| File name: | movemenoreg.vbs |
| Full analysis: | https://app.any.run/tasks/a351f21a-424f-46bd-8f23-335814101be0 |
| Verdict: | Malicious activity |
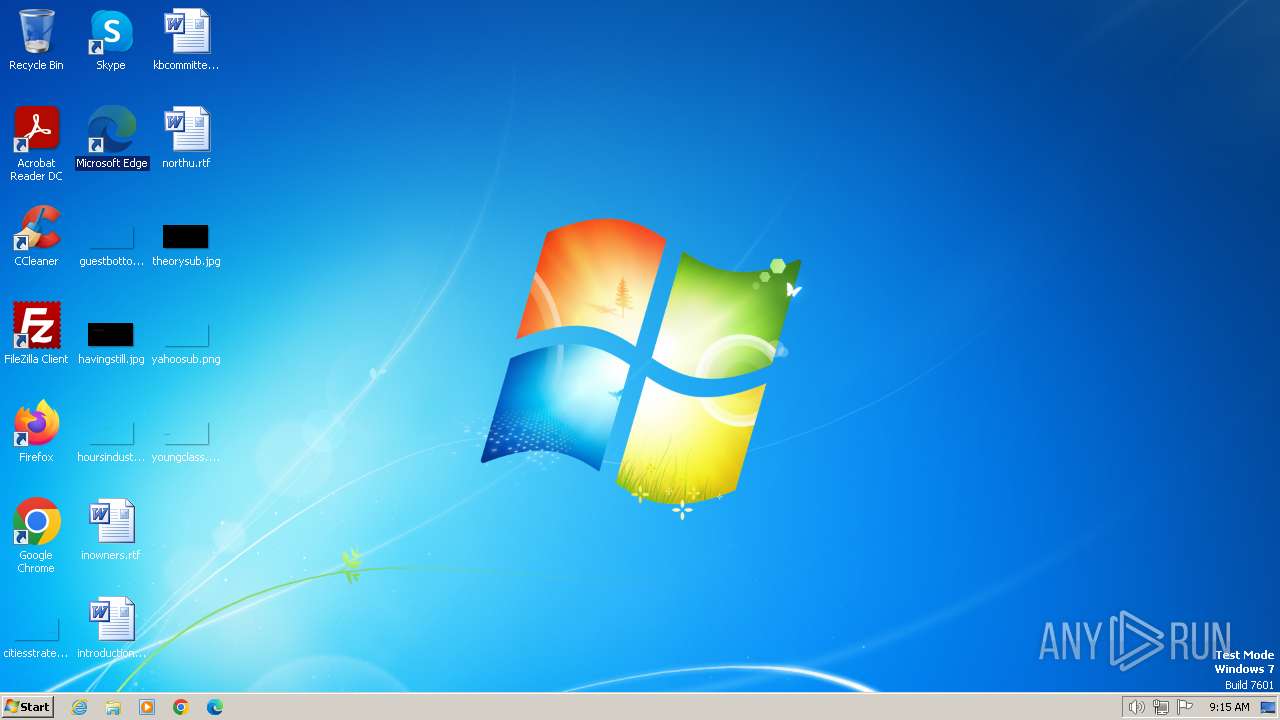
| Analysis date: | February 05, 2024, 09:15:32 |
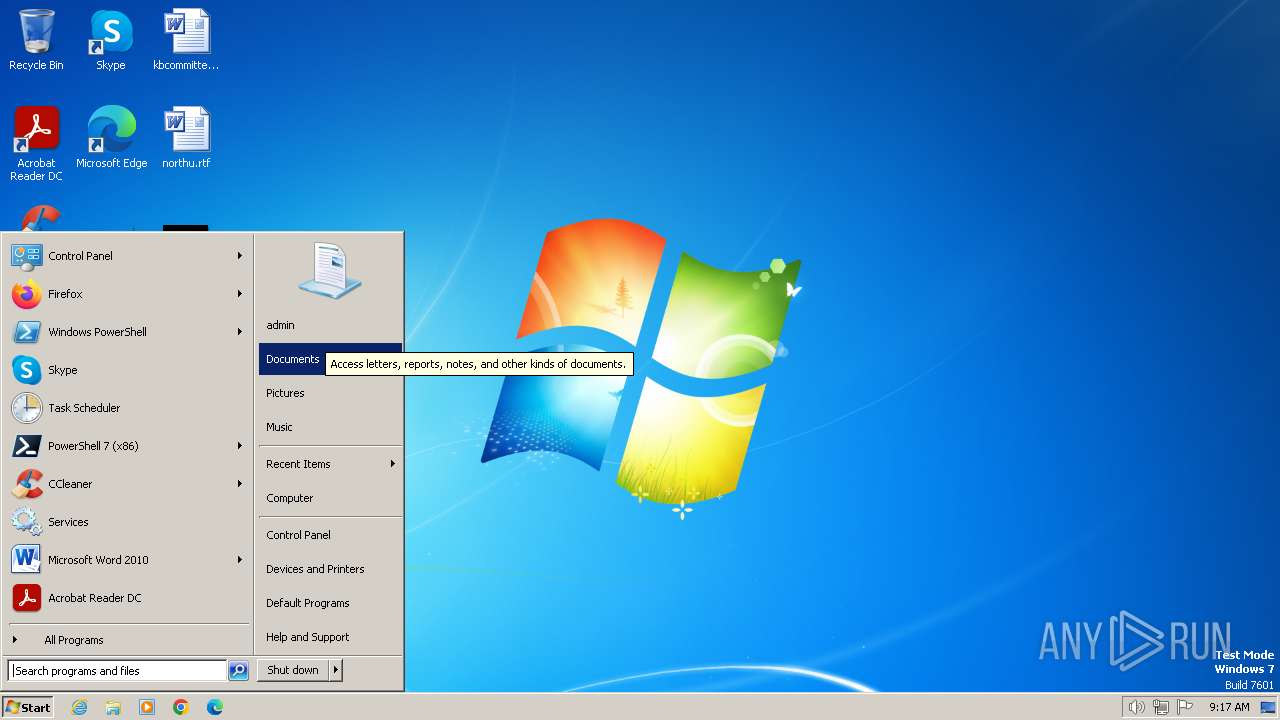
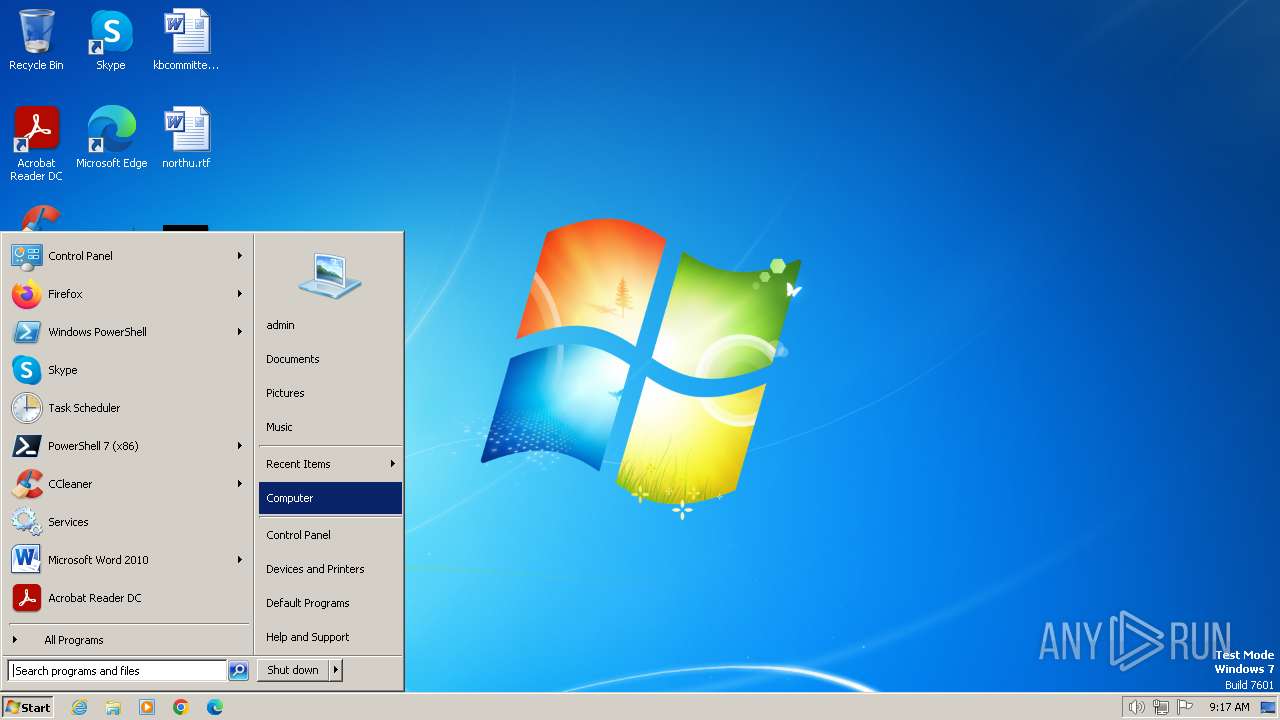
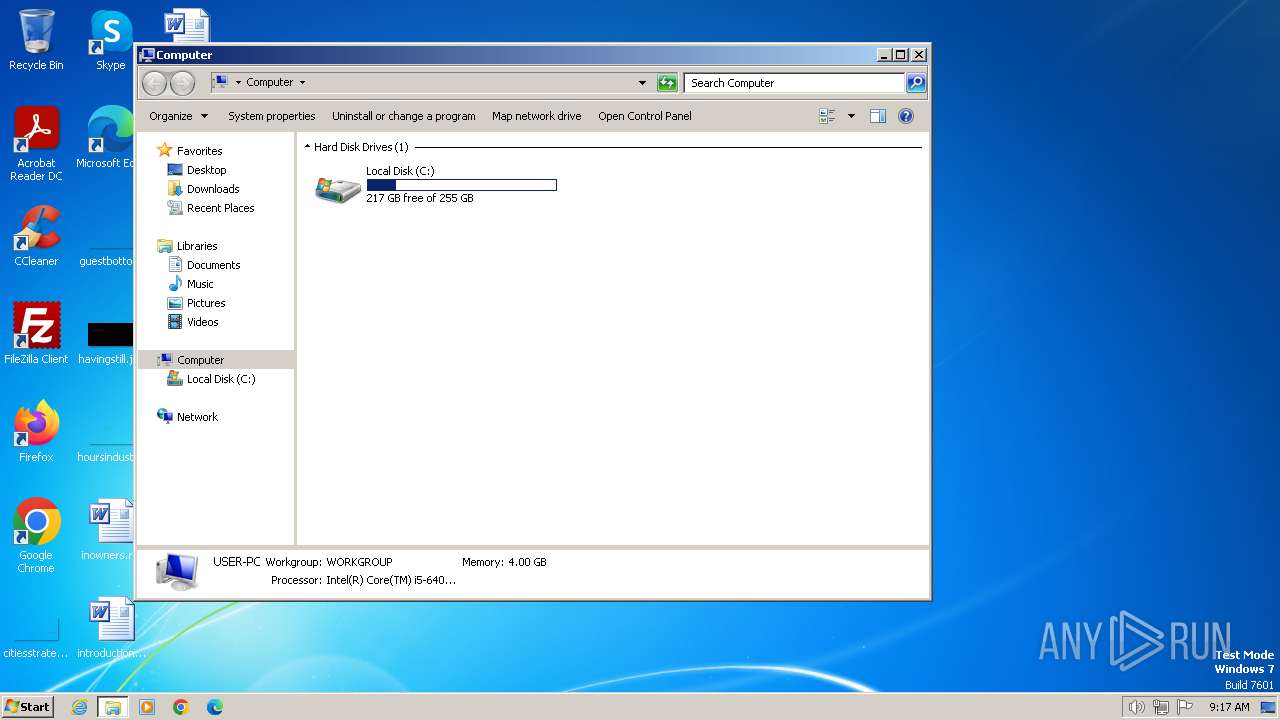
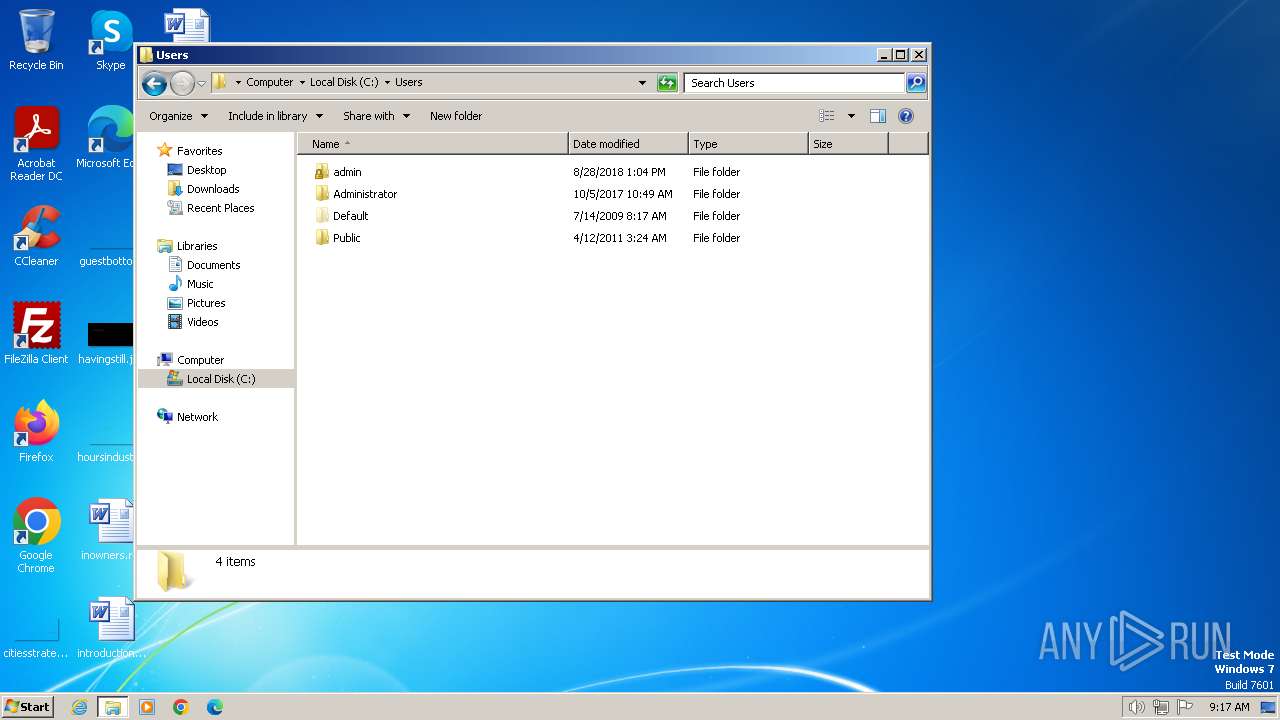
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 53C9B22CB0A40A126C8422362C2F78D8 |
| SHA1: | 0A3630B6CAB3A8658D4713F22AA66A7EB0C5D0AB |
| SHA256: | 4ECFE5DA31BA8F780BBE6A959441E9120C7C8D96D4B9EE557934E8D97C01655A |
| SSDEEP: | 48:/z2vH5s8WUdNrhGOWb/4B+GbaqoCINURMlD/x2:L2vZsKN9/m4kGzEvD/s |
MALICIOUS
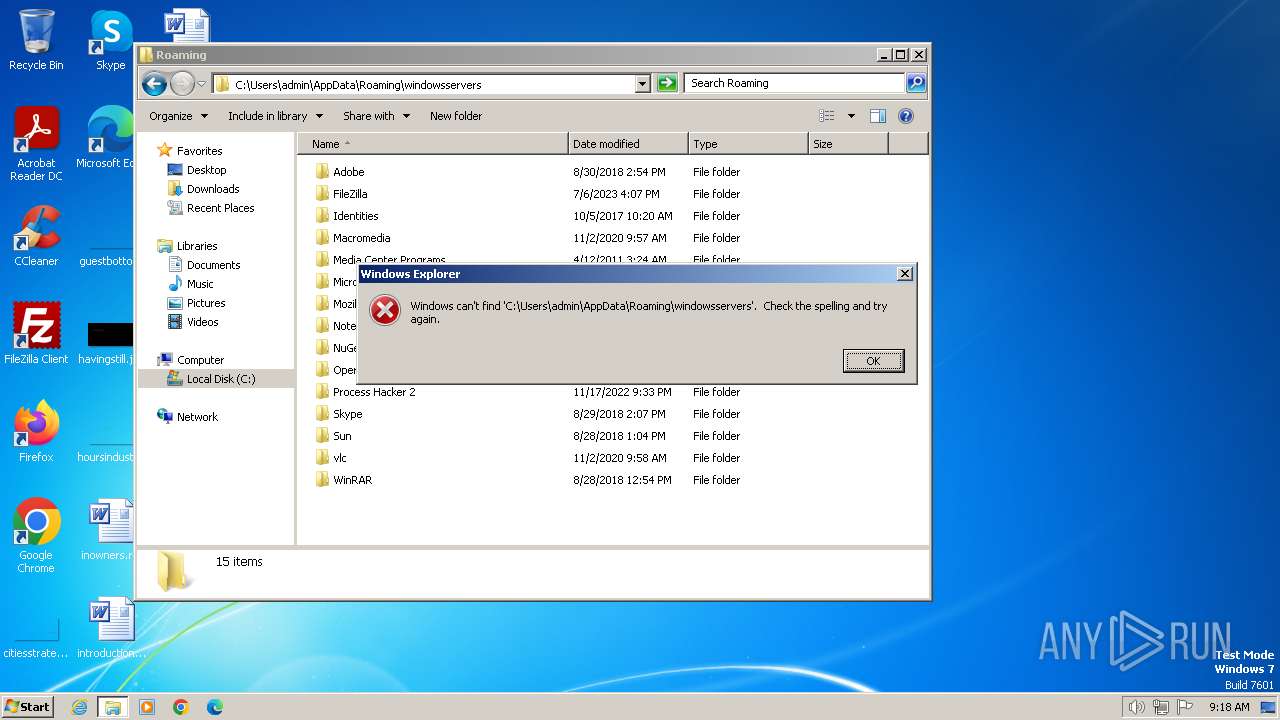
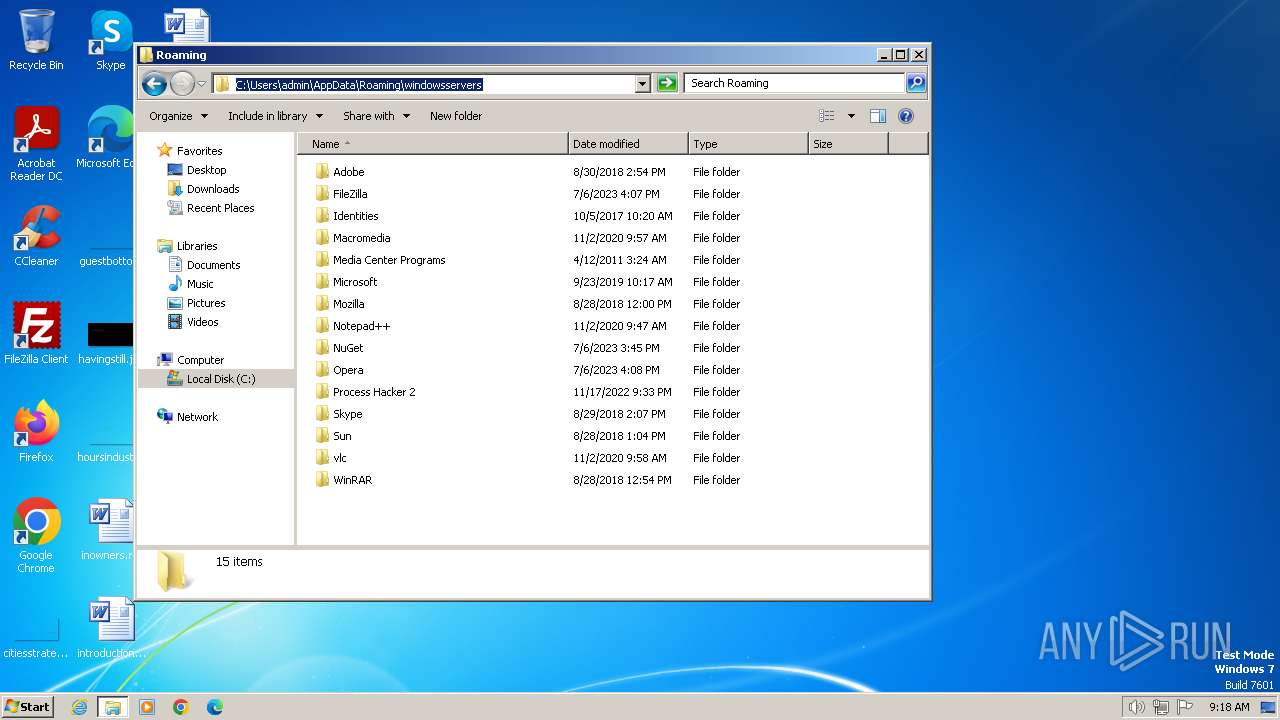
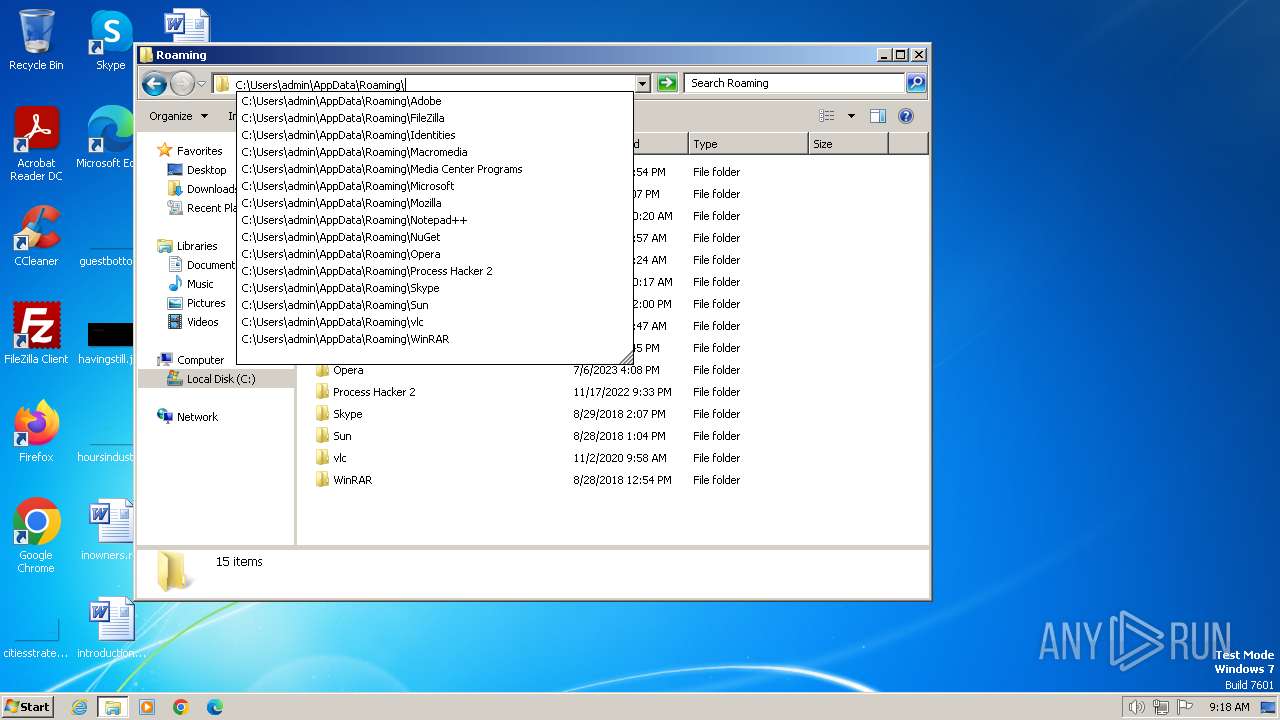
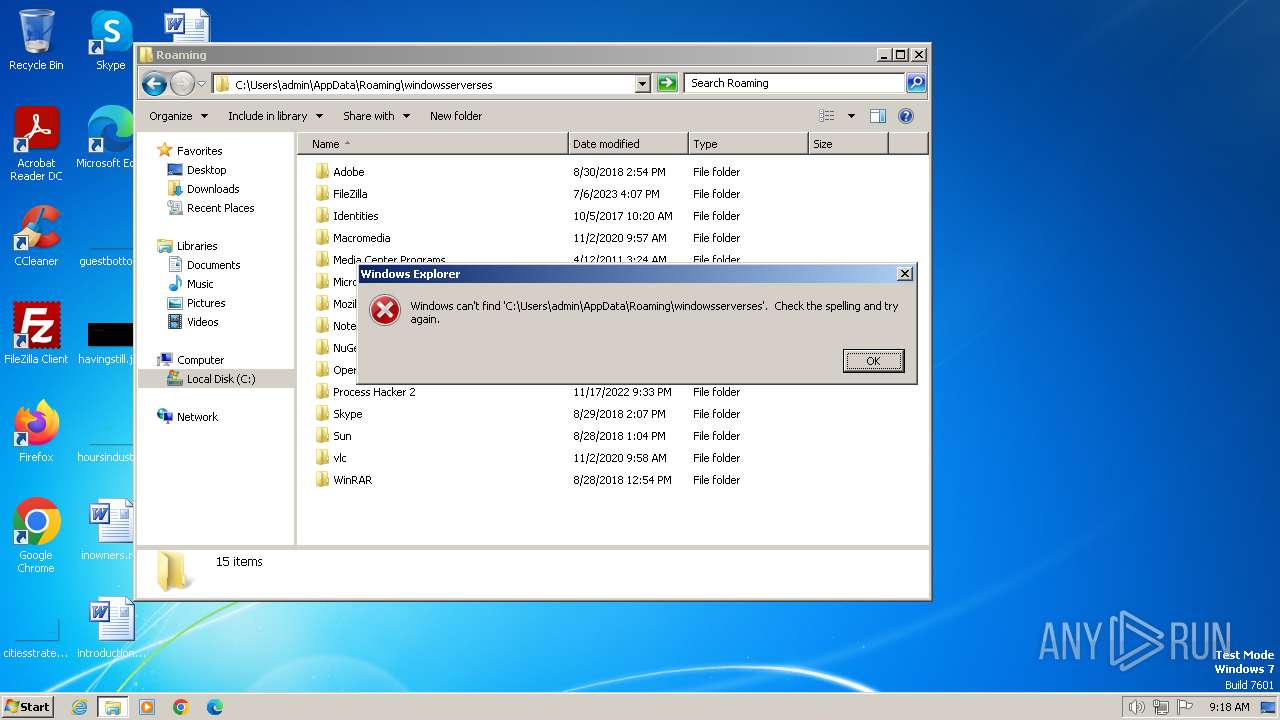
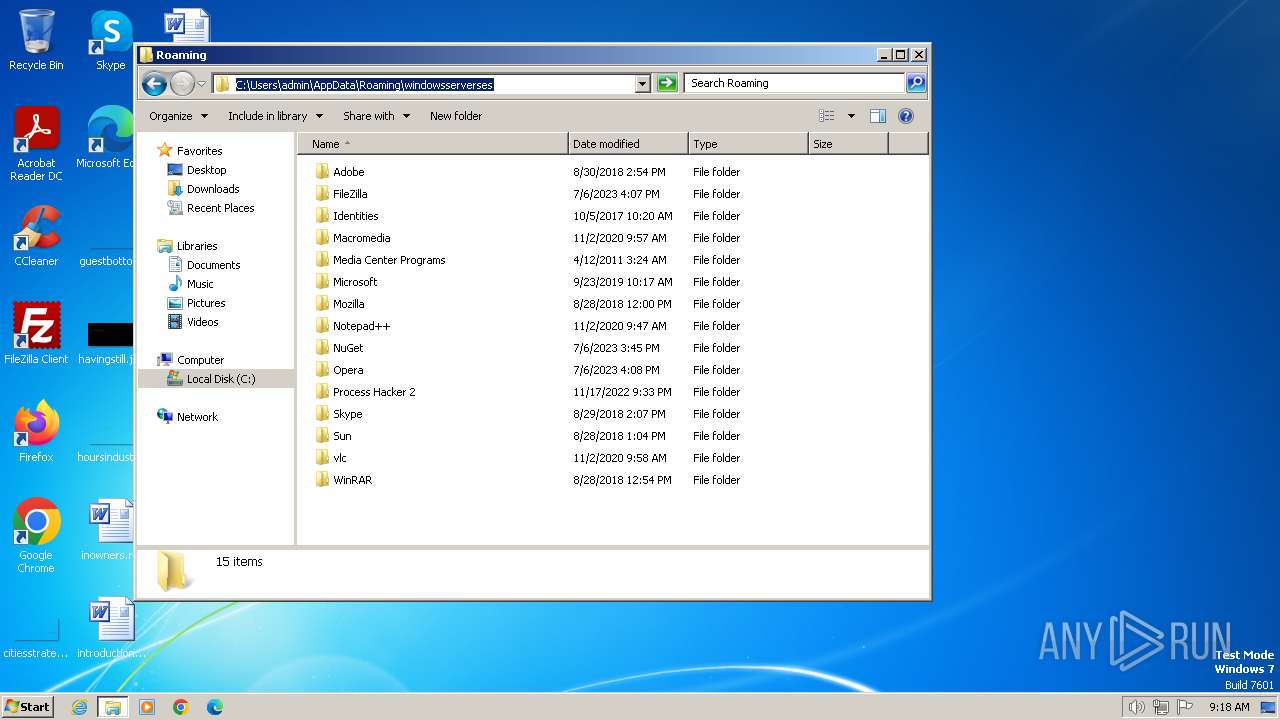
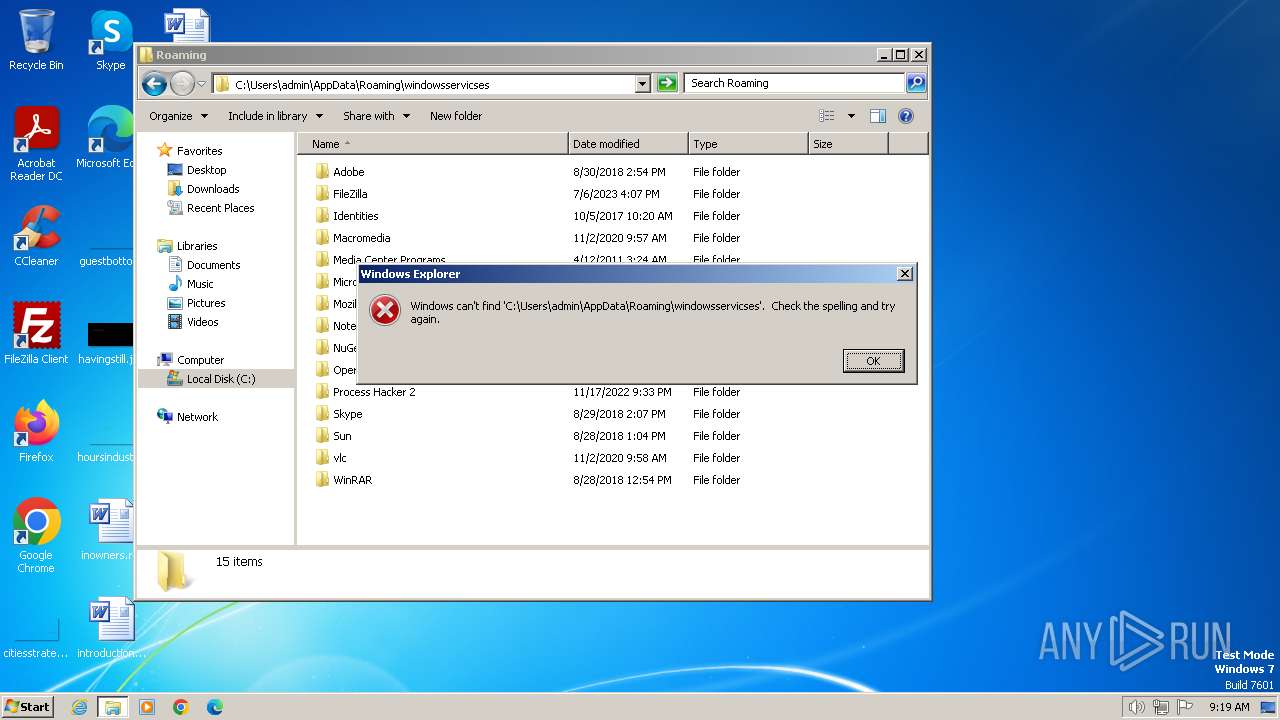
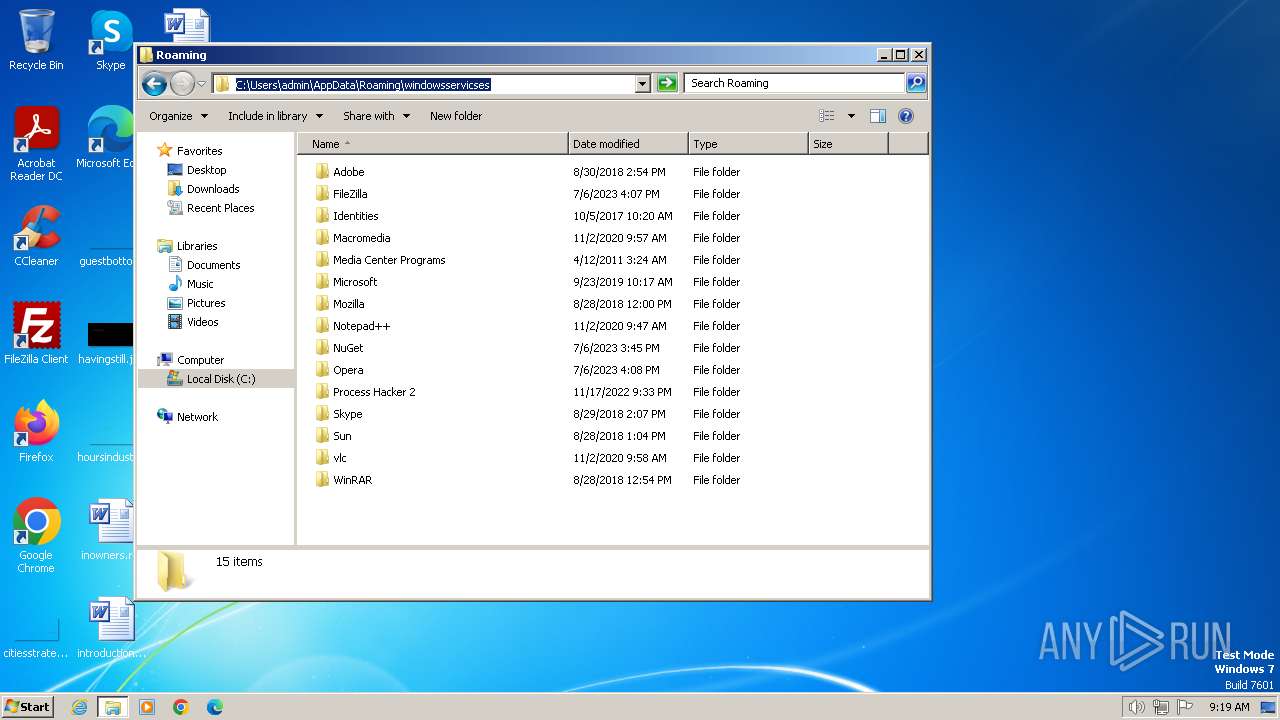
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 1380)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 1380)
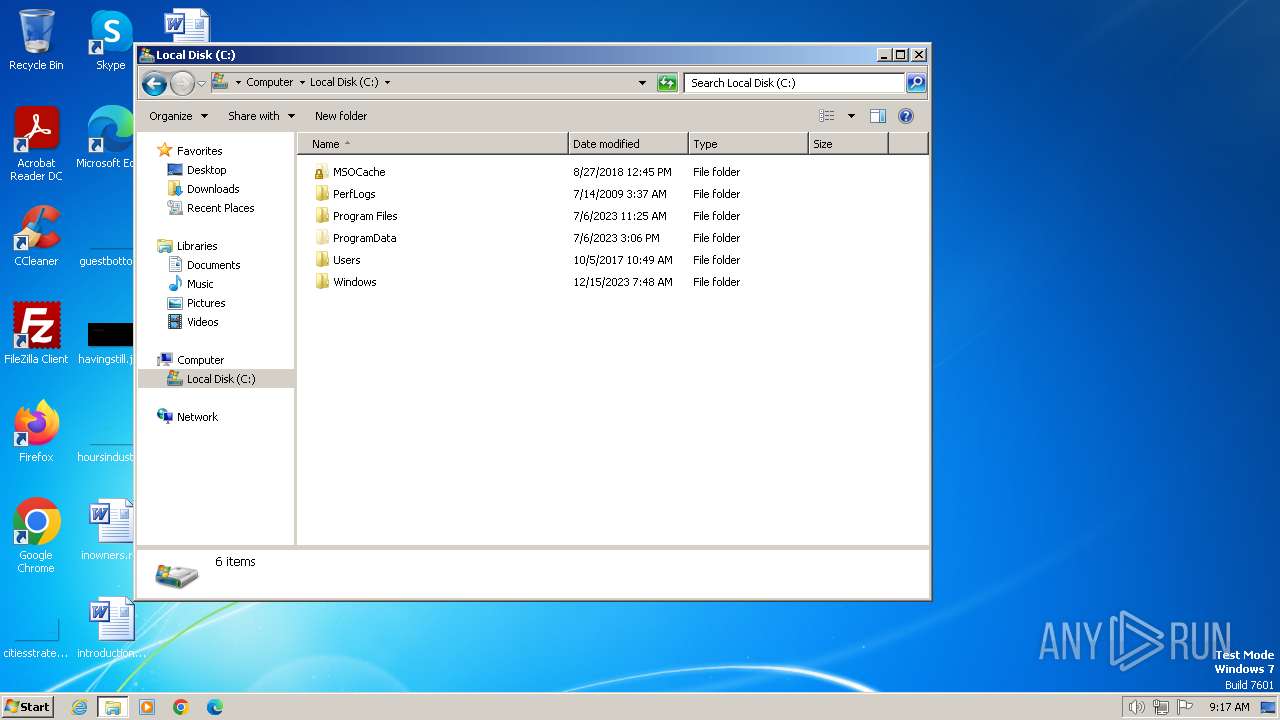
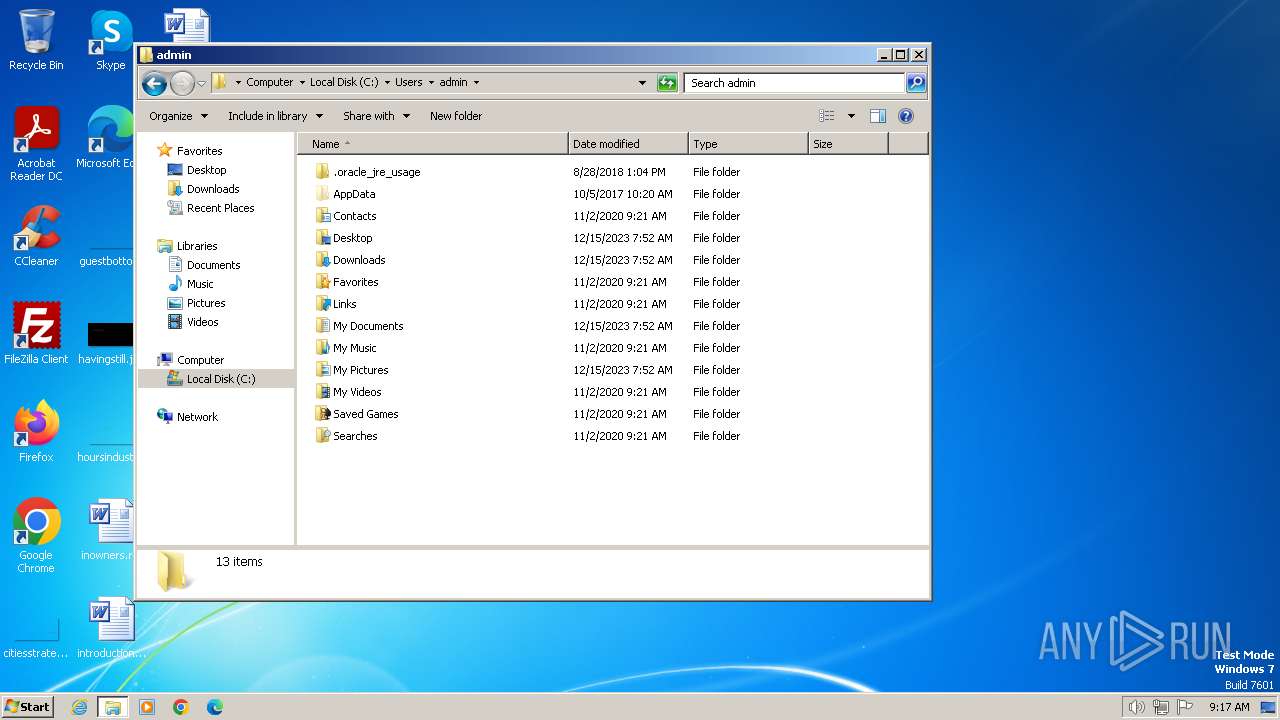
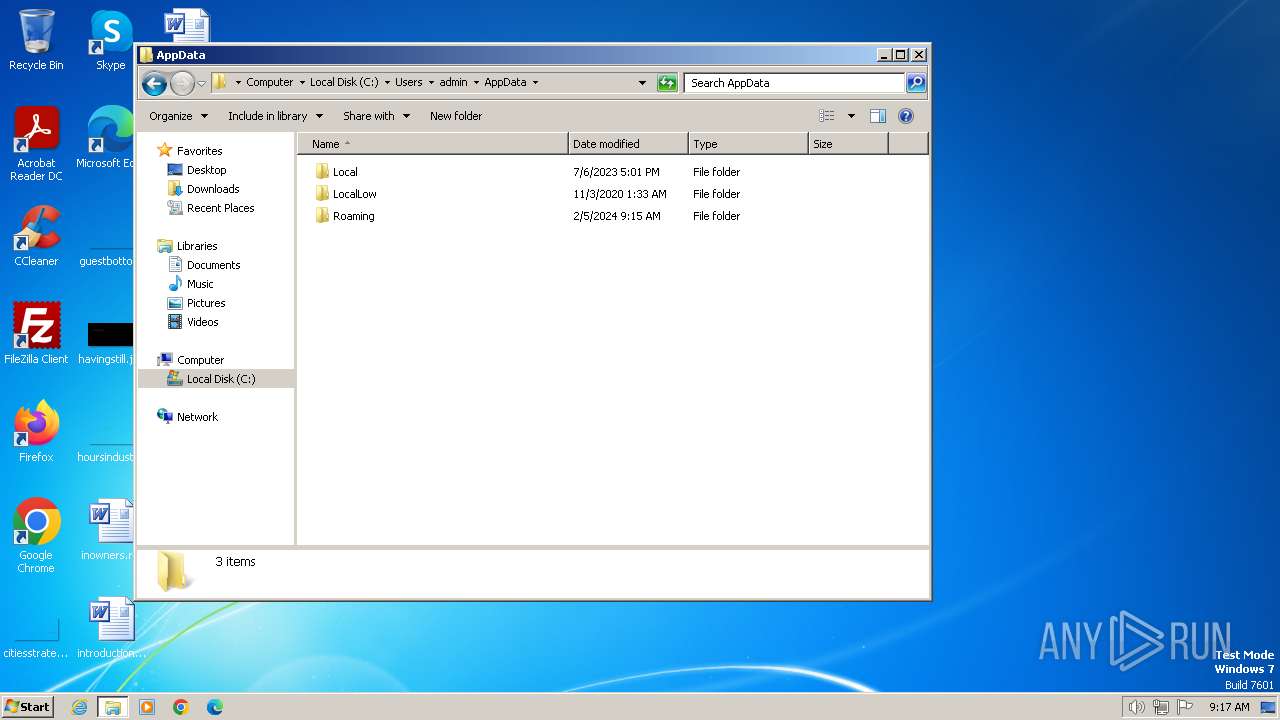
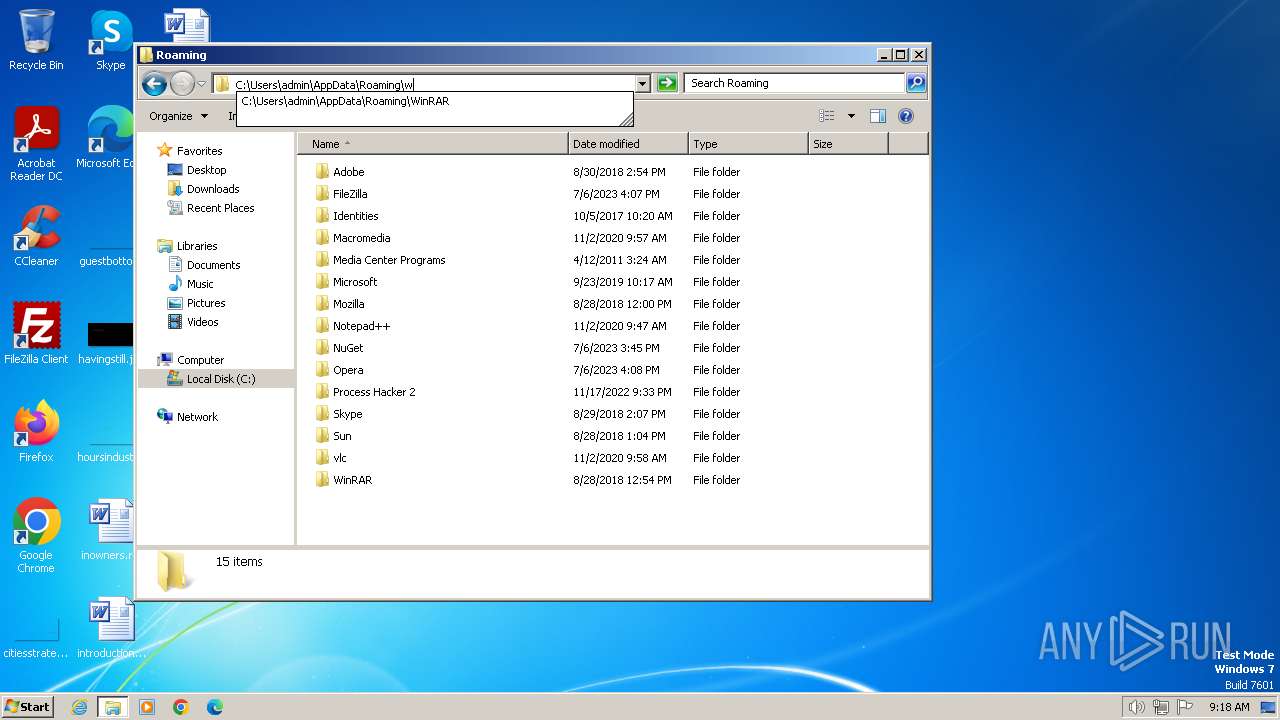
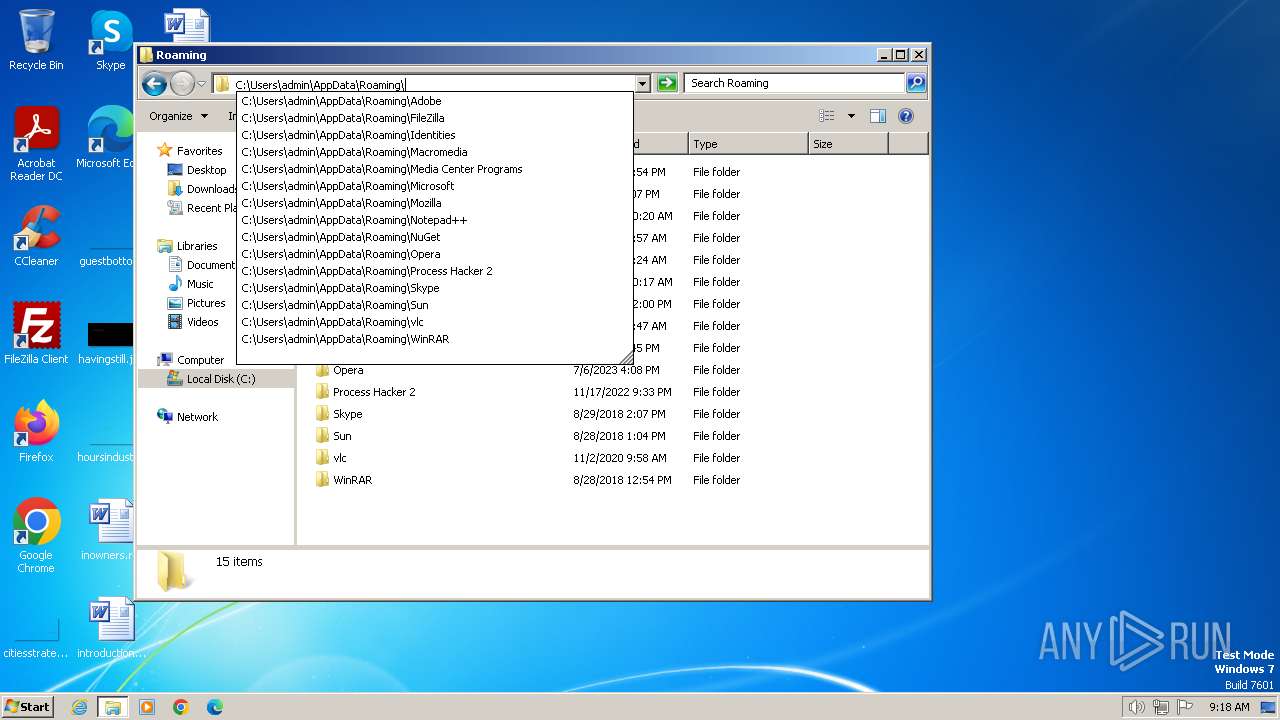
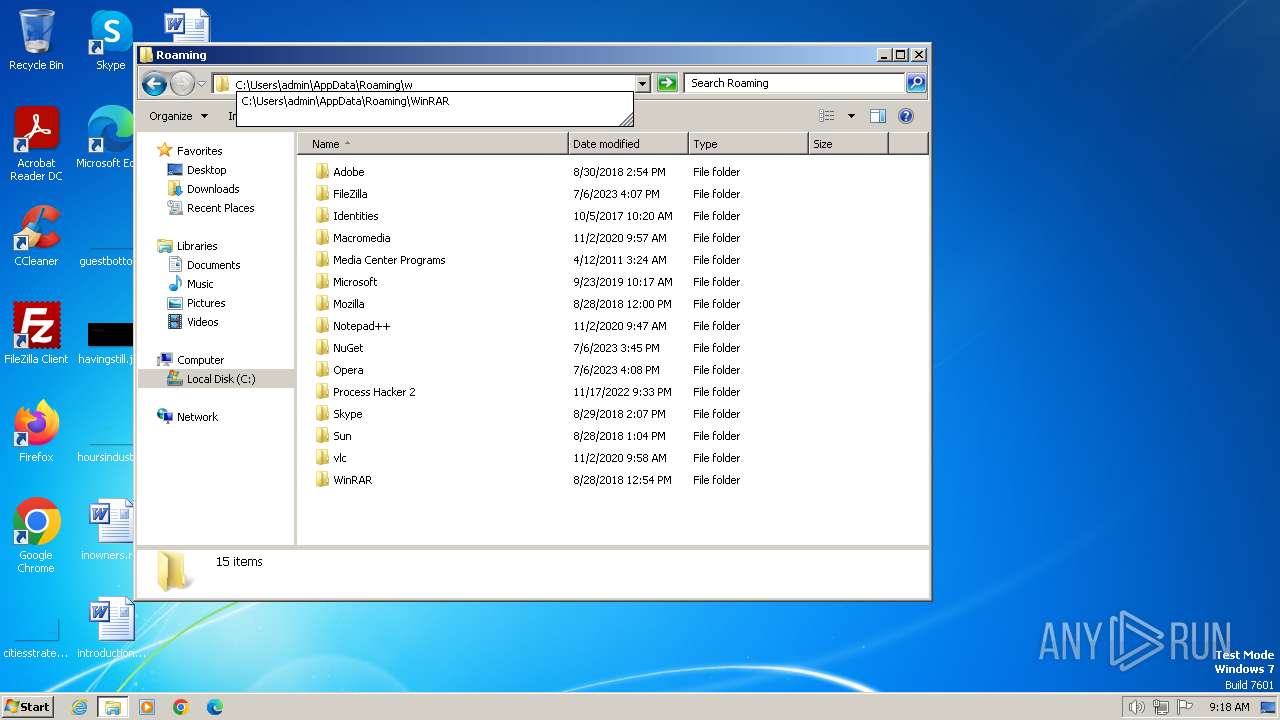
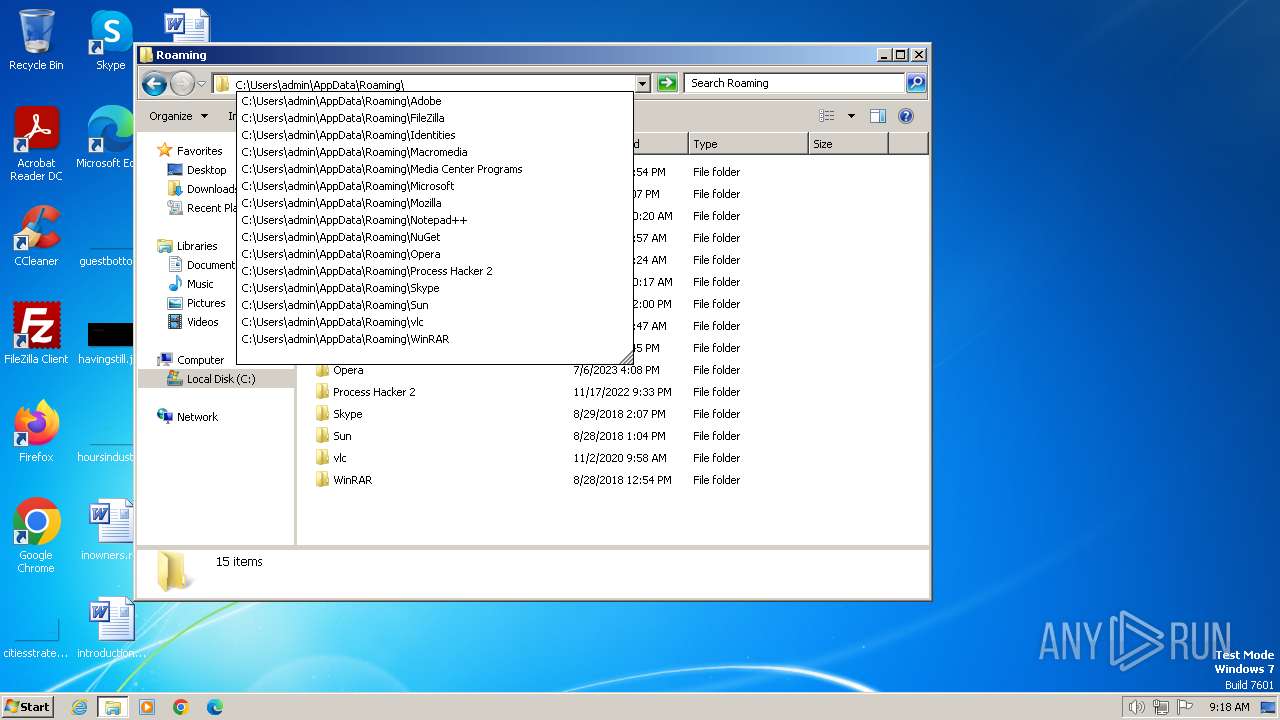
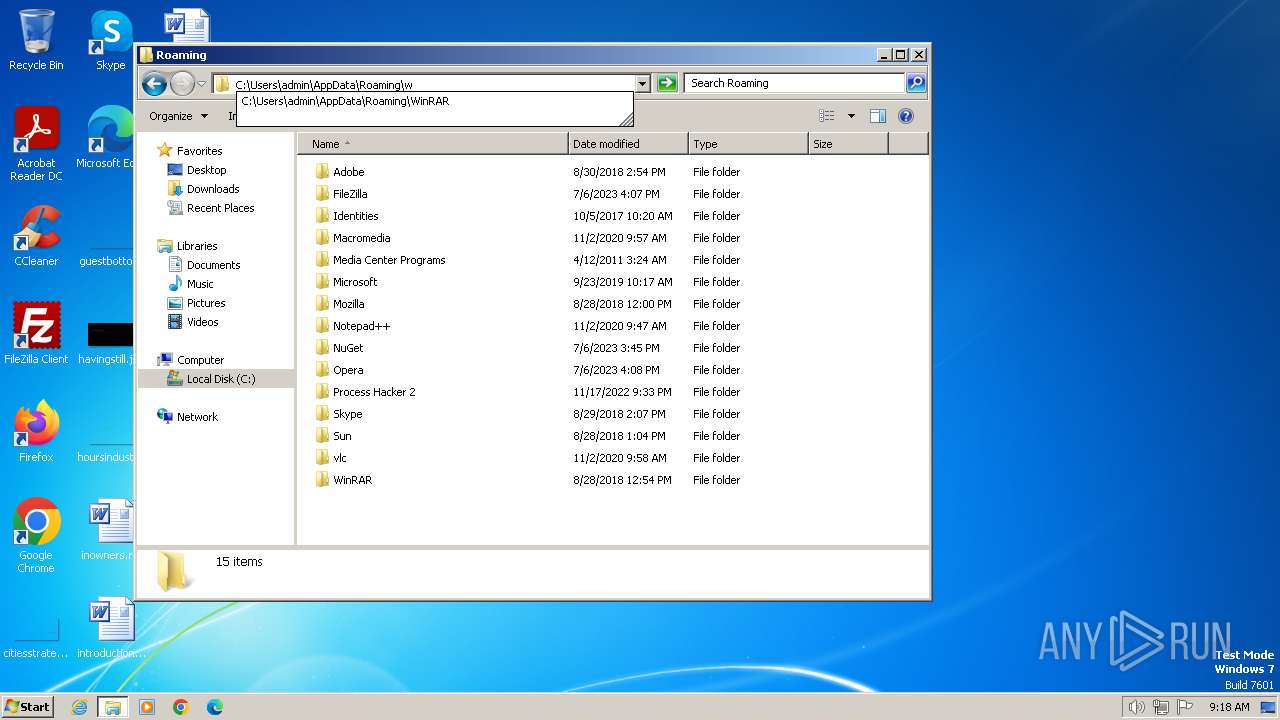
Gets %appdata% folder path (SCRIPT)
- wscript.exe (PID: 1380)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 1380)
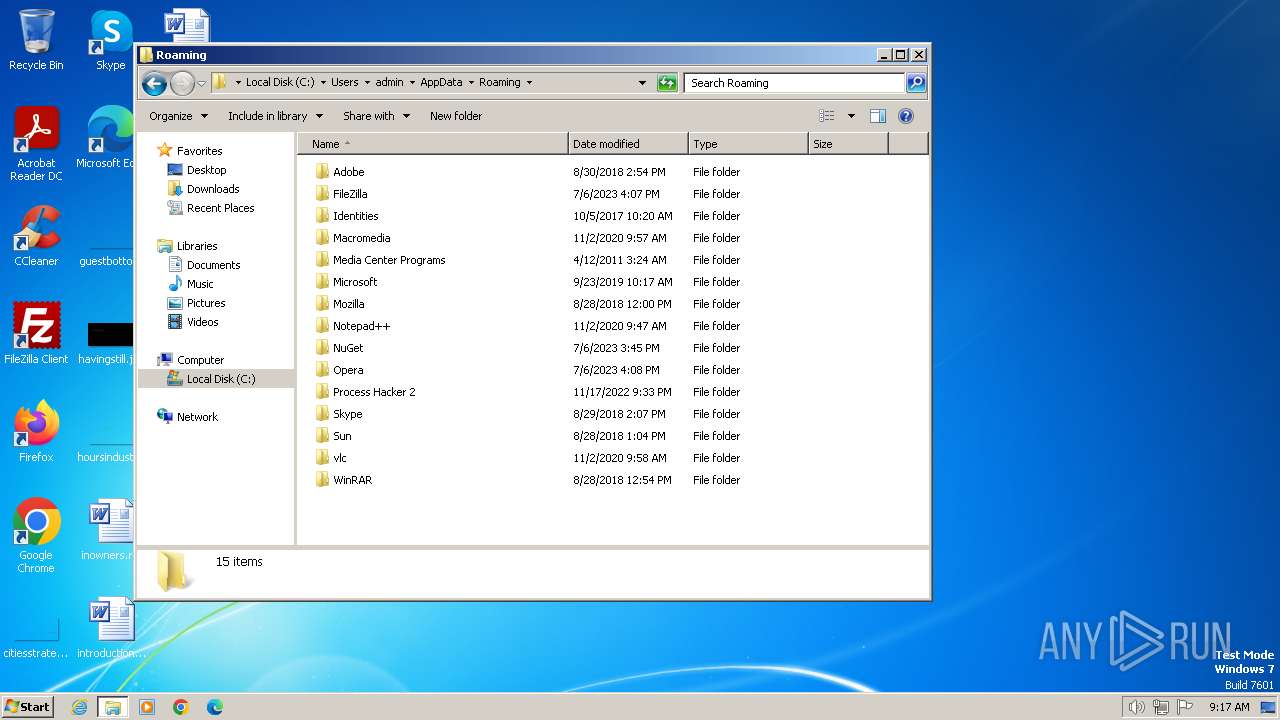
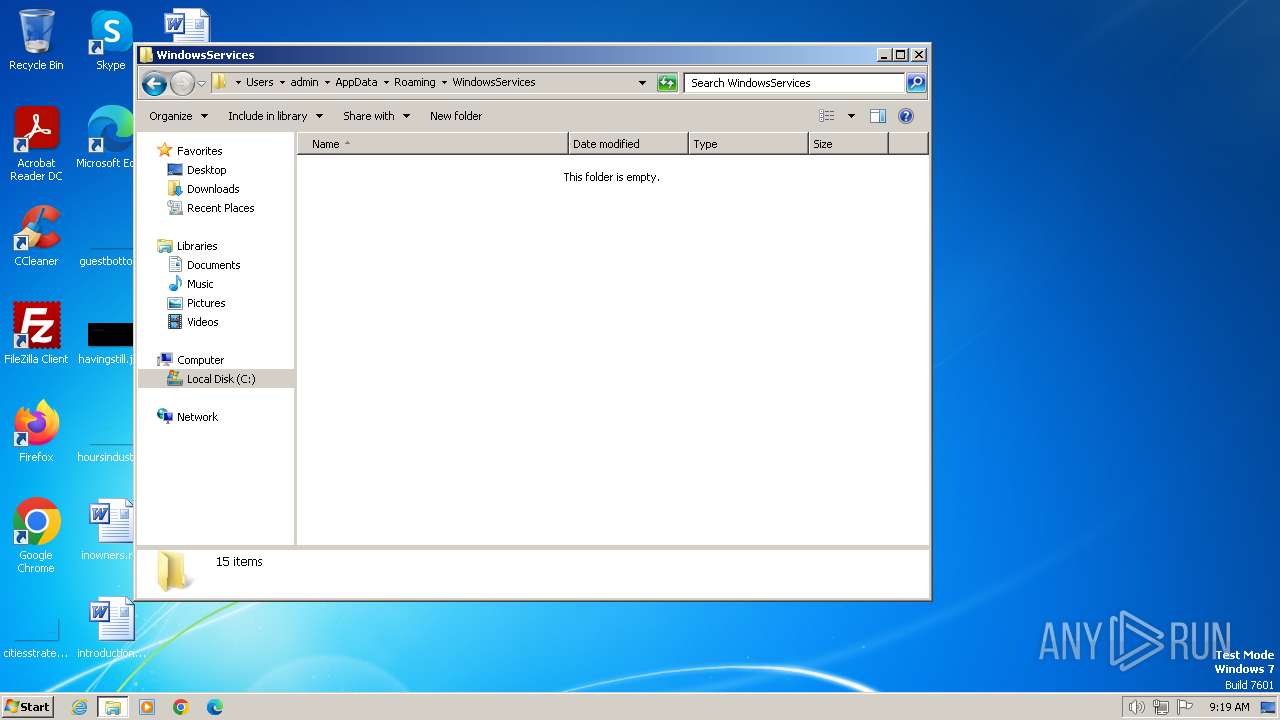
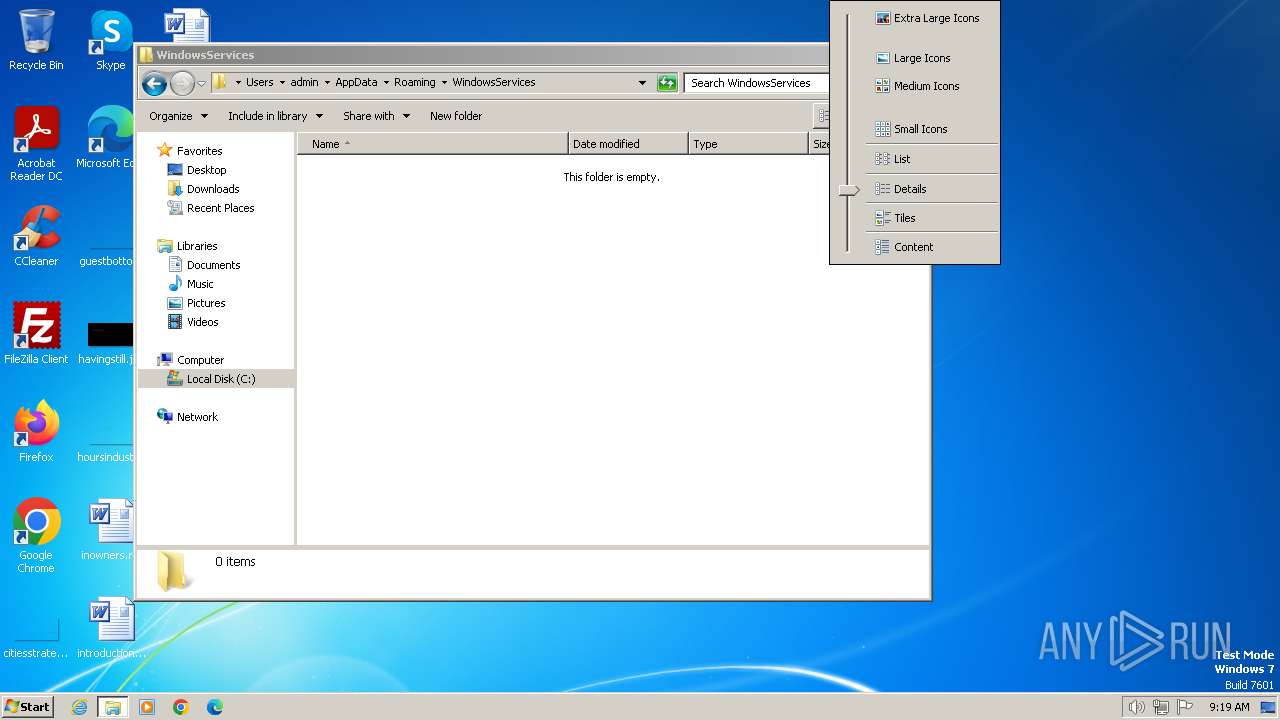
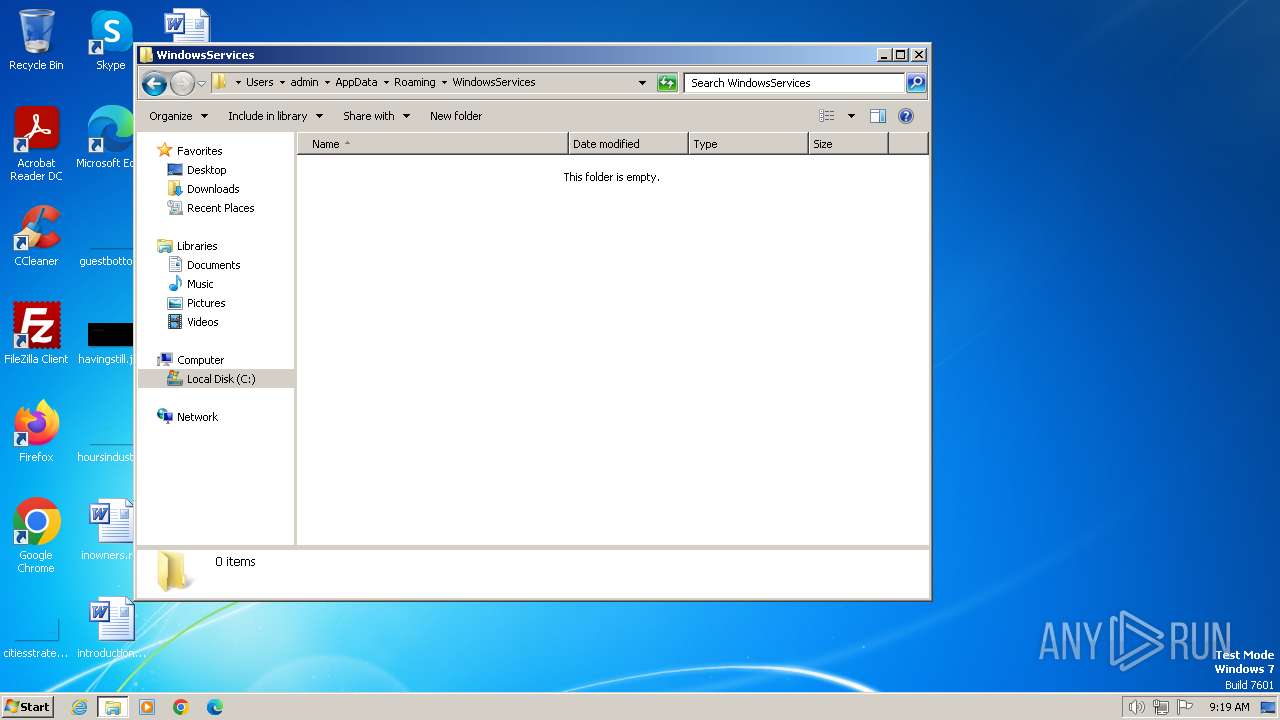
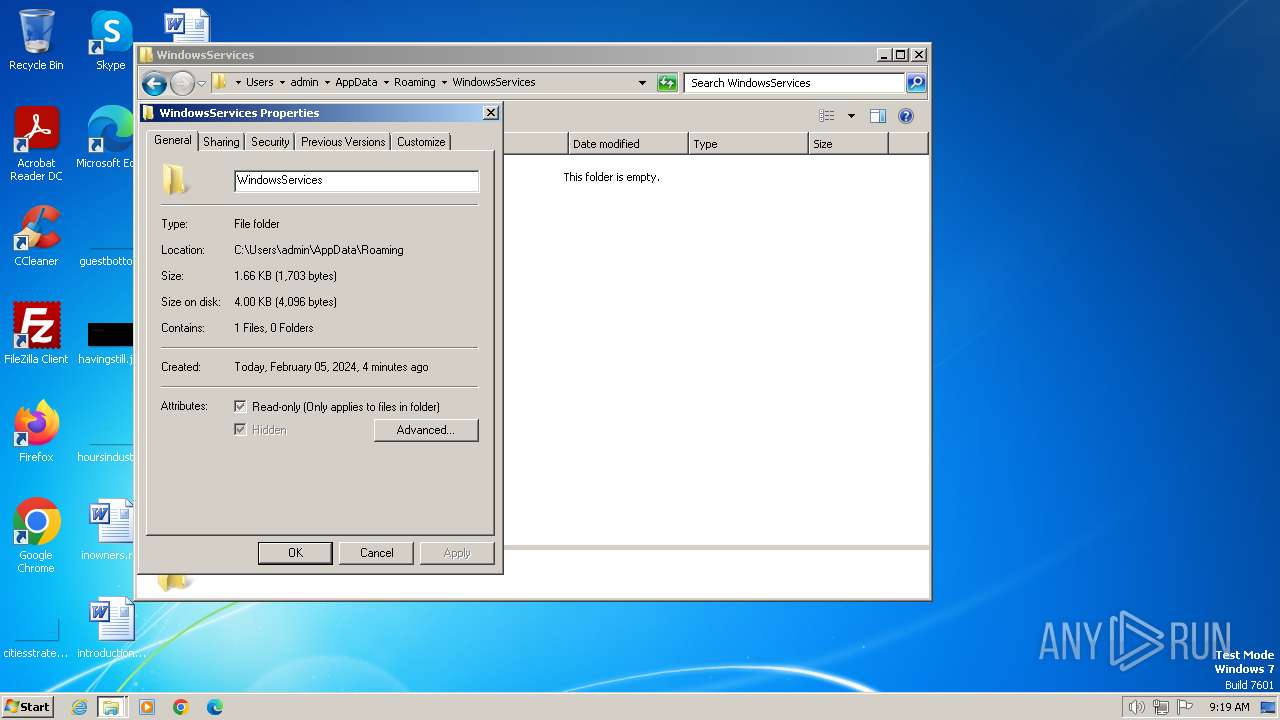
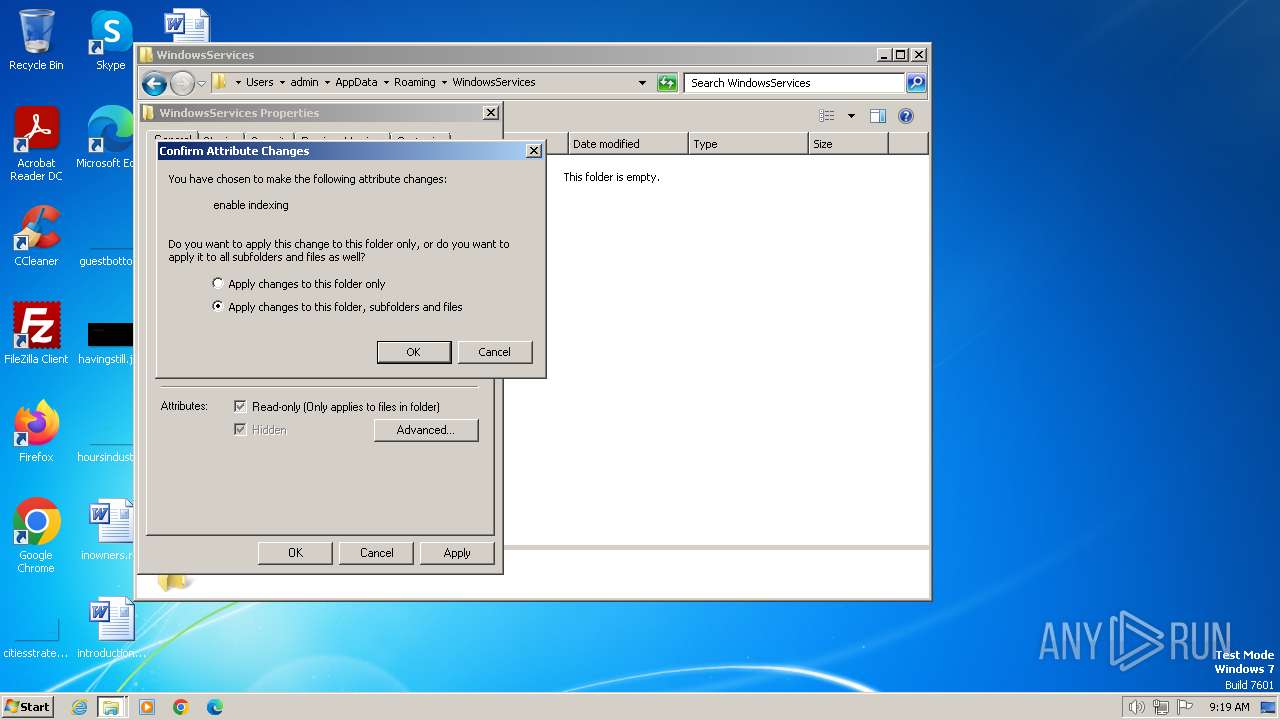
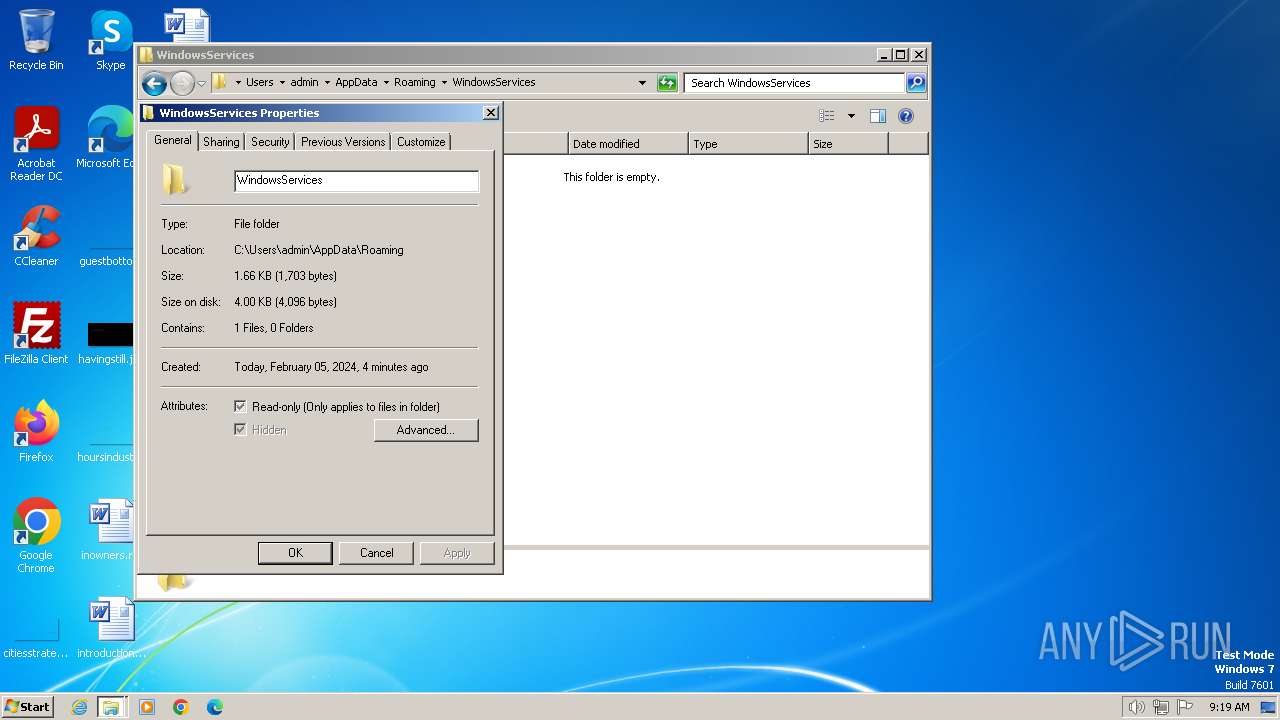
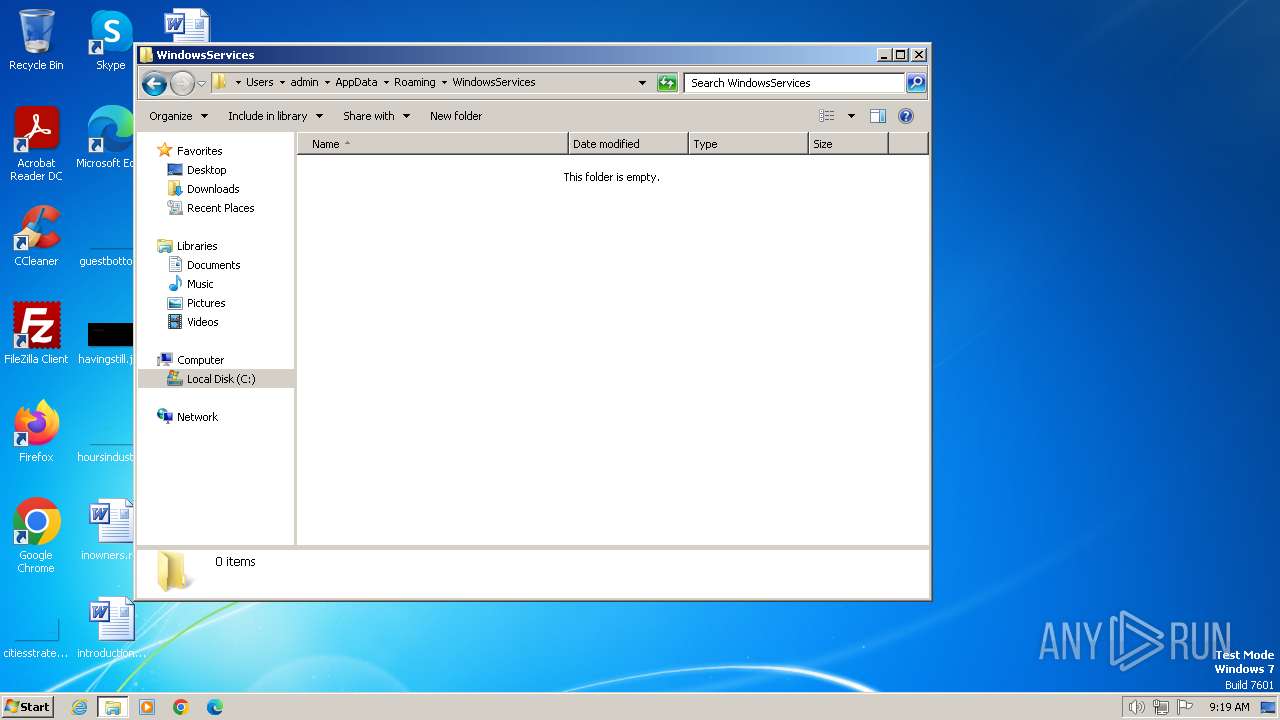
Creates a new folder (SCRIPT)
- wscript.exe (PID: 1380)
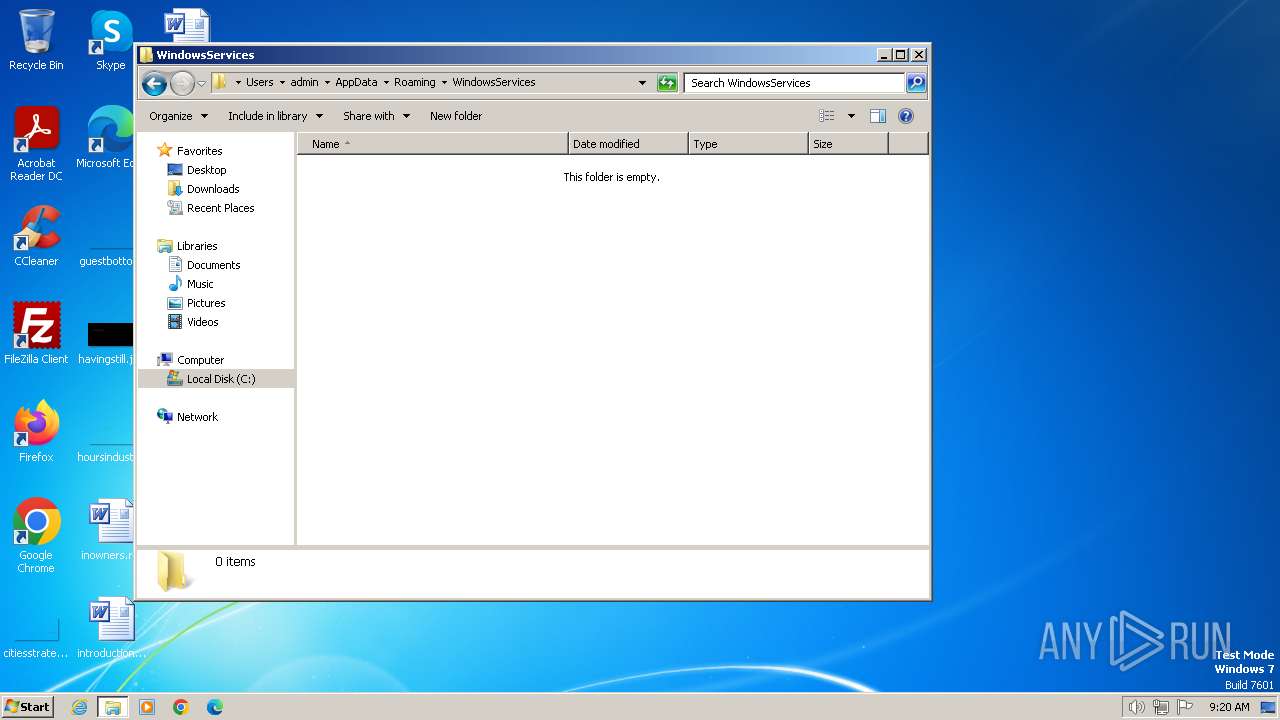
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 1380)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 1380)
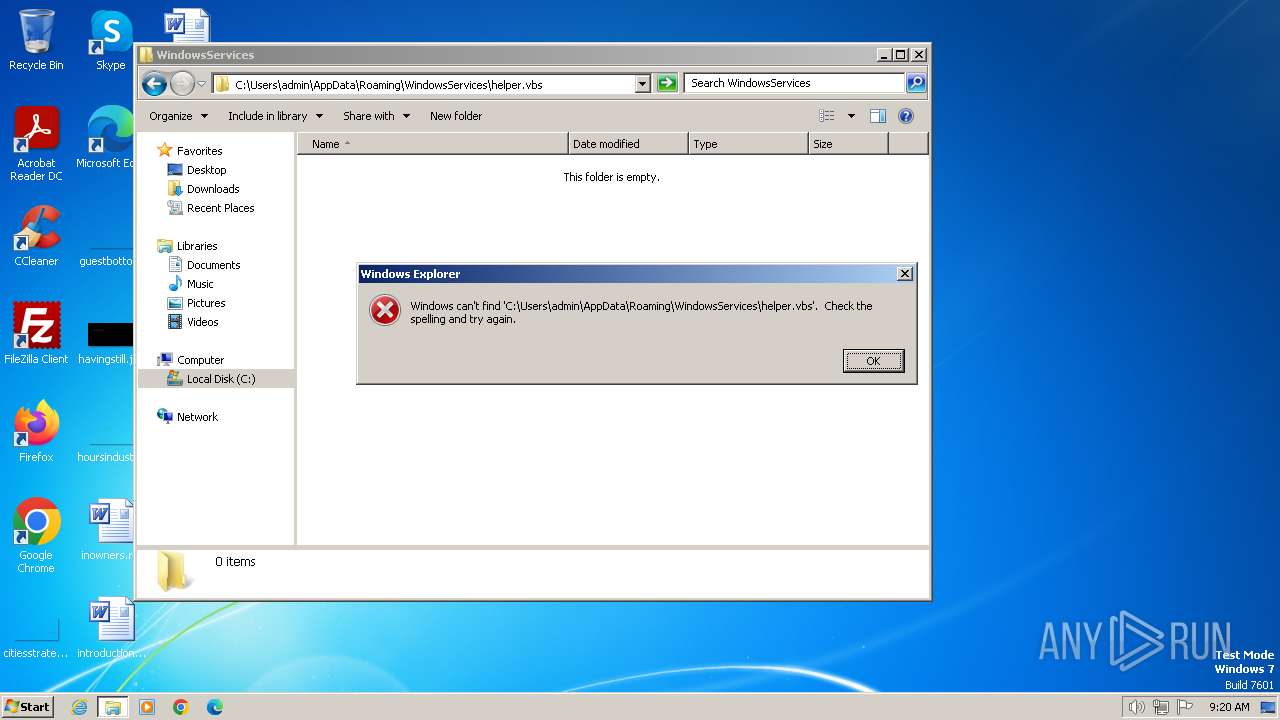
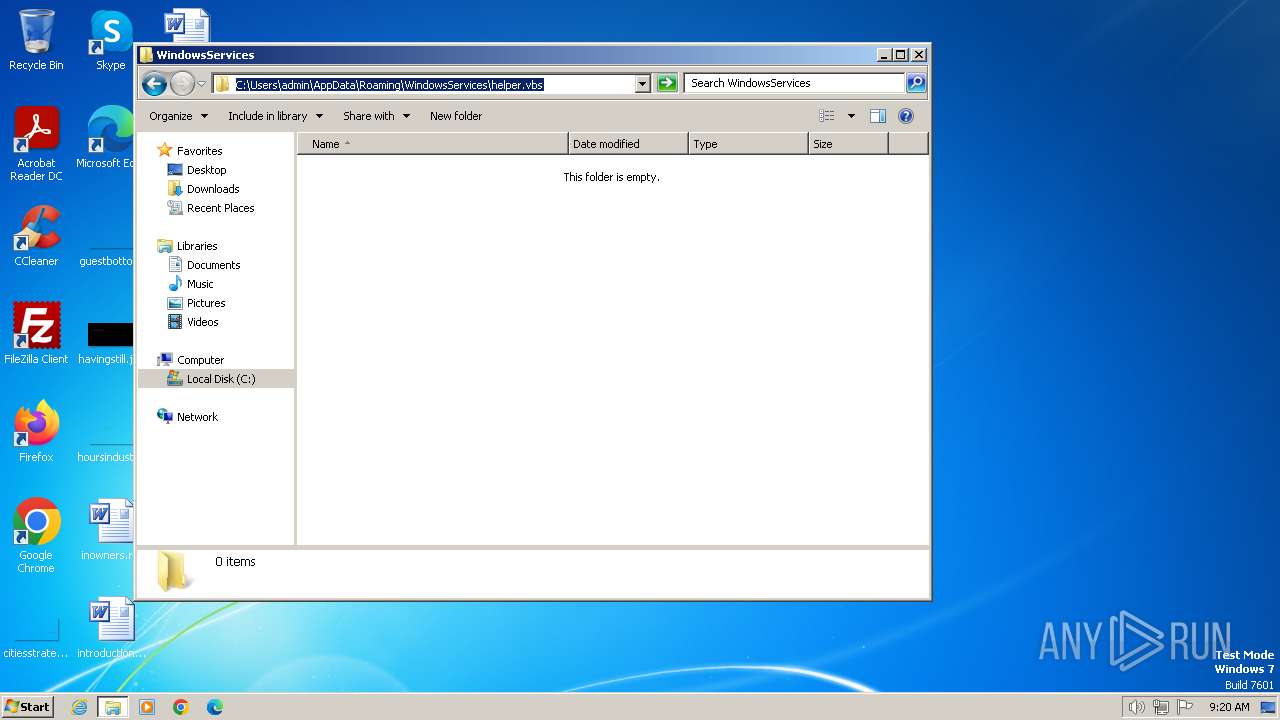
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 1380)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1380)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 1380)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 1380)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 1380)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 604)
Reads the computer name
- wmpnscfg.exe (PID: 604)
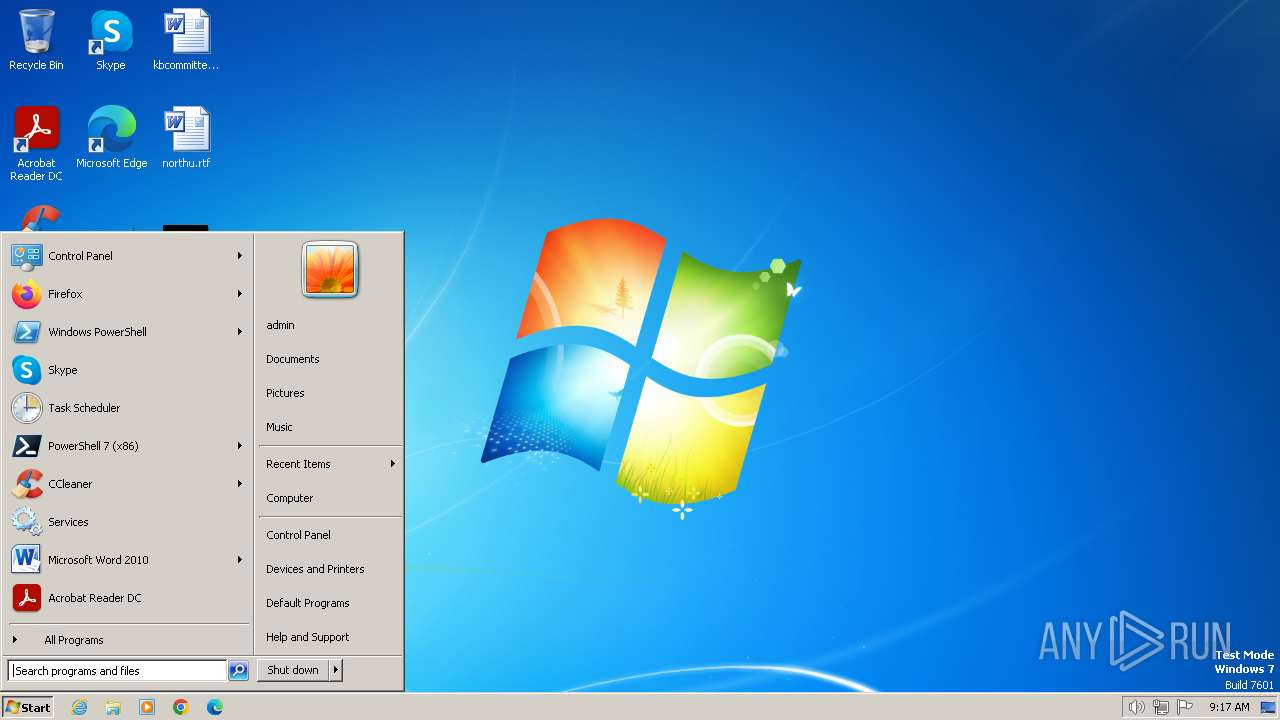
Manual execution by a user
- wmpnscfg.exe (PID: 604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\movemenoreg.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
116
Read events
116
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
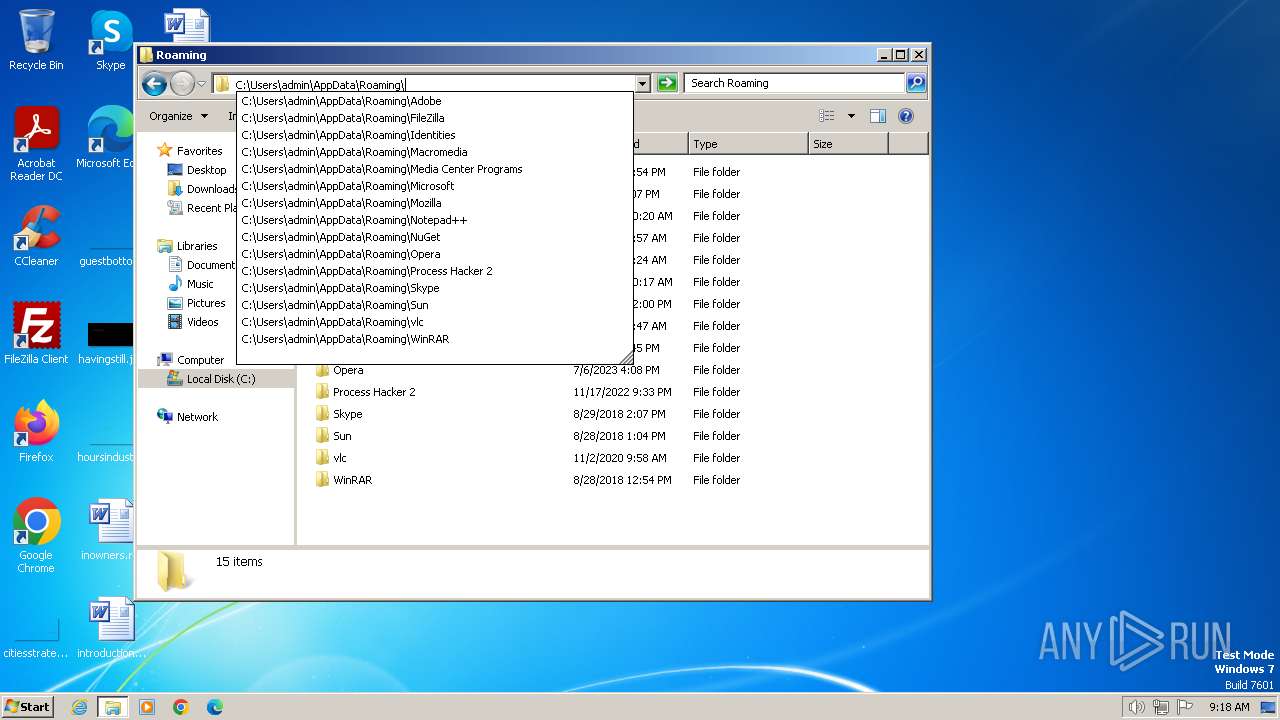
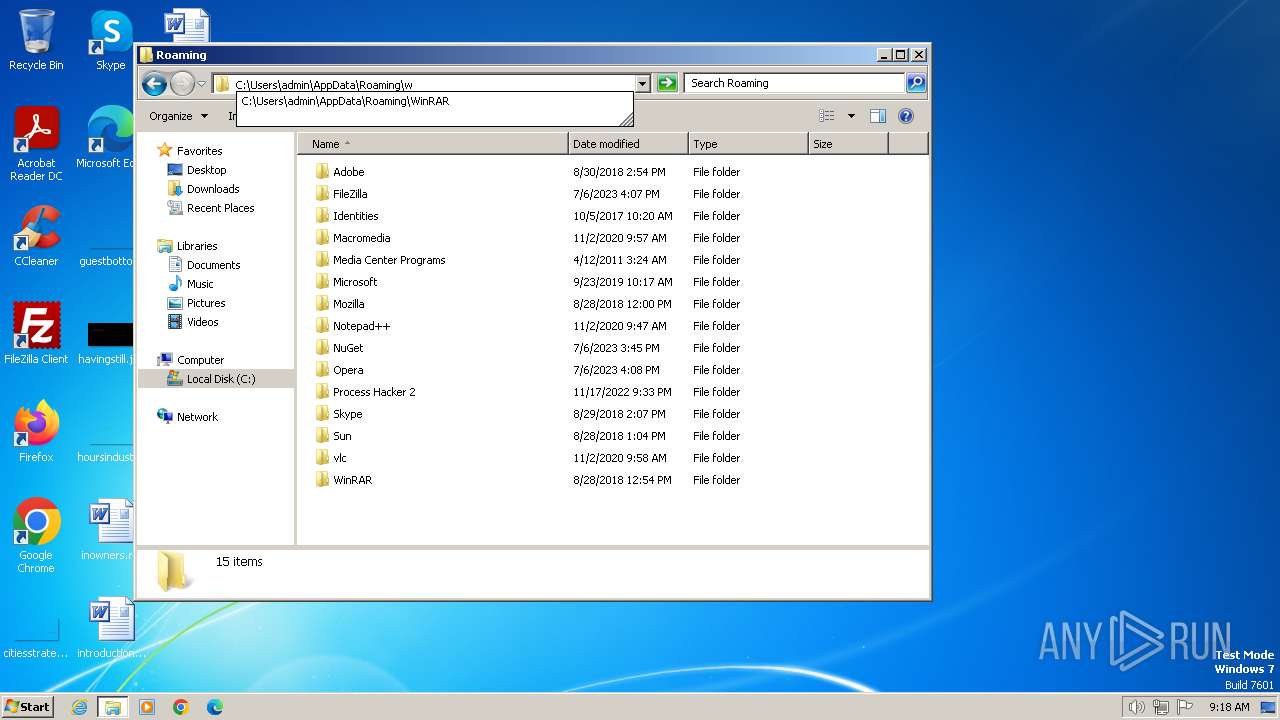
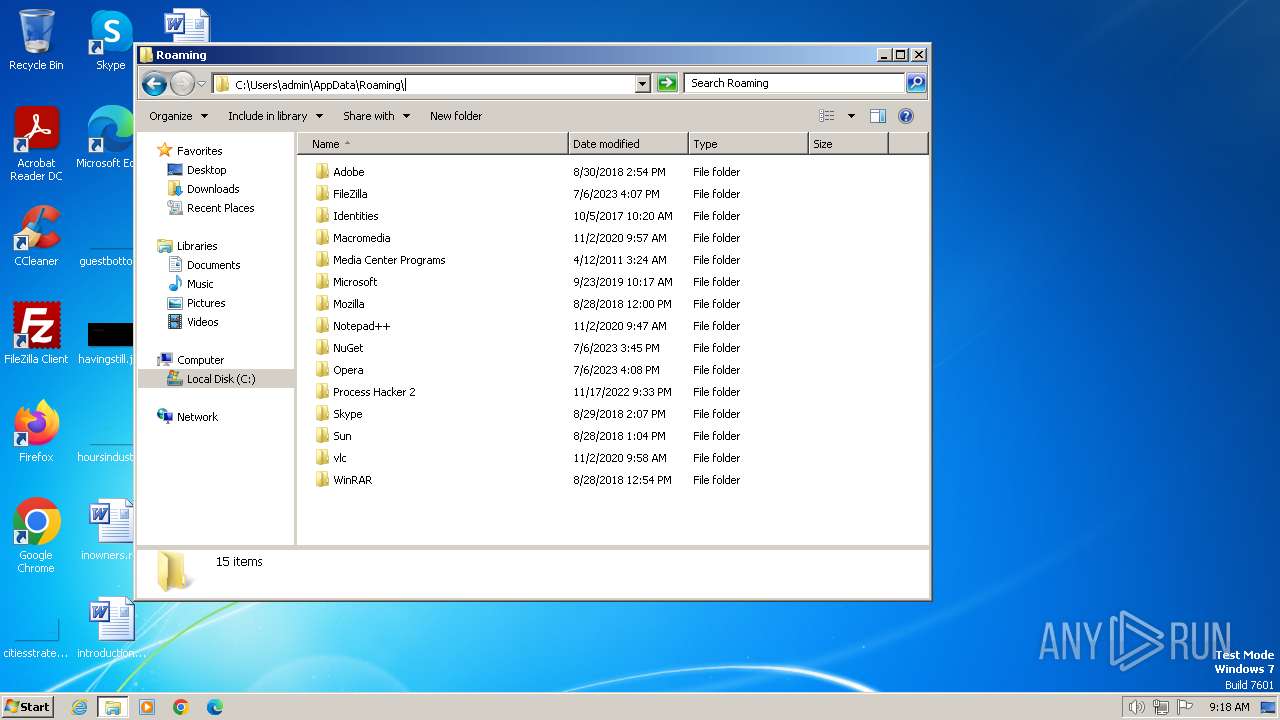
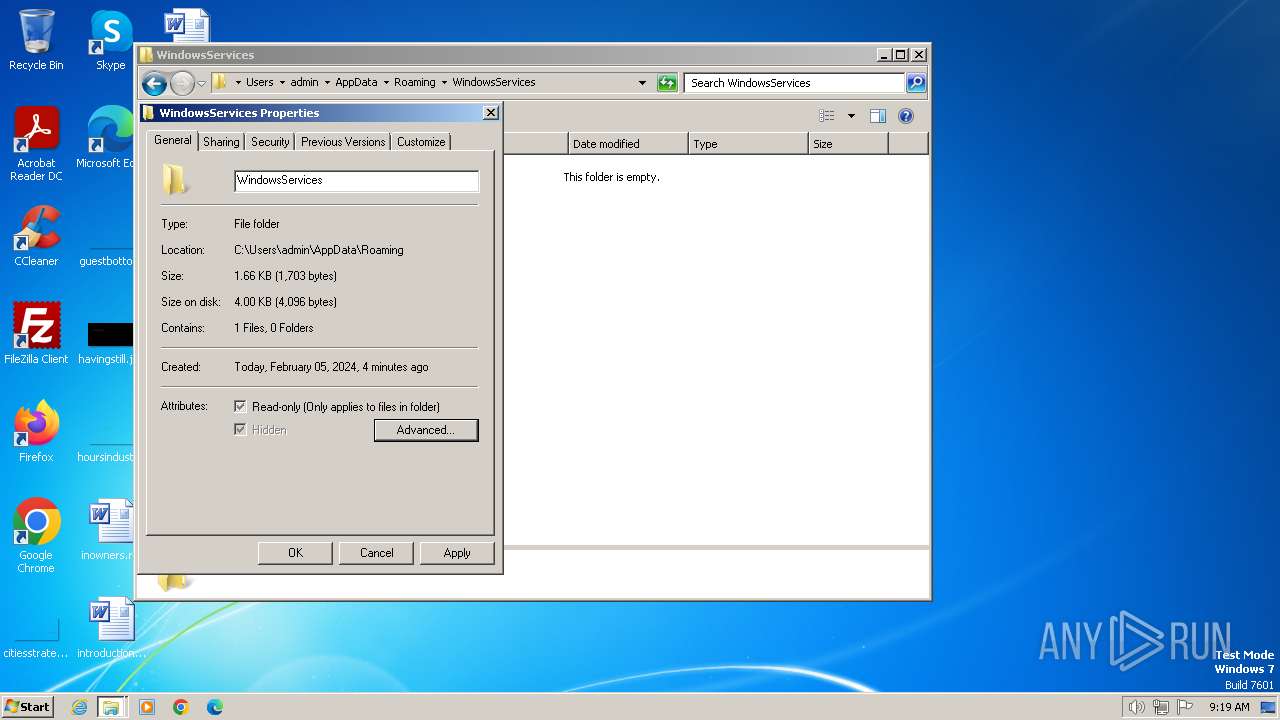
| 1380 | wscript.exe | C:\Users\admin\AppData\Roaming\WindowsServices\movemenoreg.vbs | text | |
MD5:53C9B22CB0A40A126C8422362C2F78D8 | SHA256:4ECFE5DA31BA8F780BBE6A959441E9120C7C8D96D4B9EE557934E8D97C01655A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |