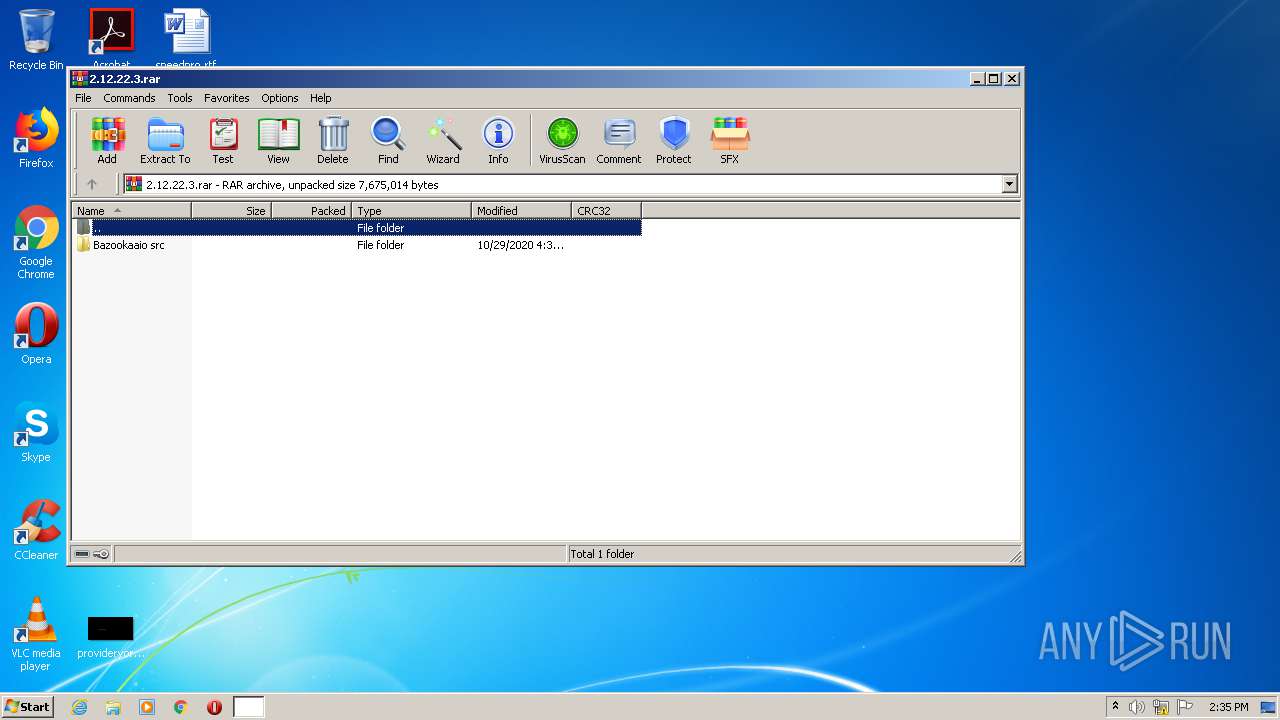
| File name: | 2.12.22.3.rar |
| Full analysis: | https://app.any.run/tasks/95f2f142-4ac4-4439-8c75-cc7c7a004506 |
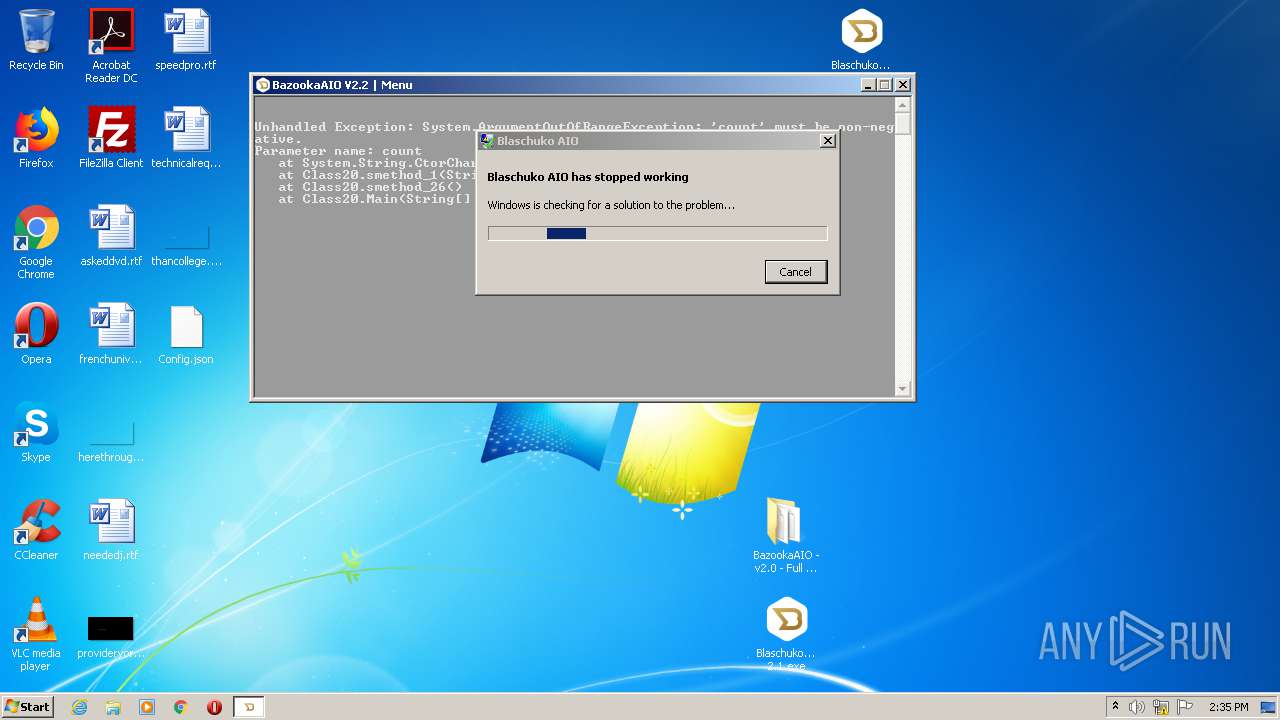
| Verdict: | Malicious activity |
| Analysis date: | October 29, 2020, 14:34:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 9948A4F3152029773427B62E6DDE4B70 |
| SHA1: | 223FA1ECFBF1B19ACE4383CE9B67B6AC81D84708 |
| SHA256: | 4EDBD4AD265B7074602720DAB2C9CB248F03480AA33EE923DB946DE173A4130A |
| SSDEEP: | 98304:ieShT8CQzHDBb5S0+j2xbhP1SUZ3OSSXhd9KxTJ2qtpXNzft:LShxQzdbg0+j2VlZ3OSSX5CTJ1Nzl |
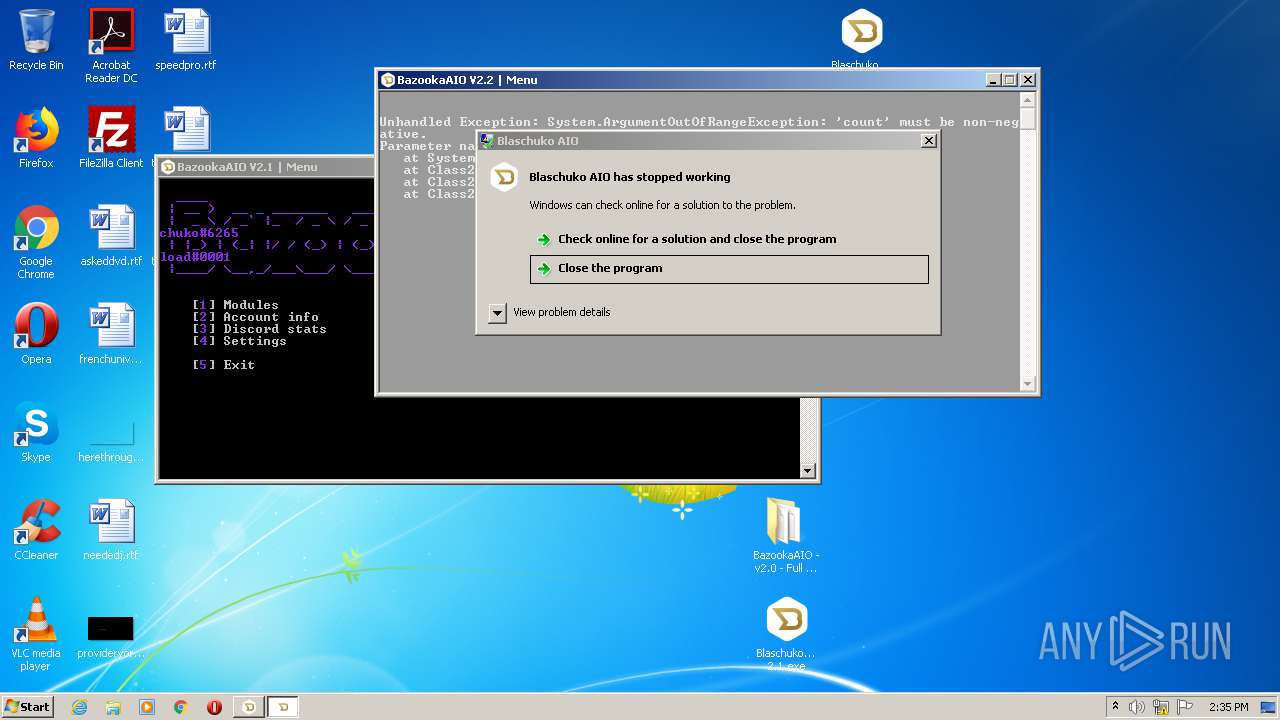
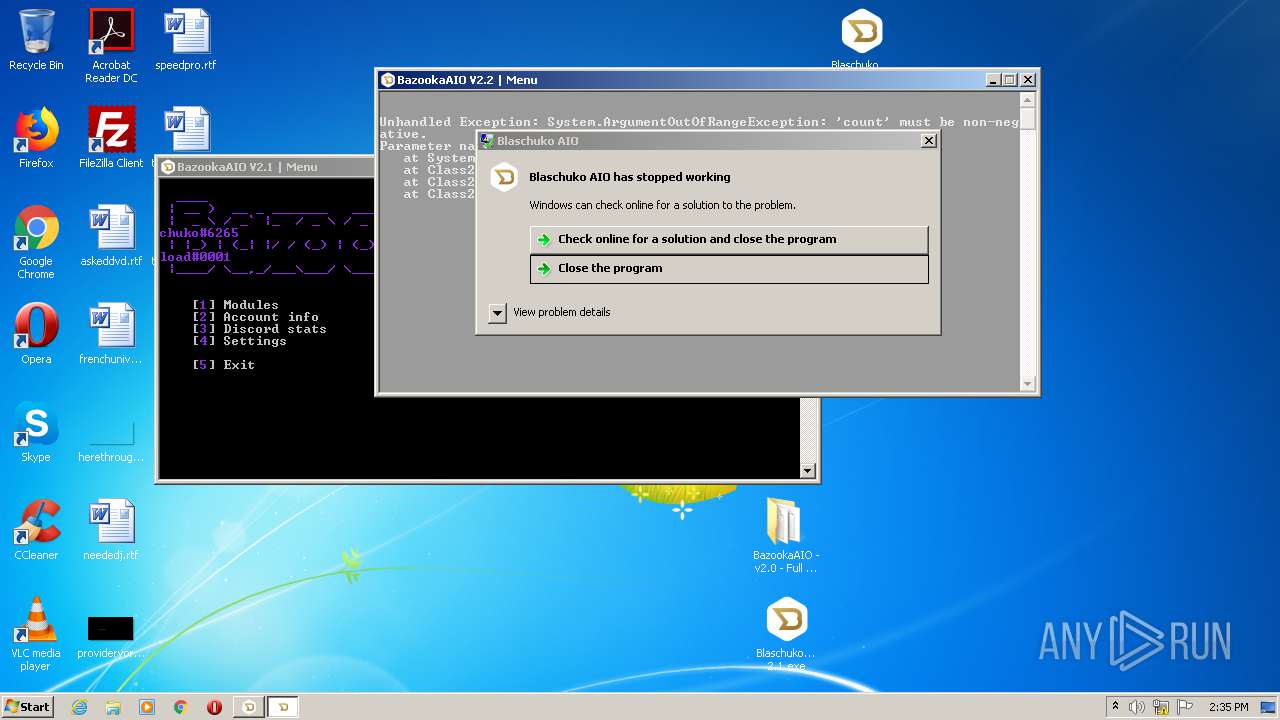
MALICIOUS
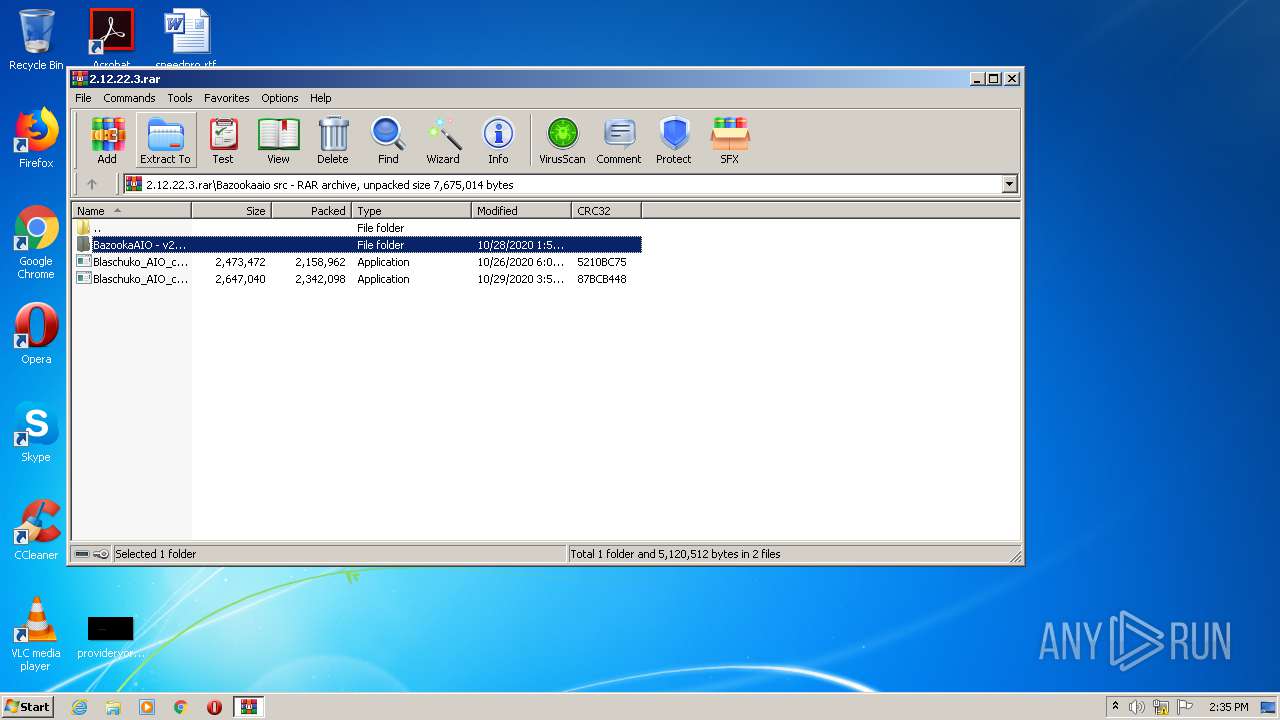
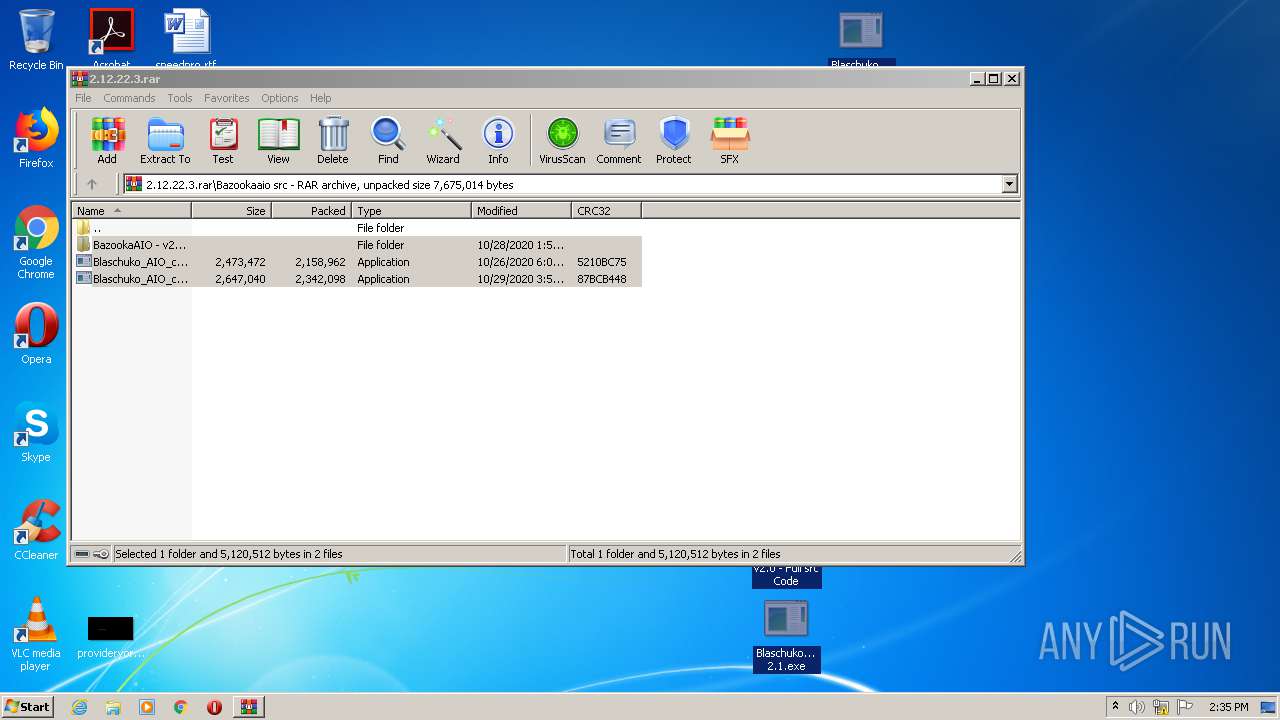
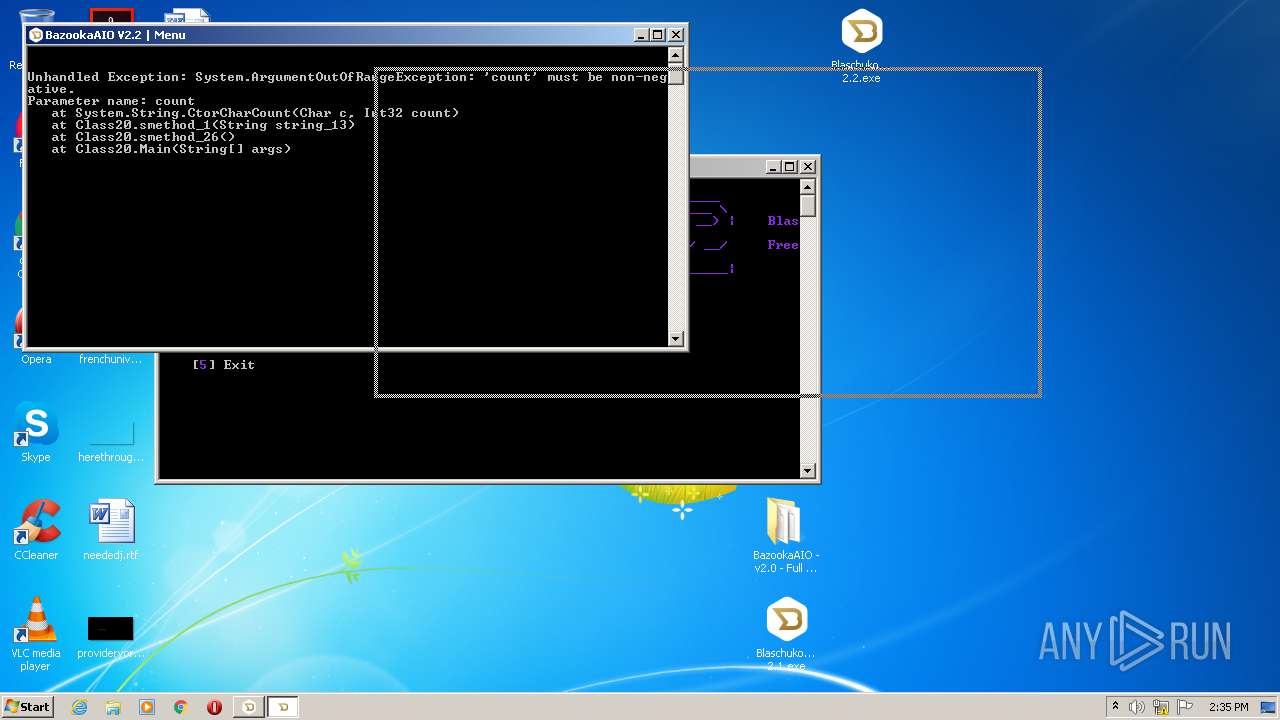
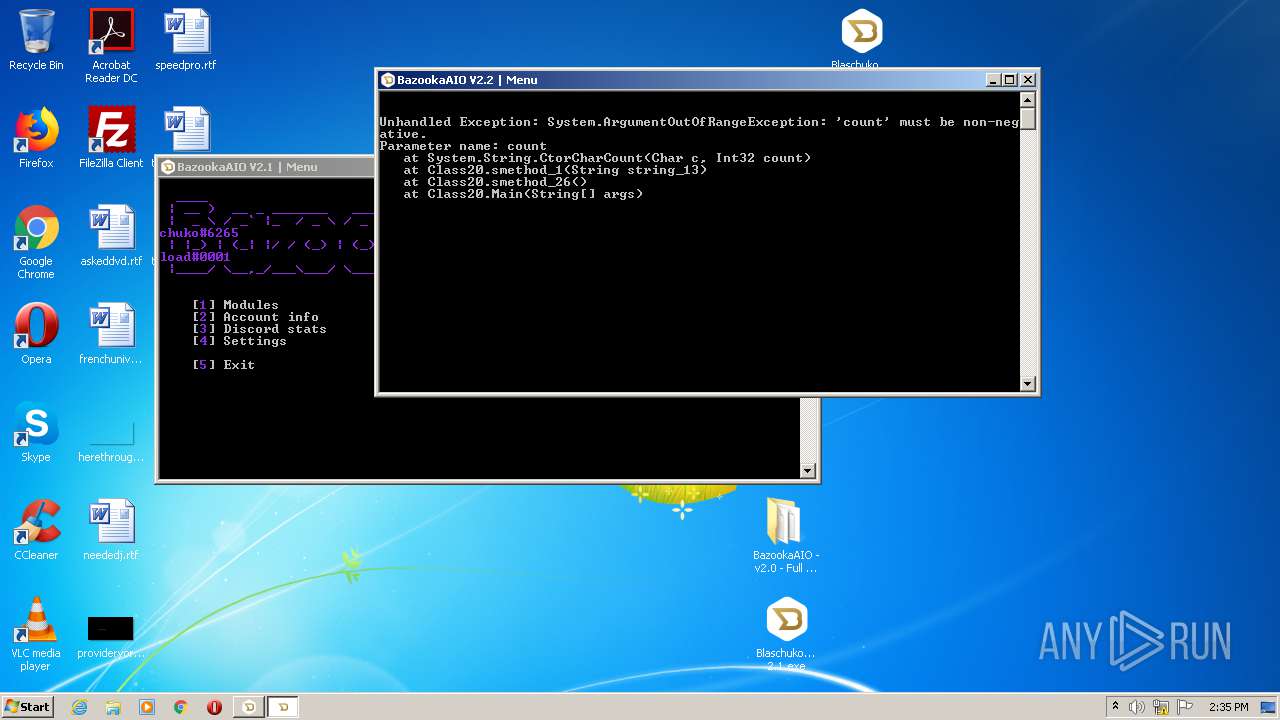
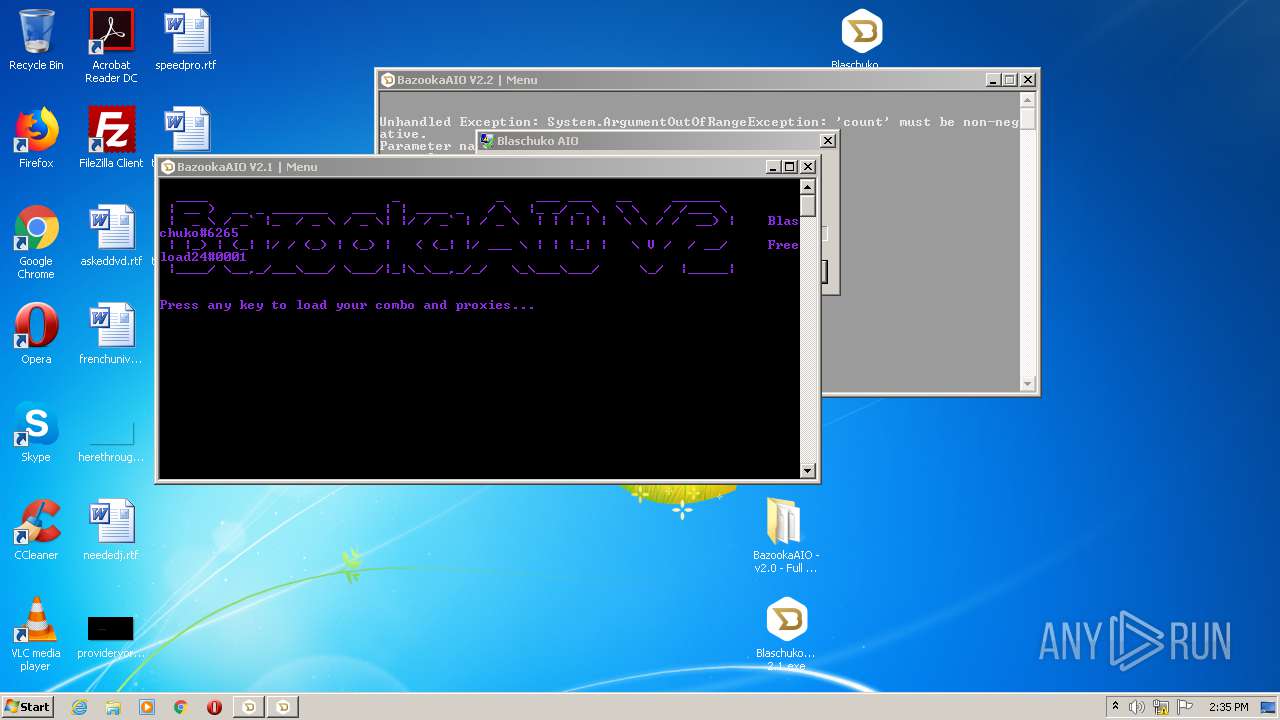
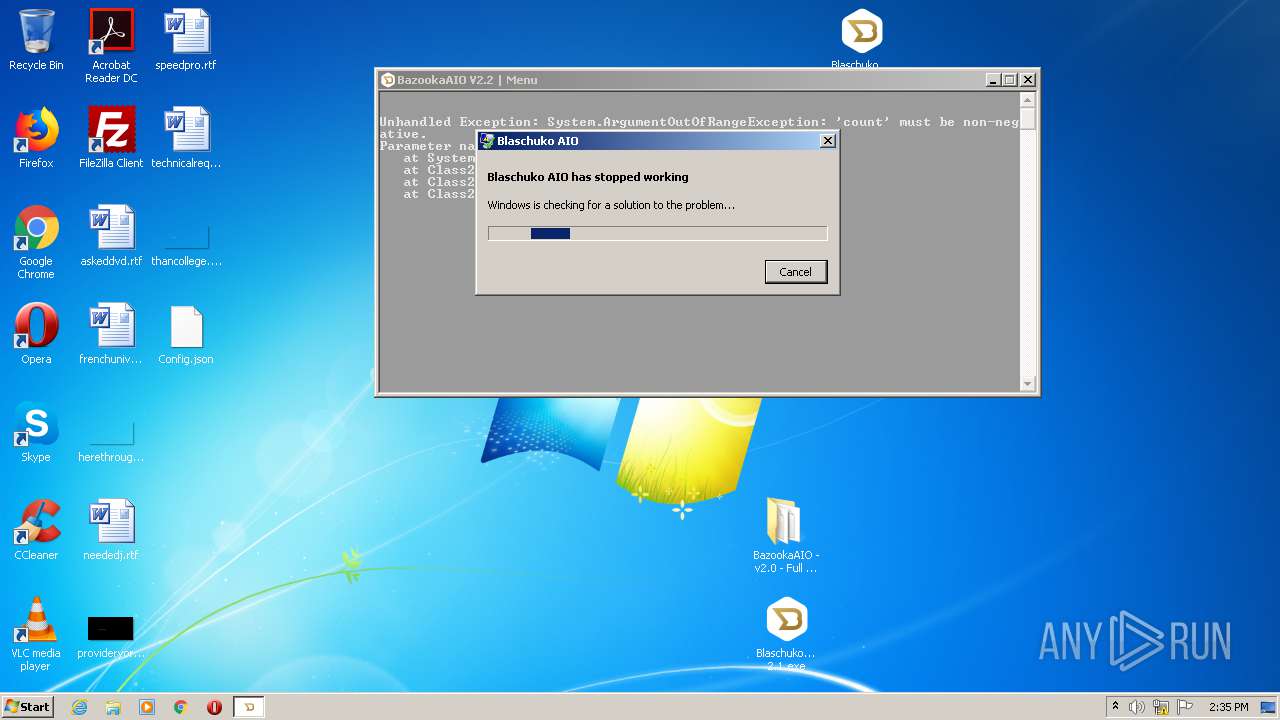
Application was dropped or rewritten from another process
- Blaschuko_AIO_cracked 2.1.exe (PID: 2276)
- Blaschuko_AIO_cracked 2.2.exe (PID: 3748)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3784)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2696)
INFO
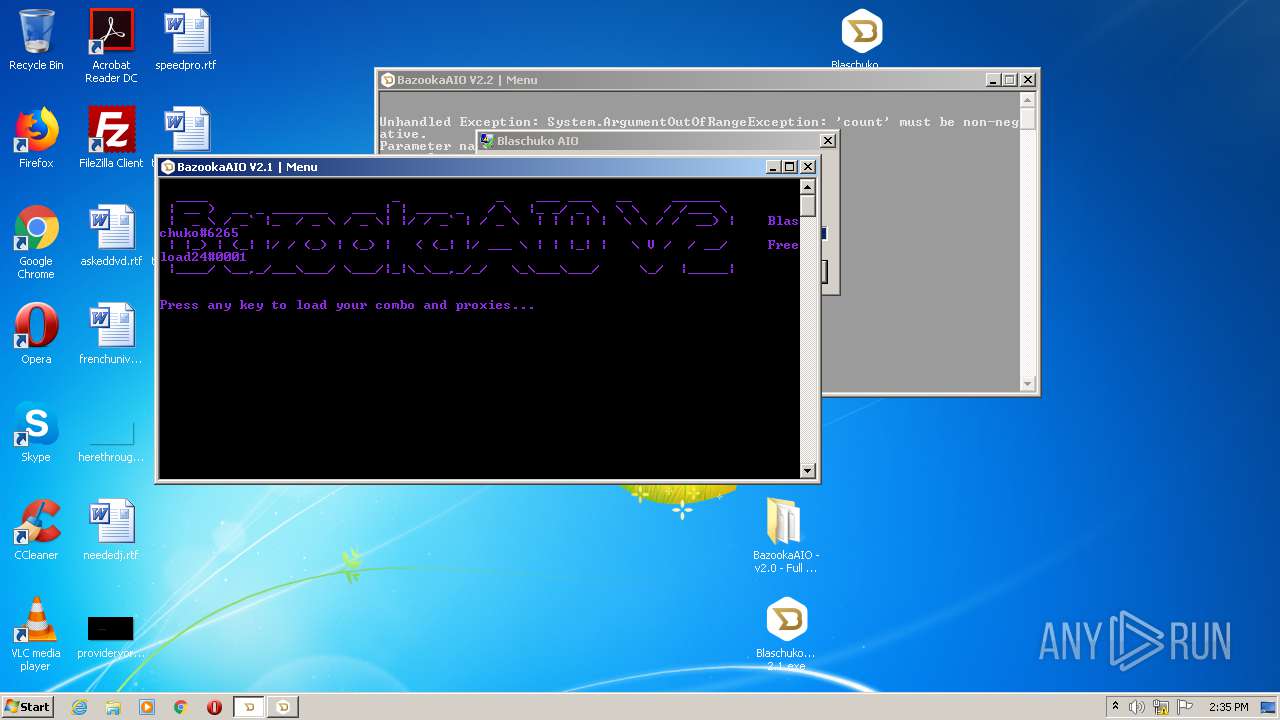
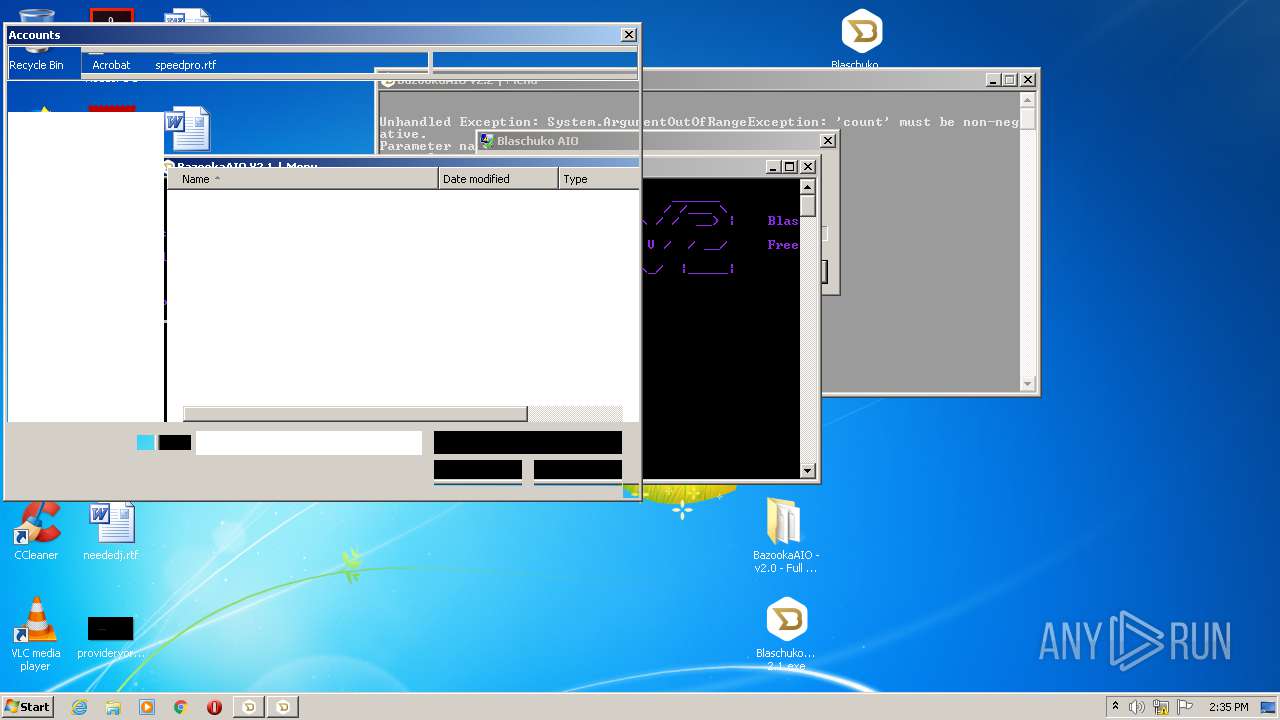
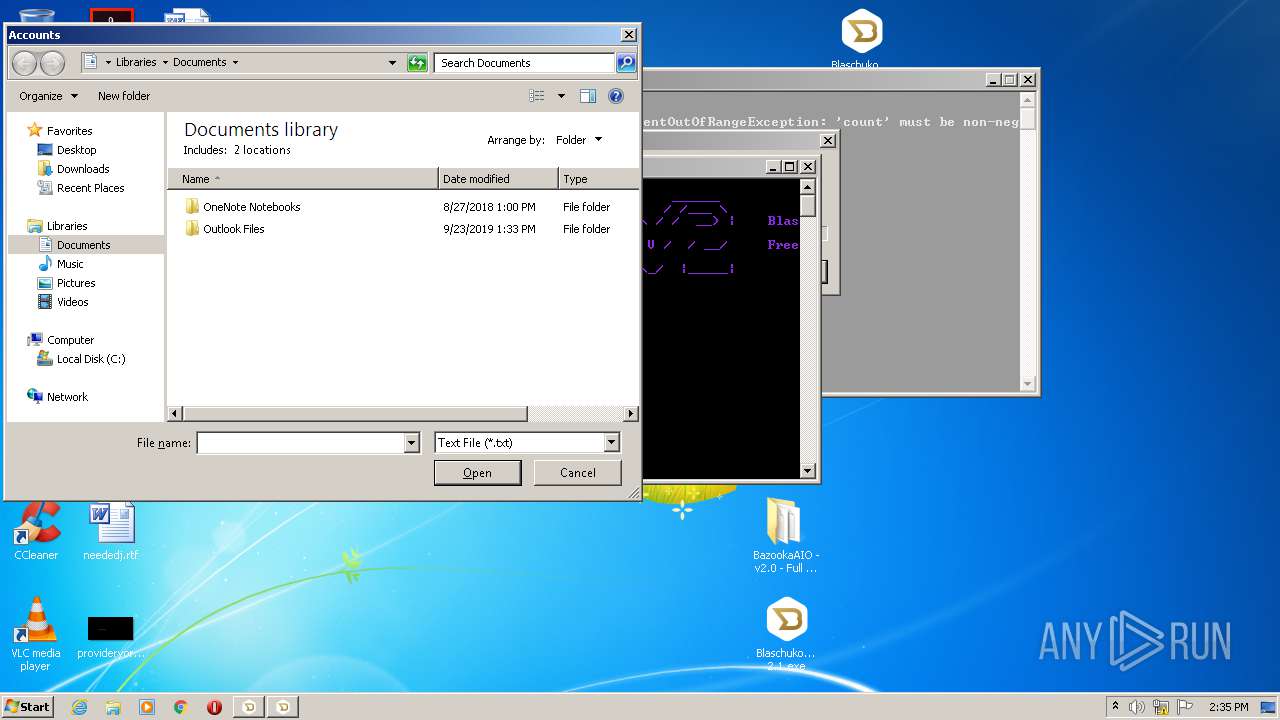
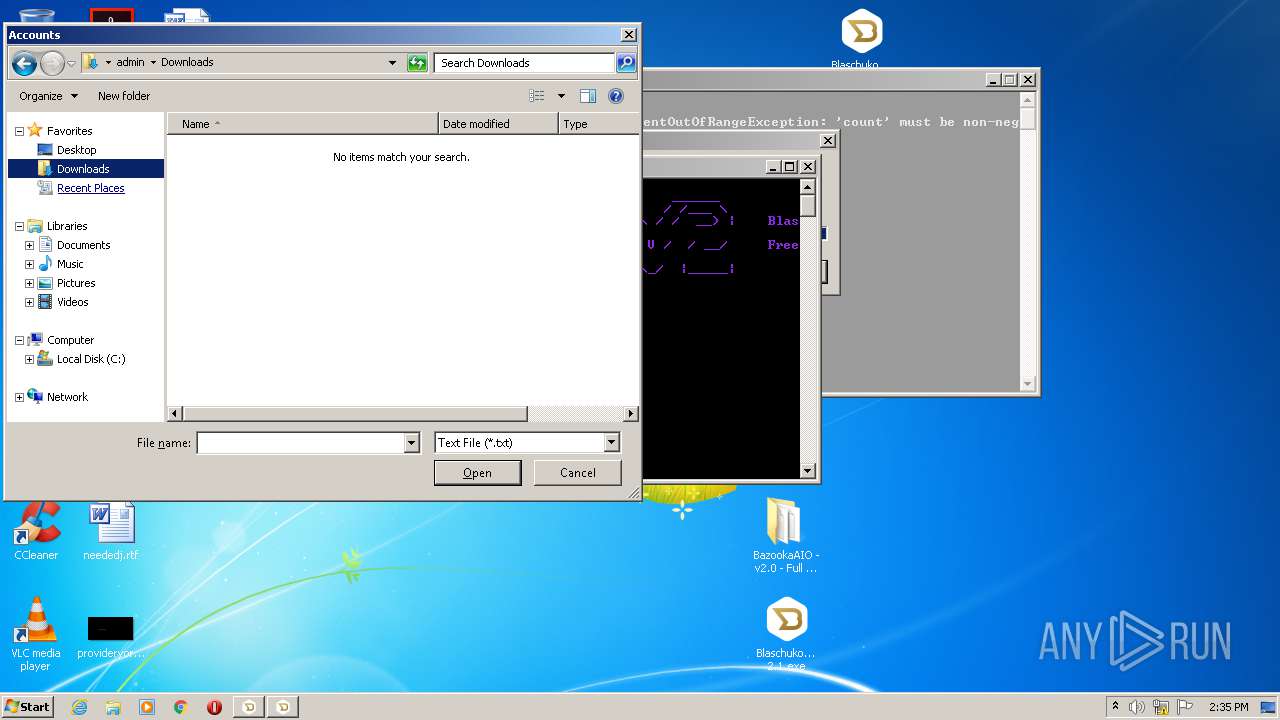
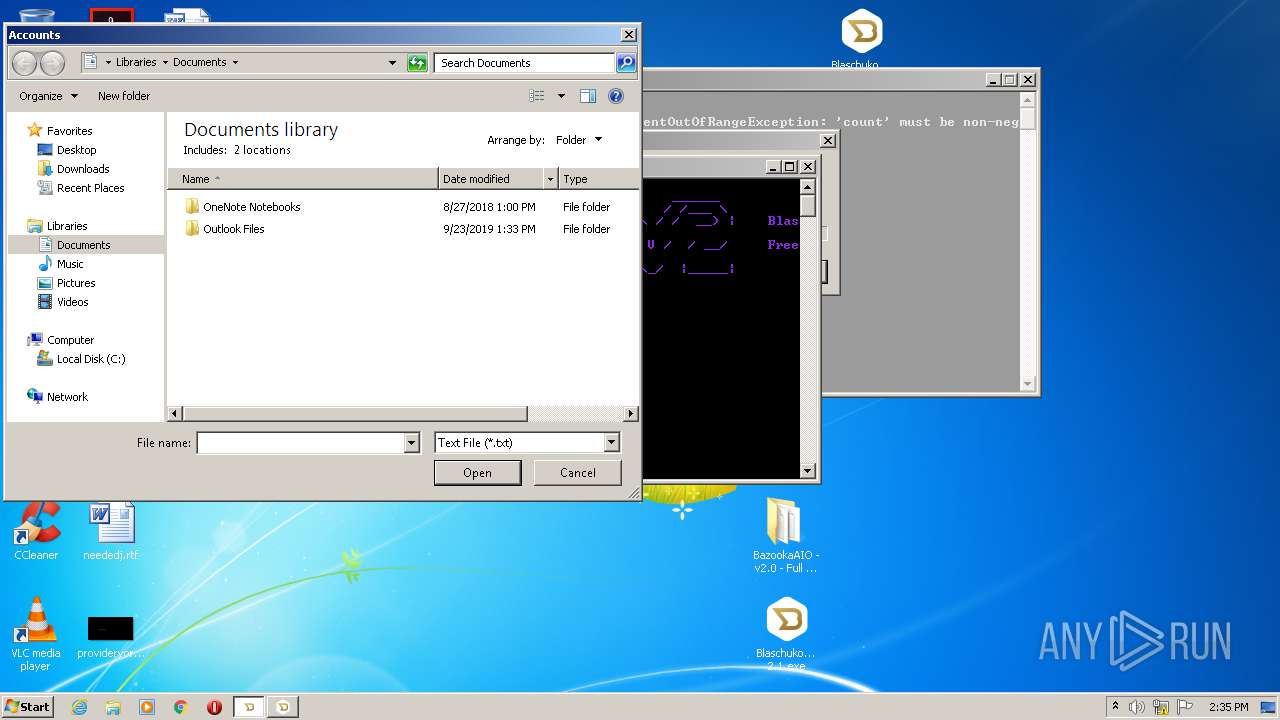
Manual execution by user
- Blaschuko_AIO_cracked 2.1.exe (PID: 2276)
- Blaschuko_AIO_cracked 2.2.exe (PID: 3748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
41
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
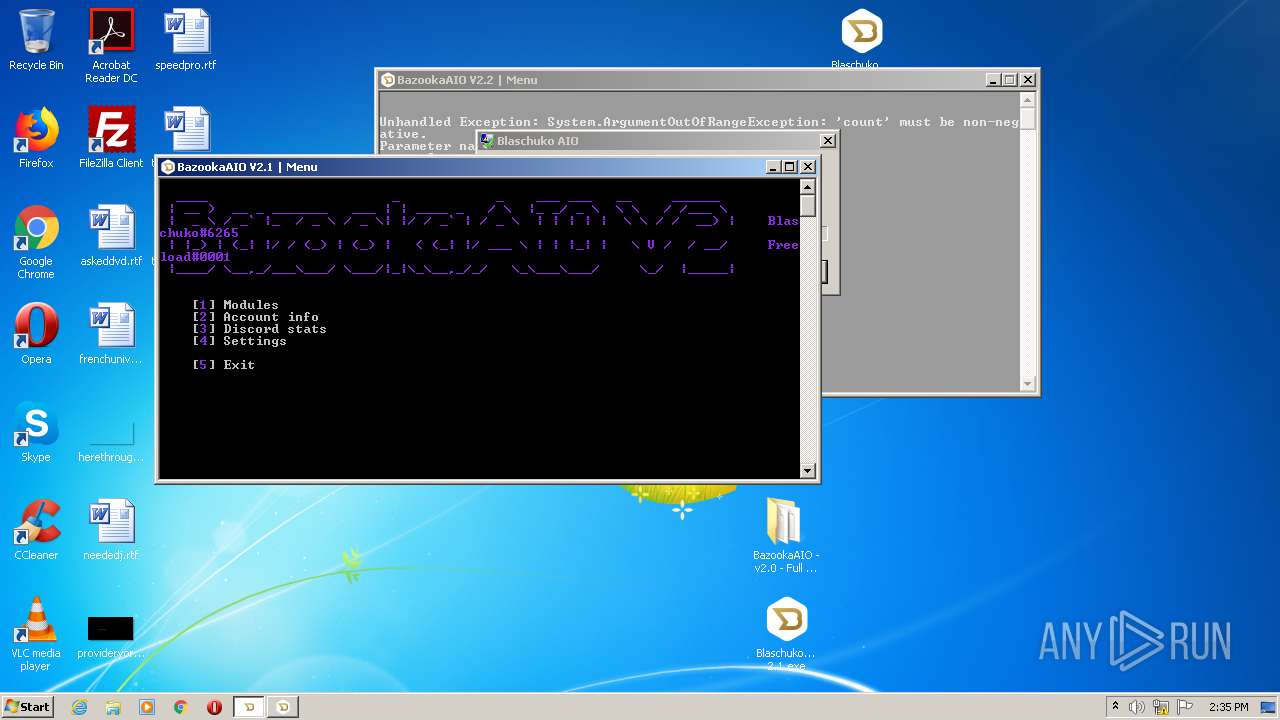
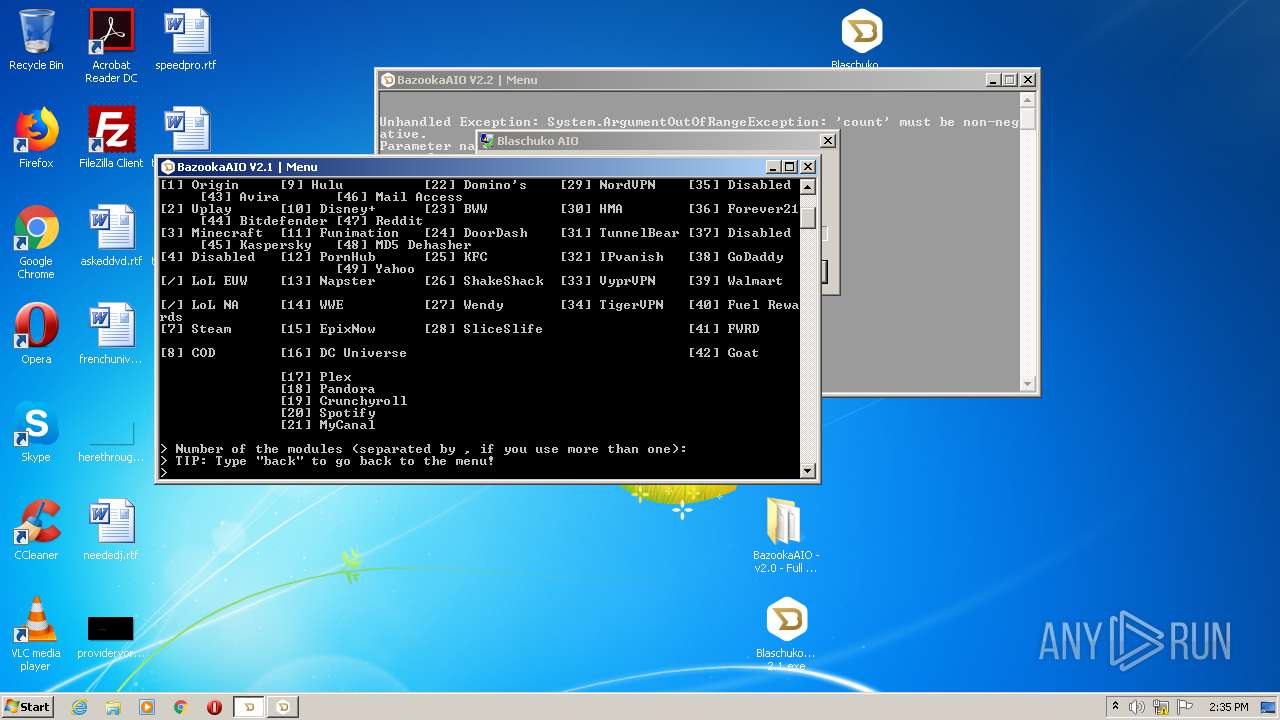
| 2276 | "C:\Users\admin\Desktop\Blaschuko_AIO_cracked 2.1.exe" | C:\Users\admin\Desktop\Blaschuko_AIO_cracked 2.1.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Blaschuko AIO Exit code: 3221225786 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2696 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\2.12.22.3.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3748 | "C:\Users\admin\Desktop\Blaschuko_AIO_cracked 2.2.exe" | C:\Users\admin\Desktop\Blaschuko_AIO_cracked 2.2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Blaschuko AIO Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3784 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 601
Read events
1 427
Write events
171
Delete events
3
Modification events
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\2.12.22.3.rar | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
8
Suspicious files
5
Text files
36
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2696.44197\Bazookaaio src\BazookaAIO - v2.0 - Full src Code\.vs\BaZookaAIO v2.0 Cracked\v16\.suo | binary | |
MD5:— | SHA256:— | |||
| 2696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2696.44197\Bazookaaio src\BazookaAIO - v2.0 - Full src Code\BaZookaAIO v2.0 Cracked.sln | text | |
MD5:— | SHA256:— | |||
| 2696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2696.44197\Bazookaaio src\BazookaAIO - v2.0 - Full src Code\bin\Debug\net461\BazookaAIO V2.pdb | binary | |
MD5:— | SHA256:— | |||
| 2696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2696.44197\Bazookaaio src\BazookaAIO - v2.0 - Full src Code\bin\Debug\net461\BazookaAIO V2.exe | executable | |
MD5:— | SHA256:— | |||
| 2696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2696.44197\Bazookaaio src\BazookaAIO - v2.0 - Full src Code\bin\Debug\net461\System.Core.dll | executable | |
MD5:— | SHA256:— | |||
| 2696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2696.44197\Bazookaaio src\BazookaAIO - v2.0 - Full src Code\obj\BaZookaAIO v2.0 Cracked.csproj.nuget.g.props | xml | |
MD5:— | SHA256:— | |||
| 2696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2696.44197\Bazookaaio src\BazookaAIO - v2.0 - Full src Code\obj\BaZookaAIO v2.0 Cracked.csproj.nuget.dgspec.json | text | |
MD5:— | SHA256:— | |||
| 2696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2696.44197\Bazookaaio src\BazookaAIO - v2.0 - Full src Code\BaZookaAIO v2.0 Cracked.csproj | text | |
MD5:— | SHA256:— | |||
| 2696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2696.44197\Bazookaaio src\BazookaAIO - v2.0 - Full src Code\bin\Debug\net461\BazookaAIO V2.exe.config | xml | |
MD5:80318442D34FD71503D6548B2A9F5490 | SHA256:C17F391D07FC4BD47047C494DE42E80B9FDBAD4A0024BDC7CABA4733E339296E | |||
| 2696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2696.44197\Bazookaaio src\BazookaAIO - v2.0 - Full src Code\bin\Debug\net461\xNet.dll | executable | |
MD5:AC1DCEDDBC66A1AB7915AC9931F0CFEC | SHA256:CC949931EF9533ADCED83F3D58862E9732E5DB7AD17B5FD4CB9D209A99EDB592 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2992 | WerFault.exe | 13.88.21.125:80 | watson.microsoft.com | Microsoft Corporation | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
watson.microsoft.com |
| whitelisted |