| URL: | http://totalsourceadp.com/ts/login.do |
| Full analysis: | https://app.any.run/tasks/161b497b-3b01-46bf-a321-d33518c09a01 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 19:07:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3EAFD03D0FE3439F730467BD6DD710F1 |
| SHA1: | 1EA7FF24A716472C6C13078C08455AB3DE901130 |
| SHA256: | 4E626F6C2FEB5893EBEBAC6B407AC4649FB96808505DCBD1681481BB69AF50C7 |
| SSDEEP: | 3:N1KKKqNQXGI58n:CKhU758 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3376)
INFO
Reads the hosts file
- chrome.exe (PID: 3376)
- chrome.exe (PID: 676)
Application launched itself
- chrome.exe (PID: 3376)
Reads settings of System Certificates
- chrome.exe (PID: 676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
28
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,13675274757459255499,15244205970833070919,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=324595830379692696 --mojo-platform-channel-handle=1568 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,13675274757459255499,15244205970833070919,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12928257876172101927 --mojo-platform-channel-handle=3252 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,13675274757459255499,15244205970833070919,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4344282339361083791 --mojo-platform-channel-handle=3888 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,13675274757459255499,15244205970833070919,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9607354326364958958 --mojo-platform-channel-handle=4092 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,13675274757459255499,15244205970833070919,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1001029464361440216 --mojo-platform-channel-handle=1040 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,13675274757459255499,15244205970833070919,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2760768292420722823 --mojo-platform-channel-handle=4028 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,13675274757459255499,15244205970833070919,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13514670271198279134 --mojo-platform-channel-handle=4808 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,13675274757459255499,15244205970833070919,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4791958224162356500 --mojo-platform-channel-handle=4044 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,13675274757459255499,15244205970833070919,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5866392810398742979 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,13675274757459255499,15244205970833070919,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18161394245532335048 --mojo-platform-channel-handle=3828 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
718
Read events
636
Write events
77
Delete events
5
Modification events
| (PID) Process: | (3464) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3376-13226785641921750 |
Value: 259 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
29
Text files
179
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E502A6A-D30.pma | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cbafcd1e-e3d1-4aba-a886-c60725742e12.tmp | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66e52.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
35
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
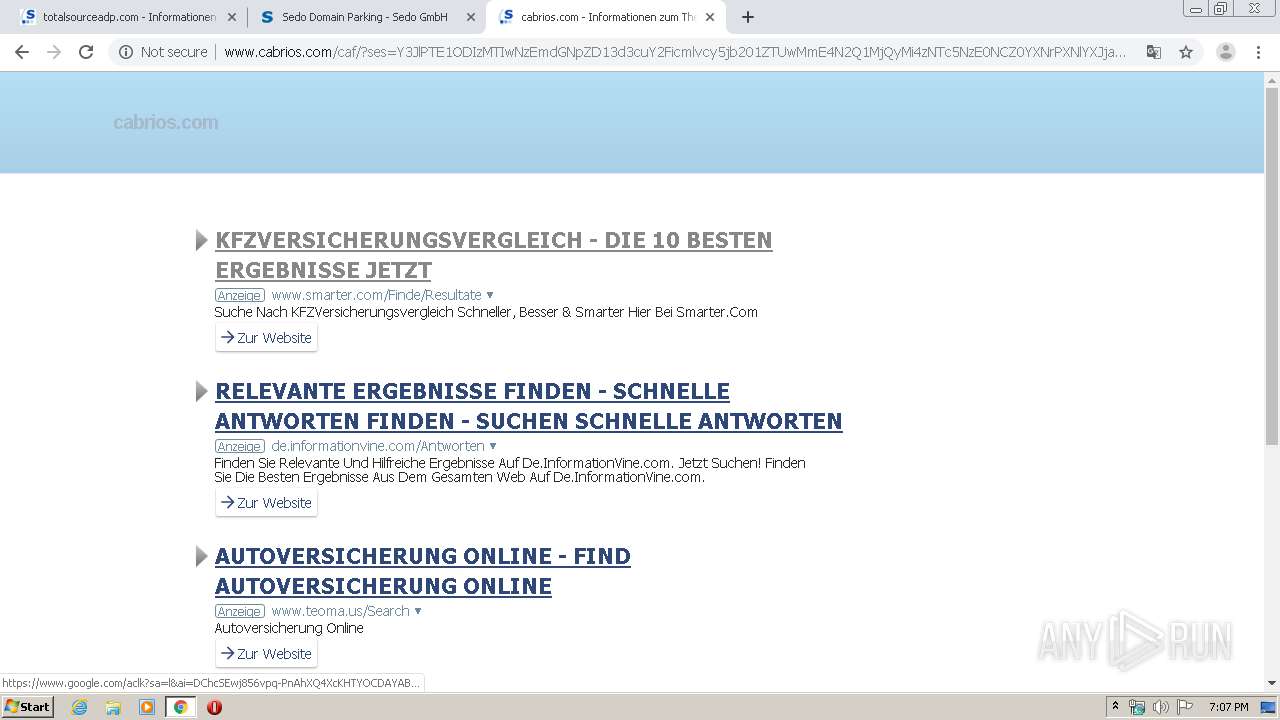
676 | chrome.exe | GET | 200 | 91.195.240.13:80 | http://www.cabrios.com/search/tsc.php?200=MjEzODI2NjYz&21=NDUuNDEuMTM4LjIwNA==&681=MTU4MjMxMjA3MWZjNWVlYzkzNTQzZTBkNGY0NWI3YzI3MDdmZTY3M2I4&crc=d3e847a691d8f10d5754a379341a076d6dced1bf&cv=1 | DE | compressed | 21.6 Kb | malicious |
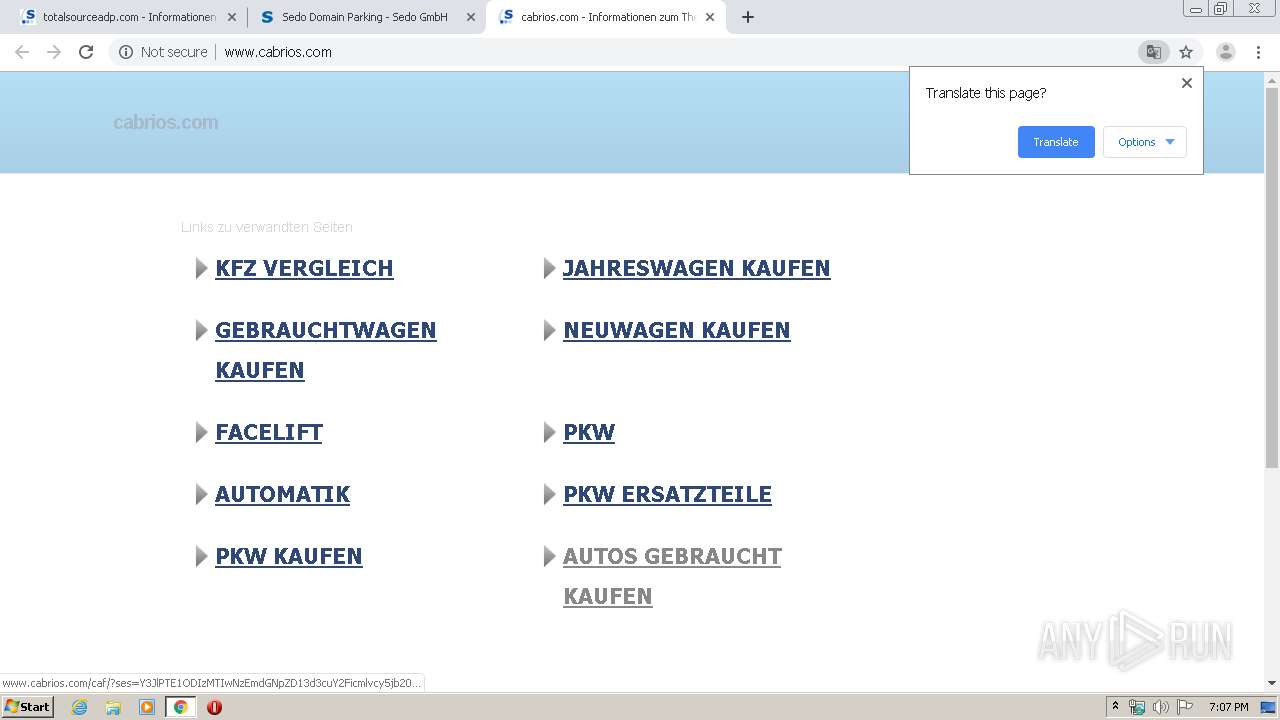
676 | chrome.exe | GET | 200 | 91.195.240.13:80 | http://www.cabrios.com/ | DE | html | 21.6 Kb | malicious |
676 | chrome.exe | GET | 200 | 91.195.240.13:80 | http://www.cabrios.com/caf/?ses=Y3JlPTE1ODIzMTIwNzEmdGNpZD13d3cuY2Ficmlvcy5jb201ZTUwMmE4N2Q1MjQyMi4zNTc5NzE0NCZ0YXNrPXNlYXJjaCZkb21haW49Y2Ficmlvcy5jb20mbGFuZ3VhZ2U9ZGUmYV9pZD0zJnNlc3Npb249cnFHaUNqT09tSjQ5UWV2R1o0M0Q=&query=Kfz%20Vergleich&afdToken=3B1gt0jcXbmr5l0m0fXXvkmQ_pYP14wDrN5d0GhPgVM4HPH3TNZQY7XqpyR7L-9zHmXvaDYIi6iHj4Fqn5Awd0OCwXItR6-OVeJRwhLFEQ | DE | html | 21.7 Kb | malicious |
676 | chrome.exe | GET | 200 | 91.195.240.13:80 | http://www.cabrios.com/search/tsc.php?200=MjEzODI2NjYz&21=NDUuNDEuMTM4LjIwNA==&681=MTU4MjMxMjA3NTVmODA0OTQ0MjRjMTU2NzhlNTUxYTUwOTAwYmE0OGNm&crc=7af7c102a9505200c96eda44c9e67c64d2e10aae&cv=1 | DE | compressed | 21.7 Kb | malicious |
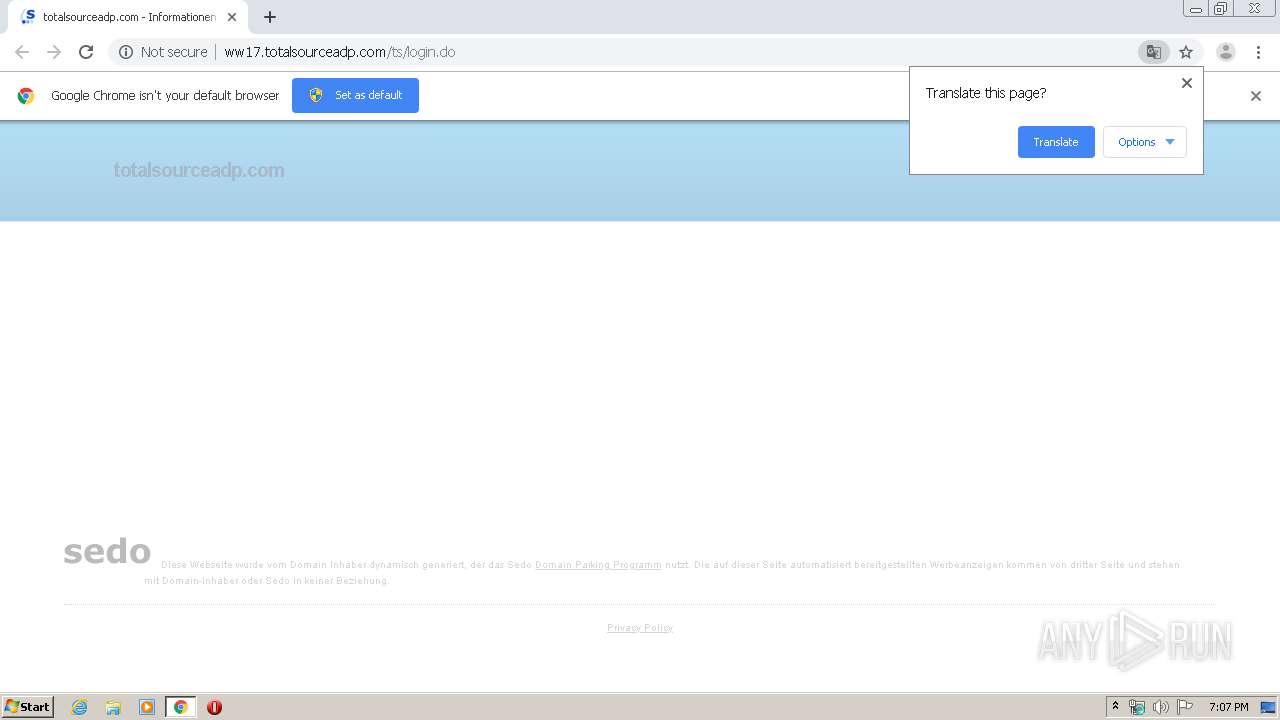
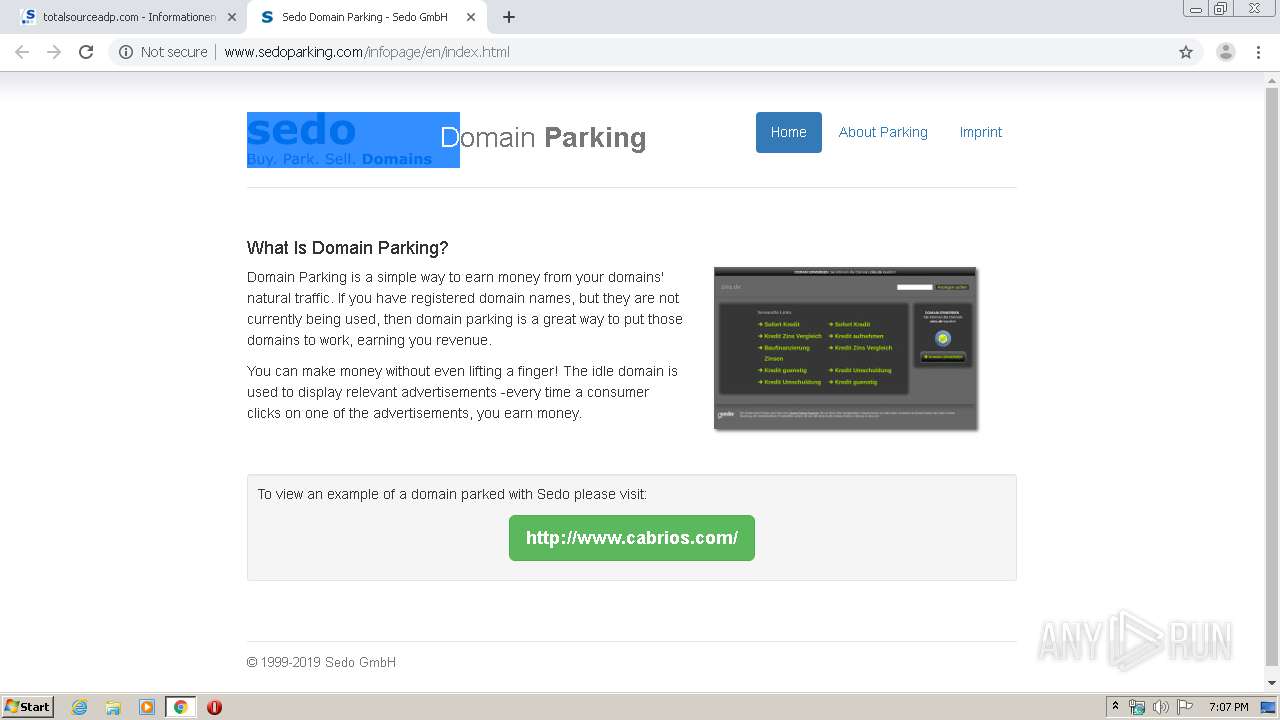
676 | chrome.exe | GET | 302 | 91.195.240.136:80 | http://www.sedoparking.com/ | DE | — | — | malicious |
676 | chrome.exe | GET | 200 | 205.234.175.175:80 | http://img.sedoparking.com/templates/index/img/bg_wrap.jpg | US | image | 404 b | whitelisted |
676 | chrome.exe | GET | 200 | 205.234.175.175:80 | http://img.sedoparking.com/infopage/css/bootstrap_infopage.css | US | text | 637 b | whitelisted |
676 | chrome.exe | GET | 200 | 205.234.175.175:80 | http://img.sedoparking.com/templates/index/img/template_limecrush.jpg | US | image | 10.5 Kb | whitelisted |
676 | chrome.exe | GET | 200 | 205.234.175.175:80 | http://img.sedoparking.com/templates/index/img/sedologo.png | US | image | 4.63 Kb | whitelisted |
676 | chrome.exe | GET | 200 | 205.234.175.175:80 | http://img.sedoparking.com/templates/brick_gfx/common/logo_2016_bbbbbb.svg | US | image | 2.02 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
676 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 103.224.182.245:80 | totalsourceadp.com | Trellian Pty. Limited | AU | malicious |
676 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 91.195.240.49:80 | ww17.totalsourceadp.com | SEDO GmbH | DE | unknown |
676 | chrome.exe | 205.234.175.175:80 | img.sedoparking.com | CacheNetworks, Inc. | US | suspicious |
676 | chrome.exe | 172.217.23.106:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 172.217.16.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 172.217.16.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 172.217.21.238:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
totalsourceadp.com |
| malicious |
accounts.google.com |
| shared |
ww17.totalsourceadp.com |
| unknown |
www.google.com |
| malicious |
img.sedoparking.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
www.sedo.com |
| whitelisted |
www.sedoparking.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
676 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |