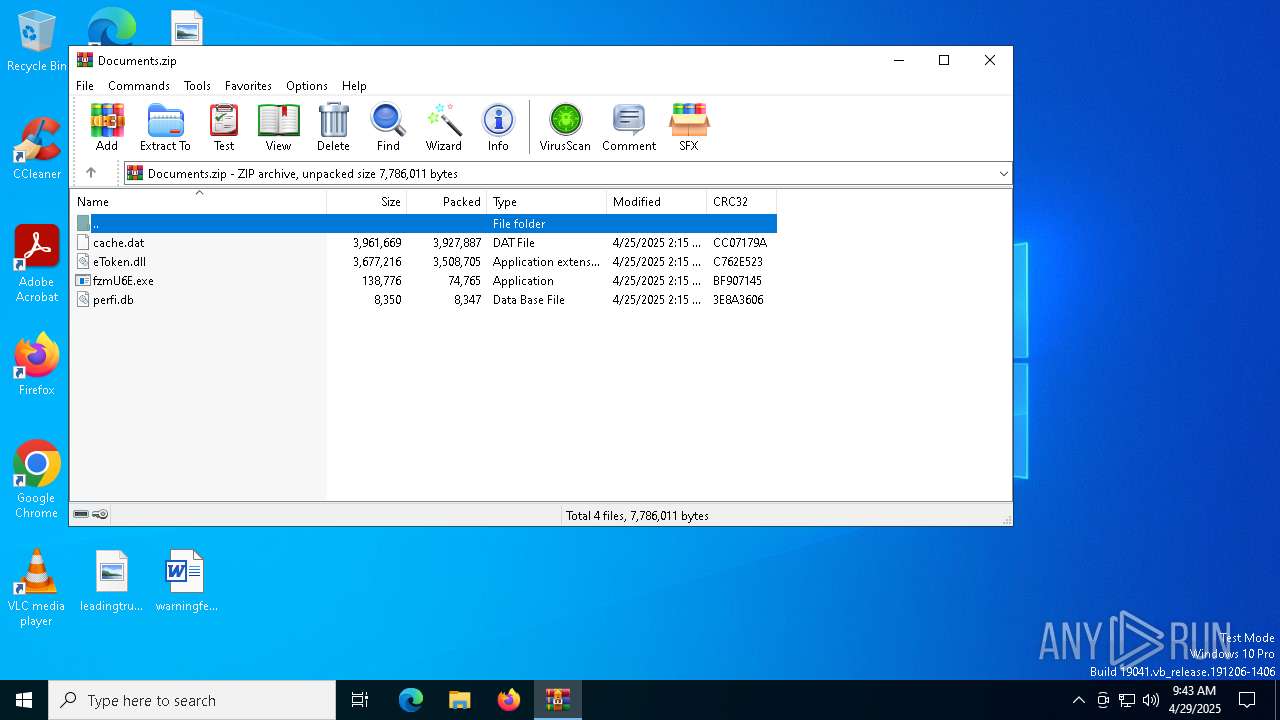
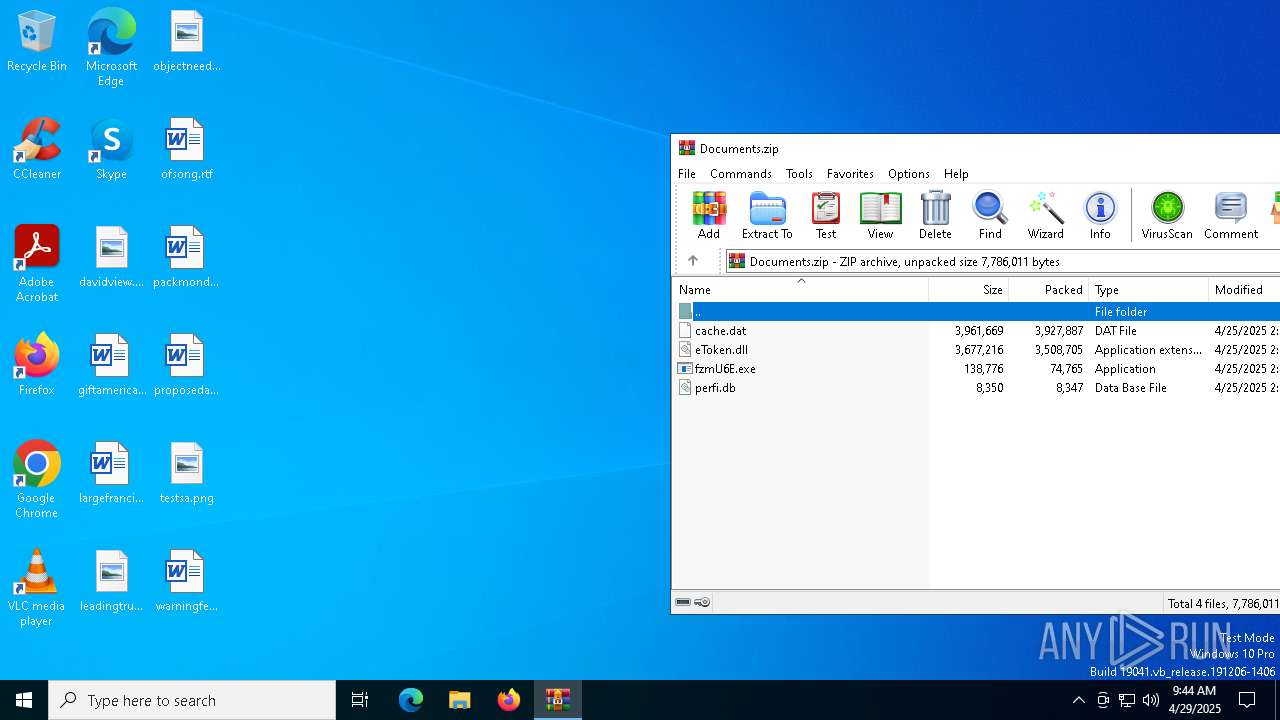
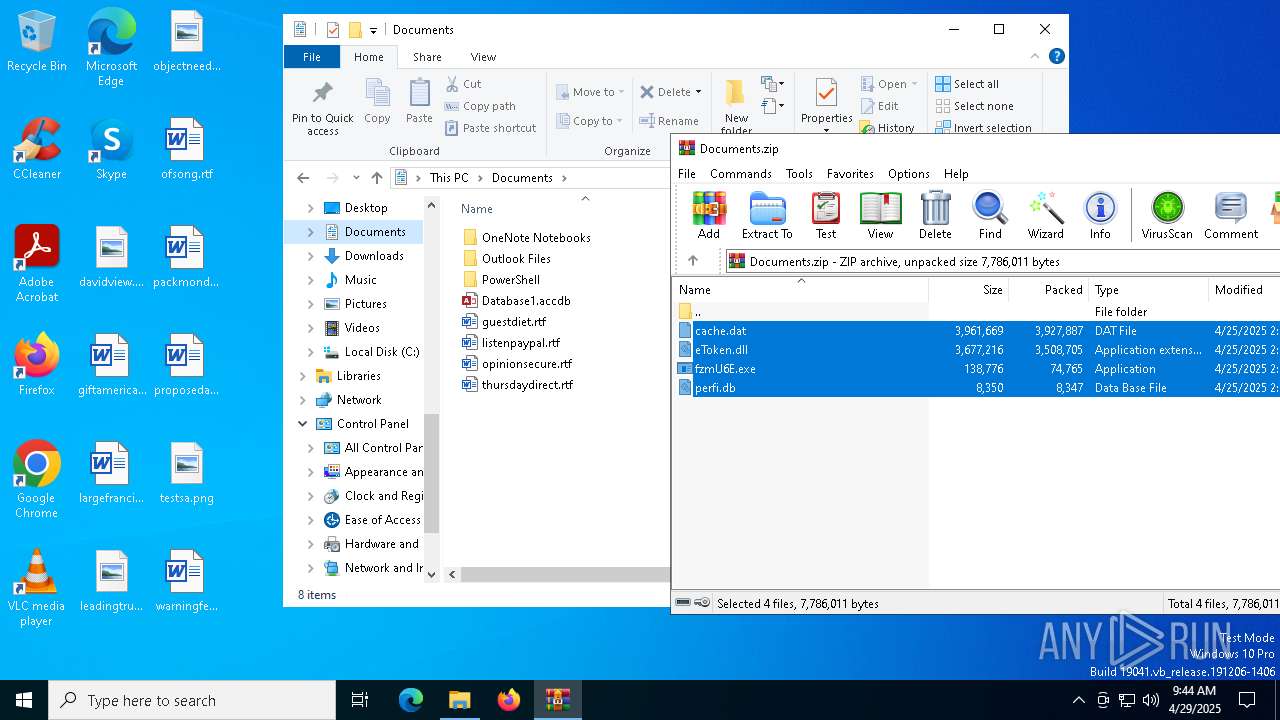
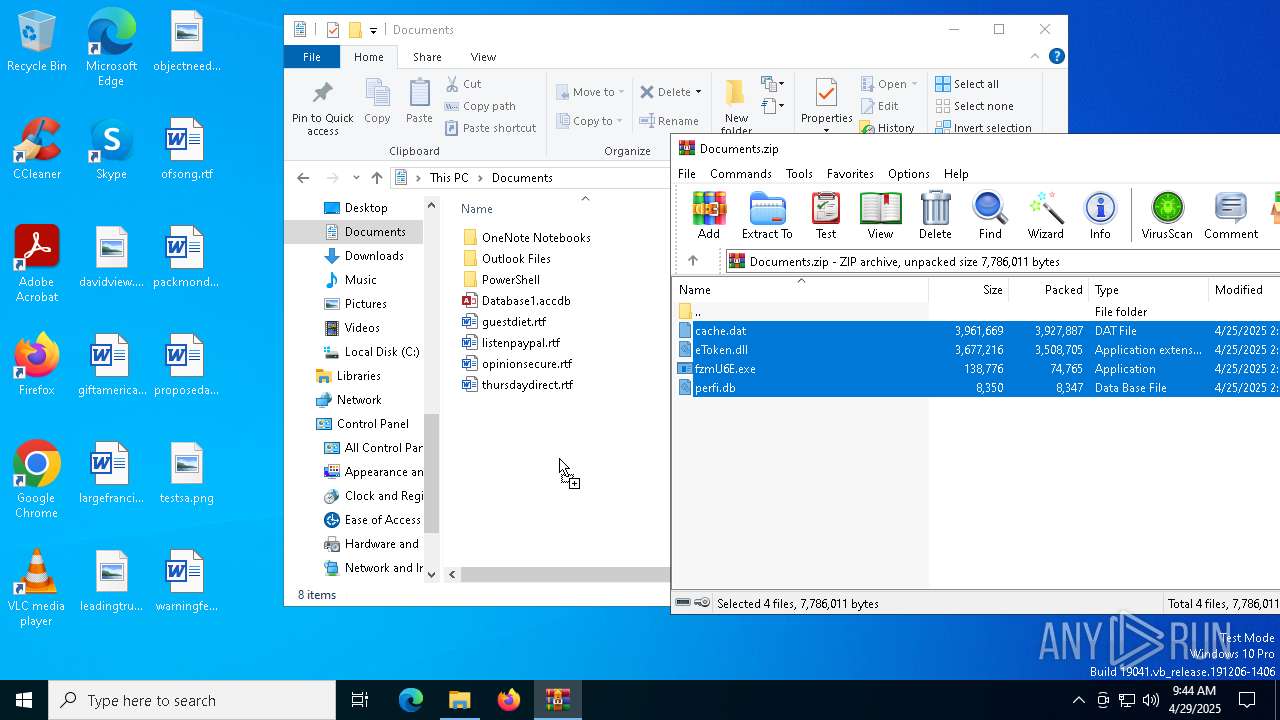
| File name: | Documents.zip |
| Full analysis: | https://app.any.run/tasks/de35dd40-3684-4654-b9bb-ed41483bf4ce |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 09:43:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 1E3B123805539AFA541E7002F491CFAB |
| SHA1: | 4022BB5A8D08C370F0C468EFFEF3DC601C11D6F1 |
| SHA256: | 4F26F3C9A6C778D582375084ABEB54CE0F4AD087880E06F926B7262CD248C170 |
| SSDEEP: | 98304:m/FSlpVg3RPzncP4Obfkc6ManA2WnCOzgx59mvqmwydEjtJPX/PdNImaRd2s3+mX:uv0+4vKQk+awKLCDH |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 5756)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 6136)
- cmd.exe (PID: 5360)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 4692)
- cmd.exe (PID: 680)
- cmd.exe (PID: 3828)
- cmd.exe (PID: 4736)
- cmd.exe (PID: 2088)
Modifies exclusions in Windows Defender
- reg.exe (PID: 904)
- reg.exe (PID: 4000)
- reg.exe (PID: 4180)
- reg.exe (PID: 2960)
- reg.exe (PID: 6752)
- reg.exe (PID: 1128)
- reg.exe (PID: 4448)
- reg.exe (PID: 6424)
- reg.exe (PID: 472)
- reg.exe (PID: 6416)
Uses NET.EXE to stop Windows Update service
- cmd.exe (PID: 4868)
- net.exe (PID: 2516)
Starts NET.EXE for service management
- cmd.exe (PID: 4868)
- net.exe (PID: 2516)
- net.exe (PID: 5968)
- net.exe (PID: 3016)
- net.exe (PID: 6424)
Changes the Windows auto-update feature
- reg.exe (PID: 5848)
Run PowerShell with an invisible window
- powershell.exe (PID: 5096)
SUSPICIOUS
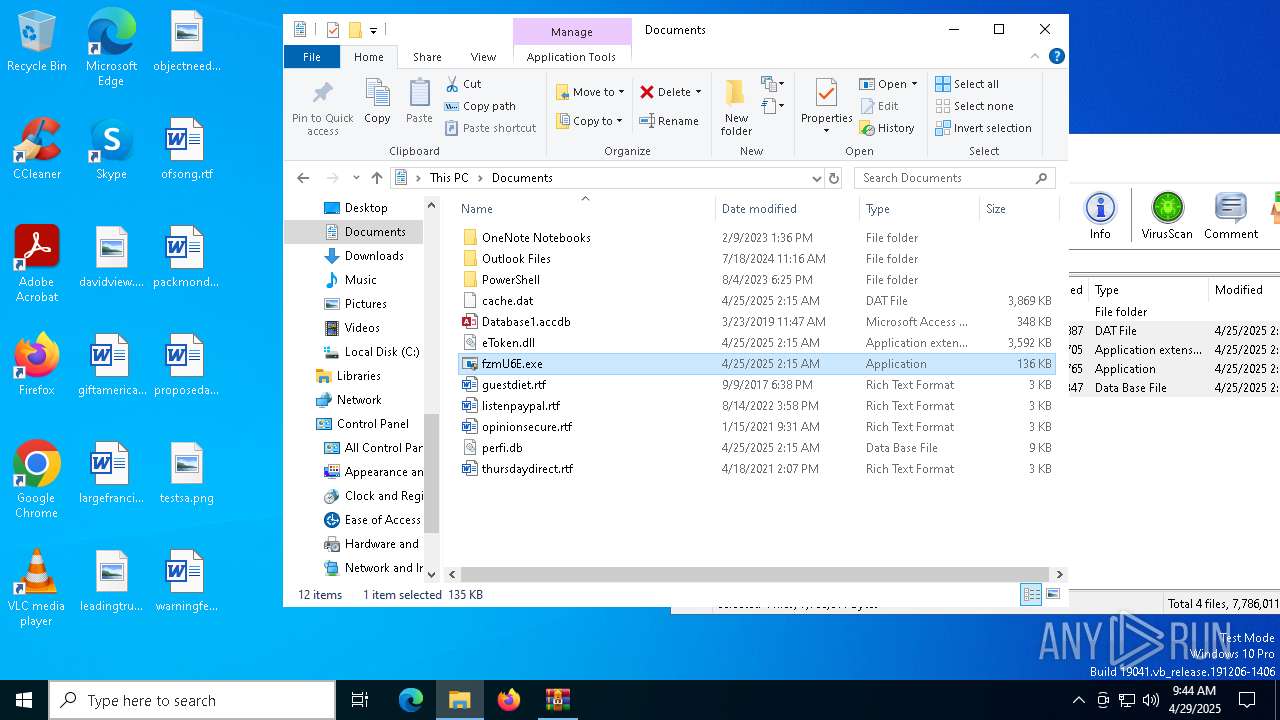
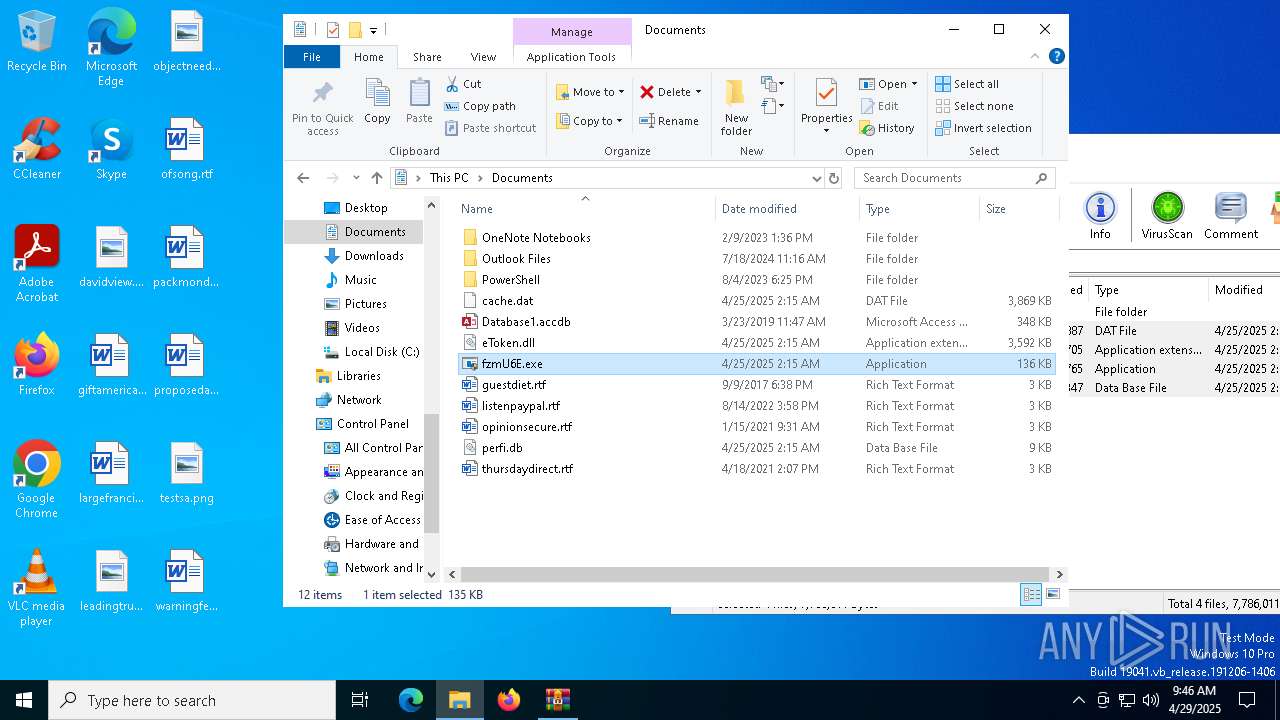
Reads the date of Windows installation
- fzmU6E.exe (PID: 6404)
Reads security settings of Internet Explorer
- fzmU6E.exe (PID: 6404)
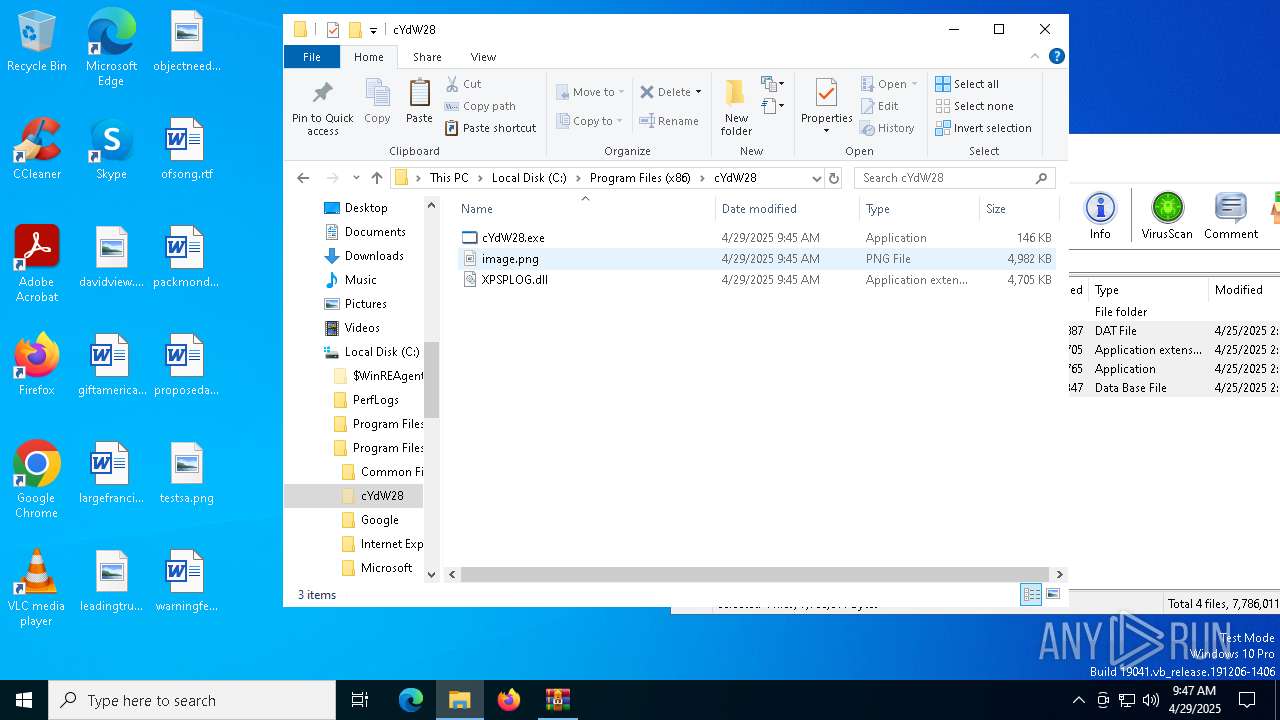
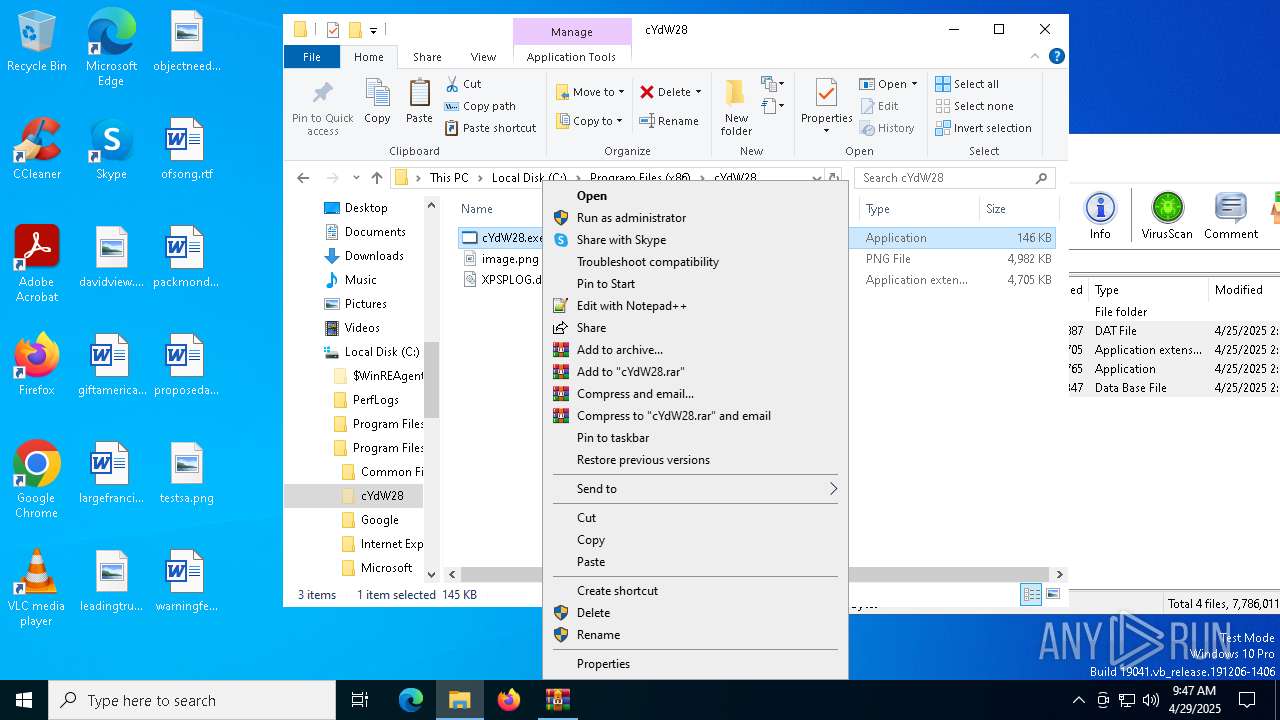
- cYdW28.exe (PID: 6576)
Starts CMD.EXE for commands execution
- fzmU6E.exe (PID: 6404)
- cYdW28.exe (PID: 6576)
Found strings related to reading or modifying Windows Defender settings
- fzmU6E.exe (PID: 6404)
- cYdW28.exe (PID: 6576)
The process executes via Task Scheduler
- cmd.exe (PID: 664)
- cmd.exe (PID: 6964)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 1812)
- cYdW28.exe (PID: 4164)
- QGE2fUX.exe (PID: 872)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 6240)
- cmd.exe (PID: 5172)
- cmd.exe (PID: 4408)
- QGE2fUX.exe (PID: 4308)
- cYdW28.exe (PID: 3032)
- cmd.exe (PID: 3956)
- QGE2fUX.exe (PID: 3020)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 664)
- cmd.exe (PID: 6964)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 1812)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 5172)
- cmd.exe (PID: 6240)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 4408)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 4868)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 2908)
- schtasks.exe (PID: 6640)
- schtasks.exe (PID: 5428)
- schtasks.exe (PID: 5384)
- schtasks.exe (PID: 6584)
- schtasks.exe (PID: 7012)
- schtasks.exe (PID: 6032)
- schtasks.exe (PID: 3304)
- schtasks.exe (PID: 3272)
- schtasks.exe (PID: 2320)
Executable content was dropped or overwritten
- fzmU6E.exe (PID: 6404)
- cYdW28.exe (PID: 6576)
Hides command output
- cmd.exe (PID: 4868)
The process deletes folder without confirmation
- cYdW28.exe (PID: 6576)
Windows service management via SC.EXE
- sc.exe (PID: 2152)
- sc.exe (PID: 2552)
- sc.exe (PID: 2616)
- sc.exe (PID: 6244)
- sc.exe (PID: 4692)
- sc.exe (PID: 3804)
- sc.exe (PID: 6980)
- sc.exe (PID: 4648)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 4868)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 4868)
Creates or modifies Windows services
- reg.exe (PID: 5540)
- reg.exe (PID: 4968)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 5096)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4868)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 4868)
INFO
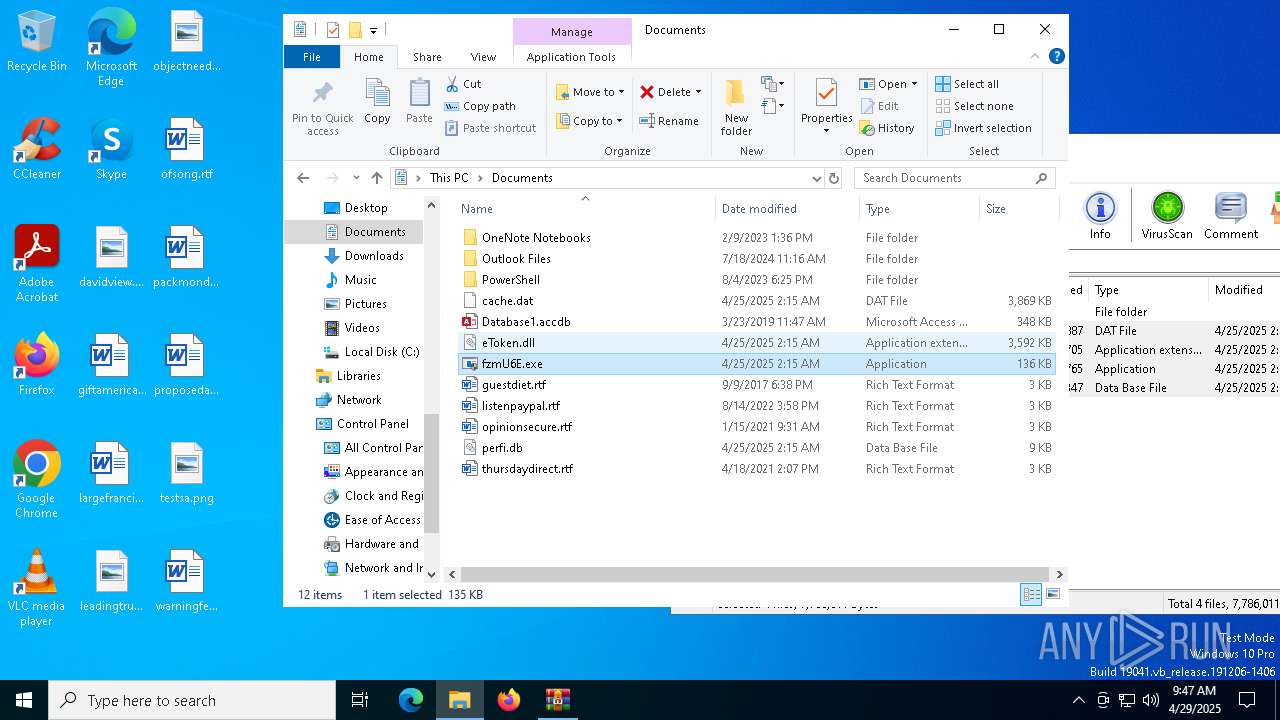
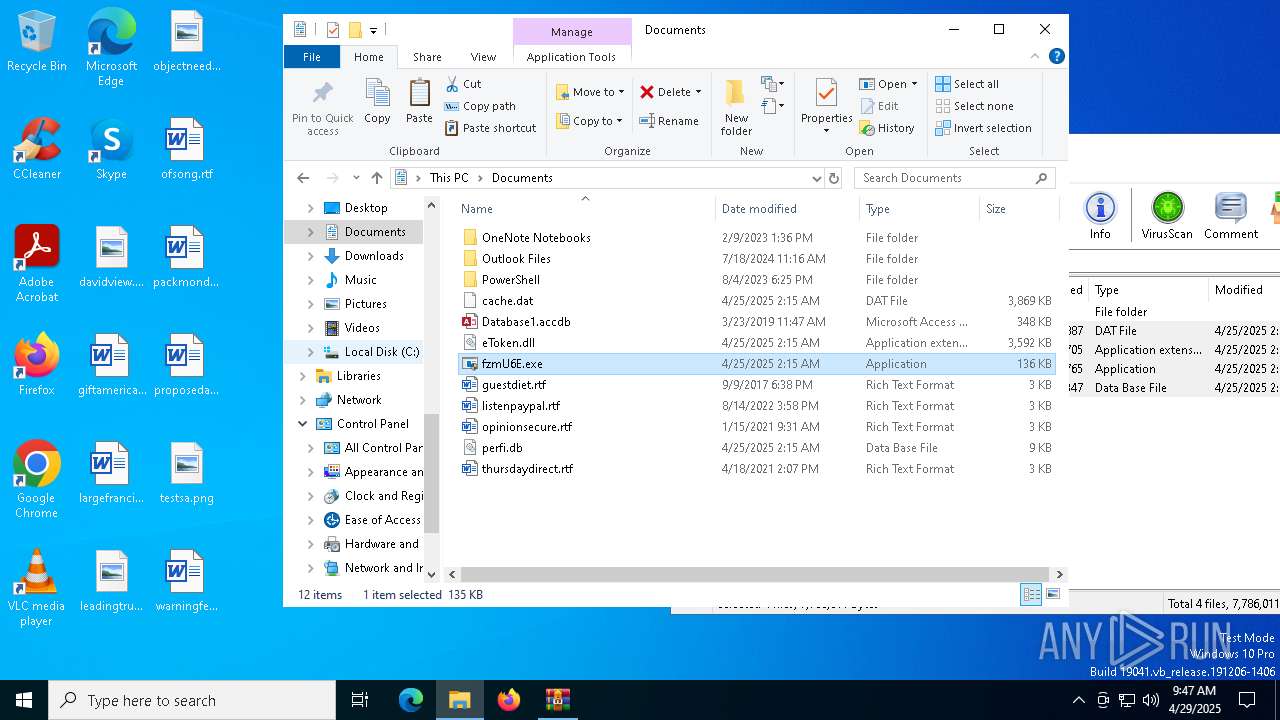
Manual execution by a user
- fzmU6E.exe (PID: 6404)
- fzmU6E.exe (PID: 1272)
- cYdW28.exe (PID: 6576)
The sample compiled with english language support
- WinRAR.exe (PID: 2384)
- cYdW28.exe (PID: 6576)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2384)
Checks supported languages
- fzmU6E.exe (PID: 6404)
- cYdW28.exe (PID: 6576)
- QGE2fUX.exe (PID: 872)
- cYdW28.exe (PID: 4164)
- QGE2fUX.exe (PID: 4308)
- cYdW28.exe (PID: 3032)
Reads the computer name
- fzmU6E.exe (PID: 6404)
- cYdW28.exe (PID: 6576)
- cYdW28.exe (PID: 4164)
- QGE2fUX.exe (PID: 872)
- QGE2fUX.exe (PID: 4308)
- cYdW28.exe (PID: 3032)
Process checks computer location settings
- fzmU6E.exe (PID: 6404)
- cYdW28.exe (PID: 6576)
Creates files or folders in the user directory
- fzmU6E.exe (PID: 6404)
Checks proxy server information
- fzmU6E.exe (PID: 6404)
- slui.exe (PID: 6136)
Reads the machine GUID from the registry
- fzmU6E.exe (PID: 6404)
Reads the software policy settings
- fzmU6E.exe (PID: 6404)
- slui.exe (PID: 6728)
- slui.exe (PID: 6136)
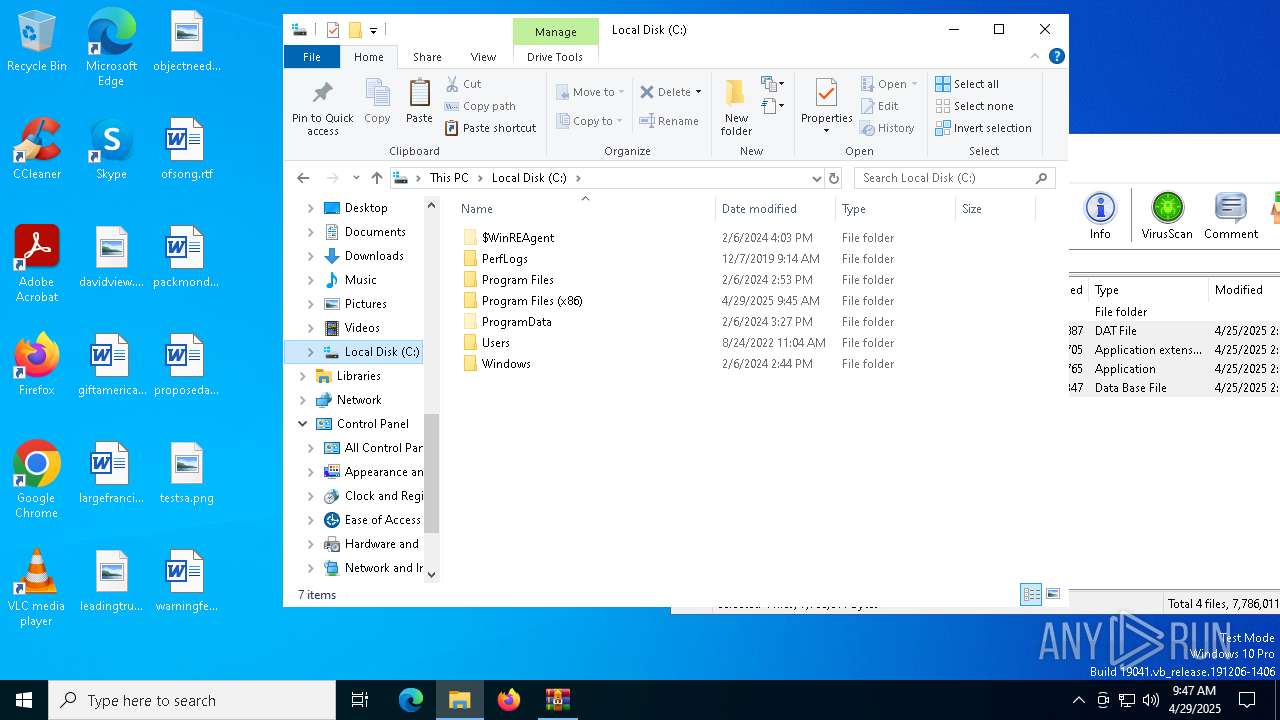
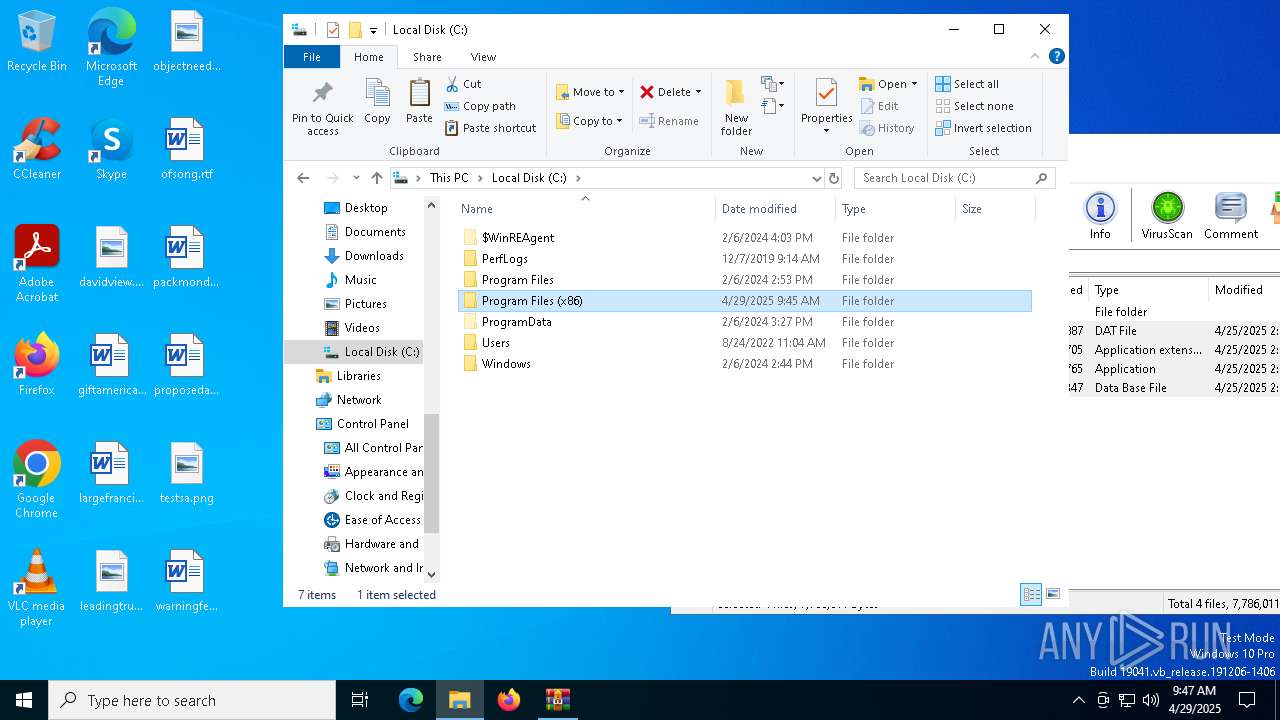
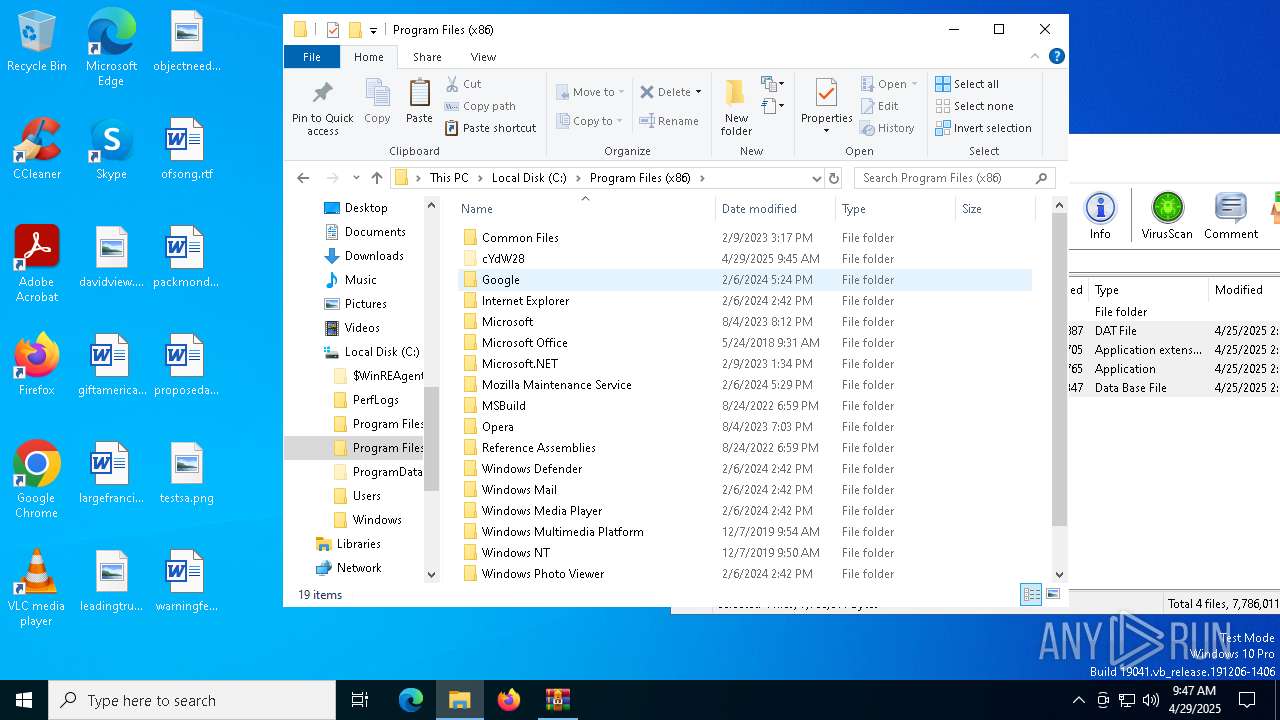
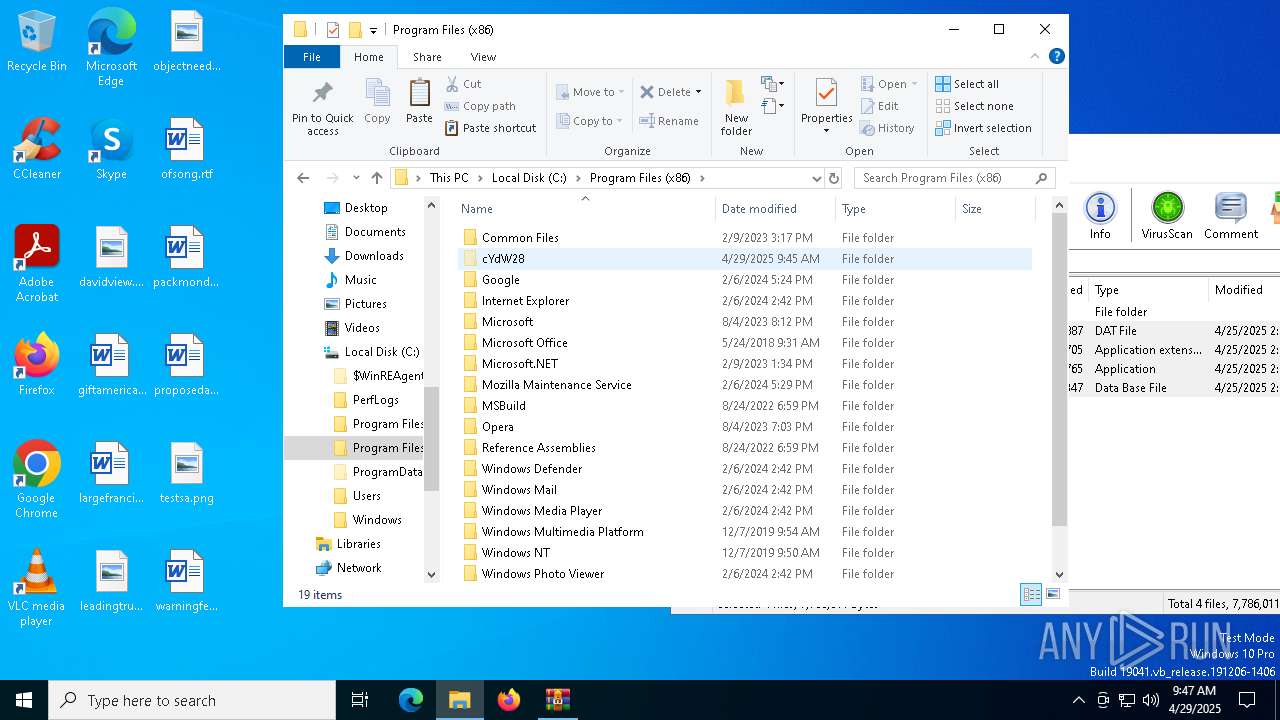
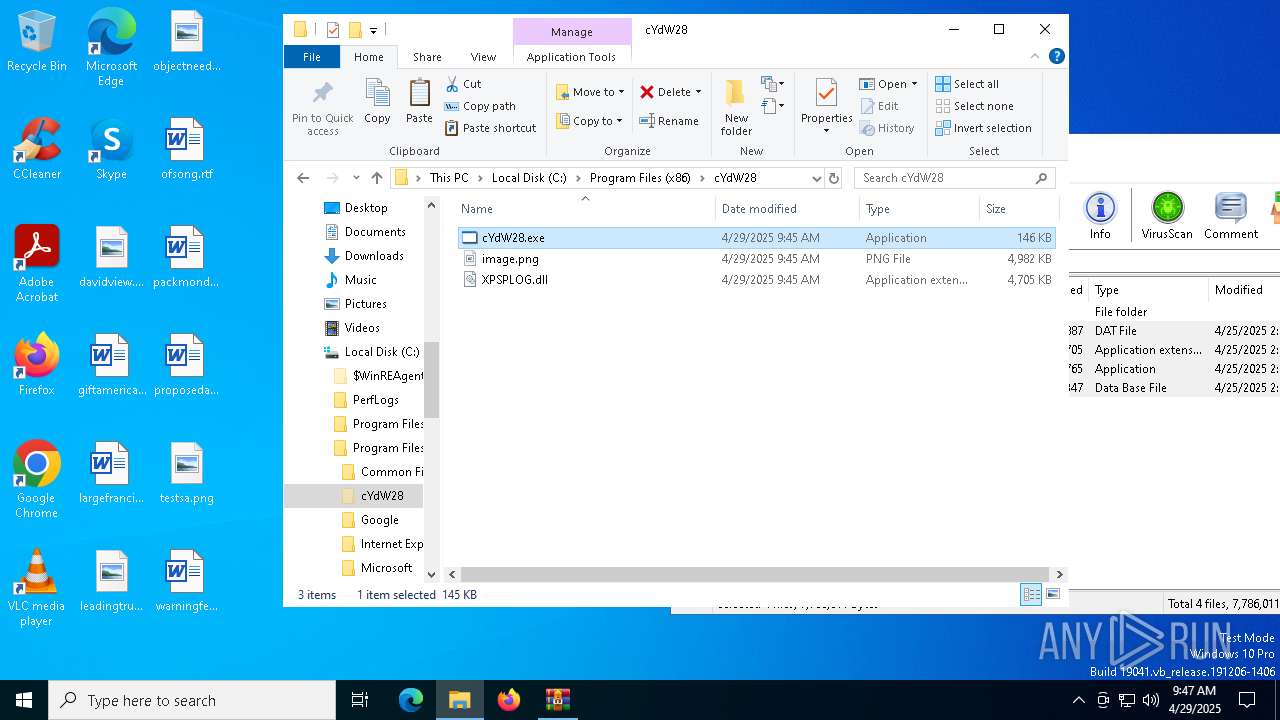
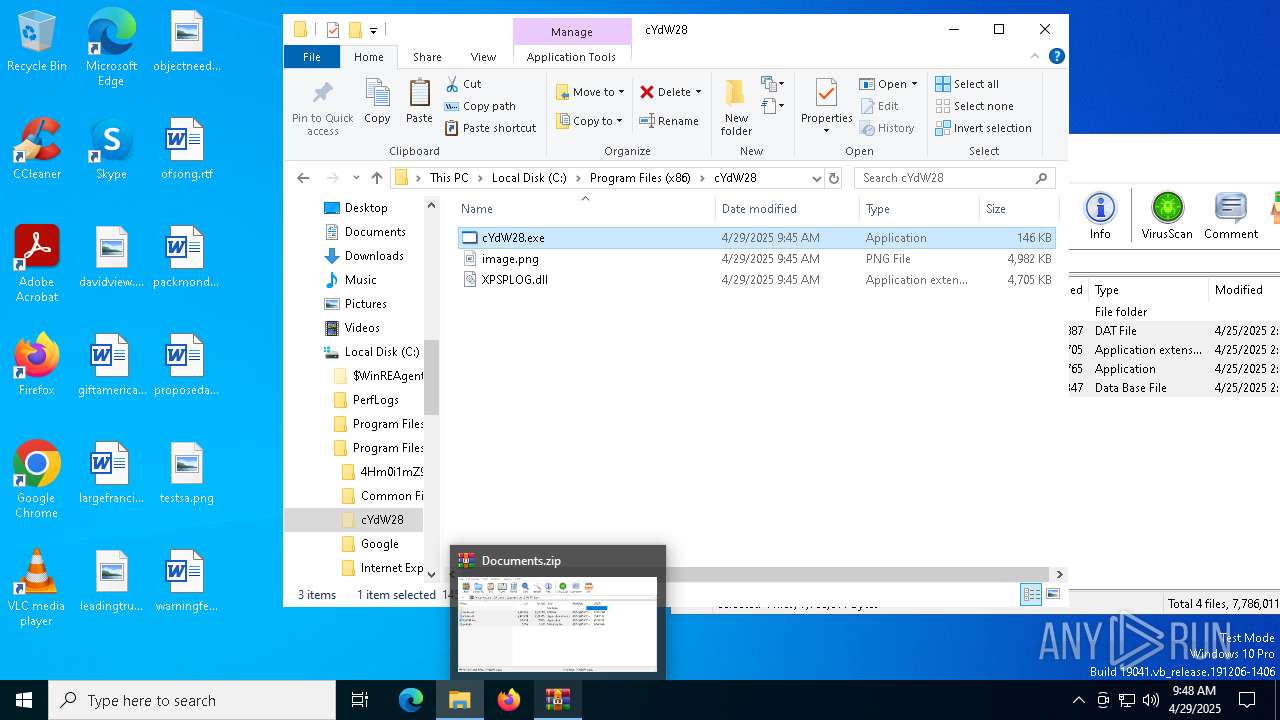
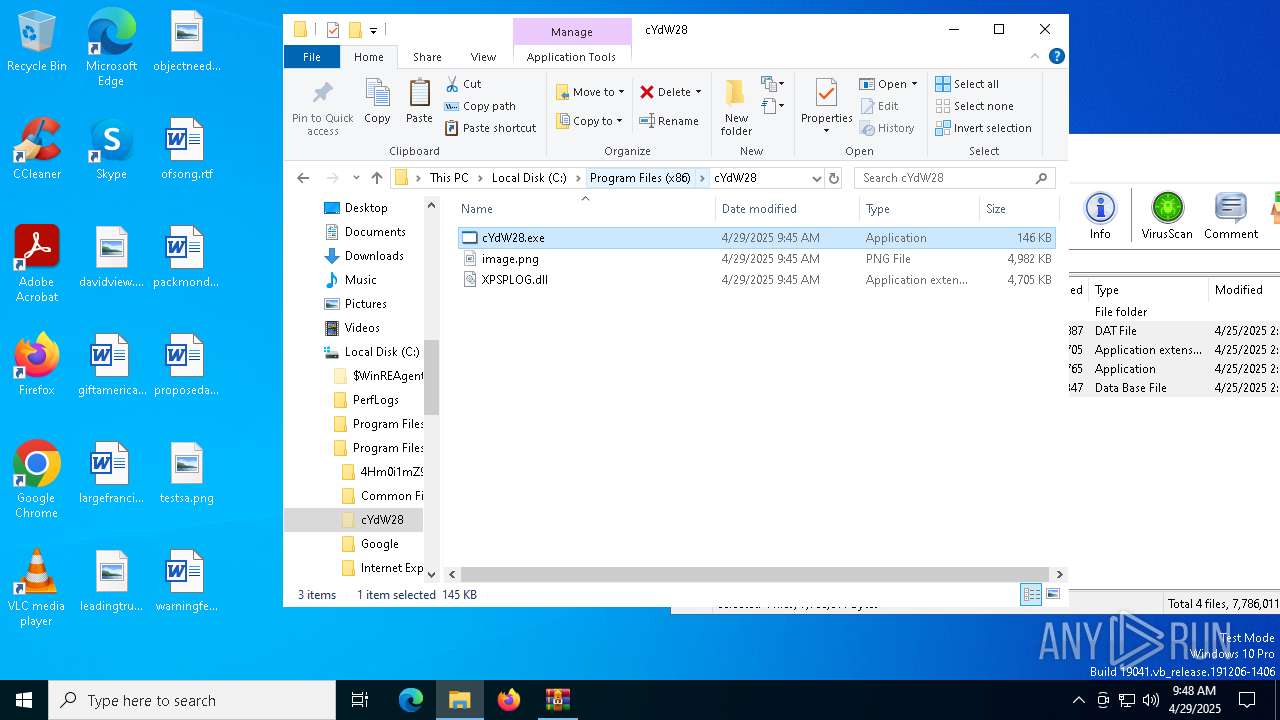
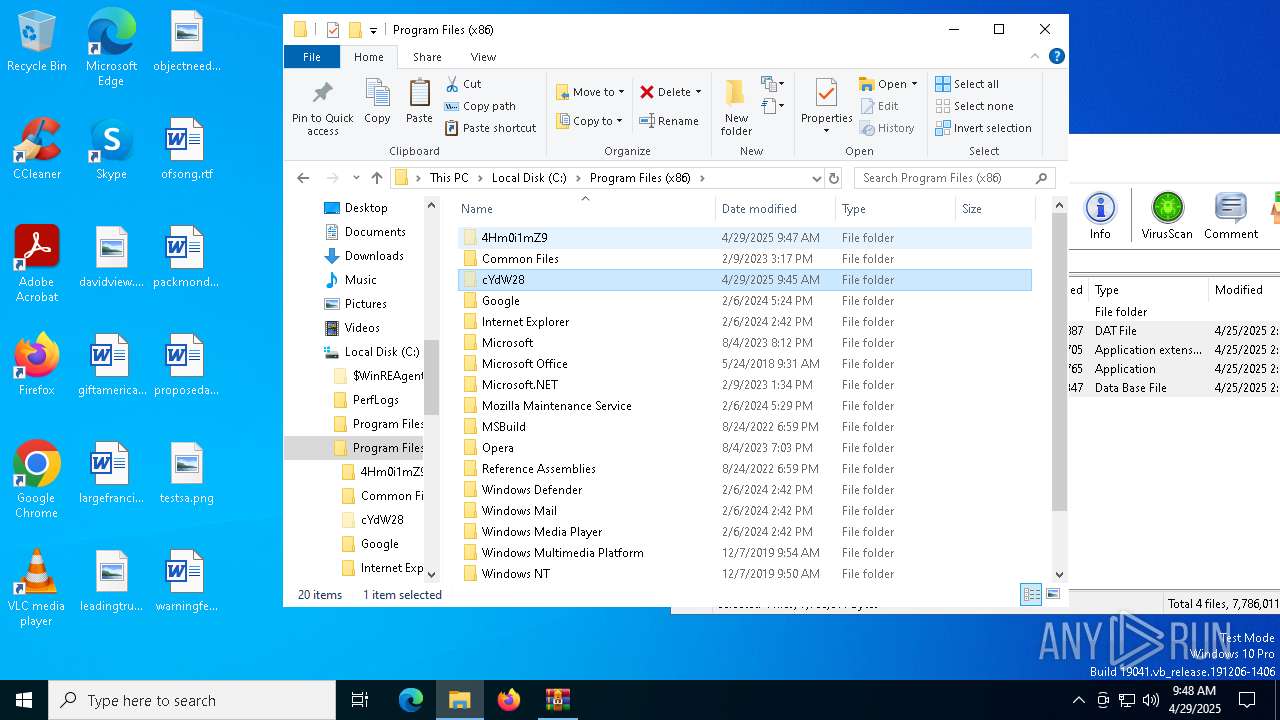
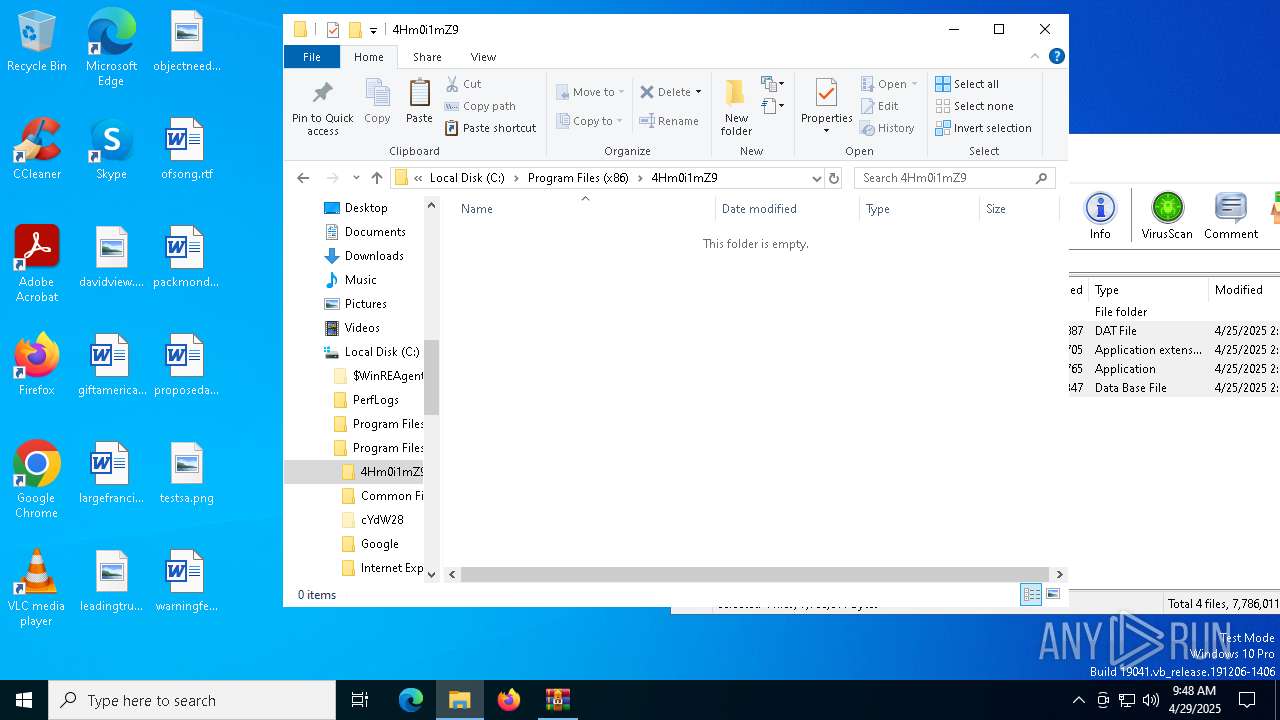
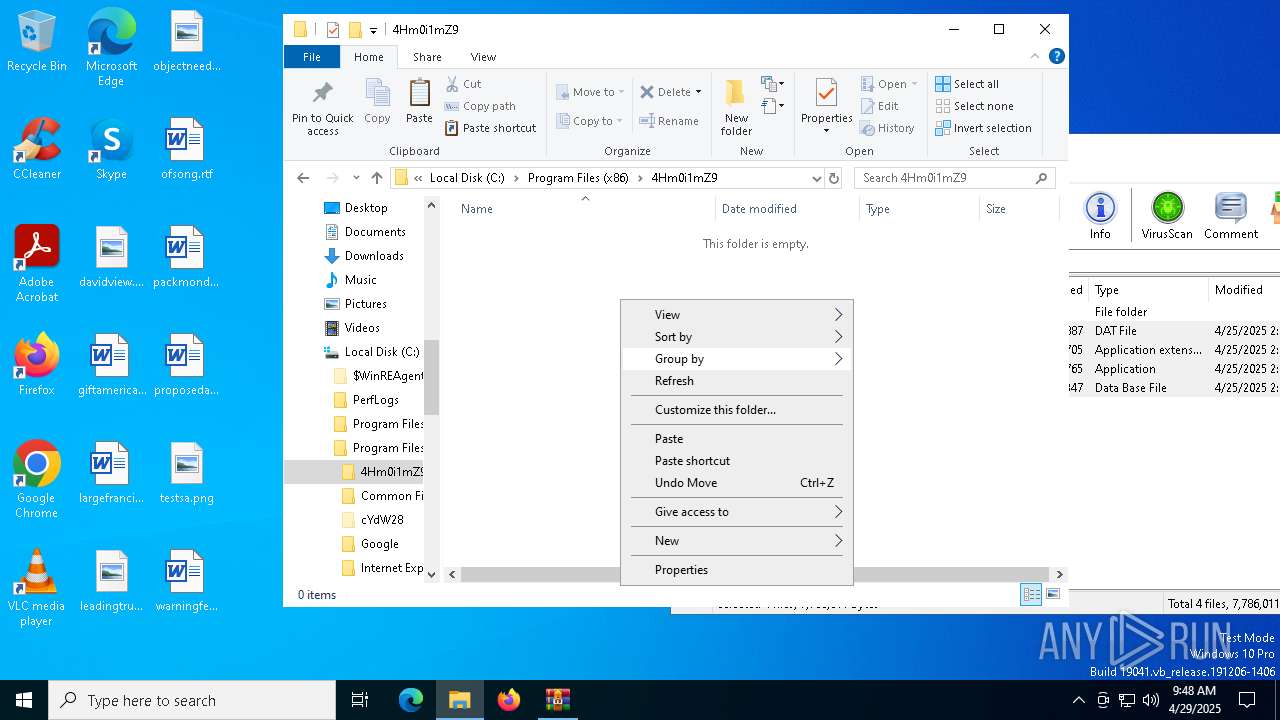
Creates files in the program directory
- cYdW28.exe (PID: 6576)
- fzmU6E.exe (PID: 6404)
Changes file name
- cmd.exe (PID: 4868)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:25 10:15:22 |
| ZipCRC: | 0xcc07179a |
| ZipCompressedSize: | 3927887 |
| ZipUncompressedSize: | 3961669 |
| ZipFileName: | cache.dat |
Total processes
257
Monitored processes
123
Malicious processes
3
Suspicious processes
22
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | reg add "HKLM\SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths" /v "C:\Program Files (x86)" /t REG_DWORD /d 0 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | takeown /f C:\Windows\System32\WaaSMedicSvc.dll | C:\Windows\SysWOW64\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | "cmd.exe" /c reg add "HKLM\SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths" /v "C:\Users\admin\Documents" /t REG_DWORD /d 0 /f | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | SCHTASKS /Run /TN "Task1" | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | SCHTASKS /Create /F /TN "Task1" /SC ONCE /ST 00:00 /RL HIGHEST /RU "SYSTEM" /TR "cmd.exe /c reg add \"HKLM\SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths\" /v \"C:\Program Files (x86)\" /t REG_DWORD /d 0 /f" | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Windows\System32\cmd.exe" cmd.exe /c SCHTASKS /Create /F /TN "Task1" /SC ONCE /ST 00:00 /RL HIGHEST /RU "SYSTEM" /TR "cmd.exe /c reg add \"HKLM\SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths\" /v \"C:\Users\" /t REG_DWORD /d 0 /f" & SCHTASKS /Run /TN "Task1" & SCHTASKS /Delete /TN "Task1" /F | C:\Windows\SysWOW64\cmd.exe | — | cYdW28.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | SCHTASKS /Run /TN "Task1" | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | SCHTASKS /Run /TN "Task1" | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | C:\WINDOWS\system32\net1 stop uhssvc | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 255
Read events
14 230
Write events
25
Delete events
0
Modification events
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Documents.zip | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (904) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths |
| Operation: | write | Name: | C:\Users\admin\Documents |
Value: 0 | |||
| (PID) Process: | (6404) fzmU6E.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
6
Suspicious files
11
Text files
7
Unknown types
1
Dropped files
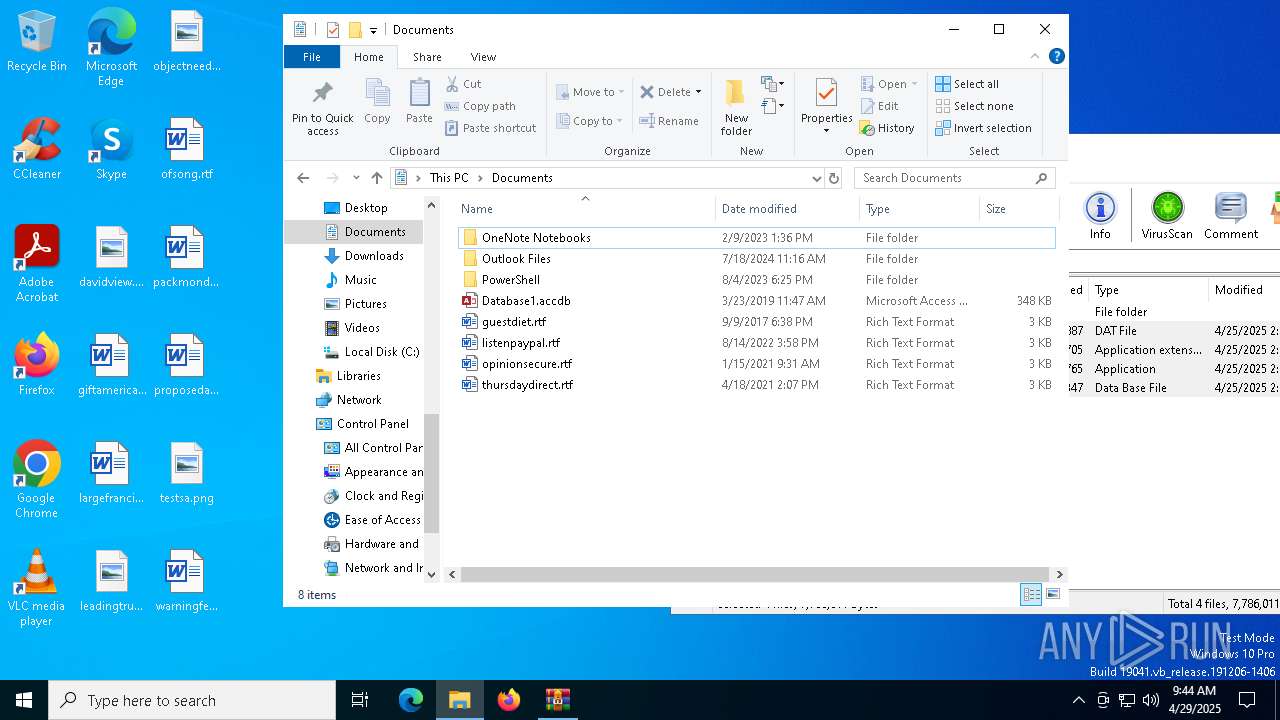
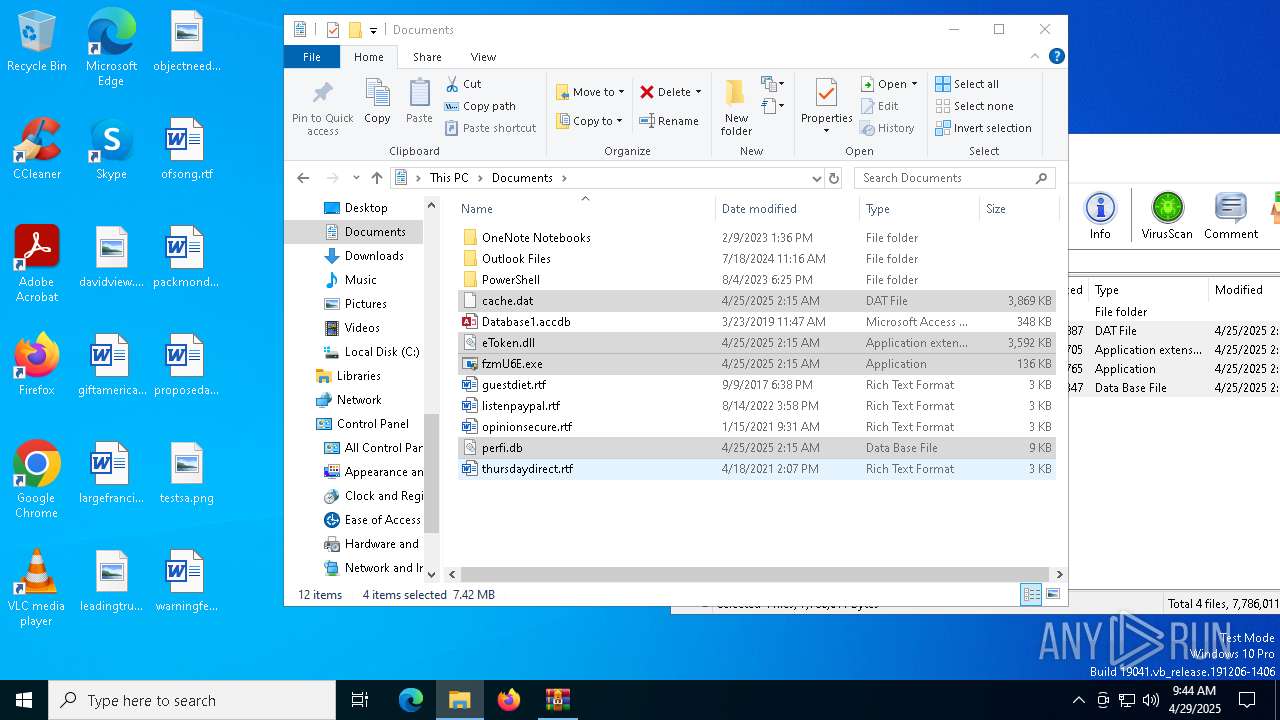
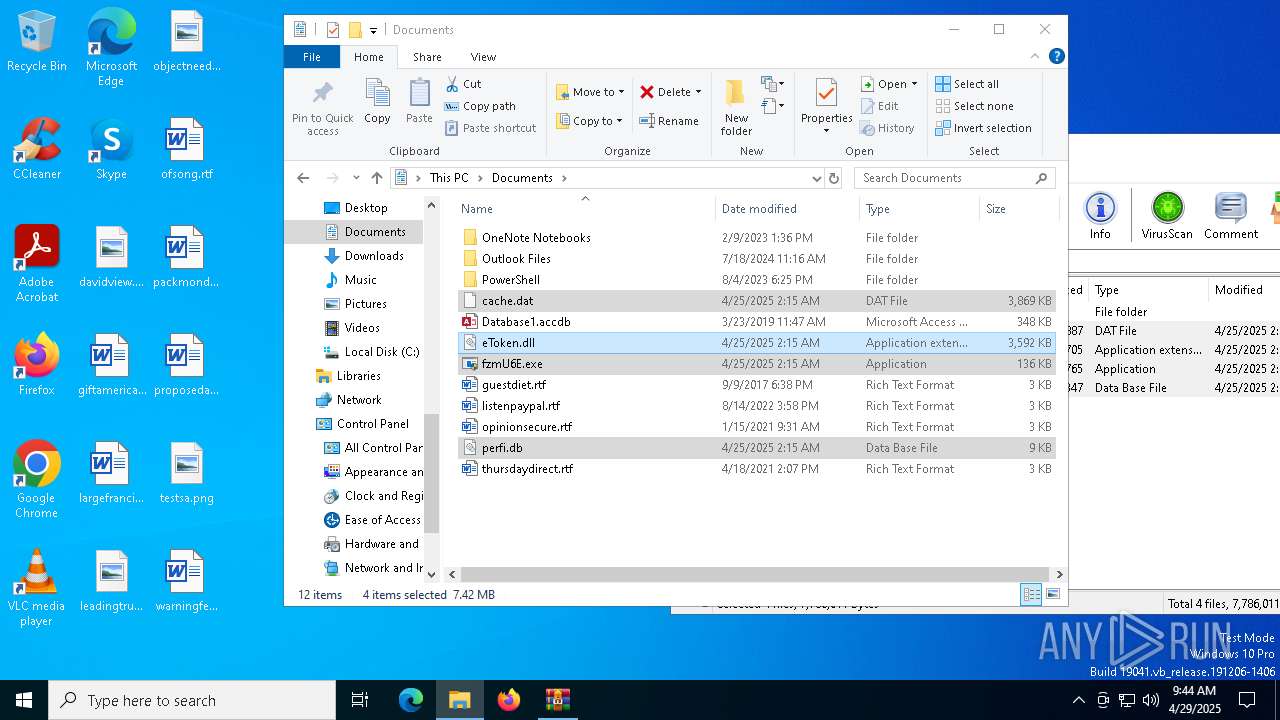
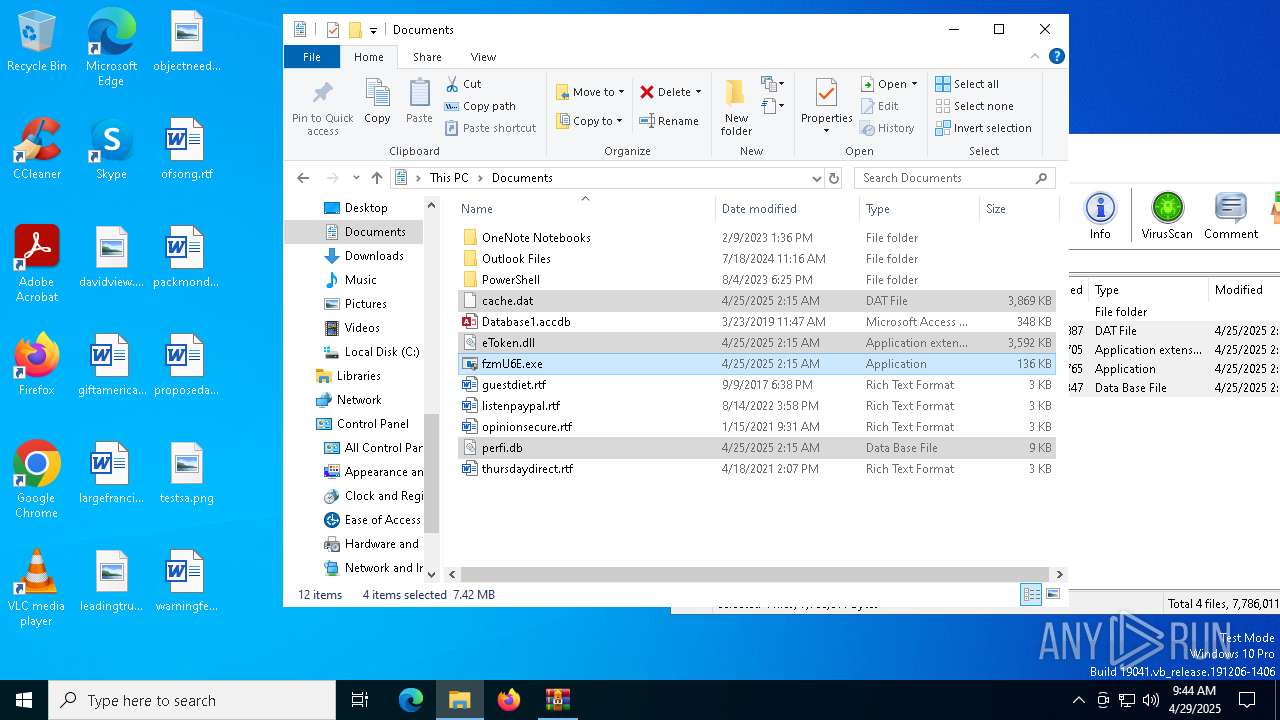
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6404 | fzmU6E.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\FOM-51[1].jpg | — | |
MD5:— | SHA256:— | |||
| 6404 | fzmU6E.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\FOM-52[1].jpg | — | |
MD5:— | SHA256:— | |||
| 6404 | fzmU6E.exe | C:\Program Files (x86)\cYdW28\image.png | — | |
MD5:— | SHA256:— | |||
| 6576 | cYdW28.exe | C:\Program Files (x86)\4Hm0i1mZ9\image.png | — | |
MD5:— | SHA256:— | |||
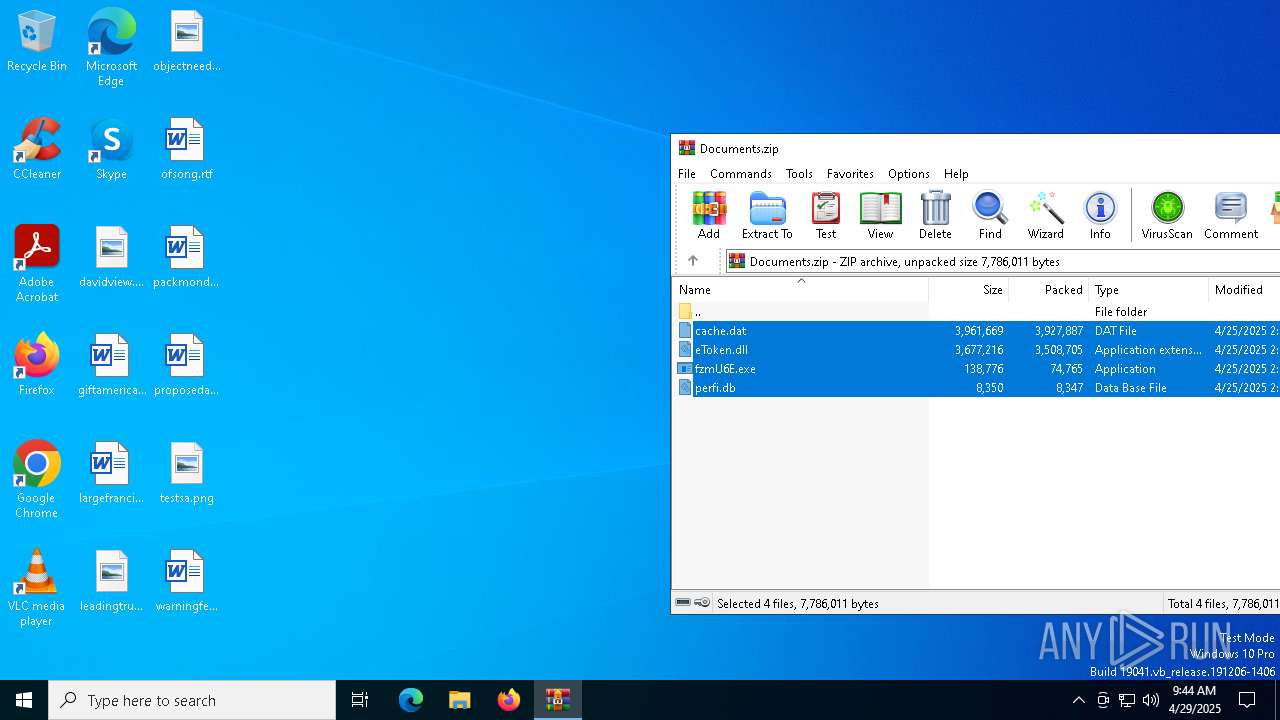
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2384.17270\eToken.dll | executable | |
MD5:017B78A8D034F17FD265B321BC7A2CFC | SHA256:773F1E61850A7E5BB8315DD5643E19E239BCDD0D539901C1B5DA31E20052F866 | |||
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2384.17270\cache.dat | image | |
MD5:599FA79EA859421BCED546351C426885 | SHA256:802AD8A2D573CE7B8CE6B901B7C7B6B516FD54E9C2B3D819F30967BC1D03A8FA | |||
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2384.17270\perfi.db | binary | |
MD5:D7B985D13484016E8540280DE8662054 | SHA256:B84C2D03219681A9AAC19915D1D63616C1D59BAD246A2D658223F0E99C345E7E | |||
| 6404 | fzmU6E.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\0DA515F703BB9B49479E8697ADB0B955_4136D3715888E22D65EBE484B233D81B | der | |
MD5:5AADB02743E59A6B2BCC37D2D9303A40 | SHA256:BFBA568B450B17D431D4FFBB1E877BA9CFFCD7F8D45CEE0DA5E939FE2F54BDC4 | |||
| 6404 | fzmU6E.exe | C:\Users\Public\Music\destopbak.ini | binary | |
MD5:55A54008AD1BA589AA210D2629C1DF41 | SHA256:4BF5122F344554C53BDE2EBB8CD2B7E3D1600AD631C385A5D7CCE23C7785459A | |||
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2384.17270\fzmU6E.exe | executable | |
MD5:DF76205EAF175184567FC44A83019B20 | SHA256:A6123E13E12A1A1D4C4A4EB034769BFE8E229C3A9877E0DD173B422E700A26AC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
27
DNS requests
20
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5408 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5408 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6404 | fzmU6E.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEQCB5auY5G81uRwv%2BheHGMha | unknown | — | — | whitelisted |
6404 | fzmU6E.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDQHuXxad%2F5c1K2Rl1mo%3D | unknown | — | — | whitelisted |
6404 | fzmU6E.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr3ovtlsca2024/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBT%2BeHEVW1om2JjNh%2BetTEbfp%2BiVWQQU2tOoCEgMNDdY7uWndS5Z%2FNbcPDgCDAu5CNI2gOuRwtqS8g%3D%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.30:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5408 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nm25.oss-cn-hangzhou.aliyuncs.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6404 | fzmU6E.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
6404 | fzmU6E.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |