| URL: | http://totalsourceadp.com/ts/login.do |
| Full analysis: | https://app.any.run/tasks/b25eca12-078c-4236-89cf-799fb672d581 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 18:18:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3EAFD03D0FE3439F730467BD6DD710F1 |
| SHA1: | 1EA7FF24A716472C6C13078C08455AB3DE901130 |
| SHA256: | 4E626F6C2FEB5893EBEBAC6B407AC4649FB96808505DCBD1681481BB69AF50C7 |
| SSDEEP: | 3:N1KKKqNQXGI58n:CKhU758 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1720)
INFO
Reads the hosts file
- chrome.exe (PID: 1720)
- chrome.exe (PID: 3900)
Application launched itself
- chrome.exe (PID: 1720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
30
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,3636438212186767846,16619227975177386843,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6545956446347034650 --mojo-platform-channel-handle=4888 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,3636438212186767846,16619227975177386843,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14820785448086129330 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,3636438212186767846,16619227975177386843,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2802479804391170399 --mojo-platform-channel-handle=4520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,3636438212186767846,16619227975177386843,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=858849798244660712 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,3636438212186767846,16619227975177386843,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14329504417147588106 --mojo-platform-channel-handle=2920 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,3636438212186767846,16619227975177386843,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17126884890242388427 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2952 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,3636438212186767846,16619227975177386843,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4417877205868969541 --mojo-platform-channel-handle=4516 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://totalsourceadp.com/ts/login.do" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
595
Read events
511
Write events
79
Delete events
5
Modification events
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1720-13226782742919375 |
Value: 259 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
45
Text files
227
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E501F17-6B8.pma | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c45319cf-e964-4aed-97f2-6bafad885db8.tmp | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa66b45.TMP | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66cdb.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
52
DNS requests
32
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3900 | chrome.exe | GET | 302 | 103.224.182.245:80 | http://totalsourceadp.com/ts/login.do | AU | — | — | malicious |
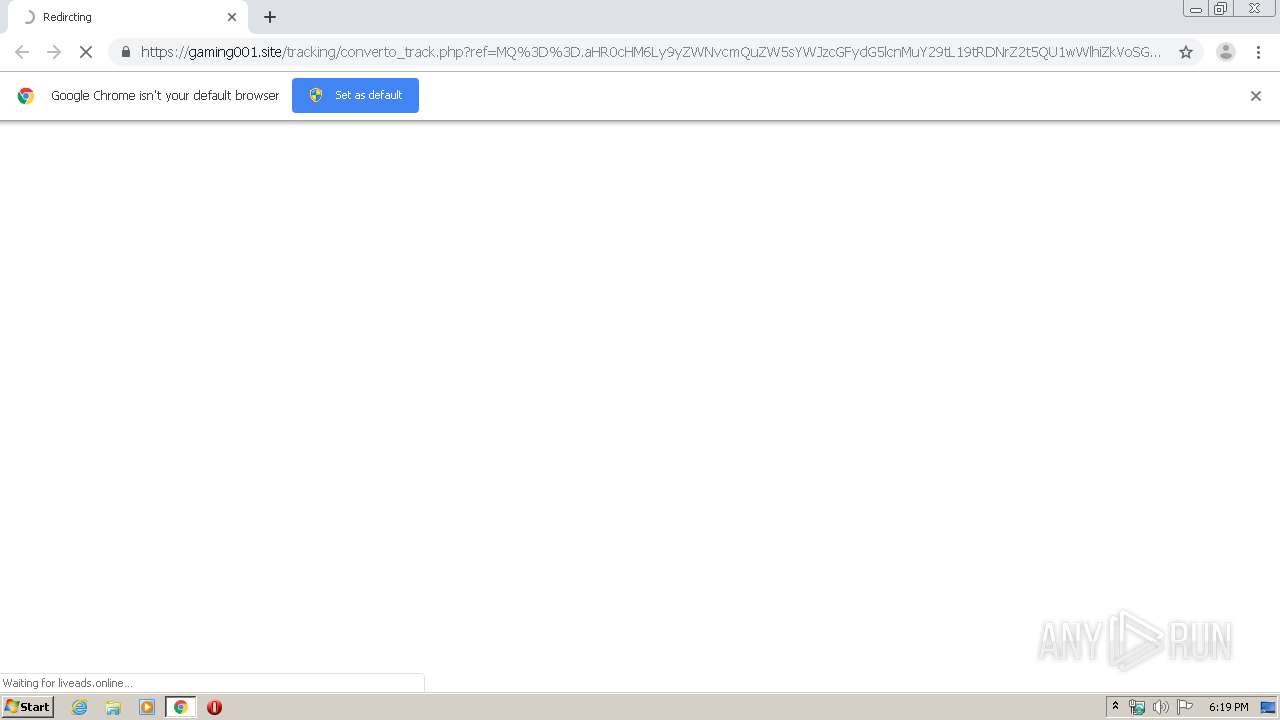
3900 | chrome.exe | GET | 302 | 174.137.155.139:80 | http://clk.rtpdn11.com/click?seat=1855312&i=tr8UpKbEp0A_0 | US | — | — | malicious |
3900 | chrome.exe | GET | 200 | 91.195.240.49:80 | http://ww17.totalsourceadp.com/search/tsc.php?200=MjU0OTk0NjEy&21=ODUuMjA2LjE3NS4yMTk=&681=MTU4MjMwOTE0NjdlMzdkYjllZDU5MDczODE2YzI1Mzg4ZWY2YTY4NGVi&crc=6e0e8f8d9e9b432ded3741b6baa65c21f96c8607&cv=1 | DE | compressed | 2.76 Kb | whitelisted |
3900 | chrome.exe | GET | 302 | 91.195.240.49:80 | http://ww17.totalsourceadp.com/search/tcerider.php?f=http%3A%2F%2Fclk.rtpdn11.com%2Fclick%3Fseat%3D1855312%26i%3Dtr8UpKbEp0A_0&v=ZGRkMjRhNWZkZDM3NDllZmVlOGQ0MzRiNzRlNjk3ZTEJMQl3dzE3LnRvdGFsc291cmNlYWRwLmNvbTVlNTAxZjE5ODJlMWQzLjQzNDk5MDM1CXd3MTcudG90YWxzb3VyY2VhZHAuY29tNWU1MDFmMTk4MmU0NDUuNzYzMzYzNzYJMTU4MjMwOTE0NglhZF81NF8w&l=OAk5NmM3MDIwYzk0ODExOGE4Y2Y4NWNjYzBiYTU1OTU4YQkwCTMwCTAJM2NjYTY5ZjkyMzg4Y2NlMDU1MTlmN2Y5NDQ5YWUwNDEJMjU0OTk0NjEyCXRvdGFsc291cmNlYWRwCTExMDEJNTQJMjAJMjUJMTU4MjMwOTE0NgkwLjAwMDM1CU4JMAkwCTAJMTExMwk4MDc3NzI3OAk4NS4yMDYuMTc1LjIxOQkw | DE | html | 345 b | whitelisted |
3900 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
3900 | chrome.exe | GET | 302 | 91.195.240.49:80 | http://ww17.totalsourceadp.com/search/redirect.php?f=http%3A%2F%2Fclk.rtpdn11.com%2Fclick%3Fseat%3D1855312%26i%3Dtr8UpKbEp0A_0&v=ZGRkMjRhNWZkZDM3NDllZmVlOGQ0MzRiNzRlNjk3ZTEJMQl3dzE3LnRvdGFsc291cmNlYWRwLmNvbTVlNTAxZjE5ODJlMWQzLjQzNDk5MDM1CXd3MTcudG90YWxzb3VyY2VhZHAuY29tNWU1MDFmMTk4MmU0NDUuNzYzMzYzNzYJMTU4MjMwOTE0NglhZF81NF8w&l=OAk5NmM3MDIwYzk0ODExOGE4Y2Y4NWNjYzBiYTU1OTU4YQkwCTMwCTAJM2NjYTY5ZjkyMzg4Y2NlMDU1MTlmN2Y5NDQ5YWUwNDEJMjU0OTk0NjEyCXRvdGFsc291cmNlYWRwCTExMDEJNTQJMjAJMjUJMTU4MjMwOTE0NgkwLjAwMDM1CU4JMAkwCTAJMTExMwk4MDc3NzI3OAk4NS4yMDYuMTc1LjIxOQkw | DE | compressed | 2.76 Kb | whitelisted |
3900 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
3900 | chrome.exe | GET | 200 | 91.195.240.49:80 | http://ww17.totalsourceadp.com/ts/login.do | DE | html | 2.76 Kb | whitelisted |
3900 | chrome.exe | GET | 200 | 87.245.222.141:80 | http://r2---sn-gxuo03g-vqne.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.206.175.219&mm=28&mn=sn-gxuo03g-vqne&ms=nvh&mt=1582308857&mv=u&mvi=1&pl=21&shardbypass=yes | GB | crx | 862 Kb | whitelisted |
3900 | chrome.exe | GET | 200 | 87.245.222.141:80 | http://r2---sn-gxuo03g-vqne.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.206.175.219&mm=28&mn=sn-gxuo03g-vqne&ms=nvh&mt=1582308857&mv=u&mvi=1&pl=21&shardbypass=yes | GB | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3900 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 174.137.155.139:80 | clk.rtpdn11.com | Webair Internet Development Company Inc. | US | suspicious |
3900 | chrome.exe | 52.29.26.88:443 | appdatum.com | Amazon.com, Inc. | DE | unknown |
3900 | chrome.exe | 104.24.96.167:443 | liveads.online | Cloudflare Inc | US | shared |
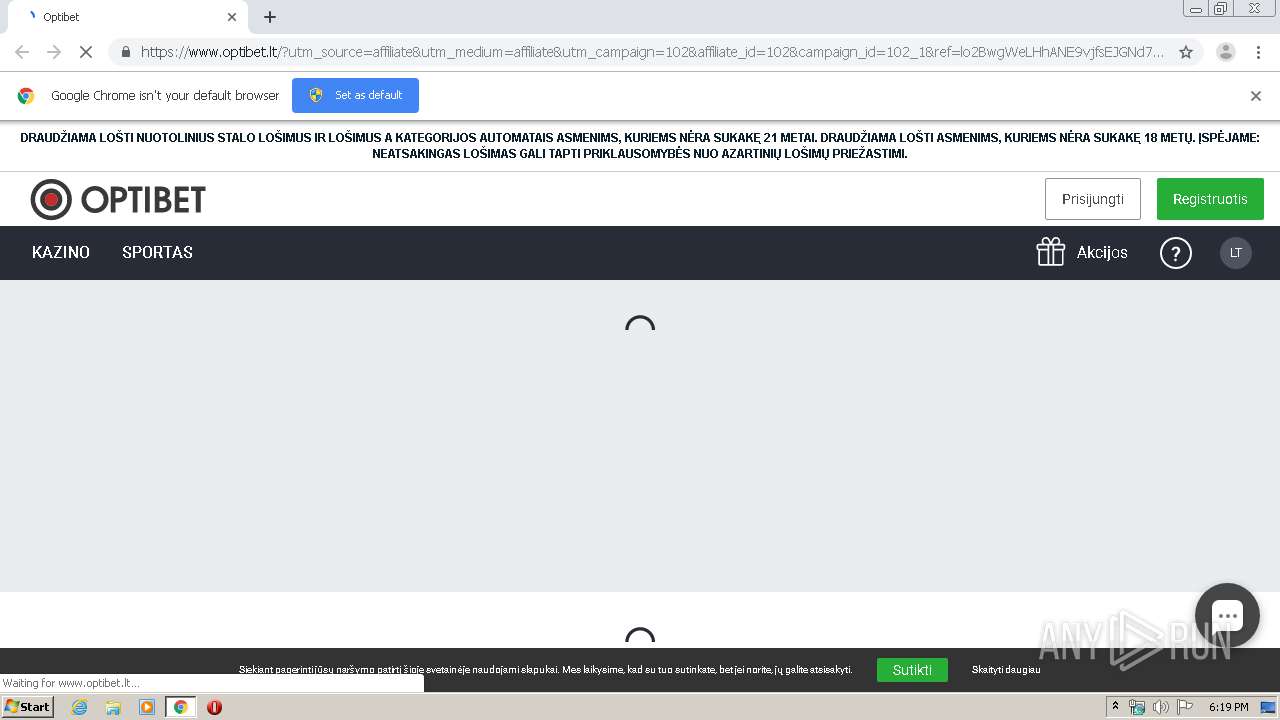
3900 | chrome.exe | 104.31.65.97:443 | gaming001.site | Cloudflare Inc | US | shared |
3900 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 104.18.229.31:443 | record.enlabspartners.com | Cloudflare Inc | US | shared |
3900 | chrome.exe | 104.26.4.189:443 | api.prod.bet | Cloudflare Inc | US | suspicious |
3900 | chrome.exe | 104.20.61.141:443 | www.optibet.lt | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
totalsourceadp.com |
| malicious |
accounts.google.com |
| shared |
ww17.totalsourceadp.com |
| unknown |
img.sedoparking.com |
| whitelisted |
clk.rtpdn11.com |
| malicious |
appdatum.com |
| whitelisted |
gaming001.site |
| malicious |
liveads.online |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3900 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |