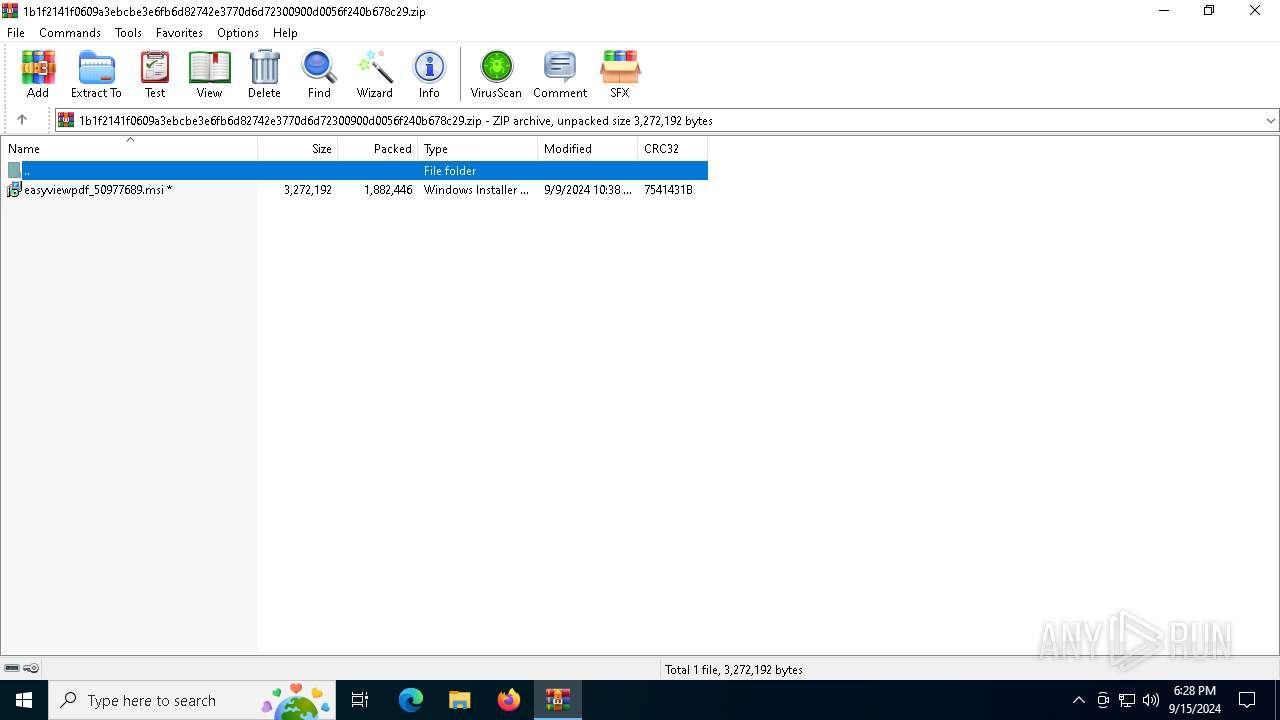
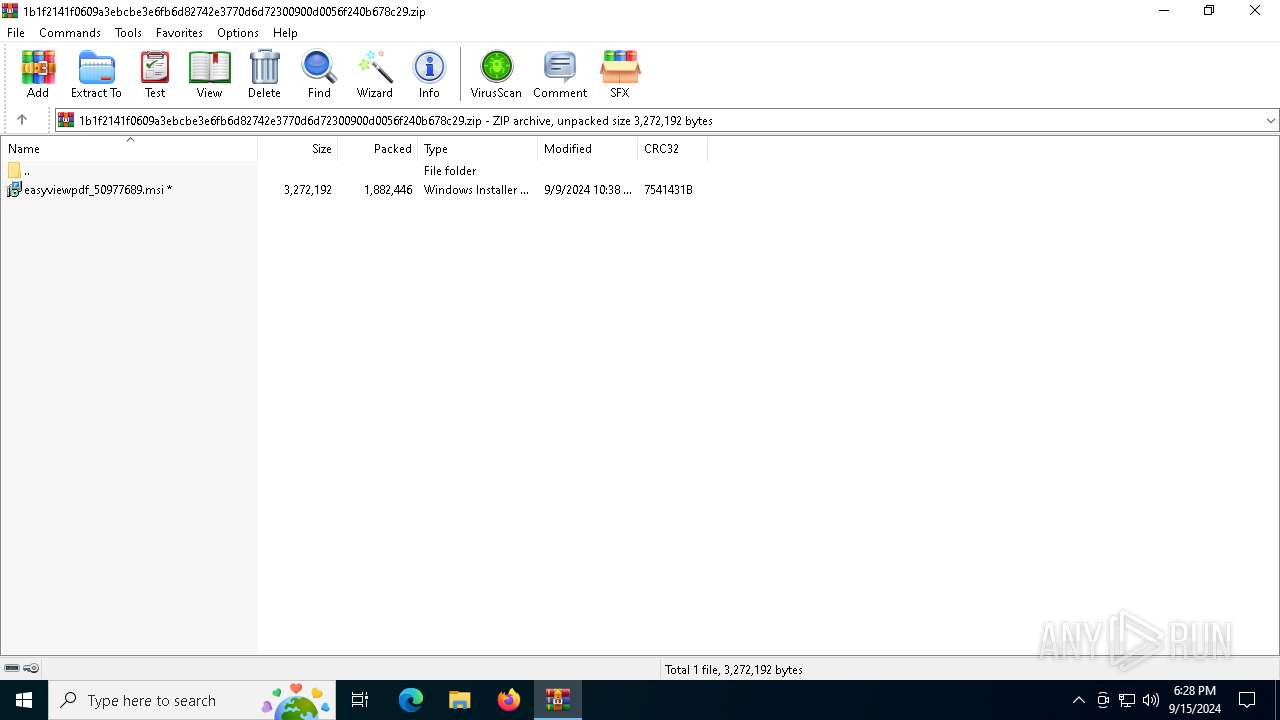
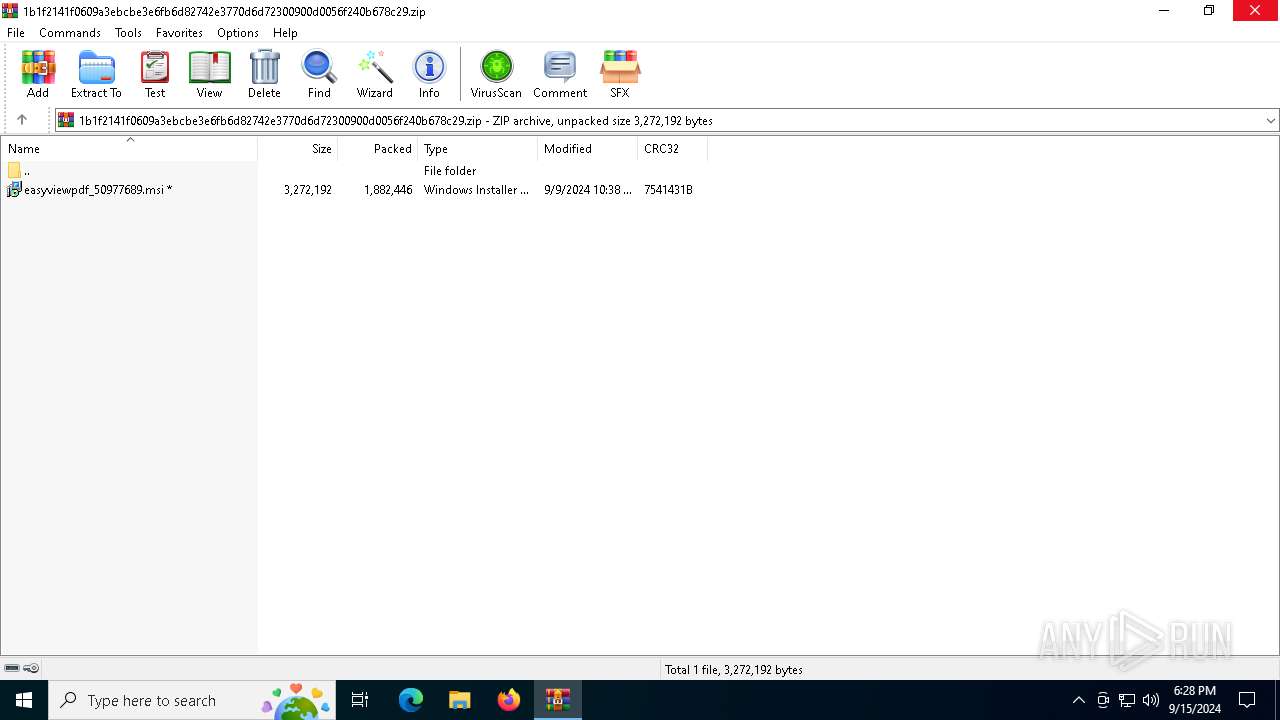
| File name: | 1b1f2141f0609a3ebcbe3e6fb6d82742e3770d6d72300900d0056f240b678c29.zip |
| Full analysis: | https://app.any.run/tasks/681e5b96-8e01-4e73-8e07-ae9e990c7ab7 |
| Verdict: | Malicious activity |
| Analysis date: | September 15, 2024, 18:28:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
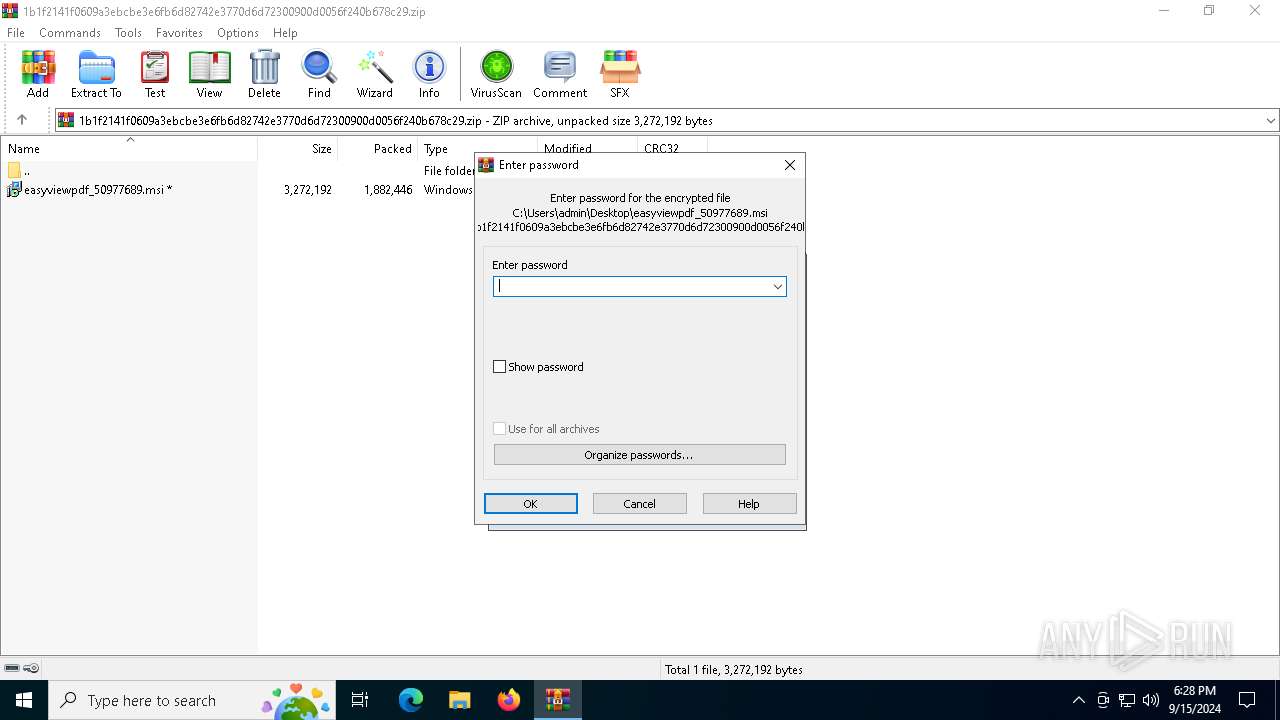
| File info: | Zip archive data, at least v2.0 to extract, compression method=AES Encrypted |
| MD5: | A15EB8D7881AA61751124D1820AD11B7 |
| SHA1: | 826A1004CE02F1A6381D1FD368BF407BD17F3ADC |
| SHA256: | 4E788A19A8BB9BFF6C4258BDE9B15E9C6B2AD97B85819A43EEAE950236FEB11E |
| SSDEEP: | 98304:FamwCGiQ/orp5VteWhOg//xgqgwpiUXEvAHtWAxUBnxJFZYXvk4LTdTiI/EbQfdt:V9sk |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1932)
Executes as Windows Service
- VSSVC.exe (PID: 876)
Checks Windows Trust Settings
- msiexec.exe (PID: 1932)
- msiexec.exe (PID: 6292)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6292)
- msiexec.exe (PID: 4344)
Executable content was dropped or overwritten
- rundll32.exe (PID: 2804)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 4344)
The executable file from the user directory is run by the CMD process
- pdfprosuite.exe (PID: 3004)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2524)
- msiexec.exe (PID: 6484)
- msiexec.exe (PID: 1932)
Checks proxy server information
- msiexec.exe (PID: 6484)
- msiexec.exe (PID: 6292)
The process uses the downloaded file
- WinRAR.exe (PID: 2524)
- msiexec.exe (PID: 4344)
- cmd.exe (PID: 4100)
- cmd.exe (PID: 6648)
- cmd.exe (PID: 6744)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 4704)
Reads the computer name
- msiexec.exe (PID: 1932)
- msiexec.exe (PID: 6292)
- msiexec.exe (PID: 4344)
- pdfprosuite.exe (PID: 3004)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6484)
Reads the software policy settings
- msiexec.exe (PID: 6484)
- msiexec.exe (PID: 6292)
- msiexec.exe (PID: 1932)
Reads Environment values
- msiexec.exe (PID: 4344)
- msiexec.exe (PID: 6292)
- pdfprosuite.exe (PID: 5796)
- pdfprosuite.exe (PID: 6184)
- pdfprosuite.exe (PID: 6212)
- pdfprosuite.exe (PID: 1292)
- pdfprosuite.exe (PID: 3004)
Checks supported languages
- msiexec.exe (PID: 1932)
- msiexec.exe (PID: 4344)
- msiexec.exe (PID: 6292)
- pdfprosuite.exe (PID: 5796)
- pdfprosuite.exe (PID: 6184)
- pdfprosuite.exe (PID: 6212)
- pdfprosuite.exe (PID: 1292)
- pdfprosuite.exe (PID: 3004)
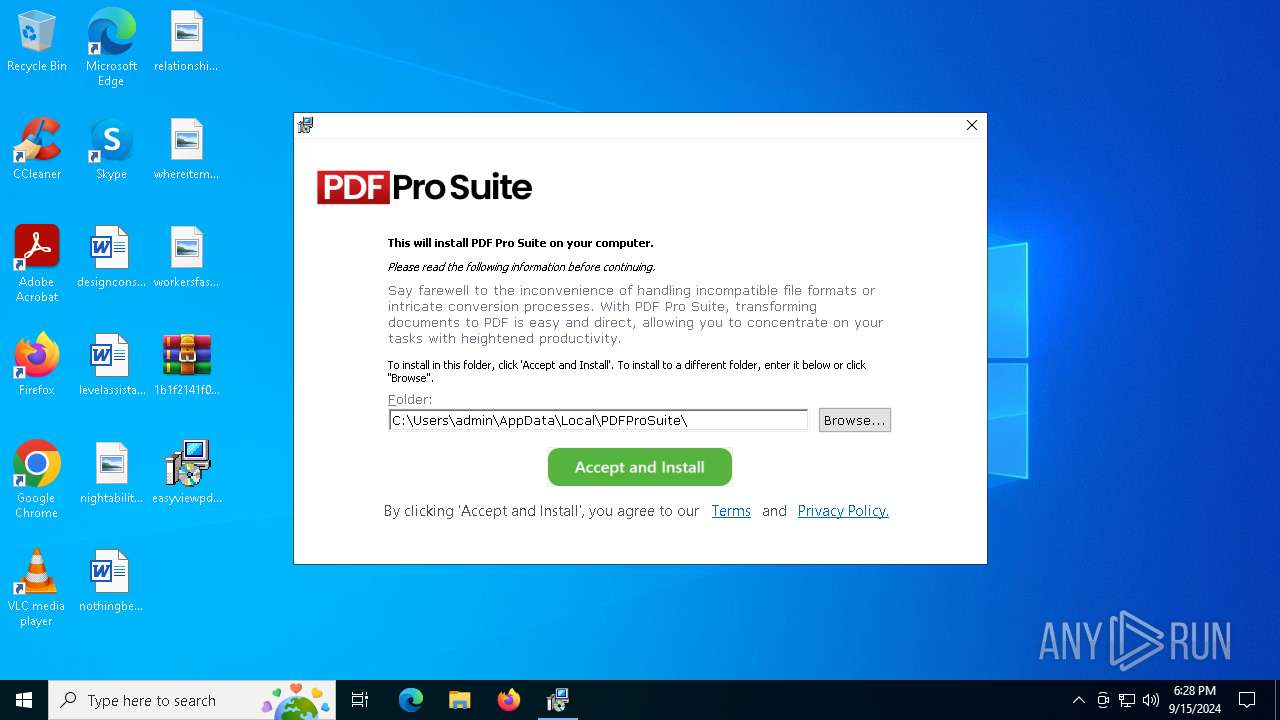
Creates files or folders in the user directory
- msiexec.exe (PID: 6484)
- msiexec.exe (PID: 1932)
- msiexec.exe (PID: 6292)
- rundll32.exe (PID: 2804)
- pdfprosuite.exe (PID: 3004)
Reads the machine GUID from the registry
- msiexec.exe (PID: 1932)
- msiexec.exe (PID: 6292)
- msiexec.exe (PID: 4344)
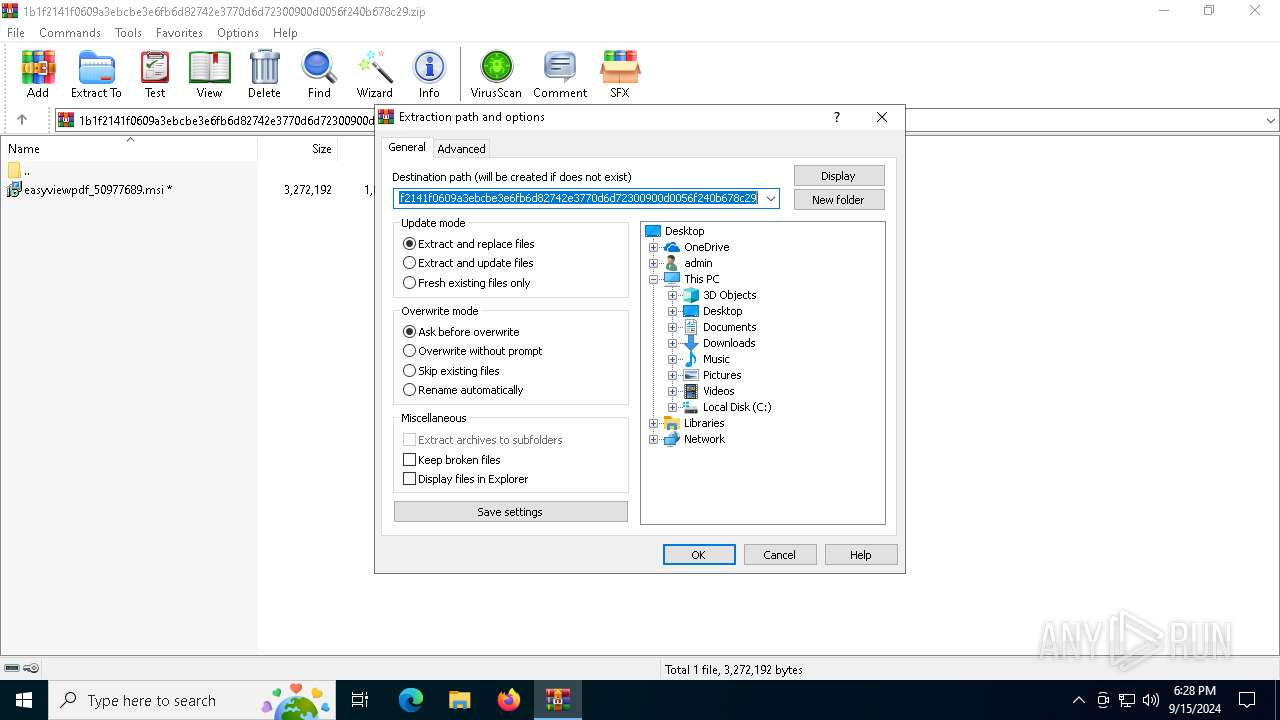
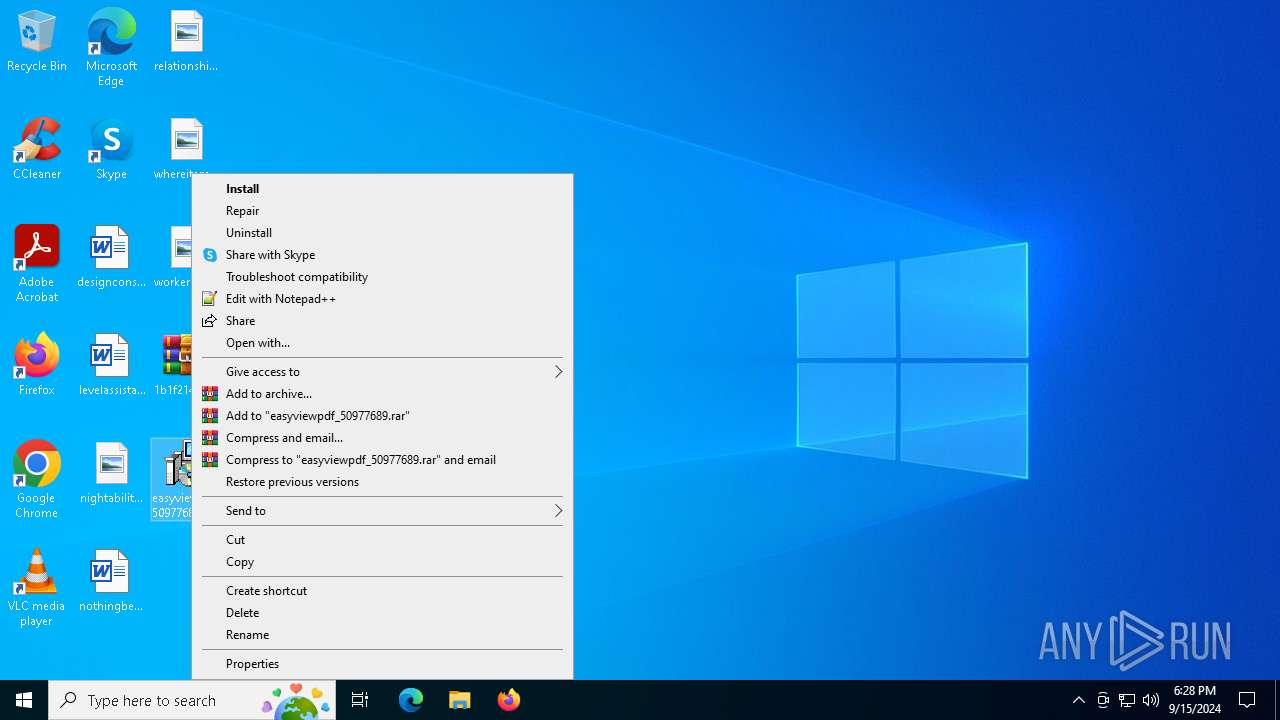
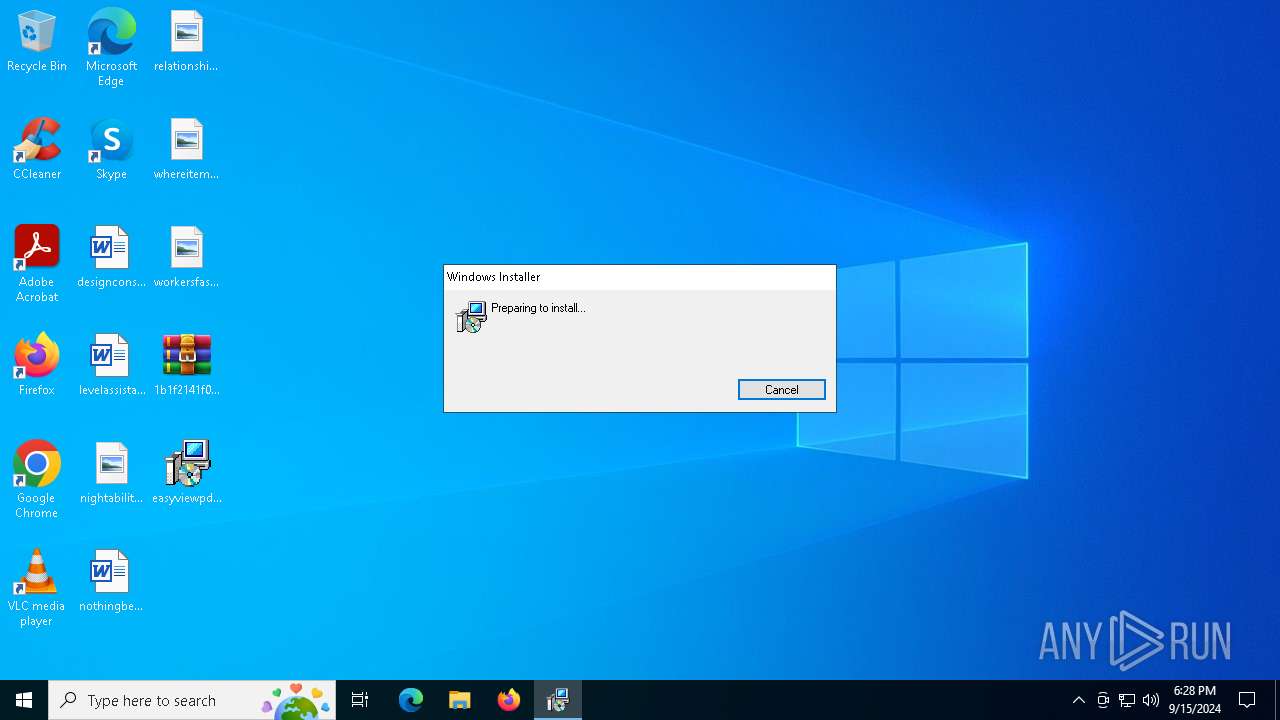
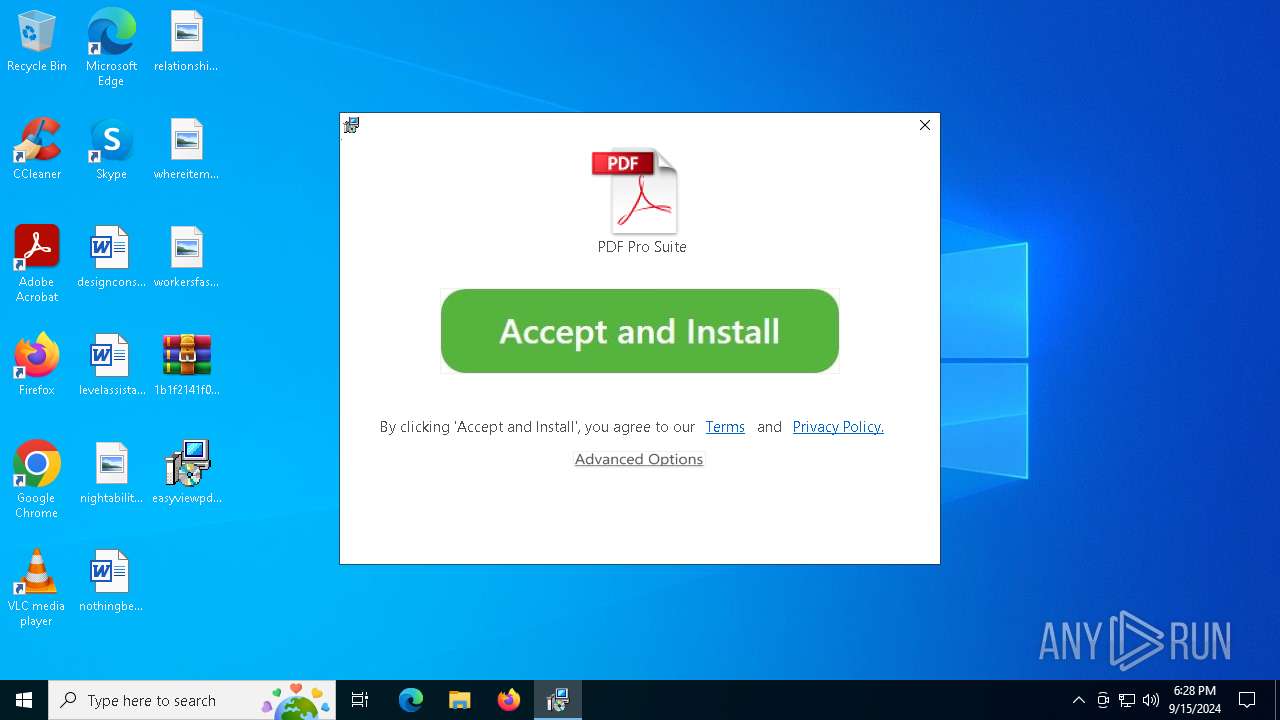
Manual execution by a user
- msiexec.exe (PID: 6484)
- cmd.exe (PID: 6648)
- cmd.exe (PID: 6744)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 4704)
Creates a software uninstall entry
- msiexec.exe (PID: 1932)
Create files in a temporary directory
- rundll32.exe (PID: 2804)
Process checks computer location settings
- msiexec.exe (PID: 4344)
Reads product name
- pdfprosuite.exe (PID: 5796)
- pdfprosuite.exe (PID: 6184)
- pdfprosuite.exe (PID: 6212)
- pdfprosuite.exe (PID: 1292)
- pdfprosuite.exe (PID: 3004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2024:09:09 22:38:52 |
| ZipCRC: | 0x7541431b |
| ZipCompressedSize: | 1882446 |
| ZipUncompressedSize: | 3272192 |
| ZipFileName: | easyviewpdf_50977689.msi |
Total processes
165
Monitored processes
29
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 788 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 876 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1292 | "C:\Users\admin\AppData\Local\PDFProSuite\pdfprosuite.exe" . | C:\Users\admin\AppData\Local\PDFProSuite\pdfprosuite.exe | — | cmd.exe | |||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js JavaScript Runtime Exit code: 1 Version: 18.17.1 Modules
| |||||||||||||||
| 1332 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1932 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2524 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\1b1f2141f0609a3ebcbe3e6fb6d82742e3770d6d72300900d0056f240b678c29.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2804 | rundll32.exe "C:\WINDOWS\Installer\MSIB716.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1292078 3285 Utility!Utility.CA.LogComplete | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3004 | "C:\Users\admin\AppData\Local\PDFProSuite\pdfprosuite.exe" . | C:\Users\admin\AppData\Local\PDFProSuite\pdfprosuite.exe | cmd.exe | ||||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js JavaScript Runtime Exit code: 1 Version: 18.17.1 Modules
| |||||||||||||||
| 4080 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | pdfprosuite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4100 | "C:\WINDOWS\system32\cmd.exe" /c "start /min /d "C:\Users\admin\AppData\Local\PDFProSuite\" PDFProSuite ." | C:\Windows\SysWOW64\cmd.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 093
Read events
20 764
Write events
311
Delete events
18
Modification events
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\1b1f2141f0609a3ebcbe3e6fb6d82742e3770d6d72300900d0056f240b678c29.zip | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
24
Suspicious files
51
Text files
15
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1932 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6484 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9CB4373A4252DE8D2212929836304EC5_0EFD07622F9D5CA3C618EB631B824B99 | binary | |
MD5:53F222492825C184767B3760B47AE0AA | SHA256:F47BB053900D43EFAA1348A65A9315EEECE368A82EE82C80EC1CAB08BAA32611 | |||
| 6484 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI110A.tmp | executable | |
MD5:421643EE7BB89E6DF092BC4B18A40FF8 | SHA256:D6B89FD5A95071E7B144D8BEDCB09B694E9CD14BFBFAFB782B17CF8413EAC6DA | |||
| 6484 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\357F04AD41BCF5FE18FCB69F60C6680F_54E4814457E6B88FC0E5C74B1F0335DA | binary | |
MD5:88F27F966B6486518CAACF95C567C25E | SHA256:A7817FF24DD0890D3E0CA42F66DF1B096FCCE0BCDD6BEE28E45853B27C698847 | |||
| 6484 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI138F.tmp | executable | |
MD5:421643EE7BB89E6DF092BC4B18A40FF8 | SHA256:D6B89FD5A95071E7B144D8BEDCB09B694E9CD14BFBFAFB782B17CF8413EAC6DA | |||
| 6484 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\357F04AD41BCF5FE18FCB69F60C6680F_54E4814457E6B88FC0E5C74B1F0335DA | binary | |
MD5:C09B4D4412B223A2482629D3E2C59C1D | SHA256:76E7DE0B56E5841BB7624195142CC7A48F8972C4F3A64CBD288BC2AD341B0E1D | |||
| 1932 | msiexec.exe | C:\Windows\Installer\136dd0.msi | executable | |
MD5:F3D4A708DAD86E2F3A359D6EDACD5C14 | SHA256:1B1F2141F0609A3EBCBE3E6FB6D82742E3770D6D72300900D0056F240B678C29 | |||
| 6484 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI133F.tmp | executable | |
MD5:421643EE7BB89E6DF092BC4B18A40FF8 | SHA256:D6B89FD5A95071E7B144D8BEDCB09B694E9CD14BFBFAFB782B17CF8413EAC6DA | |||
| 6484 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI13EF.tmp | executable | |
MD5:421643EE7BB89E6DF092BC4B18A40FF8 | SHA256:D6B89FD5A95071E7B144D8BEDCB09B694E9CD14BFBFAFB782B17CF8413EAC6DA | |||
| 1932 | msiexec.exe | C:\Windows\Installer\MSI7315.tmp | executable | |
MD5:DF6D353853F28E4C4C0464B83F5220F2 | SHA256:DC64604E2A5DD9F1C01FD583F847D871269D680F1241644DB0828E3ADAF7067B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
59
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1440 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6876 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4100 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6484 | msiexec.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEQCBTkI%2BxI6x4NL94uMAHTSA | unknown | — | — | whitelisted |
4100 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6292 | msiexec.exe | GET | 200 | 13.224.191.223:80 | http://ocsp.r2m03.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQqHI%2BsdmapawQncL1rpCEZZ8gTSAQUVdkYX9IczAHhWLS%2Bq9lVQgHXLgICEA%2BjuCOT1x259UHHR62v01I%3D | unknown | — | — | unknown |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5732 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6292 | msiexec.exe | GET | 200 | 18.65.41.80:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkzUBtJnwJkc3SmanzgxeYU%3D | unknown | — | — | unknown |
6484 | msiexec.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDACP4PKUmHSg8coXrA%3D%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6876 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6880 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6876 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6876 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1440 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1440 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
go.microsoft.com |
| whitelisted |