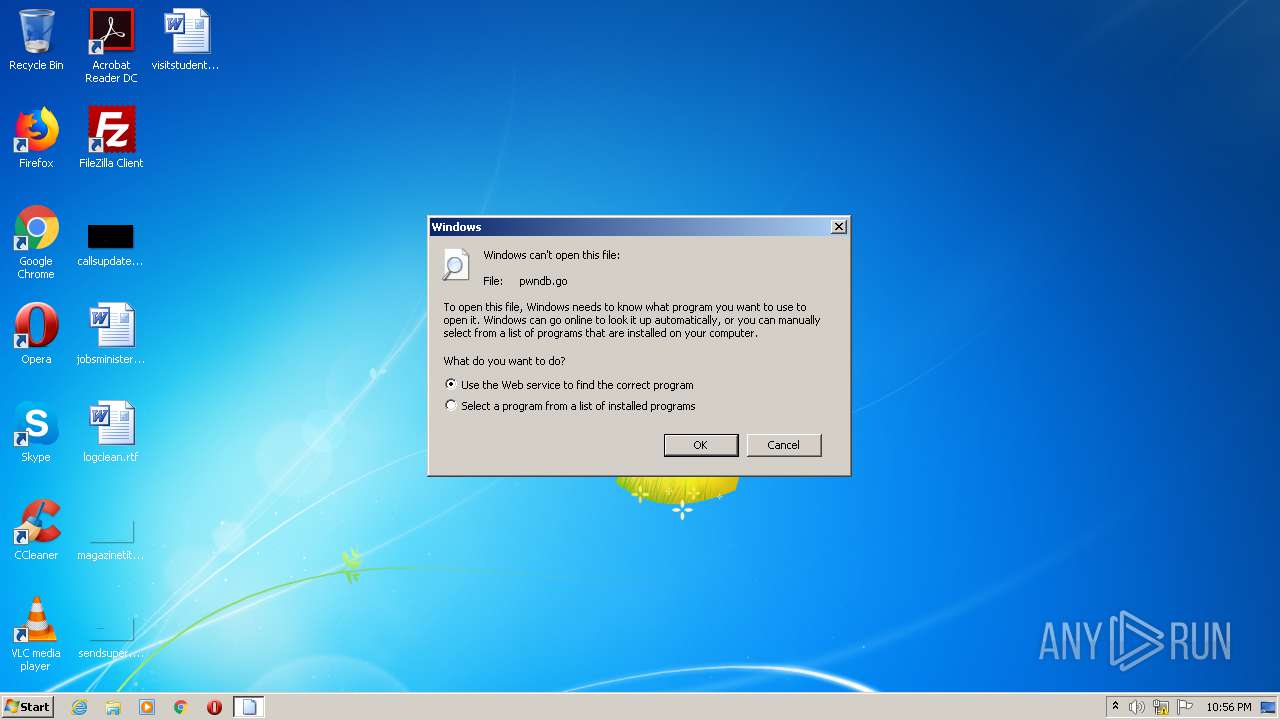
| download: | pwndb.go |
| Full analysis: | https://app.any.run/tasks/cf596896-1e11-46f5-a1ac-a402a5c38b06 |
| Verdict: | No threats detected |
| Analysis date: | November 24, 2020, 22:56:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | F5E4E1E081FB41933CF60E21B63E6680 |
| SHA1: | 4DB990F77D1D7375FC48D5EABBFFABC5D2C103ED |
| SHA256: | 4ED77857E91673B3D14769DFB5BB130E19055D61F6758B1FF0C23500B46985F6 |
| SSDEEP: | 3072:JEMPDuqw7wVb2adYVadYmadYK7+h6nN/JQzDGqnbp6ae0JqwZVj4IersMoc04owy:LPDuqw7wVb2aqVaqmaqK7+h6nN/JQzD/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
| viewport: | width=device-width |
|---|---|
| Title: | pwndb/pwndb.go at master · coj337/pwndb · GitHub |
| Description: | pwndb is a tool that looks for leaked passwords from a dark web breach database given a user or domain. - coj337/pwndb |
| appleItunesApp: | app-id=1477376905 |
| twitterImageSrc: | https://avatars2.githubusercontent.com/u/9269226?s=400&v=4 |
| twitterSite: | @github |
| twitterCard: | summary |
| twitterTitle: | coj337/pwndb |
| twitterDescription: | pwndb is a tool that looks for leaked passwords from a dark web breach database given a user or domain. - coj337/pwndb |
| requestId: | 7D83:7BCF:99501F:C6B172:5FBD8FAC |
| htmlSafeNonce: | 89fd6e6a0cfefd33601dcb9baf8a93dbe1369ce53220faccb25d2551d0218d41 |
| visitorPayload: | eyJyZWZlcnJlciI6IiIsInJlcXVlc3RfaWQiOiI3RDgzOjdCQ0Y6OTk1MDFGOkM2QjE3Mjo1RkJEOEZBQyIsInZpc2l0b3JfaWQiOiIxNzAwMzI4Mjc3OTMyNzU4MjU3IiwicmVnaW9uX2VkZ2UiOiJmcmEiLCJyZWdpb25fcmVuZGVyIjoiZnJhIn0= |
| visitorHmac: | e0530cd06fee1e45410713cc1c5e4c040f3fcbaaf35fdca7d6b420ab775e7c3d |
| cookieConsentRequired: | |
| hovercardSubjectTag: | repository:278050882 |
| githubKeyboardShortcuts: | repository,source-code |
| googleSiteVerification: | GXs5KoUUkNCoaAZn7wPN-t01Pywp9M3sEjnt_3_ZWPc |
| octolyticsHost: | collector.githubapp.com |
| octolyticsAppId: | github |
| octolyticsEventUrl: | https://collector.githubapp.com/github-external/browser_event |
| analyticsLocation: | /<user-name>/<repo-name>/blob/show |
| optimizelyDatafile: | {"version": "4", "rollouts": [], "typedAudiences": [], "anonymizeIP": true, "projectId": "16737760170", "variables": [], "featureFlags": [], "experiments": [{"status": "Running", "audienceIds": [], "variations": [{"variables": [], "id": "18630402174", "key": "launchpad"}, {"variables": [], "id": "18866331456", "key": "control"}], "id": "18651193356", "key": "_features_redesign_rollout", "layerId": "18645992876", "trafficAllocation": [{"entityId": "18630402174", "endOfRange": 500}, {"entityId": "18866331456", "endOfRange": 1000}, {"entityId": "18630402174", "endOfRange": 5000}, {"entityId": "18630402174", "endOfRange": 5500}, {"entityId": "18866331456", "endOfRange": 10000}], "forcedVariations": {"143327983.1601483920": "launchpad", "1955030087.1562868941": "launchpad", "1983887325.1550021416": "launchpad", "1947530619.1600461583": "launchpad"}}, {"status": "Running", "audienceIds": [], "variations": [{"variables": [], "id": "19136700362", "key": "show_plans"}, {"variables": [], "id": "19157700511", "key": "control"}], "id": "19062314978", "key": "account_billing_plans", "layerId": "19068014945", "trafficAllocation": [{"entityId": "19136700362", "endOfRange": 5000}, {"entityId": "19157700511", "endOfRange": 10000}], "forcedVariations": {"1238720267648ea2c88a74b410aa3c5c": "show_plans", "c4abf59d1620c671458b2a74df2a2410": "control"}}], "audiences": [{"conditions": "[\"or\", {\"match\": \"exact\", \"name\": \"$opt_dummy_attribute\", \"type\": \"custom_attribute\", \"value\": \"$opt_dummy_value\"}]", "id": "$opt_dummy_audience", "name": "Optimizely-Generated Audience for Backwards Compatibility"}], "groups": [], "attributes": [{"id": "16822470375", "key": "user_id"}, {"id": "17143601254", "key": "spammy"}, {"id": "18175660309", "key": "organization_plan"}, {"id": "18813001570", "key": "is_logged_in"}, {"id": "19073851829", "key": "geo"}], "botFiltering": false, "accountId": "16737760170", "events": [{"experimentIds": [], "id": "17911811441", "key": "hydro_click.dashboard.teacher_toolbox_cta"}, {"experimentIds": [], "id": "18124116703", "key": "submit.organizations.complete_sign_up"}, {"experimentIds": [], "id": "18145892387", "key": "no_metric.tracked_outside_of_optimizely"}, {"experimentIds": [], "id": "18178755568", "key": "click.org_onboarding_checklist.add_repo"}, {"experimentIds": [], "id": "18180553241", "key": "submit.repository_imports.create"}, {"experimentIds": [], "id": "18186103728", "key": "click.help.learn_more_about_repository_creation"}, {"experimentIds": [], "id": "18188530140", "key": "test_event.do_not_use_in_production"}, {"experimentIds": [], "id": "18191963644", "key": "click.empty_org_repo_cta.transfer_repository"}, {"experimentIds": [], "id": "18195612788", "key": "click.empty_org_repo_cta.import_repository"}, {"experimentIds": [], "id": "18210945499", "key": "click.org_onboarding_checklist.invite_members"}, {"experimentIds": [], "id": "18211063248", "key": "click.empty_org_repo_cta.create_repository"}, {"experimentIds": [], "id": "18215721889", "key": "click.org_onboarding_checklist.update_profile"}, {"experimentIds": [], "id": "18224360785", "key": "click.org_onboarding_checklist.dismiss"}, {"experimentIds": [], "id": "18234832286", "key": "submit.organization_activation.complete"}, {"experimentIds": [], "id": "18252392383", "key": "submit.org_repository.create"}, {"experimentIds": [], "id": "18257551537", "key": "submit.org_member_invitation.create"}, {"experimentIds": [], "id": "18259522260", "key": "submit.organization_profile.update"}, {"experimentIds": [], "id": "18564603625", "key": "view.classroom_select_organization"}, {"experimentIds": [], "id": "18568612016", "key": "click.classroom_sign_in_click"}, {"experimentIds": [], "id": "18572592540", "key": "view.classroom_name"}, {"experimentIds": [], "id": "18574203855", "key": "click.classroom_create_organization"}, {"experimentIds": [], "id": "18582053415", "key": "click.classroom_select_organization"}, {"experimentIds": [], "id": "18589463420", "key": "click.classroom_create_classroom"}, {"experimentIds": [], "id": "18591323364", "key": "click.classroom_create_first_classroom"}, {"experimentIds": [], "id": "18591652321", "key": "click.classroom_grant_access"}, {"experimentIds": [], "id": "18607131425", "key": "view.classroom_creation"}, {"experimentIds": [], "id": "18831680583", "key": "upgrade_account_plan"}, {"experimentIds": [], "id": "19064064515", "key": "click.signup"}, {"experimentIds": [], "id": "19075373687", "key": "click.view_account_billing_page"}, {"experimentIds": [], "id": "19077355841", "key": "click.dismiss_signup_prompt"}, {"experimentIds": ["19062314978"], "id": "19079713938", "key": "click.contact_sales"}, {"experimentIds": ["19062314978"], "id": "19120963070", "key": "click.compare_account_plans"}, {"experimentIds": ["19062314978"], "id": "19151690317", "key": "click.upgrade_account_cta"}], "revision": "338"} |
Total processes
34
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\pwndb.go | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report