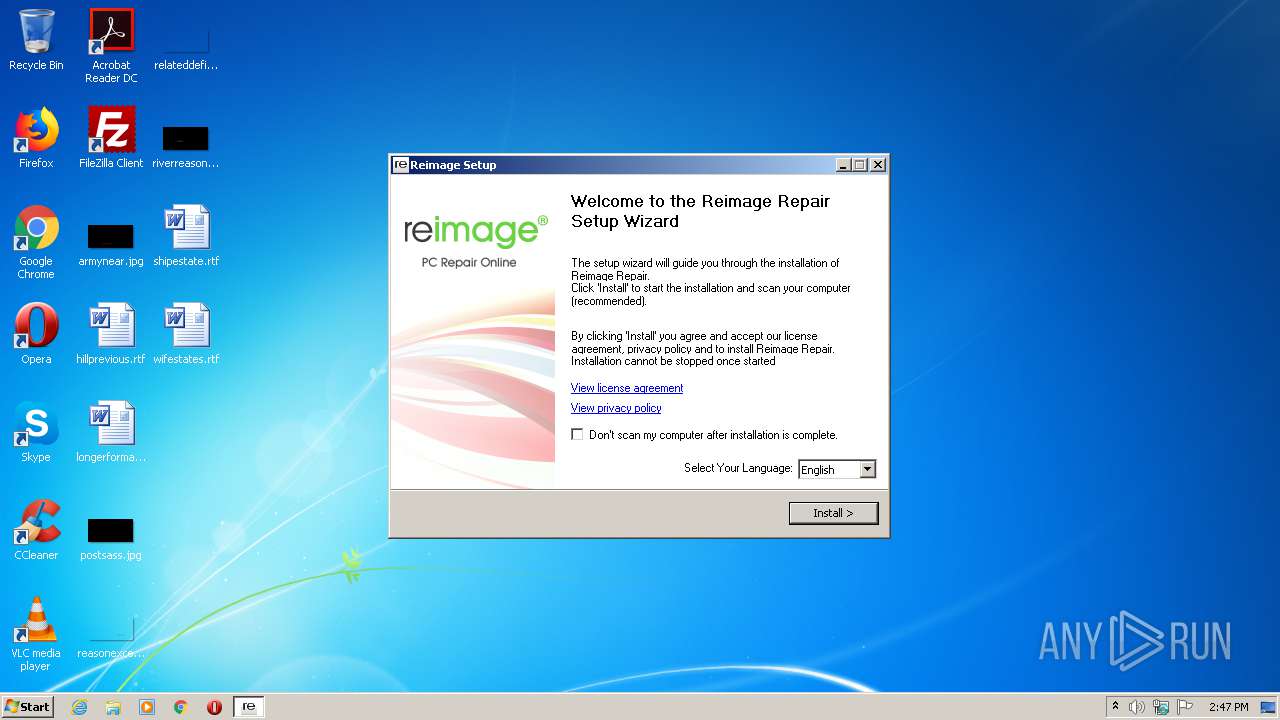
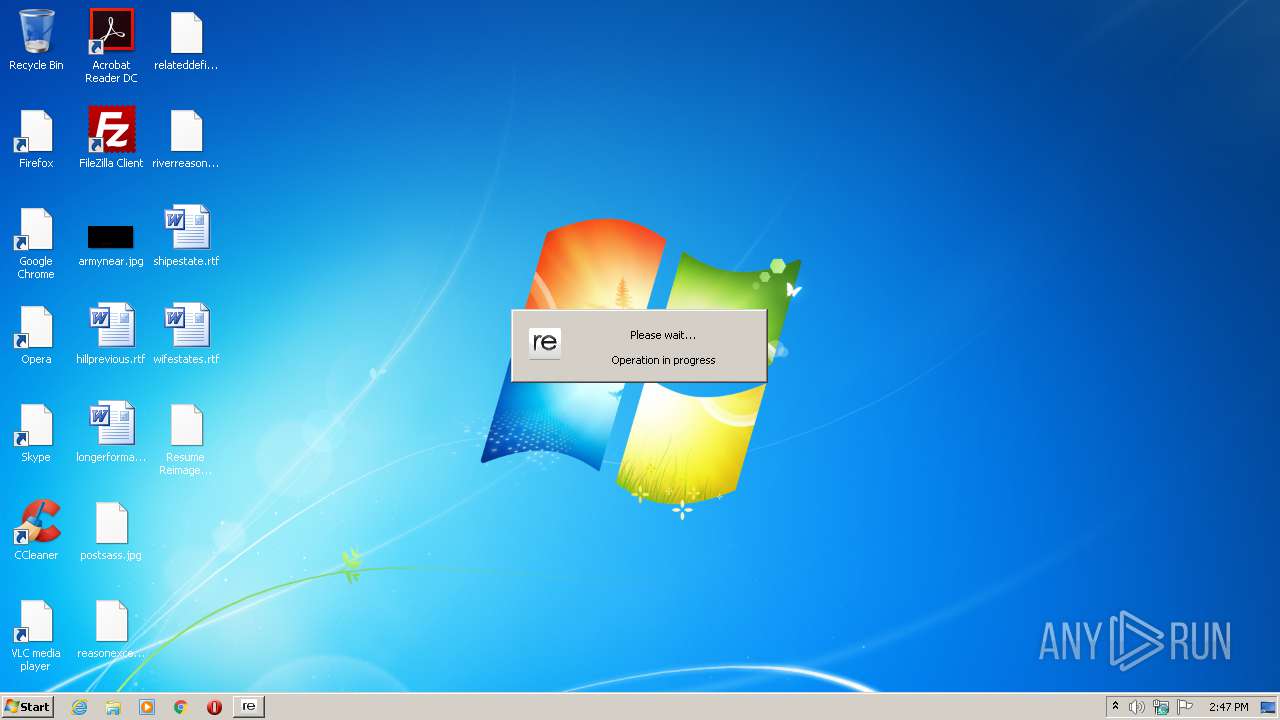
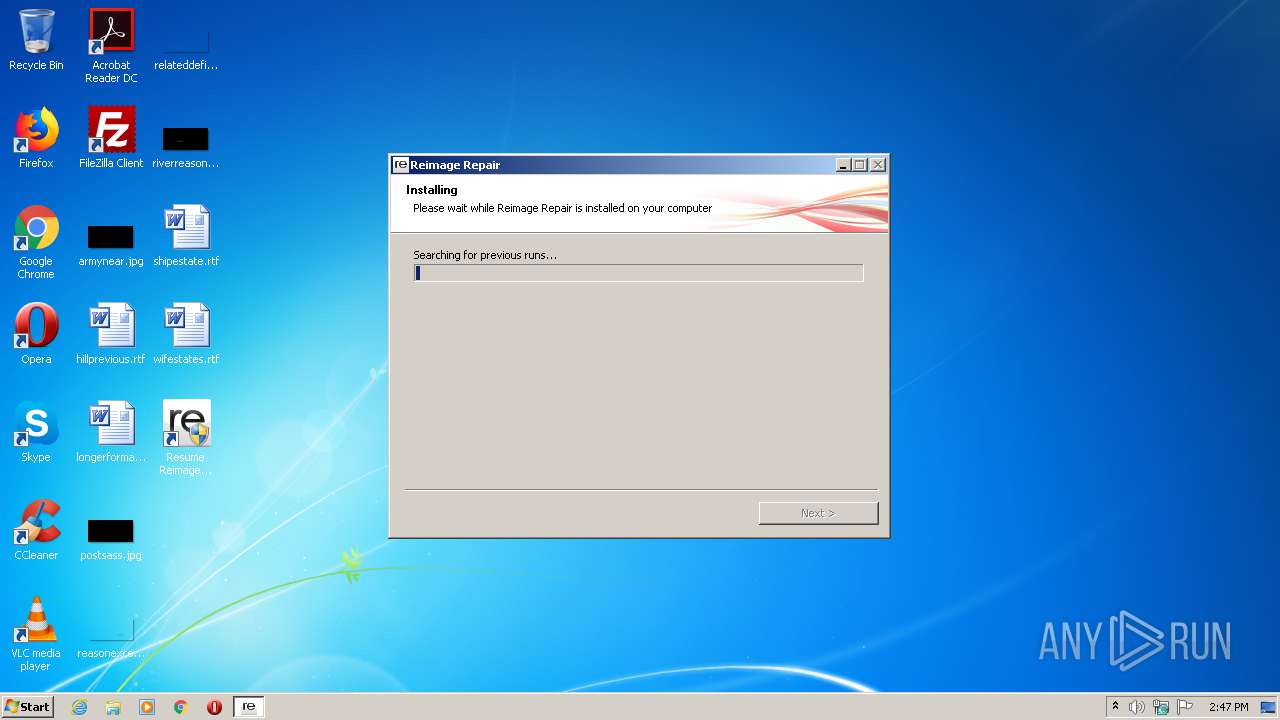
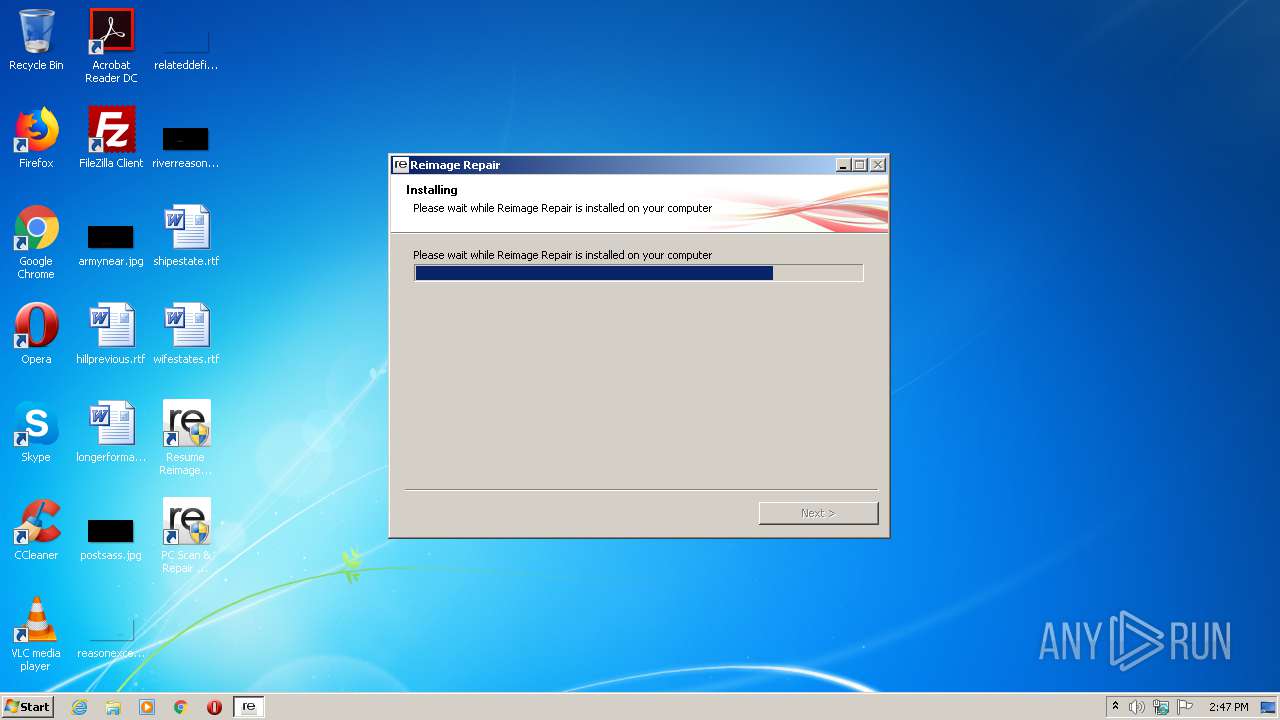
| File name: | ReimageRepair.exe |
| Full analysis: | https://app.any.run/tasks/ef710100-b537-4036-ad8a-4dc624173f0b |
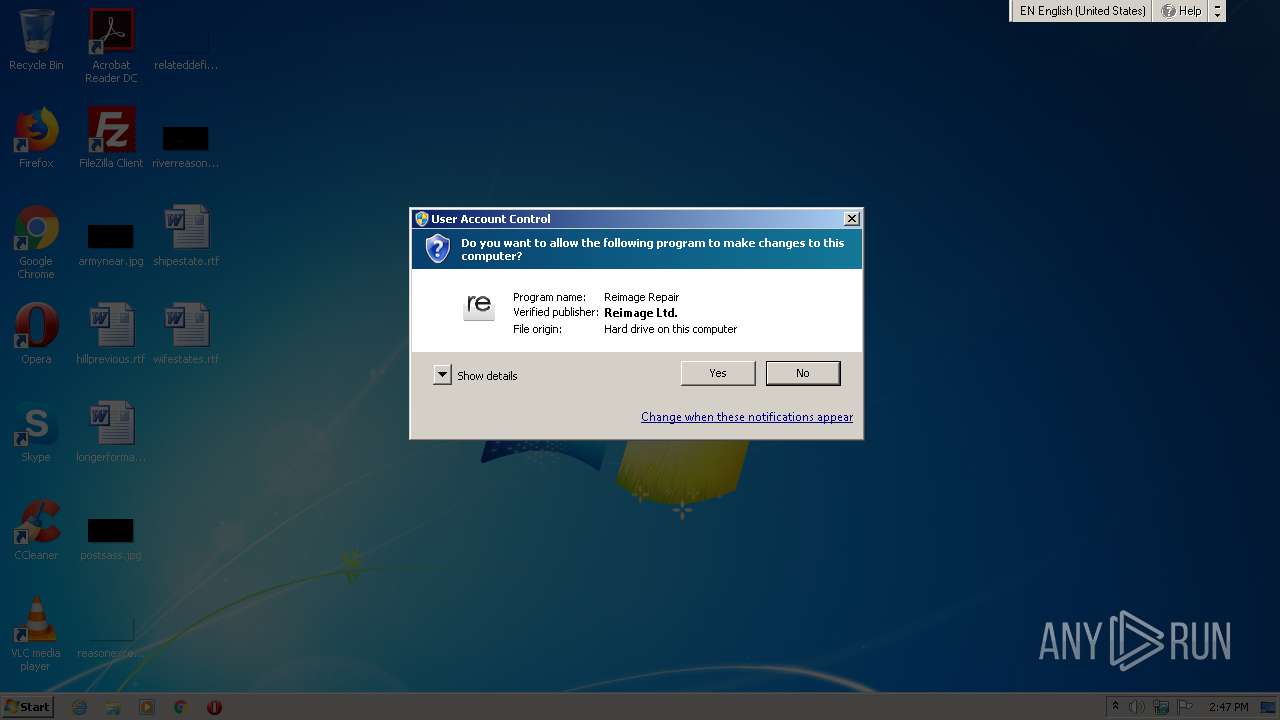
| Verdict: | Malicious activity |
| Analysis date: | May 06, 2021, 13:46:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F5AF9D859C9A031AB6BEA66048FAB6E1 |
| SHA1: | D0EE45D3534CC23CBD0D7C3765203ED926A7EB0A |
| SHA256: | 4EFD1BC1BDC12DA1BBDC597CF3F37F0C65E582F42E353CF781AC1FE422DFA68C |
| SSDEEP: | 12288:YEsvcQmY4ZHUDRHjYMCVdjQooYddMoAnUM22FT4i8BdK:Y30Q0HCFcXFRdyUKF |
MALICIOUS
Drops executable file immediately after starts
- ReimageRepair.exe (PID: 1316)
- ReimagePackage.exe (PID: 4084)
- lzma.exe (PID: 2820)
- lzma.exe (PID: 3220)
- ProtectorUpdater.exe (PID: 1744)
Steals credentials from Web Browsers
- ReimageRepair.exe (PID: 1316)
- sqlite3.exe (PID: 2296)
- sqlite3.exe (PID: 2364)
- sqlite3.exe (PID: 3584)
- sqlite3.exe (PID: 2648)
Actions looks like stealing of personal data
- ReimageRepair.exe (PID: 1316)
- sqlite3.exe (PID: 2296)
- sqlite3.exe (PID: 3584)
- sqlite3.exe (PID: 2364)
- sqlite3.exe (PID: 2648)
Application was dropped or rewritten from another process
- sqlite3.exe (PID: 2296)
- sqlite3.exe (PID: 3584)
- sqlite3.exe (PID: 2576)
- sqlite3.exe (PID: 3580)
- sqlite3.exe (PID: 3456)
- sqlite3.exe (PID: 2132)
- sqlite3.exe (PID: 2364)
- sqlite3.exe (PID: 3228)
- sqlite3.exe (PID: 1488)
- ns2540.tmp (PID: 2804)
- ns2716.tmp (PID: 2060)
- ns3061.tmp (PID: 3680)
- ns2870.tmp (PID: 3568)
- ns29D8.tmp (PID: 2276)
- ns6926.tmp (PID: 3940)
- ns915F.tmp (PID: 1916)
- ns970E.tmp (PID: 124)
- ns9D2A.tmp (PID: 476)
- sqlite3.exe (PID: 2648)
- sqlite3.exe (PID: 2472)
- nsAA3D.tmp (PID: 1752)
- sqlite3.exe (PID: 2180)
- ns9E83.tmp (PID: 984)
- nsA49E.tmp (PID: 708)
- nsB4BD.tmp (PID: 1932)
- nsBA6B.tmp (PID: 1444)
- lzma.exe (PID: 2820)
- nsC6D0.tmp (PID: 2376)
- ReimagePackage.exe (PID: 4084)
- lzma.exe (PID: 3220)
- nsC942.tmp (PID: 2396)
- nsCBB4.tmp (PID: 1332)
- nsD74E.tmp (PID: 1536)
- nsDE0E.tmp (PID: 3216)
- ProtectorUpdater.exe (PID: 1744)
Loads dropped or rewritten executable
- ReimageRepair.exe (PID: 1316)
- ReimagePackage.exe (PID: 4084)
- regsvr32.exe (PID: 832)
- ProtectorUpdater.exe (PID: 1744)
Uses TASKLIST.EXE to search for antiviruses
- cmd.exe (PID: 1952)
- cmd.exe (PID: 1424)
Registers / Runs the DLL via REGSVR32.EXE
- ReimageRepair.exe (PID: 1316)
- ReimagePackage.exe (PID: 4084)
Uses TASKLIST.EXE to search for security tools
- cmd.exe (PID: 1532)
- cmd.exe (PID: 3864)
- cmd.exe (PID: 2208)
- cmd.exe (PID: 2300)
SUSPICIOUS
Starts CMD.EXE for commands execution
- ns2540.tmp (PID: 2804)
- ns2870.tmp (PID: 3568)
- ns29D8.tmp (PID: 2276)
- ns2716.tmp (PID: 2060)
- ns3061.tmp (PID: 3680)
- ns6926.tmp (PID: 3940)
- ns915F.tmp (PID: 1916)
- ns970E.tmp (PID: 124)
- ns9E83.tmp (PID: 984)
- nsA49E.tmp (PID: 708)
- nsAA3D.tmp (PID: 1752)
- ns9D2A.tmp (PID: 476)
- nsBA6B.tmp (PID: 1444)
- nsCBB4.tmp (PID: 1332)
- nsDE0E.tmp (PID: 3216)
- nsB4BD.tmp (PID: 1932)
Reads the cookies of Mozilla Firefox
- sqlite3.exe (PID: 2296)
- sqlite3.exe (PID: 3584)
- sqlite3.exe (PID: 2364)
- sqlite3.exe (PID: 2648)
Creates files in the Windows directory
- ReimageRepair.exe (PID: 1316)
Creates files in the user directory
- sqlite3.exe (PID: 2296)
- sqlite3.exe (PID: 3584)
- sqlite3.exe (PID: 2364)
- ReimageRepair.exe (PID: 1316)
- sqlite3.exe (PID: 2648)
Executable content was dropped or overwritten
- ReimageRepair.exe (PID: 1316)
- ReimagePackage.exe (PID: 4084)
- lzma.exe (PID: 2820)
- lzma.exe (PID: 3220)
- ProtectorUpdater.exe (PID: 1744)
Reads the cookies of Google Chrome
- sqlite3.exe (PID: 2576)
- sqlite3.exe (PID: 3580)
- sqlite3.exe (PID: 2132)
- sqlite3.exe (PID: 3456)
- sqlite3.exe (PID: 1488)
- sqlite3.exe (PID: 3228)
- sqlite3.exe (PID: 2472)
- sqlite3.exe (PID: 2180)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 756)
- cmd.exe (PID: 1120)
- cmd.exe (PID: 2612)
- cmd.exe (PID: 2524)
- cmd.exe (PID: 2436)
- cmd.exe (PID: 3008)
Starts application with an unusual extension
- ReimageRepair.exe (PID: 1316)
- ReimagePackage.exe (PID: 4084)
- ProtectorUpdater.exe (PID: 1744)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2084)
- regsvr32.exe (PID: 832)
Drops a file with too old compile date
- ReimageRepair.exe (PID: 1316)
- ProtectorUpdater.exe (PID: 1744)
Creates a software uninstall entry
- ReimageRepair.exe (PID: 1316)
- ReimagePackage.exe (PID: 4084)
Creates a directory in Program Files
- ReimagePackage.exe (PID: 4084)
Creates files in the program directory
- ReimagePackage.exe (PID: 4084)
- lzma.exe (PID: 2820)
- lzma.exe (PID: 3220)
- ProtectorUpdater.exe (PID: 1744)
Drops a file that was compiled in debug mode
- ReimagePackage.exe (PID: 4084)
- lzma.exe (PID: 2820)
- lzma.exe (PID: 3220)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductVersion: | 1.956 |
|---|---|
| ProductName: | Reimage Repair |
| OriginalFileName: | ReimageRepair.exe |
| LegalTrademarks: | Reimage |
| LegalCopyright: | © Reimage 2019 |
| InternalName: | Reimage Installer |
| FileVersion: | 1.956 |
| FileDescription: | Reimage Installer |
| CompanyName: | Reimage |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.9.5.6 |
| FileVersionNumber: | 1.9.5.6 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | 6 |
| OSVersion: | 5 |
| EntryPoint: | 0x39e3 |
| UninitializedDataSize: | 16896 |
| InitializedDataSize: | 446976 |
| CodeSize: | 28672 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| TimeStamp: | 2012:02:24 20:19:59+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:19:59 |
| Detected languages: |
|
| CompanyName: | Reimage |
| FileDescription: | Reimage Installer |
| FileVersion: | 1.956 |
| InternalName: | Reimage Installer |
| LegalCopyright: | © Reimage 2019 |
| LegalTrademarks: | Reimage |
| OriginalFilename: | ReimageRepair.exe |
| ProductName: | Reimage Repair |
| ProductVersion: | 1.956 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:19:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006F10 | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49788 |
.rdata | 0x00008000 | 0x00002A92 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39389 |
.data | 0x0000B000 | 0x00067EBC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.47278 |
.ndata | 0x00073000 | 0x00331000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x003A4000 | 0x0000682D | 0x00006A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.44043 |
.reloc | 0x003AB000 | 0x00000F8A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 2.2245 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.4032 | 1461 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 0 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 3.23969 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.69442 | 544 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
137
Monitored processes
68
Malicious processes
9
Suspicious processes
15
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Users\admin\AppData\Local\Temp\nsk2444.tmp\ns970E.tmp" cmd /C tasklist /FI "IMAGENAME eq GeoProxy.exe" > C:\Users\admin\AppData\Local\Temp\IsProcessActive.txt | C:\Users\admin\AppData\Local\Temp\nsk2444.tmp\ns970E.tmp | — | ReimageRepair.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 272 | cmd /c ""C:\Users\admin\AppData\Local\Temp\FF.bat" > C:\Users\admin\AppData\Local\Temp\FF.txt" | C:\Windows\system32\cmd.exe | — | ns2540.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 288 | tasklist /FI "IMAGENAME eq Reimage.exe" | C:\Windows\system32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 476 | "C:\Users\admin\AppData\Local\Temp\nsk2444.tmp\ns9D2A.tmp" "C:\Users\admin\AppData\Local\Temp\FF.bat" > C:\Users\admin\AppData\Local\Temp\FF.txt | C:\Users\admin\AppData\Local\Temp\nsk2444.tmp\ns9D2A.tmp | — | ReimageRepair.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 632 | tasklist /FI "IMAGENAME eq avupdate.exe" | C:\Windows\system32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 708 | "C:\Users\admin\AppData\Local\Temp\nsk2444.tmp\nsA49E.tmp" cmd /C tasklist /FI "IMAGENAME eq Fiddler.exe" > C:\Users\admin\AppData\Local\Temp\IsProcessActive.txt | C:\Users\admin\AppData\Local\Temp\nsk2444.tmp\nsA49E.tmp | — | ReimageRepair.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 756 | cmd /C tasklist /FI "IMAGENAME eq Reimage.exe" > C:\Users\admin\AppData\Local\Temp\IsProcessActive.txt | C:\Windows\system32\cmd.exe | — | ns29D8.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 832 | regsvr32 /s "C:\Program Files\Reimage\Reimage Repair\REI_Axcontrol.dll" | C:\Windows\system32\regsvr32.exe | — | ReimagePackage.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 900 | tasklist /FI "IMAGENAME eq REI_avira.exe" | C:\Windows\system32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 984 | "C:\Users\admin\AppData\Local\Temp\nsk2444.tmp\ns9E83.tmp" cmd /C tasklist /FI "IMAGENAME eq Wireshark.exe" > C:\Users\admin\AppData\Local\Temp\IsProcessActive.txt | C:\Users\admin\AppData\Local\Temp\nsk2444.tmp\ns9E83.tmp | — | ReimageRepair.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 049
Read events
863
Write events
113
Delete events
73
Modification events
| (PID) Process: | (1316) ReimageRepair.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1316) ReimageRepair.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1316) ReimageRepair.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1316) ReimageRepair.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1316) ReimageRepair.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1316) ReimageRepair.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1316) ReimageRepair.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1316) ReimageRepair.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Reimage\Reimage Repair |
| Operation: | write | Name: | Installer Language |
Value: 1033 | |||
| (PID) Process: | (1316) ReimageRepair.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 74 | |||
| (PID) Process: | (2084) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{f414c260-6ac0-11cf-b6d1-00aa00bbbb58}\Implemented Categories\{F0B7A1A1-9847-11CF-8F20-00805F2CD064} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
58
Suspicious files
5
Text files
45
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1316 | ReimageRepair.exe | C:\Users\admin\AppData\Local\Temp\nsa252F.tmp | — | |
MD5:— | SHA256:— | |||
| 1316 | ReimageRepair.exe | C:\Users\admin\AppData\Local\Temp\FF.bat | — | |
MD5:— | SHA256:— | |||
| 1316 | ReimageRepair.exe | C:\Users\admin\AppData\Local\Temp\nsk2444.tmp\ns2540.tmp | — | |
MD5:— | SHA256:— | |||
| 2296 | sqlite3.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 1316 | ReimageRepair.exe | C:\Users\admin\AppData\Local\Temp\nsb2706.tmp | — | |
MD5:— | SHA256:— | |||
| 1316 | ReimageRepair.exe | C:\Users\admin\AppData\Local\Temp\nsk2444.tmp\ns2716.tmp | — | |
MD5:— | SHA256:— | |||
| 3584 | sqlite3.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 1316 | ReimageRepair.exe | C:\Users\admin\AppData\Local\Temp\nsg285F.tmp | — | |
MD5:— | SHA256:— | |||
| 2364 | sqlite3.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 1316 | ReimageRepair.exe | C:\Users\admin\AppData\Local\Temp\nsk2444.tmp\ns3061.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
6
DNS requests
3
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1744 | ProtectorUpdater.exe | GET | 200 | 205.185.208.80:80 | http://cdnrep.reimage.com/protector_version.xml | US | xml | 574 b | whitelisted |
1316 | ReimageRepair.exe | GET | 200 | 205.185.208.80:80 | http://cdnrep.reimageplus.com/cfl/cfl1956b.rei | US | binary | 969 Kb | suspicious |
1744 | ProtectorUpdater.exe | GET | 200 | 205.185.208.80:80 | http://cdnrep.reimage.com/prot/ProtectorPackage2027a.exe | US | executable | 5.26 Mb | whitelisted |
1744 | ProtectorUpdater.exe | GET | 200 | 161.47.7.14:80 | http://www.reimageplus.com/scan_agent_events.php?version=2027&SessionID=98292e41-8b05-4dfc-b029-692576454d71&MinorSessionID=c462592a7e394f37a3b78b9bd4&id=INSVR¶m=2027&trackutil= | US | text | 2 b | suspicious |
1316 | ReimageRepair.exe | GET | 200 | 161.47.7.14:80 | http://www.reimageplus.com/installer.php?tracking=&sessionid=98292e41-8b05-4dfc-b029-692576454d71 | US | xml | 75 b | suspicious |
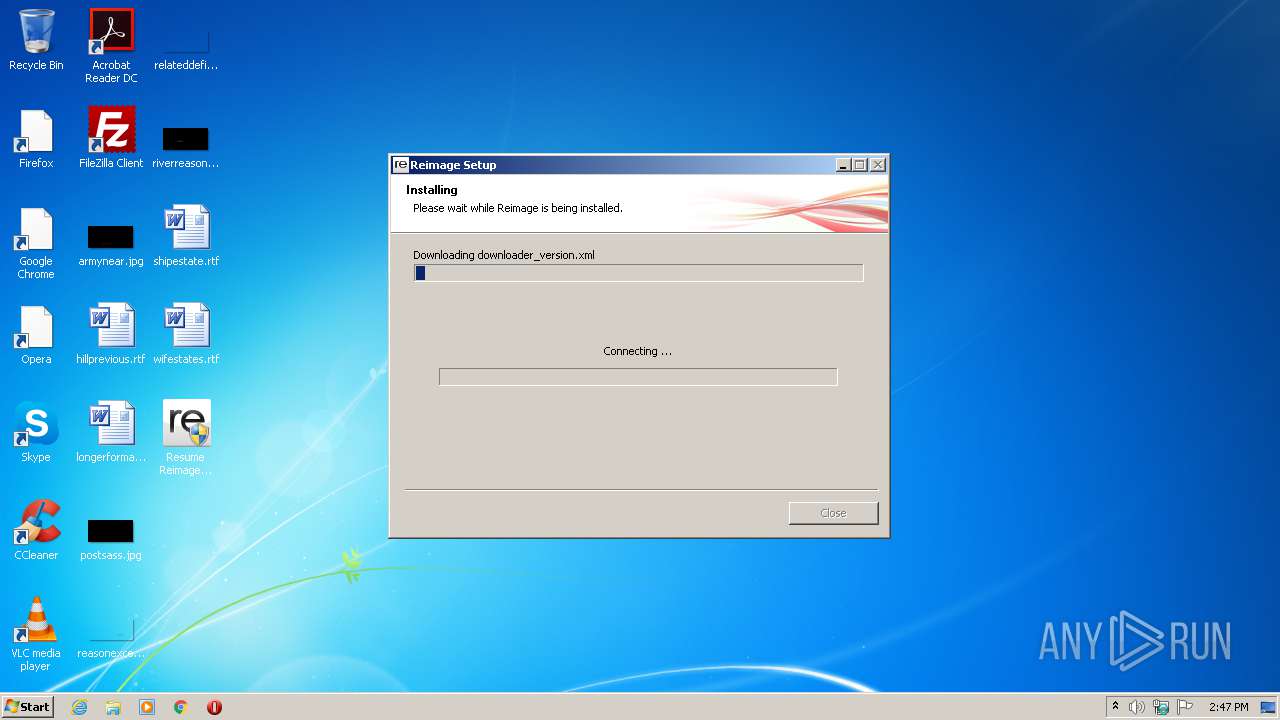
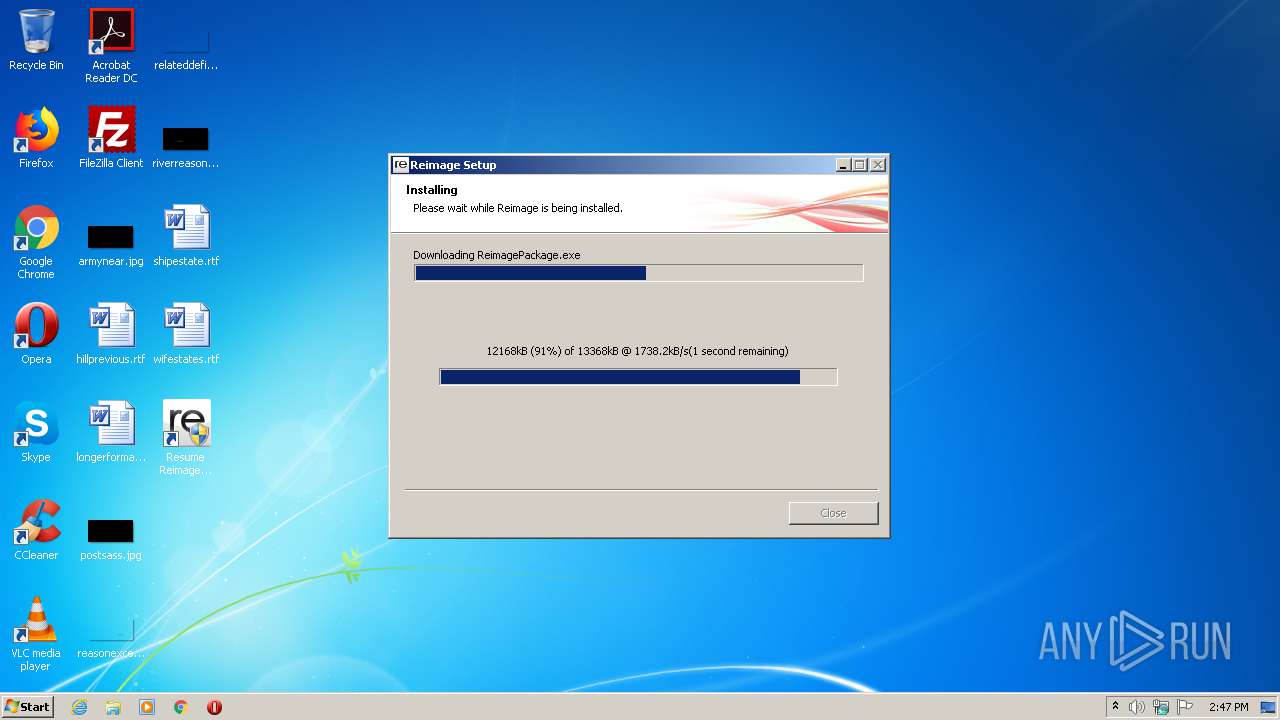
1316 | ReimageRepair.exe | GET | 200 | 205.185.208.80:80 | http://cdnrep.reimageplus.com/ver/ReimagePackage1956b.exe | US | executable | 13.0 Mb | suspicious |
1316 | ReimageRepair.exe | GET | 200 | 205.185.208.80:80 | http://cdnrep.reimage.com/downloader_version.xml | US | xml | 418 b | whitelisted |
1316 | ReimageRepair.exe | GET | 200 | 205.185.208.80:80 | http://cdnrep.reimage.com/repair_version.xml | US | xml | 1.09 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1316 | ReimageRepair.exe | 161.47.7.14:80 | www.reimageplus.com | Rackspace Ltd. | US | malicious |
1316 | ReimageRepair.exe | 205.185.208.80:80 | cdnrep.reimage.com | Highwinds Network Group, Inc. | US | suspicious |
1744 | ProtectorUpdater.exe | 205.185.208.80:80 | cdnrep.reimage.com | Highwinds Network Group, Inc. | US | suspicious |
1744 | ProtectorUpdater.exe | 161.47.7.14:80 | www.reimageplus.com | Rackspace Ltd. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.reimageplus.com |
| suspicious |
cdnrep.reimage.com |
| whitelisted |
cdnrep.reimageplus.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1316 | ReimageRepair.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
1316 | ReimageRepair.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
1316 | ReimageRepair.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
1316 | ReimageRepair.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
1316 | ReimageRepair.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
1316 | ReimageRepair.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
1316 | ReimageRepair.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1316 | ReimageRepair.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
1316 | ReimageRepair.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
1744 | ProtectorUpdater.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |