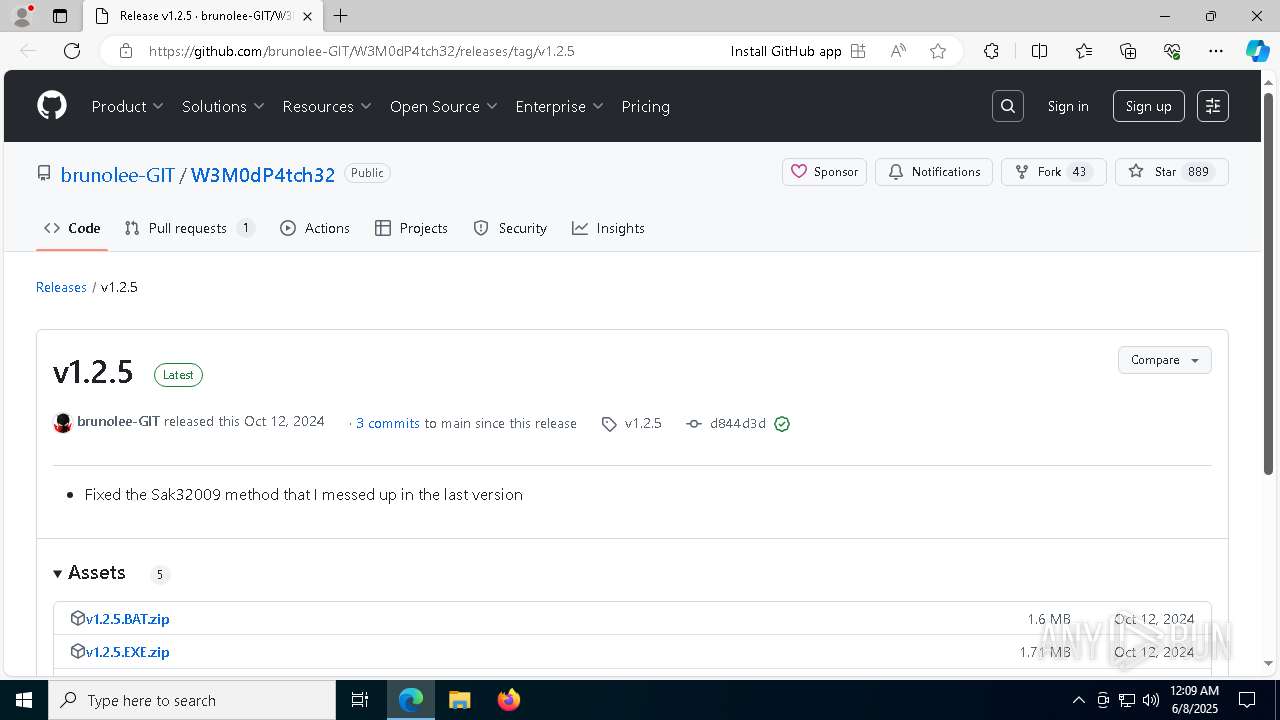
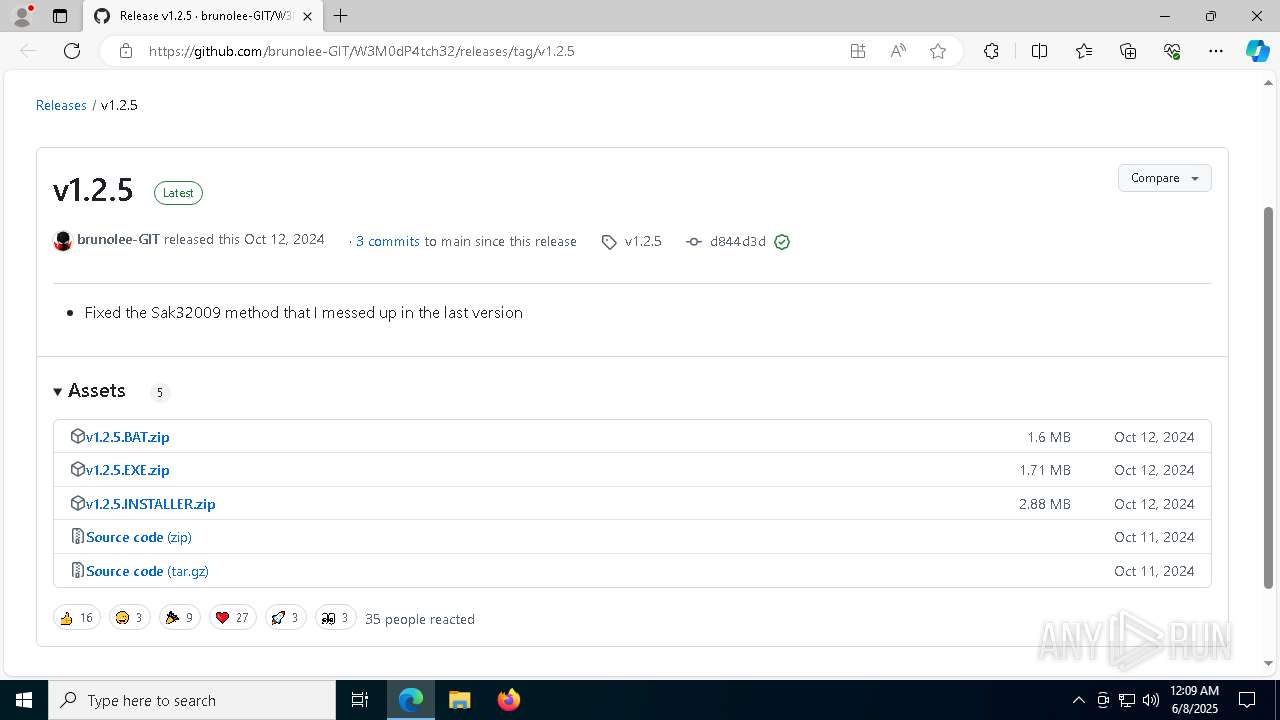
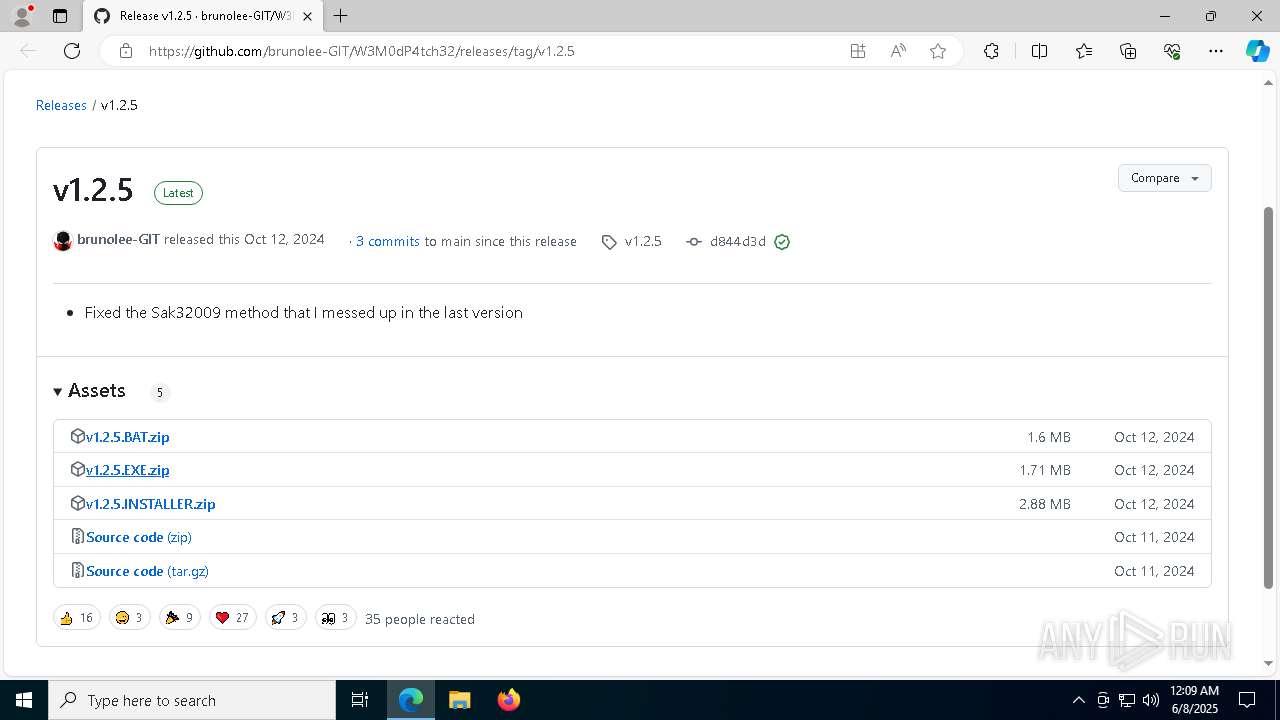
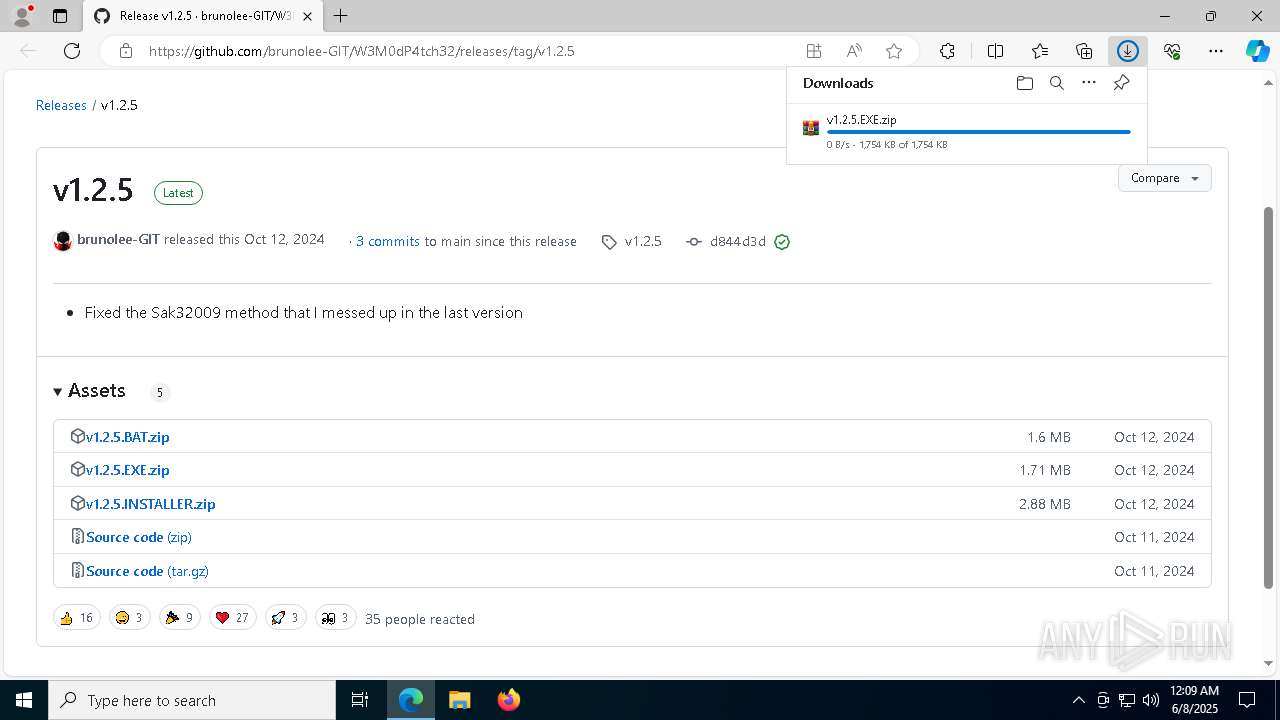
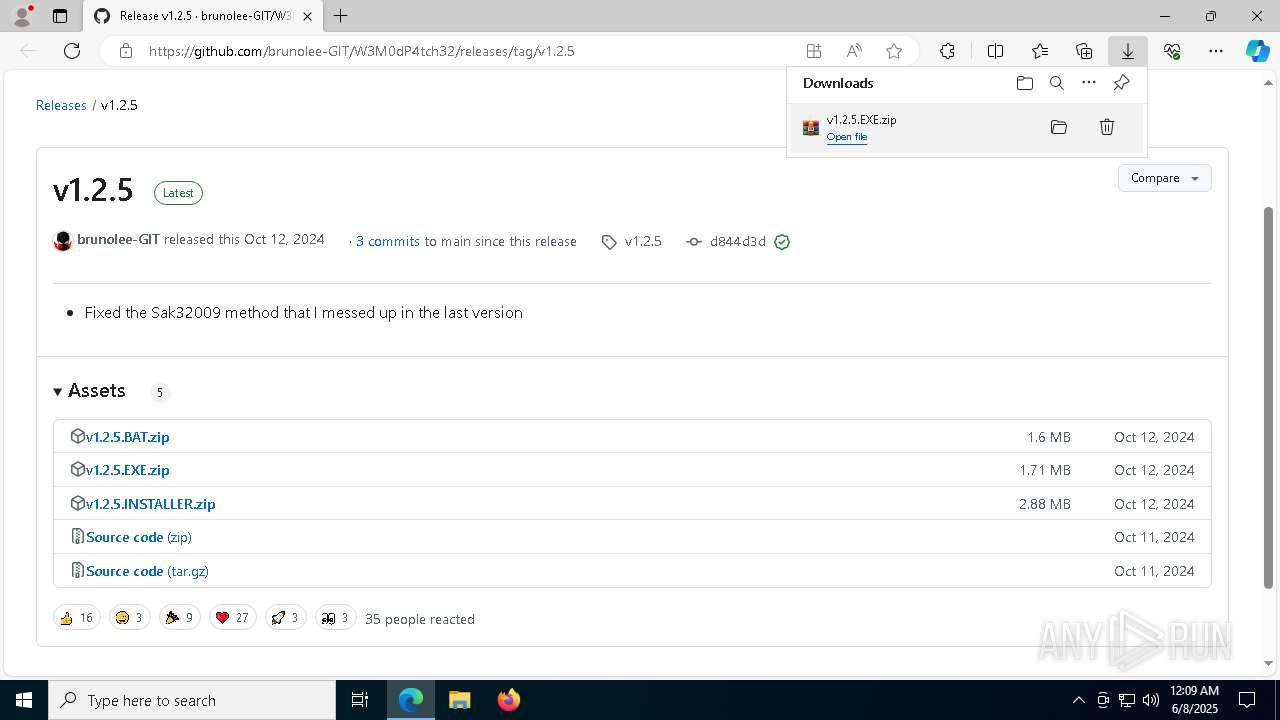
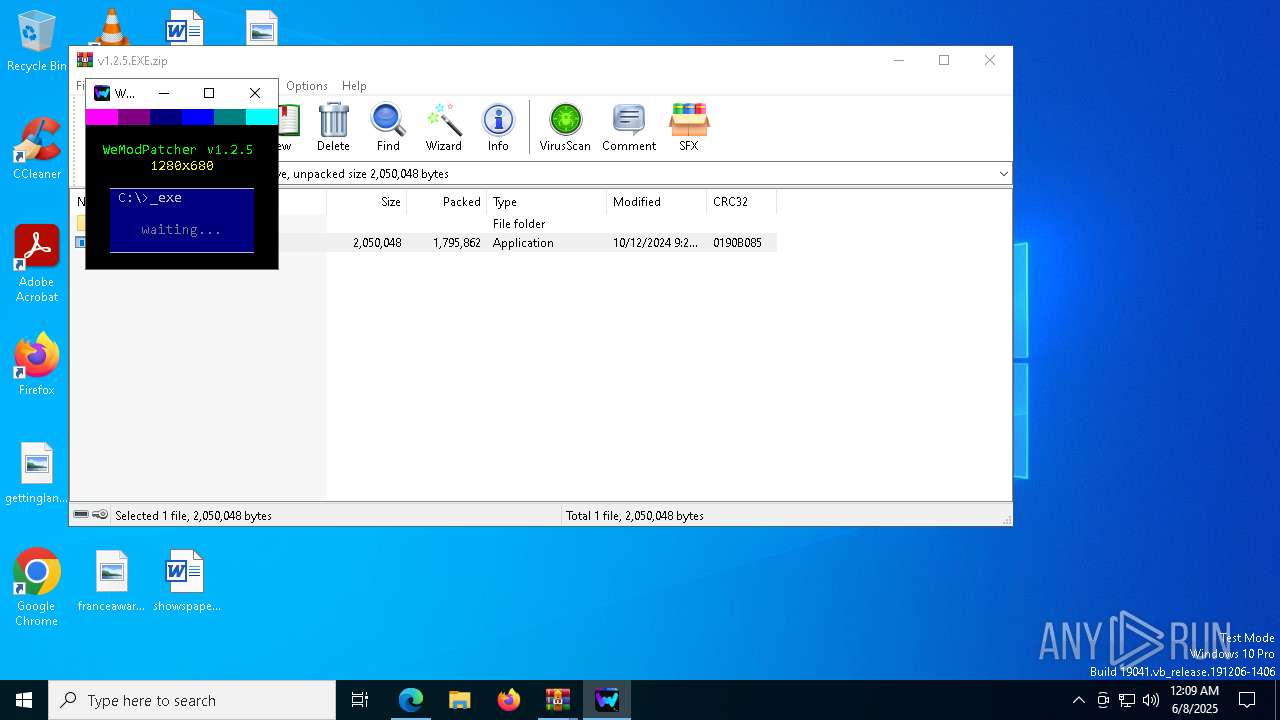
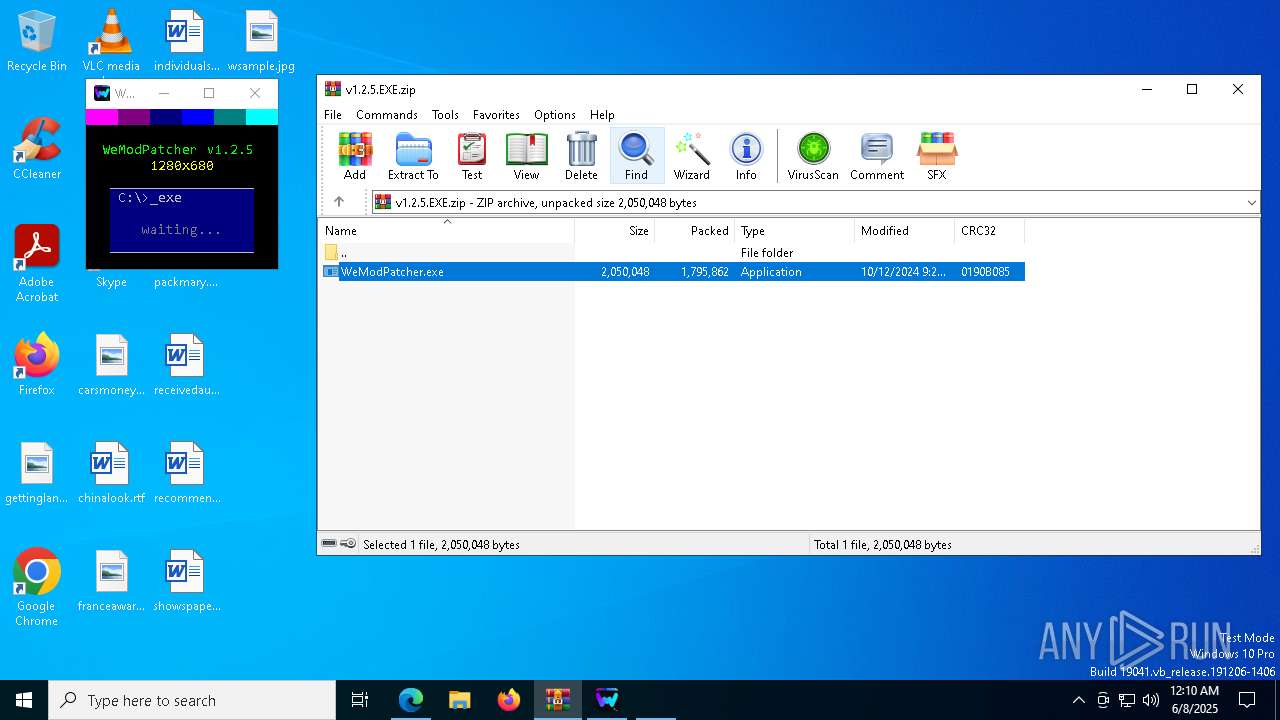
| URL: | https://github.com/brunolee-GIT/W3M0dP4tch32/releases/tag/v1.2.5 |
| Full analysis: | https://app.any.run/tasks/e51f650d-dfd2-4a41-a140-3a1487ad63d4 |
| Verdict: | Malicious activity |
| Analysis date: | June 08, 2025, 00:09:12 |
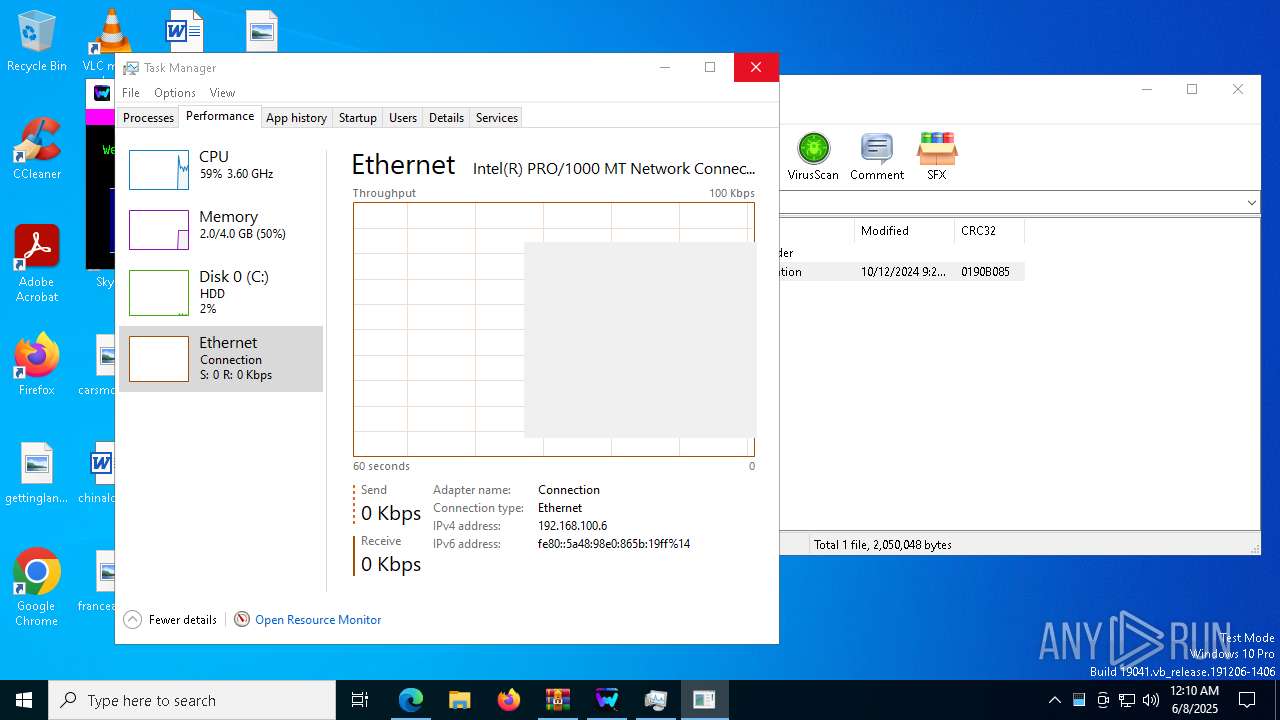
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C5B415E70393321D62EBE8065F2C4187 |
| SHA1: | 65235B3914B53AA76F18BFB8566D614535ED4CE3 |
| SHA256: | 4EEB4D57B946770BB124D691D1C1A605D26EE3EB3871B10900980666470DBED4 |
| SSDEEP: | 3:N8tEd3FJlyWkRRG+0qK/:2uxYRGXx/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
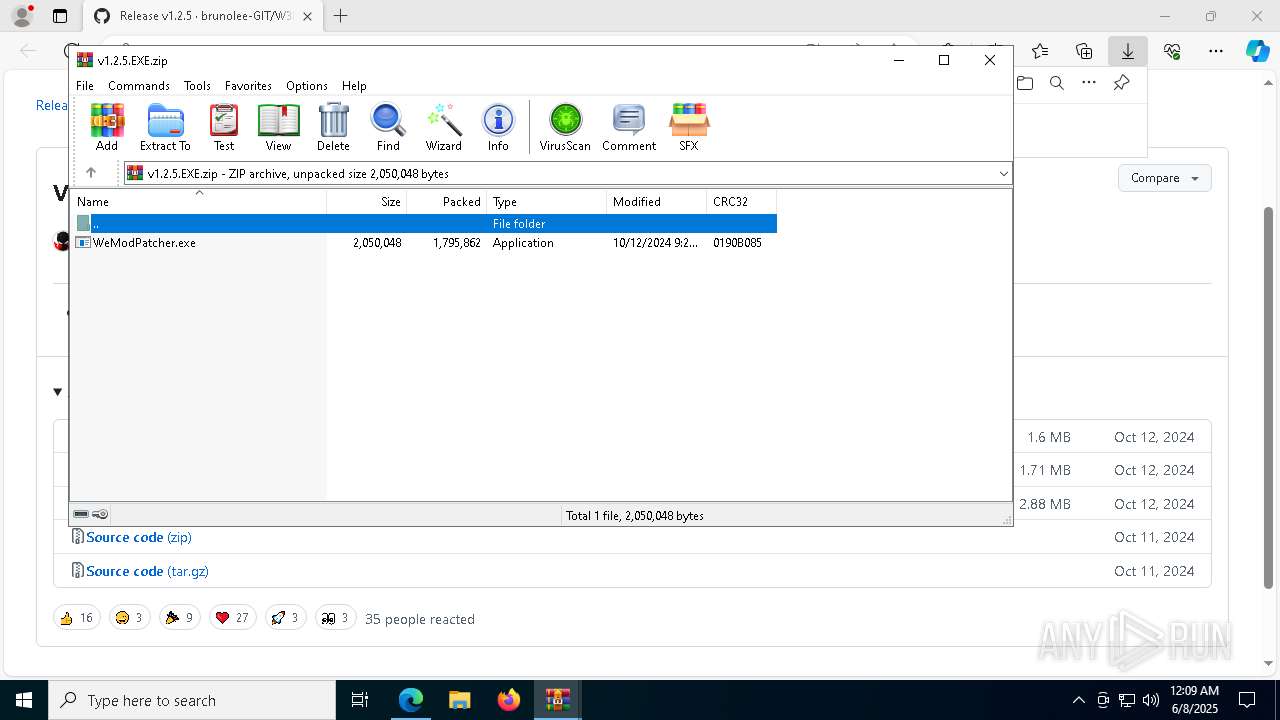
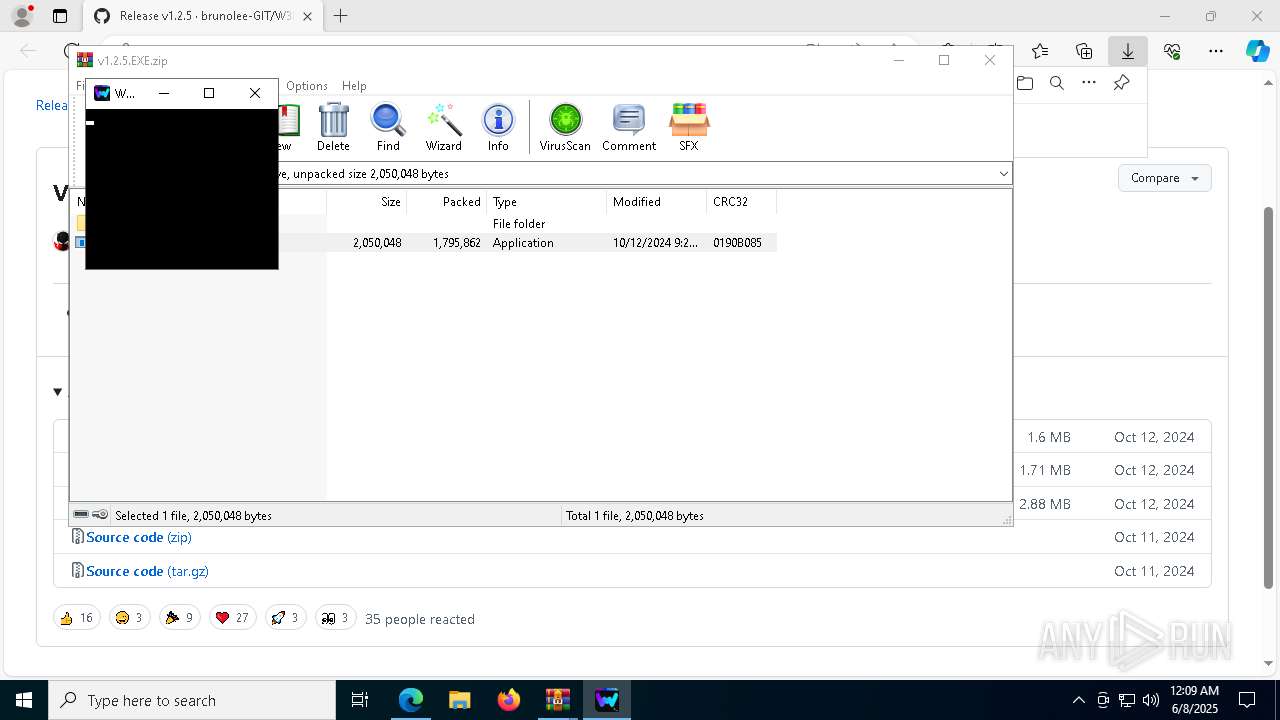
Executing commands from a ".bat" file
- WeModPatcher.exe (PID: 7468)
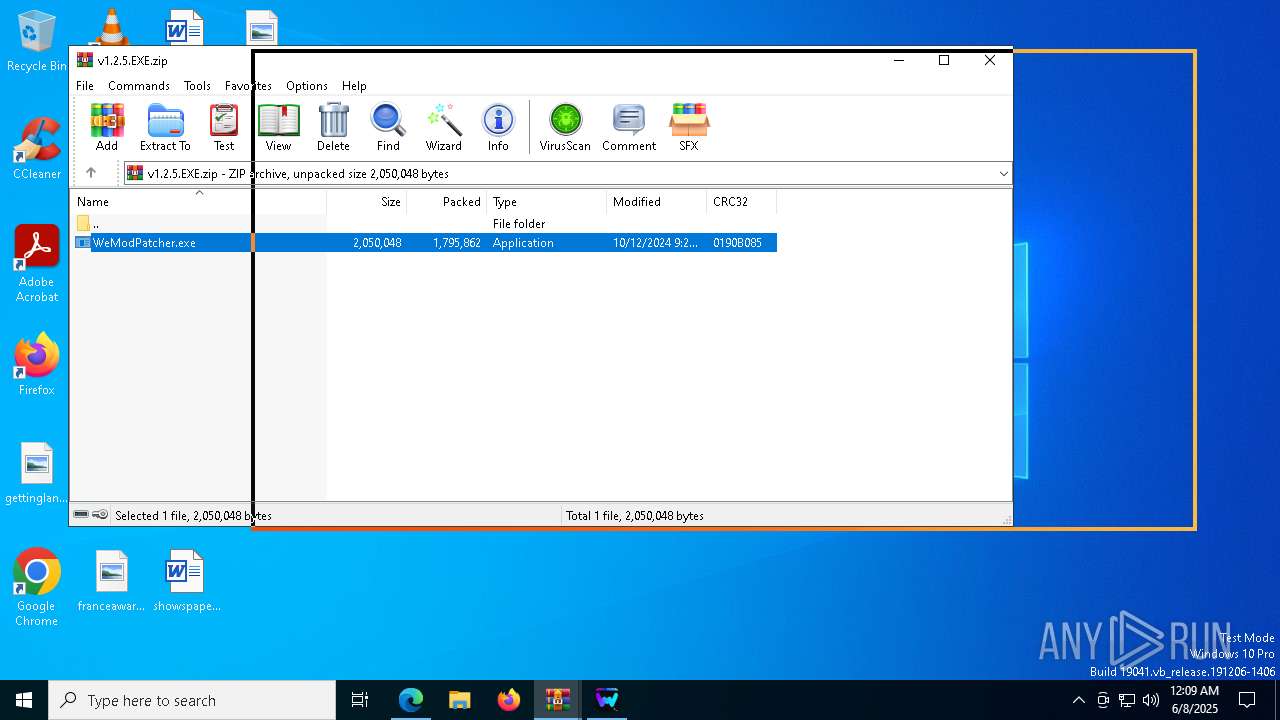
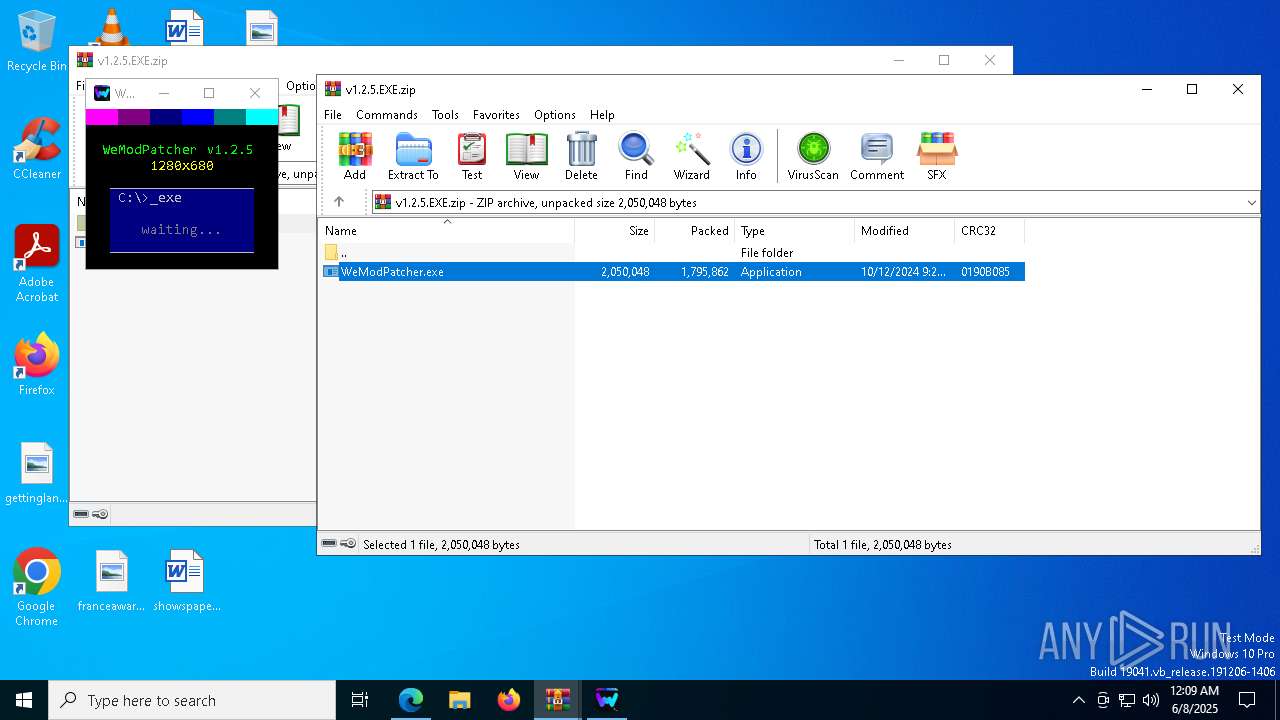
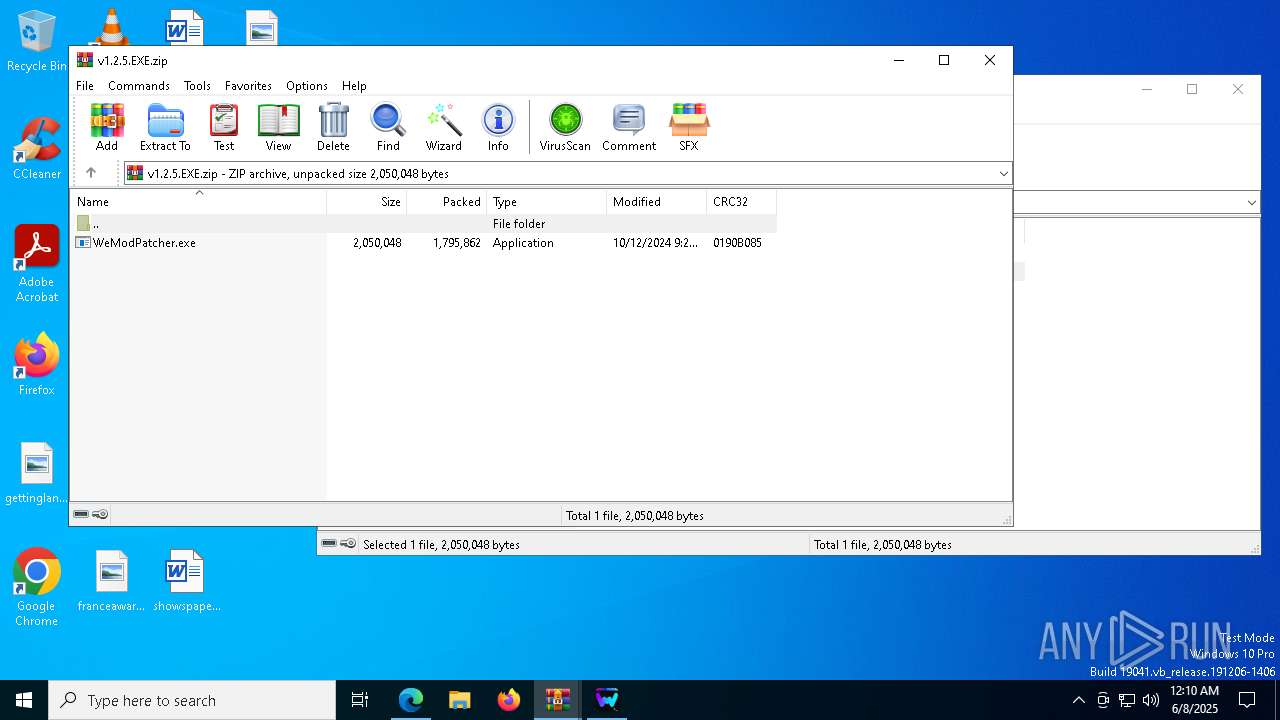
Drops 7-zip archiver for unpacking
- WeModPatcher.exe (PID: 7468)
Execution of CURL command
- cmd.exe (PID: 2516)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2516)
- WeModPatcher.exe (PID: 7468)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8100)
Get information on the list of running processes
- cmd.exe (PID: 616)
- cmd.exe (PID: 4424)
- cmd.exe (PID: 2516)
- cmd.exe (PID: 5868)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4424)
- cmd.exe (PID: 8128)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 8004)
- cmd.exe (PID: 6516)
- cmd.exe (PID: 7440)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 4020)
- cmd.exe (PID: 2516)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 7916)
- cmd.exe (PID: 864)
- cmd.exe (PID: 7444)
- cmd.exe (PID: 1132)
Starts NET.EXE to display or manage information about active sessions
- net.exe (PID: 7992)
- cmd.exe (PID: 2516)
Application launched itself
- cmd.exe (PID: 2516)
Starts application with an unusual extension
- cmd.exe (PID: 2516)
- cmd.exe (PID: 660)
Executes application which crashes
- mshta.exe (PID: 7300)
- mshta.exe (PID: 540)
- mshta.exe (PID: 6560)
- mshta.exe (PID: 5556)
- mshta.exe (PID: 240)
INFO
Reads the computer name
- identity_helper.exe (PID: 5260)
- curl.exe (PID: 6712)
Application launched itself
- msedge.exe (PID: 6940)
Reads Environment values
- identity_helper.exe (PID: 5260)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8100)
The sample compiled with english language support
- msedge.exe (PID: 6108)
- WinRAR.exe (PID: 8100)
- msedge.exe (PID: 6940)
- WeModPatcher.exe (PID: 7468)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6940)
Checks supported languages
- WeModPatcher.exe (PID: 7468)
- curl.exe (PID: 6712)
- chcp.com (PID: 6564)
- identity_helper.exe (PID: 5260)
- chcp.com (PID: 3272)
- mode.com (PID: 7460)
Create files in a temporary directory
- WeModPatcher.exe (PID: 7468)
Launching a file from the Downloads directory
- msedge.exe (PID: 6940)
Execution of CURL command
- cmd.exe (PID: 2064)
Changes the display of characters in the console
- cmd.exe (PID: 2516)
- cmd.exe (PID: 660)
Starts MODE.COM to configure console settings
- mode.com (PID: 7460)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7528)
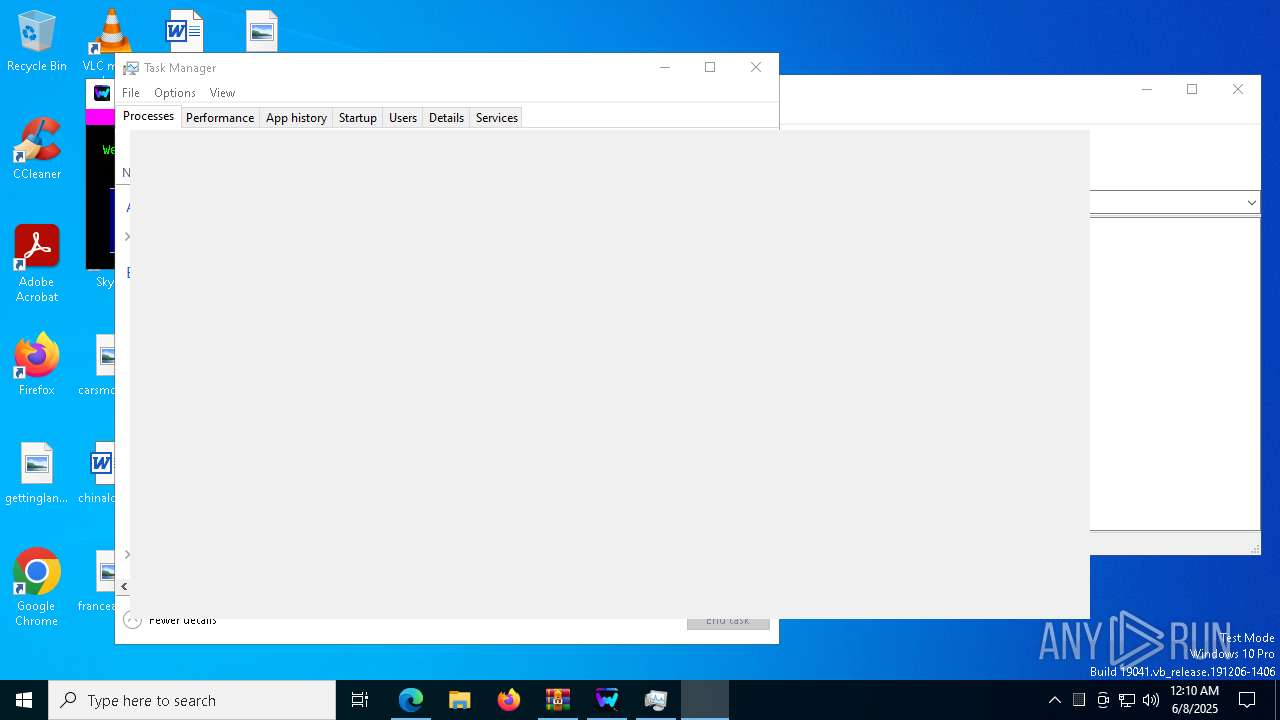
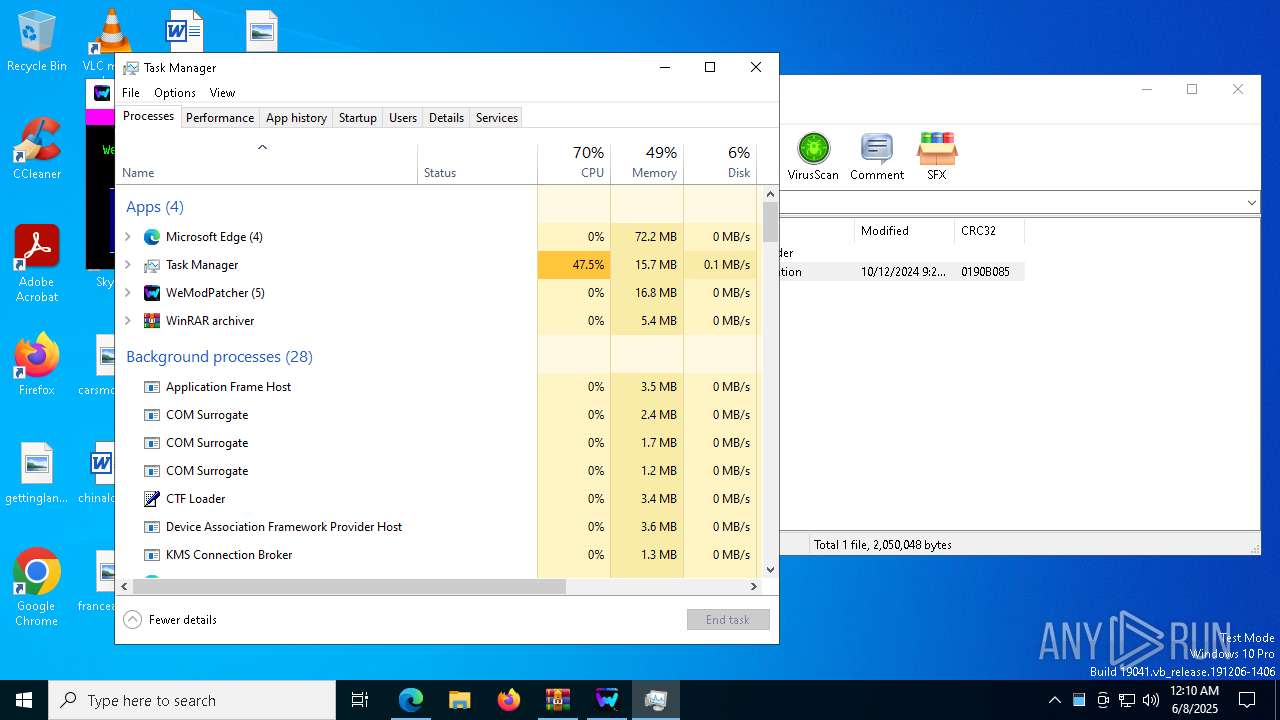
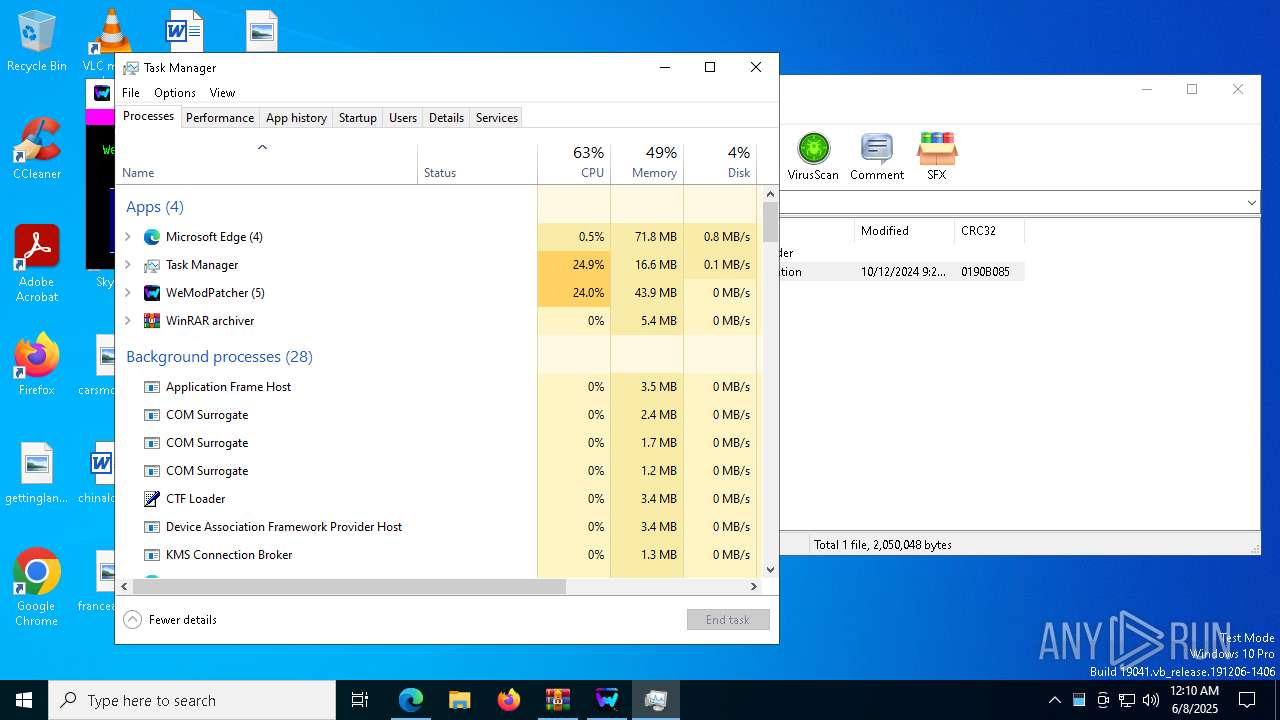
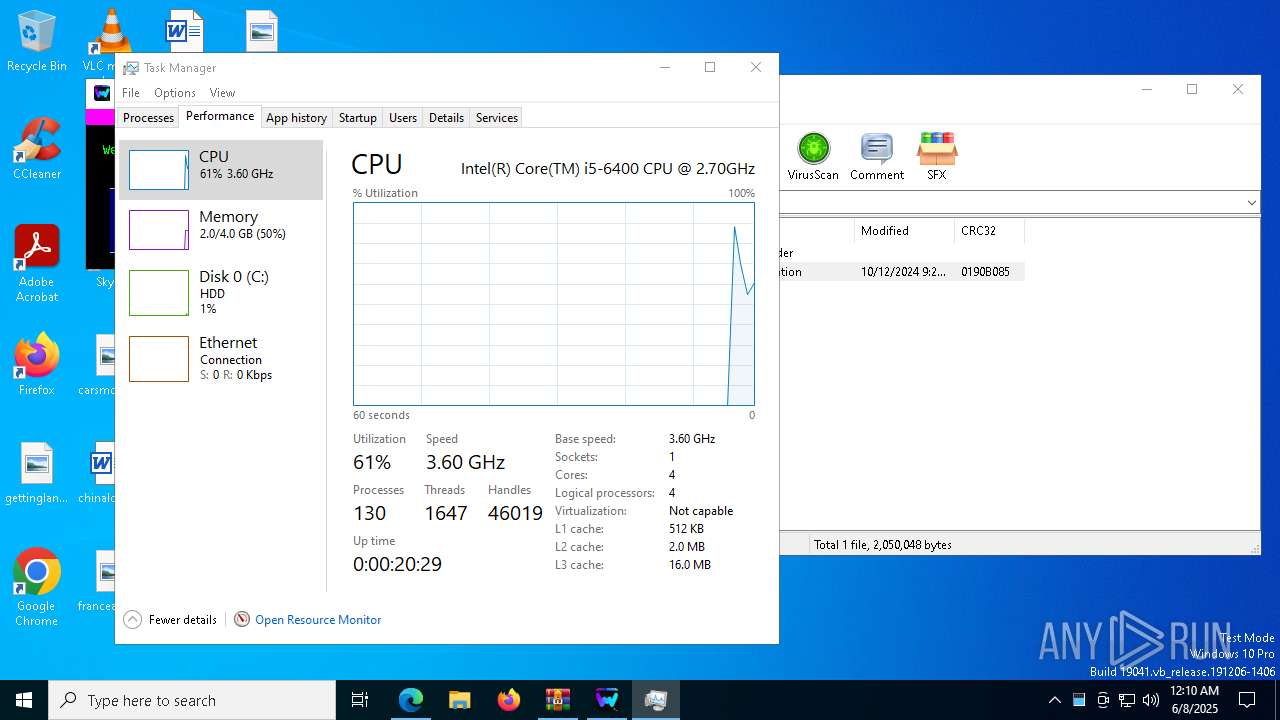
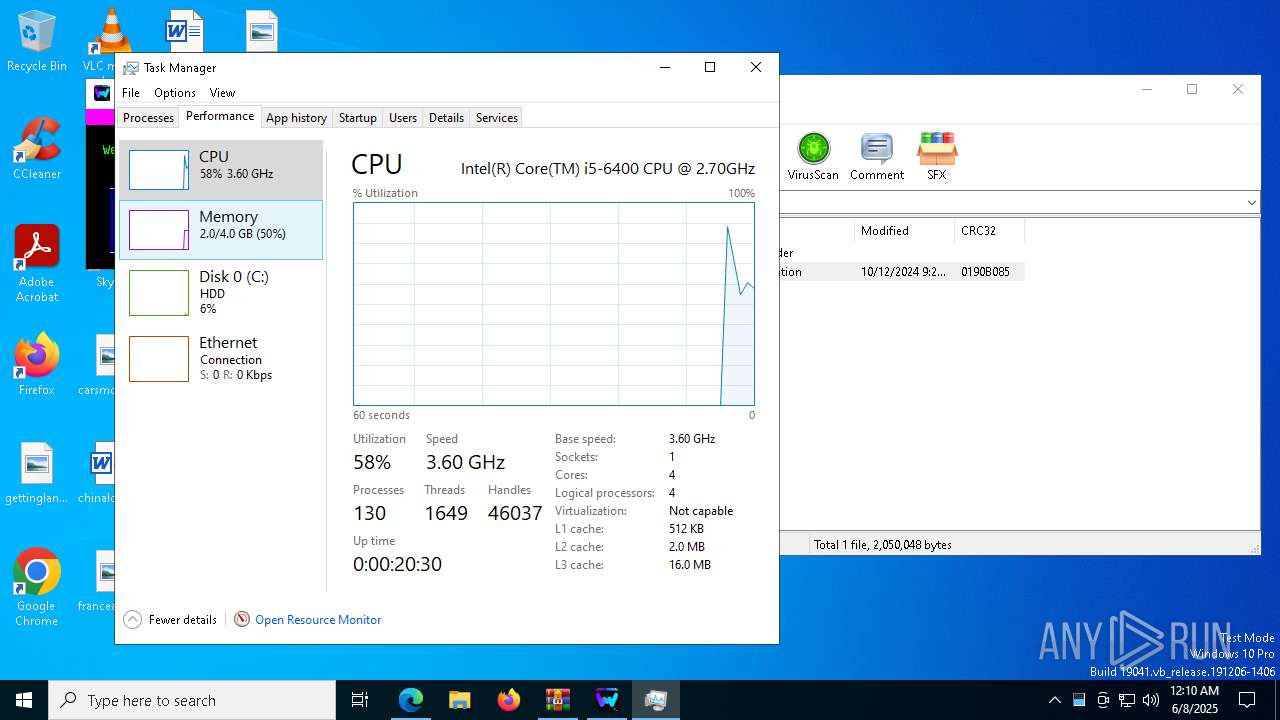
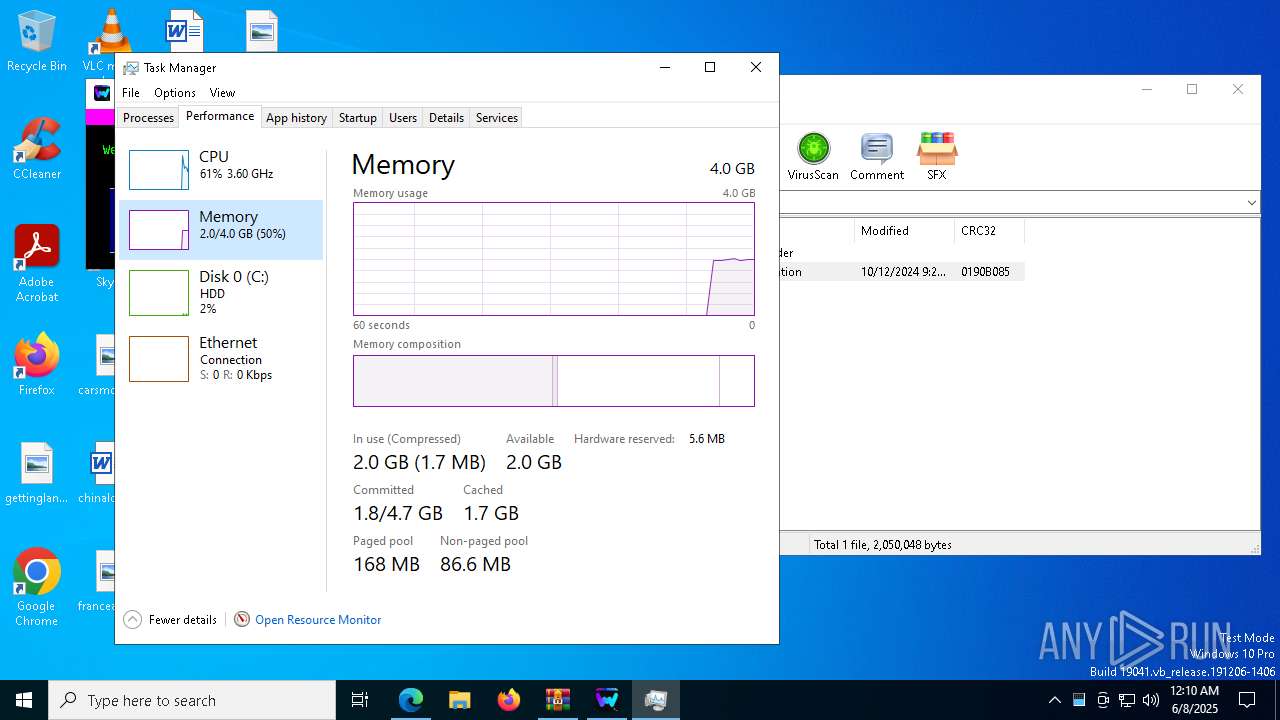
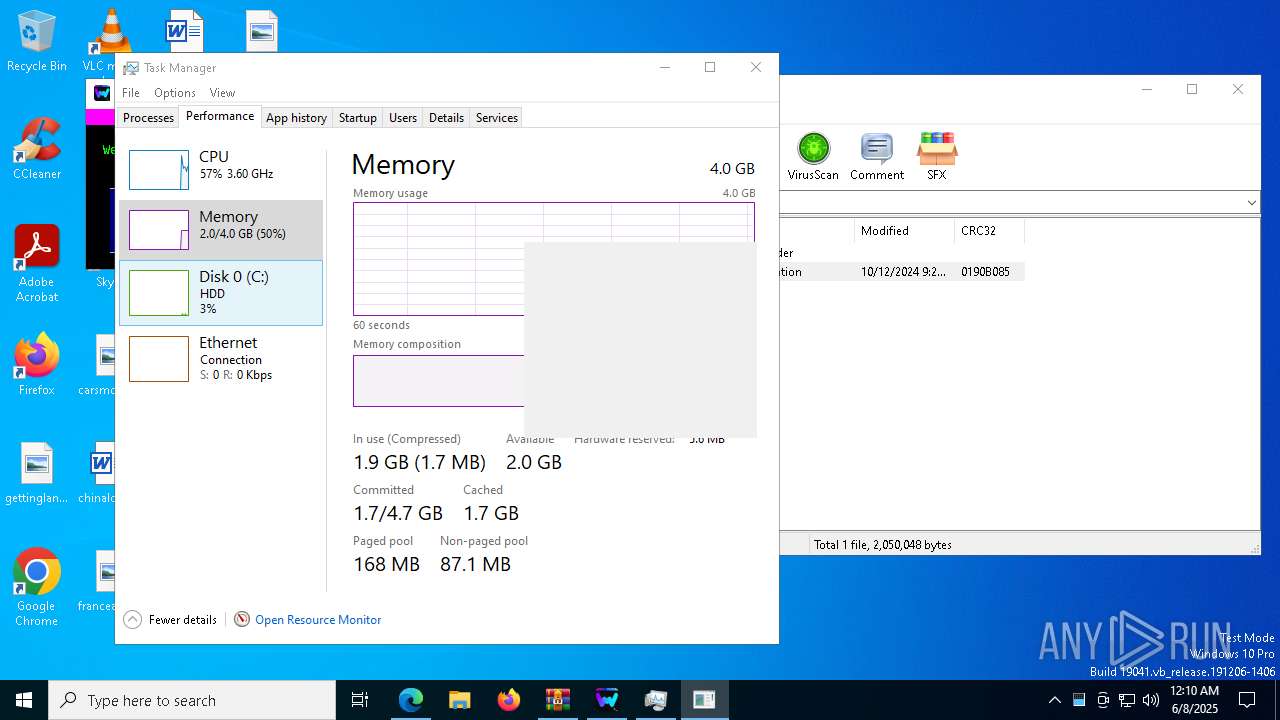
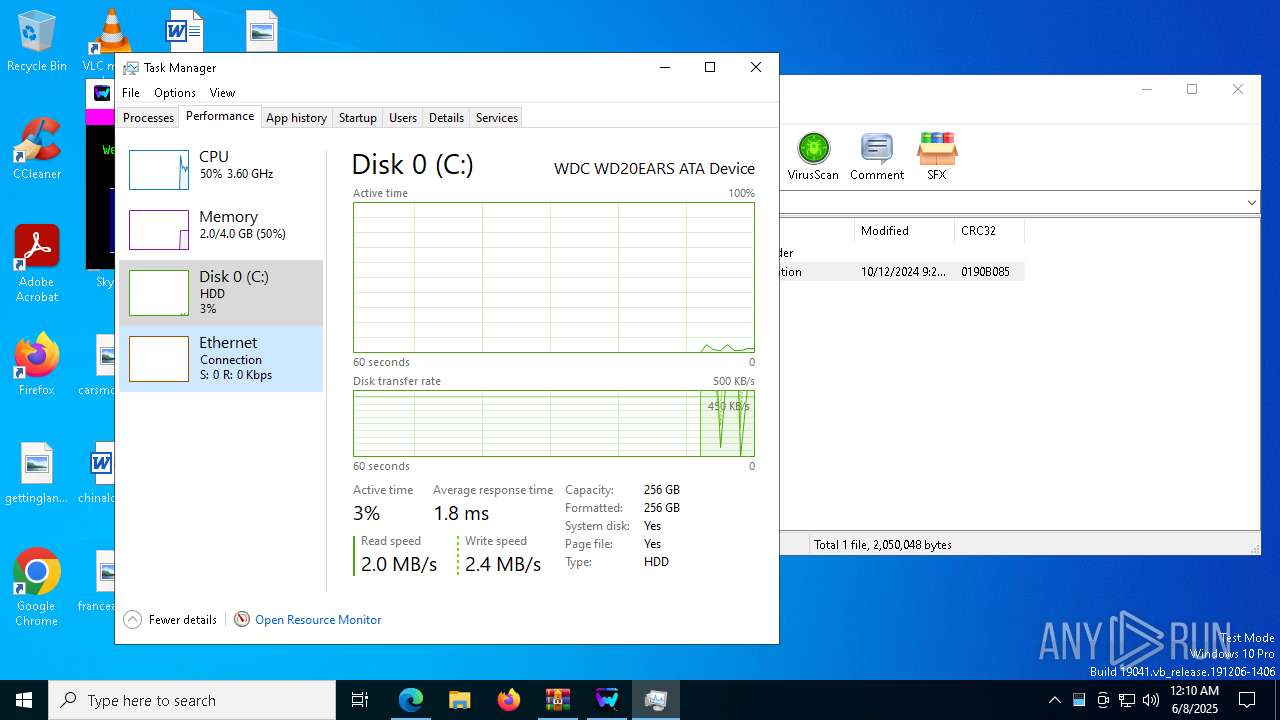
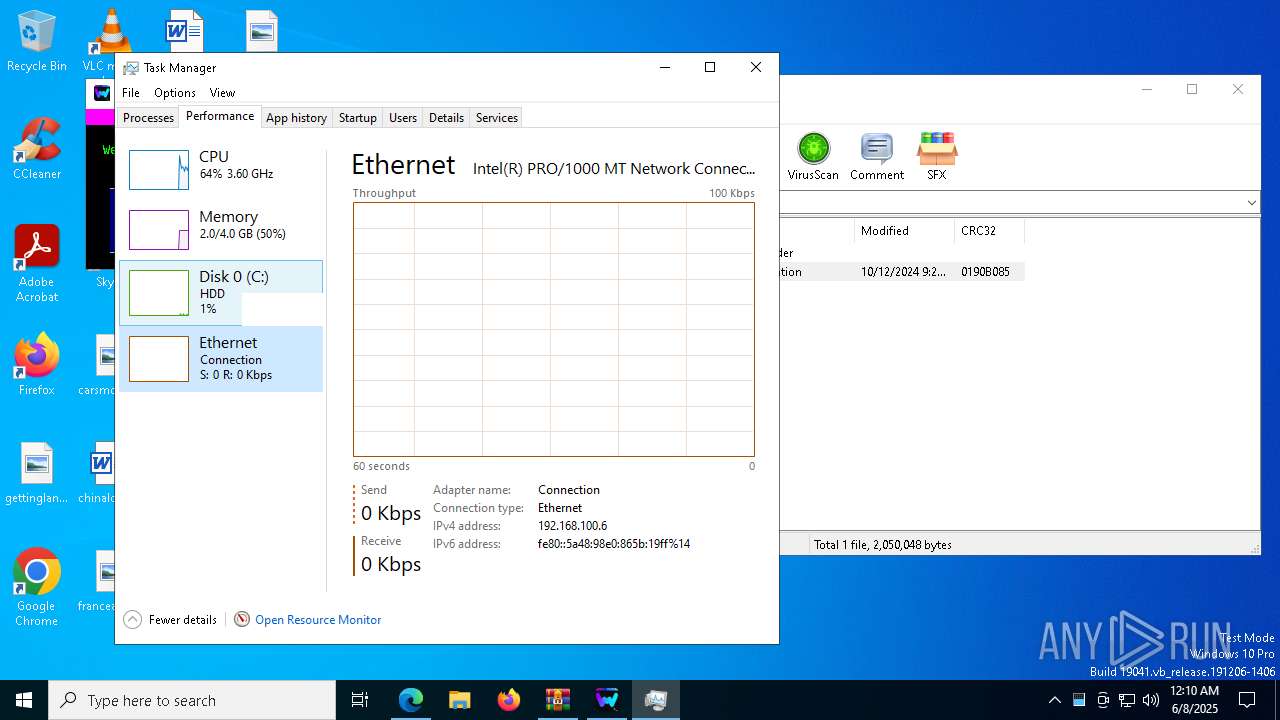
Manual execution by a user
- Taskmgr.exe (PID: 7128)
- Taskmgr.exe (PID: 5324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
247
Monitored processes
111
Malicious processes
2
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | powershell -Command "[console]::title='WeModPatcher'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | powershell -Command "[string]([Version]'1.2.5', [Version]'1.2.5' | measure-object -maximum).maximum" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | mshta.exe "C:\Users\admin\AppData\Local\Temp\Rar$EXa8100.18601\Launcher.hta" | C:\Windows\System32\mshta.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 3221225477 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | mshta.exe "C:\Users\admin\AppData\Local\Temp\Rar$EXa8100.18601\Launcher.hta" | C:\Windows\System32\mshta.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 3221225477 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | C:\WINDOWS\system32\cmd.exe /c tasklist /NH /FI "WindowTitle eq "WeModPatcher"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | C:\WINDOWS\system32\cmd.exe /c chcp | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "(Get-FileHash Options.ini -Algorithm MD5).Hash" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4784 --field-trial-handle=2220,i,6553060065748106808,1848397093774432231,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "Add-Type -AssemblyName System.Windows.Forms;([System.Windows.Forms.Screen]::AllScreens).WorkingArea.Width" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | powershell -Command "(Get-FileHash Options.ini -Algorithm MD5).Hash" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
94 725
Read events
94 679
Write events
45
Delete events
1
Modification events
| (PID) Process: | (6940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6940) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EBD1B98E9A952F00 | |||
| (PID) Process: | (6940) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 161BBF8E9A952F00 | |||
| (PID) Process: | (6940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328570 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6F639E2B-A12A-4892-A0BF-CEF057E2302E} | |||
| (PID) Process: | (6940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328570 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3C47DDE8-4F4D-42DF-93AB-F3CEEFBE2B99} | |||
| (PID) Process: | (6940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328570 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {90B8B1D0-92DB-4D00-B383-4004CE636C58} | |||
| (PID) Process: | (6940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328570 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4FBCE29C-24FF-4E8E-9103-8051C7CEBE8C} | |||
Executable files
7
Suspicious files
311
Text files
70
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11f7bb.TMP | — | |
MD5:— | SHA256:— | |||
| 6940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f7ca.TMP | — | |
MD5:— | SHA256:— | |||
| 6940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF11f7ca.TMP | — | |
MD5:— | SHA256:— | |||
| 6940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RF11f7da.TMP | — | |
MD5:— | SHA256:— | |||
| 6940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF11f7f9.TMP | — | |
MD5:— | SHA256:— | |||
| 6940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11f7f9.TMP | — | |
MD5:— | SHA256:— | |||
| 6940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
61
DNS requests
61
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7200 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7200 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
864 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
6108 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6108 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
6108 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6940 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6108 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |