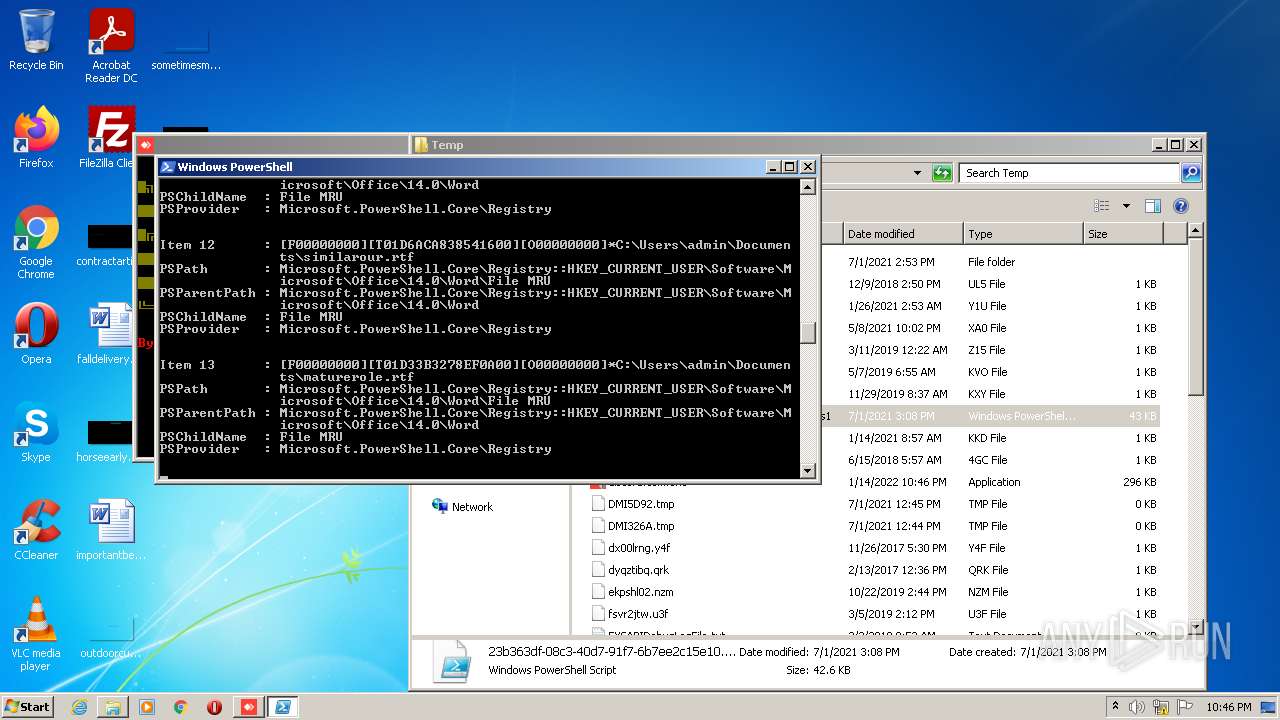
Reads Microsoft Office registry keys
- powershell.exe (PID: 3688)
Reads the computer name
- net1.exe (PID: 1608)
- chrome.exe (PID: 484)
- chrome.exe (PID: 2164)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 736)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 4056)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 3588)
Reads settings of System Certificates
- powershell_ise.exe (PID: 3648)
- chrome.exe (PID: 2164)
Application launched itself
- chrome.exe (PID: 484)
Reads the hosts file
- chrome.exe (PID: 484)
- chrome.exe (PID: 2164)
Reads the date of Windows installation
- chrome.exe (PID: 3048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
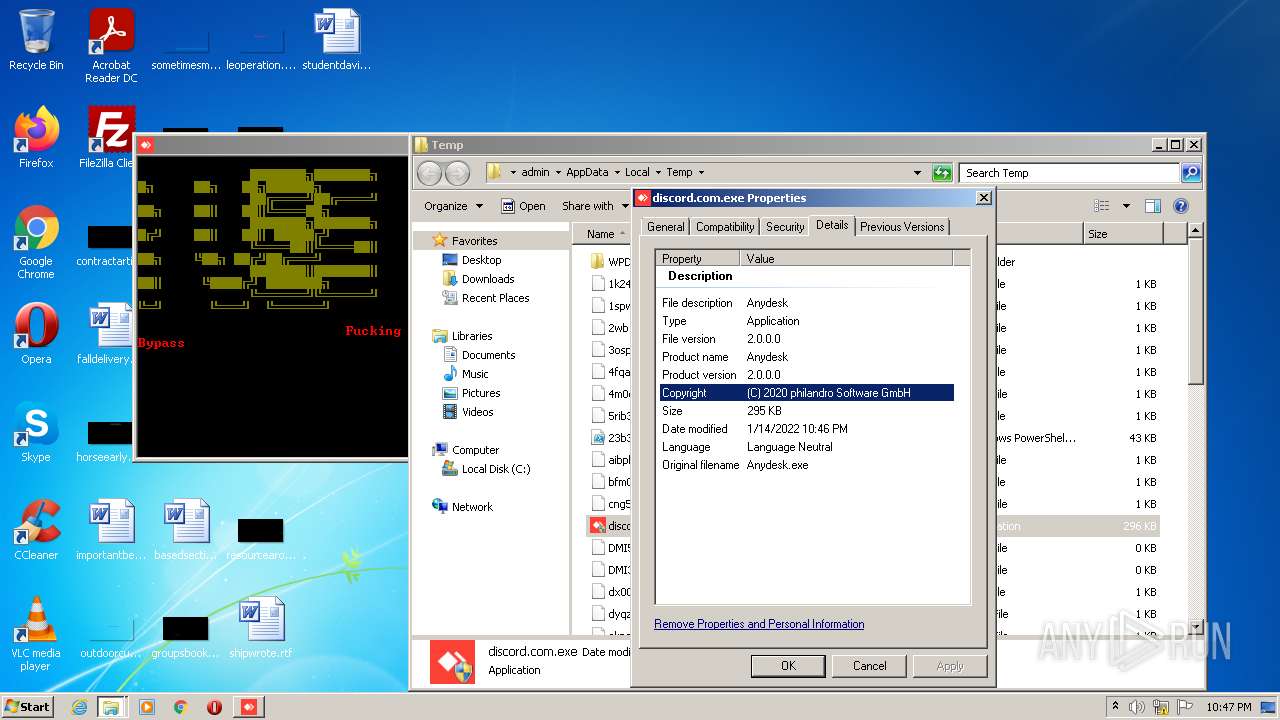
| AssemblyVersion: | 2.0.0.0 |
|---|---|
| ProductVersion: | 2.0.0.0 |
| ProductName: | Anydesk |
| OriginalFileName: | Anydesk.exe |
| LegalTrademarks: | - |
| LegalCopyright: | (C) 2020 philandro Software GmbH |
| InternalName: | Anydesk.exe |
| FileVersion: | 2.0.0.0 |
| FileDescription: | Anydesk |
| CompanyName: | philandro Software GmbH |
| Comments: | Anydesk |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 2.0.0.0 |
| FileVersionNumber: | 2.0.0.0 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x33faf |
| UninitializedDataSize: | - |
| InitializedDataSize: | 14848 |
| CodeSize: | 15872 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| TimeStamp: | 2101:10:16 18:00:38+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 09-Sep-1965 09:32:22 |
| Comments: | Anydesk |
| CompanyName: | philandro Software GmbH |
| FileDescription: | Anydesk |
| FileVersion: | 2.0.0.0 |
| InternalName: | Anydesk.exe |
| LegalCopyright: | (C) 2020 philandro Software GmbH |
| LegalTrademarks: | - |
| OriginalFilename: | Anydesk.exe |
| ProductName: | Anydesk |
| ProductVersion: | 2.0.0.0 |
| Assembly Version: | 2.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-Sep-1965 09:32:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00003D18 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.vmp0 | 0x00006000 | 0x0002A4C6 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.vmp1 | 0x00032000 | 0x00045FE8 | 0x00046000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.06095 |
.rsrc | 0x00078000 | 0x00003788 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.50511 |
.reloc | 0x0007C000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.122276 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.99765 | 3370 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 2.29968 | 1640 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.6735 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.73746 | 488 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.69265 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.74268 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
111
Monitored processes
57
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
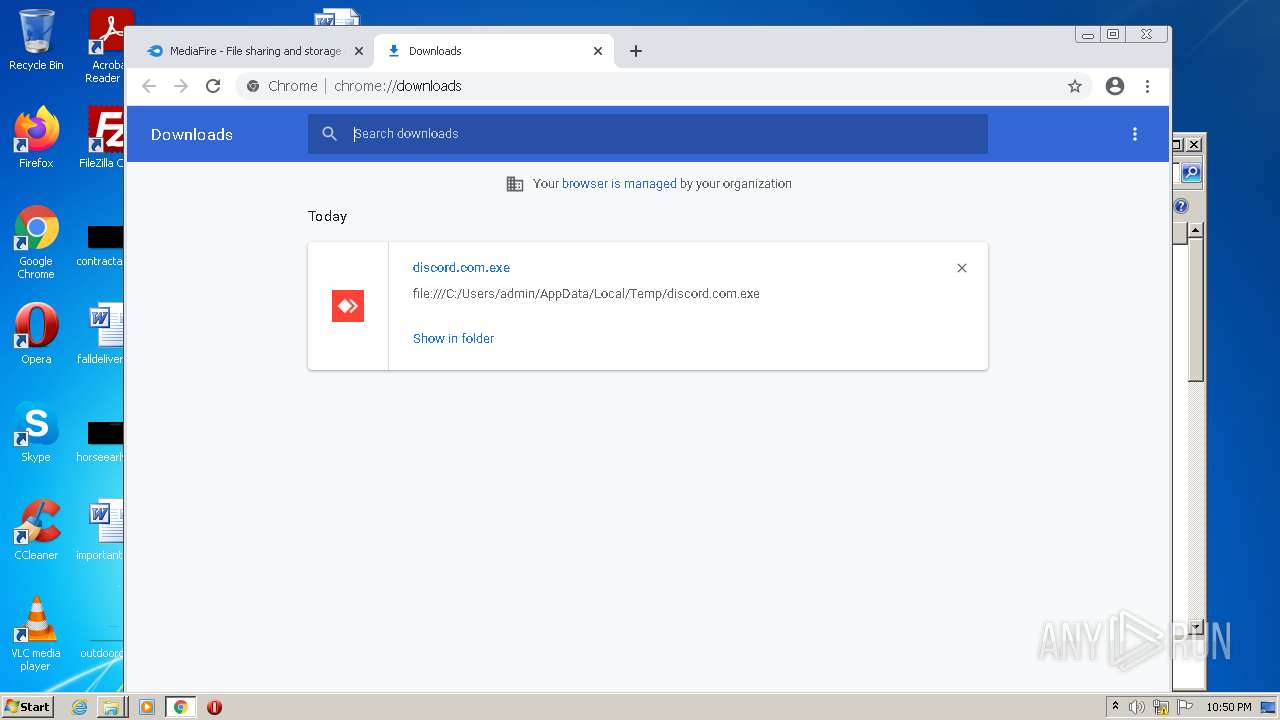
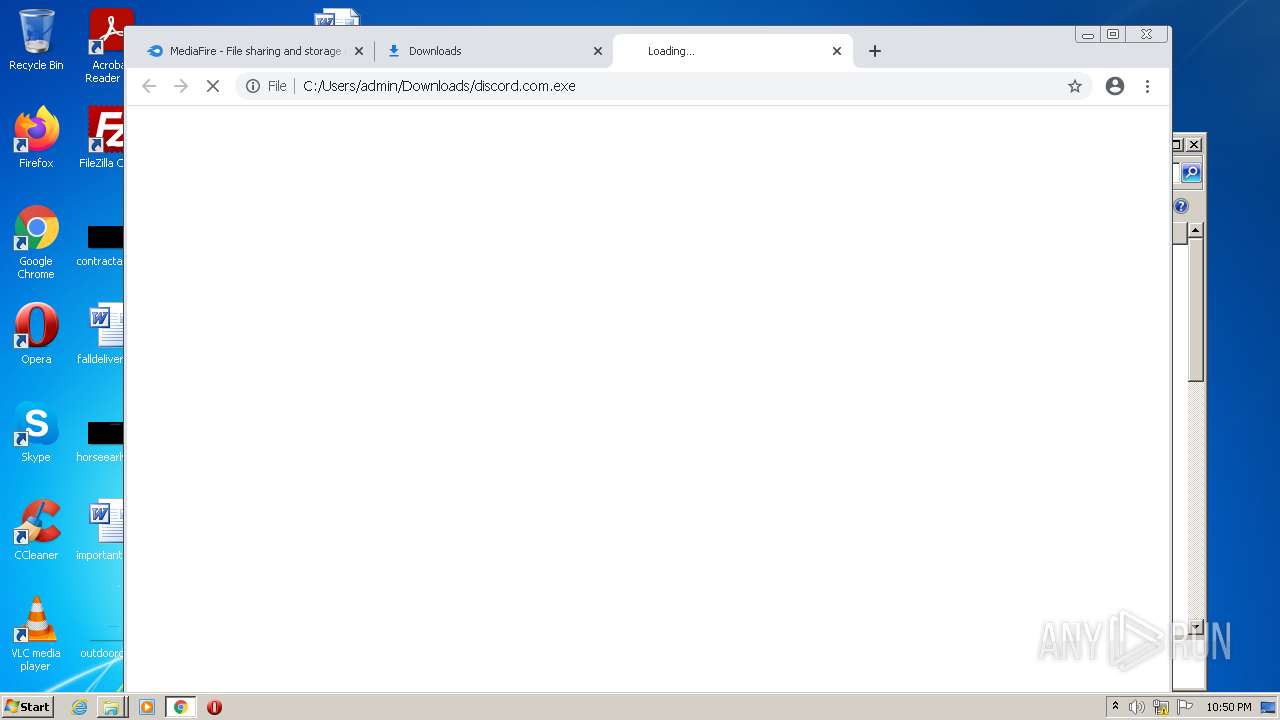
| 276 | "C:\Users\admin\AppData\Local\Temp\discord.com.exe" | C:\Users\admin\AppData\Local\Temp\discord.com.exe | Explorer.EXE | ||||||||||||
User: admin Company: philandro Software GmbH Integrity Level: HIGH Description: Anydesk Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1064,6932819320894883783,12435438007222973384,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3520 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1064,6932819320894883783,12435438007222973384,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2576 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 736 | "C:\Users\admin\AppData\Local\Temp\discord.com.exe" | C:\Users\admin\AppData\Local\Temp\discord.com.exe | — | Explorer.EXE | |||||||||||
User: admin Company: philandro Software GmbH Integrity Level: MEDIUM Description: Anydesk Exit code: 3221226540 Version: 2.0.0.0 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1064,6932819320894883783,12435438007222973384,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2840 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1064,6932819320894883783,12435438007222973384,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3272 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,6932819320894883783,12435438007222973384,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1364 | "cmd.exe" | C:\Windows\system32\cmd.exe | — | discord.com.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,6932819320894883783,12435438007222973384,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
20 888
Read events
20 615
Write events
265
Delete events
8
Modification events
| (PID) Process: | (3688) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3688) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3688) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3688) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3688) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3688) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\File MRU |
| Operation: | write | Name: | Item 10 |
Value: [F00000000][T01D2EF8613CC9280][O00000000]*C:\Users\admin\Documents\officevery.rtf | |||
| (PID) Process: | (3688) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\File MRU |
| Operation: | write | Name: | Item 11 |
Value: [F00000000][T01D61080DF998380][O00000000]*C:\Users\admin\Documents\trafficplan.rtf | |||
| (PID) Process: | (3688) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\File MRU |
| Operation: | write | Name: | Item 12 |
Value: [F00000000][T01D6ACA838541600][O00000000]*C:\Users\admin\Documents\similarour.rtf | |||
| (PID) Process: | (3688) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\File MRU |
| Operation: | write | Name: | Item 13 |
Value: [F00000000][T01D33B3278EF0A00][O00000000]*C:\Users\admin\Documents\maturerole.rtf | |||
| (PID) Process: | (3688) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\IntelliForms\Storage2 |
| Operation: | write | Name: | 1489F923C4DCA729178B3E3233458550D8DDDF2945 |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000056E494AB42D3C40B244FA52F2874BE3000000000200000000001066000000010000200000004238EAFD13FF0CF184C4F16AE0B9853EF81557309C6E0B2B756891896C98778C000000000E8000000002000020000000F1B06E6CB65EF598FC911719177698B2740686300066EE7A67AD6AD55F508754900000000C7871765EC3379A3FE9308E271624CAE6990A67928494A99D4A24ED7DC598A25EB0A09AF77AAB21D8D7A4B81C402BE66D5AB3475AAE19800CA56023B0F3039EA696BCC7732C8BB1786C3F7535342B26FEA86245B3D59A257326DEEDF502A271DD07FF09B66D06B103B65E9D47555E7166769D4D53316C84552042F3828FF4F270B48A57F16A7E4FB8C8E794505D4F72400000004BFE0314FCD6E0A5212ACCD0A0249D29B8EF7262A43FE8CCD83DDDD7CA811C697F2176A072FD7579247EA073085C29C855B76FC27CC359860EDA41647E21E134 | |||
Executable files
5
Suspicious files
214
Text files
190
Unknown types
25
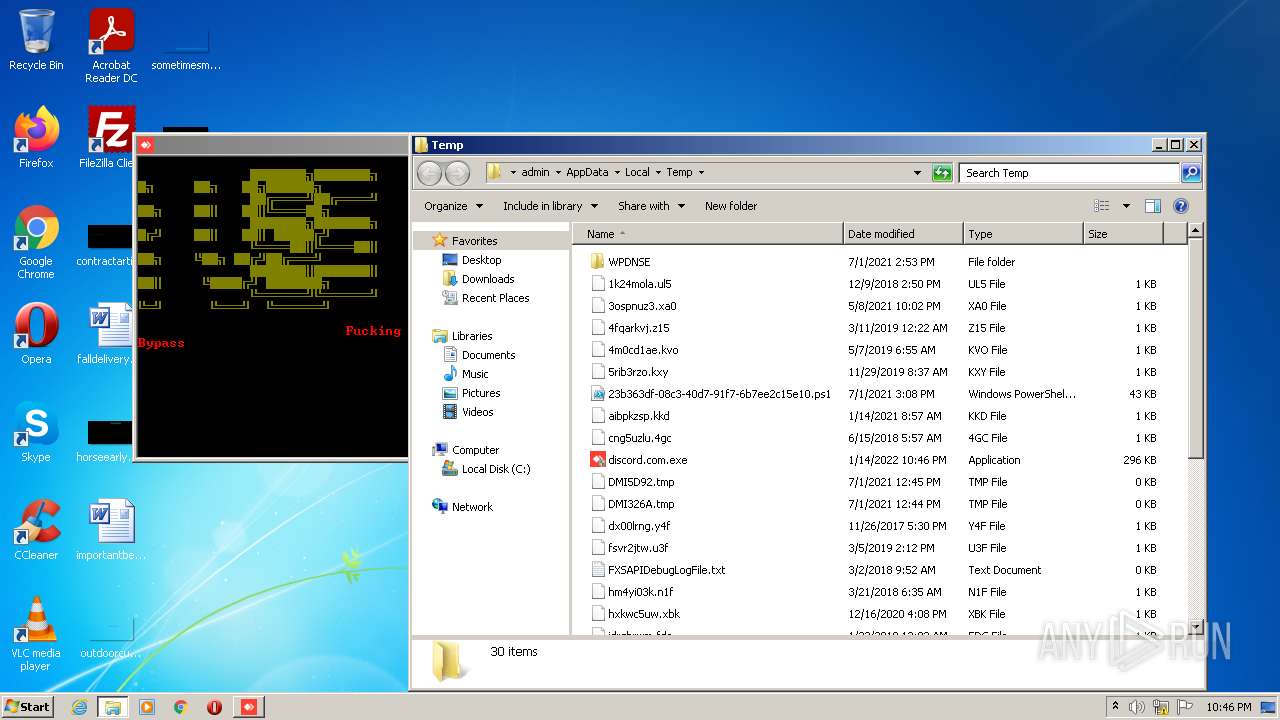
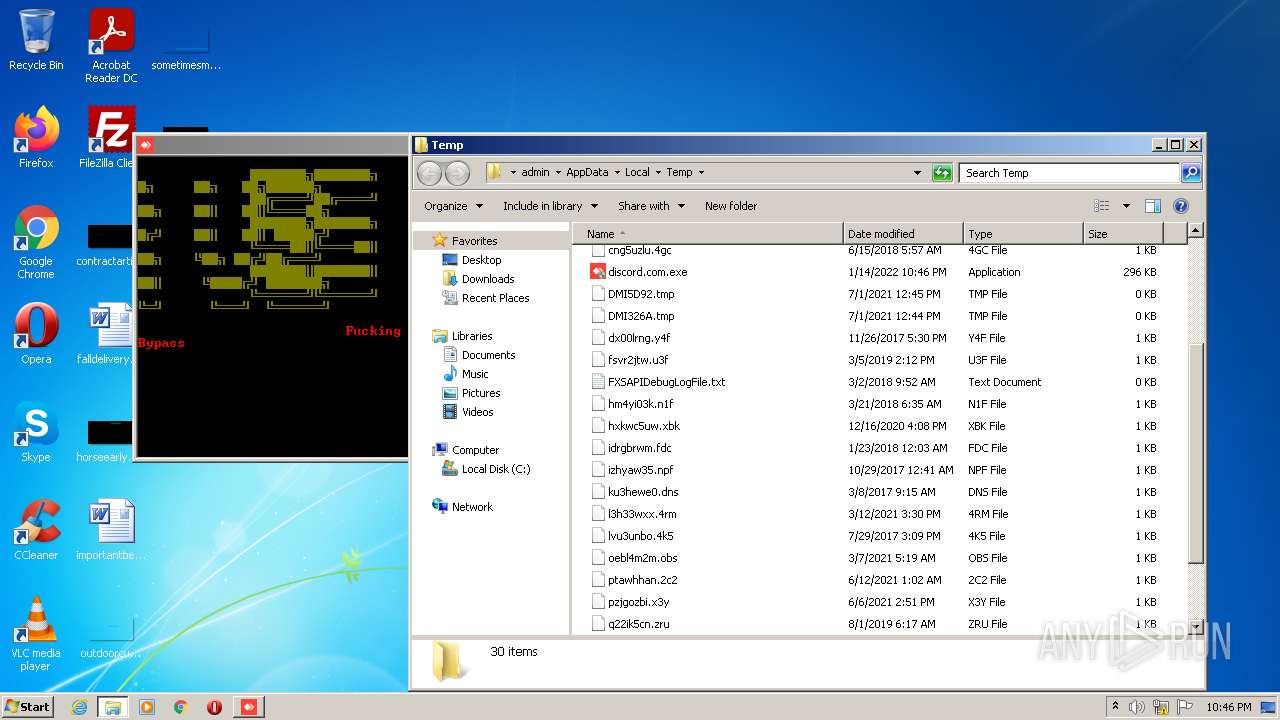
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3688 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFecacd.TMP | binary | |
MD5:— | SHA256:— | |||
| 3688 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4FIWCSPHR450RLYYSREO.temp | binary | |
MD5:— | SHA256:— | |||
| 3688 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\matteros.jpg.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3688 | powershell.exe | C:\Users\admin\Desktop\nextdoes.png | image | |
MD5:— | SHA256:— | |||
| 3688 | powershell.exe | C:\Users\admin\Desktop\leoperation.png | image | |
MD5:— | SHA256:— | |||
| 3688 | powershell.exe | C:\Users\admin\Desktop\resourcearound.jpg | image | |
MD5:— | SHA256:— | |||
| 3688 | powershell.exe | C:\Users\admin\Desktop\poabstract.rtf | text | |
MD5:— | SHA256:— | |||
| 3688 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\leoperation.png.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3688 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\groupsbook.jpg.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3688 | powershell.exe | C:\Users\admin\Desktop\studentdavid.rtf | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
50
DNS requests
49
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
872 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
872 | svchost.exe | HEAD | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/p6tdgdqb2yivlossrf26vulw4q_2763/jflookgnkcckhobaglndicnbbgbonegd_2763_all_arglytk4g4e7ivpqlqt2zfg3sy.crx3 | US | — | — | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 5.63 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 9.69 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 9.70 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 20.9 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 88.5 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 9.69 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | bs | 399 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 43.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
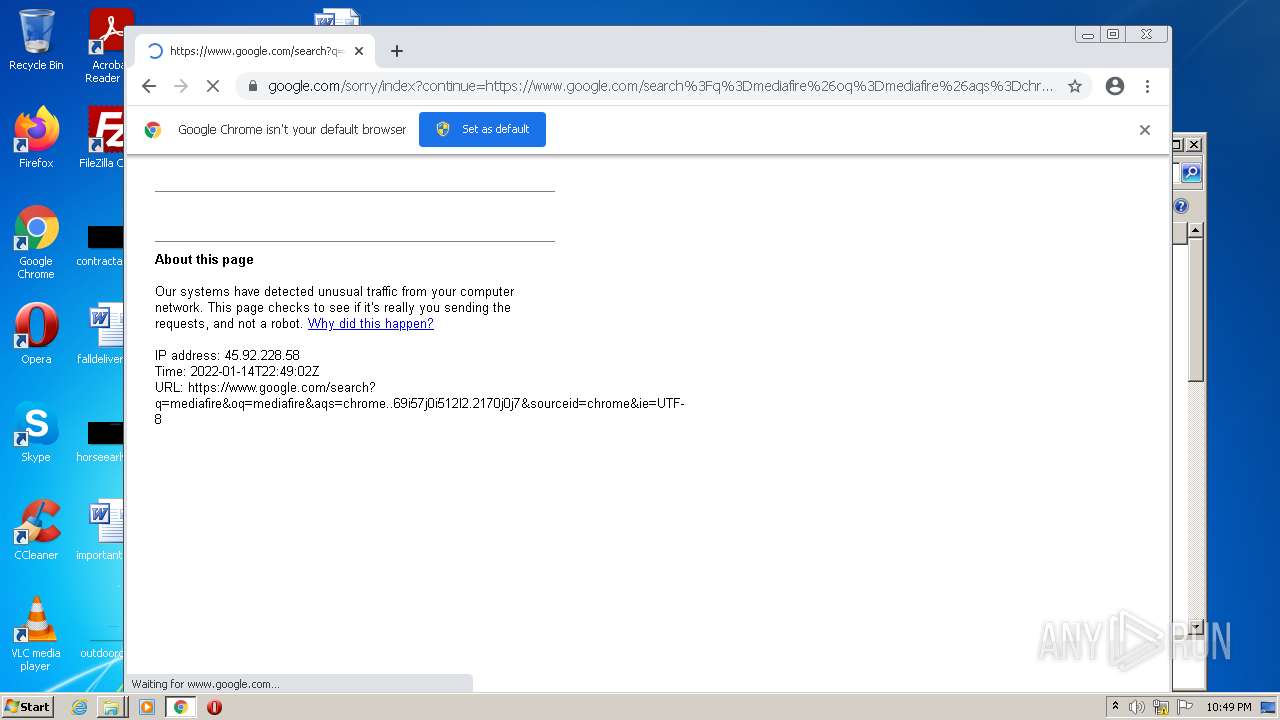
2164 | chrome.exe | 142.250.184.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 142.250.185.100:443 | www.google.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 142.250.185.77:443 | accounts.google.com | Google Inc. | US | suspicious |
2164 | chrome.exe | 142.250.185.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 142.250.185.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 142.250.185.206:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 216.58.212.161:443 | lh5.googleusercontent.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 142.250.186.106:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 142.250.185.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 142.250.186.46:443 | consent.google.com | Google Inc. | US | whitelisted |
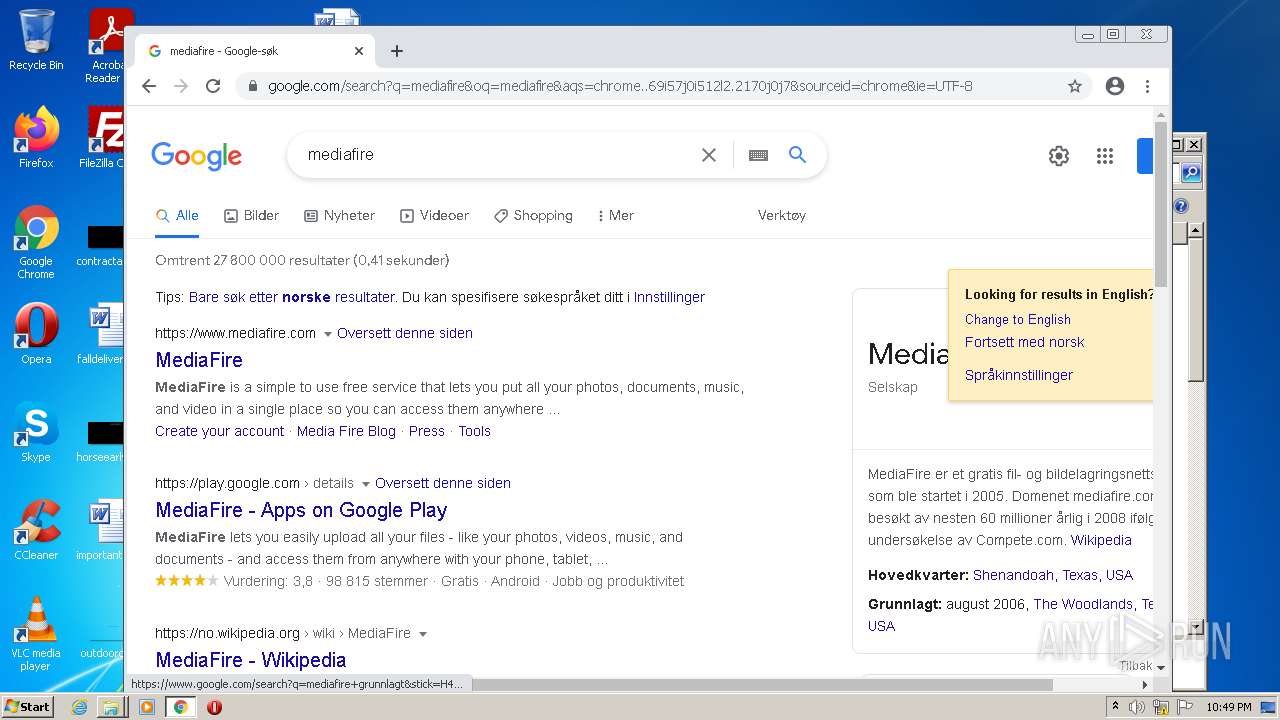
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
Threats
Process | Message |
|---|---|
powershell_ise.exe | PimcManager::LoadWisptis failed to ShellExecuteEx.
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|