| File name: | dnscrypt-proxy-x64-2.1.6.msi |
| Full analysis: | https://app.any.run/tasks/a841a87c-1df4-4230-859a-1dc82a38aca9 |
| Verdict: | Malicious activity |
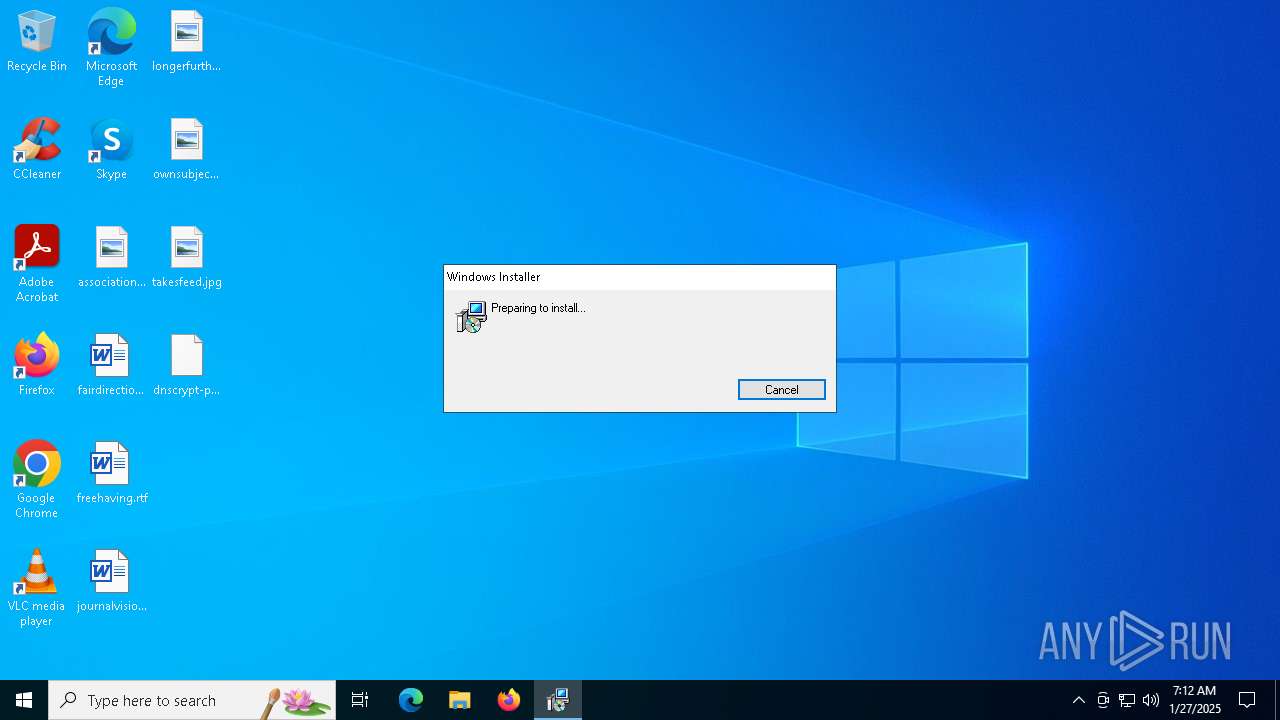
| Analysis date: | January 27, 2025, 07:12:18 |
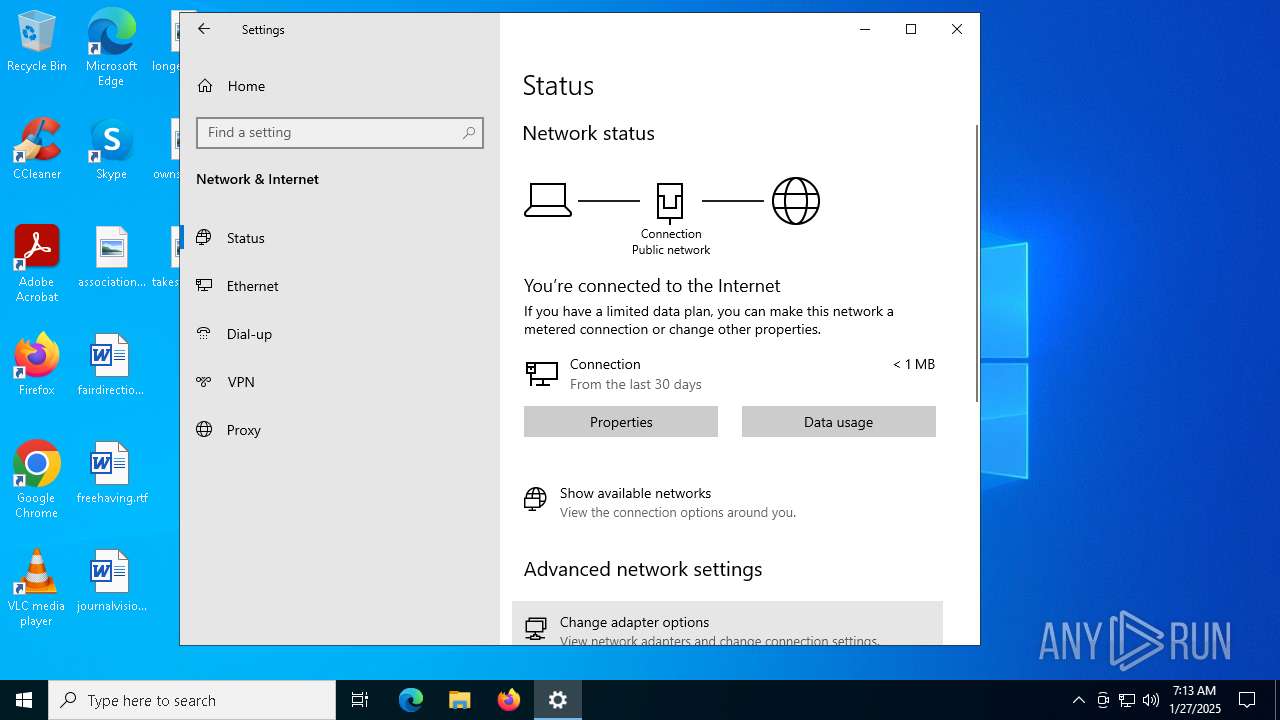
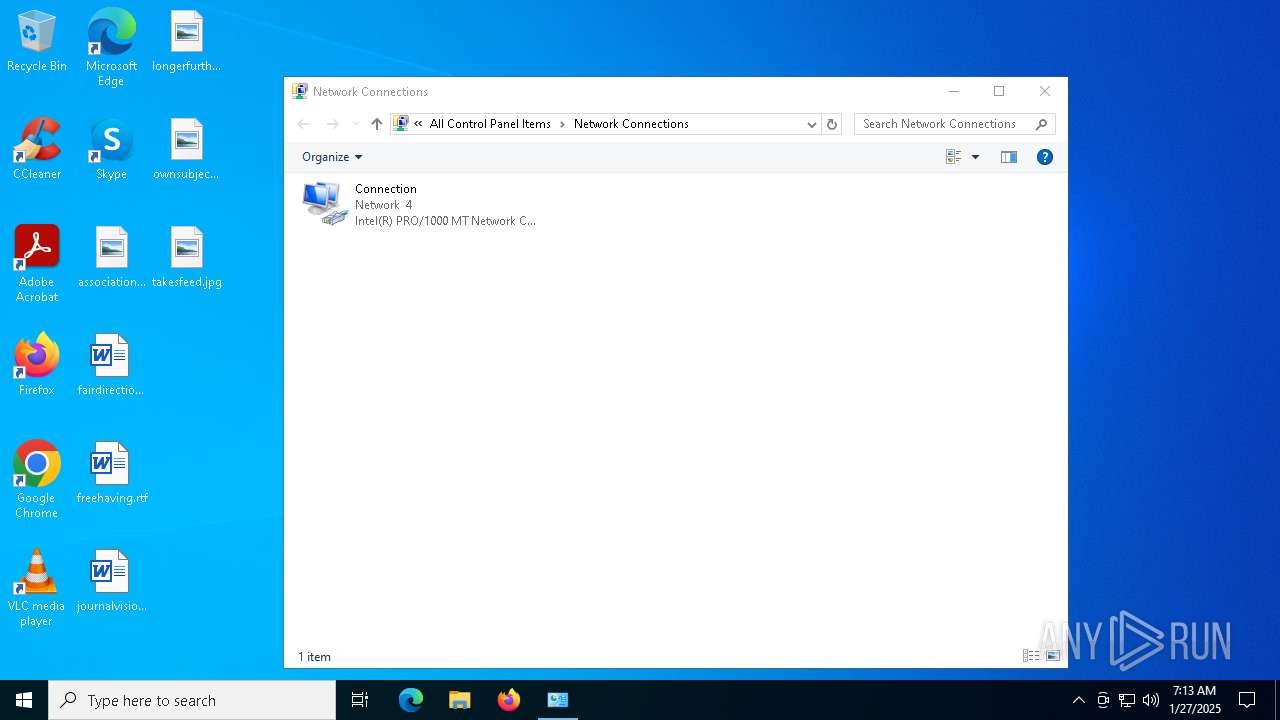
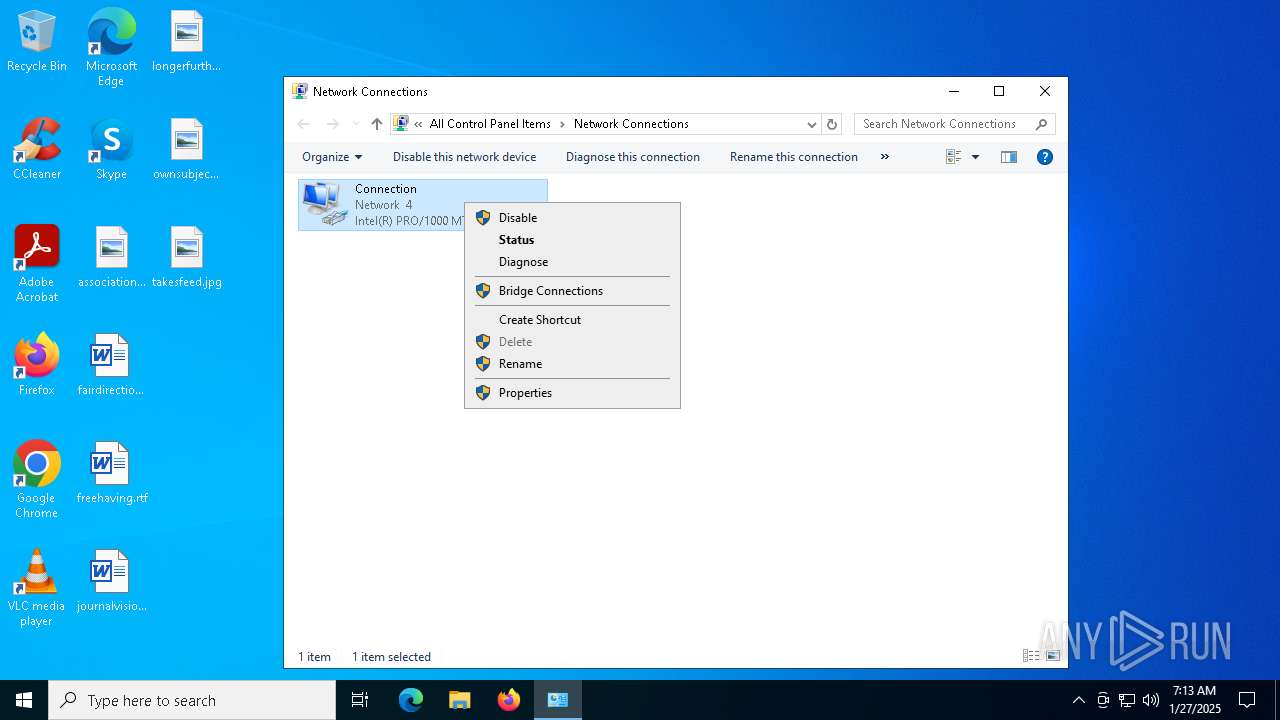
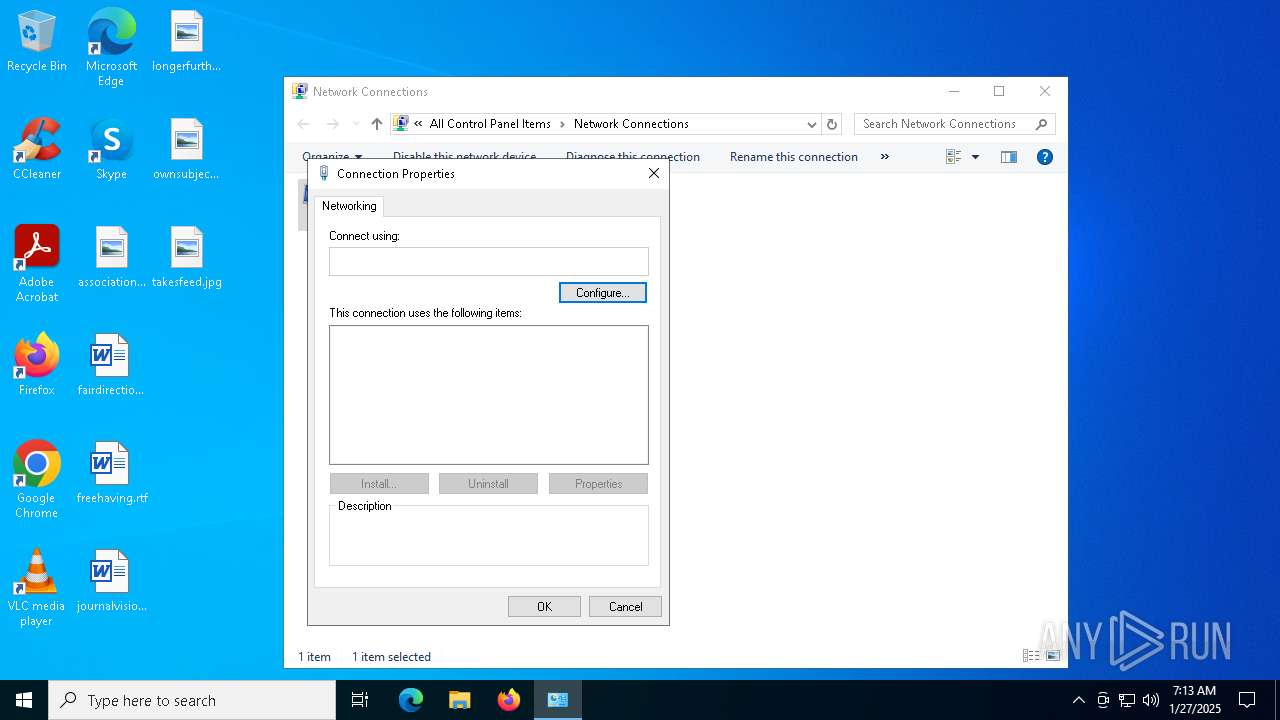
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 5.0, MSI Installer, Code page: 1252, Title: Installation Database, Subject: dnscrypt-proxy, Author: DNSCrypt, Keywords: Installer, Comments: Windows Installer Package, Template: x64;1033, Revision Number: {1F360627-8094-4E9B-8823-A04D2348311F}, Create Time/Date: Fri Jan 10 23:38:22 2025, Last Saved Time/Date: Fri Jan 10 23:38:22 2025, Number of Pages: 200, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (), Security: 2 |
| MD5: | CE2F9A9B44C807C55CA722D60CCE57CD |
| SHA1: | D8542975C2C583B0B5B38F8E04B99902EF38B944 |
| SHA256: | 4F534006A0C02FBEE29235B542C5F563DAD9CFD893BF7831463C2E8A00B70B3E |
| SSDEEP: | 98304:fSPlujMc06gn4Z0xWD3NVTwAfmNy0Ul5FSvoaTx2sFqPFQM6gj8Cd8uuQlH9SouK:q20xE/wsG8GvO |
MALICIOUS
No malicious indicators.SUSPICIOUS
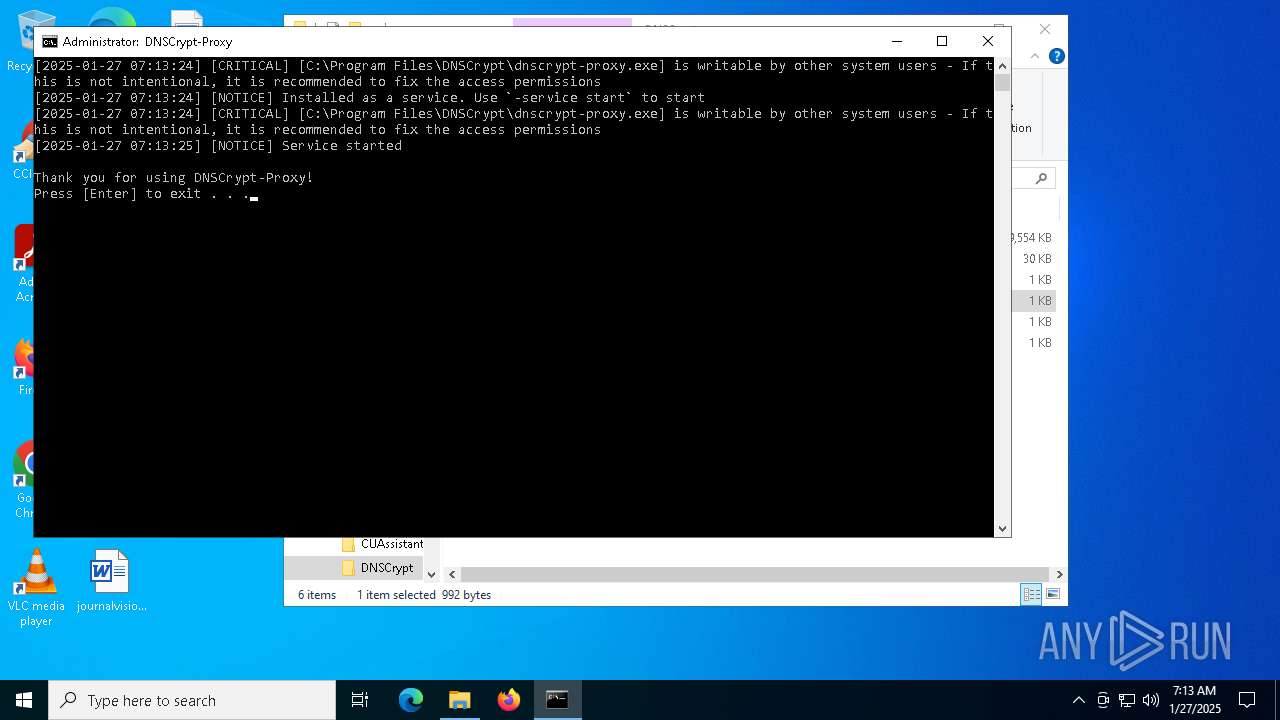
Executes as Windows Service
- VSSVC.exe (PID: 6228)
- dnscrypt-proxy.exe (PID: 6216)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6168)
Identifying current user with WHOAMI command
- cmd.exe (PID: 6932)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6932)
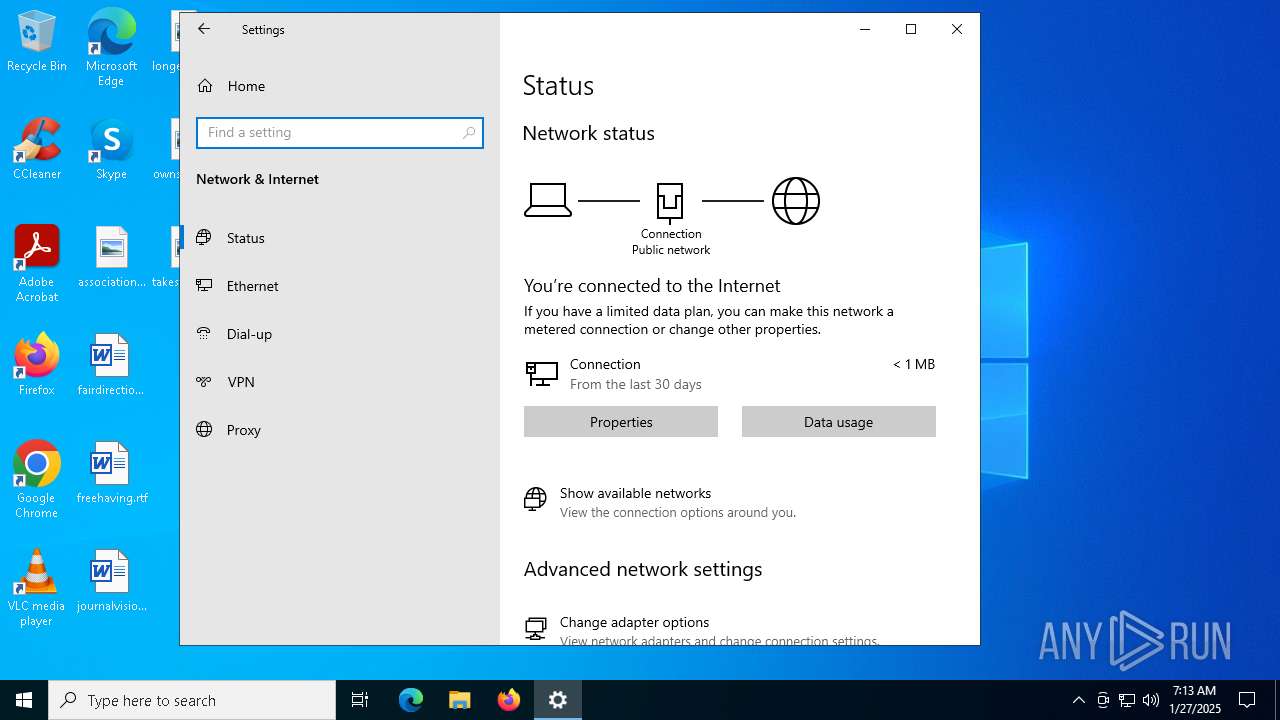
Connects to unusual port
- dnscrypt-proxy.exe (PID: 6216)
Adds/modifies Windows certificates
- dnscrypt-proxy.exe (PID: 6216)
INFO
Reads the computer name
- msiexec.exe (PID: 6168)
- dnscrypt-proxy.exe (PID: 6404)
- dnscrypt-proxy.exe (PID: 5308)
- dnscrypt-proxy.exe (PID: 6216)
Checks supported languages
- msiexec.exe (PID: 6168)
- dnscrypt-proxy.exe (PID: 6404)
- dnscrypt-proxy.exe (PID: 5308)
- dnscrypt-proxy.exe (PID: 6216)
An automatically generated document
- msiexec.exe (PID: 6096)
Manages system restore points
- SrTasks.exe (PID: 7108)
Creates a software uninstall entry
- msiexec.exe (PID: 6168)
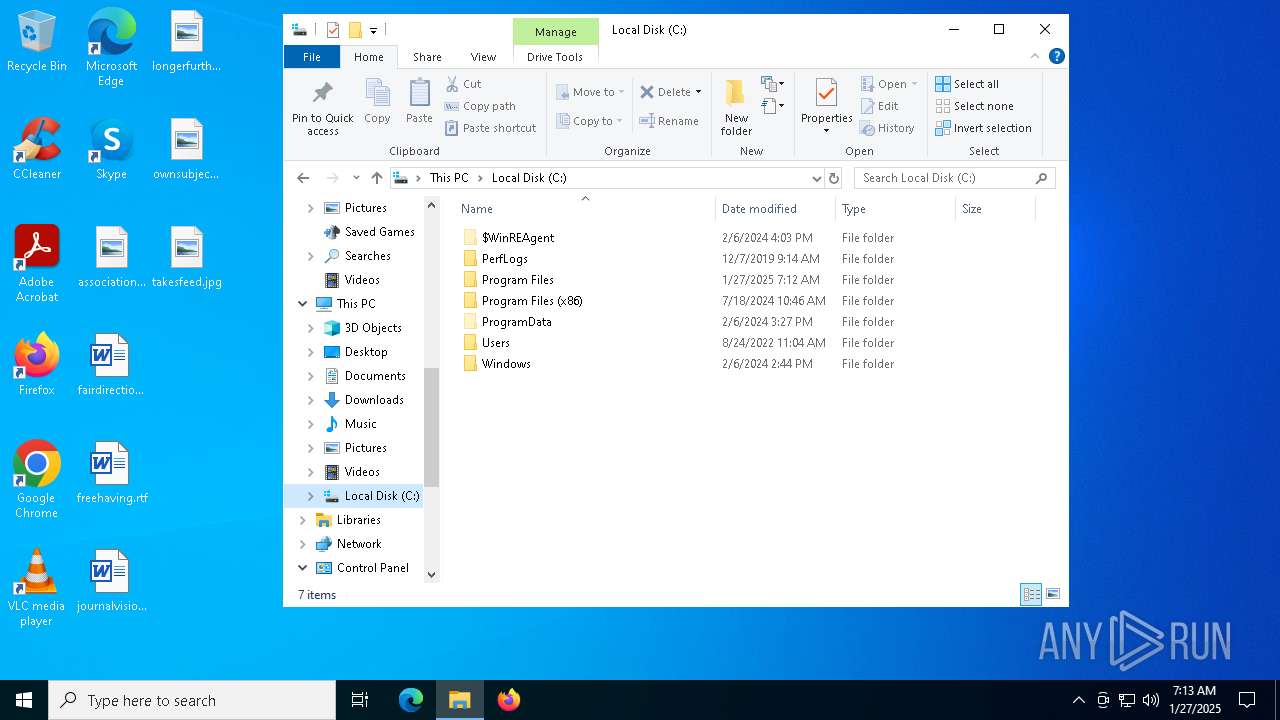
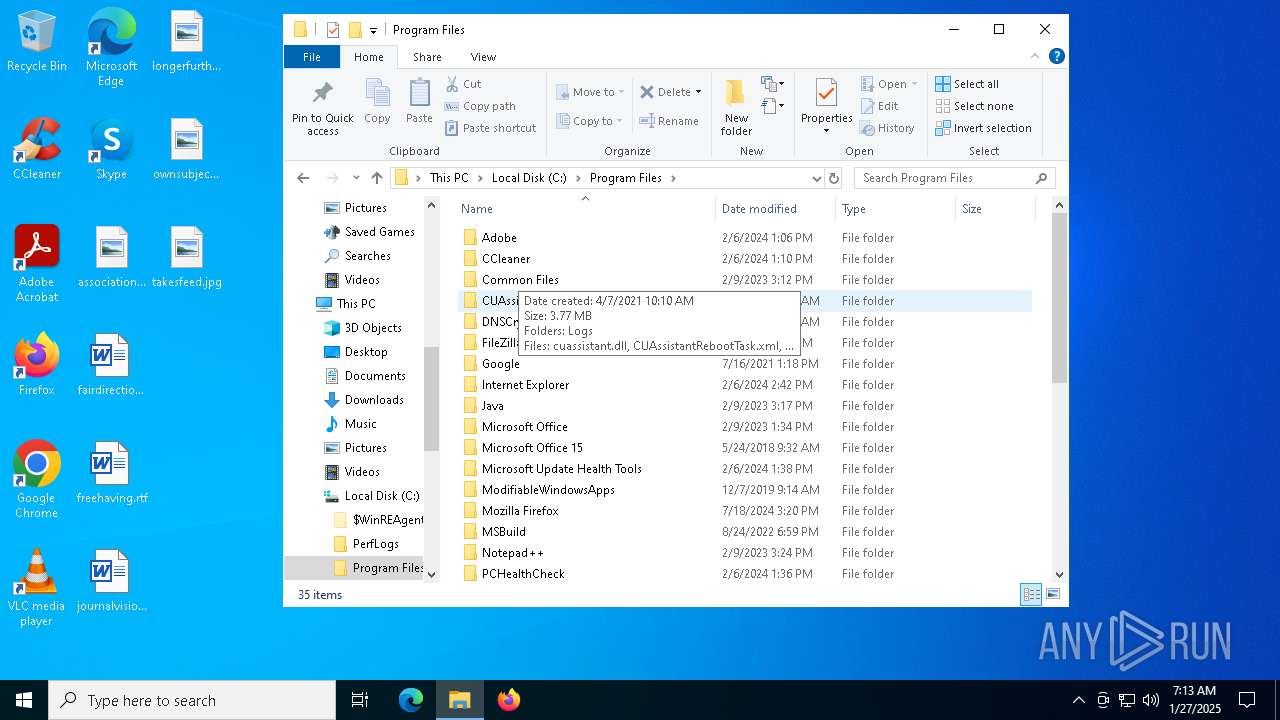
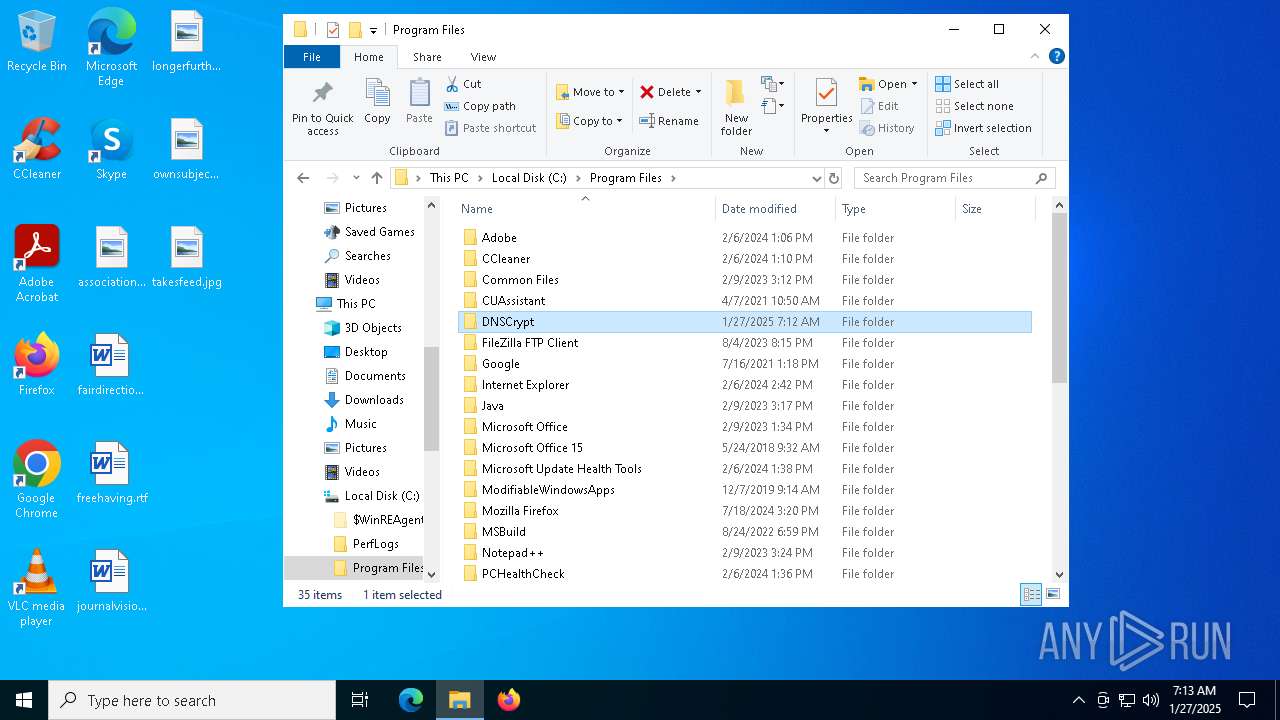
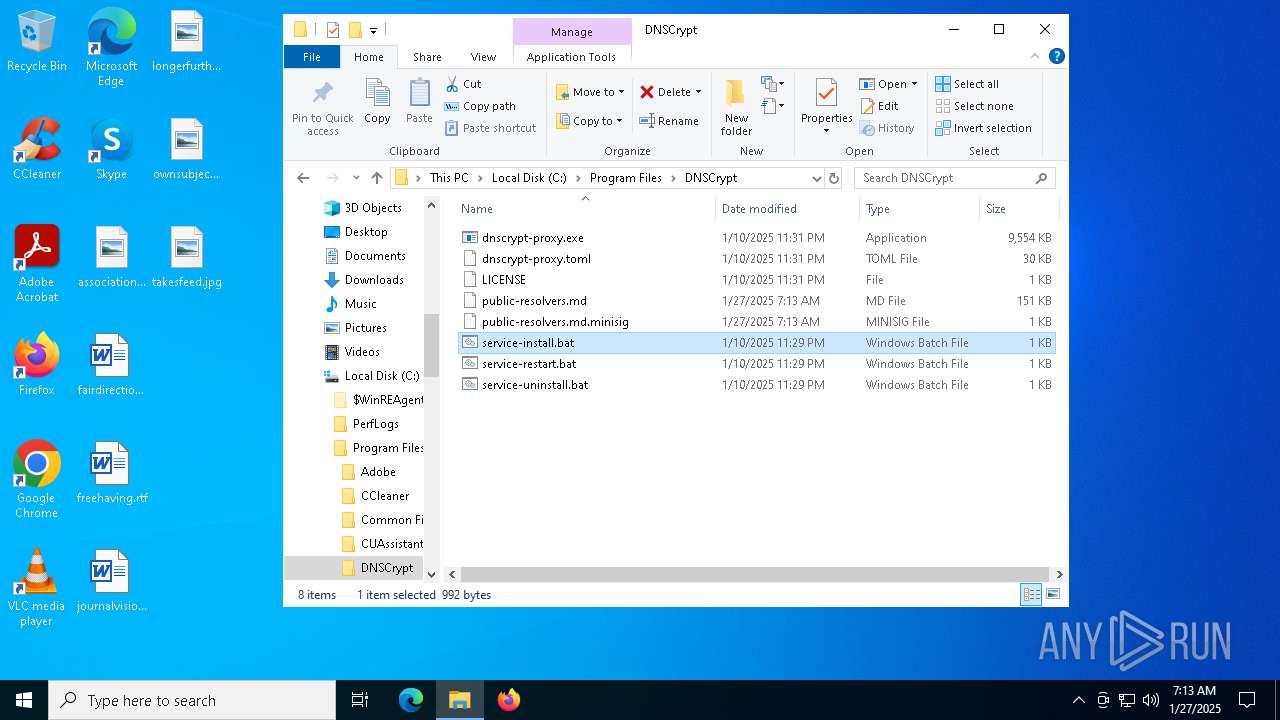
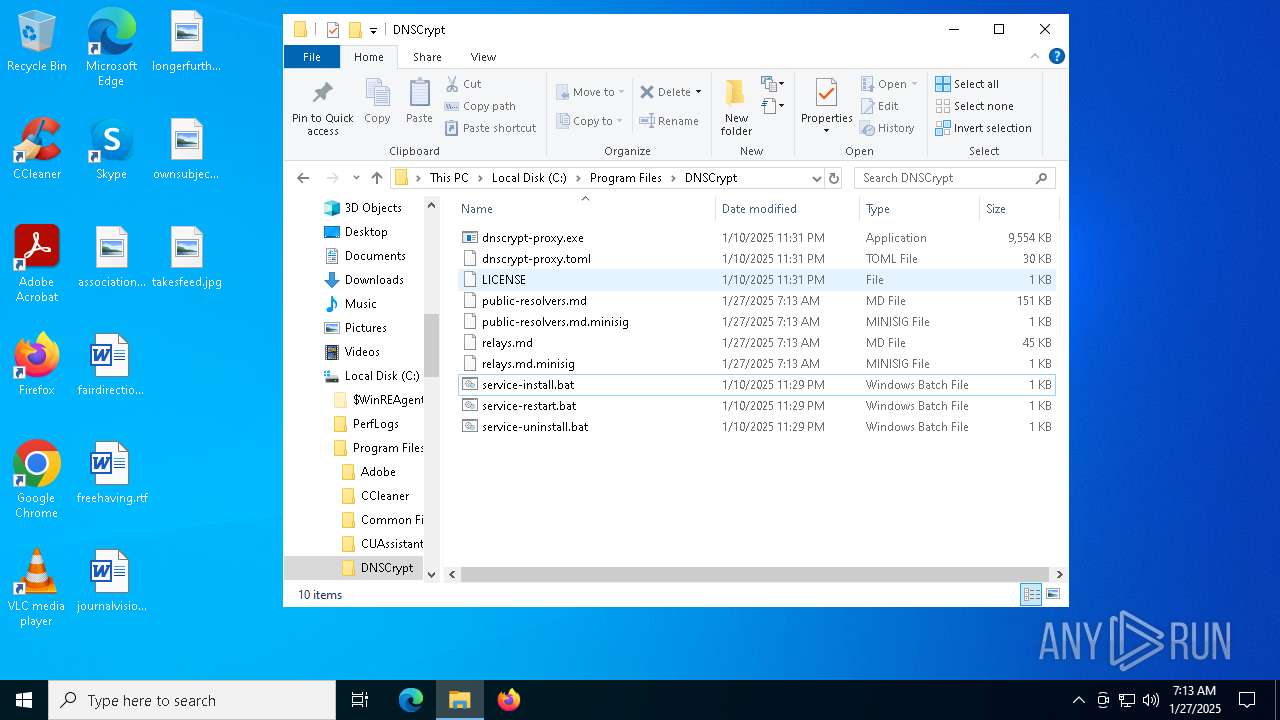
Executable content was dropped or overwritten
- msiexec.exe (PID: 6168)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 6396)
- explorer.exe (PID: 3620)
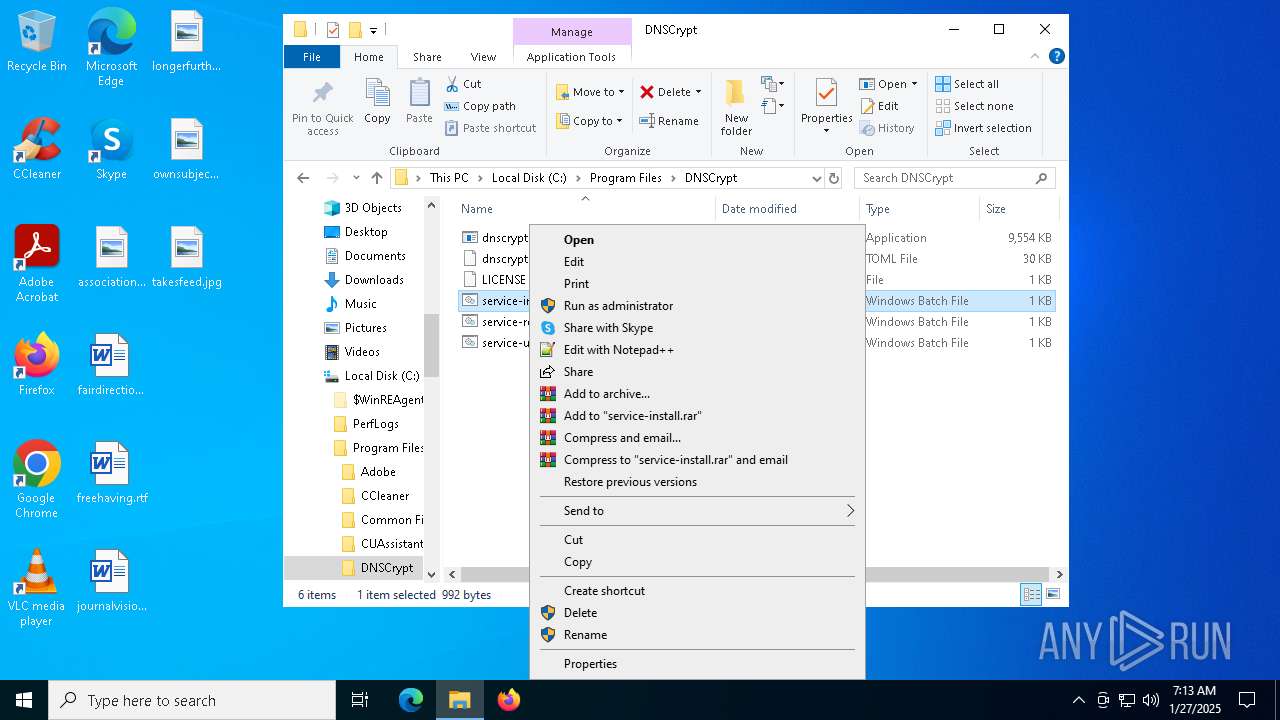
Manual execution by a user
- cmd.exe (PID: 6932)
- chrome.exe (PID: 6880)
Reads the software policy settings
- dnscrypt-proxy.exe (PID: 6216)
Creates files in the program directory
- dnscrypt-proxy.exe (PID: 6216)
Disables trace logs
- explorer.exe (PID: 3620)
Reads the machine GUID from the registry
- dnscrypt-proxy.exe (PID: 6216)
Checks transactions between databases Windows and Oracle
- explorer.exe (PID: 3620)
Application launched itself
- chrome.exe (PID: 6880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .mst | | | Windows SDK Setup Transform Script (88.7) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | dnscrypt-proxy |
| Author: | DNSCrypt |
| Keywords: | Installer |
| Comments: | Windows Installer Package |
| Template: | x64;1033 |
| RevisionNumber: | {1F360627-8094-4E9B-8823-A04D2348311F} |
| CreateDate: | 2025:01:10 23:38:22 |
| ModifyDate: | 2025:01:10 23:38:22 |
| Pages: | 200 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset () |
| Security: | Read-only recommended |
Total processes
177
Monitored processes
39
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=3444 --field-trial-handle=1980,i,5697748239488102582,2896648082064459616,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=3684 --field-trial-handle=1980,i,5697748239488102582,2896648082064459616,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=4332 --field-trial-handle=1980,i,5697748239488102582,2896648082064459616,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ff825cddc40,0x7ff825cddc4c,0x7ff825cddc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --mojo-platform-channel-handle=3296 --field-trial-handle=1980,i,5697748239488102582,2896648082064459616,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6116 --field-trial-handle=1980,i,5697748239488102582,2896648082064459616,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3620 | C:\WINDOWS\explorer.exe /factory,{5BD95610-9434-43C2-886C-57852CC8A120} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3580 --field-trial-handle=1980,i,5697748239488102582,2896648082064459616,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5920 --field-trial-handle=1980,i,5697748239488102582,2896648082064459616,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --mojo-platform-channel-handle=3324 --field-trial-handle=1980,i,5697748239488102582,2896648082064459616,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
25 014
Read events
24 113
Write events
862
Delete events
39
Modification events
| (PID) Process: | (6168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000678057D28A70DB01181800003C180000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000678057D28A70DB01181800003C180000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000F1B2B6D28A70DB01181800003C180000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000F1B2B6D28A70DB01181800003C180000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000C016B9D28A70DB01181800003C180000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000009FE1BDD28A70DB01181800003C180000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000EEC265D38A70DB01181800003C180000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000003F776AD38A70DB0118180000C0180000E8030000010000000000000000000000702EE4F71539E3408DE3B75A51DBA46A00000000000000000000000000000000 | |||
| (PID) Process: | (6228) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000CC7576D38A70DB015418000070180000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
15
Suspicious files
354
Text files
50
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6168 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
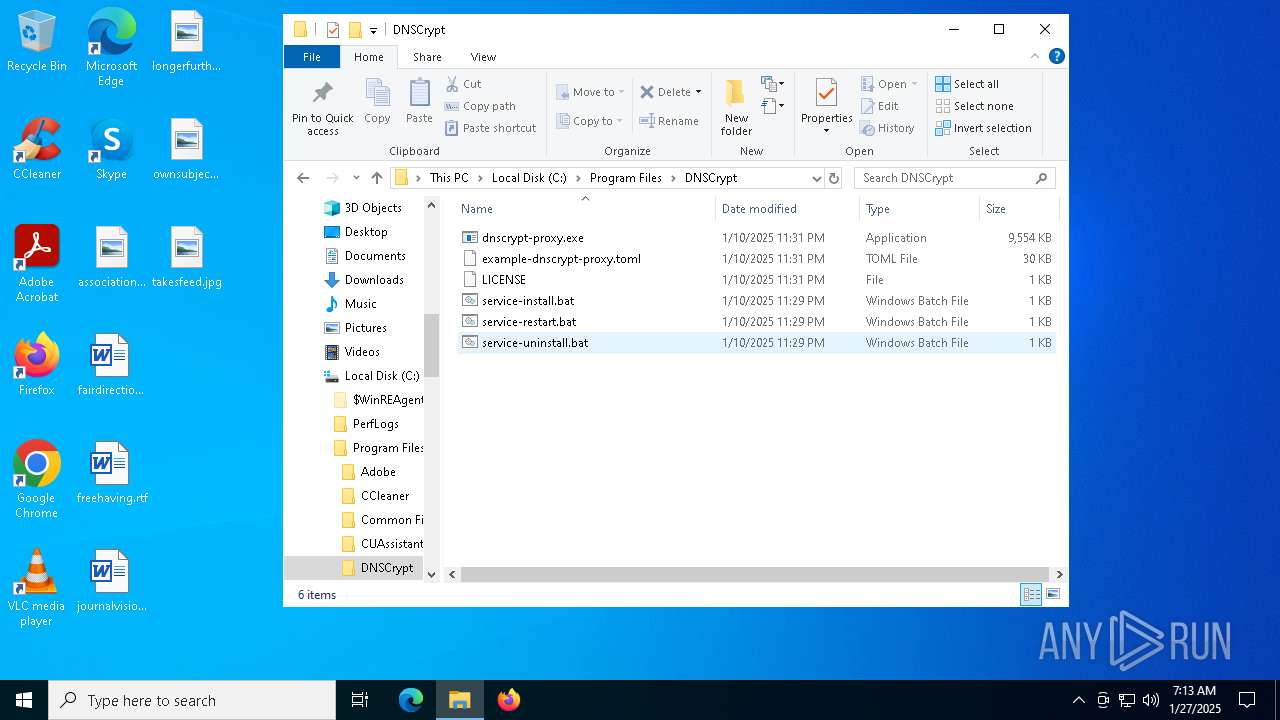
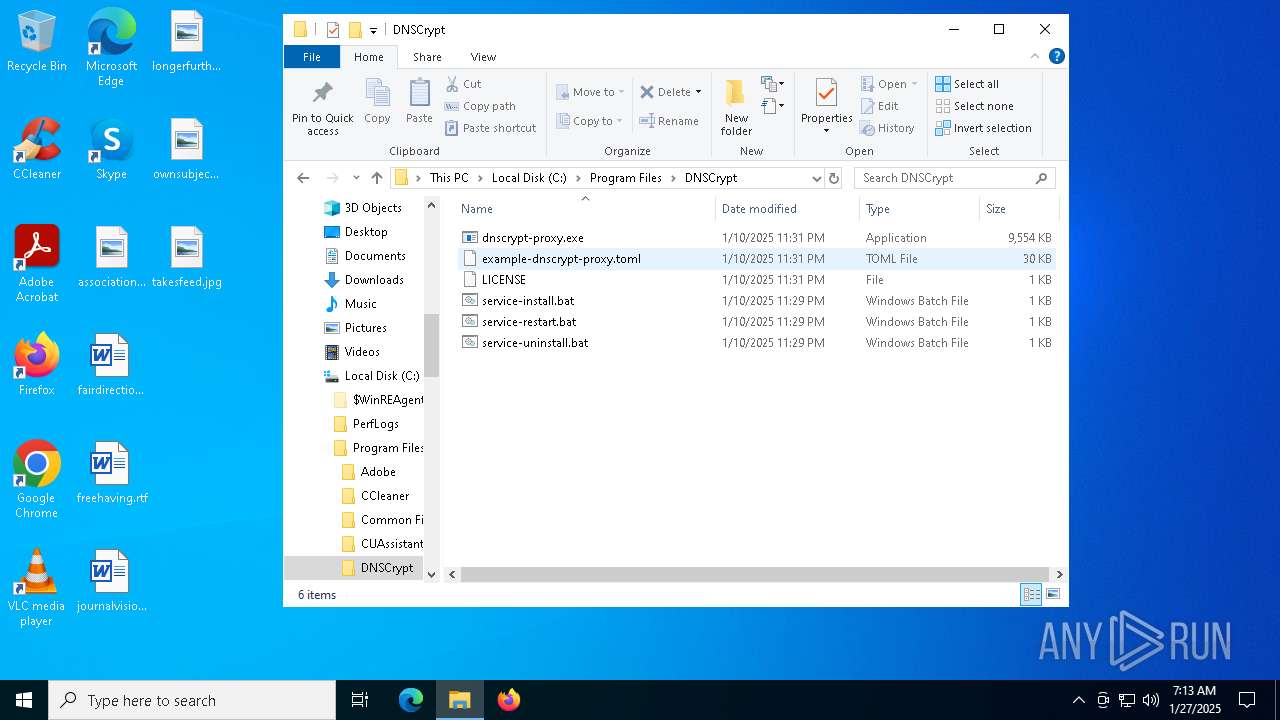
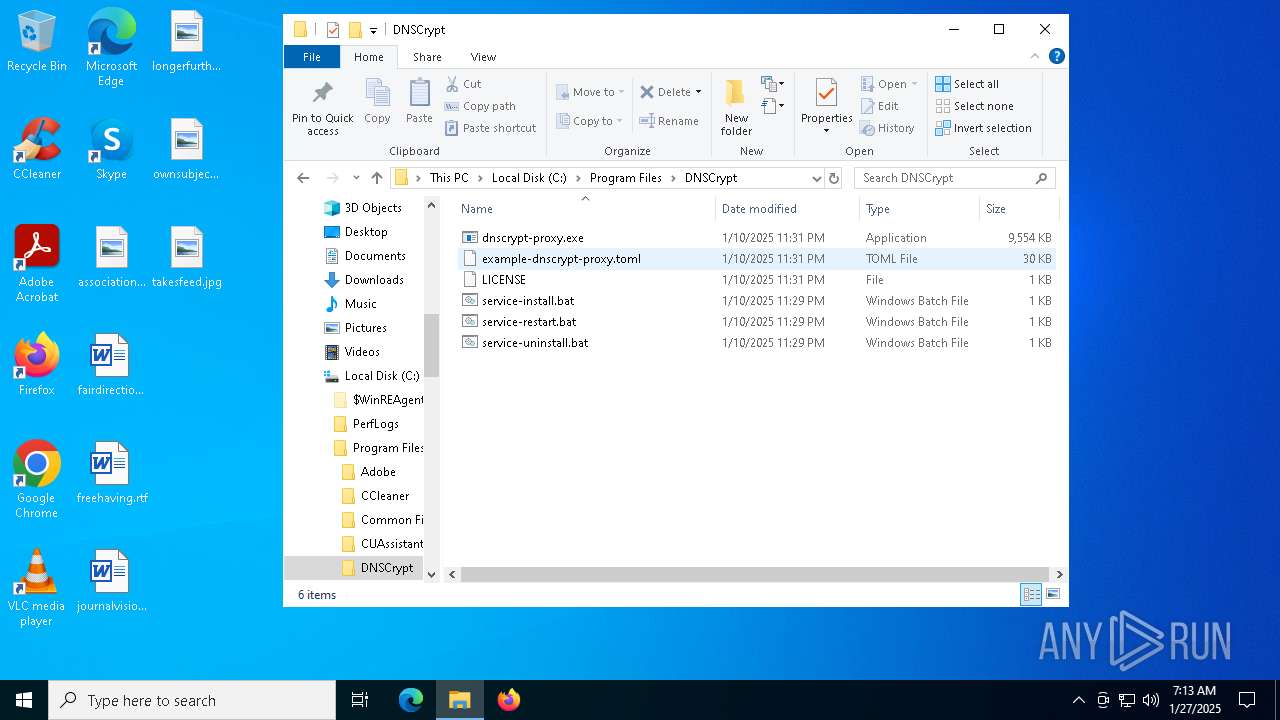
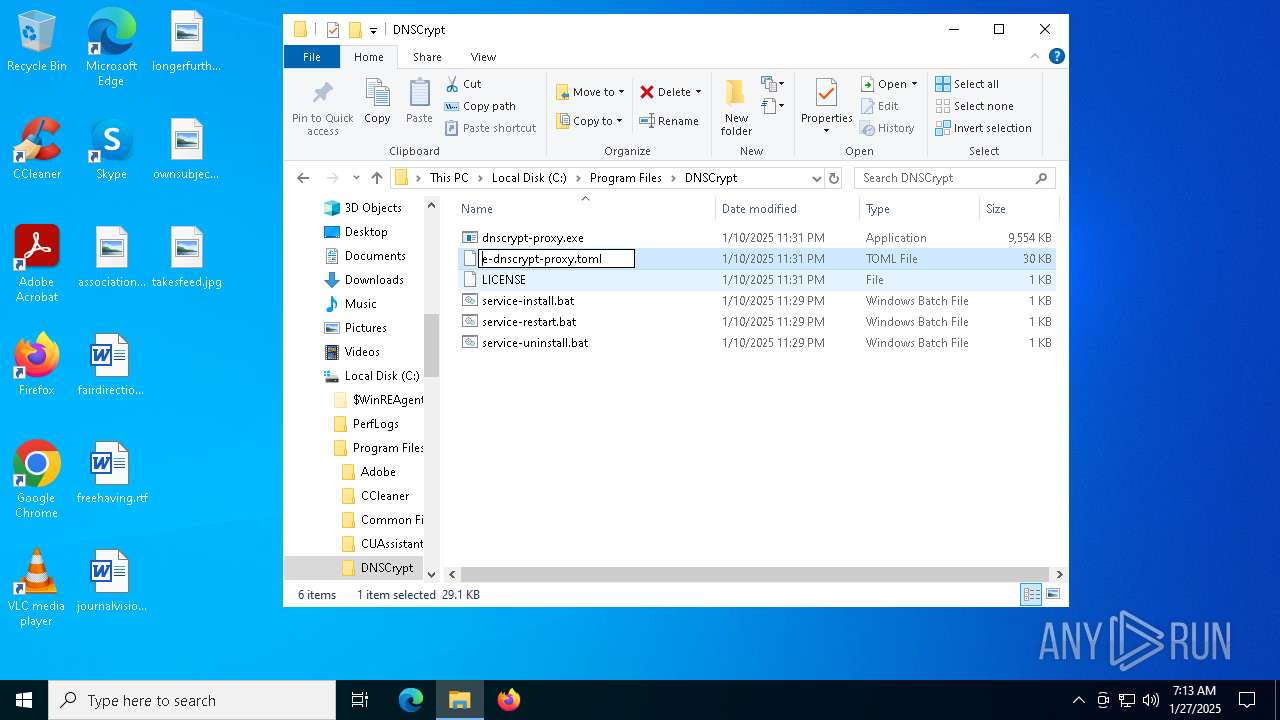
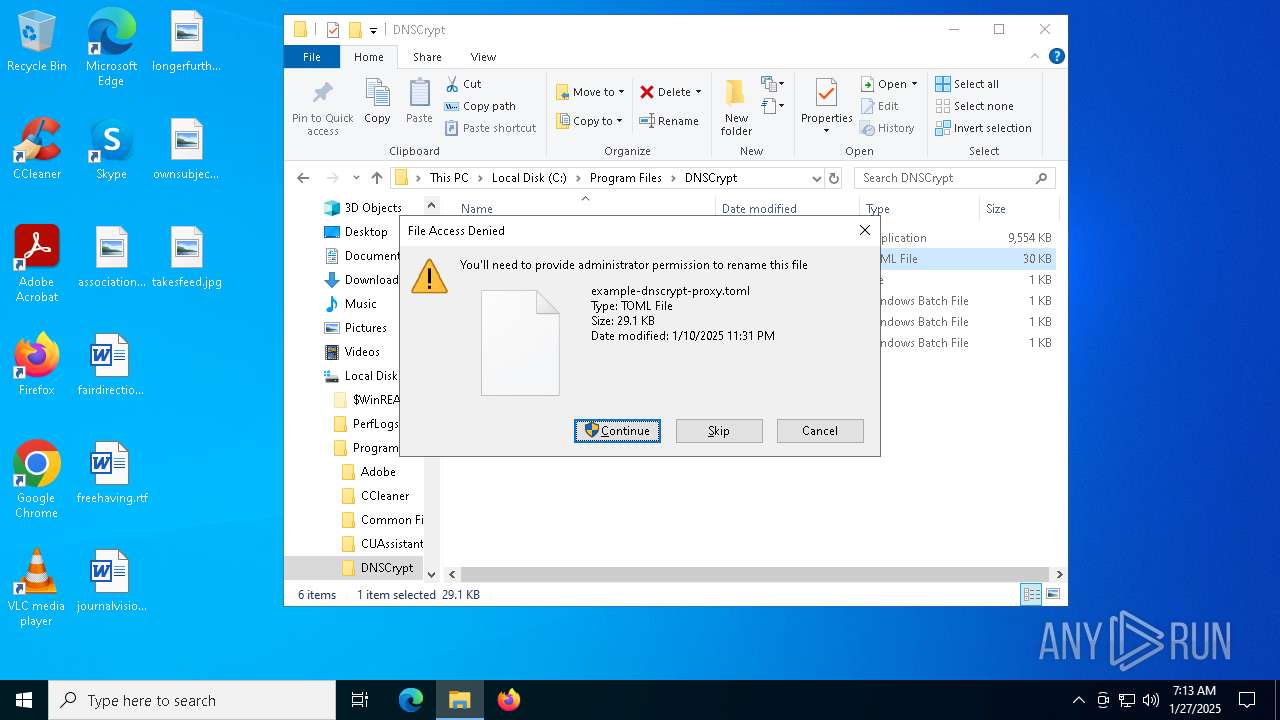
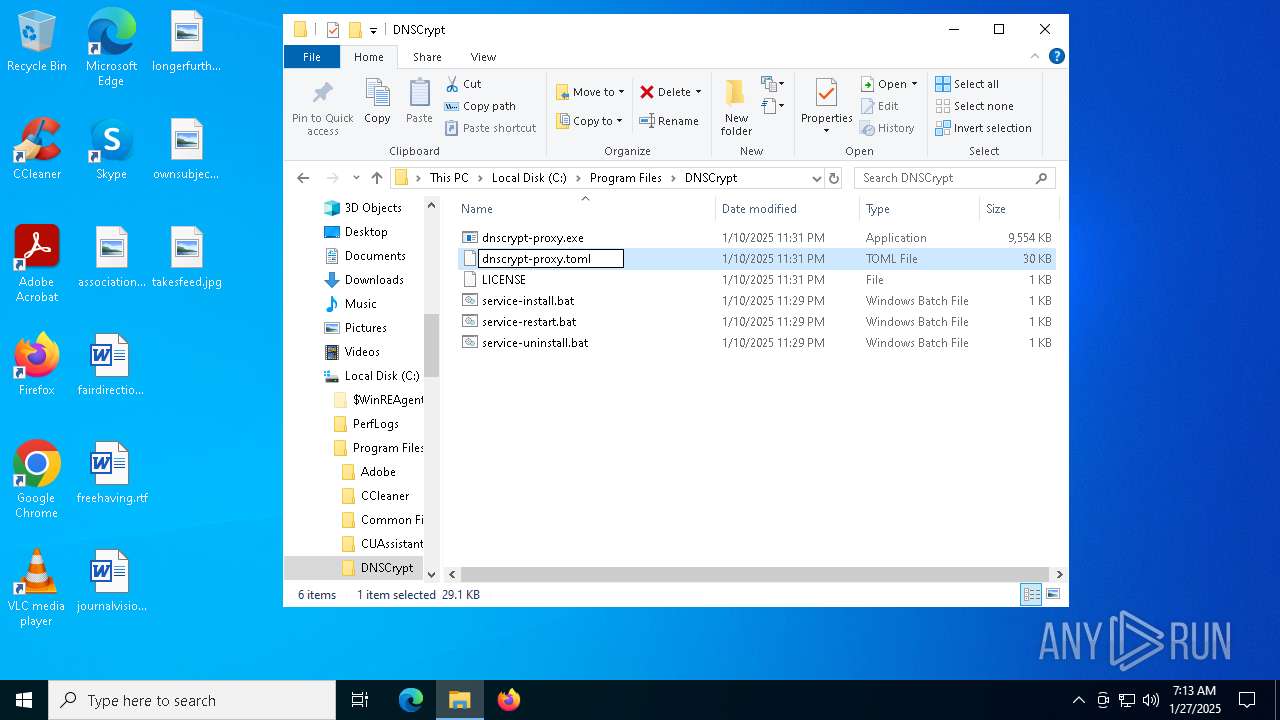
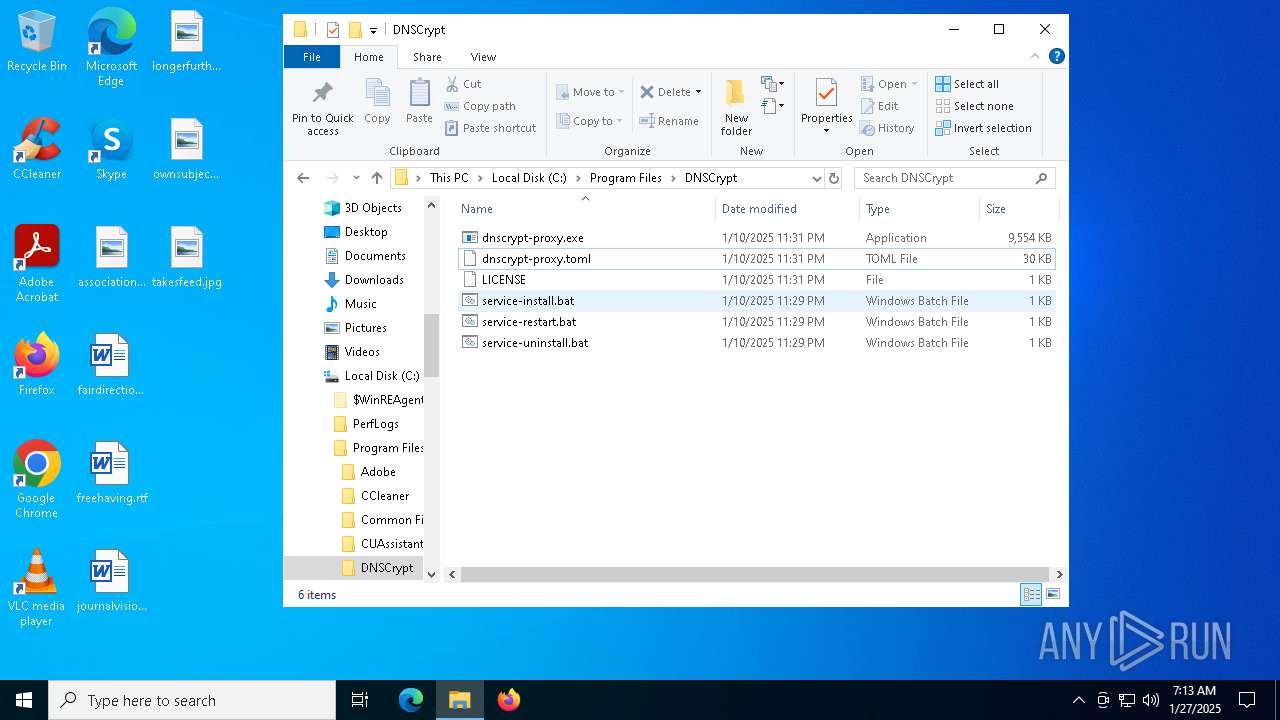
| 6168 | msiexec.exe | C:\Program Files\DNSCrypt\example-dnscrypt-proxy.toml | text | |
MD5:1C05C333FB7BF92CD322C3D56D7FD083 | SHA256:D25078E3FDB52602BC331B17D24EE81420A5556F62C8F087D7EACAE3559F288E | |||
| 6168 | msiexec.exe | C:\Windows\Installer\MSIC9FA.tmp | binary | |
MD5:5CAA2DAB72574AEB37F44E08DBBBC70D | SHA256:AB59EFB4CED6C20FD3BBB5428E224695B12E51055E29B54CECD5AEFC62078679 | |||
| 6168 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:D72EBDA8E1E1AFF96F9340EE0B9A513D | SHA256:3D1B5355D9D4B55A6EAEAF81B8332DBE1443D6EB0B7B1863447F2808E90D2936 | |||
| 6168 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:E33901084BADC5CAF145B5AFB807D541 | SHA256:0C6960B872EB583243F58170394D7F21B62A5668FE38BE48E7B5FD0FFA6B8F14 | |||
| 6168 | msiexec.exe | C:\Program Files\DNSCrypt\service-restart.bat | text | |
MD5:48D5D506079190F17336D7965B7F8F64 | SHA256:CE3EB0DF48AB86C88D26FC0CB9F953FDEF7B3ECD8BE07FAF402E6635A4FFB6D6 | |||
| 6168 | msiexec.exe | C:\Windows\Installer\13c662.msi | executable | |
MD5:CE2F9A9B44C807C55CA722D60CCE57CD | SHA256:4F534006A0C02FBEE29235B542C5F563DAD9CFD893BF7831463C2E8A00B70B3E | |||
| 6168 | msiexec.exe | C:\Windows\Temp\~DFED2338ED3E54632B.TMP | binary | |
MD5:E33901084BADC5CAF145B5AFB807D541 | SHA256:0C6960B872EB583243F58170394D7F21B62A5668FE38BE48E7B5FD0FFA6B8F14 | |||
| 6168 | msiexec.exe | C:\Program Files\DNSCrypt\dnscrypt-proxy.exe | executable | |
MD5:E948264DA336F6BF3B9C3D3937468493 | SHA256:6F08EDE08B3BF940942DFC37D91DB02F425F05791A92762E754918111C204E19 | |||
| 6168 | msiexec.exe | C:\Program Files\DNSCrypt\service-install.bat | text | |
MD5:AB87D533C77929B32F332FB797D0A1C2 | SHA256:04C1AC6ED9EEA7C56C82BB78013F5F5D8ED1DD84C8B9CAB8234FCA552402662A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
740
DNS requests
25
Threats
42
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
900 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
900 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6480 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6100 | SystemSettings.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6100 | SystemSettings.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
236 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.21.65.154:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
1176 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1752 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
900 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6216 | dnscrypt-proxy.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6216 | dnscrypt-proxy.exe | Generic Protocol Command Decode | SURICATA QUIC error on data |
6216 | dnscrypt-proxy.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6216 | dnscrypt-proxy.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6216 | dnscrypt-proxy.exe | Generic Protocol Command Decode | SURICATA QUIC error on data |
6216 | dnscrypt-proxy.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6216 | dnscrypt-proxy.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6216 | dnscrypt-proxy.exe | Misc activity | ET INFO Observed DNS over HTTPS Domain in TLS SNI (freedns .controld .com) |
6216 | dnscrypt-proxy.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6216 | dnscrypt-proxy.exe | Misc activity | ET INFO Observed DNS Over HTTPS Domain in TLS SNI (open .dns0 .eu) |