| File name: | Verify.exe |
| Full analysis: | https://app.any.run/tasks/d6c19ead-0be9-4f02-957c-2e78bc2a9ca1 |
| Verdict: | Malicious activity |
| Analysis date: | March 02, 2023, 14:15:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 117305D46C5011B671EA32B1EF6556E1 |
| SHA1: | C088FC138D5FB0978BAD858AD0AF662F4B29ED61 |
| SHA256: | 4F418EB8CD167031987130A169638843EB0A6ED1E93E5F4B947226B32B444609 |
| SSDEEP: | 6144:iNeeqnuqGLmpTIhwLKQrU4PyZn9pi3A4qAFouX/bEH1aoV/A96aV:iNeSqrpkiy4YK34uX/IH1aoV66a |
MALICIOUS
Drops the executable file immediately after the start
- Verify.exe (PID: 3288)
Application was dropped or rewritten from another process
- RapidCRC.exe (PID: 3792)
SUSPICIOUS
Executable content was dropped or overwritten
- Verify.exe (PID: 3288)
Executing commands from a ".bat" file
- Verify.exe (PID: 3288)
Starts CMD.EXE for commands execution
- Verify.exe (PID: 3288)
INFO
Checks supported languages
- Verify.exe (PID: 3288)
- RapidCRC.exe (PID: 3792)
- wmpnscfg.exe (PID: 3740)
The process checks LSA protection
- RapidCRC.exe (PID: 3792)
- wmpnscfg.exe (PID: 3740)
Reads the machine GUID from the registry
- RapidCRC.exe (PID: 3792)
- wmpnscfg.exe (PID: 3740)
Create files in a temporary directory
- Verify.exe (PID: 3288)
Reads the computer name
- RapidCRC.exe (PID: 3792)
- wmpnscfg.exe (PID: 3740)
Creates files or folders in the user directory
- RapidCRC.exe (PID: 3792)
Manual execution by a user
- wmpnscfg.exe (PID: 3740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (61.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.8) |
| .exe | | | Win32 Executable (generic) (10.1) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.5) |
EXIF
EXE
| Comments: | - |
|---|---|
| ProductVersion: | 0. 0. 0. 0 |
| ProductName: | Verify Tool |
| OriginalFileName: | Verify.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Masquerade Repack |
| InternalName: | - |
| FileVersion: | 0. 0. 0. 0 |
| FileDescription: | Verify Tool |
| CompanyName: | Masquerade Repack |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0xaab10 |
| UninitializedDataSize: | 425984 |
| InitializedDataSize: | 4096 |
| CodeSize: | 270336 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 2016:05:10 22:18:20+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-May-2016 22:18:20 |
| Detected languages: |
|
| CompanyName: | Masquerade Repack |
| FileDescription: | Verify Tool |
| FileVersion: | 0. 0. 0. 0 |
| InternalName: | - |
| LegalCopyright: | Masquerade Repack |
| LegalTrademarks: | - |
| OriginalFilename: | Verify.exe |
| ProductName: | Verify Tool |
| ProductVersion: | 0. 0. 0. 0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 10-May-2016 22:18:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00068000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00069000 | 0x00042000 | 0x00041E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.76347 |
.rsrc | 0x000AB000 | 0x00001000 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.38782 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.23888 | 768 | Latin 1 / Western European | English - United States | RT_VERSION |
99 | 3 | 8 | Latin 1 / Western European | UNKNOWN | UNKNOWN |
4090 | 7.56621 | 1732 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 7.33273 | 508 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 6.74099 | 204 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 7.19939 | 376 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 7.48666 | 916 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 7.50832 | 860 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4096 | 7.39598 | 640 | Latin 1 / Western European | UNKNOWN | RT_STRING |
ITEMS | 0 | 538226 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
KERNEL32.DLL |
SHFolder.dll |
advapi32.dll |
oleaut32.dll |
user32.dll |
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3288 | "C:\Users\admin\AppData\Local\Temp\Verify.exe" | C:\Users\admin\AppData\Local\Temp\Verify.exe | Explorer.EXE | ||||||||||||
User: admin Company: Masquerade Repack Integrity Level: MEDIUM Description: Verify Tool Exit code: 0 Version: 0. 0. 0. 0 Modules
| |||||||||||||||
| 3600 | cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\8DJCU5ML.bat" "C:\Users\admin\AppData\Local\Temp\Verify.exe" " | C:\Windows\system32\cmd.exe | — | Verify.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3740 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
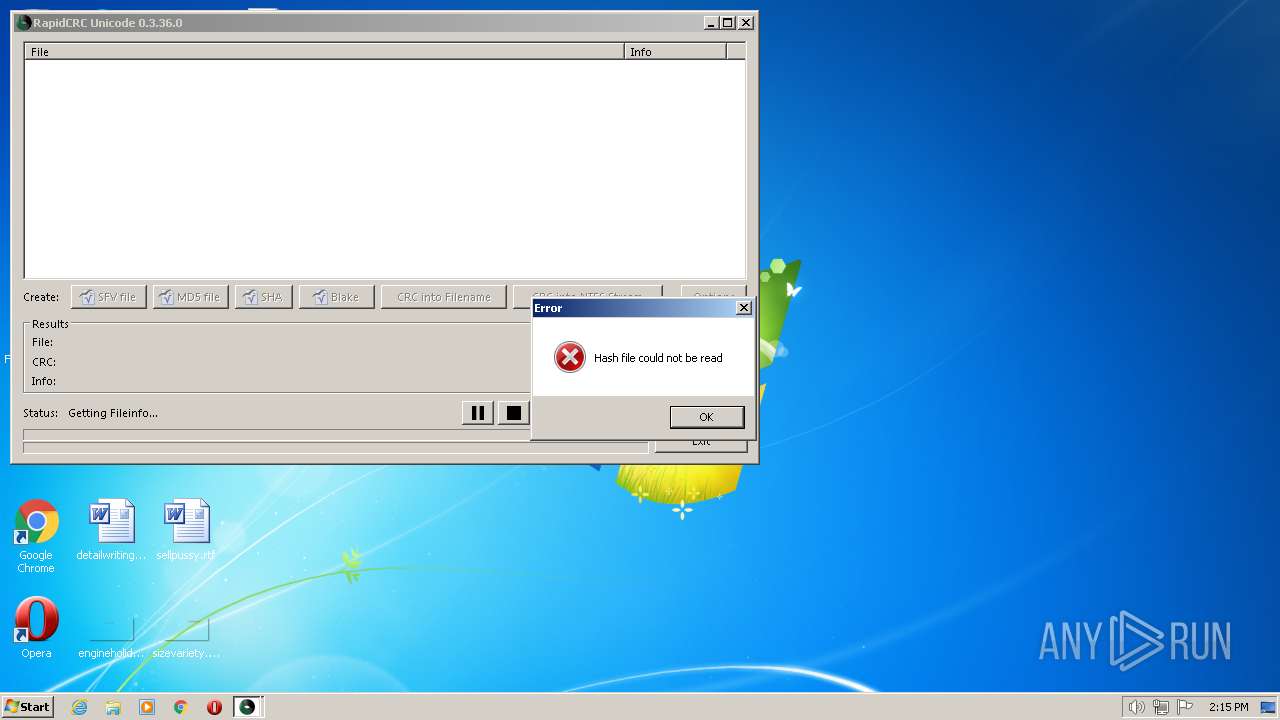
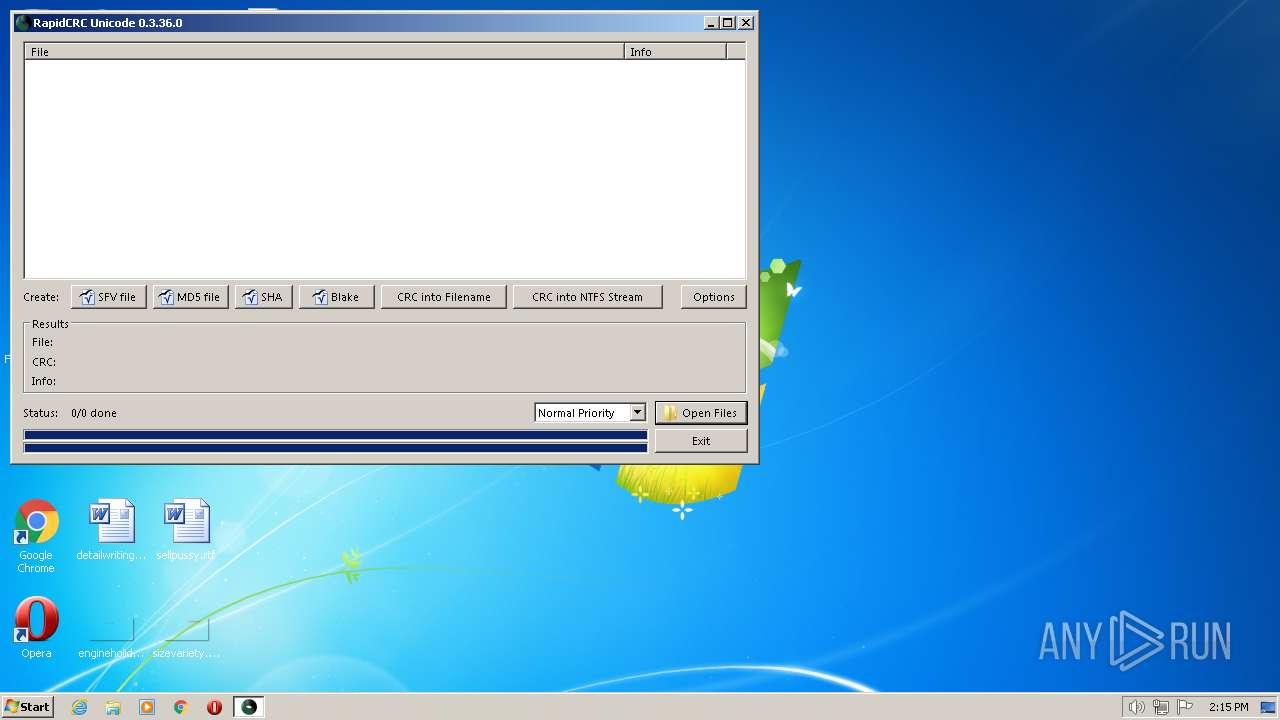
| 3792 | "C:\Users\admin\AppData\Local\Temp\\qb10C0D75.E6\rapidcrc.exe" "C:\Users\admin\AppData\Local\Temp\masquerade.md5" | C:\Users\admin\AppData\Local\Temp\qb10C0D75.E6\RapidCRC.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: RapidCRC Unicode Exit code: 0 Version: 0.3.36.0 Modules
| |||||||||||||||
Total events
226
Read events
204
Write events
16
Delete events
6
Modification events
| (PID) Process: | (3740) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{50FF6C9D-1B5A-41D6-8BB0-71979871A7E9}\{6892E7D5-ABAC-46AB-81CF-DF3BFE79A5EE} |
| Operation: | write | Name: | Reason |
Value: 565 | |||
| (PID) Process: | (3740) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{50FF6C9D-1B5A-41D6-8BB0-71979871A7E9}\{6892E7D5-ABAC-46AB-81CF-DF3BFE79A5EE} |
| Operation: | write | Name: | ID |
Value: S-1-5-21-1302019708-1500728564-335382590-1000 | |||
| (PID) Process: | (3740) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{50FF6C9D-1B5A-41D6-8BB0-71979871A7E9}\{6892E7D5-ABAC-46AB-81CF-DF3BFE79A5EE} |
| Operation: | write | Name: | Data |
Value: ignored | |||
| (PID) Process: | (3740) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{50FF6C9D-1B5A-41D6-8BB0-71979871A7E9}\{6892E7D5-ABAC-46AB-81CF-DF3BFE79A5EE} |
| Operation: | write | Name: | Scope |
Value: ignored | |||
| (PID) Process: | (3740) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{B8ECC31C-9278-4C55-A213-F19A3B41AC3E}\{6892E7D5-ABAC-46AB-81CF-DF3BFE79A5EE} |
| Operation: | write | Name: | Reason |
Value: 565 | |||
| (PID) Process: | (3740) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{B8ECC31C-9278-4C55-A213-F19A3B41AC3E}\{6892E7D5-ABAC-46AB-81CF-DF3BFE79A5EE} |
| Operation: | write | Name: | ID |
Value: S-1-5-21-1302019708-1500728564-335382590-1000 | |||
| (PID) Process: | (3740) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{B8ECC31C-9278-4C55-A213-F19A3B41AC3E}\{6892E7D5-ABAC-46AB-81CF-DF3BFE79A5EE} |
| Operation: | write | Name: | Data |
Value: ignored | |||
| (PID) Process: | (3740) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{50FF6C9D-1B5A-41D6-8BB0-71979871A7E9}\{6892E7D5-ABAC-46AB-81CF-DF3BFE79A5EE} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3740) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{B8ECC31C-9278-4C55-A213-F19A3B41AC3E}\{6892E7D5-ABAC-46AB-81CF-DF3BFE79A5EE} |
| Operation: | write | Name: | Scope |
Value: ignored | |||
| (PID) Process: | (3740) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{50FF6C9D-1B5A-41D6-8BB0-71979871A7E9} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
2
Suspicious files
2
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3792 | RapidCRC.exe | C:\Users\admin\AppData\Roaming\RapidCRC\options_unicode.bin | binary | |
MD5:8346B07054330A26A3D22FAD398BE24E | SHA256:F68470CA99FFC81139F6873502DFBA08DB5067F868CC2A9732D4104E84D4034D | |||
| 3288 | Verify.exe | C:\Users\admin\AppData\Local\Temp\8DJCU5ML.bat | text | |
MD5:08463D5D07166B8BA0CD7E4EAB2FDDCB | SHA256:3D7F760899C327D769BBDB879899423CC15A71C68A06122635B204A71362D066 | |||
| 3288 | Verify.exe | C:\Users\admin\AppData\Local\Temp\qb10C0D75.E6\masquerade.md5 | text | |
MD5:0963192BA205BDE7C7691C0876F2A1C0 | SHA256:6063ECB8DC14676D60FB033D5BDC3A70BB09D1CD83C51079FCCF056F6E9D4C58 | |||
| 3288 | Verify.exe | C:\Users\admin\AppData\Local\Temp\qb10C0D75.E6\RapidCRC.exe | executable | |
MD5:713B258DBBF1156E5856DF19BF2317BC | SHA256:DB4B322099CECD8D9E55F4F7674B1C48F69A4E2CCE4B784BA9F1CD8248C510D8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report