| URL: | https://theaudioastronaut.com/res444.php?4-68747470733a2f2f74322e726c71706f6e61776975792e72752f754a736557472f-https%3A%2F%2Fna4.docusign.net%2FSigning%2FError.aspx%3Fe=e4e46502-e17b-4c5c-927c-e927787f7599&scope=556caf4b-c6c2-4e0c-9630-2e2ca25b39e1 |
| Full analysis: | https://app.any.run/tasks/16c6514b-5724-4375-9ab4-bfce730ec569 |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 18:57:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C512FA3BB60B0F15303B106981CAC1FE |
| SHA1: | 8CC72D35DDC1407CA99F0220951632B495CD2926 |
| SHA256: | 4EF93A050721AFF65B5A996486C03A23C6BC47E55CF7589E67E1846E5AF711FC |
| SSDEEP: | 6:2vQK5cu0ReSieFRFsagnR1zwxADDKfV0rHoESs6yUZALE:21cu7HeW1EhfVc9GN5 |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 4792)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
151
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 4792 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2604 --field-trial-handle=2320,i,16194277592197507296,15814343983252007256,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
18
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\Network Persistent State~RF2b6dbc.TMP | binary | |
MD5:2A21453795942FD88CBB06714604B9FD | SHA256:5DFE0384325B556EE4B8668E502312B9BA6ADC298CD9213DDFA528CB959ADC06 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\d7dad890-2a3d-4cee-8a0f-0aaa1f37ce3c.tmp | binary | |
MD5:FDC928600E63D48E904F8F98C48F6C1C | SHA256:506548371F2898D103E8BCCDFE5AC7C1C6974265AEED5554459ACF03F31D6498 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\Network Persistent State~RF2c579f.TMP | binary | |
MD5:ED74D0CC3CAB53CA501F3CD6C50FAA1A | SHA256:331BB0DA5A3BE7843A14503DA9547E7309F3631916C6112882FF36D75025E7EE | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\70a18bdb-246c-4db2-99fb-9fa16de19a9f.tmp | binary | |
MD5:ED74D0CC3CAB53CA501F3CD6C50FAA1A | SHA256:331BB0DA5A3BE7843A14503DA9547E7309F3631916C6112882FF36D75025E7EE | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\Network Persistent State | binary | |
MD5:ED74D0CC3CAB53CA501F3CD6C50FAA1A | SHA256:331BB0DA5A3BE7843A14503DA9547E7309F3631916C6112882FF36D75025E7EE | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\bfb78987-79c0-4f0d-94f0-67fa6ba6c0a1.tmp | binary | |
MD5:EB73435B2353918A4E784242ADFECAB0 | SHA256:621CAC4EC9F76C200EFA4E6FDDF2BA3AA289C93DCA8D83EAFEFB8E14A2445F4B | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\b5c846cf-e9db-452a-abab-6248216ac05a.tmp | binary | |
MD5:5F091A7EEFDF3D1E633DE95C982E53C8 | SHA256:BCC6D24A937B36A636FB19EA7FAF55D55A4364A9A4253349D805DF134FB6ECD6 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000bb | compressed | |
MD5:CA6E0DCAF6FE11E3B4D4D299ECBAB7A6 | SHA256:F4A93CF3834C5F3BBBAB2BA619425FB1415050A847F5BC12CD6B0BAB5E68074E | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\Network Persistent State~RF2e7d7d.TMP | binary | |
MD5:EB73435B2353918A4E784242ADFECAB0 | SHA256:621CAC4EC9F76C200EFA4E6FDDF2BA3AA289C93DCA8D83EAFEFB8E14A2445F4B | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\TransportSecurity~RF2b9634.TMP | binary | |
MD5:5F091A7EEFDF3D1E633DE95C982E53C8 | SHA256:BCC6D24A937B36A636FB19EA7FAF55D55A4364A9A4253349D805DF134FB6ECD6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
71
DNS requests
44
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 302 | 104.18.95.41:443 | https://challenges.cloudflare.com/turnstile/v0/api.js?render=explicit | unknown | — | — | — |
— | — | HEAD | 200 | 23.218.208.109:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | — |
— | — | GET | — | 104.18.95.41:443 | https://challenges.cloudflare.com/cdn-cgi/challenge-platform/h/g/orchestrate/chl_api/v1?ray=8f182ee06ad74fe4&lang=auto | unknown | — | — | — |
— | — | GET | — | 104.18.94.41:443 | https://challenges.cloudflare.com/cdn-cgi/challenge-platform/h/g/turnstile/if/ov2/av0/rcv/kpyhc/0x4AAAAAAA0sILsJMpzIlaz1/auto/fbE/normal/auto/ | unknown | — | — | — |
— | — | GET | 200 | 13.107.246.45:443 | https://xpaywalletcdn.azureedge.net/mswallet/ExpressCheckout/v2/GetEligibleSites?version=0&type=commonConfig&IsStable=false | unknown | binary | 481 b | whitelisted |
— | — | GET | 200 | 104.17.24.14:443 | https://cdnjs.cloudflare.com/ajax/libs/crypto-js/4.0.0/crypto-js.min.js | unknown | binary | 46.8 Kb | whitelisted |
— | — | GET | 200 | 23.218.208.109:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | binary | 55 b | whitelisted |
— | — | GET | 200 | 13.107.246.45:443 | https://xpaywalletcdn.azureedge.net/mswallet/ExpressCheckout/v2/GetEligibleSites?version=0&type=topSite&IsStable=false | unknown | binary | 497 b | whitelisted |
— | — | GET | 200 | 69.49.245.172:443 | https://theaudioastronaut.com/res444.php?4-68747470733a2f2f74322e726c71706f6e61776975792e72752f754a736557472f-https%3A%2F%2Fna4.docusign.net%2FSigning%2FError.aspx%3Fe=e4e46502-e17b-4c5c-927c-e927787f7599&scope=556caf4b-c6c2-4e0c-9630-2e2ca25b39e1 | unknown | html | 3.56 Kb | — |
— | — | GET | 200 | 104.17.25.14:443 | https://cdnjs.cloudflare.com/ajax/libs/crypto-js/4.1.1/crypto-js.min.js | unknown | binary | 47.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2768 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4304 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4792 | msedge.exe | 20.189.173.26:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4668 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
5988 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4792 | msedge.exe | 69.49.245.172:443 | theaudioastronaut.com | UNIFIEDLAYER-AS-1 | US | unknown |
3704 | svchost.exe | 23.218.208.109:443 | fs.microsoft.com | AKAMAI-AS | DE | whitelisted |
4792 | msedge.exe | 104.126.37.131:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4792 | msedge.exe | 104.17.24.14:443 | cdnjs.cloudflare.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
theaudioastronaut.com |
| unknown |
fs.microsoft.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.bing.com |
| whitelisted |
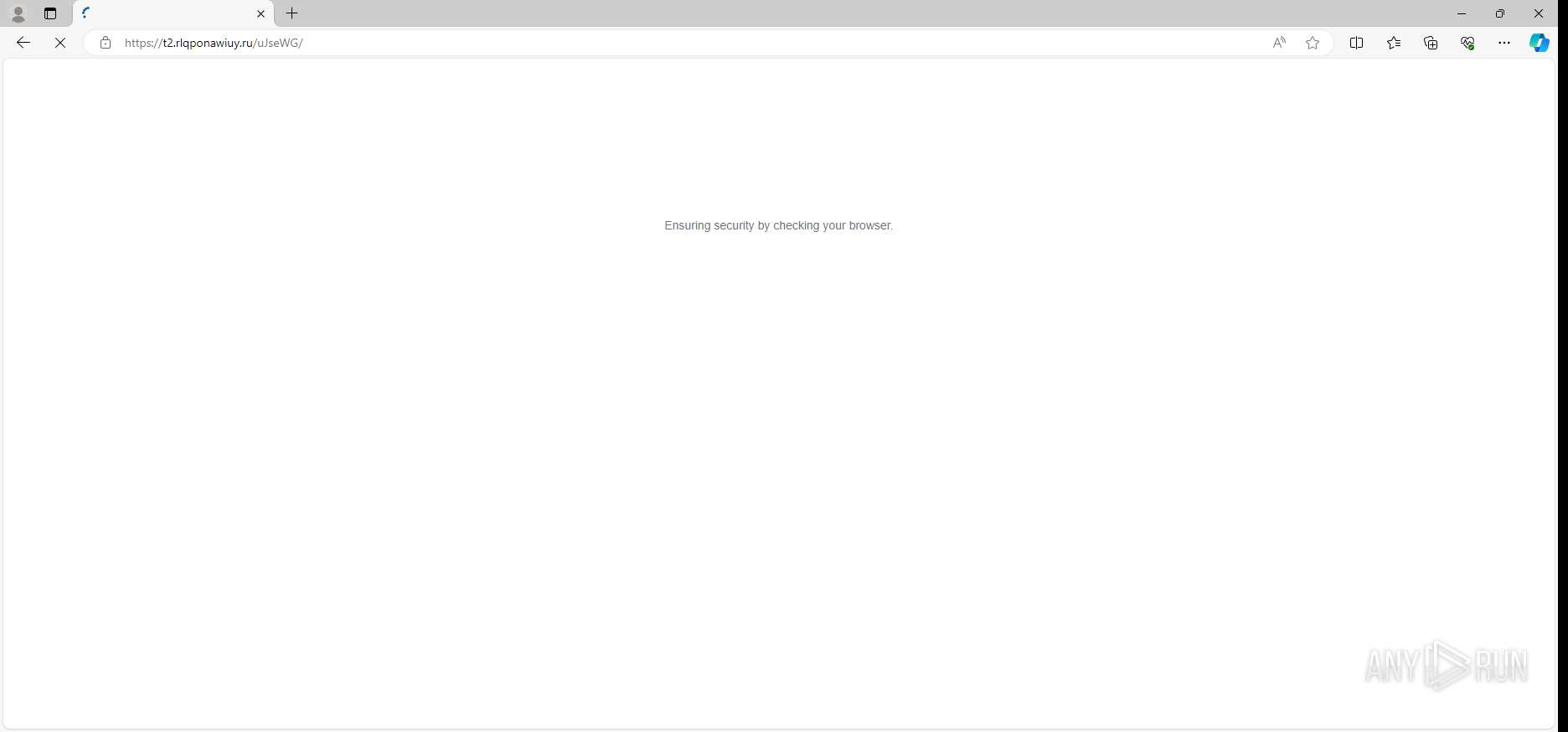
t2.rlqponawiuy.ru |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
code.jquery.com |
| whitelisted |
challenges.cloudflare.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Storms-1747`s Phishing domain by CrossDomain ( .rlqponawiuy .ru) |
— | — | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Storms-1747`s Phishing domain by CrossDomain ( .rlqponawiuy .ru) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |