analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
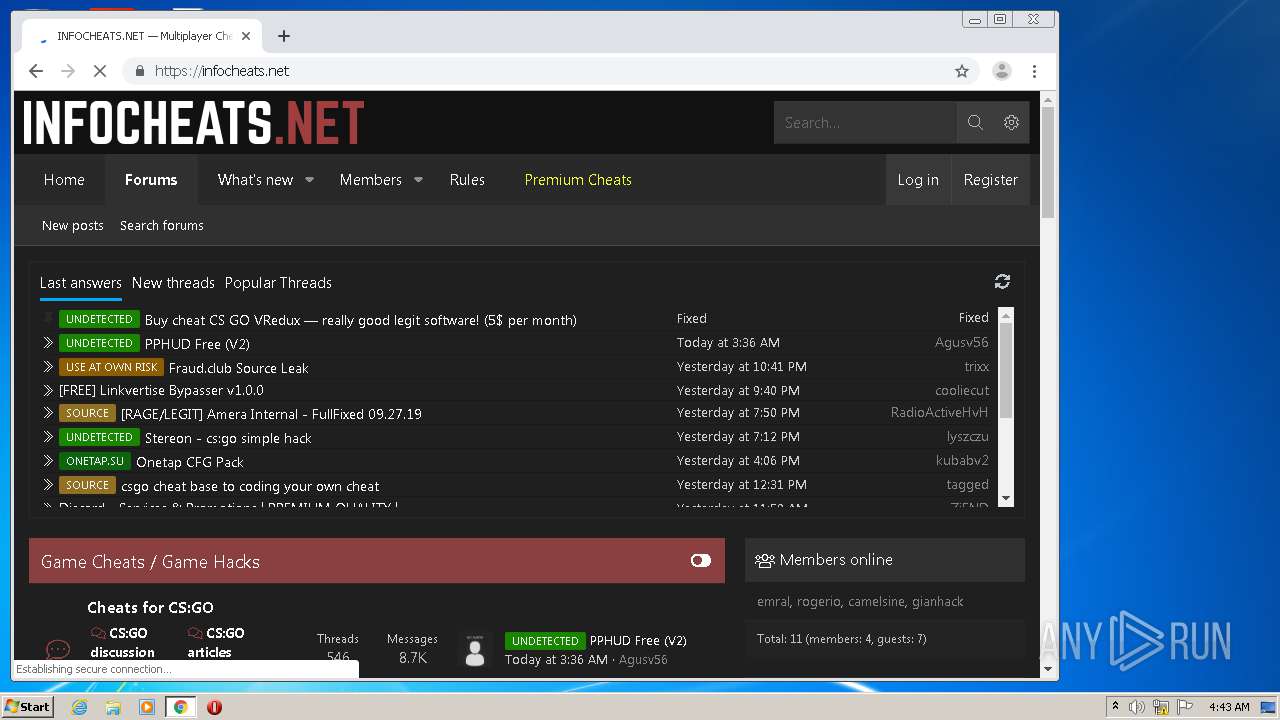
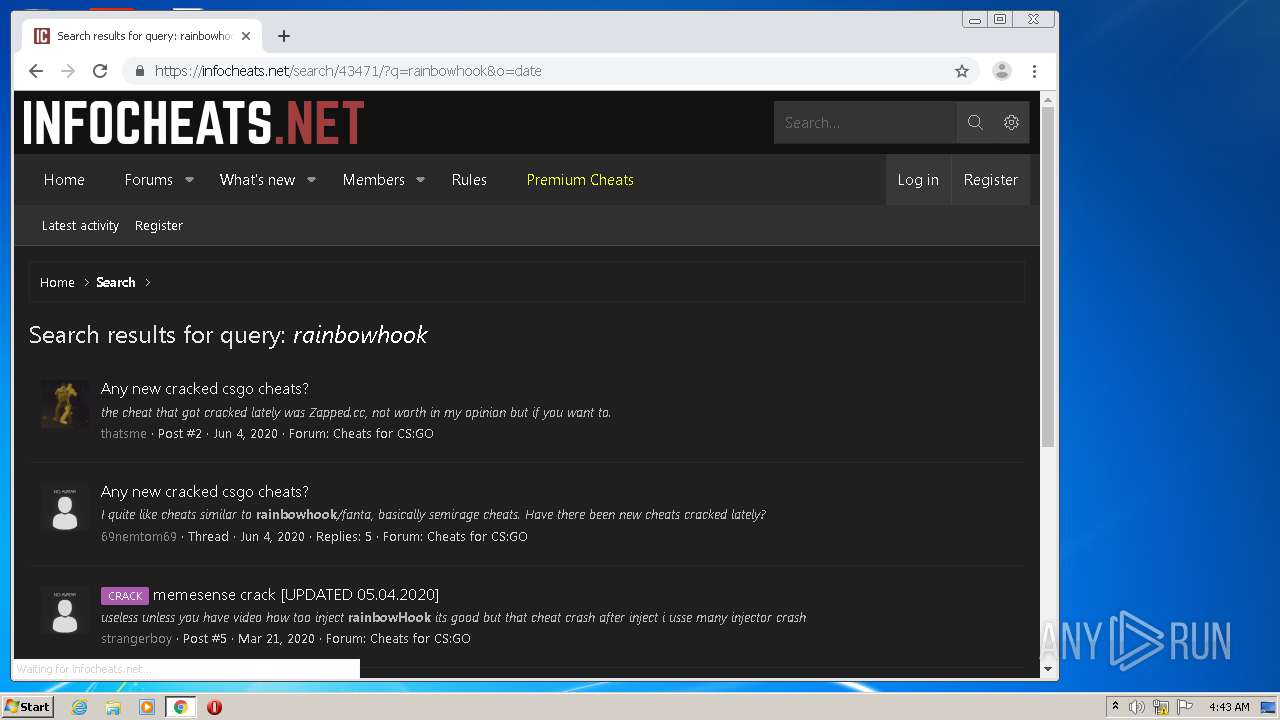
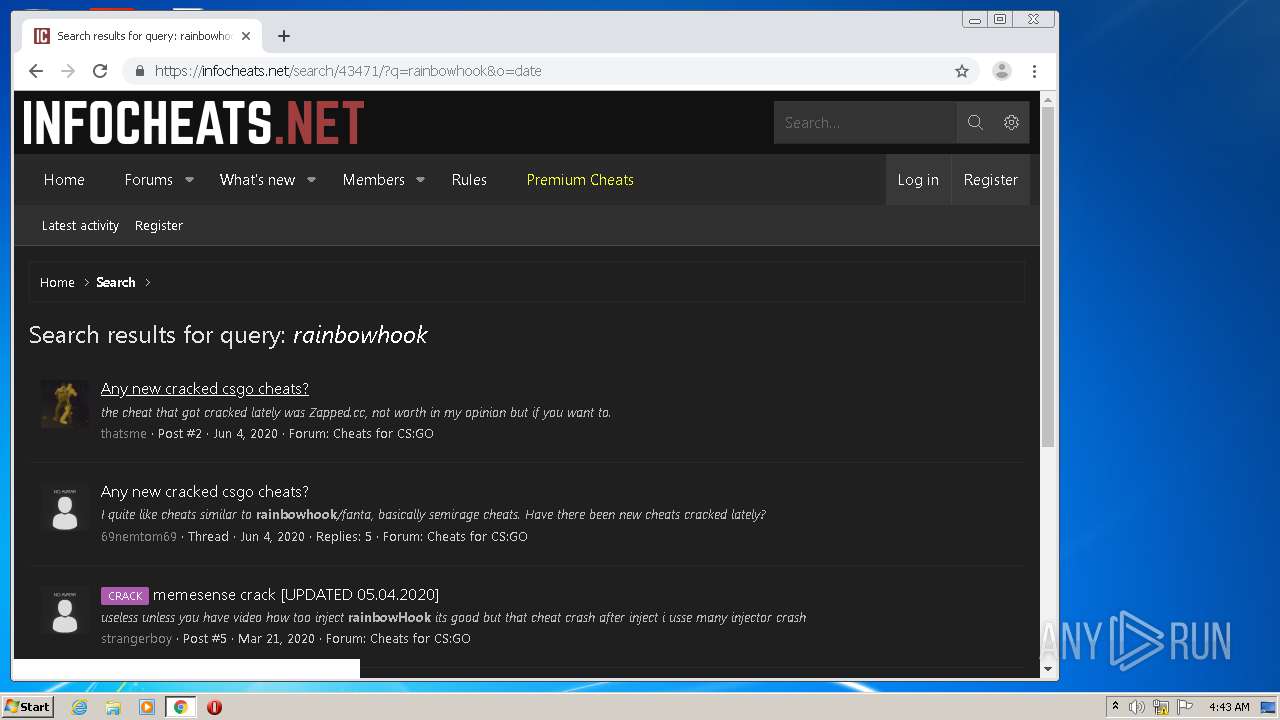
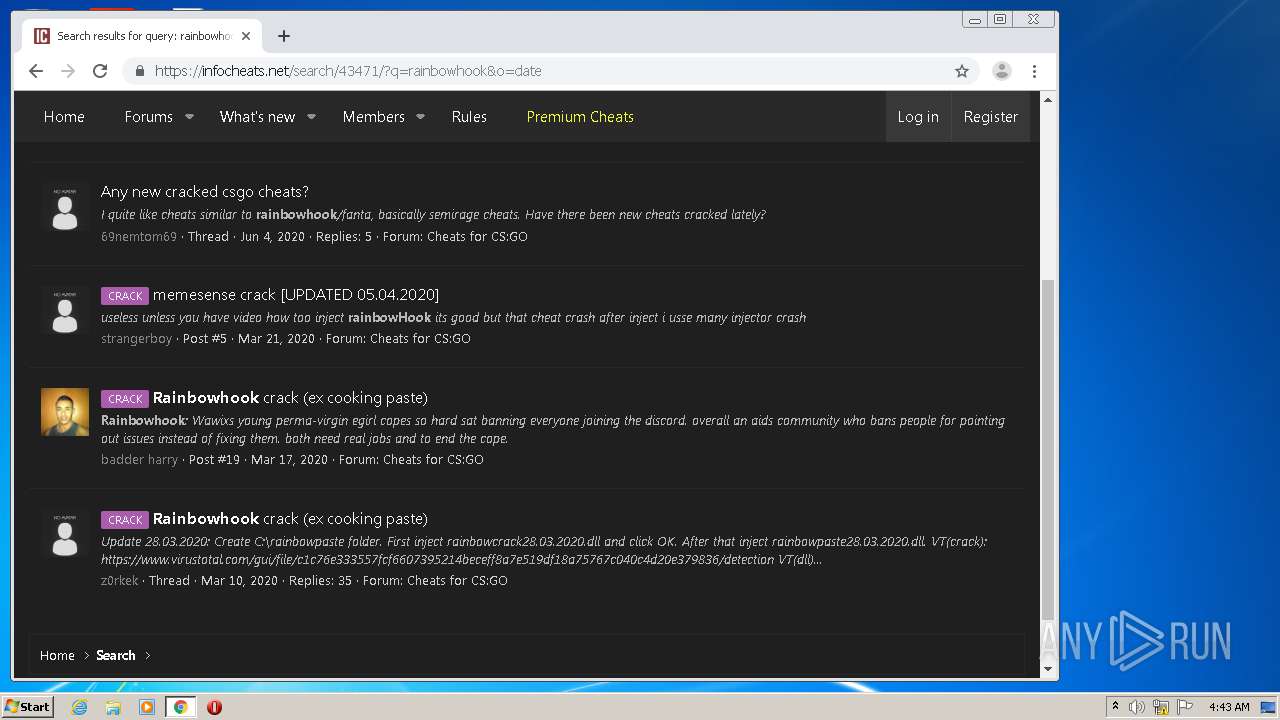
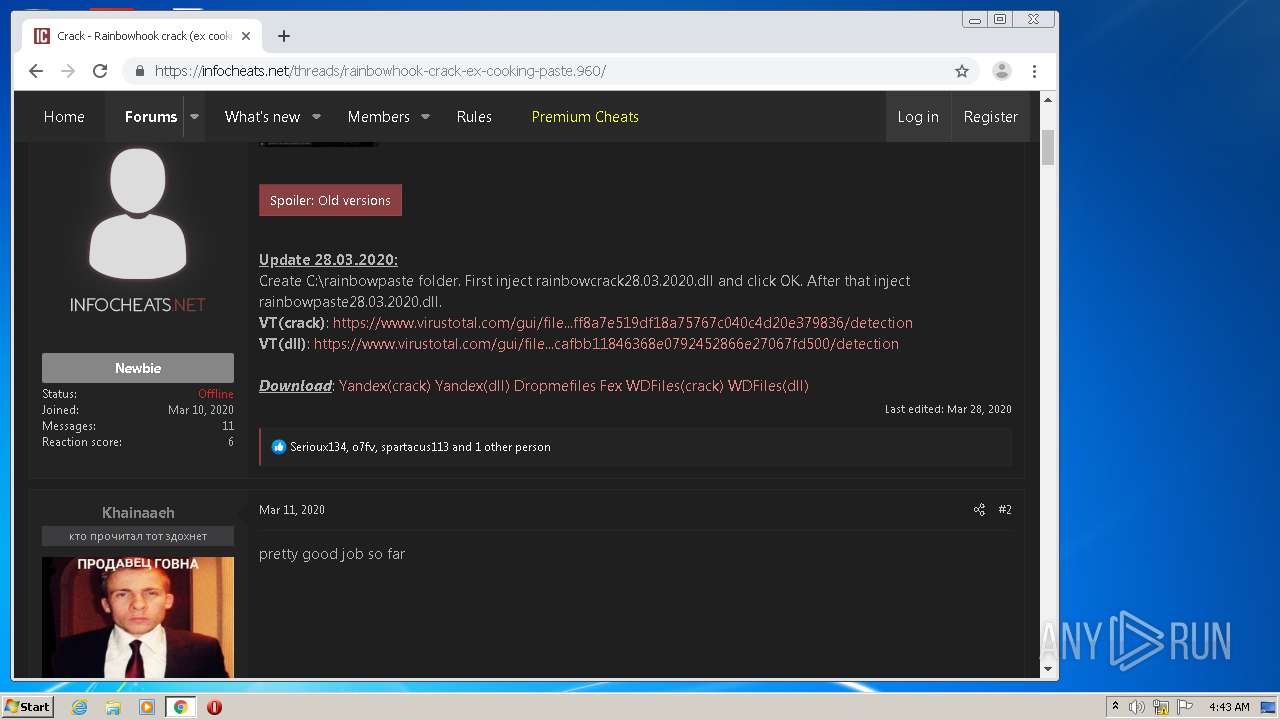
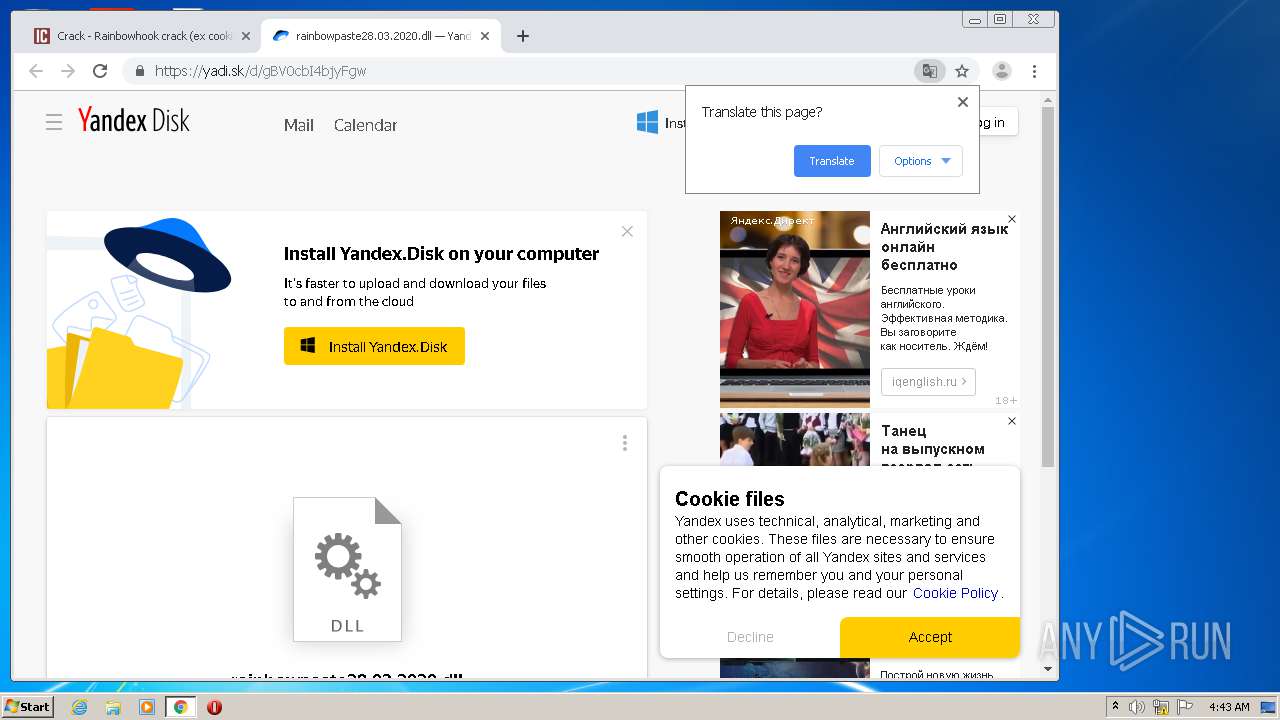
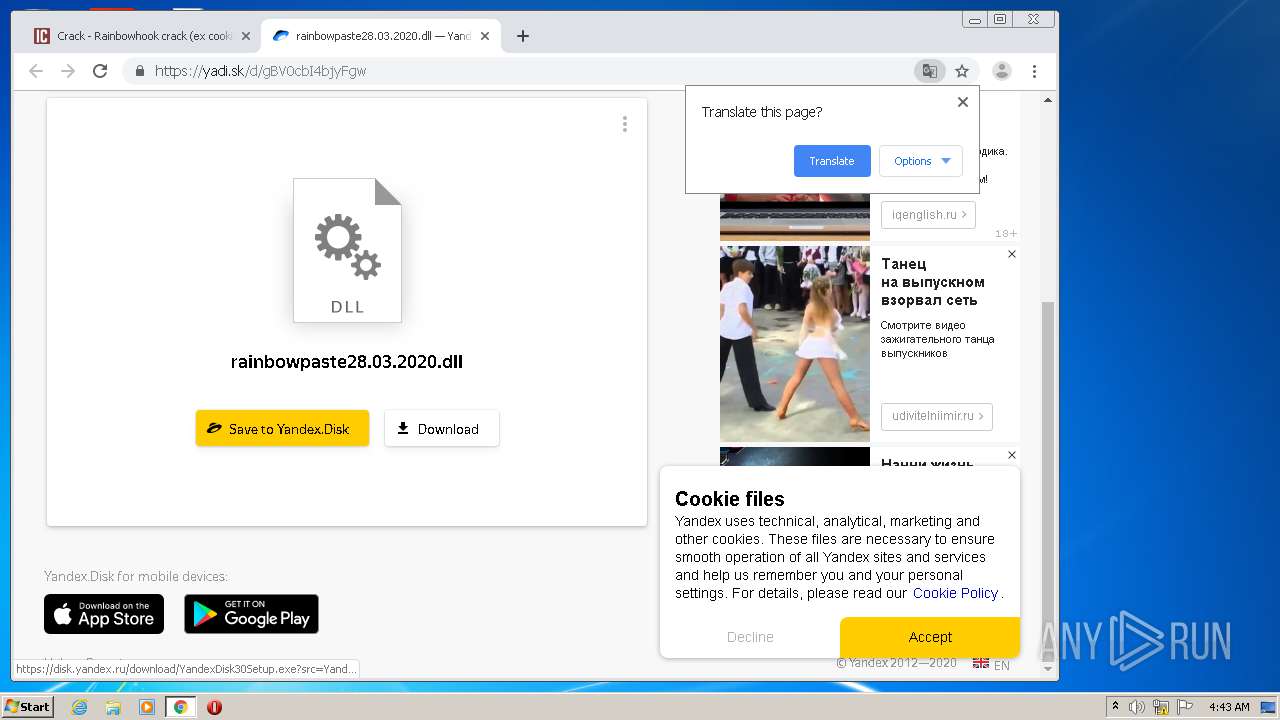
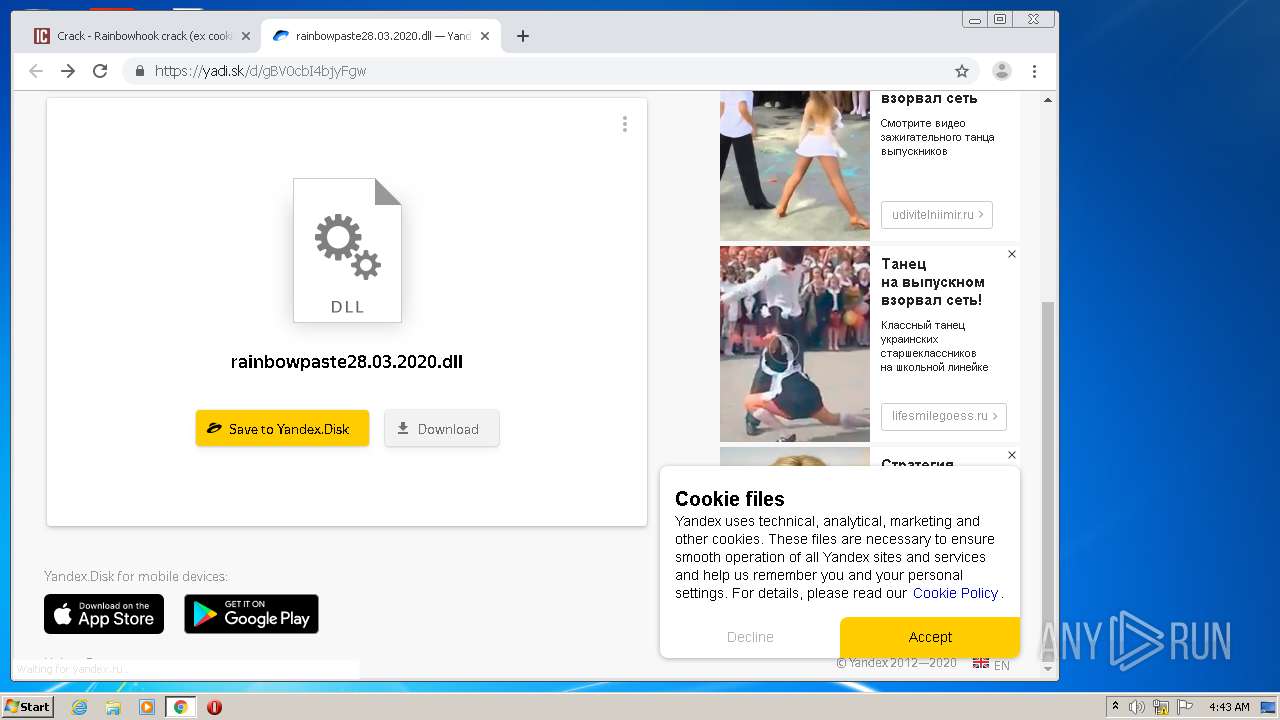
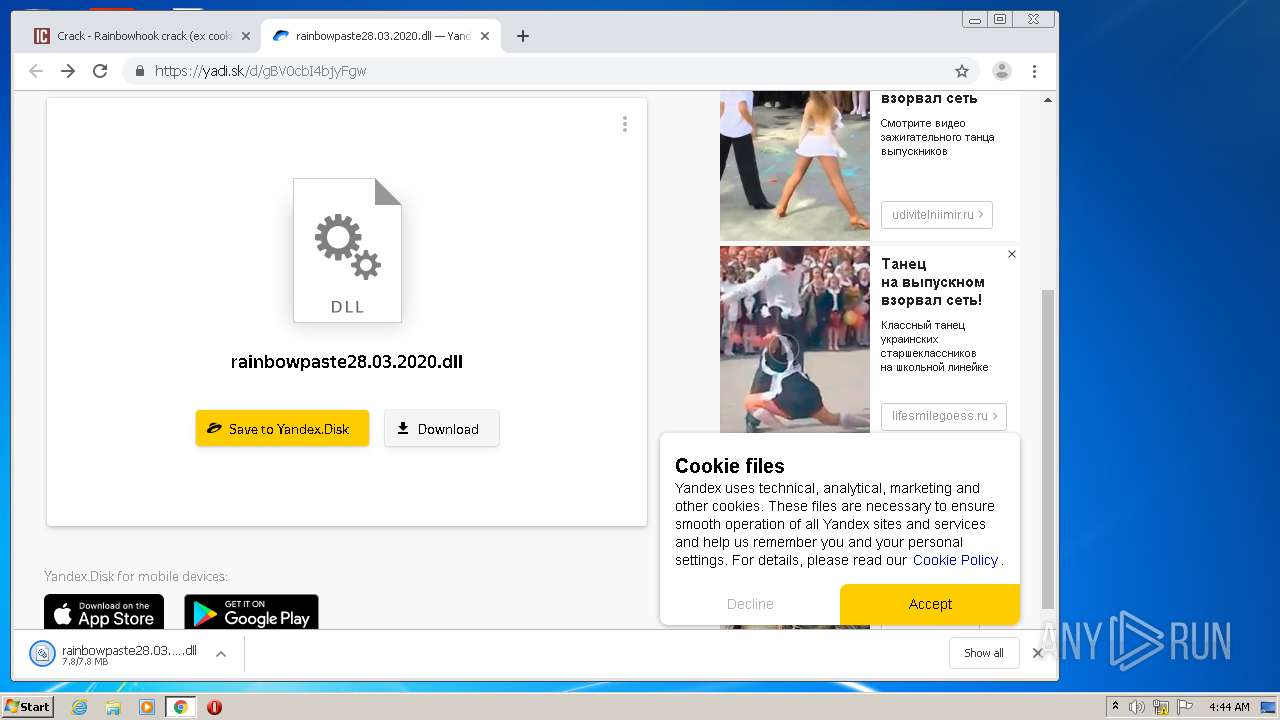
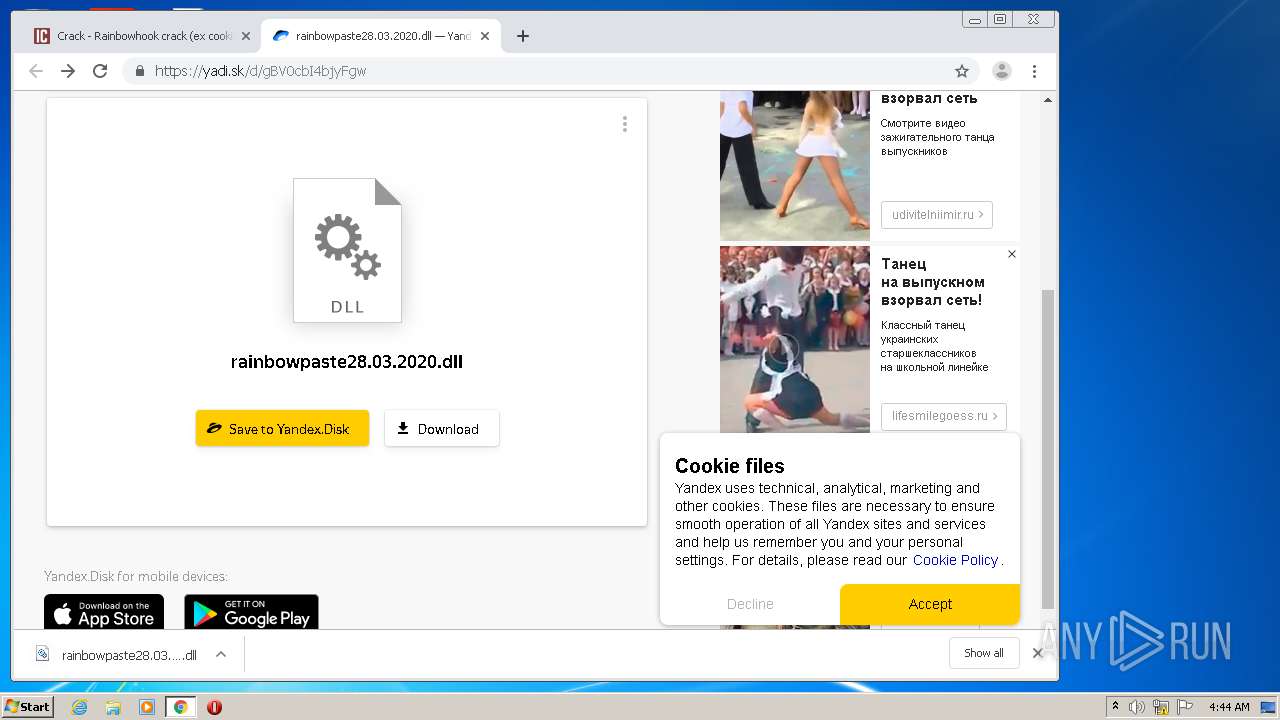
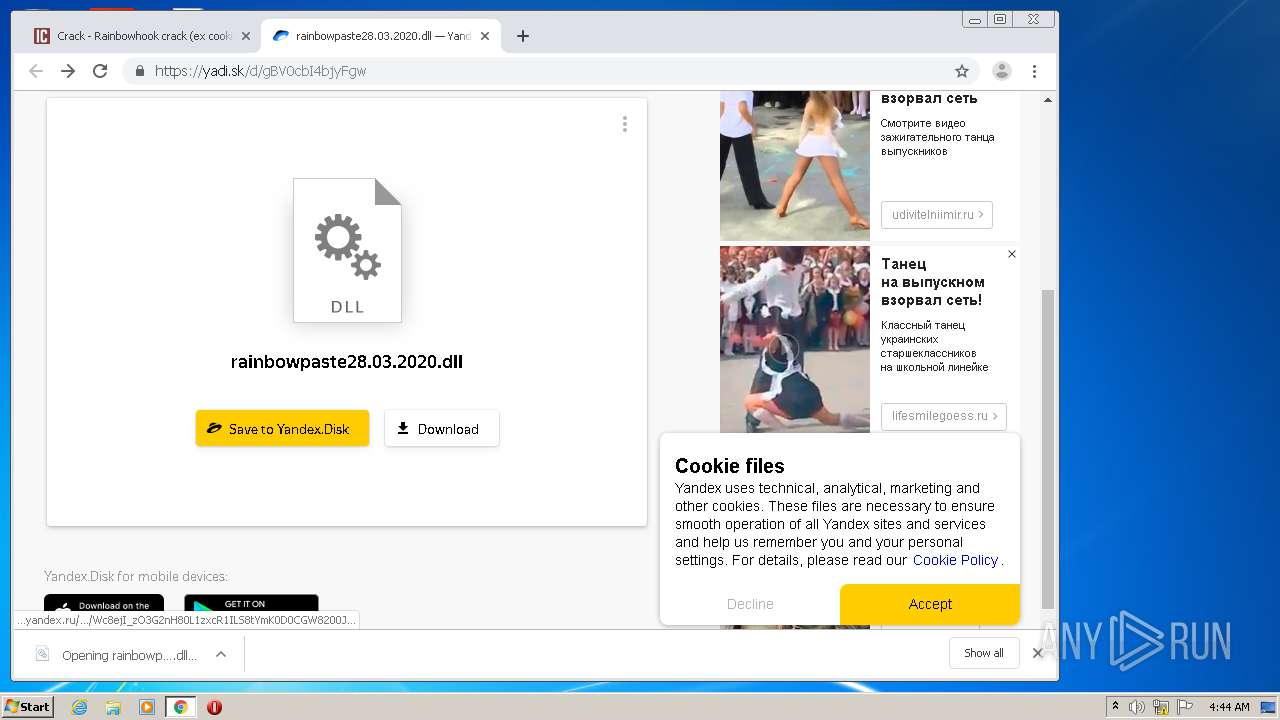
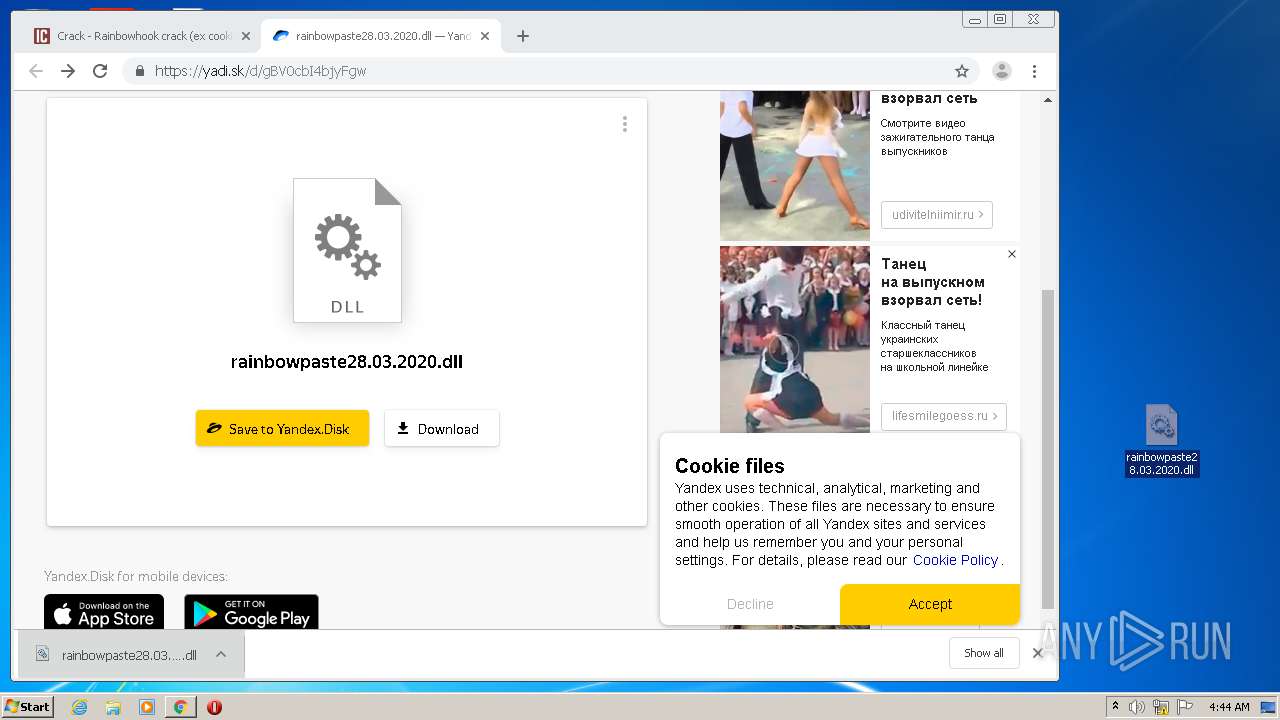
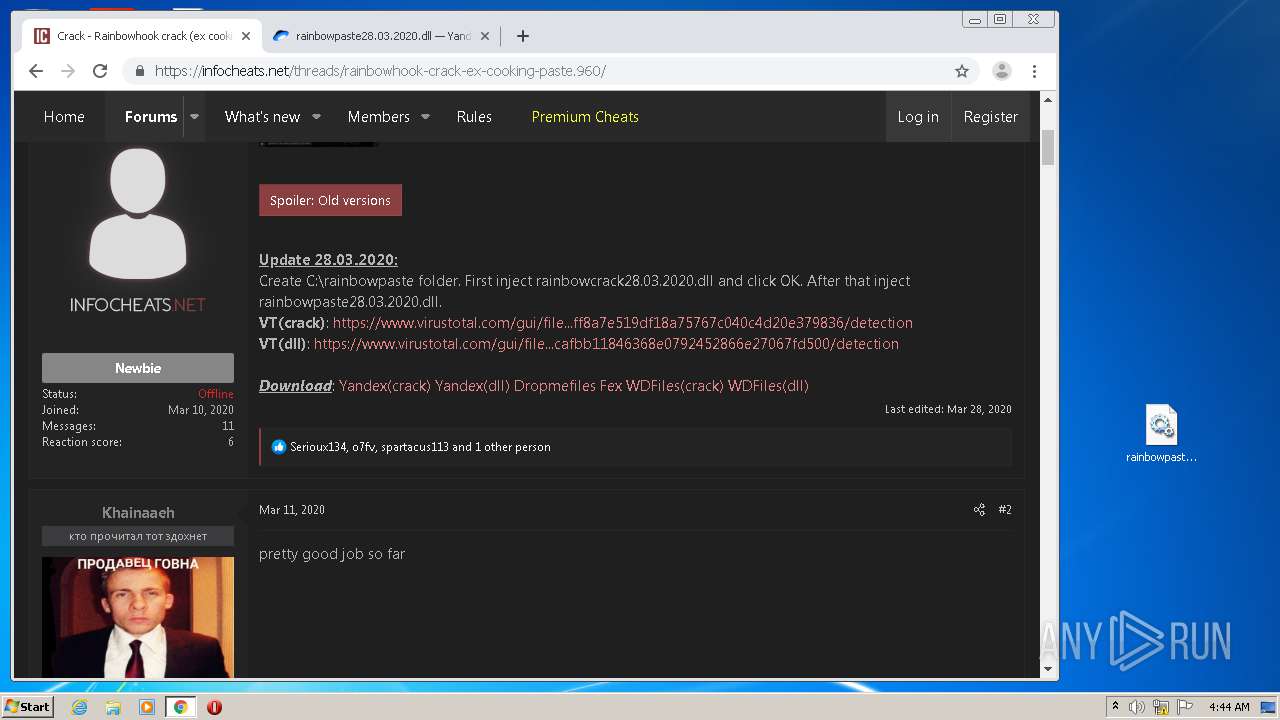
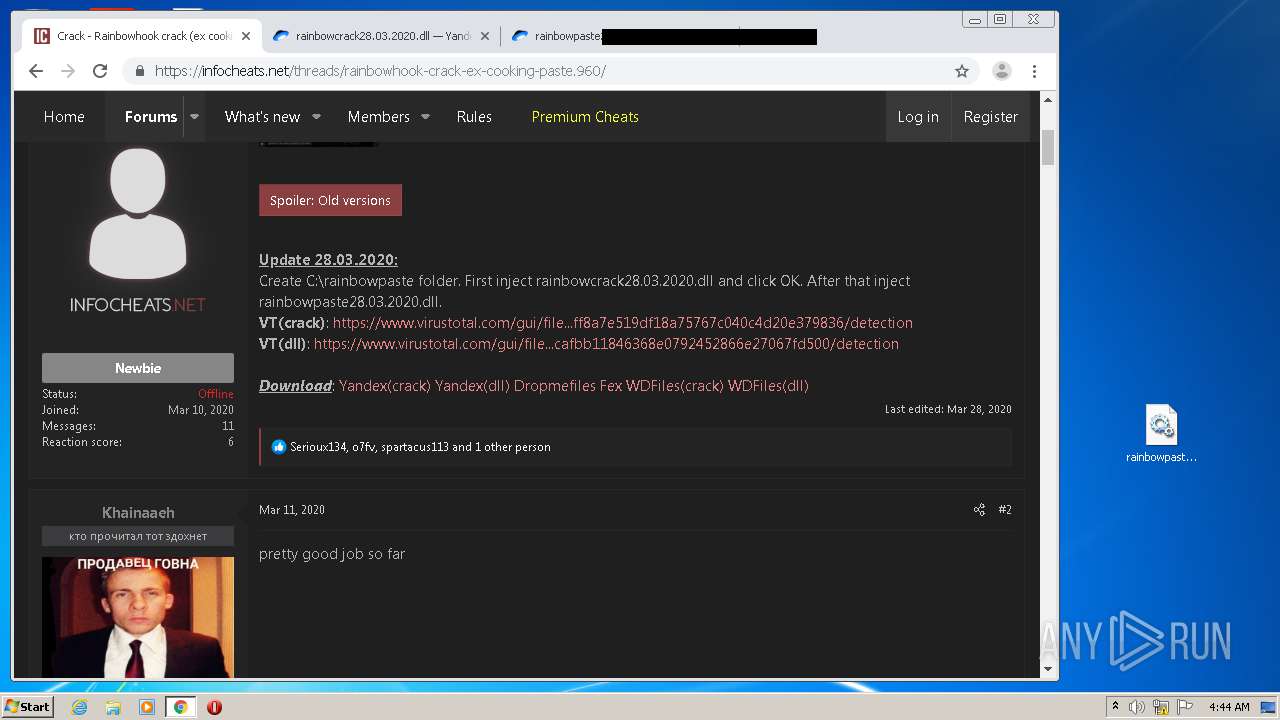
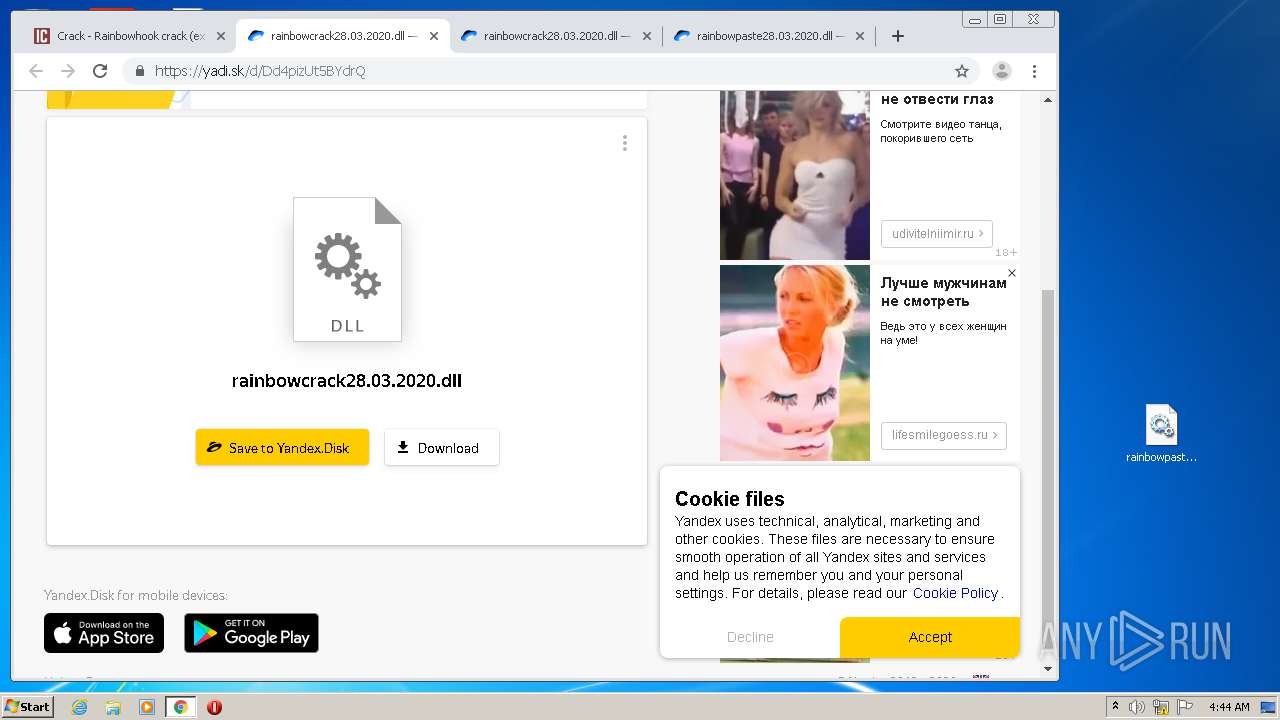
| download: | rainbowhook-crack-ex-cooking-paste.960 |
| Full analysis: | https://app.any.run/tasks/dad829a4-3ea1-4955-a8f1-f6a2e03fe591 |
| Verdict: | Malicious activity |
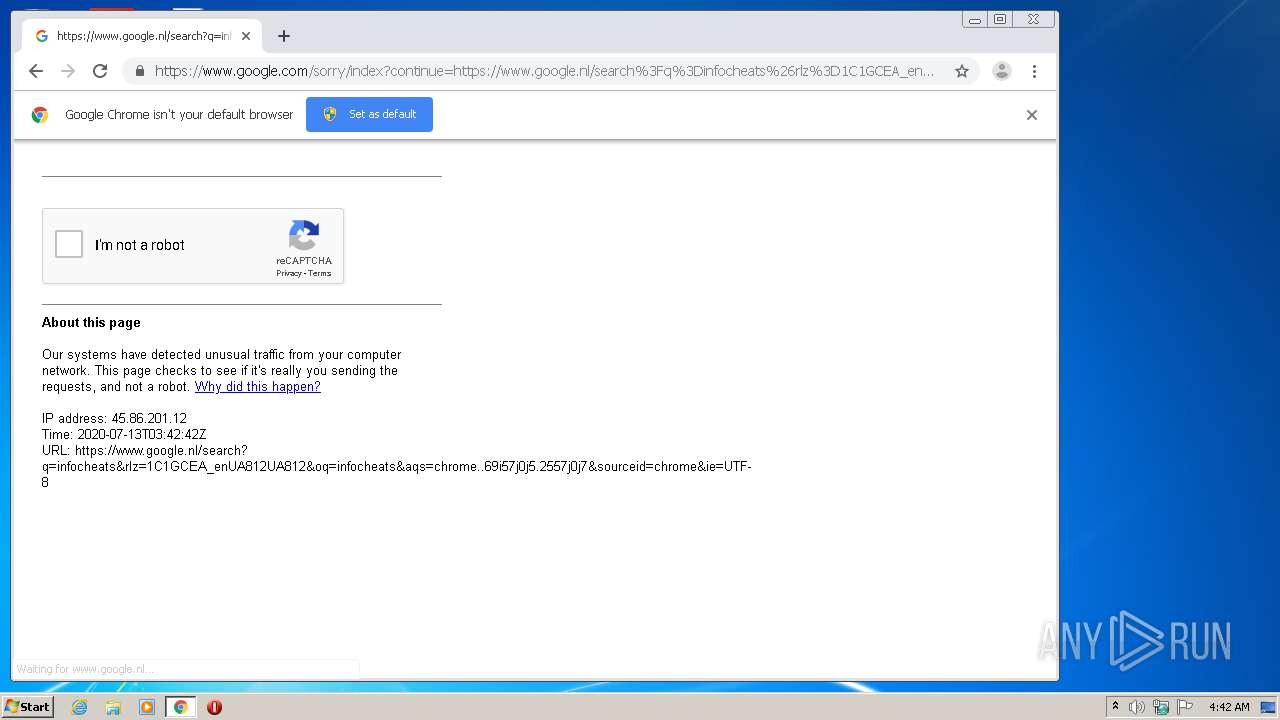
| Analysis date: | July 13, 2020, 03:42:08 |
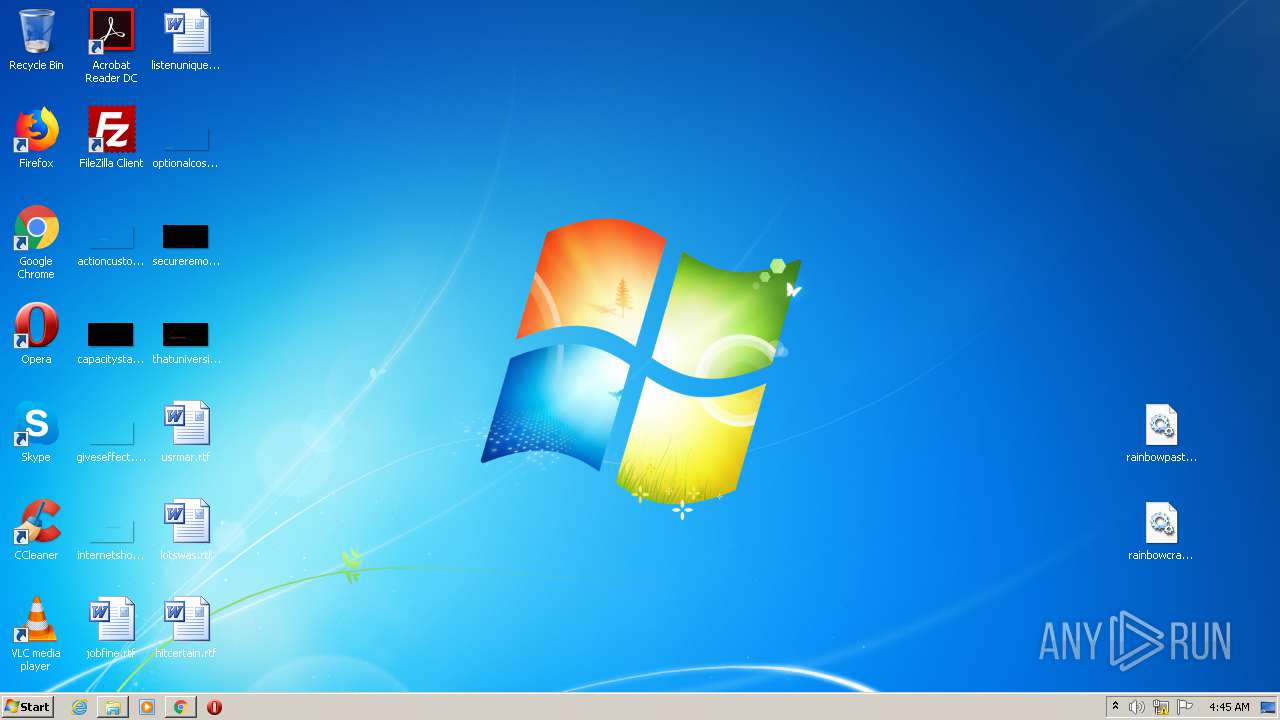
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with no line terminators |
| MD5: | 3F7CA7BB55A11E68B4336540F82046A7 |
| SHA1: | D4B2F4A9E995428A02095FA21038E4B2D66246BD |
| SHA256: | 4EE367935A10B7F4E7F97B6F7DCDBF822D99C4833907932F2E68FBB400E237EC |
| SSDEEP: | 12:kIqJmWHov6mIDQYvdrWwXVZQ34l3zxv/3C4XL03uFs5ClTJBJLYLPZ5d9OI:k3ToymIsYv5WuVLFxSWLHw09L0p9OI |
MALICIOUS
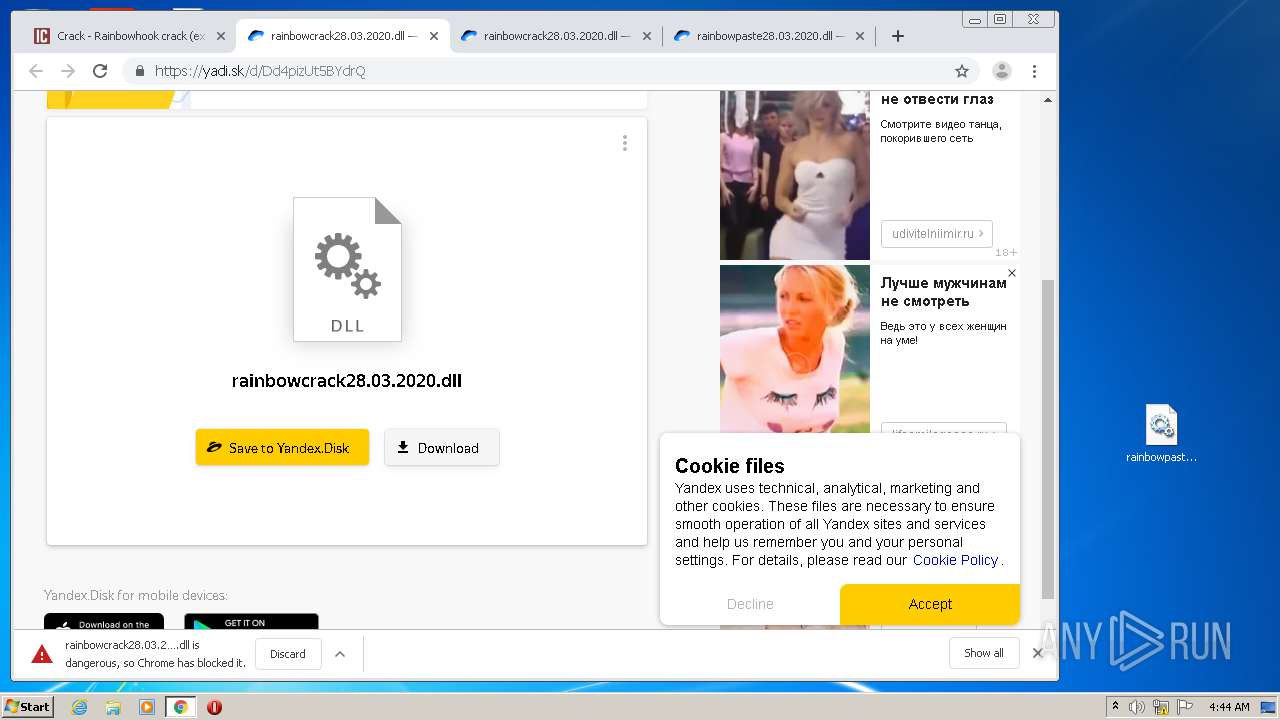
Loads dropped or rewritten executable
- explorer.exe (PID: 308)
- SearchProtocolHost.exe (PID: 4072)
SUSPICIOUS
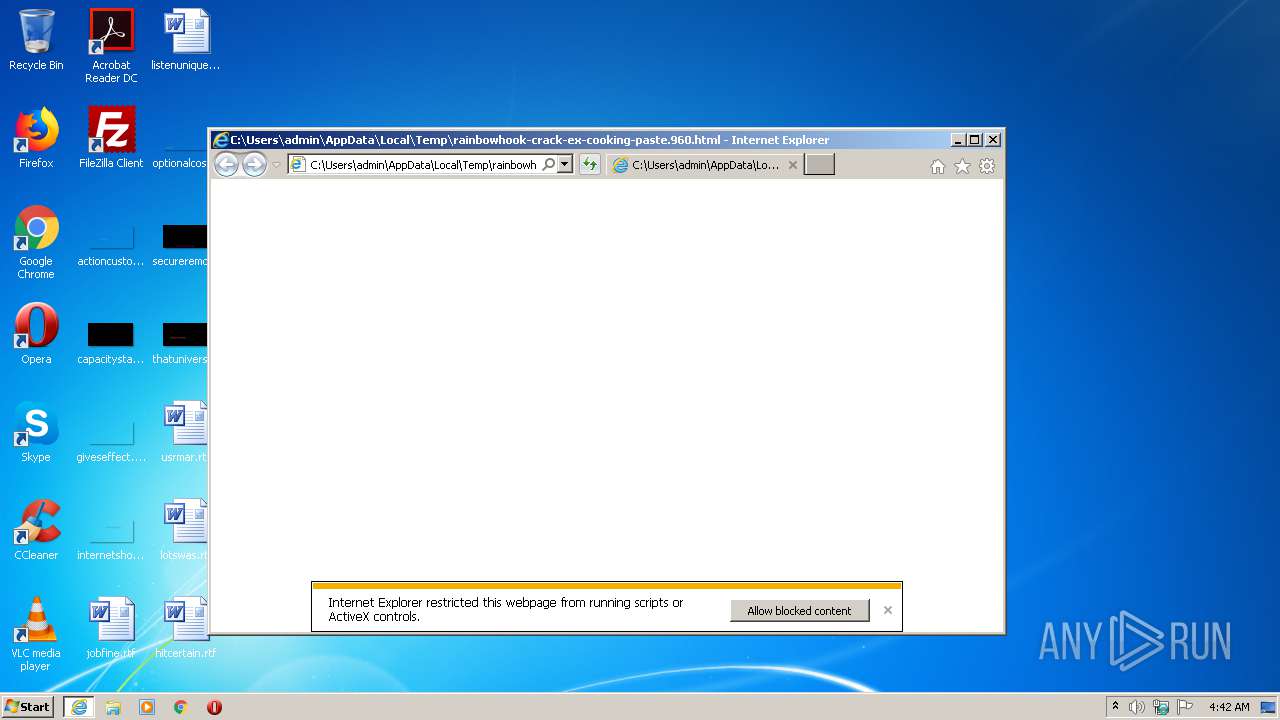
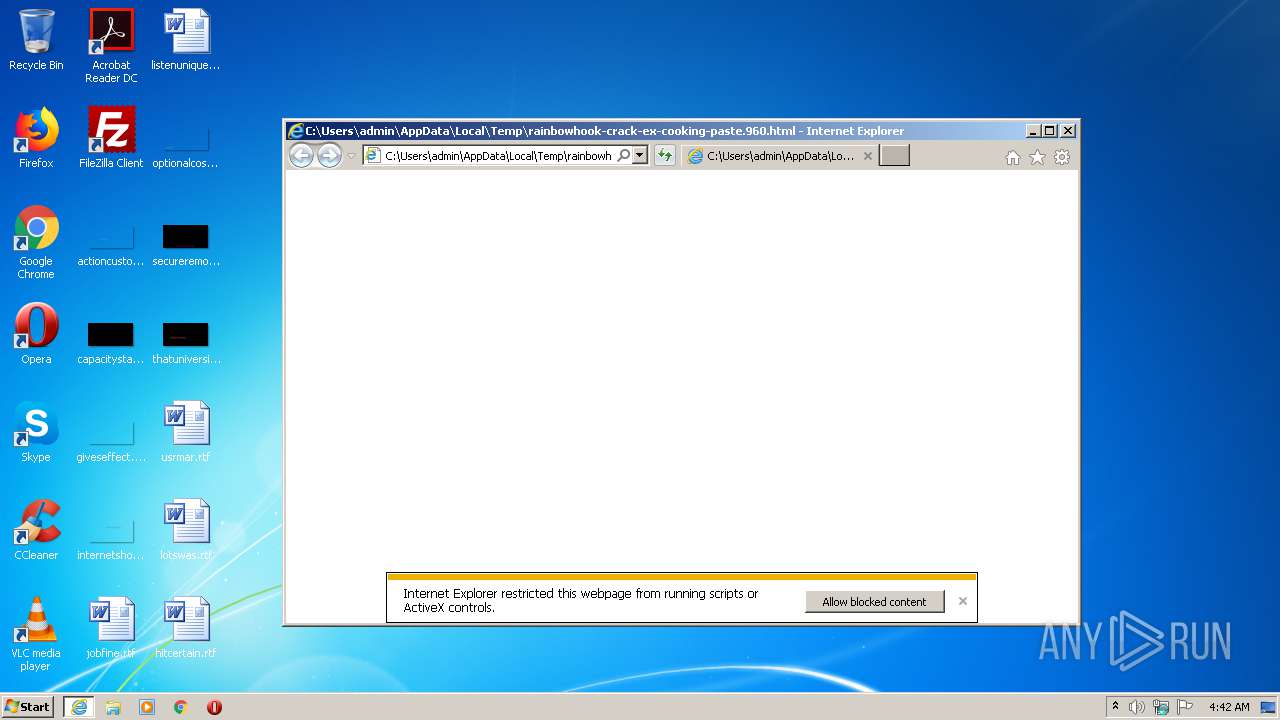
Starts Internet Explorer
- explorer.exe (PID: 308)
- rundll32.exe (PID: 3748)
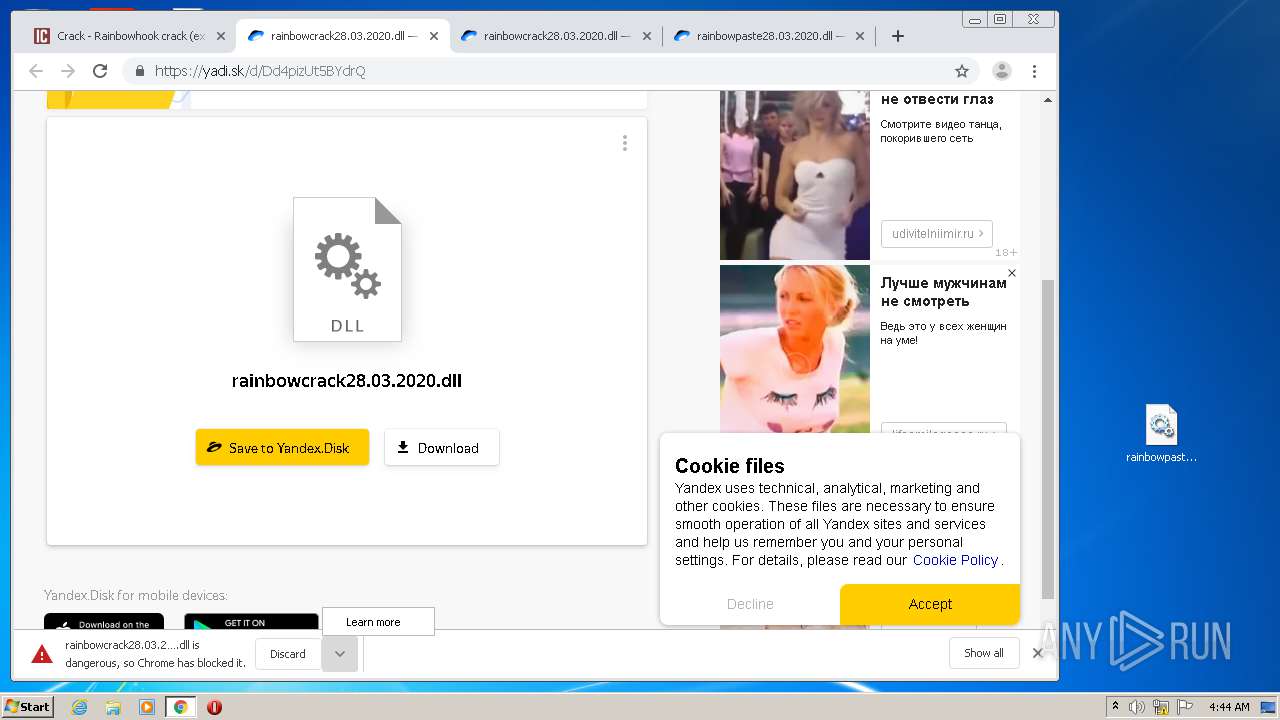
Executable content was dropped or overwritten
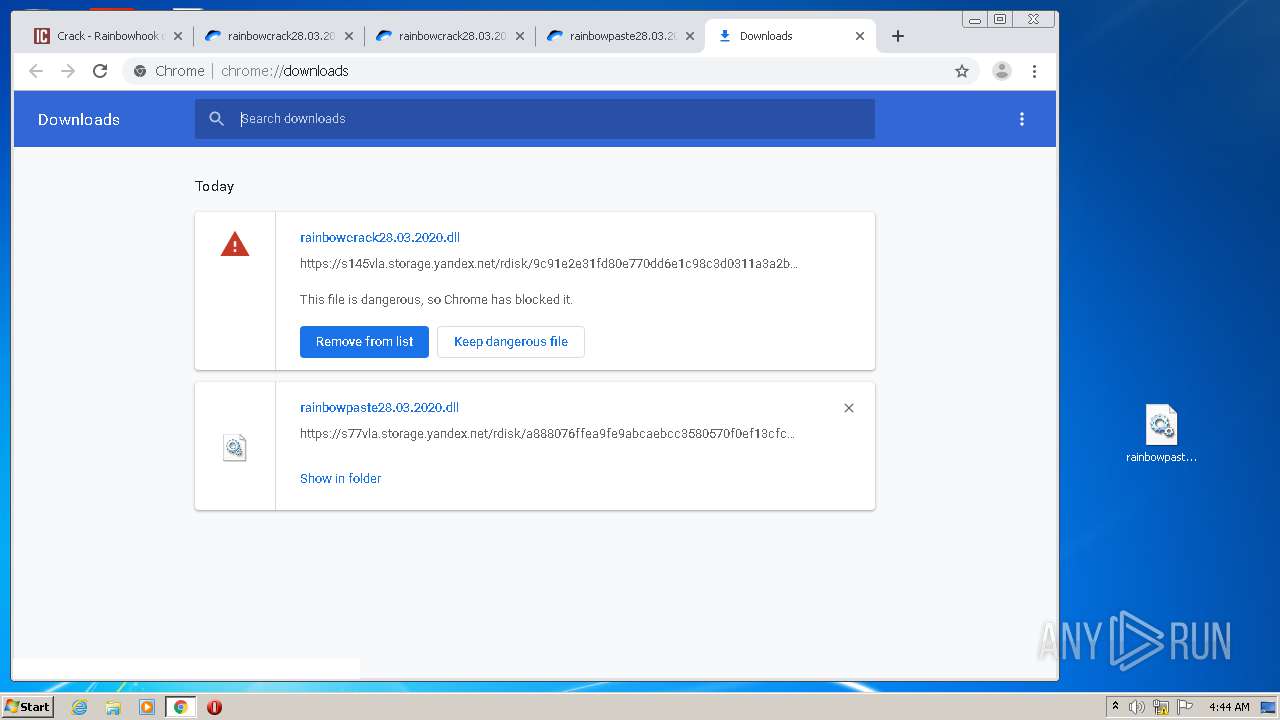
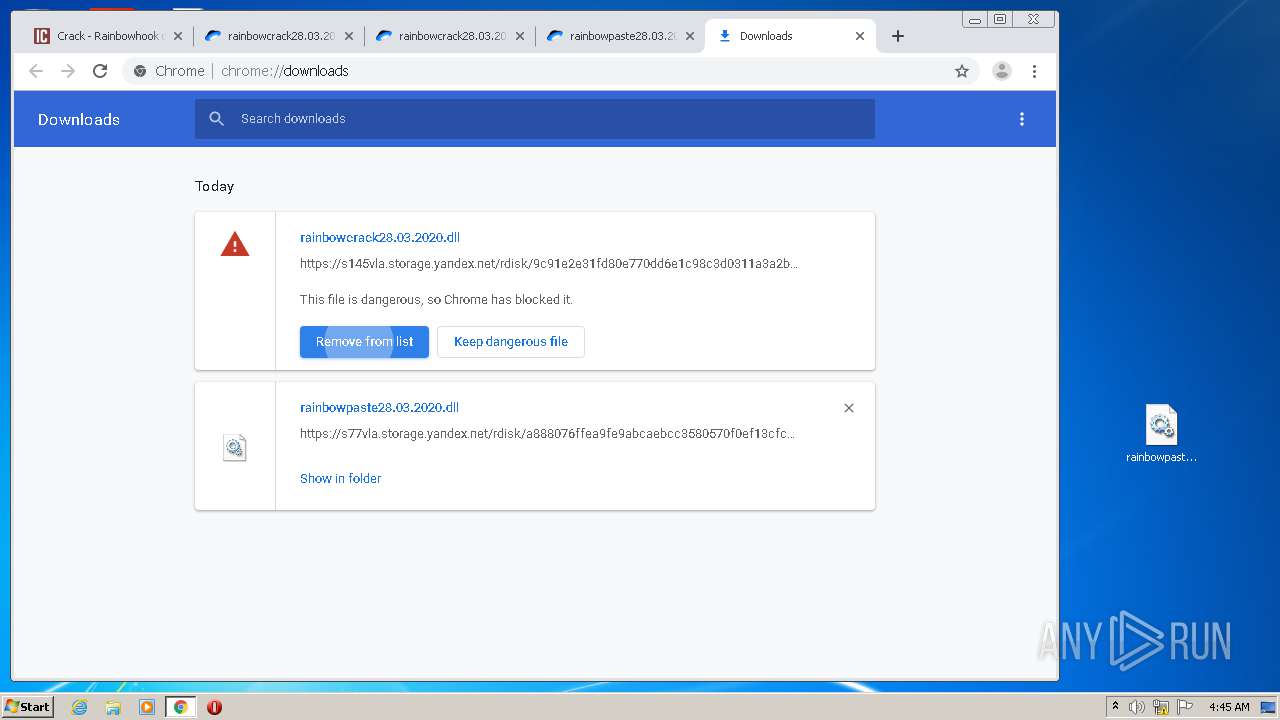
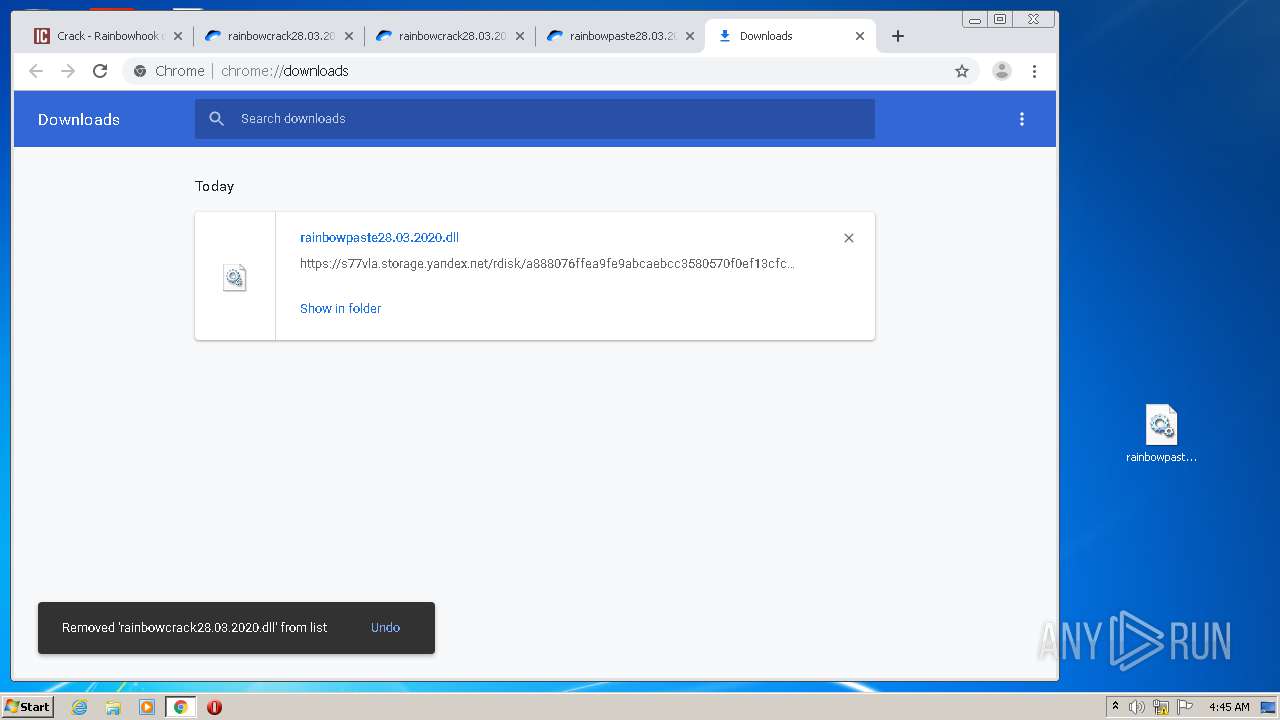
- chrome.exe (PID: 2816)
- chrome.exe (PID: 932)
- explorer.exe (PID: 308)
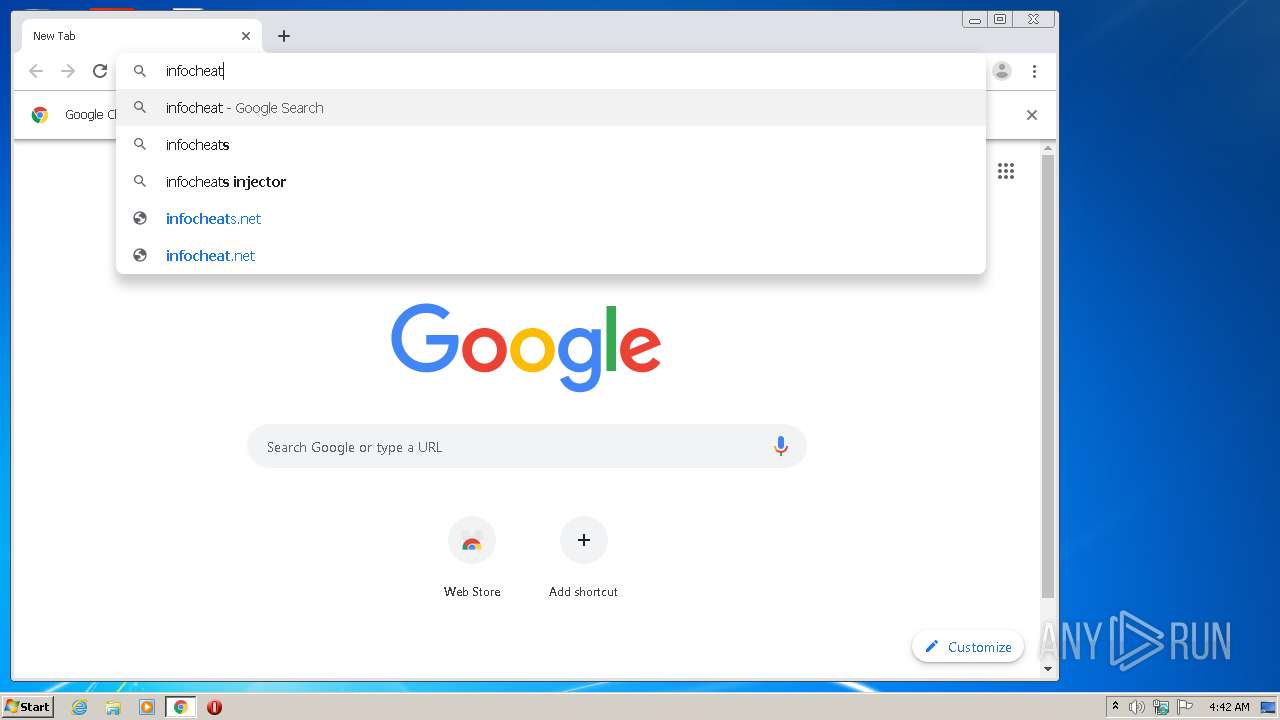
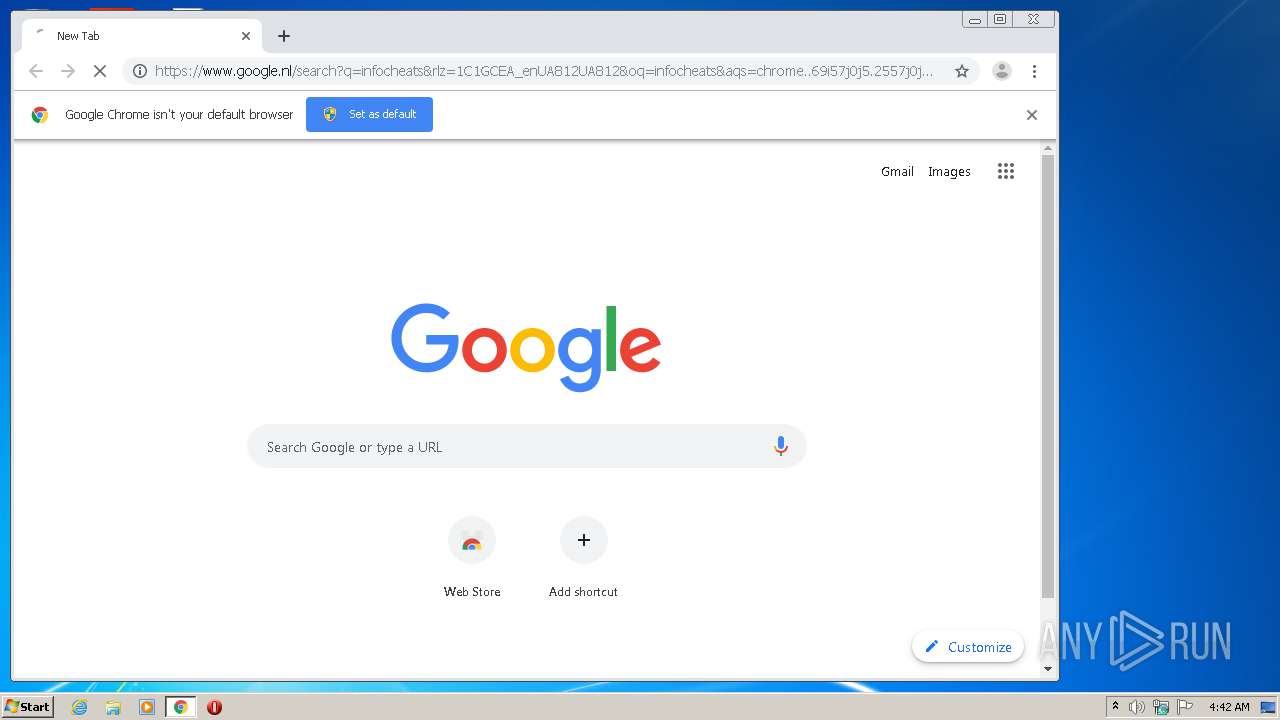
Modifies files in Chrome extension folder
- chrome.exe (PID: 2816)
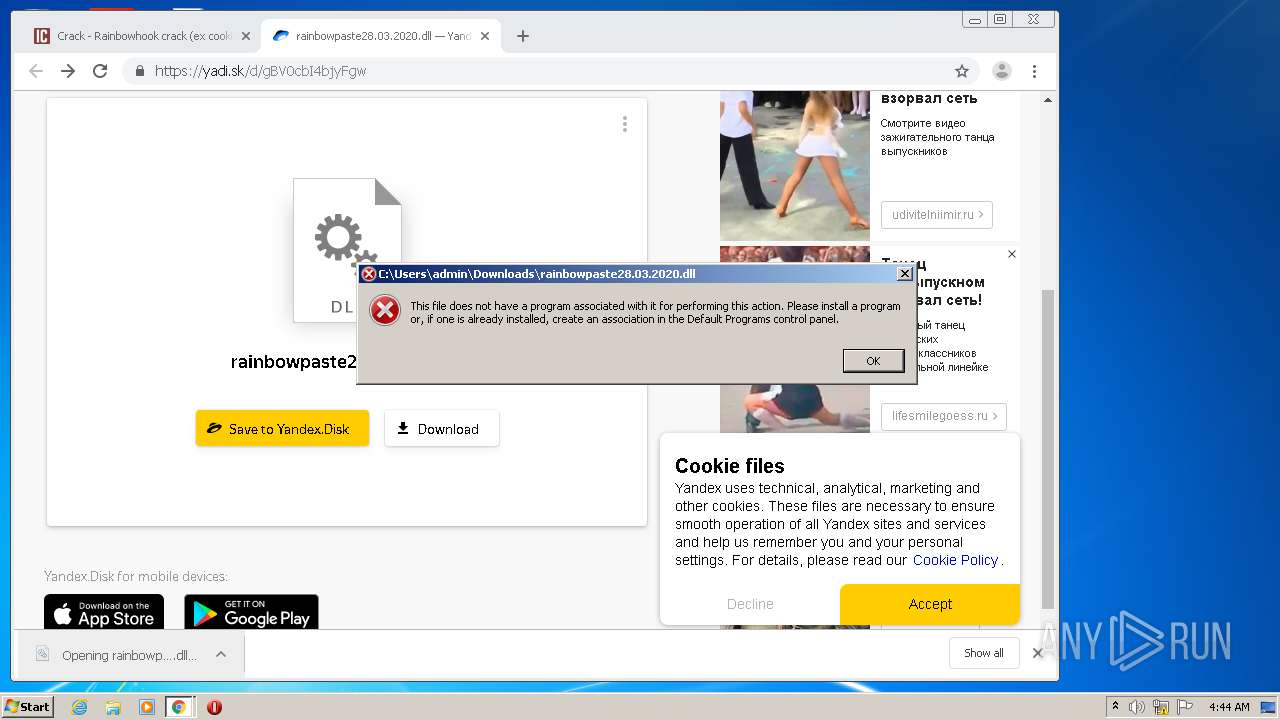
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 308)
INFO
Application launched itself
- iexplore.exe (PID: 1704)
- iexplore.exe (PID: 980)
- chrome.exe (PID: 2816)
Reads Internet Cache Settings
- iexplore.exe (PID: 1704)
- iexplore.exe (PID: 3720)
- chrome.exe (PID: 2816)
- iexplore.exe (PID: 868)
- iexplore.exe (PID: 2604)
Changes internet zones settings
- iexplore.exe (PID: 1704)
- iexplore.exe (PID: 868)
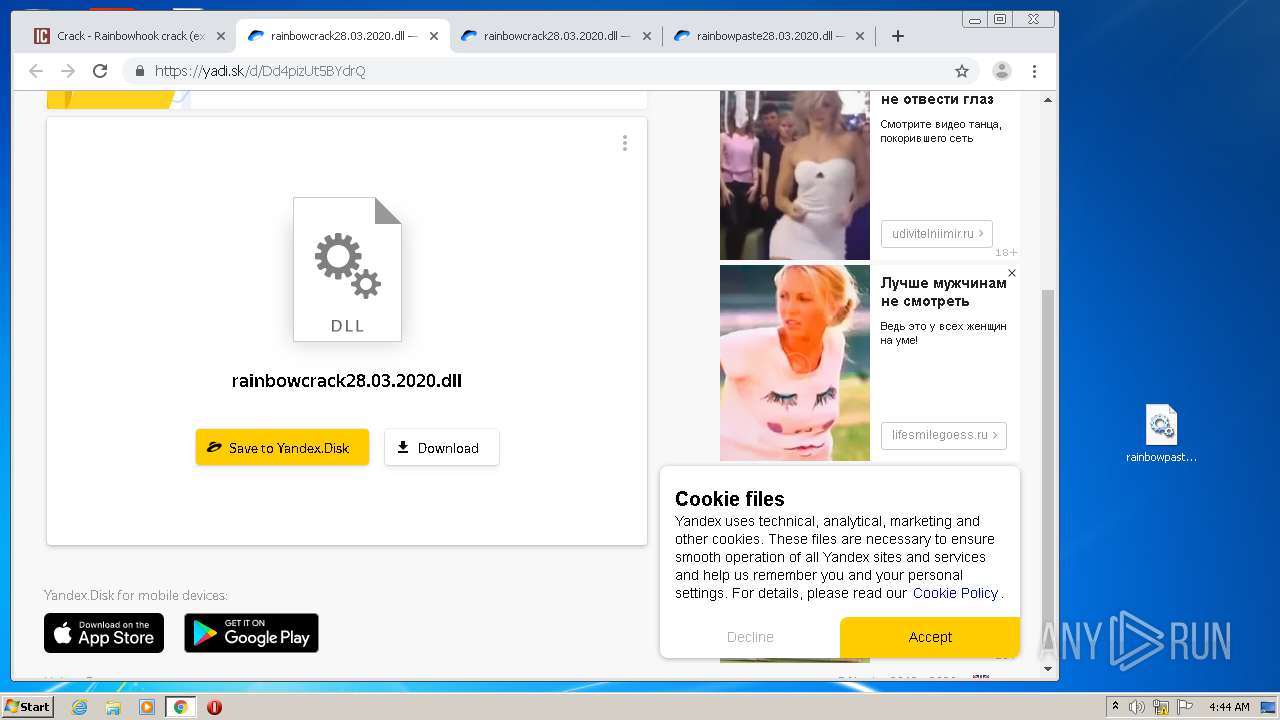
Manual execution by user
- chrome.exe (PID: 2816)
Reads the hosts file
- chrome.exe (PID: 2816)
- chrome.exe (PID: 932)
Reads internet explorer settings
- iexplore.exe (PID: 980)
- iexplore.exe (PID: 2604)
Creates files in the user directory
- iexplore.exe (PID: 2604)
Reads settings of System Certificates
- iexplore.exe (PID: 2604)
- chrome.exe (PID: 932)
- iexplore.exe (PID: 868)
- iexplore.exe (PID: 1704)
Changes settings of System certificates
- iexplore.exe (PID: 868)
- iexplore.exe (PID: 1704)
Adds / modifies Windows certificates
- iexplore.exe (PID: 868)
- iexplore.exe (PID: 1704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
97
Monitored processes
58
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1704 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\rainbowhook-crack-ex-cooking-paste.960.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 980 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1704 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3720 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1704 CREDAT:333057 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ea9a9d0,0x6ea9a9e0,0x6ea9a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2864 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,11977400807270281006,13176128951154549423,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1285576143397497621 --mojo-platform-channel-handle=968 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,11977400807270281006,13176128951154549423,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=13883201646201352422 --mojo-platform-channel-handle=1552 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,11977400807270281006,13176128951154549423,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7181965260594973947 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,11977400807270281006,13176128951154549423,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12600492090361784239 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
16 326
Read events
4 597
Write events
0
Delete events
0
Modification events
Executable files
14
Suspicious files
149
Text files
376
Unknown types
16
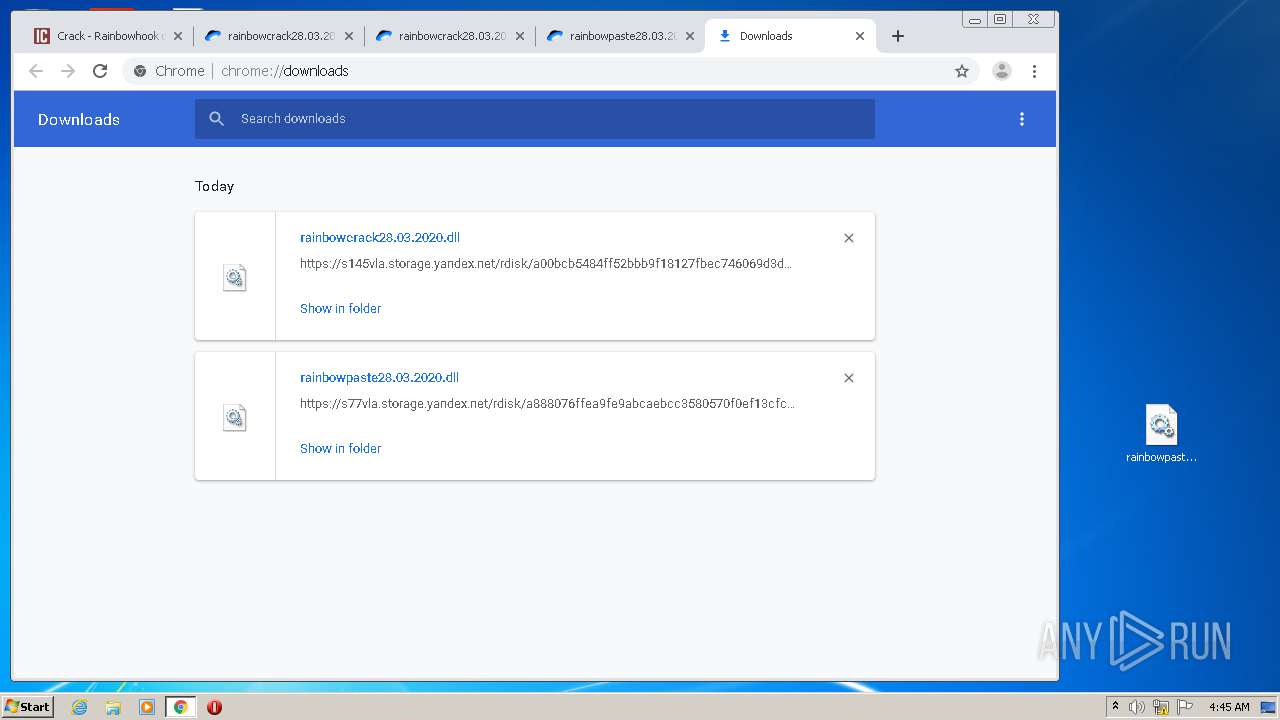
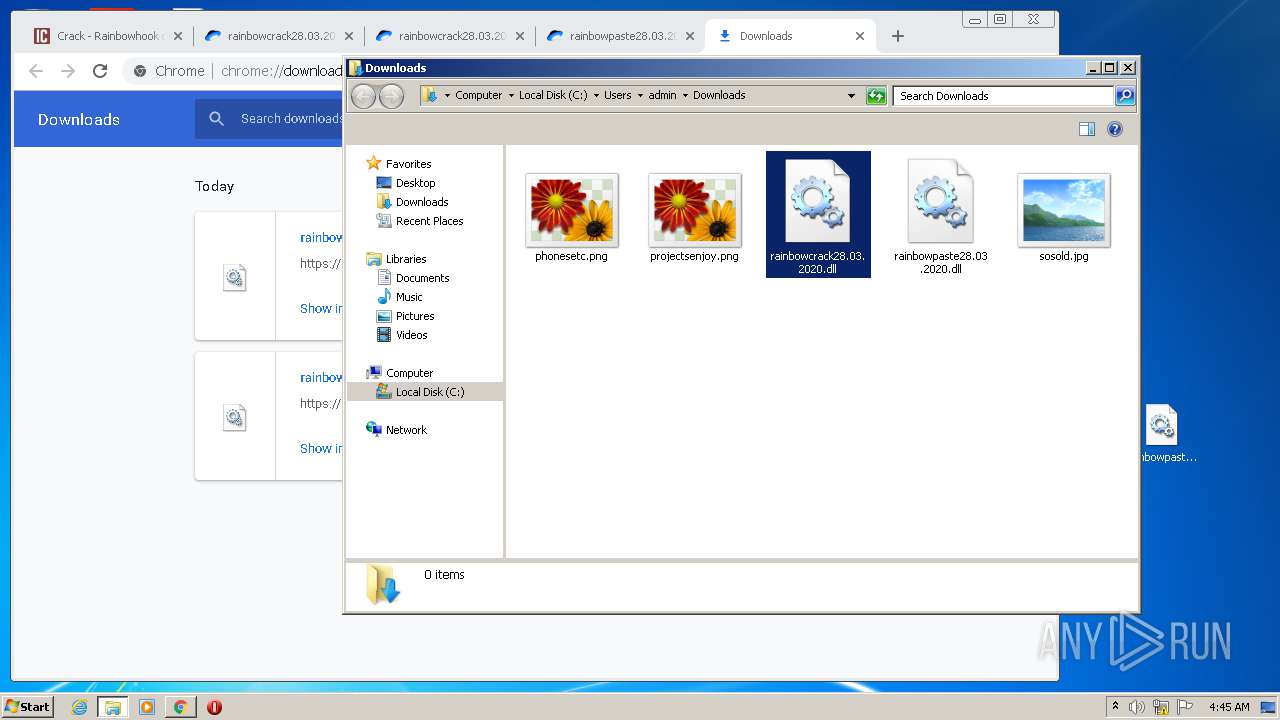
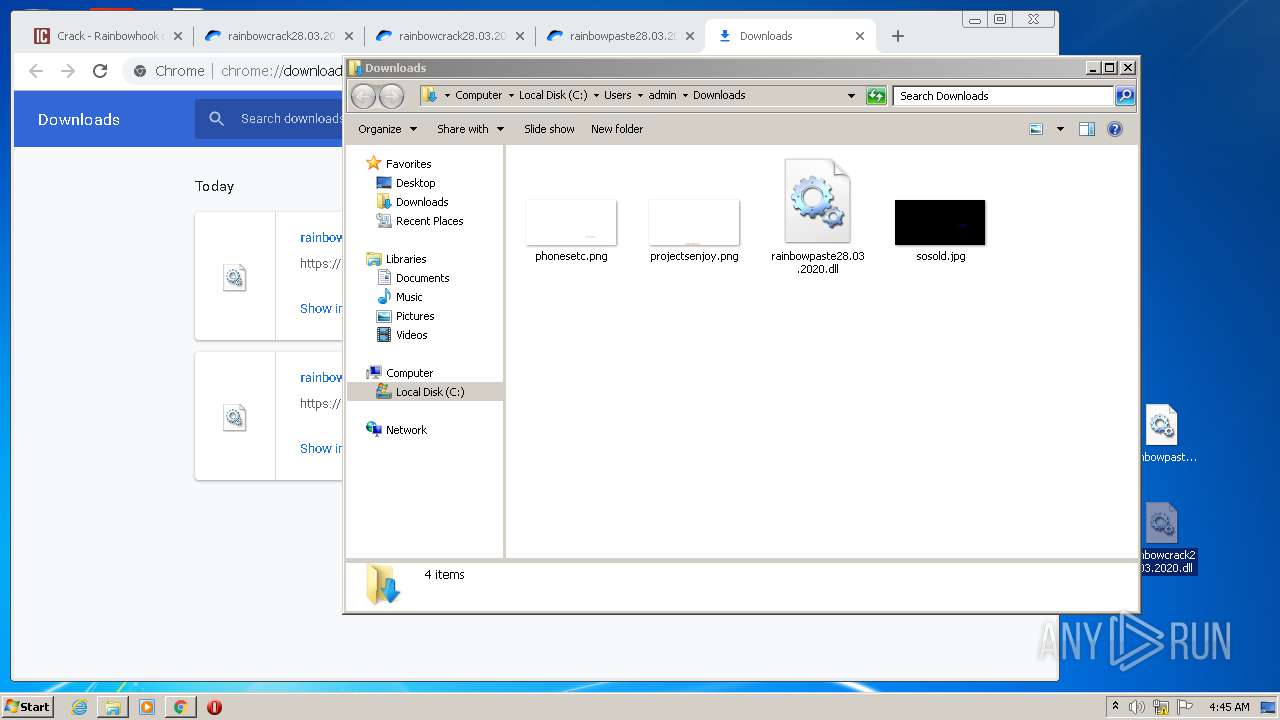
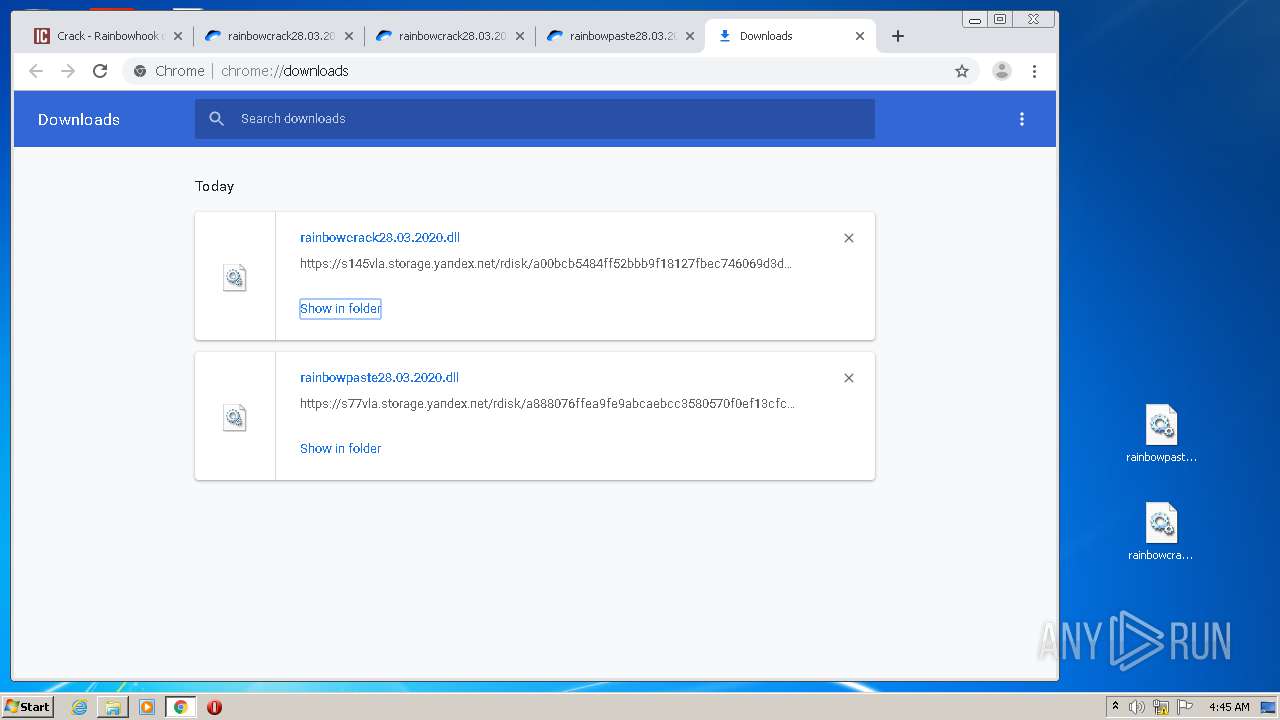
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1704 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1704 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1A44F760DDBDFBC3.TMP | — | |
MD5:— | SHA256:— | |||
| 1704 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8390F81248B37E48.TMP | — | |
MD5:— | SHA256:— | |||
| 1704 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF87C77ABD002AD9E7.TMP | — | |
MD5:— | SHA256:— | |||
| 1704 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB2CC4725DE24AD5F.TMP | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0BD82A-B00.pma | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f8b2aa39-3edc-43fe-a079-9be3ca879452.tmp | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10a059.TMP | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
133
DNS requests
94
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
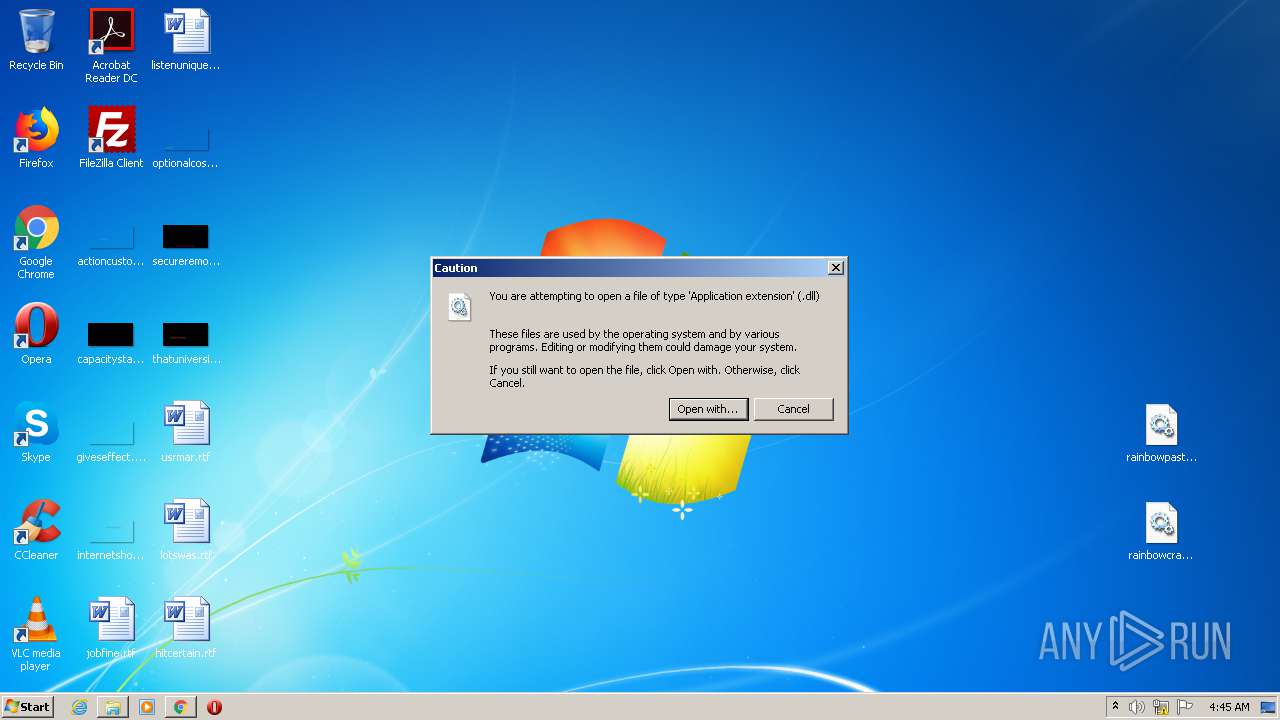
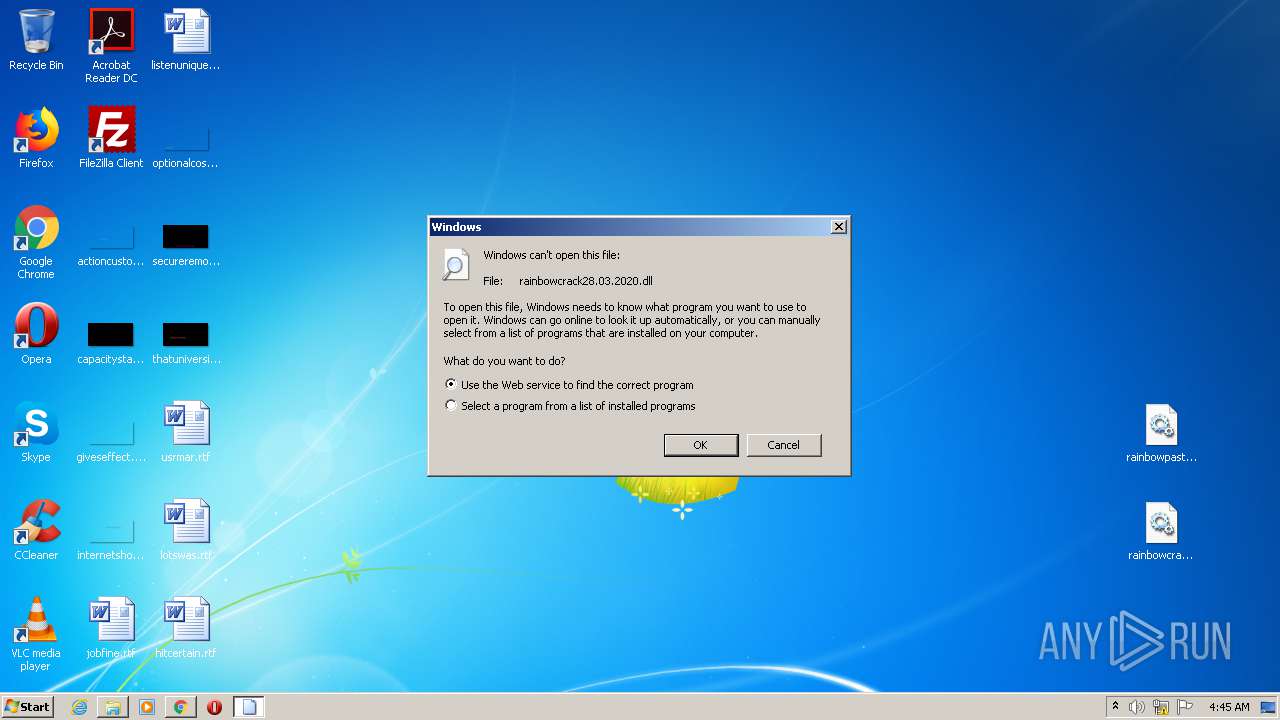
2604 | iexplore.exe | GET | 301 | 2.16.186.24:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=dll | unknown | — | — | whitelisted |
2604 | iexplore.exe | GET | 302 | 88.221.62.148:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=dll | unknown | — | — | whitelisted |
1704 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1704 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1704 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
932 | chrome.exe | GET | 200 | 74.125.8.140:80 | http://r6---sn-5hnednlk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=45.86.201.12&mm=28&mn=sn-5hnednlk&ms=nvh&mt=1594611159&mv=u&mvi=6&pl=27&shardbypass=yes | US | crx | 823 Kb | whitelisted |
932 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
1704 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
932 | chrome.exe | GET | 200 | 74.125.100.73:80 | http://r4---sn-5hne6nsz.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=45.86.201.12&mm=28&mn=sn-5hne6nsz&ms=nvh&mt=1594611159&mv=u&mvi=4&pl=27&shardbypass=yes | US | crx | 293 Kb | whitelisted |
932 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1704 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
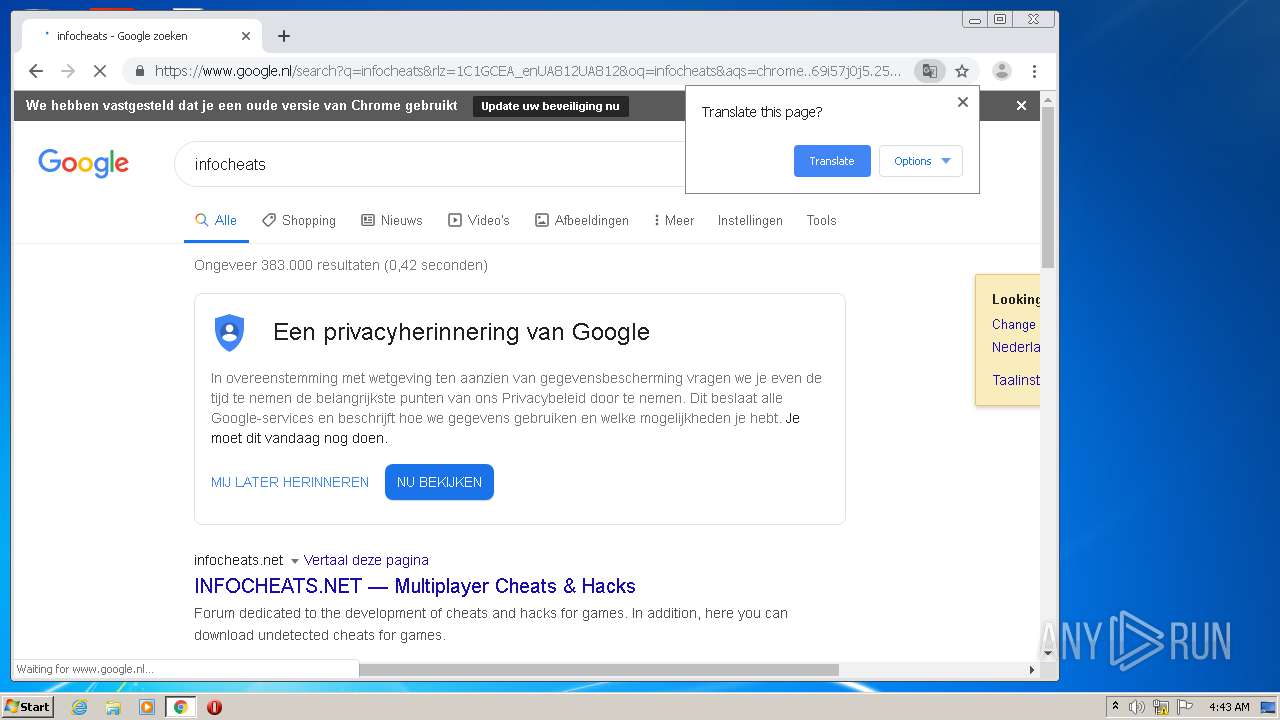
932 | chrome.exe | 216.58.205.227:443 | www.google.nl | Google Inc. | US | whitelisted |
932 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
932 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.21.238:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
932 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
932 | chrome.exe | 172.217.18.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
932 | chrome.exe | 216.58.206.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
— | — | 216.58.212.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
932 | chrome.exe | 74.125.100.73:80 | r4---sn-5hne6nsz.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |