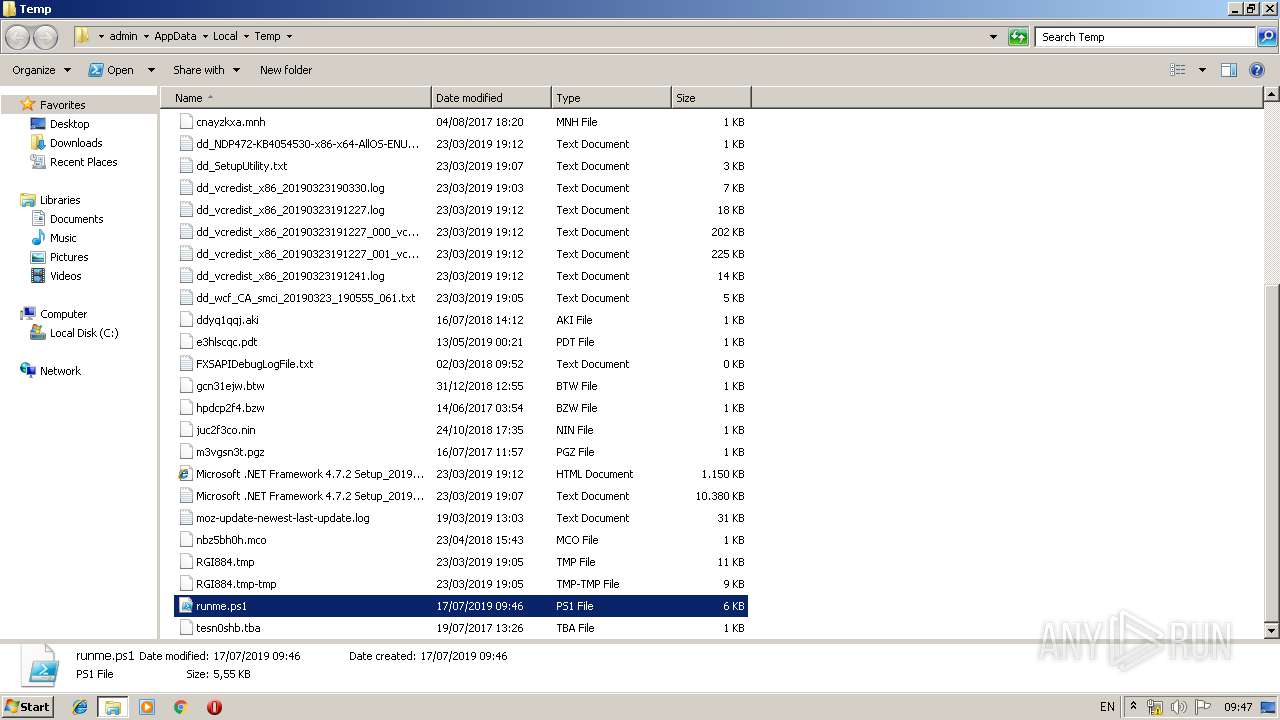
| File name: | runme.ps1 |
| Full analysis: | https://app.any.run/tasks/f6294631-633a-4a54-aeb1-20ebdb6f7577 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 08:46:13 |
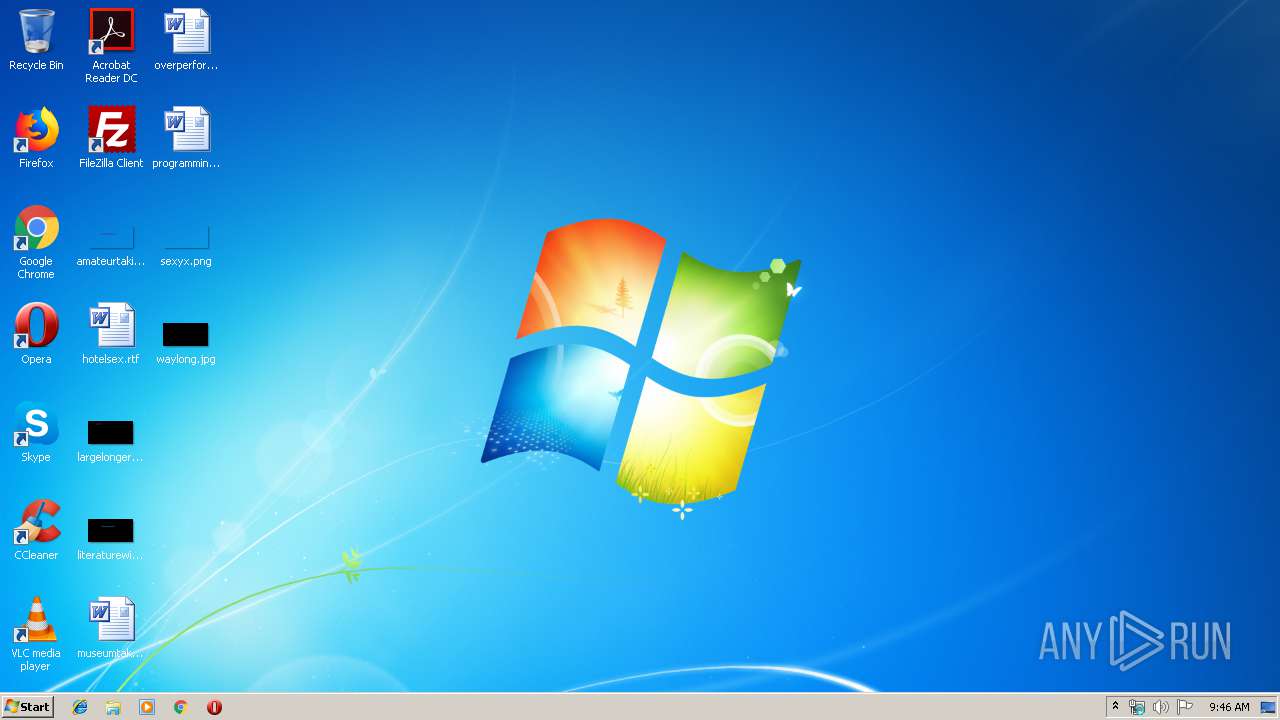
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines |
| MD5: | 1E37FCB71879AA31B326D6104B72402D |
| SHA1: | 8EDCF0F632F8A829C0A452E5C6C3068195BC9293 |
| SHA256: | 4E8FEAD76646878BE4EA42F5F8C89F081055D2CD65A127A1D865ACC8FBE2D23A |
| SSDEEP: | 96:Wh7B2NTFh45fmn0c8WOJ/BF2zcx1Sjkk/YVVMNS5cyhYlUFh19lu5sBmP:EsFqmbpABF3akk/YVVASyCrrUP |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- rundll32.exe (PID: 3220)
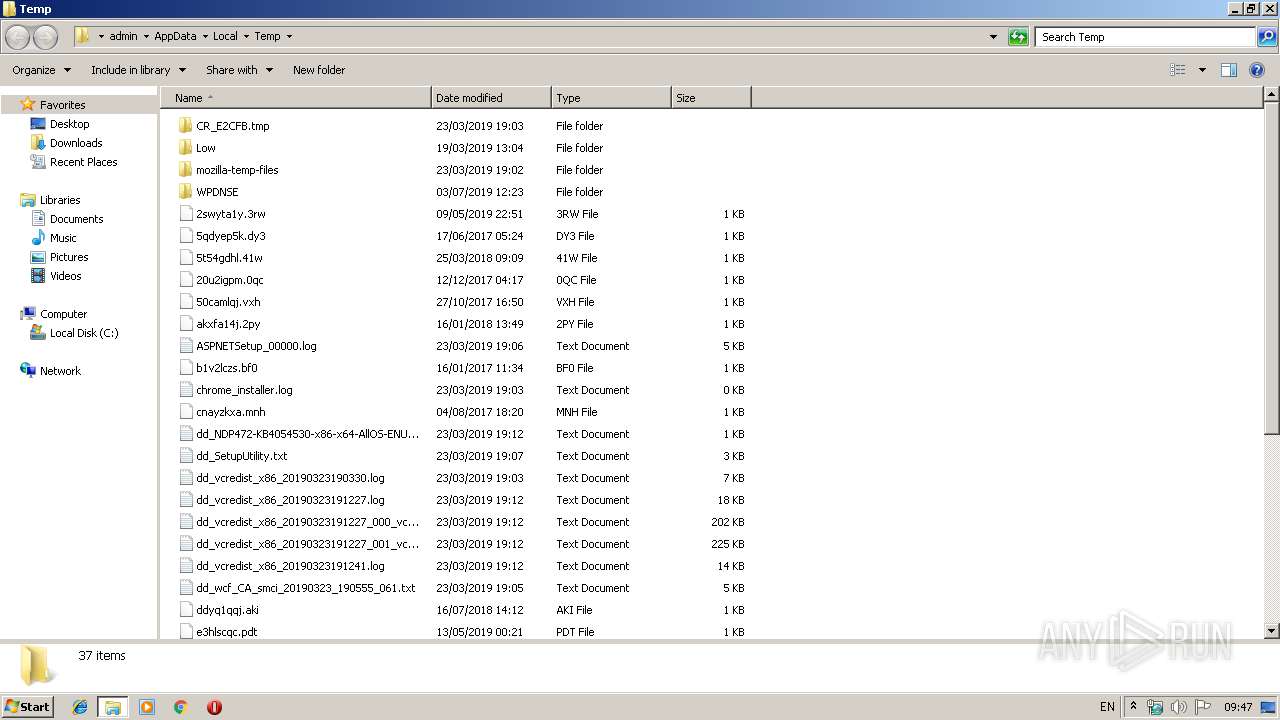
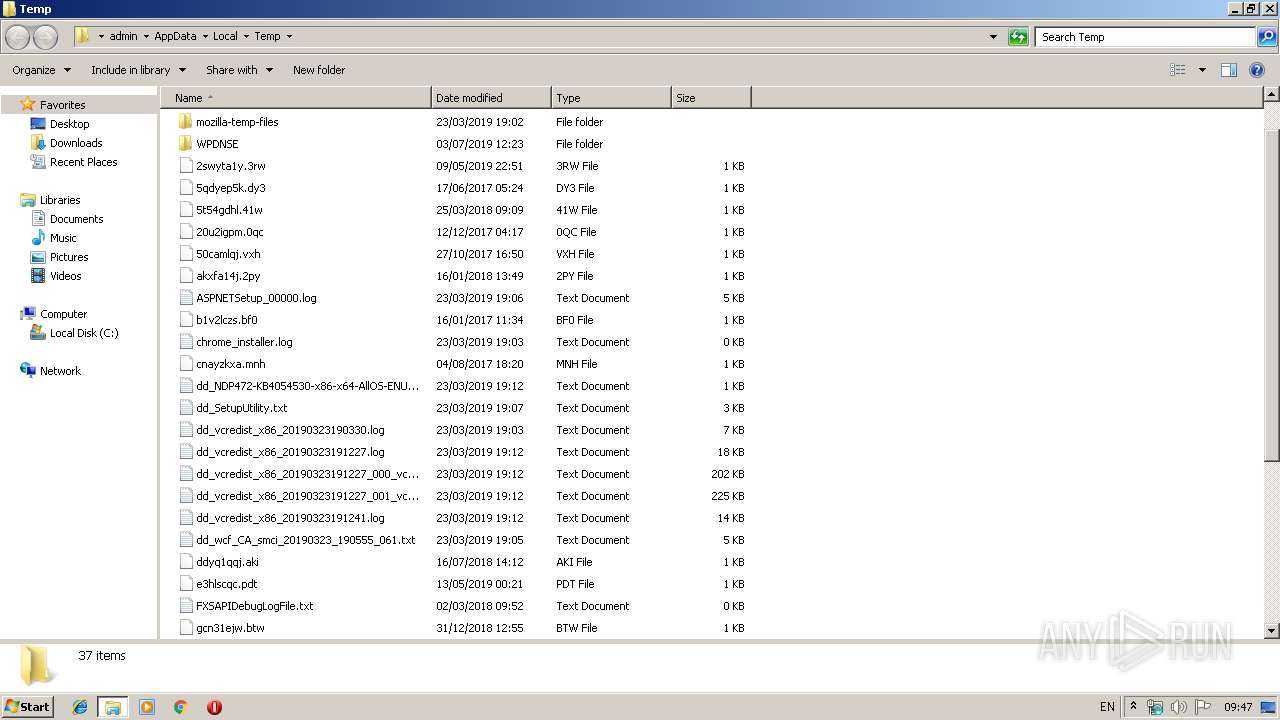
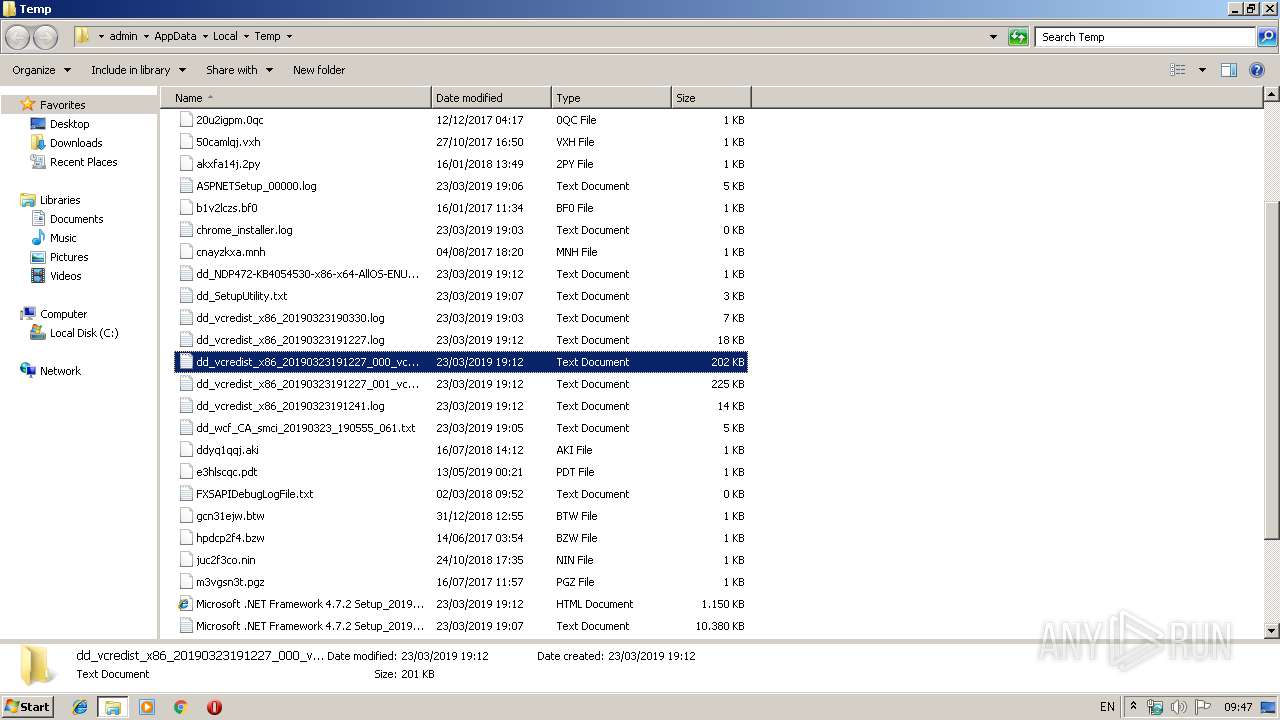
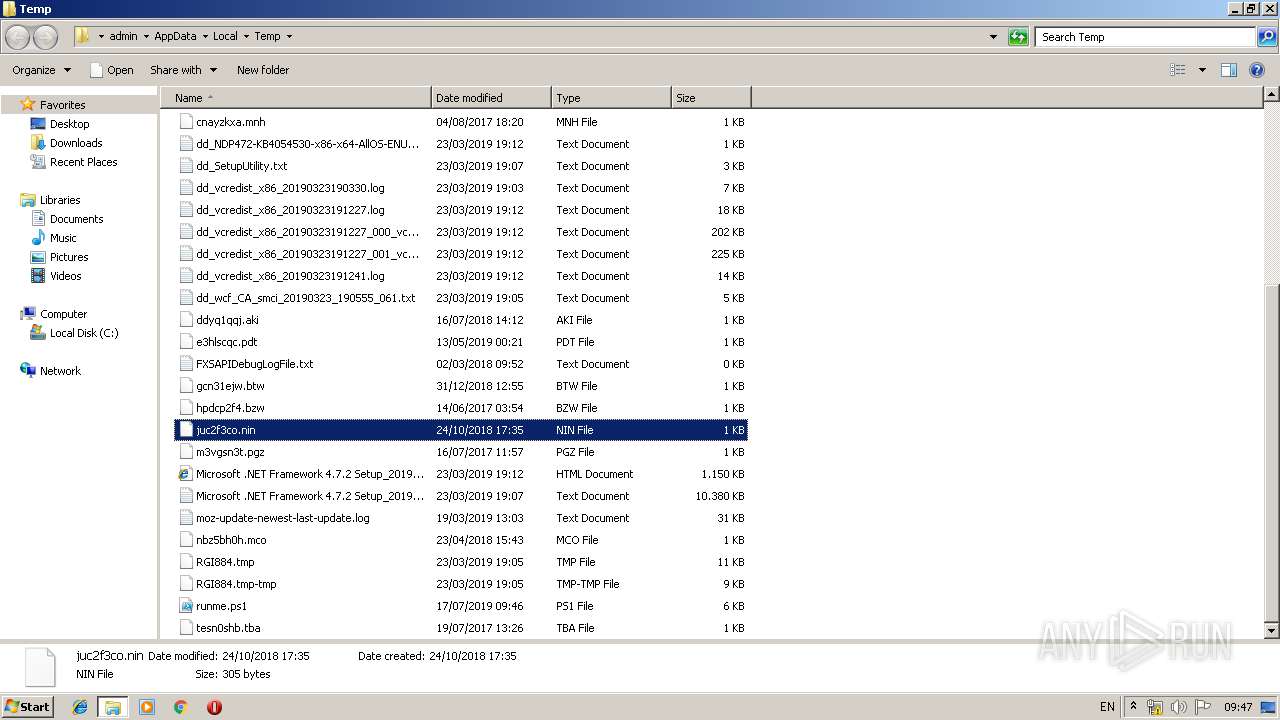
Creates files in the user directory
- powershell.exe (PID: 3544)
- powershell.exe (PID: 3364)
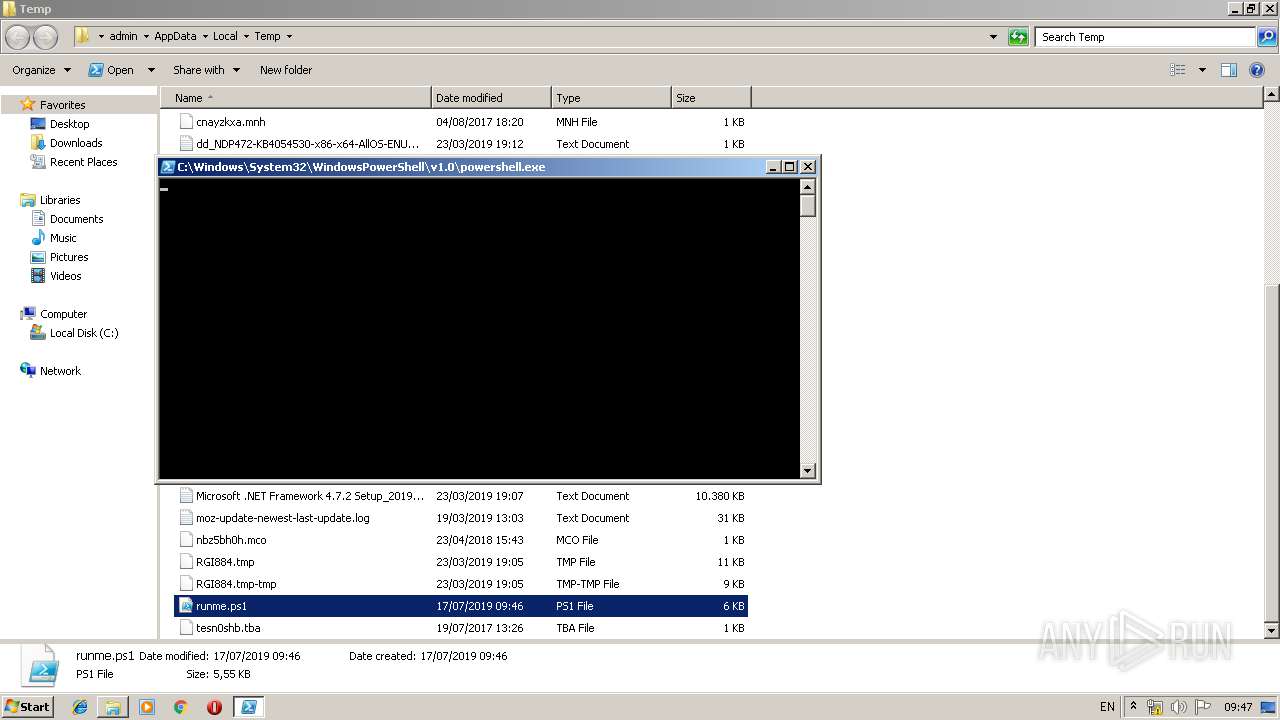
PowerShell script executed
- powershell.exe (PID: 3544)
- powershell.exe (PID: 3364)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 3220)
INFO
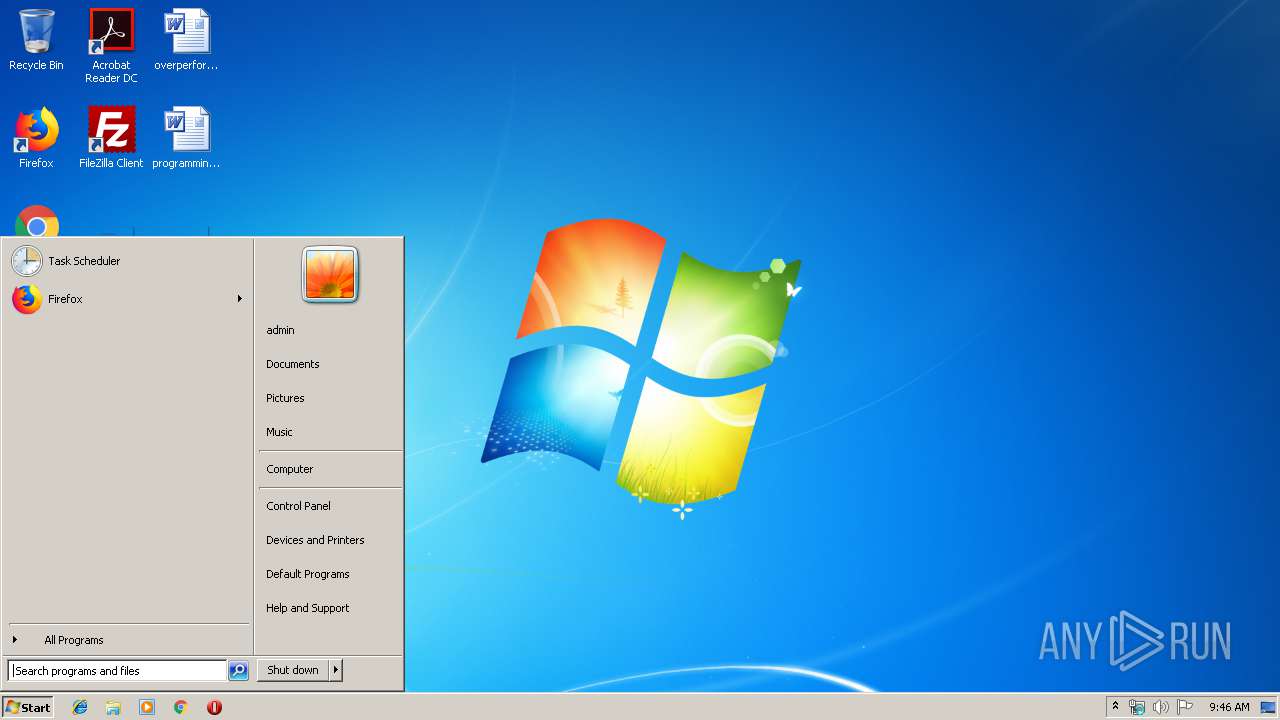
Manual execution by user
- rundll32.exe (PID: 3220)
- verclsid.exe (PID: 3436)
- powershell.exe (PID: 3364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
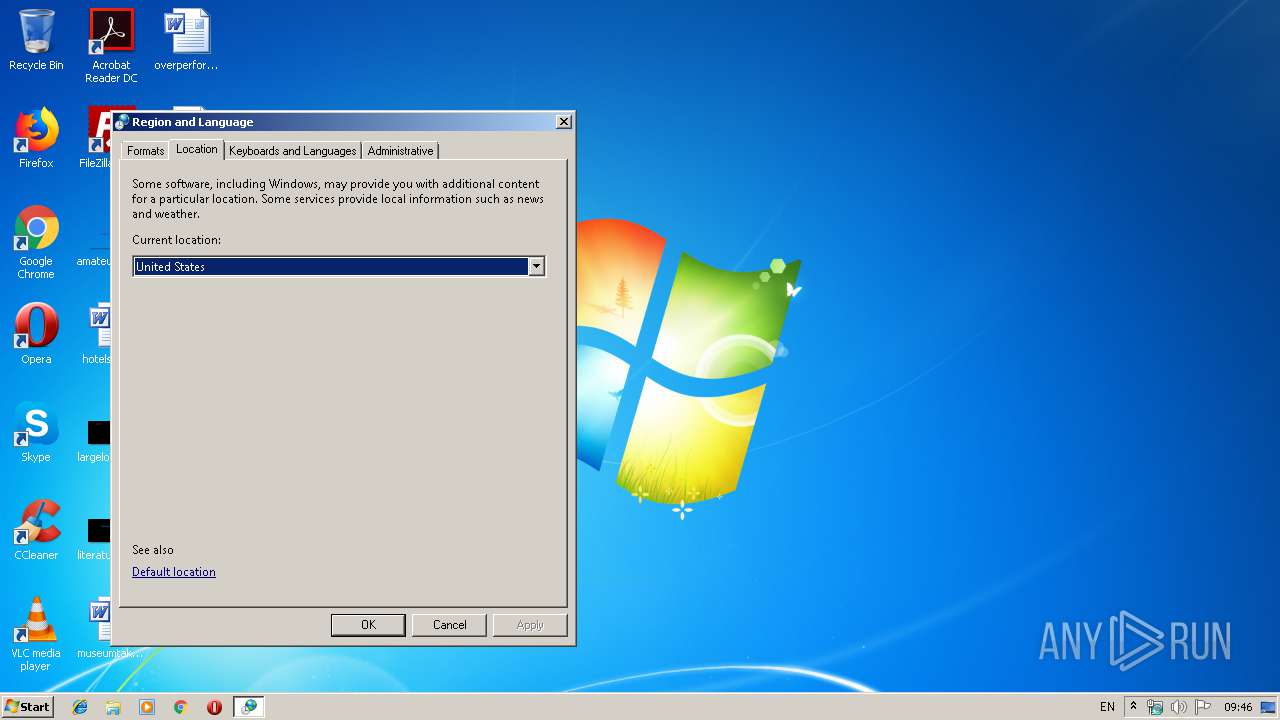
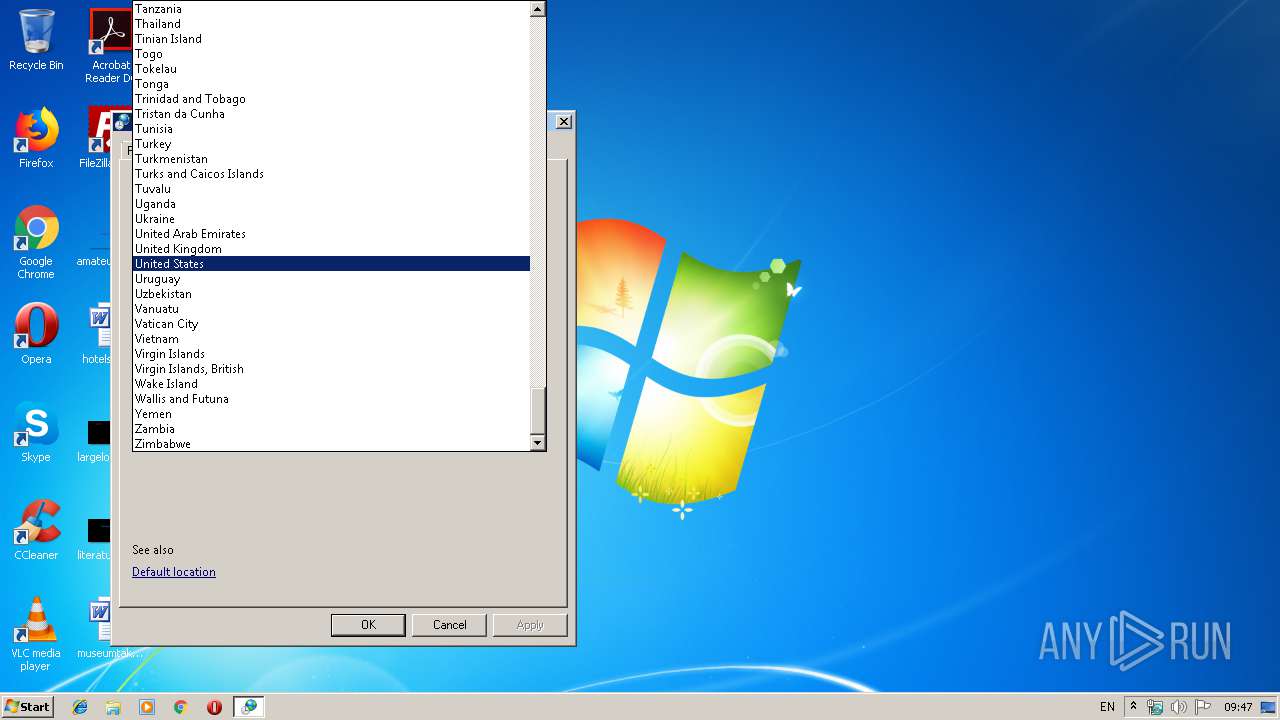
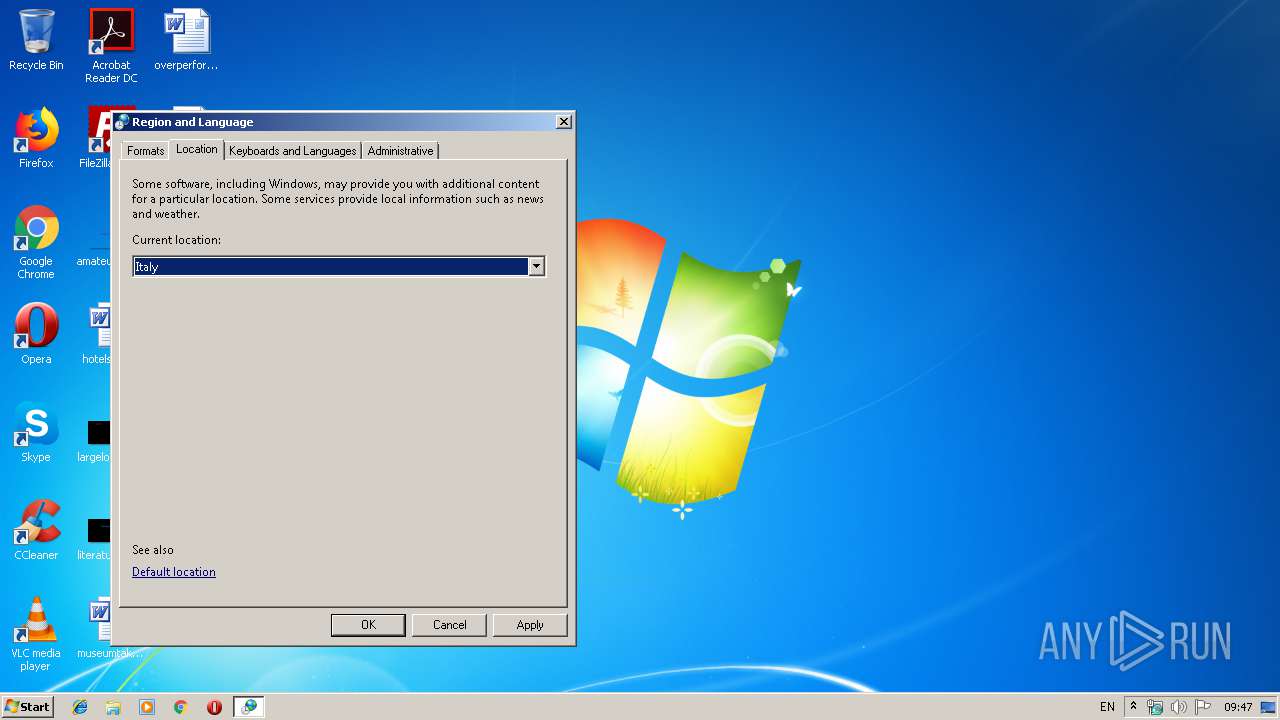
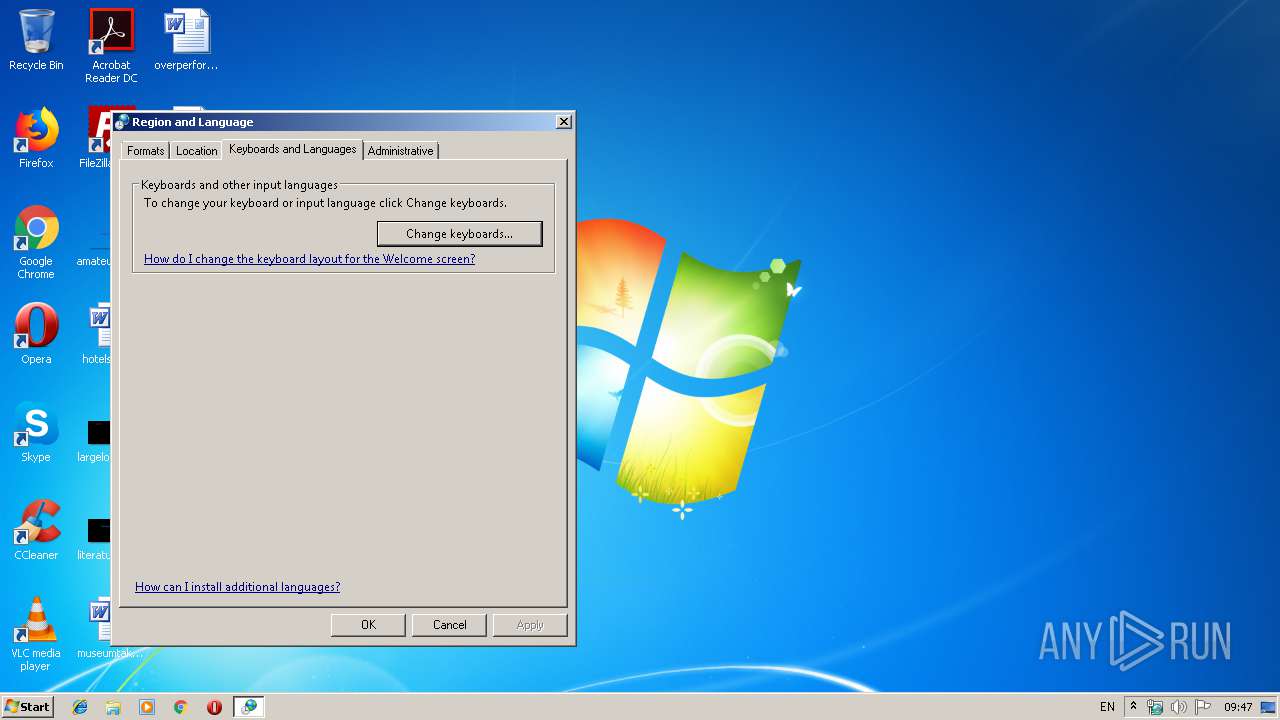
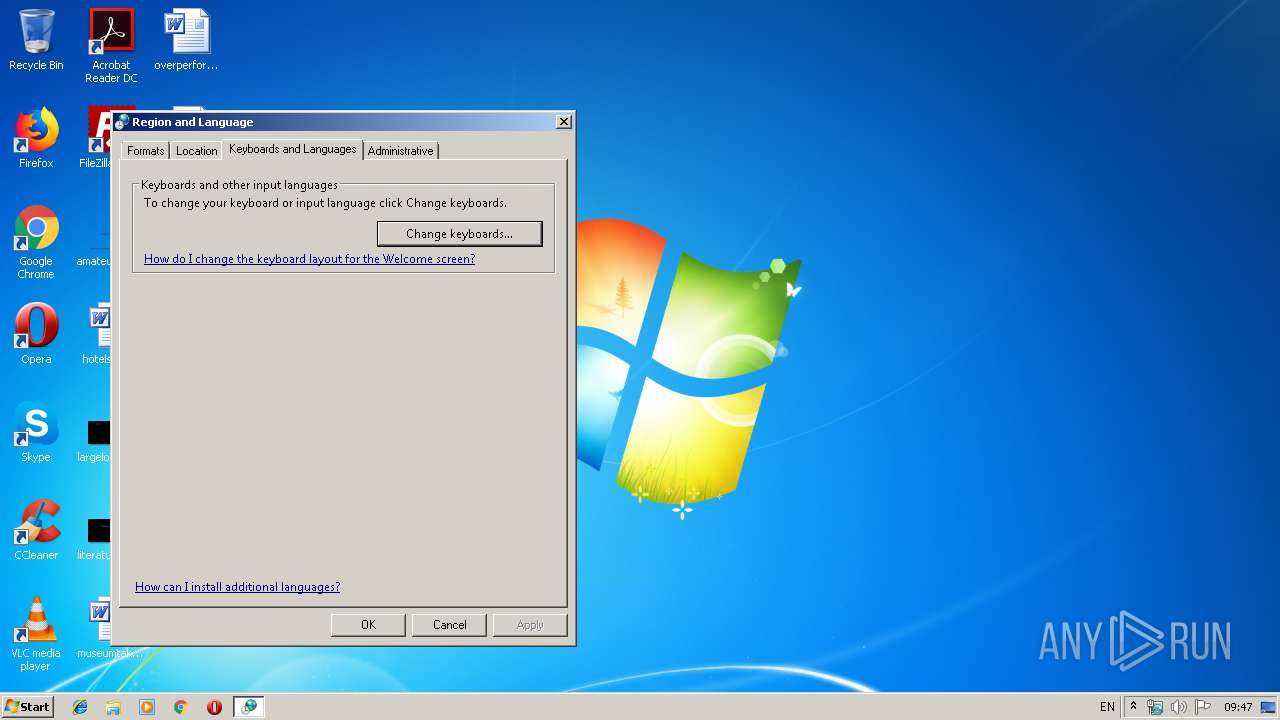
| 3072 | "C:\Windows\system32\rundll32.exe" shell32.dll,Control_RunDLL input.dll | C:\Windows\system32\rundll32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3220 | "C:\Windows\System32\rundll32.exe" C:\Windows\System32\shell32.dll,Control_RunDLL C:\Windows\System32\intl.cpl | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
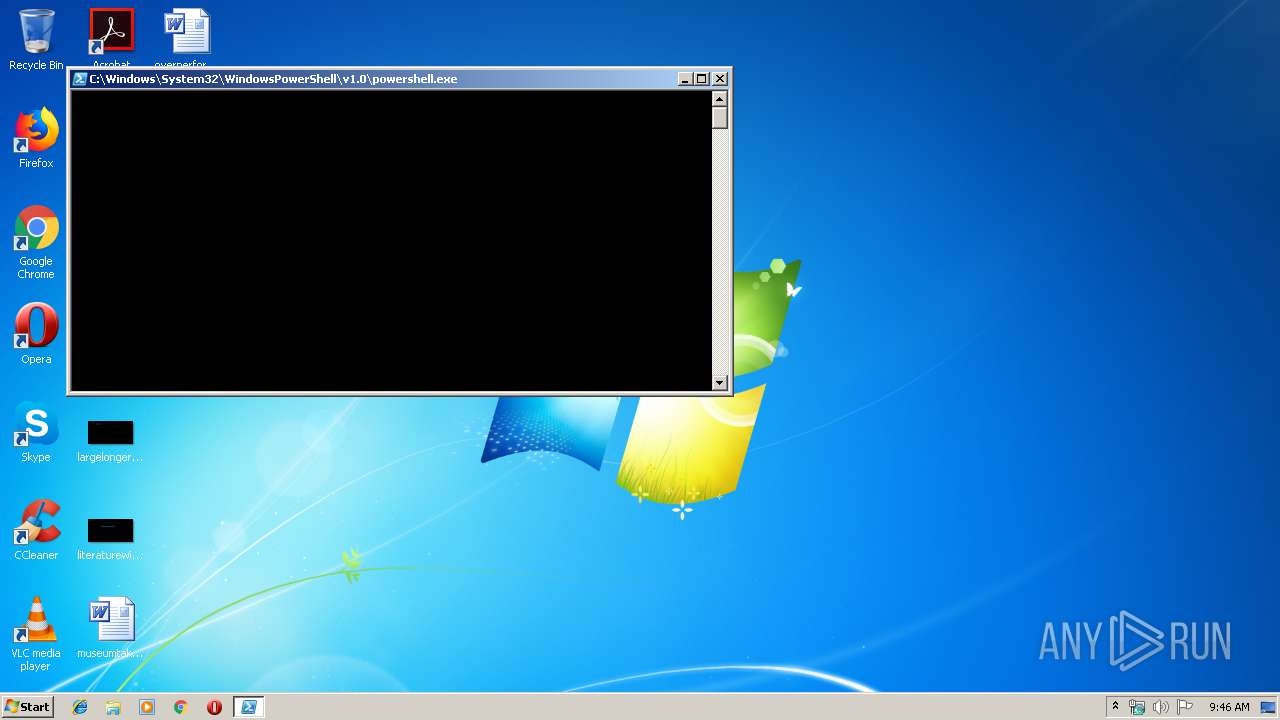
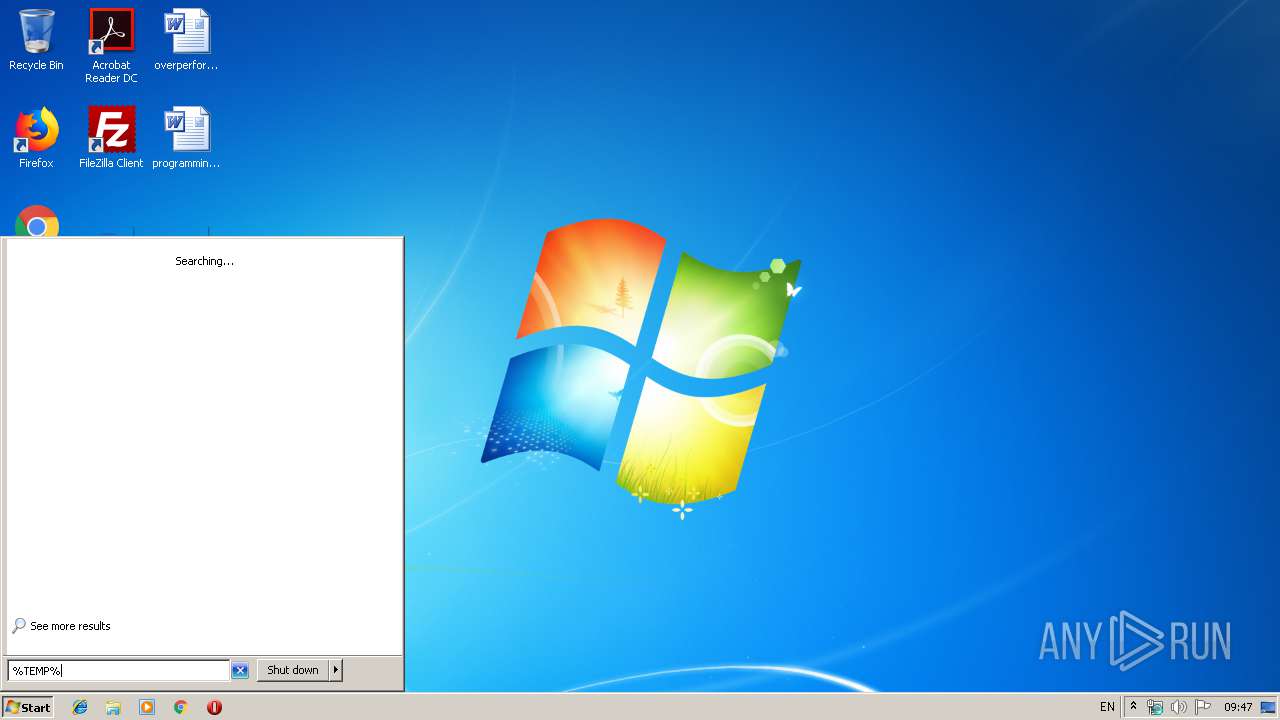
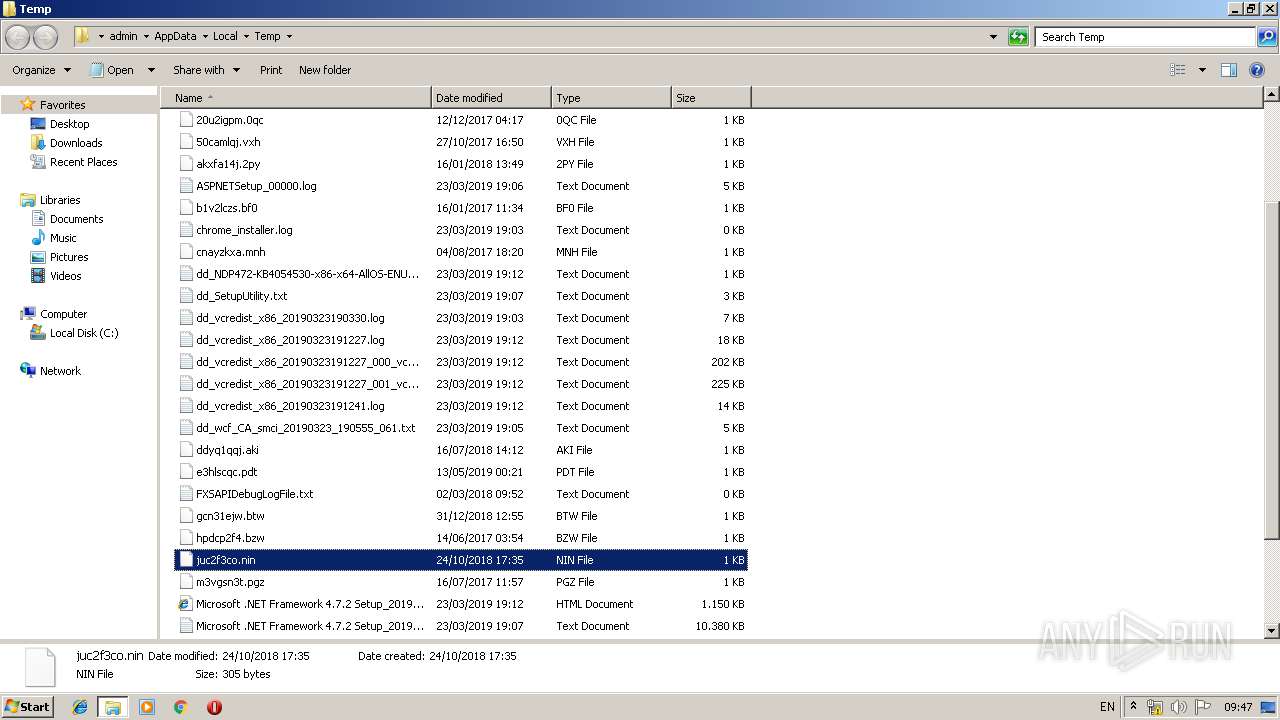
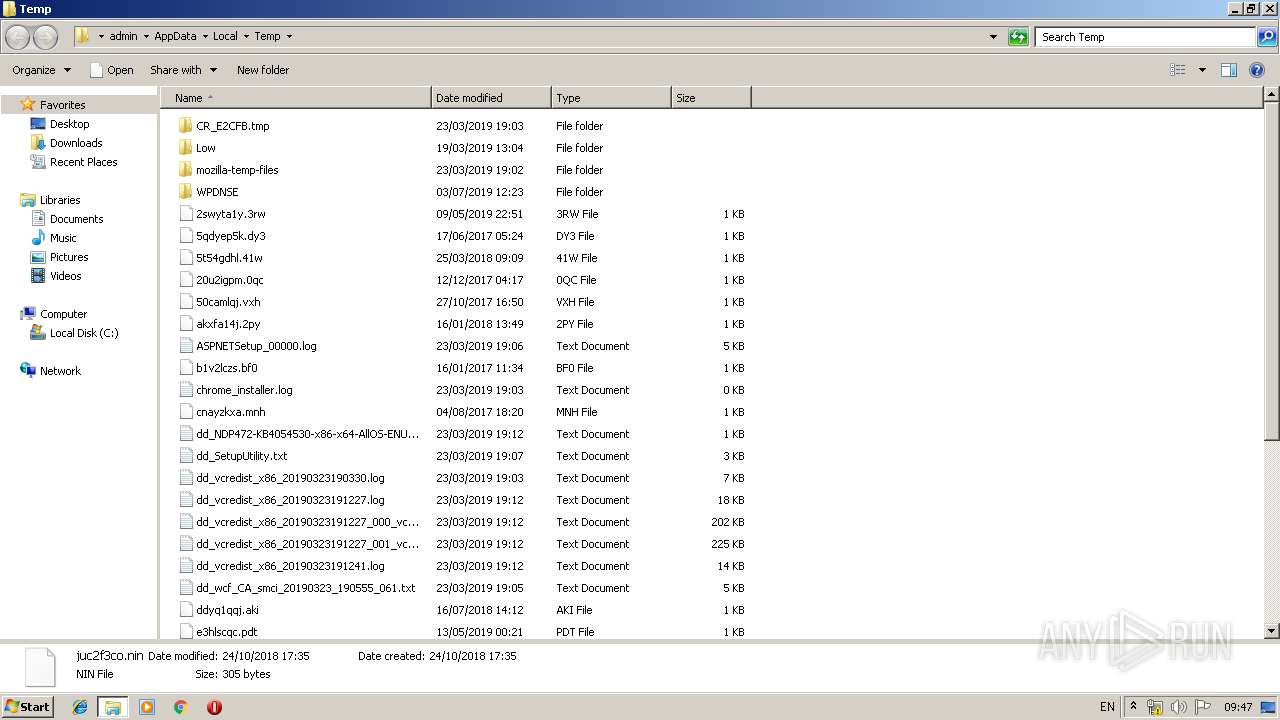
| 3364 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\runme.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3396 | C:\Windows\system32\mctadmin.exe | C:\Windows\system32\mctadmin.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MCTAdmin Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3436 | "C:\Windows\system32\verclsid.exe" /S /C {0B2C9183-C9FA-4C53-AE21-C900B0C39965} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\system32\verclsid.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3544 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\runme.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 369
Read events
580
Write events
768
Delete events
21
Modification events
| (PID) Process: | (3544) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3544) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3544) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
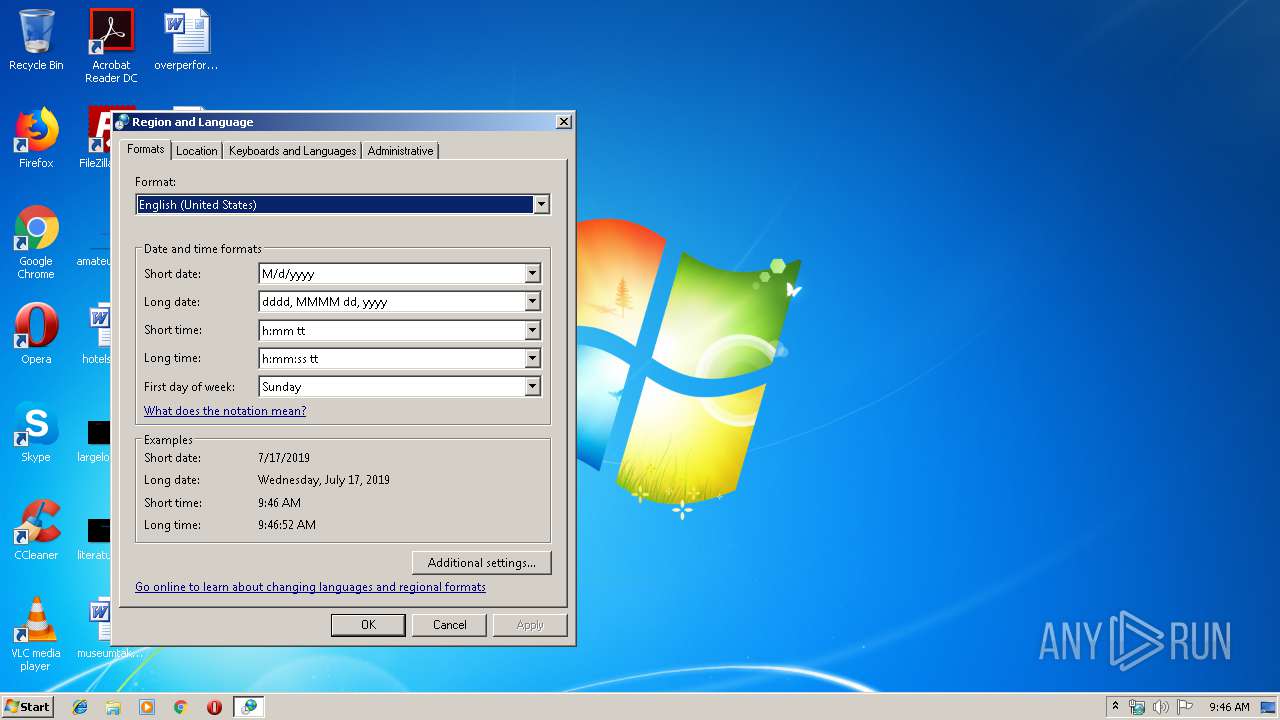
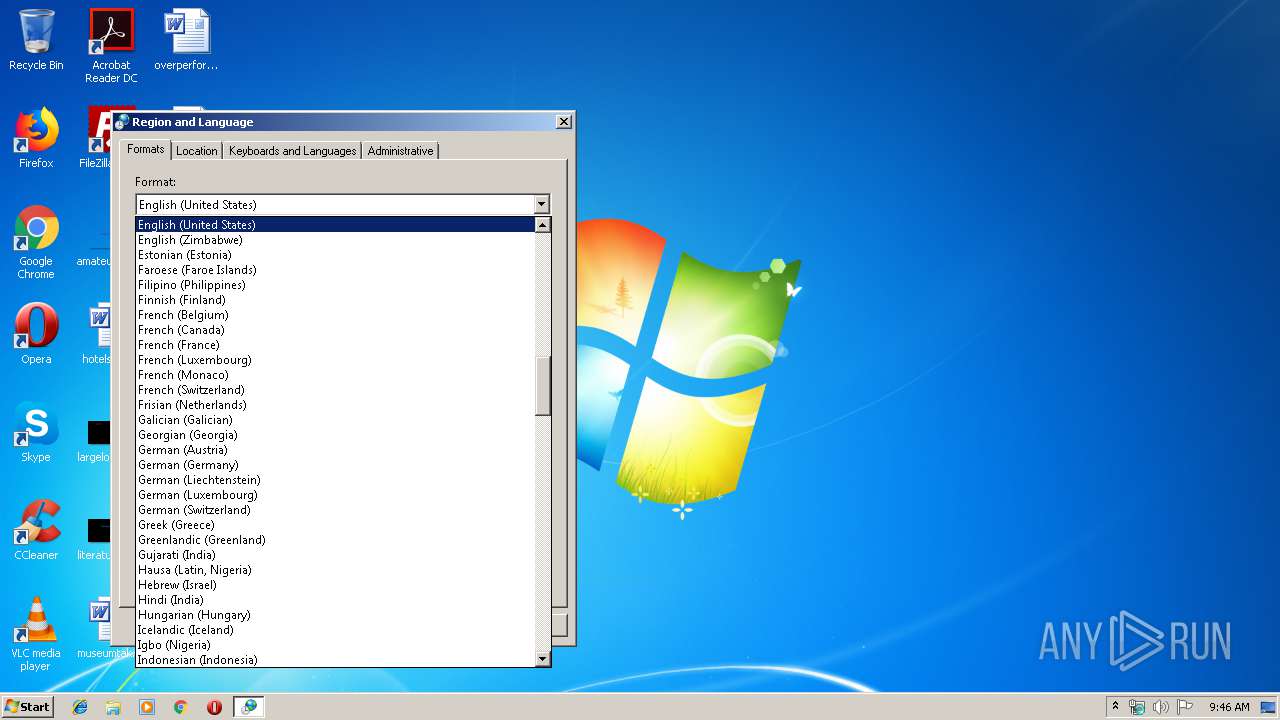
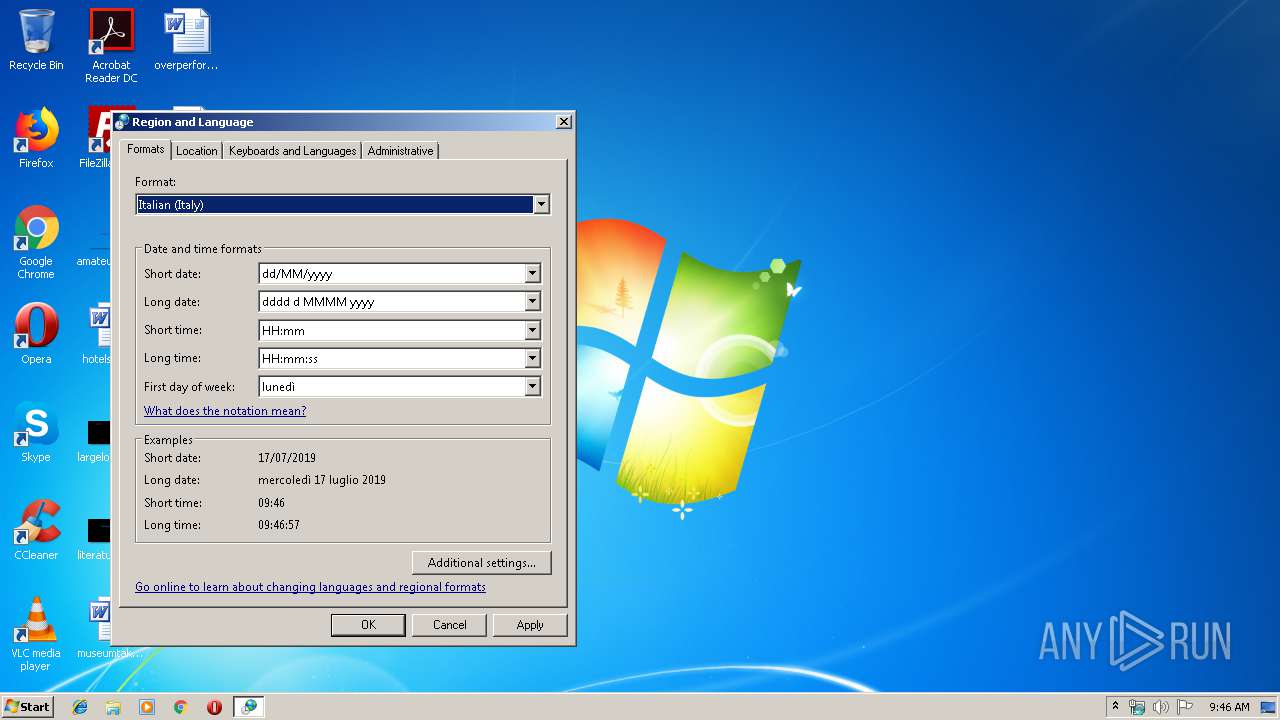
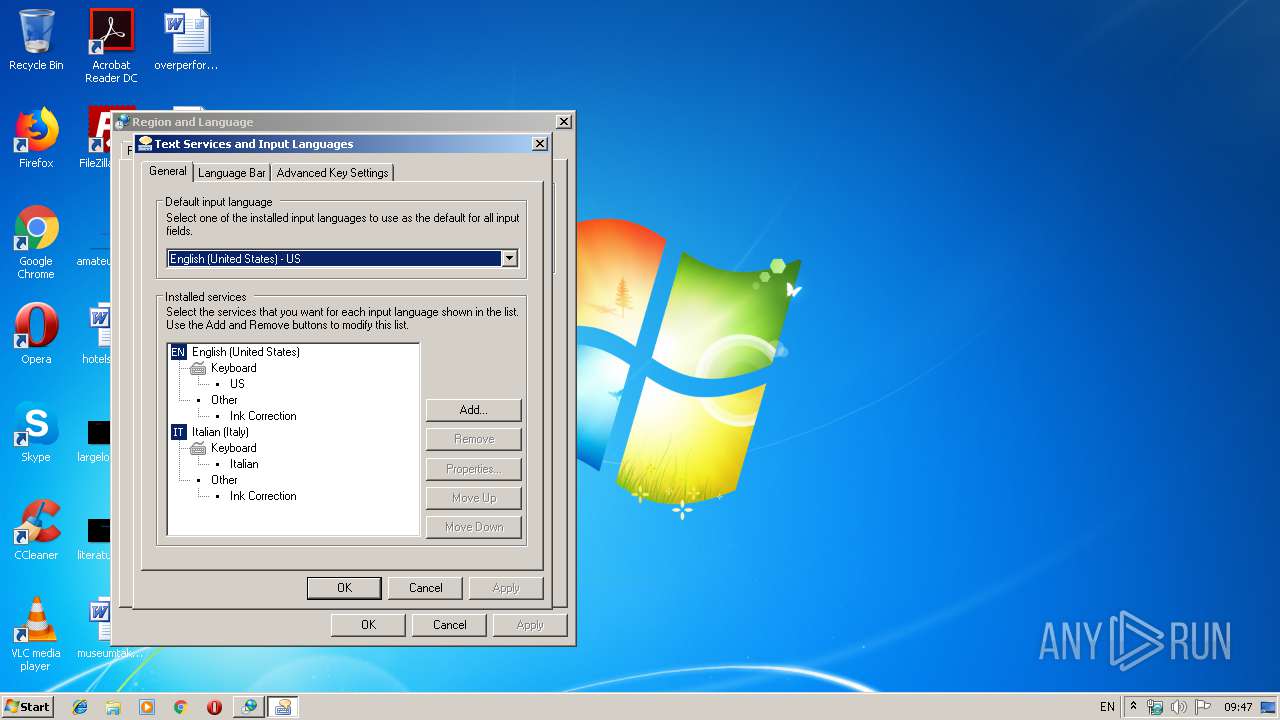
| (PID) Process: | (3220) rundll32.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | LocaleName |
Value: it-IT | |||
| (PID) Process: | (3220) rundll32.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | iCalendarType |
Value: 1 | |||
| (PID) Process: | (3220) rundll32.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | s1159 |
Value: | |||
| (PID) Process: | (3220) rundll32.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | s2359 |
Value: | |||
| (PID) Process: | (3220) rundll32.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | sTimeFormat |
Value: HH:mm:ss | |||
| (PID) Process: | (3220) rundll32.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | iTime |
Value: 1 | |||
| (PID) Process: | (3220) rundll32.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | iTLZero |
Value: 1 | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3544 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PJRG3OZIQSHL3DSEXZMW.temp | — | |
MD5:— | SHA256:— | |||
| 3364 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8VGRPV6PYLVLEVGODW5D.temp | — | |
MD5:— | SHA256:— | |||
| 3544 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3544 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF17cf85.TMP | binary | |
MD5:— | SHA256:— | |||
| 3364 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3364 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF18cadc.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3364 | powershell.exe | 185.158.249.75:443 | woeiuyfgowe.xyz | easystores GmbH | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
woeiuyfgowe.xyz |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3364 | powershell.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |