| File name: | Procmon.exe |
| Full analysis: | https://app.any.run/tasks/60abda5f-4238-4d1d-af74-52e9af4f4cd1 |
| Verdict: | Malicious activity |
| Analysis date: | December 19, 2018, 05:54:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 42D273490F10FA08B60BF51BFD66BA3B |
| SHA1: | 68BCDD6164F22B571149C3A95CDA0A5729B3BA38 |
| SHA256: | 4F3156E1AF647DB77781B21AA701E390F28FB08818BD6E673806B97C8B395930 |
| SSDEEP: | 49152:gVlvpIwlozsEbQfXvBIsyBjuv11f1jKwsRAVnB7l:AhpEzsE0vJTCjut1qyVnT |
MALICIOUS
Loads the Task Scheduler COM API
- Procmon.exe (PID: 3792)
SUSPICIOUS
Modifies the open verb of a shell class
- Procmon.exe (PID: 3792)
Application launched itself
- Procmon.exe (PID: 3112)
Creates files in the driver directory
- Procmon.exe (PID: 3792)
Creates files in the Windows directory
- Procmon.exe (PID: 3792)
Creates or modifies windows services
- Procmon.exe (PID: 3792)
Removes files from Windows directory
- Procmon.exe (PID: 3792)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:13 00:29:25+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 585216 |
| InitializedDataSize: | 1594368 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x755cb |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.50.0.0 |
| ProductVersionNumber: | 3.50.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Process Monitor |
| FileVersion: | 3.5 |
| InternalName: | Process Monitor |
| LegalCopyright: | Copyright © 1996-2018 Mark Russinovich |
| OriginalFileName: | Process Monitor |
| ProductName: | Sysinternals Procmon |
| ProductVersion: | 3.5 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Feb-2018 23:29:25 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Process Monitor |
| FileVersion: | 3.50 |
| InternalName: | Process Monitor |
| LegalCopyright: | Copyright © 1996-2018 Mark Russinovich |
| OriginalFilename: | Process Monitor |
| ProductName: | Sysinternals Procmon |
| ProductVersion: | 3.50 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 12-Feb-2018 23:29:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008EC87 | 0x0008EE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5114 |
.rdata | 0x00090000 | 0x0002BB18 | 0x0002BC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.41608 |
.data | 0x000BC000 | 0x0000977C | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.78601 |
.rsrc | 0x000C6000 | 0x00146C08 | 0x00146E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10668 |
.reloc | 0x0020D000 | 0x0000900C | 0x00009200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.69287 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.16291 | 2084 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.26098 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 4.09301 | 1384 | UNKNOWN | English - United States | RT_ICON |
4 | 5.41795 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 5.17862 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 4.26977 | 1128 | UNKNOWN | English - United States | RT_ICON |
7 | 1.57156 | 296 | UNKNOWN | English - United States | RT_ICON |
8 | 1.61781 | 296 | UNKNOWN | English - United States | RT_ICON |
9 | 1.77545 | 296 | UNKNOWN | English - United States | RT_ICON |
10 | 1.88589 | 296 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
FLTLIB.DLL |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
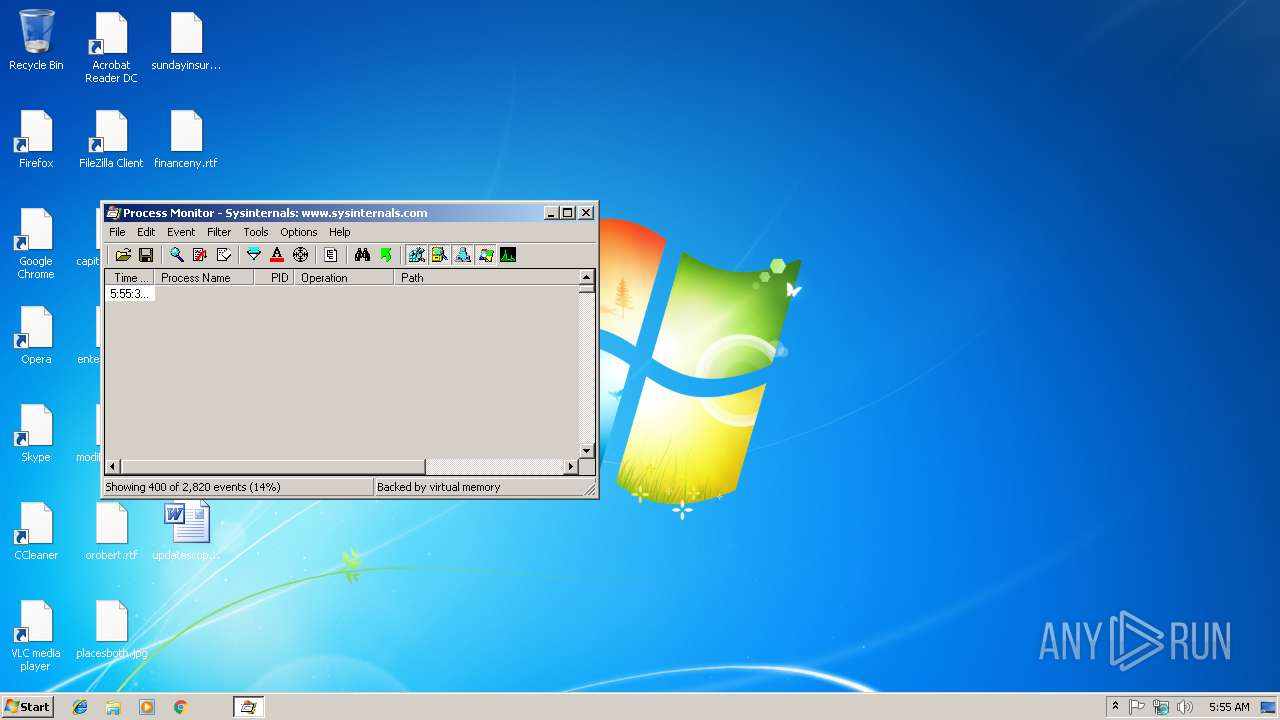
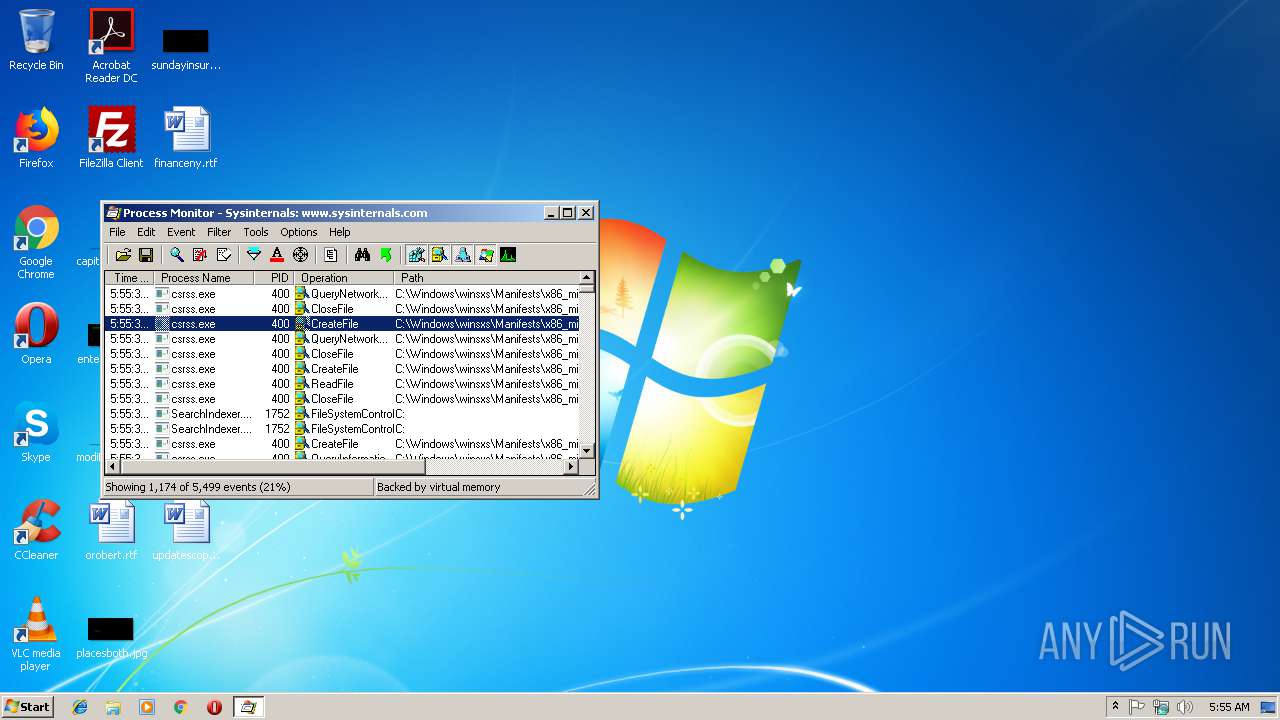
Total processes
37
Monitored processes
2
Malicious processes
2
Suspicious processes
0
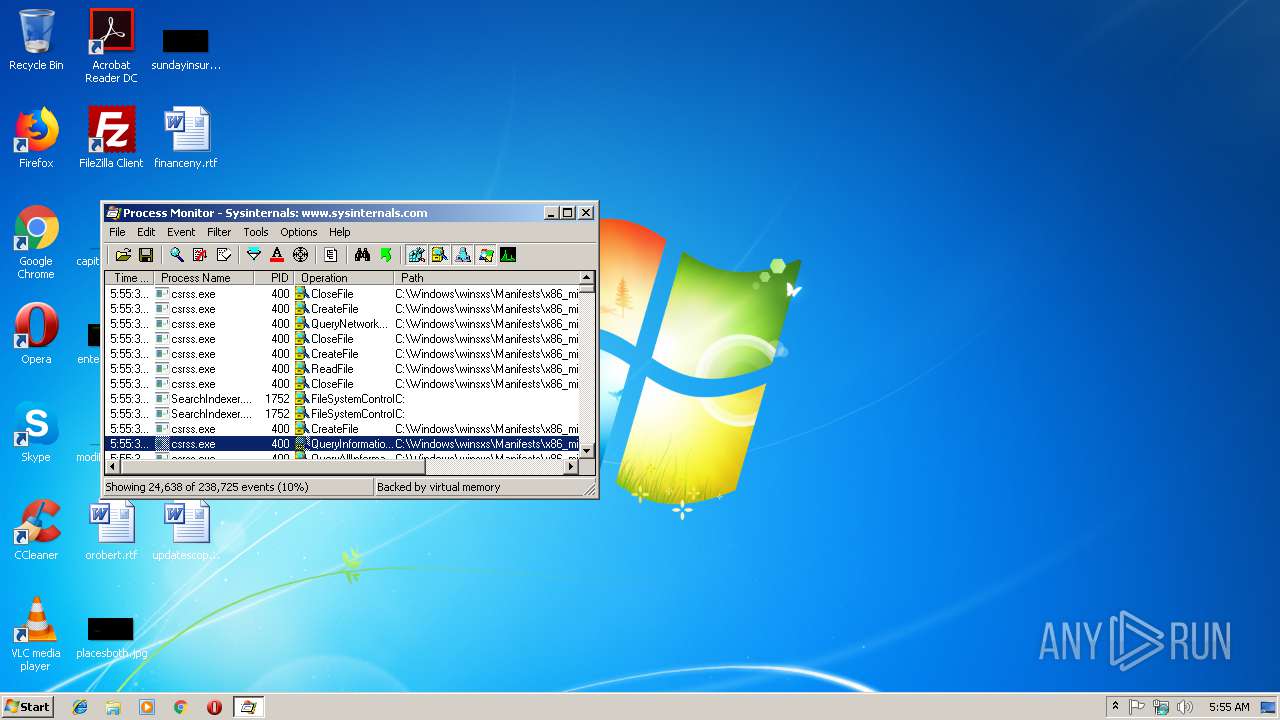
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3112 | "C:\Users\admin\AppData\Local\Temp\Procmon.exe" | C:\Users\admin\AppData\Local\Temp\Procmon.exe | — | explorer.exe | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Process Monitor Exit code: 0 Version: 3.50 Modules
| |||||||||||||||
| 3792 | "C:\Users\admin\AppData\Local\Temp\Procmon.exe" | C:\Users\admin\AppData\Local\Temp\Procmon.exe | Procmon.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: HIGH Description: Process Monitor Exit code: 0 Version: 3.50 Modules
| |||||||||||||||
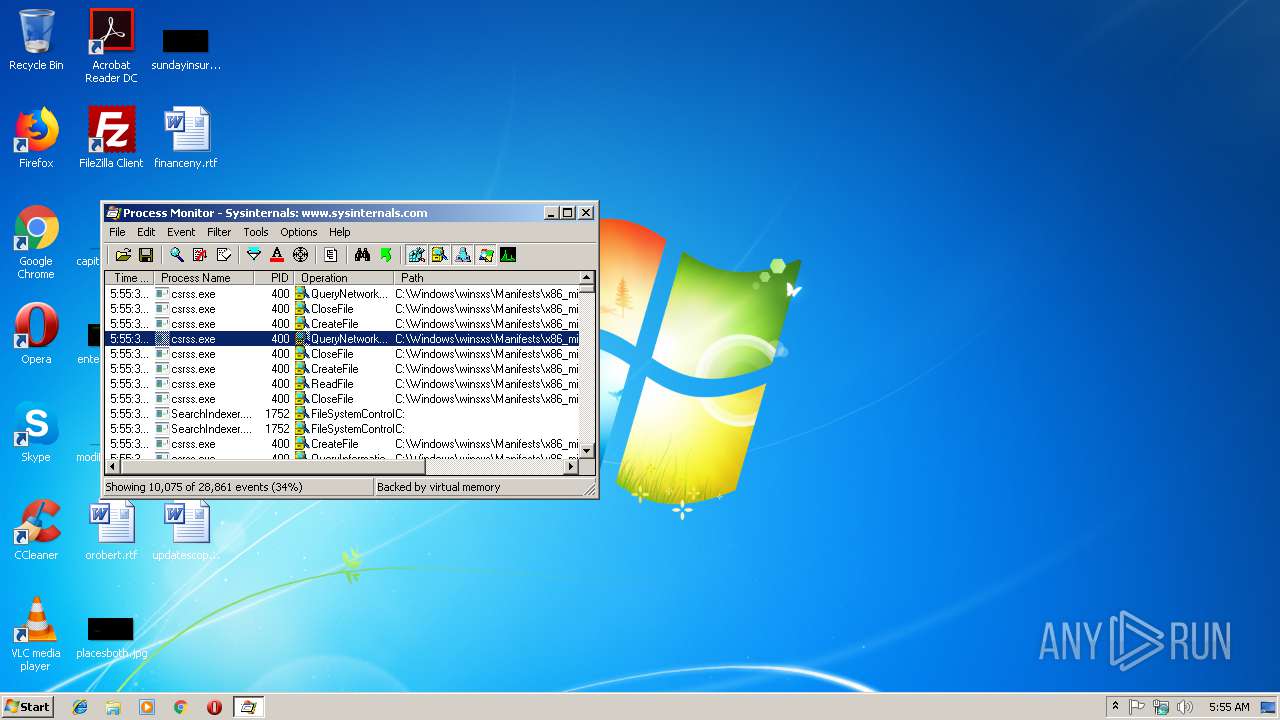
Total events
451
Read events
405
Write events
41
Delete events
5
Modification events
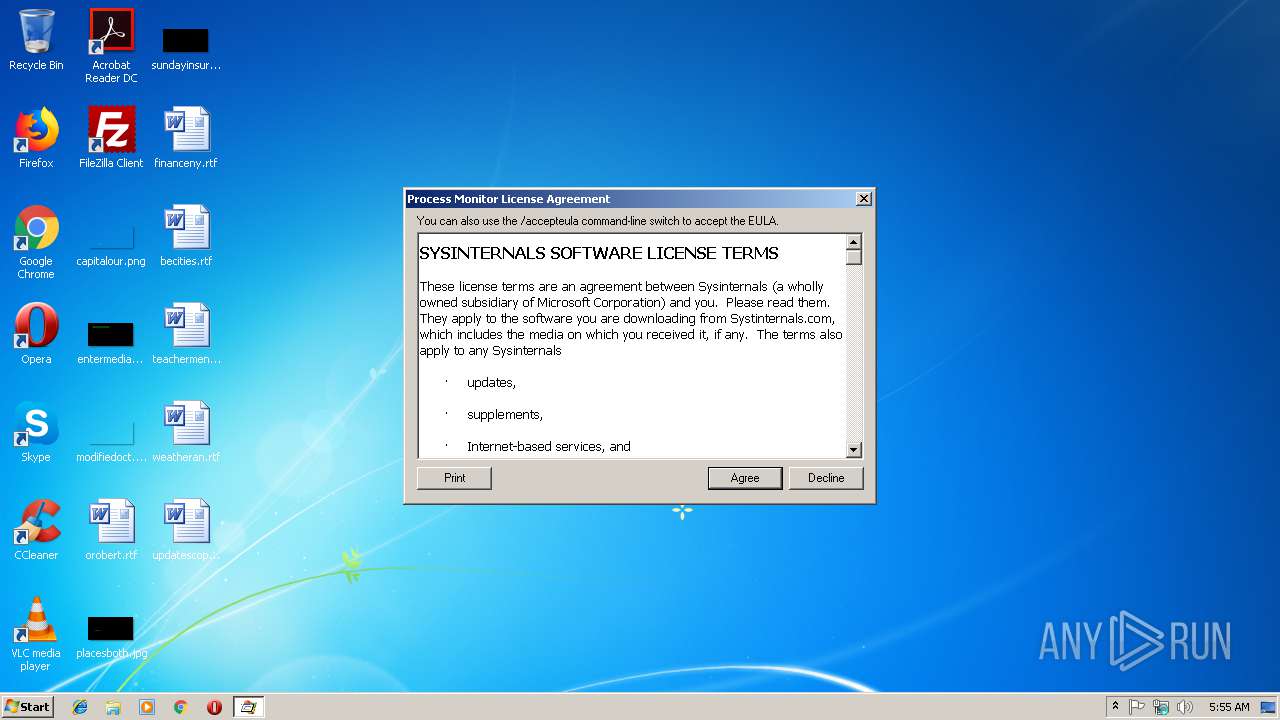
| (PID) Process: | (3112) Procmon.exe | Key: | HKEY_CURRENT_USER\Software\Sysinternals\Process Monitor |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
| (PID) Process: | (3112) Procmon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3112) Procmon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3792) Procmon.exe | Key: | HKEY_CURRENT_USER\Software\Sysinternals\Process Monitor |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
| (PID) Process: | (3792) Procmon.exe | Key: | HKEY_CLASSES_ROOT\.PML |
| Operation: | write | Name: | |
Value: ProcMon.Logfile.1 | |||
| (PID) Process: | (3792) Procmon.exe | Key: | HKEY_CLASSES_ROOT\ProcMon.Logfile.1 |
| Operation: | write | Name: | |
Value: ProcMon Log File | |||
| (PID) Process: | (3792) Procmon.exe | Key: | HKEY_CLASSES_ROOT\ProcMon.Logfile.1\shell\open\command |
| Operation: | write | Name: | |
Value: "C:\Users\admin\AppData\Local\Temp\Procmon.exe" /OpenLog "%1" | |||
| (PID) Process: | (3792) Procmon.exe | Key: | HKEY_CLASSES_ROOT\ProcMon.Logfile.1\DefaultIcon |
| Operation: | write | Name: | |
Value: "C:\Users\admin\AppData\Local\Temp\Procmon.exe",0 | |||
| (PID) Process: | (3792) Procmon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 52 | |||
| (PID) Process: | (3792) Procmon.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\PROCMON24 |
| Operation: | write | Name: | Type |
Value: 2 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3792 | Procmon.exe | C:\Windows\system32\Drivers\PROCMON24.SYS | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report