| File name: | dllhost.exe |
| Full analysis: | https://app.any.run/tasks/4a210042-437a-4e82-b323-d1bbe276460c |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 18:32:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 03DE5BF95EF6377B657201F7340CEB6A |
| SHA1: | 92A287540EB8311912FB318B187BB4259A7B6945 |
| SHA256: | 4F56137A93FCDC2B239E4A64D8FC3BE86F4D8CABC4B3DD4ACE06021DFE1A19F4 |
| SSDEEP: | 98304:PigchhKmohYAcGYUWhT1n1BrSNkPN6a2mlj4OBXA1i7brParBtmf1T50tQZQc+1F:fIxOUOIFF2Co9roQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
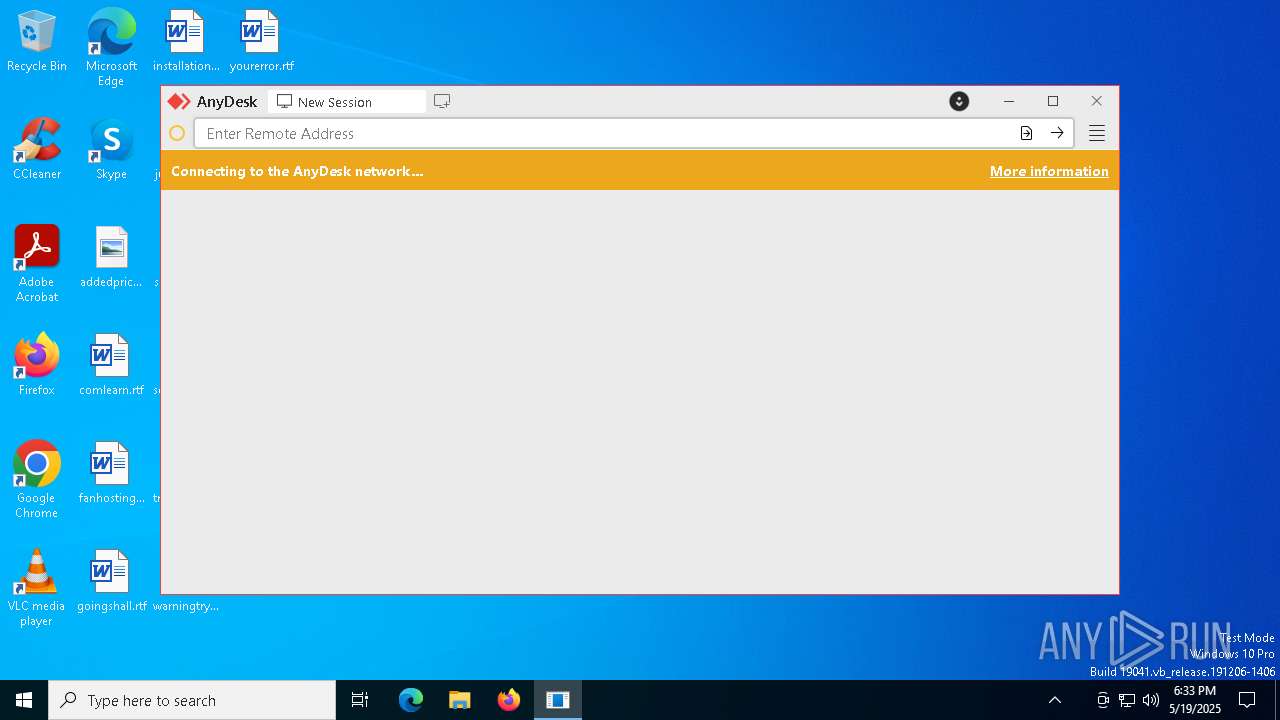
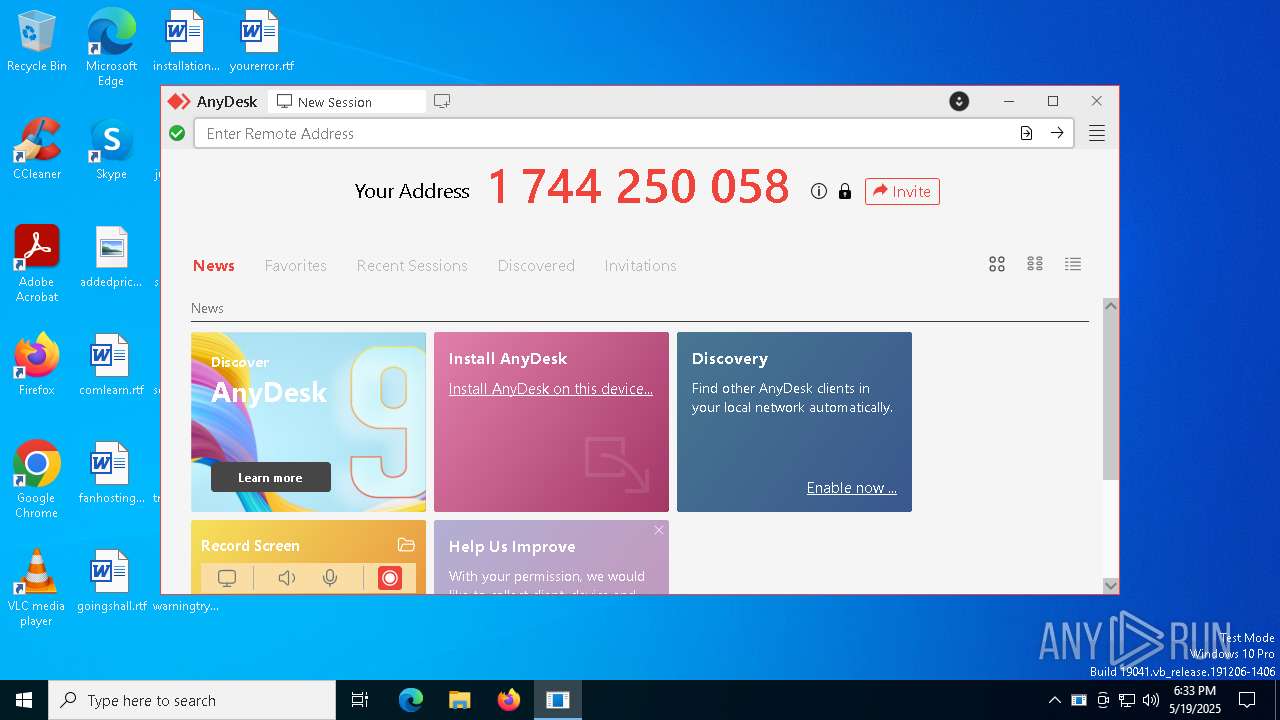
ANYDESK mutex has been found
- dllhost.exe (PID: 5680)
- dllhost.exe (PID: 7220)
- dllhost.exe (PID: 7228)
Application launched itself
- dllhost.exe (PID: 5680)
INFO
The sample compiled with english language support
- dllhost.exe (PID: 5680)
Reads the computer name
- dllhost.exe (PID: 5680)
- dllhost.exe (PID: 7228)
- dllhost.exe (PID: 7220)
Checks supported languages
- dllhost.exe (PID: 5680)
- dllhost.exe (PID: 7228)
- dllhost.exe (PID: 7220)
Creates files or folders in the user directory
- dllhost.exe (PID: 5680)
- dllhost.exe (PID: 7228)
- dllhost.exe (PID: 7220)
Process checks whether UAC notifications are on
- dllhost.exe (PID: 5680)
Reads the machine GUID from the registry
- dllhost.exe (PID: 7220)
Reads CPU info
- dllhost.exe (PID: 7228)
Checks proxy server information
- dllhost.exe (PID: 7228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:04:02 19:57:26+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 10752 |
| InitializedDataSize: | 7738880 |
| UninitializedDataSize: | 27911168 |
| EntryPoint: | 0x3653 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.5.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | dllhost |
| FileDescription: | dllhost |
| FileVersion: | 1.2.0 |
| ProductName: | dllhost |
| ProductVersion: | 1.2 |
| LegalCopyright: | (C) 2025 dllhost |
Total processes
131
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5680 | "C:\Users\admin\AppData\Local\Temp\dllhost.exe" | C:\Users\admin\AppData\Local\Temp\dllhost.exe | — | explorer.exe | |||||||||||
User: admin Company: dllhost Integrity Level: MEDIUM Description: dllhost Version: 1.2.0 Modules
| |||||||||||||||
| 7220 | "C:\Users\admin\AppData\Local\Temp\dllhost.exe" --local-service | C:\Users\admin\AppData\Local\Temp\dllhost.exe | dllhost.exe | ||||||||||||
User: admin Company: dllhost Integrity Level: MEDIUM Description: dllhost Version: 1.2.0 Modules
| |||||||||||||||
| 7228 | "C:\Users\admin\AppData\Local\Temp\dllhost.exe" --local-control | C:\Users\admin\AppData\Local\Temp\dllhost.exe | — | dllhost.exe | |||||||||||
User: admin Company: dllhost Integrity Level: MEDIUM Description: dllhost Version: 1.2.0 Modules
| |||||||||||||||
Total events
1 023
Read events
1 023
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
3
Text files
184
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5680 | dllhost.exe | C:\Users\admin\AppData\Roaming\AnyDesk\system.conf~RF10d841.TMP | — | |
MD5:— | SHA256:— | |||
| 5680 | dllhost.exe | C:\Users\admin\AppData\Roaming\AnyDesk\user.conf~RF10d870.TMP | — | |
MD5:— | SHA256:— | |||
| 5680 | dllhost.exe | C:\Users\admin\AppData\Roaming\AnyDesk\user.conf~RF10d92b.TMP | — | |
MD5:— | SHA256:— | |||
| 5680 | dllhost.exe | C:\Users\admin\AppData\Roaming\AnyDesk\user.conf~RF10d9a8.TMP | — | |
MD5:— | SHA256:— | |||
| 5680 | dllhost.exe | C:\Users\admin\AppData\Roaming\AnyDesk\user.conf~RF10db3f.TMP | — | |
MD5:— | SHA256:— | |||
| 5680 | dllhost.exe | C:\Users\admin\AppData\Roaming\AnyDesk\user.conf~RF10db4e.TMP | — | |
MD5:— | SHA256:— | |||
| 5680 | dllhost.exe | C:\Users\admin\AppData\Roaming\AnyDesk\user.conf~RF10db5e.TMP | — | |
MD5:— | SHA256:— | |||
| 5680 | dllhost.exe | C:\Users\admin\AppData\Roaming\AnyDesk\user.conf~RF10db6e.TMP | — | |
MD5:— | SHA256:— | |||
| 7220 | dllhost.exe | C:\Users\admin\AppData\Roaming\AnyDesk\system.conf~RF10de0d.TMP | — | |
MD5:— | SHA256:— | |||
| 7228 | dllhost.exe | C:\Users\admin\AppData\Roaming\AnyDesk\user.conf~RF10de5c.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
17
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7792 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7792 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7220 | dllhost.exe | 195.181.174.174:443 | boot.net.anydesk.com | Datacamp Limited | DE | whitelisted |
7220 | dllhost.exe | 195.181.174.176:443 | relay-7fe0f546.net.anydesk.com | Datacamp Limited | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
boot.net.anydesk.com |
| whitelisted |
relay-7fe0f546.net.anydesk.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET REMOTE_ACCESS Anydesk Relay Domain (net .anydesk .com) in DNS Lookup |
2196 | svchost.exe | Misc activity | ET REMOTE_ACCESS Anydesk Domain (boot .net .anydesk .com) in DNS Lookup |
2196 | svchost.exe | Misc activity | ET REMOTE_ACCESS Anydesk Relay Domain (net .anydesk .com) in DNS Lookup |