| File name: | FYDLoad_inflvto_32.exe |
| Full analysis: | https://app.any.run/tasks/46ead865-cf4b-41d0-b6f2-1e4fc4922212 |
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2019, 11:59:13 |
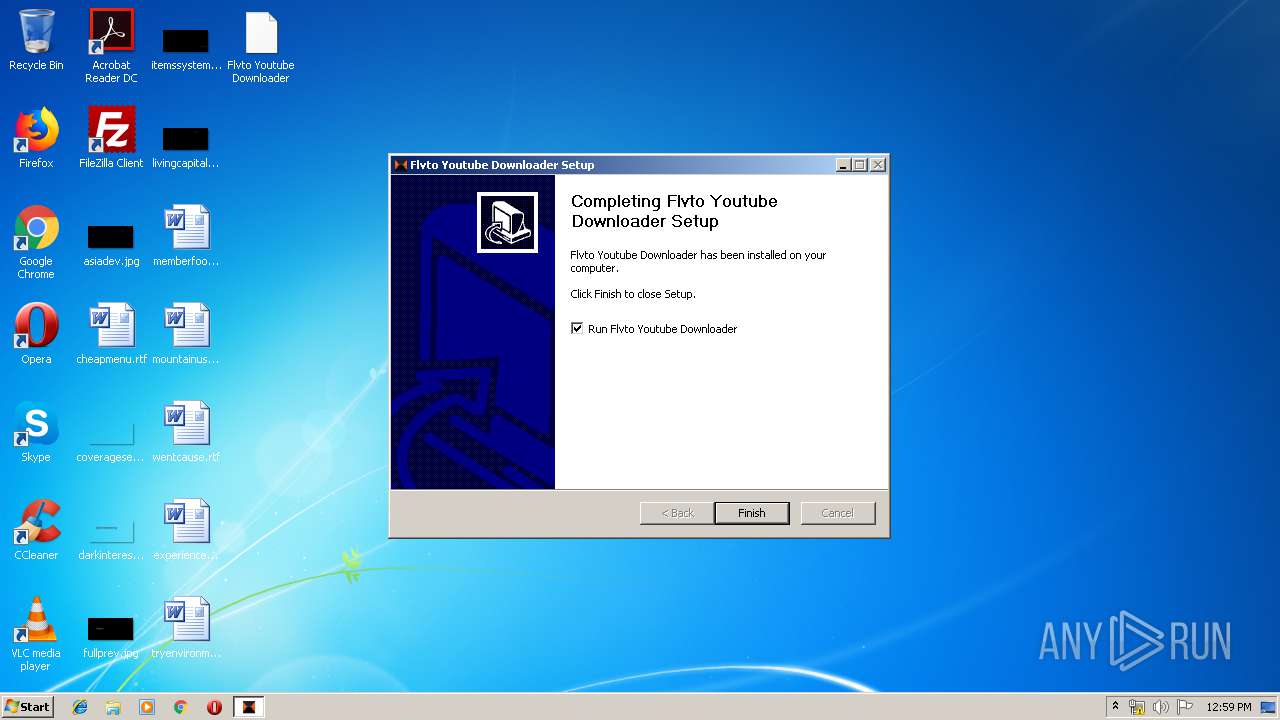
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
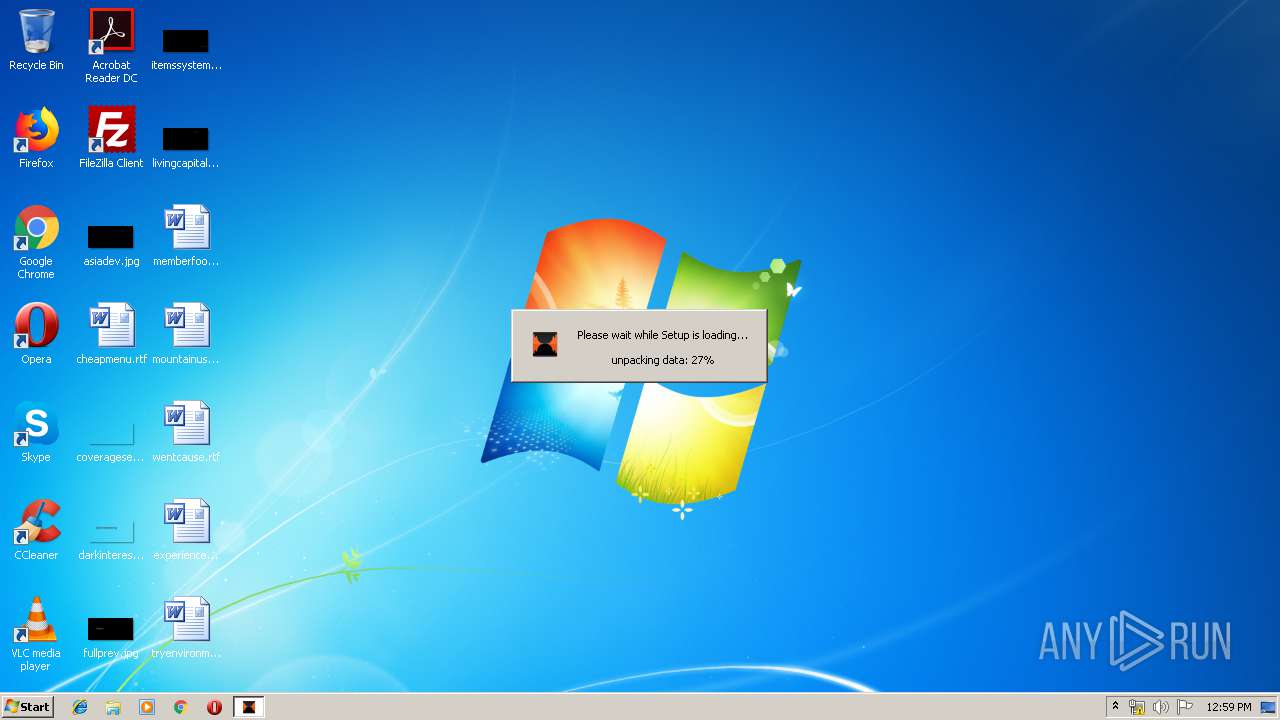
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 4A660D65CF519BBE32A8F930975CD8C0 |
| SHA1: | B8EC9AB1201CF05757C81823DB71B1BE01288FA4 |
| SHA256: | 4E77028D635FA32447986B996D712C6E0041AC490CD8CE951289EAD03E99BEE5 |
| SSDEEP: | 393216:f0cH51i3B/O32LTA7pvtn0jFCytwsVDLOl0dwevQ7y3ry9/:f0ewQGMv9BMHOKi7ur0/ |
MALICIOUS
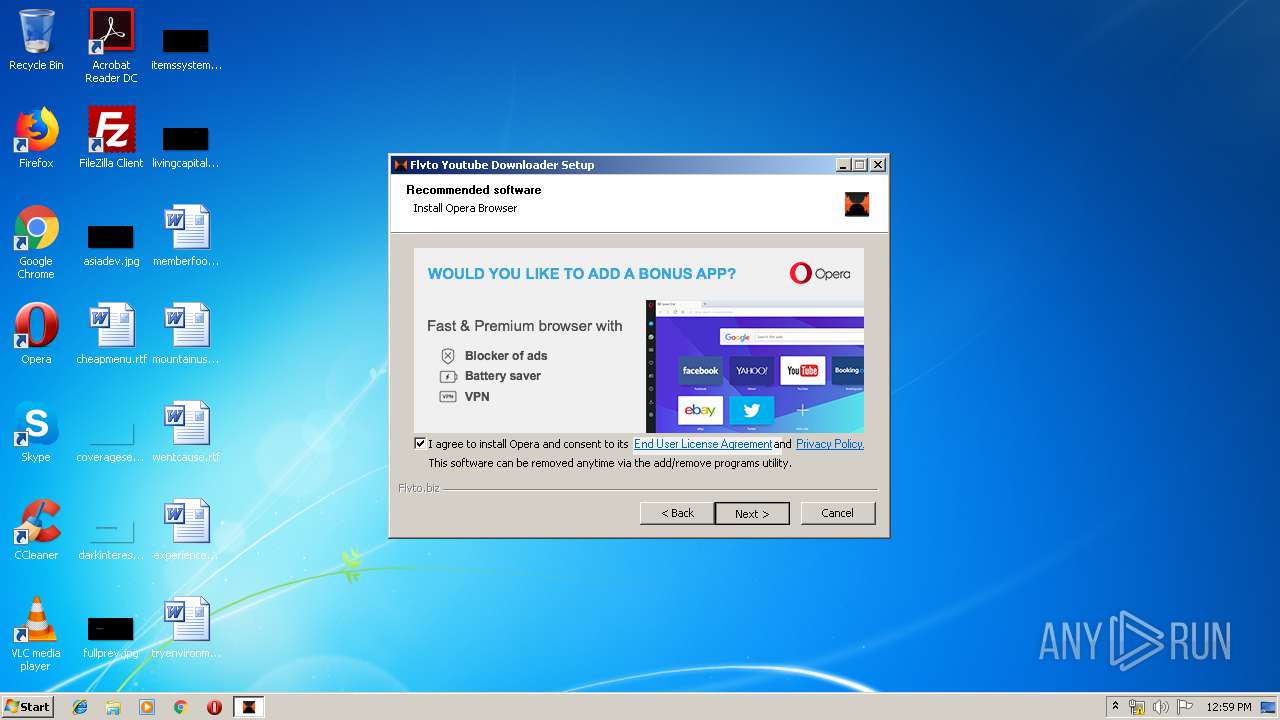
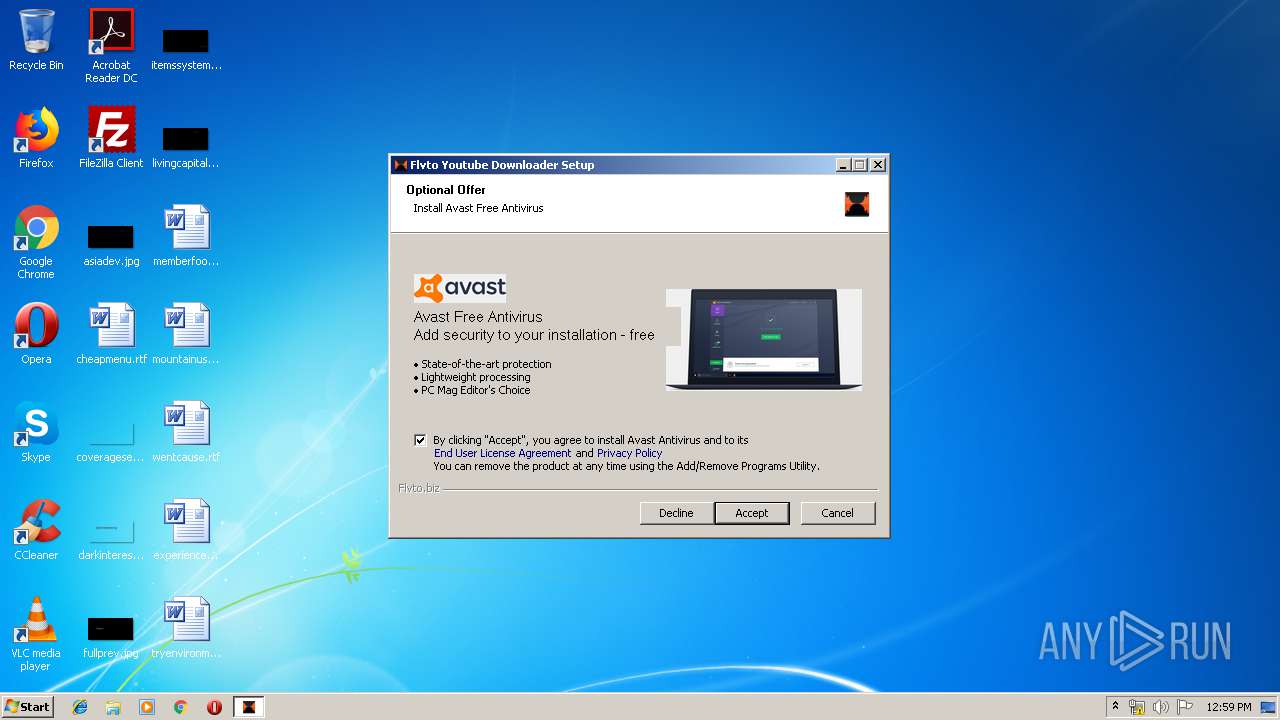
Loads dropped or rewritten executable
- FYDLoad_inflvto_32.exe (PID: 3768)
- FlvtoYoutubeDownloader.Redesign.exe (PID: 2832)
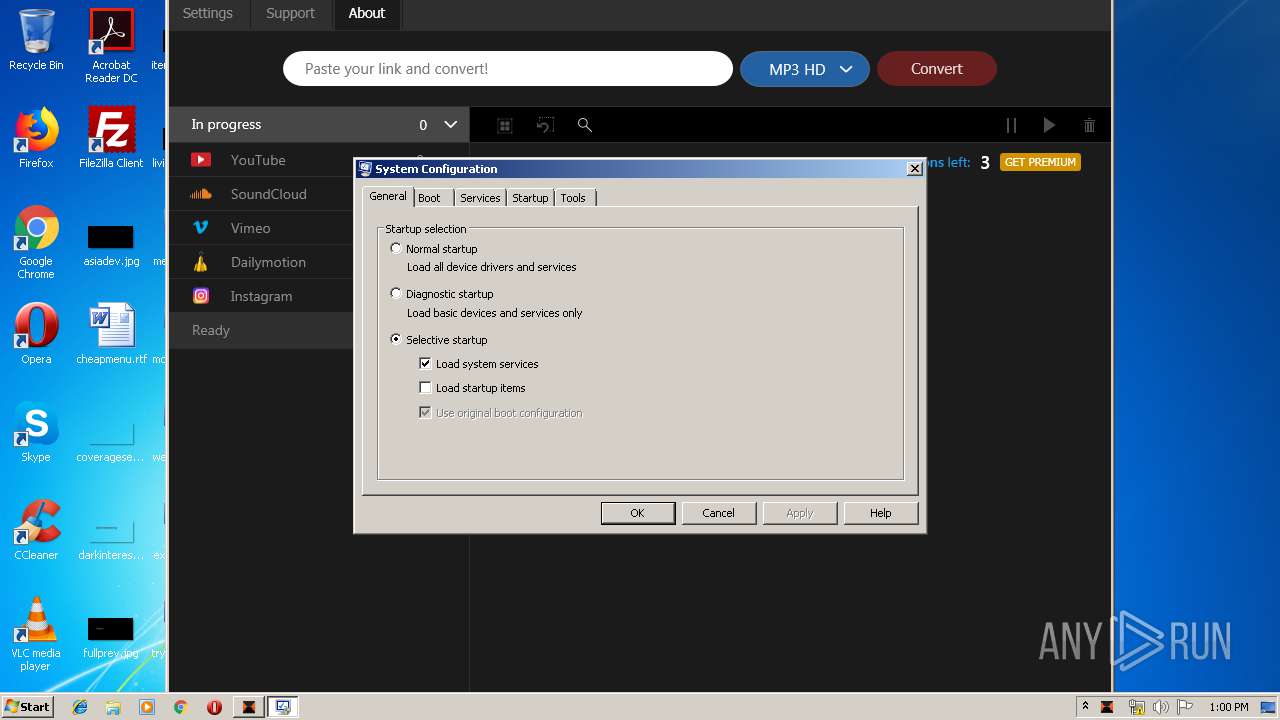
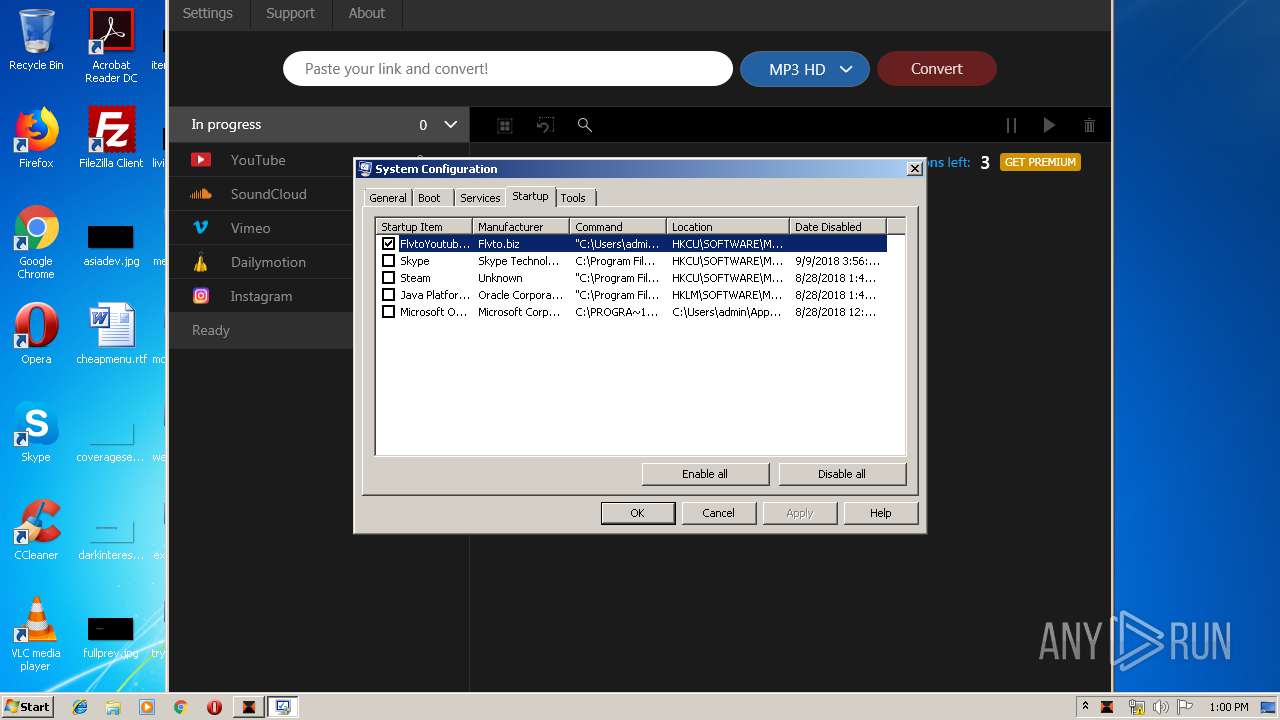
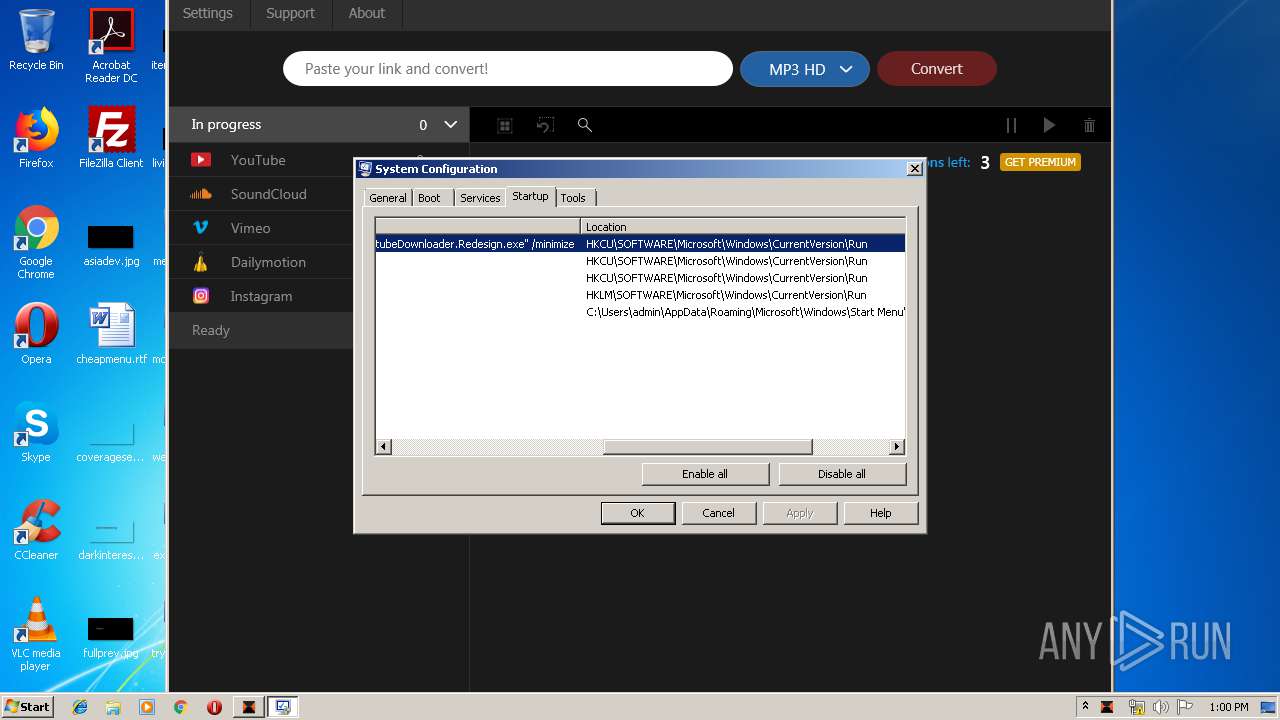
Changes the autorun value in the registry
- FYDLoad_inflvto_32.exe (PID: 3768)
Application was dropped or rewritten from another process
- FlvtoYoutubeDownloader.Redesign.exe (PID: 2832)
Changes settings of System certificates
- FlvtoYoutubeDownloader.Redesign.exe (PID: 2832)
SUSPICIOUS
Modifies the open verb of a shell class
- FYDLoad_inflvto_32.exe (PID: 3768)
Creates files in the user directory
- FYDLoad_inflvto_32.exe (PID: 3768)
Executable content was dropped or overwritten
- FYDLoad_inflvto_32.exe (PID: 3768)
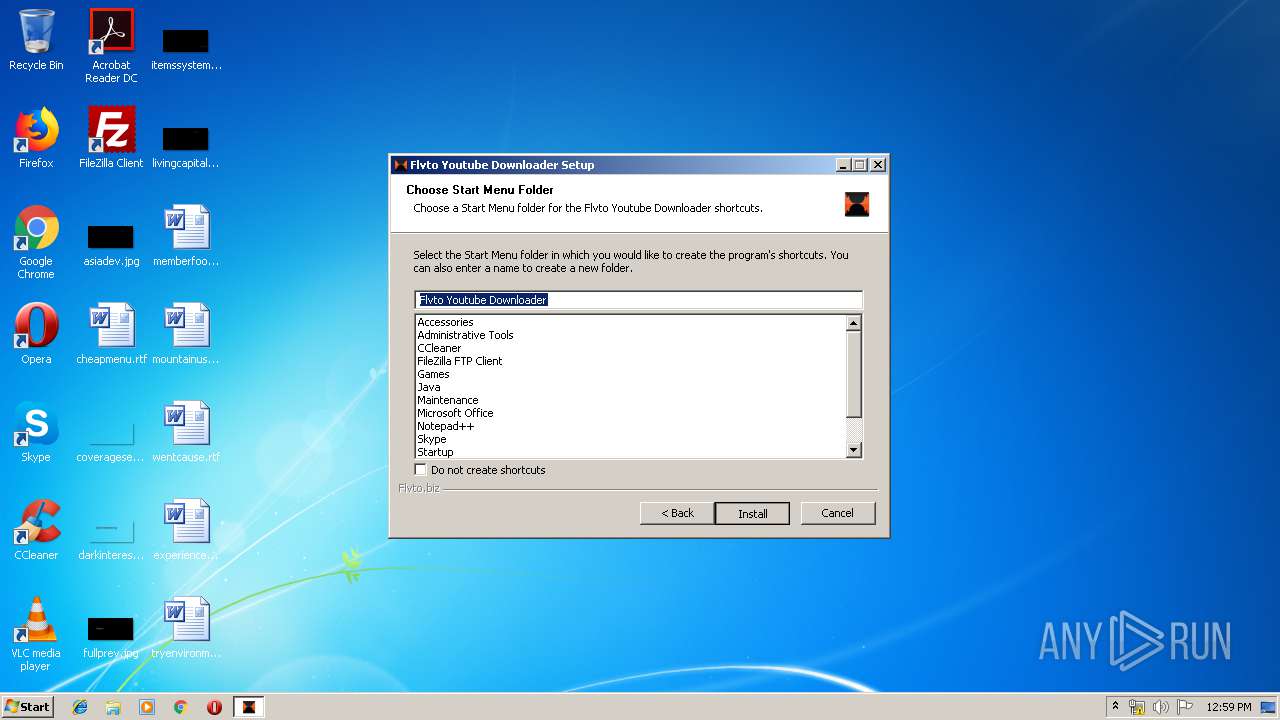
Creates a software uninstall entry
- FYDLoad_inflvto_32.exe (PID: 3768)
Reads Environment values
- FlvtoYoutubeDownloader.Redesign.exe (PID: 2832)
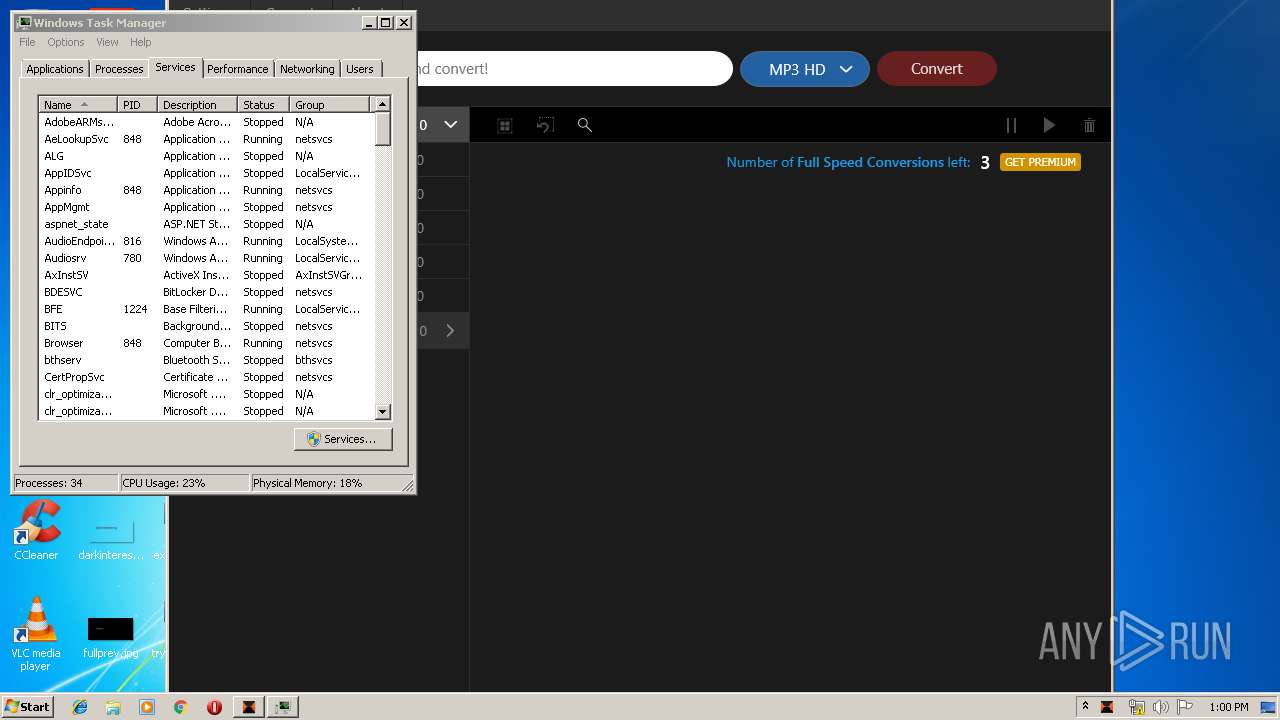
Low-level read access rights to disk partition
- msconfig.exe (PID: 2516)
Adds / modifies Windows certificates
- FlvtoYoutubeDownloader.Redesign.exe (PID: 2832)
INFO
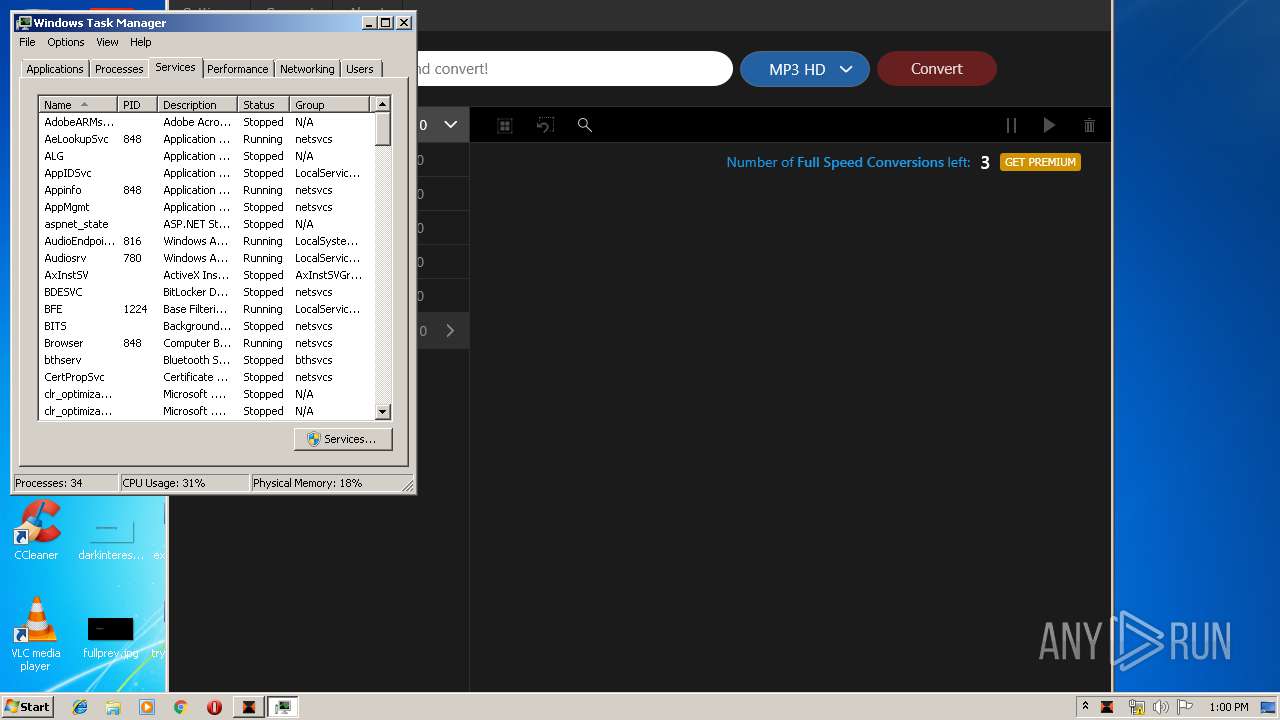
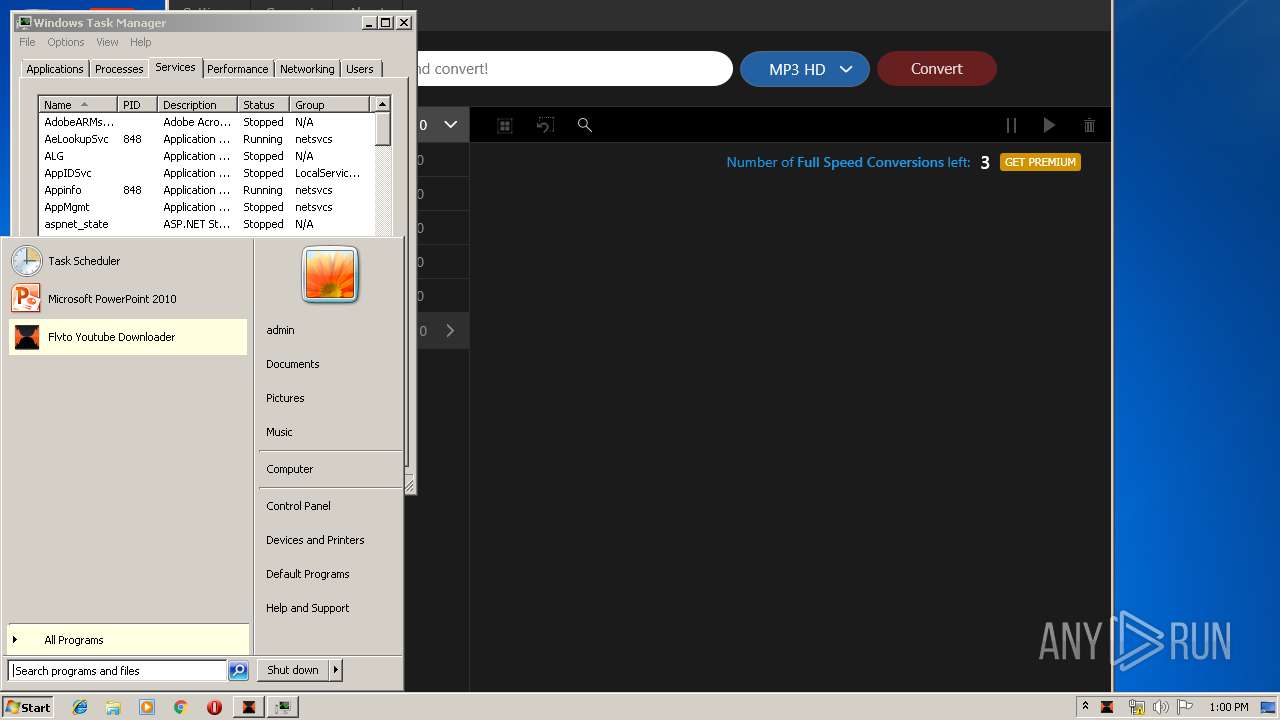
Manual execution by user
- taskmgr.exe (PID: 2392)
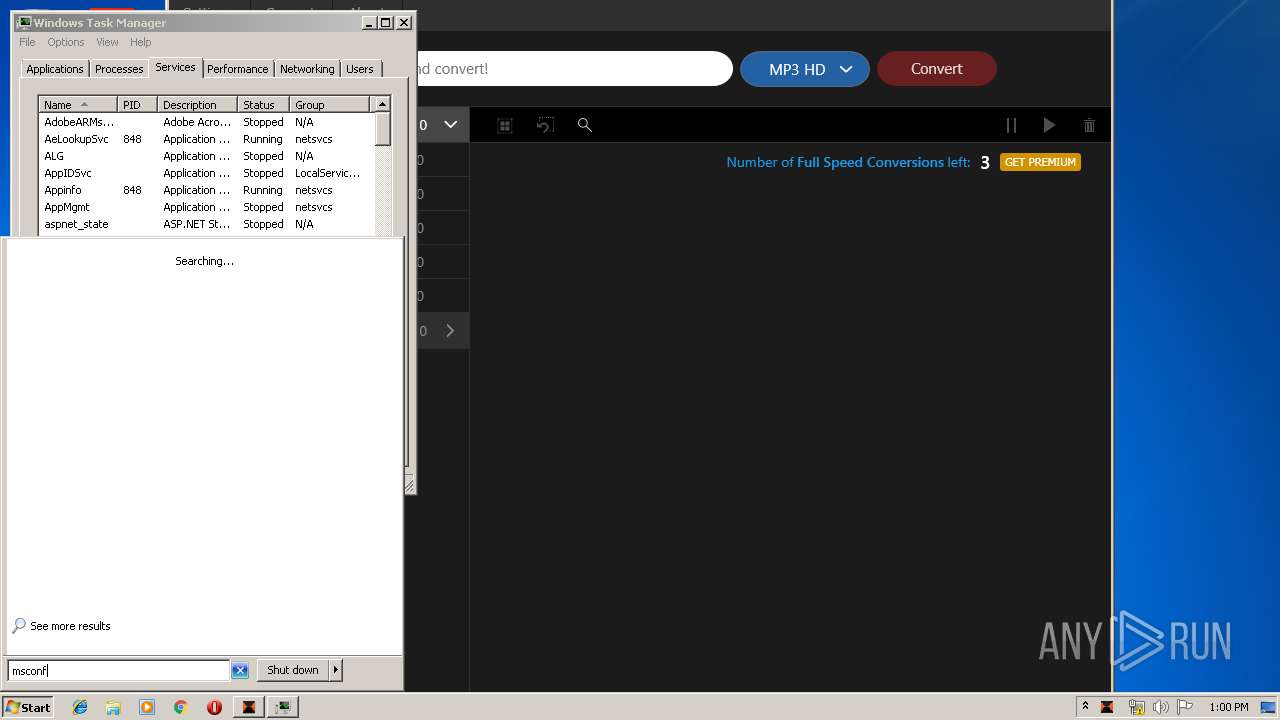
- msconfig.exe (PID: 3548)
- msconfig.exe (PID: 2516)
Dropped object may contain Bitcoin addresses
- FlvtoYoutubeDownloader.Redesign.exe (PID: 2832)
Reads settings of System Certificates
- FlvtoYoutubeDownloader.Redesign.exe (PID: 2832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:36+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x34a5 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.6.40 |
| ProductVersionNumber: | 1.3.6.40 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
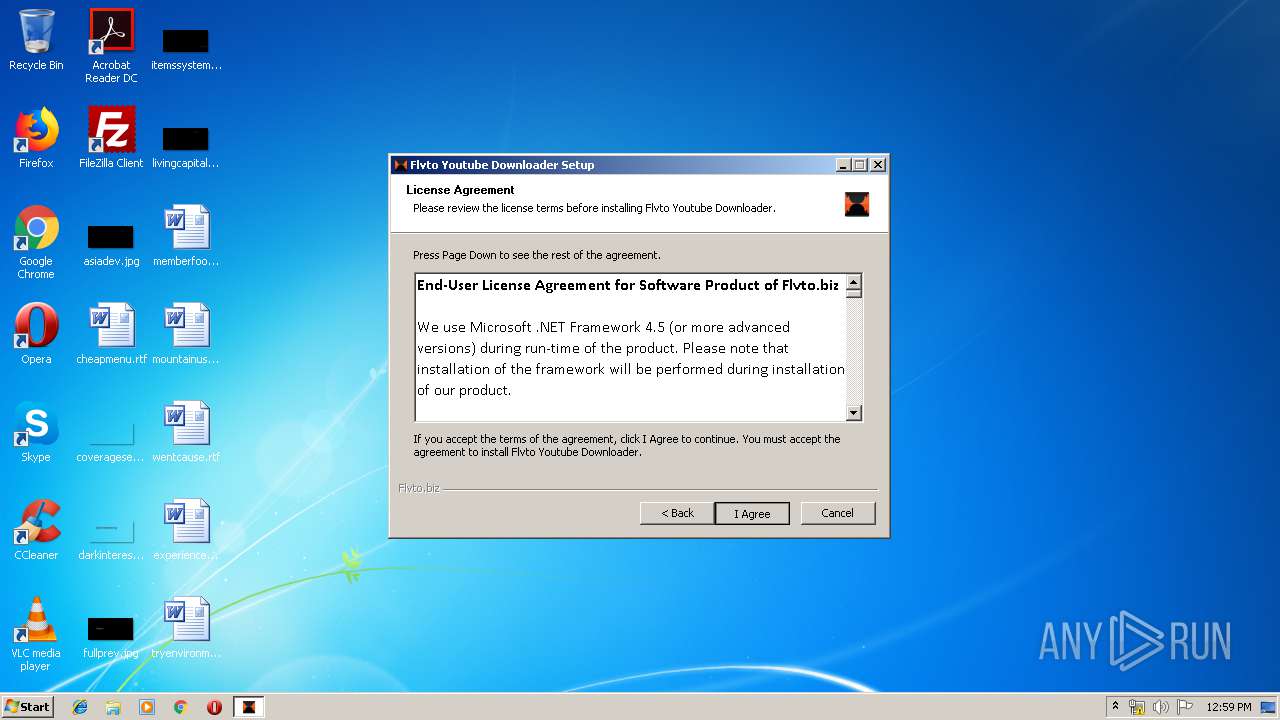
| CompanyName: | Flvto.biz |
| CompanyWebsite: | www.flvto.biz |
| FileDescription: | - |
| FileVersion: | 1.3.6 |
| LegalCopyright: | - |
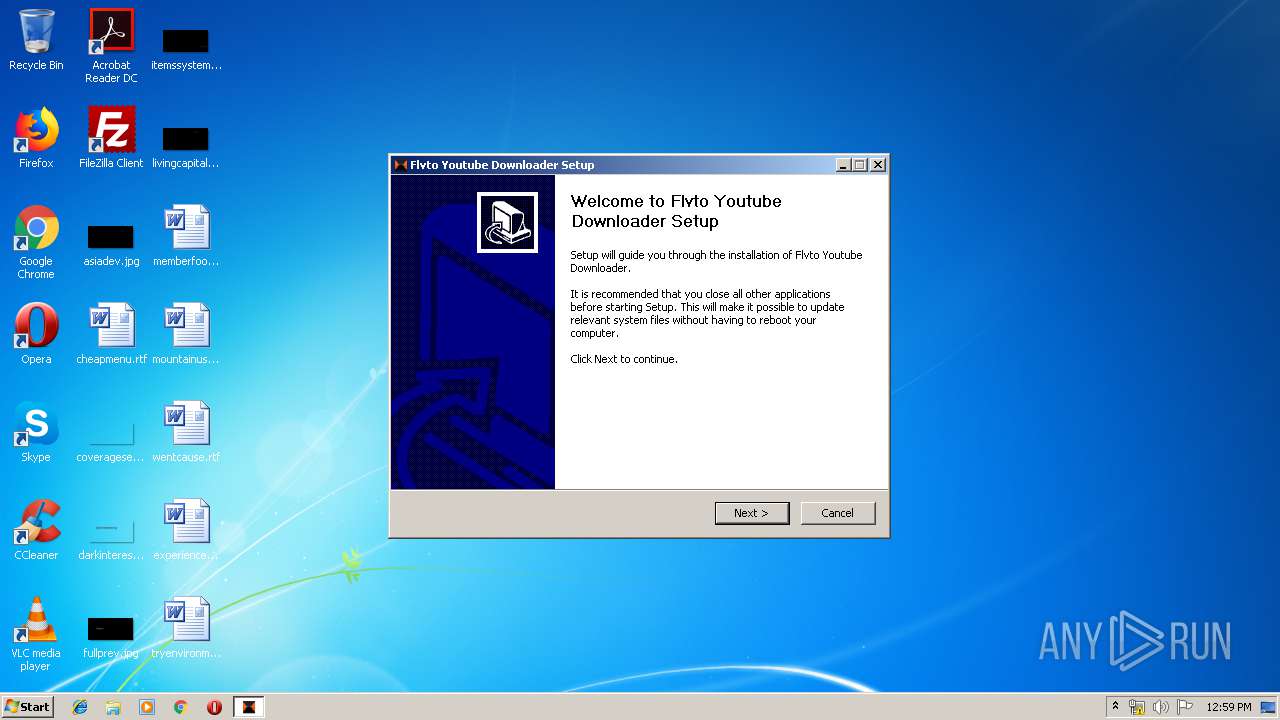
| ProductName: | Flvto Youtube Downloader |
| ProductVersion: | 1.3.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:36 |
| Detected languages: |
|
| CompanyName: | Flvto.biz |
| CompanyWebsite: | www.flvto.biz |
| FileDescription: | - |
| FileVersion: | 1.3.6 |
| LegalCopyright: | - |
| ProductName: | Flvto Youtube Downloader |
| ProductVersion: | 1.3.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006409 | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41619 |
.rdata | 0x00008000 | 0x00001396 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15491 |
.data | 0x0000A000 | 0x00020358 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.0044 |
.ndata | 0x0002B000 | 0x00055000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00080000 | 0x0001AD78 | 0x0001AE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.35614 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29627 | 1066 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.21204 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 4.43687 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 4.36616 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 5.21587 | 2440 | UNKNOWN | English - United States | RT_ICON |
6 | 4.44378 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.93166 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
46
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2392 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2516 | "C:\Windows\system32\msconfig.exe" | C:\Windows\system32\msconfig.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: System Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
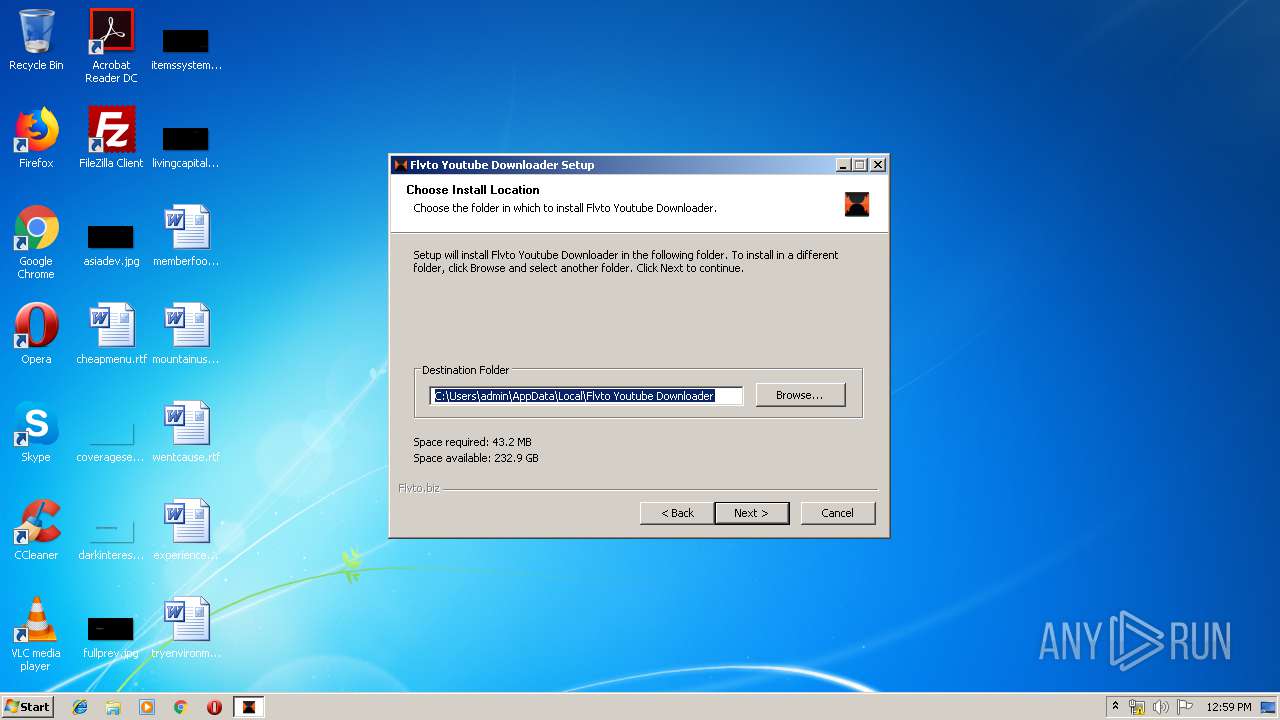
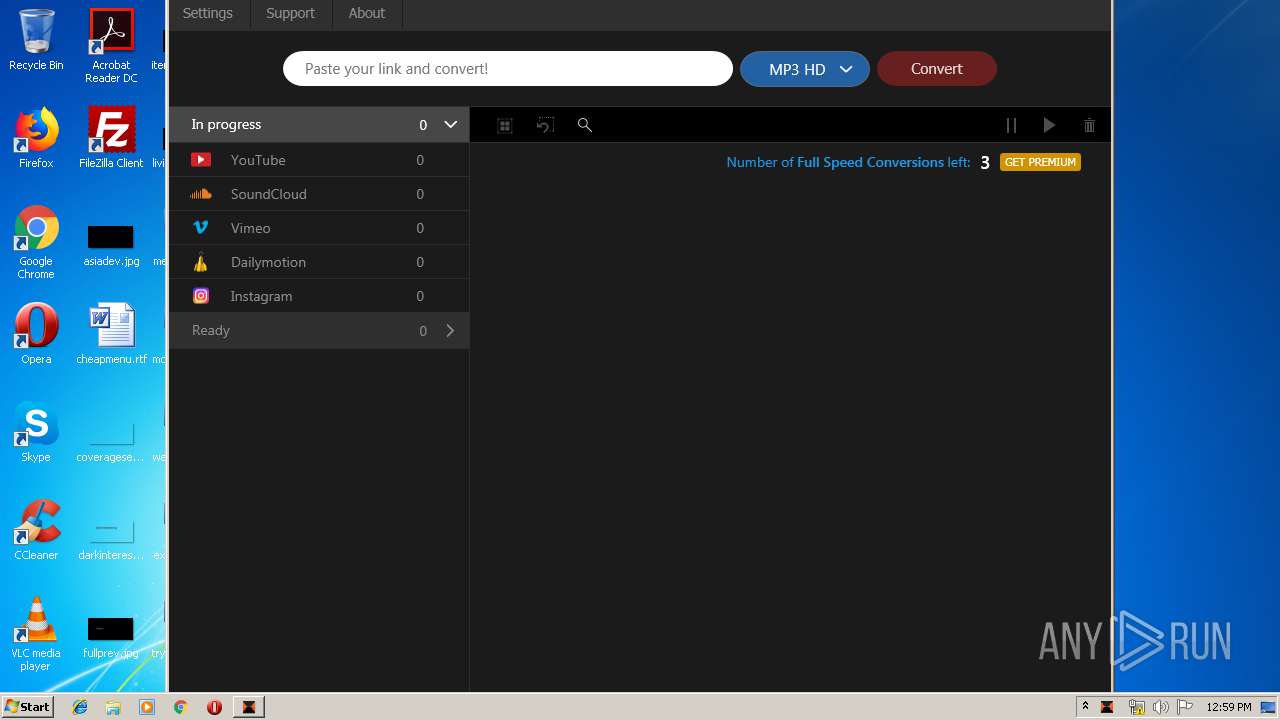
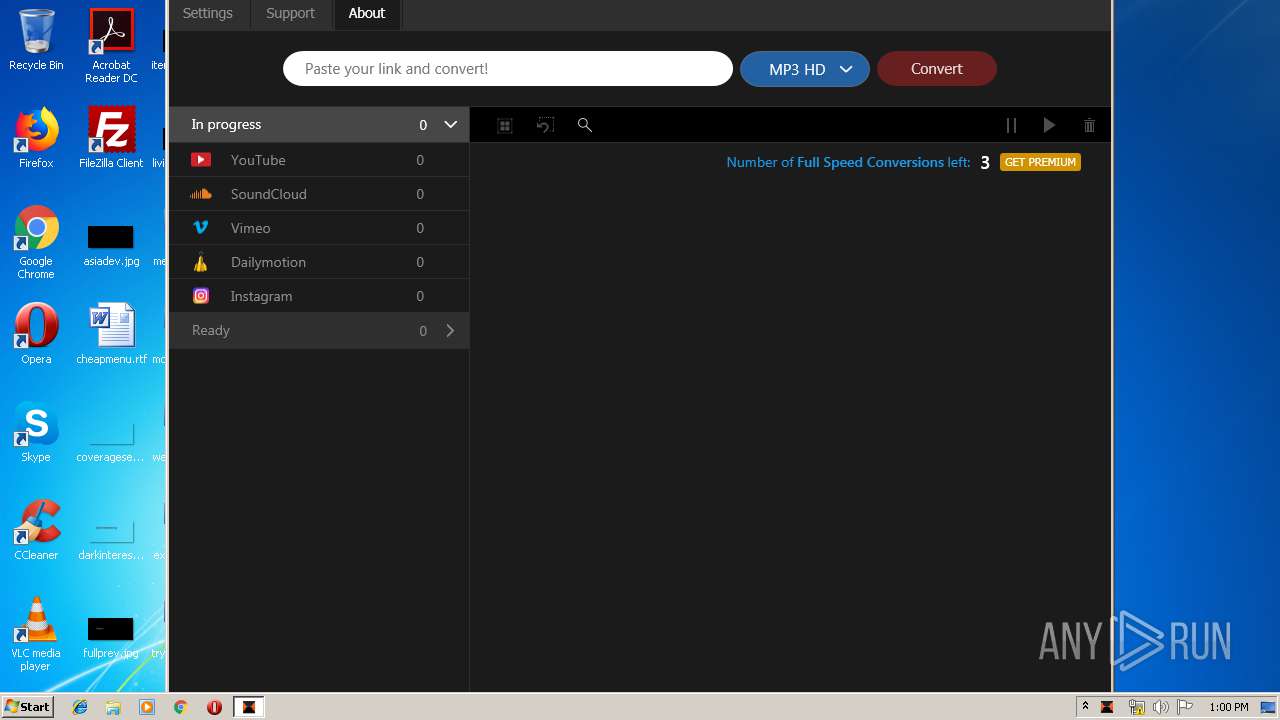
| 2832 | "C:\Users\admin\AppData\Local\Flvto Youtube Downloader\FlvtoYoutubeDownloader.Redesign.exe" | C:\Users\admin\AppData\Local\Flvto Youtube Downloader\FlvtoYoutubeDownloader.Redesign.exe | FYDLoad_inflvto_32.exe | ||||||||||||
User: admin Company: Flvto.biz Integrity Level: HIGH Description: FlvtoYoutubeDownloader.Redesign Exit code: 0 Version: 1.3.6.8 Modules
| |||||||||||||||
| 3416 | "C:\Users\admin\AppData\Local\Temp\FYDLoad_inflvto_32.exe" | C:\Users\admin\AppData\Local\Temp\FYDLoad_inflvto_32.exe | — | explorer.exe | |||||||||||
User: admin Company: Flvto.biz Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.3.6 Modules
| |||||||||||||||
| 3548 | "C:\Windows\system32\msconfig.exe" | C:\Windows\system32\msconfig.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: System Configuration Utility Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3768 | "C:\Users\admin\AppData\Local\Temp\FYDLoad_inflvto_32.exe" | C:\Users\admin\AppData\Local\Temp\FYDLoad_inflvto_32.exe | explorer.exe | ||||||||||||
User: admin Company: Flvto.biz Integrity Level: HIGH Exit code: 0 Version: 1.3.6 Modules
| |||||||||||||||
Total events
621
Read events
549
Write events
72
Delete events
0
Modification events
| (PID) Process: | (3768) FYDLoad_inflvto_32.exe | Key: | HKEY_CURRENT_USER\Software\FlvtoConverter |
| Operation: | write | Name: | Guid |
Value: 67e6c5ae-616d-d4a0-c300-000000b1b1 | |||
| (PID) Process: | (3768) FYDLoad_inflvto_32.exe | Key: | HKEY_CURRENT_USER\Software\FlvtoConverter |
| Operation: | write | Name: | filepath |
Value: FYDLoad_inflvto_32%2Eexe | |||
| (PID) Process: | (3768) FYDLoad_inflvto_32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FYDLoad_inflvto_32_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3768) FYDLoad_inflvto_32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FYDLoad_inflvto_32_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3768) FYDLoad_inflvto_32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FYDLoad_inflvto_32_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3768) FYDLoad_inflvto_32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FYDLoad_inflvto_32_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3768) FYDLoad_inflvto_32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FYDLoad_inflvto_32_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3768) FYDLoad_inflvto_32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FYDLoad_inflvto_32_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3768) FYDLoad_inflvto_32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FYDLoad_inflvto_32_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3768) FYDLoad_inflvto_32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FYDLoad_inflvto_32_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
70
Suspicious files
4
Text files
17
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3768 | FYDLoad_inflvto_32.exe | C:\Users\admin\AppData\Local\Temp\nss134.tmp\Dialer.dll | executable | |
MD5:— | SHA256:— | |||
| 3768 | FYDLoad_inflvto_32.exe | C:\Users\admin\AppData\Local\Temp\nss134.tmp\avast-logo-filled-gray-92x29.bmp | image | |
MD5:— | SHA256:— | |||
| 3768 | FYDLoad_inflvto_32.exe | C:\Users\admin\AppData\Local\Temp\nss134.tmp\laptop-en-filled-gray-196x102.bmp | image | |
MD5:— | SHA256:— | |||
| 3768 | FYDLoad_inflvto_32.exe | C:\Users\admin\AppData\Local\Temp\nss134.tmp\banner.bmp | image | |
MD5:— | SHA256:— | |||
| 3768 | FYDLoad_inflvto_32.exe | C:\Users\admin\AppData\Local\Temp\nss134.tmp\INetC.dll | executable | |
MD5:40D7ECA32B2F4D29DB98715DD45BFAC5 | SHA256:85E03805F90F72257DD41BFDAA186237218BBB0EC410AD3B6576A88EA11DCCB9 | |||
| 3768 | FYDLoad_inflvto_32.exe | C:\Users\admin\AppData\Local\Temp\nss134.tmp\System.dll | executable | |
MD5:0D7AD4F45DC6F5AA87F606D0331C6901 | SHA256:3EB38AE99653A7DBC724132EE240F6E5C4AF4BFE7C01D31D23FAF373F9F2EACA | |||
| 3768 | FYDLoad_inflvto_32.exe | C:\Users\admin\AppData\Local\Temp\nss134.tmp\nsDialogs.dll | executable | |
MD5:466179E1C8EE8A1FF5E4427DBB6C4A01 | SHA256:1E40211AF65923C2F4FD02CE021458A7745D28E2F383835E3015E96575632172 | |||
| 3768 | FYDLoad_inflvto_32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\collect[1] | text | |
MD5:E0AA021E21DDDBD6D8CECEC71E9CF564 | SHA256:565339BC4D33D72817B583024112EB7F5CDF3E5EEF0252D6EC1B9C9A94E12BB3 | |||
| 3768 | FYDLoad_inflvto_32.exe | C:\Users\admin\AppData\Local\Temp\nss134.tmp\nsProcess.dll | executable | |
MD5:F0438A894F3A7E01A4AAE8D1B5DD0289 | SHA256:30C6C3DD3CC7FCEA6E6081CE821ADC7B2888542DAE30BF00E881C0A105EB4D11 | |||
| 3768 | FYDLoad_inflvto_32.exe | C:\Users\admin\AppData\Local\Temp\nss134.tmp\fin.txt | text | |
MD5:E0AA021E21DDDBD6D8CECEC71E9CF564 | SHA256:565339BC4D33D72817B583024112EB7F5CDF3E5EEF0252D6EC1B9C9A94E12BB3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
9
DNS requests
9
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2832 | FlvtoYoutubeDownloader.Redesign.exe | GET | 200 | 95.216.164.80:80 | http://pay.flvtool.com/paddle/is-active-user?device_guid=67e6c5ae-616d-d4a0-c300-000000b1b1 | DE | text | 18 b | unknown |
2832 | FlvtoYoutubeDownloader.Redesign.exe | POST | 200 | 172.217.21.206:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
2832 | FlvtoYoutubeDownloader.Redesign.exe | GET | 200 | 95.216.164.80:80 | http://pay.flvtool.com/paddle/is-active-user?device_guid=67e6c5ae-616d-d4a0-c300-000000b1b1 | DE | text | 18 b | unknown |
2832 | FlvtoYoutubeDownloader.Redesign.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
3768 | FYDLoad_inflvto_32.exe | GET | 200 | 94.130.238.205:80 | http://api.flvto.com/collect?v=1&tid=UA-304558-67&cid=67e6c5ae-616d-d4a0-c300-000000b1b1&t=event&ec=install&ea=finish_app_full&el=FYDLoad_inflvto_32%2Eexe | DE | text | 2 b | suspicious |
3768 | FYDLoad_inflvto_32.exe | GET | 200 | 94.130.238.205:80 | http://api.flvto.com/collect?v=1&tid=UA-304558-67&cid=67e6c5ae-616d-d4a0-c300-000000b1b1&t=event&ec=install&ea=install_app_full&el=FYDLoad_inflvto_32%2Eexe | DE | text | 2 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3768 | FYDLoad_inflvto_32.exe | 94.130.238.205:80 | api.flvto.com | Hetzner Online GmbH | DE | suspicious |
2832 | FlvtoYoutubeDownloader.Redesign.exe | 95.216.164.80:80 | pay.flvtool.com | Hetzner Online GmbH | DE | unknown |
— | — | 104.20.60.238:443 | checkout.paddle.com | Cloudflare Inc | US | shared |
2832 | FlvtoYoutubeDownloader.Redesign.exe | 205.185.216.42:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2832 | FlvtoYoutubeDownloader.Redesign.exe | 54.148.119.29:443 | api.amplitude.com | Amazon.com, Inc. | US | unknown |
2832 | FlvtoYoutubeDownloader.Redesign.exe | 104.20.0.53:443 | v3.paddleapi.com | Cloudflare Inc | US | shared |
2832 | FlvtoYoutubeDownloader.Redesign.exe | 94.130.238.208:443 | api.flvto.biz | Hetzner Online GmbH | DE | unknown |
— | — | 172.217.21.206:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2832 | FlvtoYoutubeDownloader.Redesign.exe | 104.20.1.53:443 | v3.paddleapi.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.flvto.com |
| suspicious |
pay.flvtool.com |
| unknown |
api.flvto.biz |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
api.amplitude.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
checkout.paddle.com |
| suspicious |
v3.paddleapi.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3768 | FYDLoad_inflvto_32.exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
3768 | FYDLoad_inflvto_32.exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |
3768 | FYDLoad_inflvto_32.exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
3768 | FYDLoad_inflvto_32.exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |
2 ETPRO signatures available at the full report