| download: | index.html |
| Full analysis: | https://app.any.run/tasks/c89e4fdb-22d7-4364-a67f-872af1486abc |
| Verdict: | No threats detected |
| Analysis date: | November 01, 2018, 01:54:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | 59D37926F8481380580AB2CFD7CAF46C |
| SHA1: | FB0F028C791FEA310188899C1C198A1620CC2D03 |
| SHA256: | 4E6D6C57633FBFB1E3C7B74FA3E9A73C904C7B14A190C9F8664EE3FBA3C7BA09 |
| SSDEEP: | 192:70DluR5Ibb4OYD2fD/dqy4vPlij+WHJwEVjlyW0p/iWAX7Oxy77LvCNOpruvtqOg:70ZuqE6znA/urlzvCbn/XDy |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
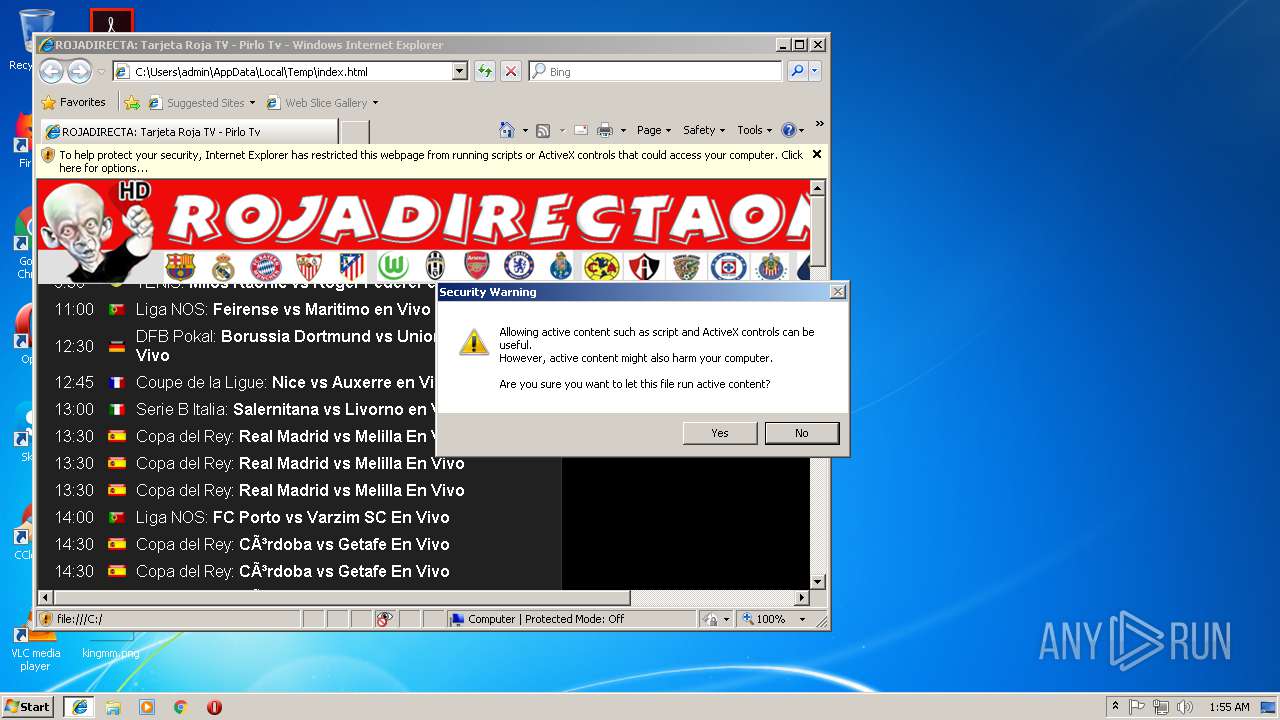
Reads internet explorer settings
- iexplore.exe (PID: 3416)
- iexplore.exe (PID: 2284)
Changes internet zones settings
- iexplore.exe (PID: 1000)
Reads Internet Cache Settings
- iexplore.exe (PID: 3416)
- iexplore.exe (PID: 2284)
Creates files in the user directory
- iexplore.exe (PID: 3416)
- iexplore.exe (PID: 2284)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3280)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2644)
- iexplore.exe (PID: 1000)
Changes settings of System certificates
- iexplore.exe (PID: 3416)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3416)
Application launched itself
- iexplore.exe (PID: 1000)
Reads settings of System Certificates
- iexplore.exe (PID: 2284)
- iexplore.exe (PID: 3416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
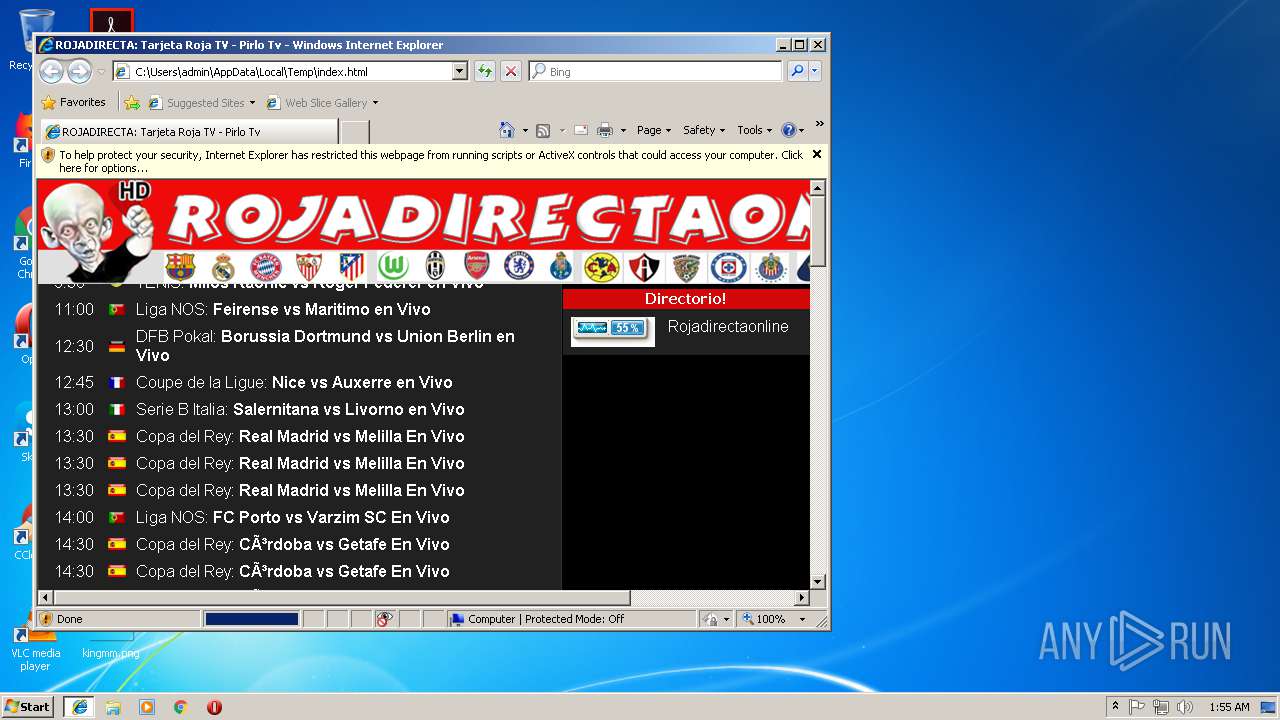
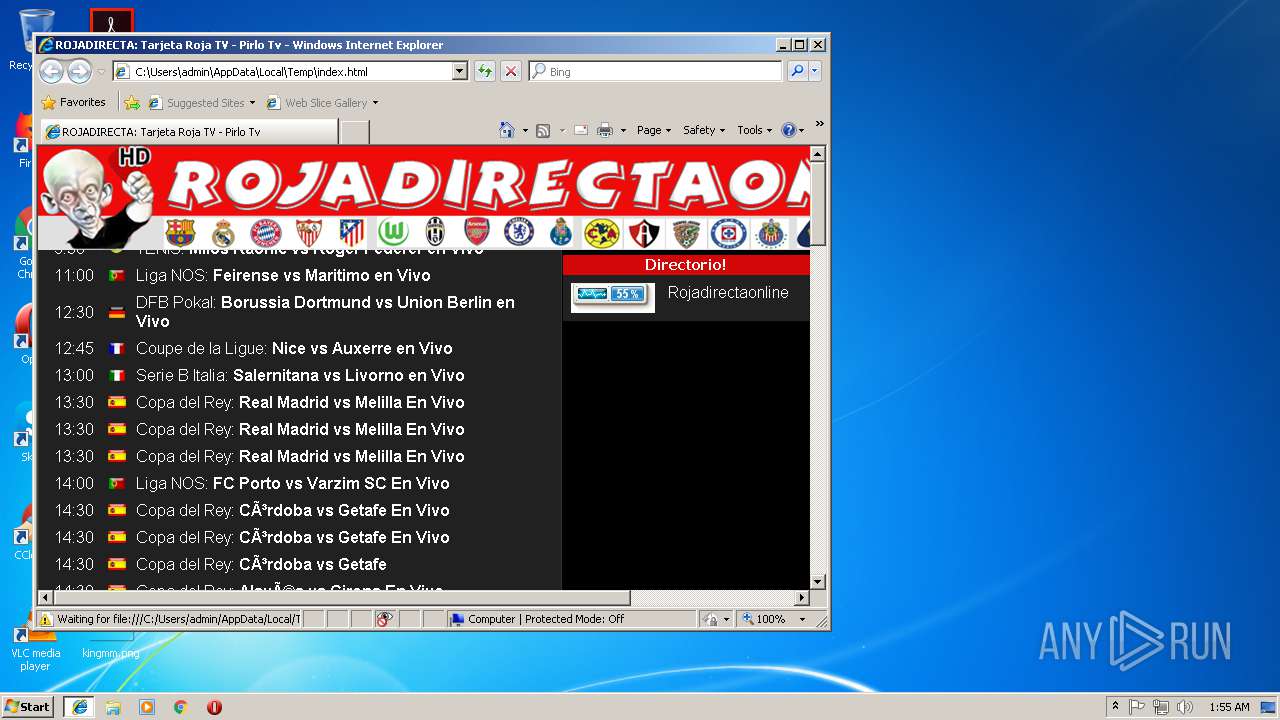
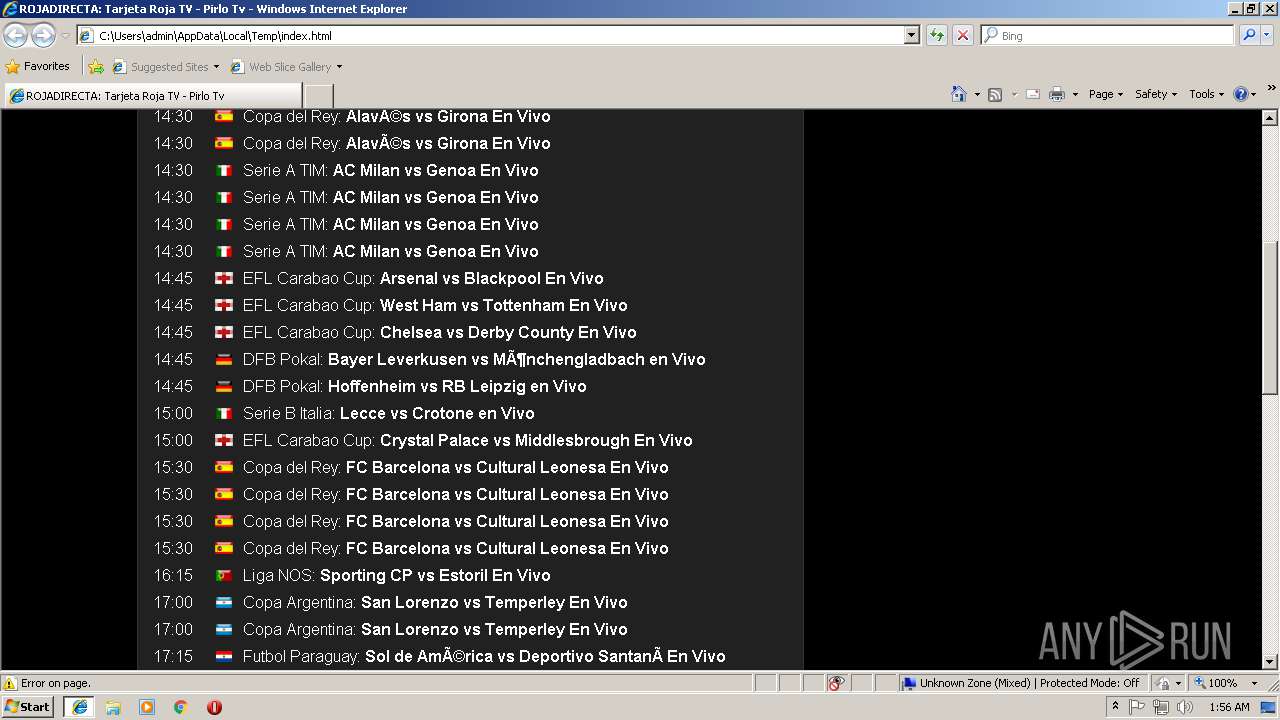
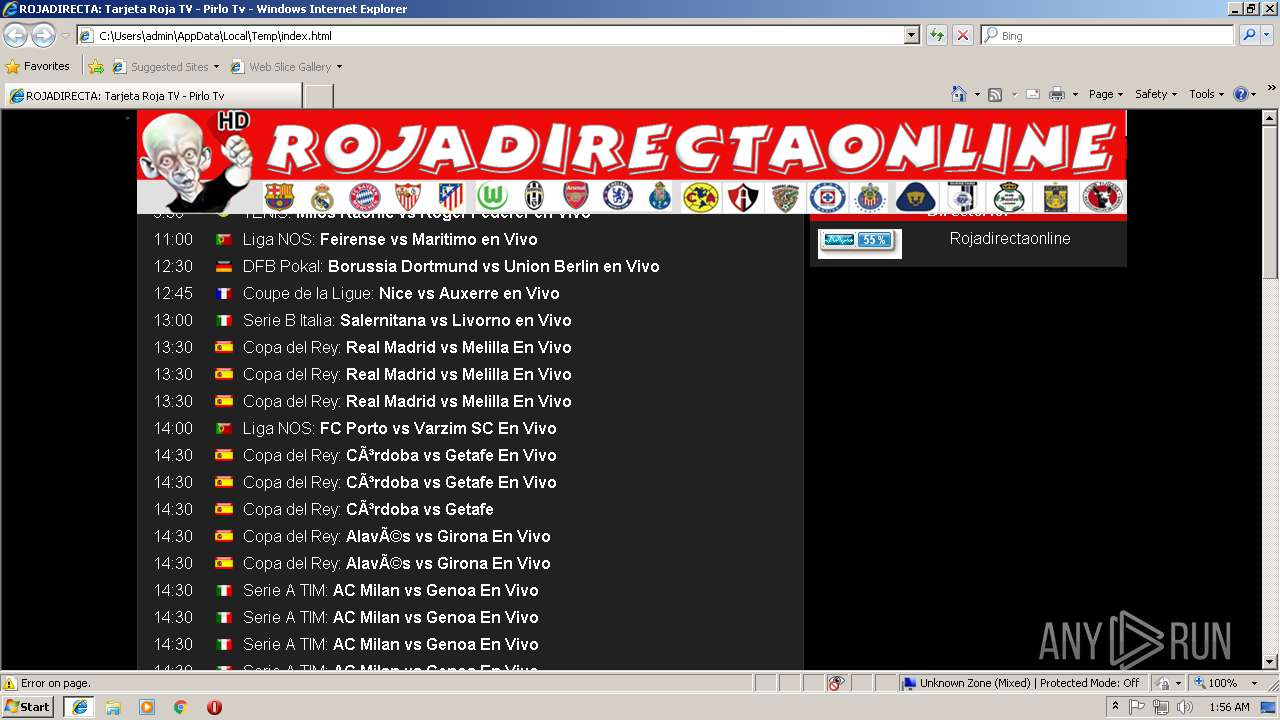
HTML
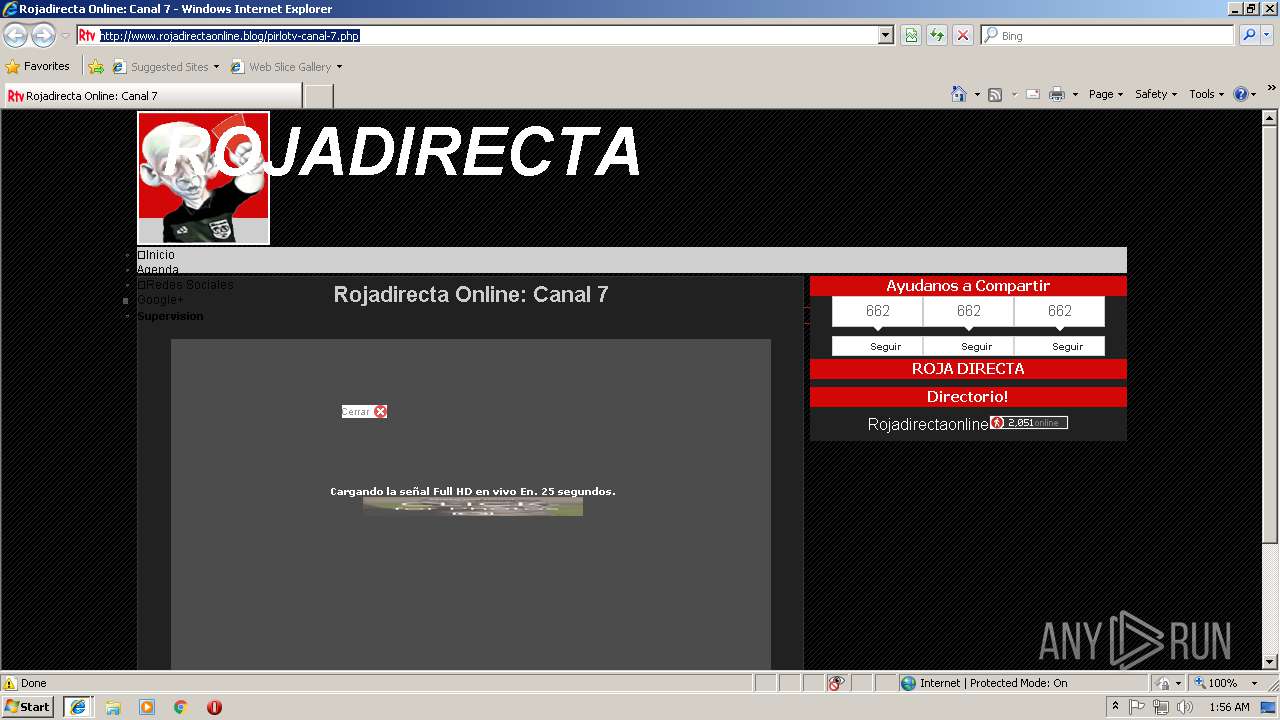
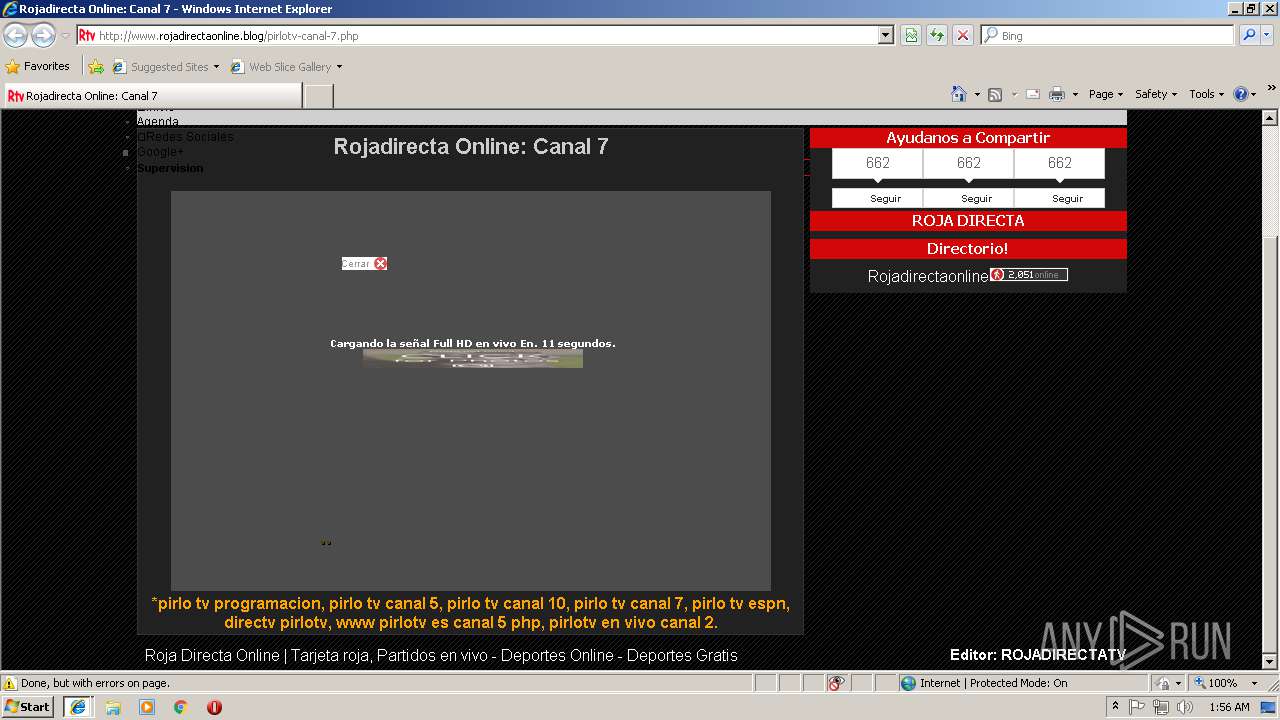
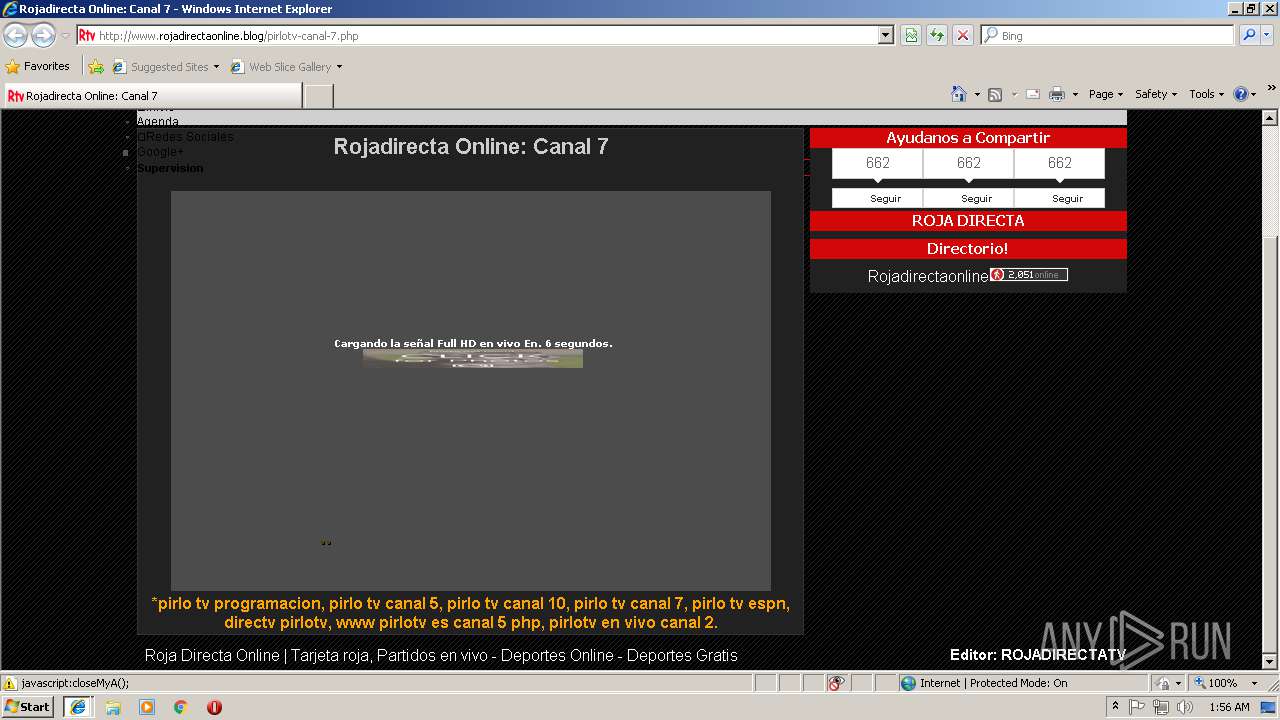
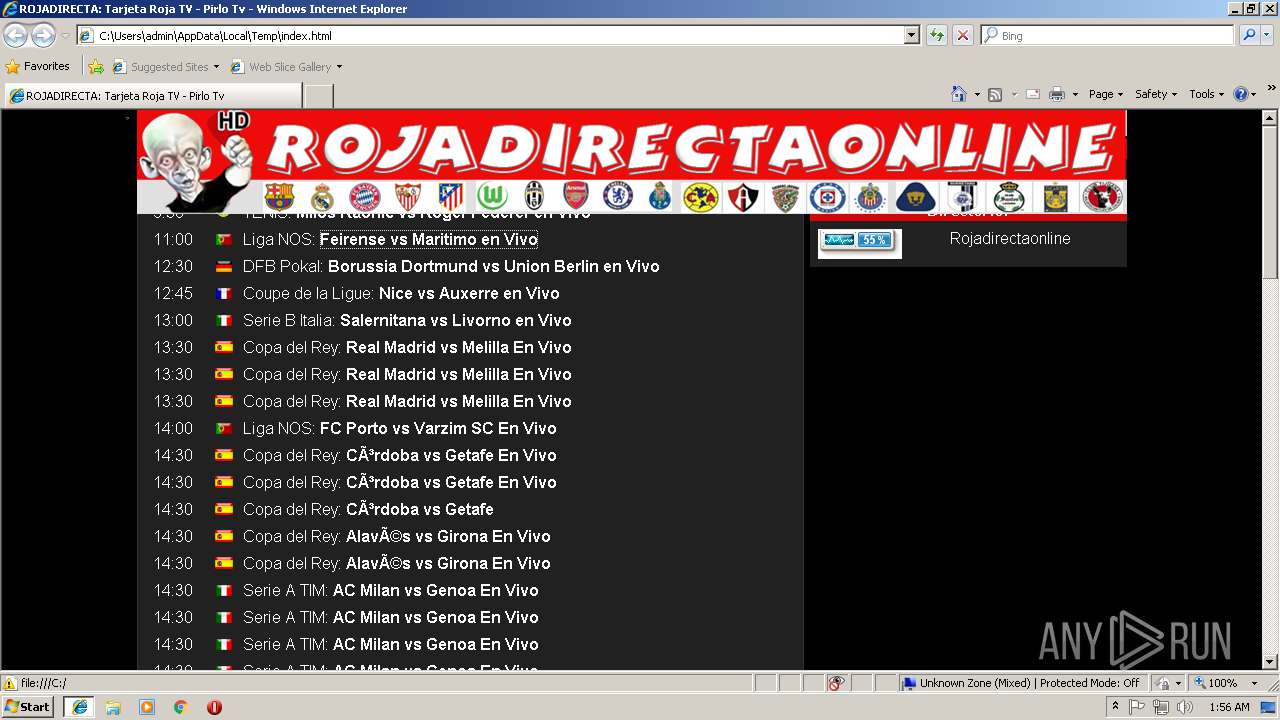
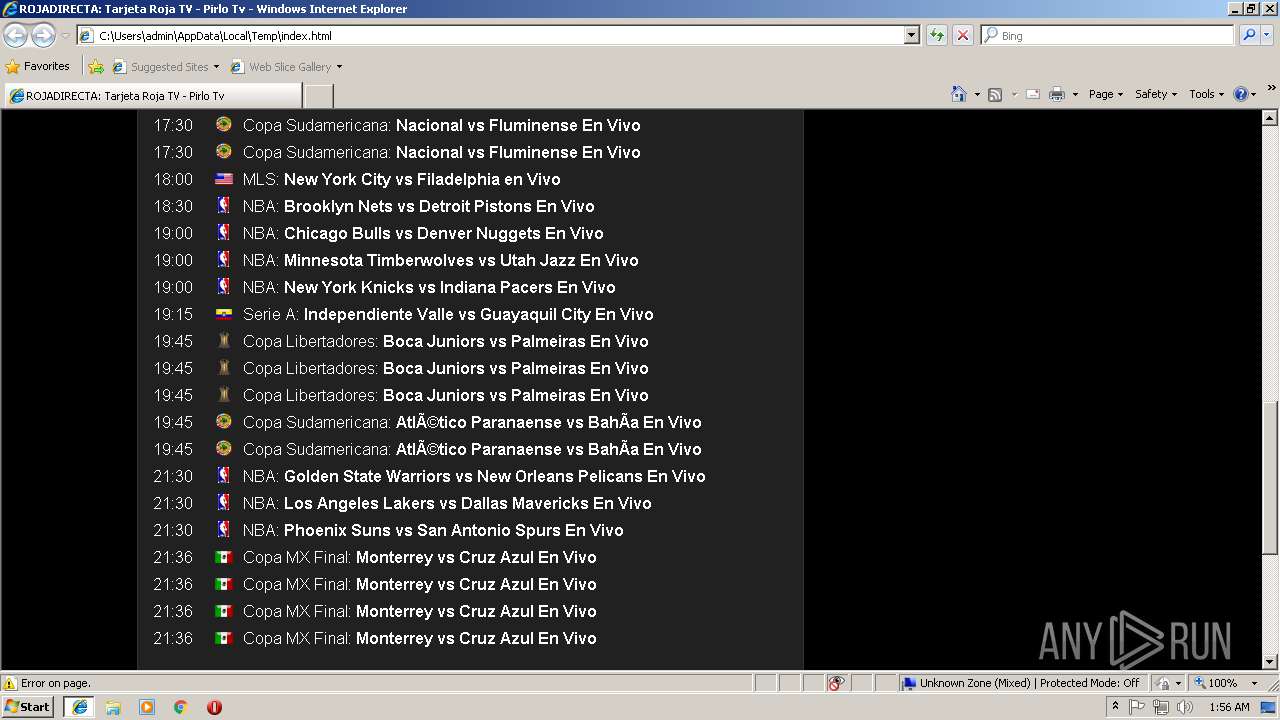
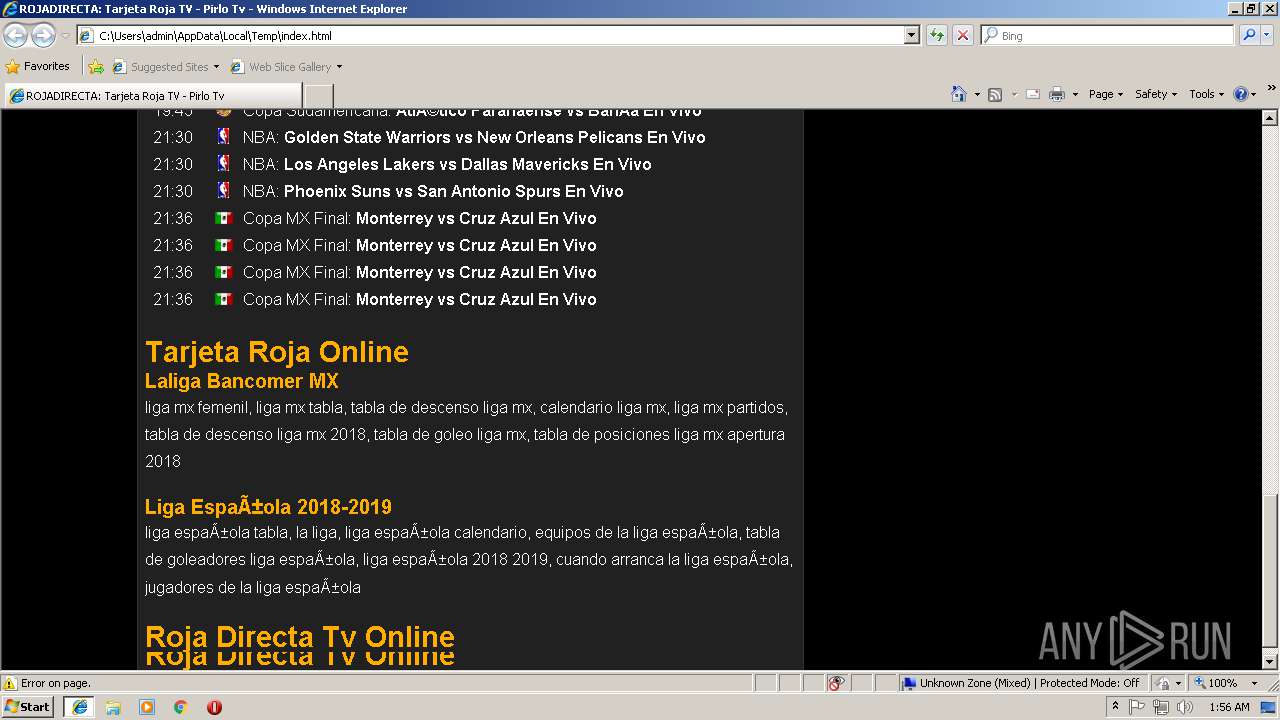
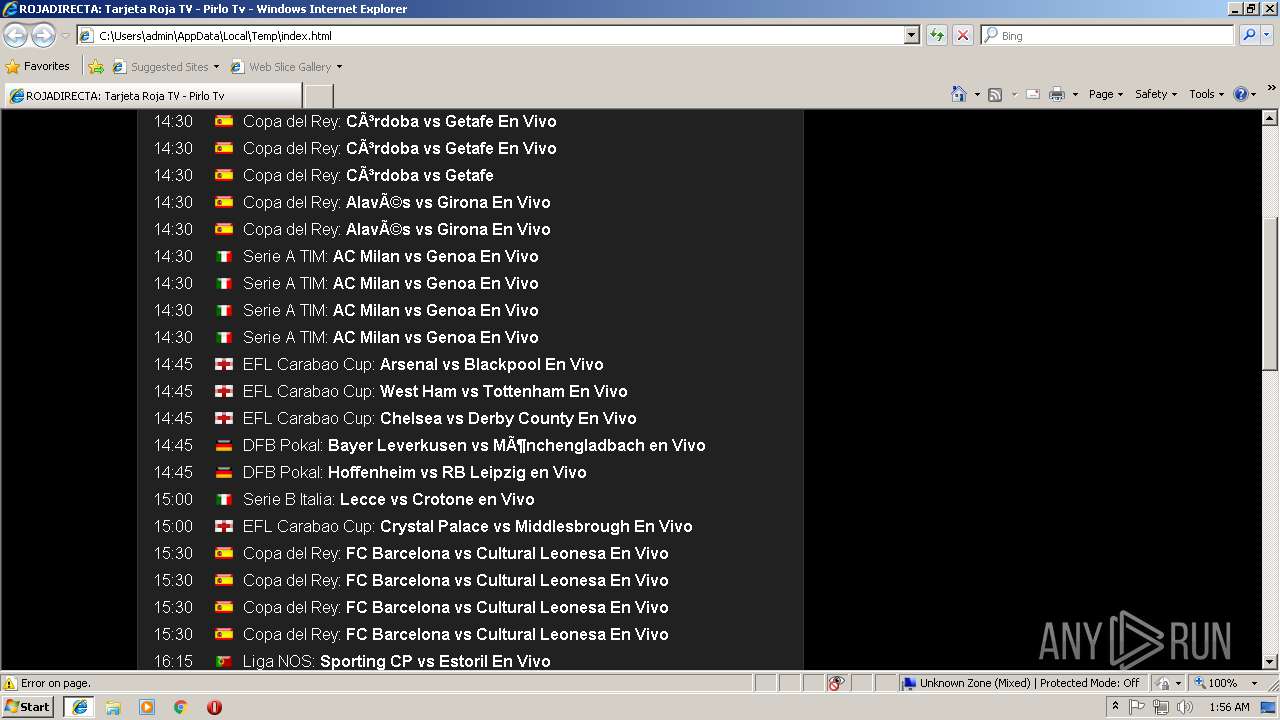
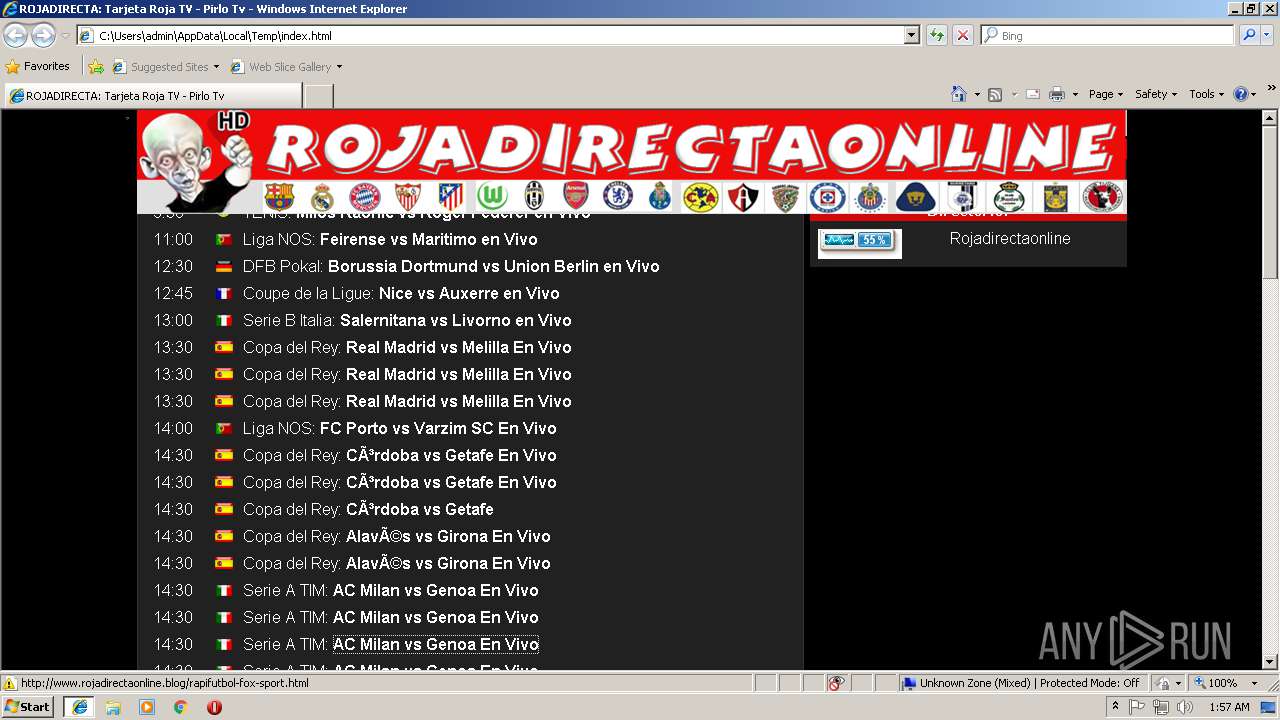
| Title: | ROJADIRECTA: Tarjeta Roja TV - Pirlo Tv |
|---|---|
| Description: | roja directa online, Tarjeta Roja Tv, ROJADIRECTA, rojadirecta tv, Elitegol, VipGoal, rojadirecta.es, rojadirecta.me, PirloTv, Partido en Vivo, Tv por Internet, Barcelona, Bayern Munich, Real Madrid, Juventus. |
| Keywords: | tarjeta roja, tarjetaroja, rojadirecta, roja tarjeta, laroja, Champions League, Barcelona, PSG, Bayern Munich, Real Madrid, Atlético Madrid y Mónaco vs Juventus, ver Justin TV, PirloTv, Ronaldo7, Ver Futbol Online, Futbol en vivo, Futbol por Internet, TarjetarojaTv, ver en vivo, tv online, Tarjetaroja, Tarjetaroja Tv, Roja Directa, Rojadirecta, Futbol online, Futbol en directo, Deportes online, resultados de Futbol. Television en vivo por internet, CMD en vivo, directv, La liga BBVA, Brasil 2014, TV en vivo, deportes, en vivo, psg, barca, online, Liga MX, 2015, ao vivo, jogo, assistir, watch live, Copa Pilsener |
| Author: | Roja Directa |
| Robots: | index,follow |
| GoogleBot: | index |
| Refresh: | 2000 |
| CacheControl: | max-age = 3600 |
| ContentLanguage: | es |
| Distribution: | global |
| yandexVerification: | fb53d7f6b8ca1d30 |
| viewport: | width=device-width, user-scalable=no, initial-scale=1.0, maximum-scale=1.0, minimum-scale=1.0 |
| twitterCard: | summary |
| twitterSite: | @Roja Directa |
| twitterTitle: | ROJADIRECTA: Tarjeta Roja TV - Pirlo Tv - Futbol en Vivo |
| twitterDescription: | rojdirecta, rojodirecto, Rojadirecta Tv Online, La Liga Santander 2018/19, Champions League, Barcelona, PSG, Bayern Munich, Real Madrid, Atlético Madrid y Mónaco vs Juventus en Directo Online Gratis, http://rojadirecta.com/, www.rojadirecta.org, roja direct, roja tv, futbol en vivo gratis por, www.tarjetaroja.com ver partidos, targetaroja, rojadirecto.com, http://www.rojadirecta.com/, rojadirecta.com ver partidos gratis, roja directa .com, rojadiecta, rojadirectagratis, rojadirecta partidos gratis, www.rojadirecta.com, roja directa futbol en vivo. |
| twitterImage: | http://www.rojadirectaonline.blog/Rojadirectaonline.png |
Total processes
38
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1000 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1000 CREDAT:268545 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2644 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3280 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3416 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1000 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 095
Read events
924
Write events
166
Delete events
5
Modification events
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {32ACBBC7-DD79-11E8-BFAB-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070B0004000100010037001900B703 | |||
Executable files
0
Suspicious files
10
Text files
148
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\suda[1].png | image | |
MD5:— | SHA256:— | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\rojadirectaonline[1].png | image | |
MD5:— | SHA256:— | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\fr[1].png | image | |
MD5:— | SHA256:— | |||
| 3416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\pt[1].png | image | |
MD5:— | SHA256:— | |||
| 3416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\en[1].png | image | |
MD5:— | SHA256:— | |||
| 3416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\platform[1].js | text | |
MD5:— | SHA256:— | |||
| 3416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\ar[1].png | image | |
MD5:— | SHA256:— | |||
| 3416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\D2YPIJ90\lib[1].png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
82
TCP/UDP connections
111
DNS requests
48
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3416 | iexplore.exe | GET | — | 67.202.94.86:80 | http://whos.amung.us/swidget/al3jk83qjo.png | US | — | — | whitelisted |
3416 | iexplore.exe | GET | 204 | 208.100.17.184:80 | http://ic.tynt.com/b/p?id=dozu_eBdKr6jrIaKkv7mNO&lm=0&ts=1541037353956&dn=TI&iso=1&img=http%3A%2F%2Fwww.rojadirectaonline.blog%2FRojadirectaonline.png&ct=ROJADIRECTA%20Online&t=ROJADIRECTA%3A%20Tarjeta%20Roja%20TV%20-%20Pirlo%20Tv | US | — | — | whitelisted |
3416 | iexplore.exe | GET | 204 | 208.100.17.184:80 | http://ic.tynt.com/b/p?id=dozu_eBdKr6jrIaKkv7mNO&lm=0&ts=1541037353956&dn=TI&iso=1&img=http%3A%2F%2Fwww.rojadirectaonline.blog%2FRojadirectaonline.png&ct=ROJADIRECTA%20Online | US | — | — | whitelisted |
3416 | iexplore.exe | GET | 204 | 208.100.17.184:80 | http://ic.tynt.com/b/p?id=dozu_eBdKr6jrIaKkv7mNO&lm=0&ts=1541037353956&dn=TI&iso=1&img=http%3A%2F%2Fwww.rojadirectaonline.blog%2FRojadirectaonline.png&ct=ROJADIRECTA%20Online&t=ROJADIRECTA%3A%20Tarjeta%20Roja%20TV%20-%20Pirlo%20Tv&cu=http%3A%2F%2Fwww.rojadirectaonline.blog%2F | US | — | — | whitelisted |
3416 | iexplore.exe | GET | 204 | 208.100.17.184:80 | http://ic.tynt.com/b/p?id=dozu_eBdKr6jrIaKkv7mNO&lm=0&ts=1541037353956&dn=TI&iso=1&img=http%3A%2F%2Fwww.rojadirectaonline.blog%2FRojadirectaonline.png | US | — | — | whitelisted |
3416 | iexplore.exe | GET | 204 | 208.100.17.184:80 | http://ic.tynt.com/b/p?id=dozu_eBdKr6jrIaKkv7mNO&lm=0&ts=1541037353956&dn=TI&iso=1 | US | — | — | whitelisted |
3416 | iexplore.exe | GET | 307 | 67.202.94.86:80 | http://whos.amung.us/swidget/al3jk83qjo.png | US | — | — | whitelisted |
3416 | iexplore.exe | GET | 307 | 67.202.94.86:80 | http://whos.amung.us/swidget/al3jk83qjo.png | US | — | — | whitelisted |
3416 | iexplore.exe | GET | 200 | 172.64.97.22:80 | http://www.rojadirectaonline.blog/rojadirectaonline.png | US | image | 111 Kb | shared |
3416 | iexplore.exe | GET | 200 | 185.225.208.133:80 | http://widgets.amung.us/small/20/2038.png | unknown | image | 340 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3416 | iexplore.exe | 178.162.223.114:443 | img.webme.com | Leaseweb Deutschland GmbH | DE | unknown |
3416 | iexplore.exe | 46.229.169.130:443 | webstatsdomain.org | DataWeb Global Group B.V. | US | unknown |
3416 | iexplore.exe | 172.64.97.22:80 | www.rojadirectaonline.blog | Cloudflare Inc | US | shared |
— | — | 216.58.205.137:137 | www.blogblog.com | Google Inc. | US | unknown |
4 | System | 216.58.205.137:445 | www.blogblog.com | Google Inc. | US | unknown |
3416 | iexplore.exe | 176.56.226.176:80 | www.rojadirecta.me | RouteLabel V.O.F. | NL | unknown |
1000 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3416 | iexplore.exe | 67.202.94.86:80 | whos.amung.us | Steadfast | US | suspicious |
3416 | iexplore.exe | 185.225.208.133:80 | widgets.amung.us | — | — | suspicious |
3416 | iexplore.exe | 104.16.87.26:80 | cdn.tynt.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
apis.google.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.rojadirectaonline.blog |
| unknown |
img.webme.com |
| unknown |
webstatsdomain.org |
| whitelisted |
www.blogblog.com |
| whitelisted |
www.rojadirecta.me |
| unknown |
whos.amung.us |
| whitelisted |
www.bing.com |
| whitelisted |
widgets.amung.us |
| whitelisted |