| File name: | 000.exe |
| Full analysis: | https://app.any.run/tasks/149e4243-6082-440e-9ff4-9ad59eede66f |
| Verdict: | Malicious activity |
| Analysis date: | April 24, 2019, 23:06:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | F2B7074E1543720A9A98FDA660E02688 |
| SHA1: | 1029492C1A12789D8AF78D54ADCB921E24B9E5CA |
| SHA256: | 4EA1F2ECF7EB12896F2CBF8683DAE8546D2B8DC43CF7710D68CE99E127C0A966 |
| SSDEEP: | 3072:eaLA1++iCeFj0im6X/AXpT8vVMCcHVcdhghUuz1o9Y:fLJlC6j0CX4XmvWHVcd62uO9 |
MALICIOUS
Task Manager has been disabled (taskmgr)
- 000.exe (PID: 3548)
Changes the login/logoff helper path in the registry
- 000.exe (PID: 3548)
Writes to a start menu file
- cmd.exe (PID: 2164)
SUSPICIOUS
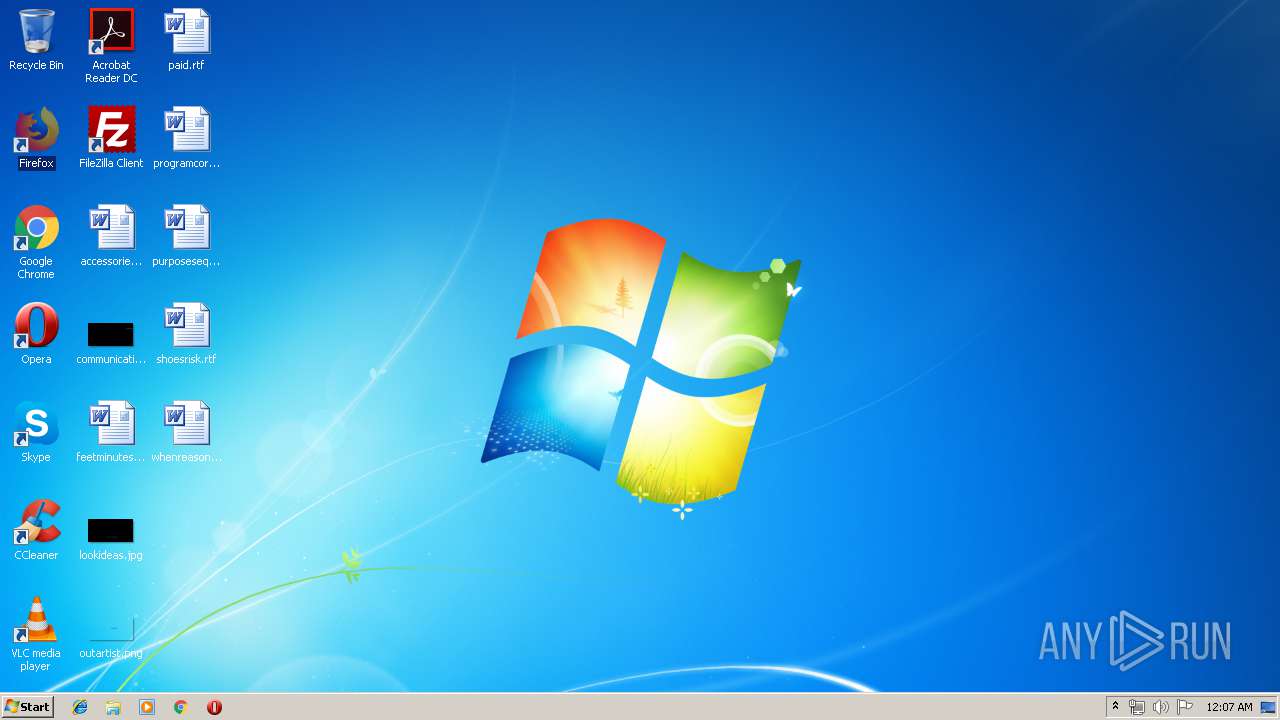
Changes the desktop background image
- 000.exe (PID: 3548)
Executable content was dropped or overwritten
- 000.exe (PID: 3548)
- cmd.exe (PID: 2164)
Starts CMD.EXE for commands execution
- 000.exe (PID: 3548)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2164)
Creates files in the program directory
- cmd.exe (PID: 2164)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:09:22 15:02:11+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 6978560 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6a9a8e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | 000 |
| FileVersion: | 0.0.0.0 |
| InternalName: | 000.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | 000.exe |
| ProductName: | 000 |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Sep-2016 13:02:11 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | 000 |
| FileVersion: | 0.0.0.0 |
| InternalName: | 000.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | 000.exe |
| ProductName: | 000 |
| ProductVersion: | 0.0.0.0 |
| Assembly Version: | 0.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 22-Sep-2016 13:02:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x006A7A94 | 0x006A7C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.751954 |
.rsrc | 0x006AA000 | 0x00000FD8 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.03405 |
.reloc | 0x006AC000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.0055 | 3174 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
43
Monitored processes
8
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2164 | cmd /c ""C:\Users\admin\AppData\Local\Temp\windl.bat"" | C:\Windows\system32\cmd.exe | 000.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2664 | "C:\Users\admin\AppData\Local\Temp\000.exe" | C:\Users\admin\AppData\Local\Temp\000.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 000 Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2744 | wmic useraccount where name='admin' set FullName='UR NEXT' | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2840 | taskkill /f /im explorer.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2920 | wmic useraccount where name='admin' rename 'UR NEXT' | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3548 | "C:\Users\admin\AppData\Local\Temp\000.exe" | C:\Users\admin\AppData\Local\Temp\000.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 000 Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
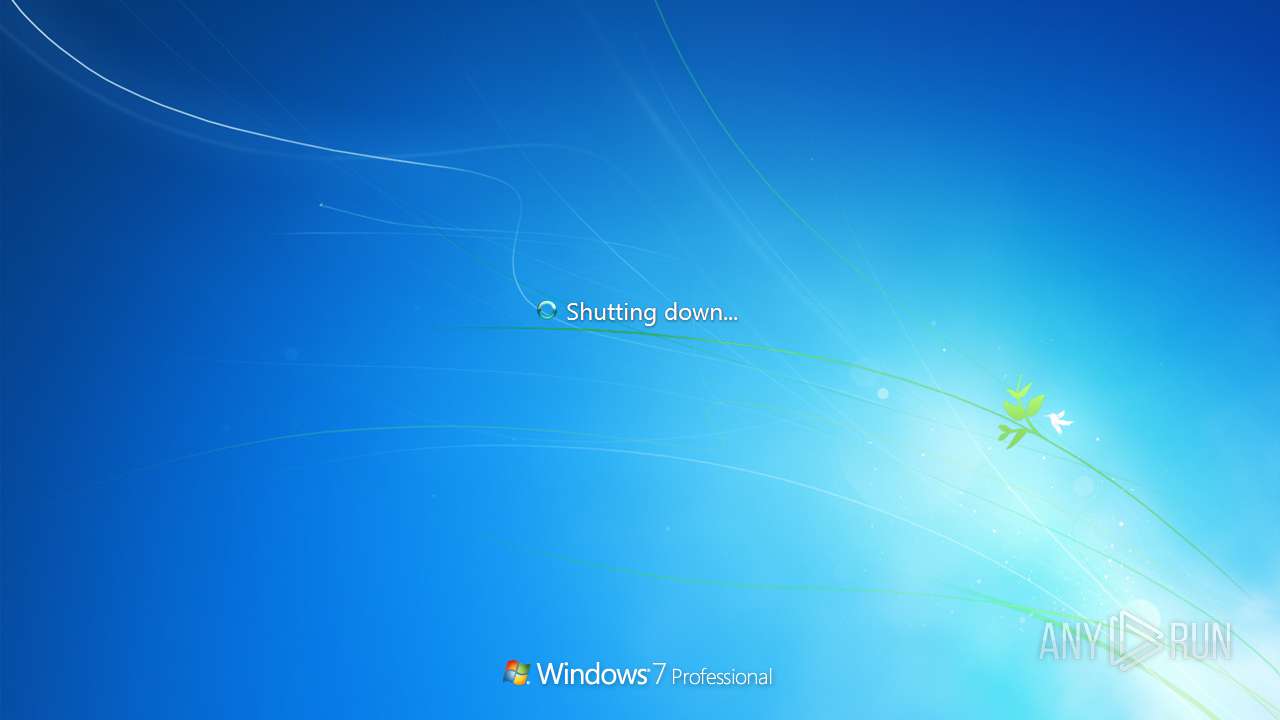
| 3700 | shutdown /f /r /t 0 | C:\Windows\system32\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3780 | taskkill /f /im taskmgr.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
478
Read events
436
Write events
42
Delete events
0
Modification events
| (PID) Process: | (3548) 000.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\txtfile\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Temp\icon.ico | |||
| (PID) Process: | (3548) 000.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: | |||
| (PID) Process: | (3548) 000.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (3548) 000.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | AutoRestartShell |
Value: 0 | |||
| (PID) Process: | (3548) 000.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: 000.exe | |||
| (PID) Process: | (3548) 000.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3548) 000.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3548) 000.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | LastScreensaverSetThreadExecutionState |
Value: 2147483648 | |||
| (PID) Process: | (3548) 000.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | LastScreensaverState |
Value: 4 | |||
| (PID) Process: | (3548) 000.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | AutoMetadataCurrentDownloadCount |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
404
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3548 | 000.exe | C:\Users\admin\AppData\Local\Temp\icon.ico | image | |
MD5:A4B9662CF3B6EA6626F6081C0D8C13F3 | SHA256:84A1C2713642090523F05D9FB015C537FD210D3200CADAF442BB67CF1834B356 | |||
| 2164 | cmd.exe | C:\Users\admin\Desktop\UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR N0XT.txt | text | |
MD5:9037EBF0A18A1C17537832BC73739109 | SHA256:38C889B5D7BDCB79BBCB55554C520A9CE74B5BFC29C19D1E4CB1419176C99F48 | |||
| 2164 | cmd.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup\rniw.exe | executable | |
MD5:9232120B6FF11D48A90069B25AA30ABC | SHA256:70FAA0E1498461731F873D3594F20CBF2BEAA6F123A06B66F9DF59A9CDF862BE | |||
| 3548 | 000.exe | C:\Users\admin\AppData\Local\Temp\one.rtf | text | |
MD5:6FBD6CE25307749D6E0A66EBBC0264E7 | SHA256:E152B106733D9263D3CF175F0B6197880D70ACB753F8BDE8035A3E4865B31690 | |||
| 3548 | 000.exe | C:\Users\admin\AppData\Local\Temp\text.txt | text | |
MD5:9037EBF0A18A1C17537832BC73739109 | SHA256:38C889B5D7BDCB79BBCB55554C520A9CE74B5BFC29C19D1E4CB1419176C99F48 | |||
| 2164 | cmd.exe | C:\Users\admin\Desktop\UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR N1XT.txt | text | |
MD5:9037EBF0A18A1C17537832BC73739109 | SHA256:38C889B5D7BDCB79BBCB55554C520A9CE74B5BFC29C19D1E4CB1419176C99F48 | |||
| 3548 | 000.exe | C:\Users\admin\AppData\Local\Temp\v.mp4 | 3g2 | |
MD5:D2774B188AB5DDE3E2DF5033A676A0B4 | SHA256:95374CF300097872A546D89306374E7CF2676F7A8B4C70274245D2DCCFC79443 | |||
| 2164 | cmd.exe | C:\Users\admin\Desktop\UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR N3XT.txt | text | |
MD5:9037EBF0A18A1C17537832BC73739109 | SHA256:38C889B5D7BDCB79BBCB55554C520A9CE74B5BFC29C19D1E4CB1419176C99F48 | |||
| 2164 | cmd.exe | C:\Users\admin\Desktop\UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR N4XT.txt | text | |
MD5:9037EBF0A18A1C17537832BC73739109 | SHA256:38C889B5D7BDCB79BBCB55554C520A9CE74B5BFC29C19D1E4CB1419176C99F48 | |||
| 2164 | cmd.exe | C:\Users\admin\Desktop\UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR N5XT.txt | text | |
MD5:9037EBF0A18A1C17537832BC73739109 | SHA256:38C889B5D7BDCB79BBCB55554C520A9CE74B5BFC29C19D1E4CB1419176C99F48 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report