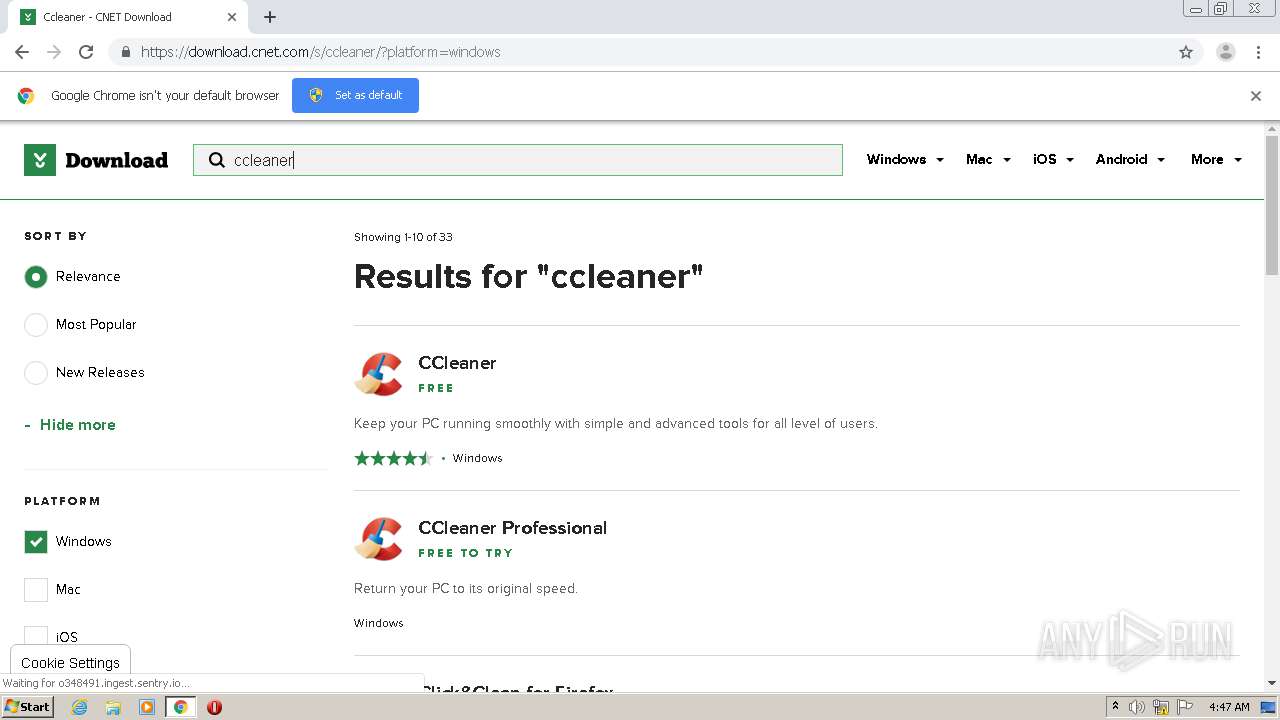
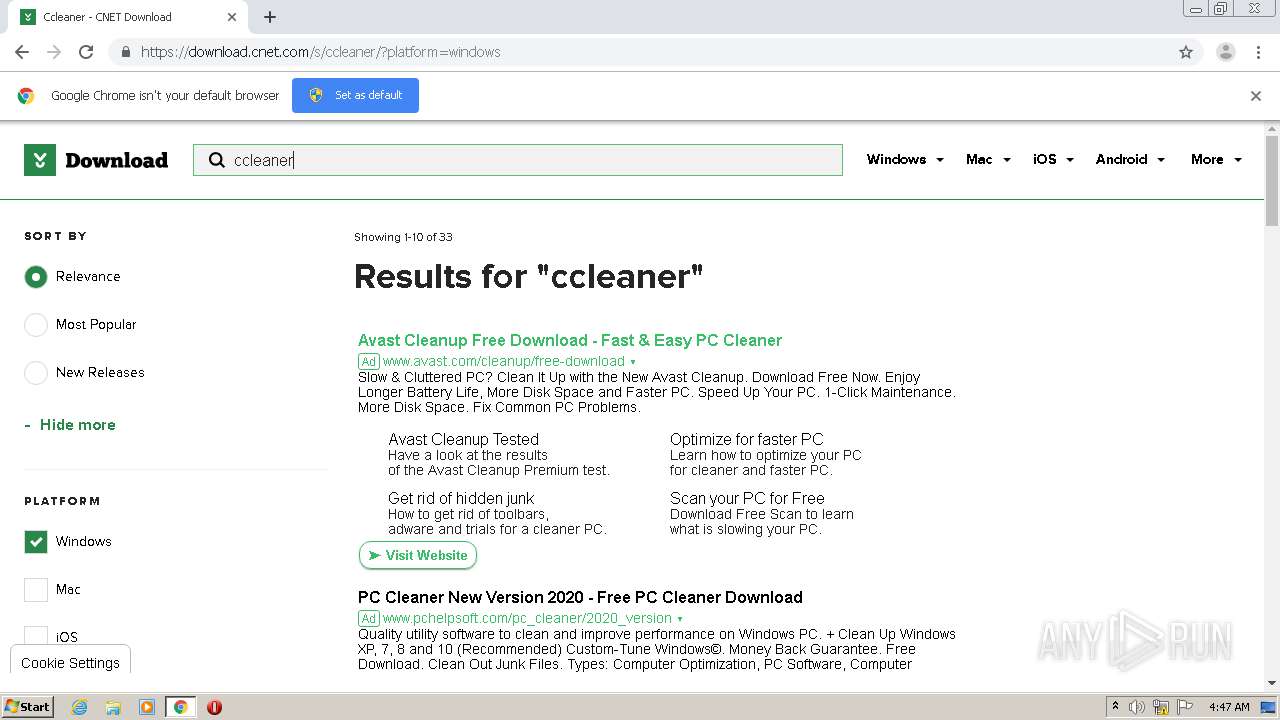
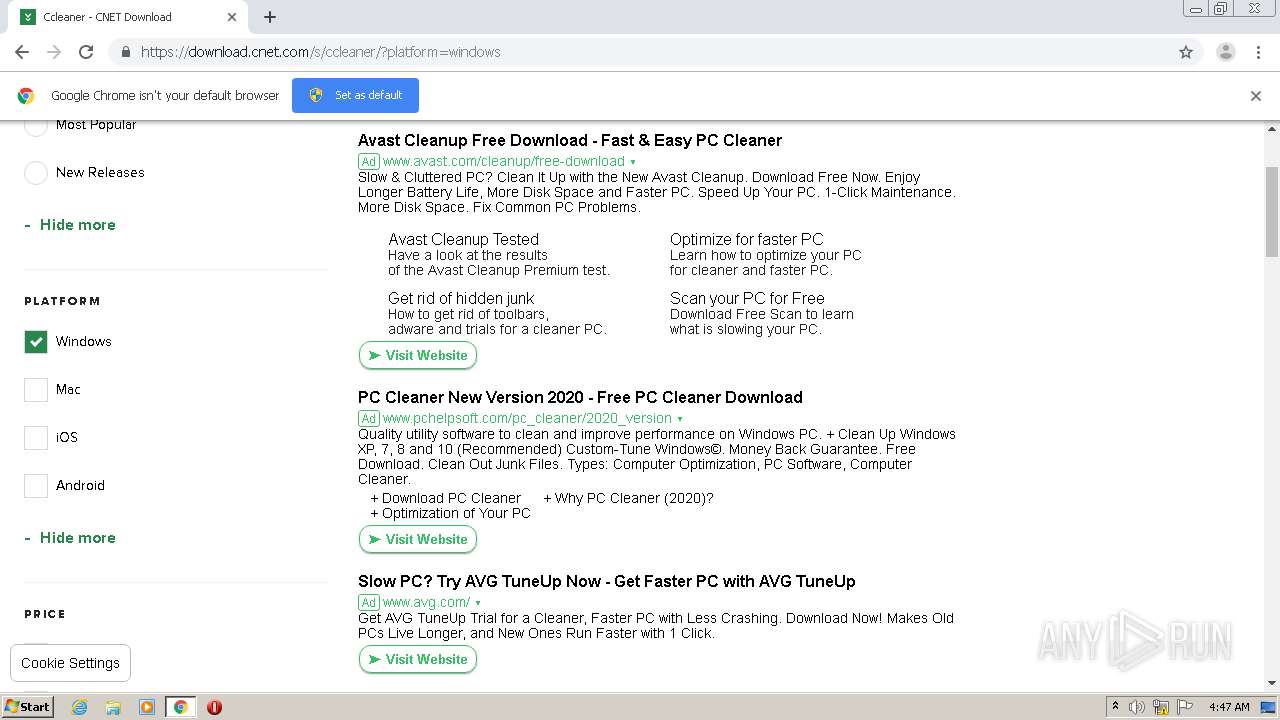
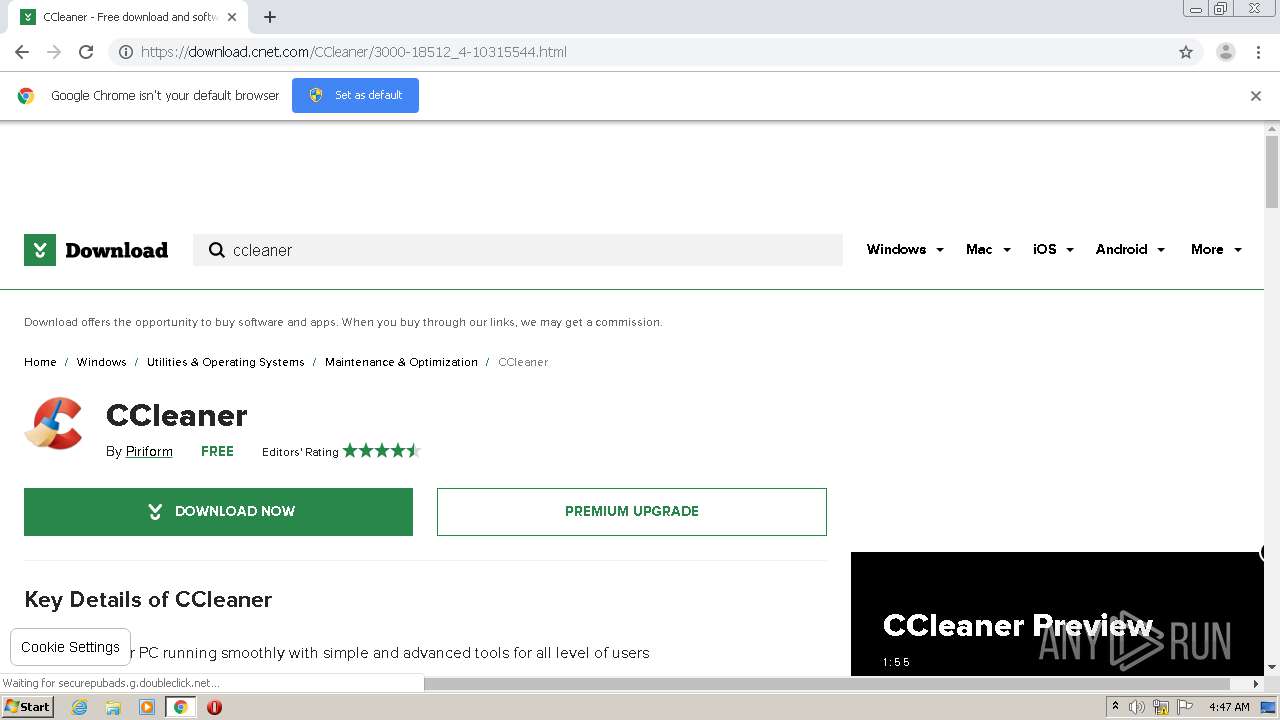
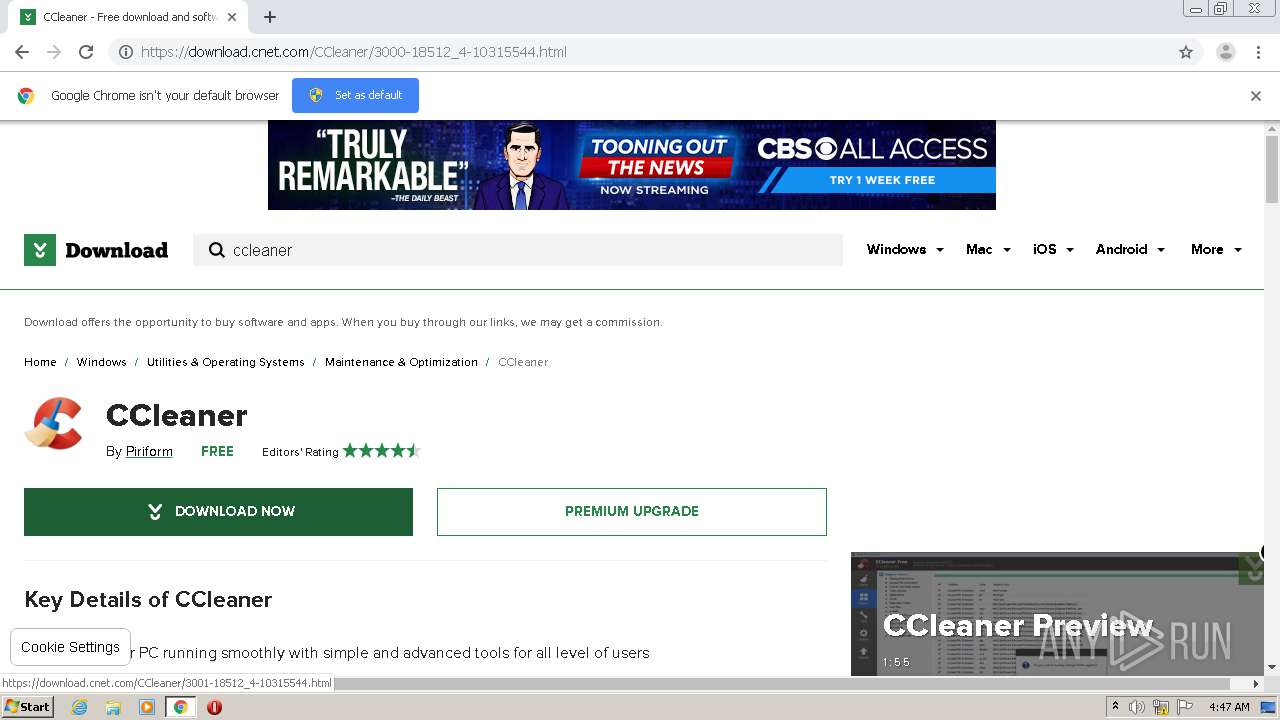
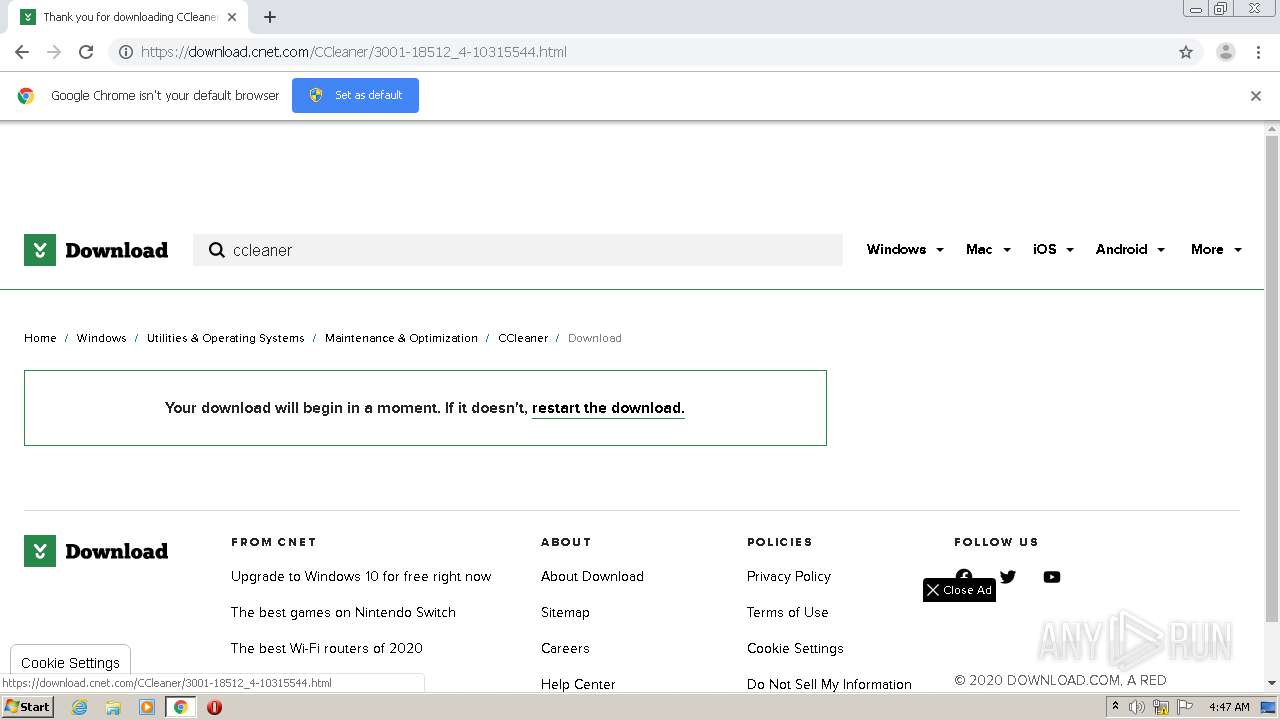
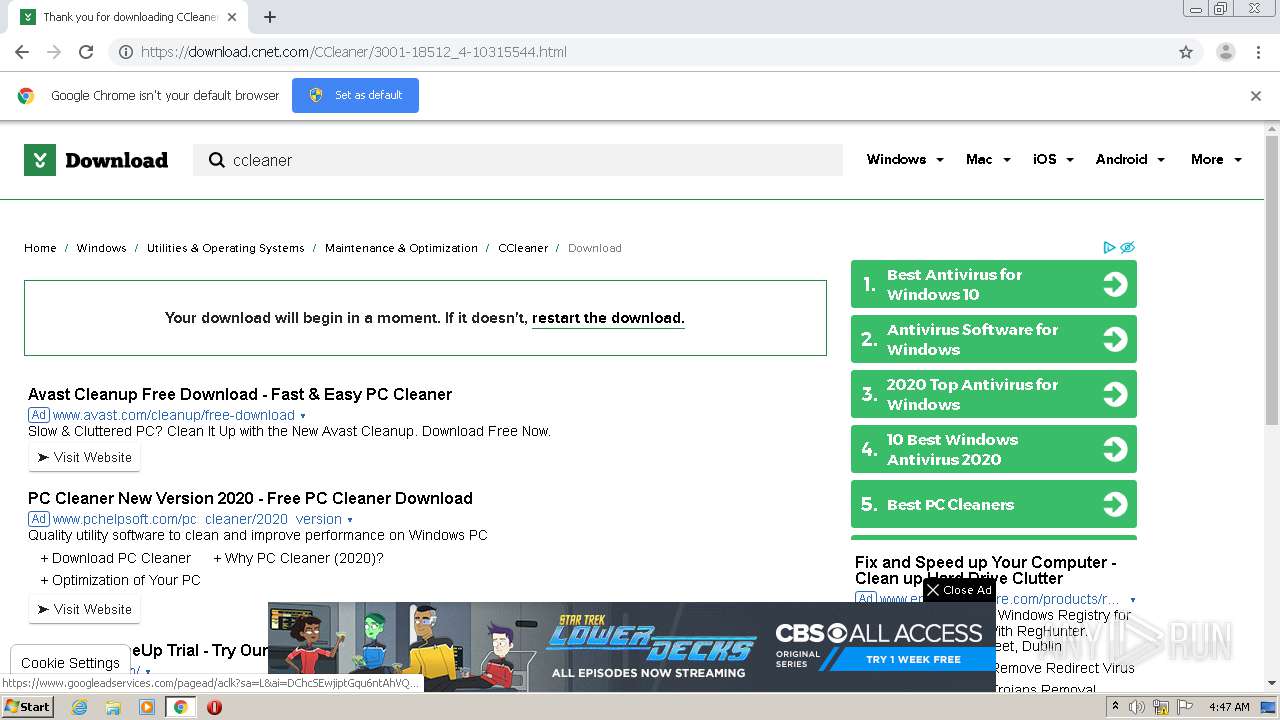
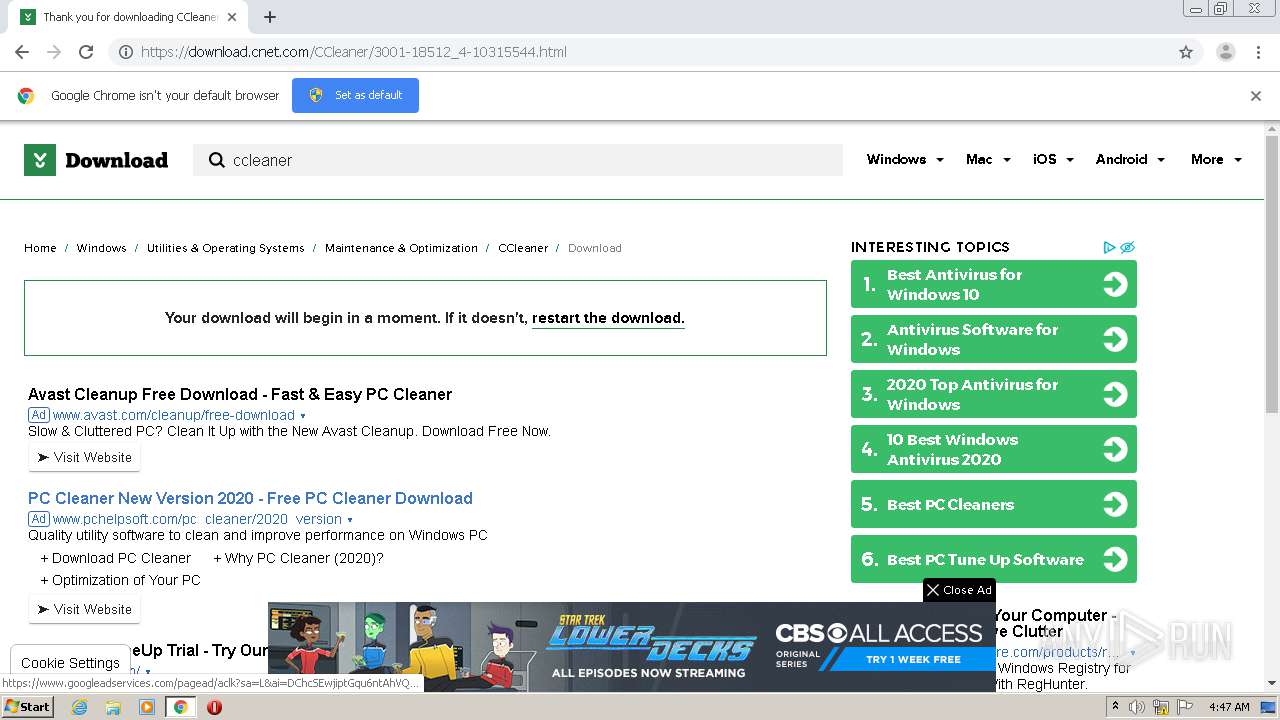
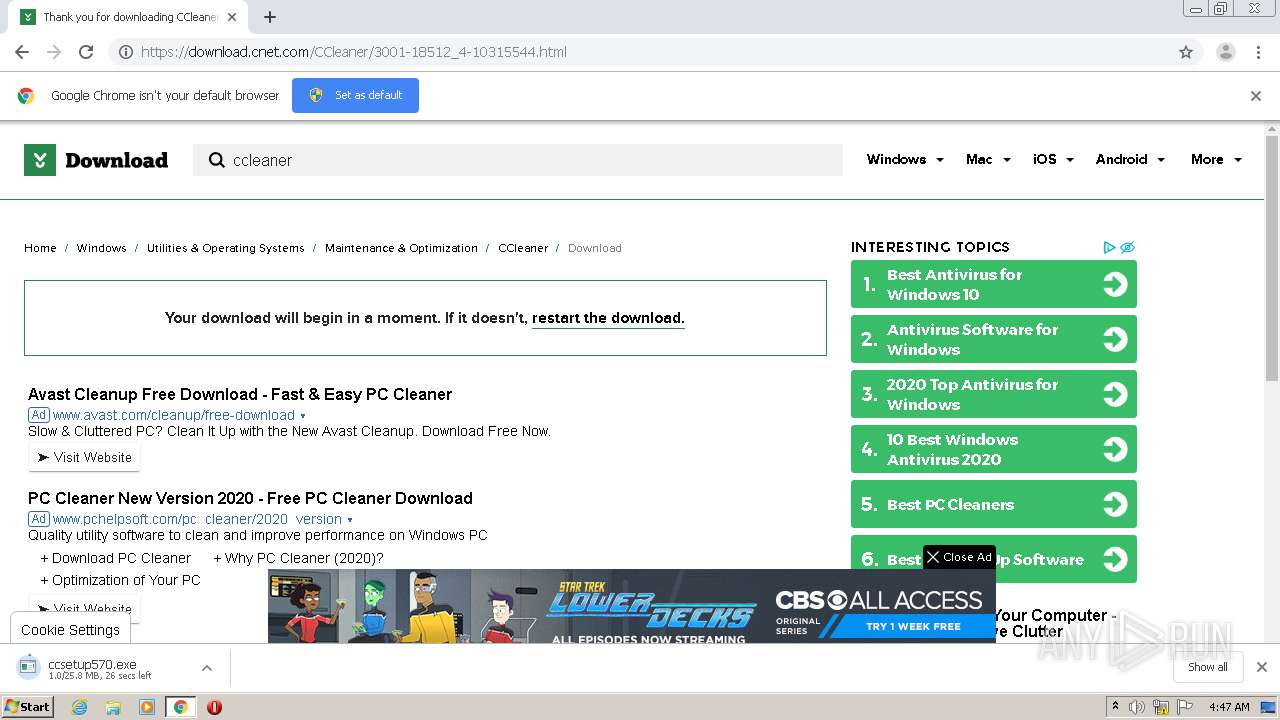
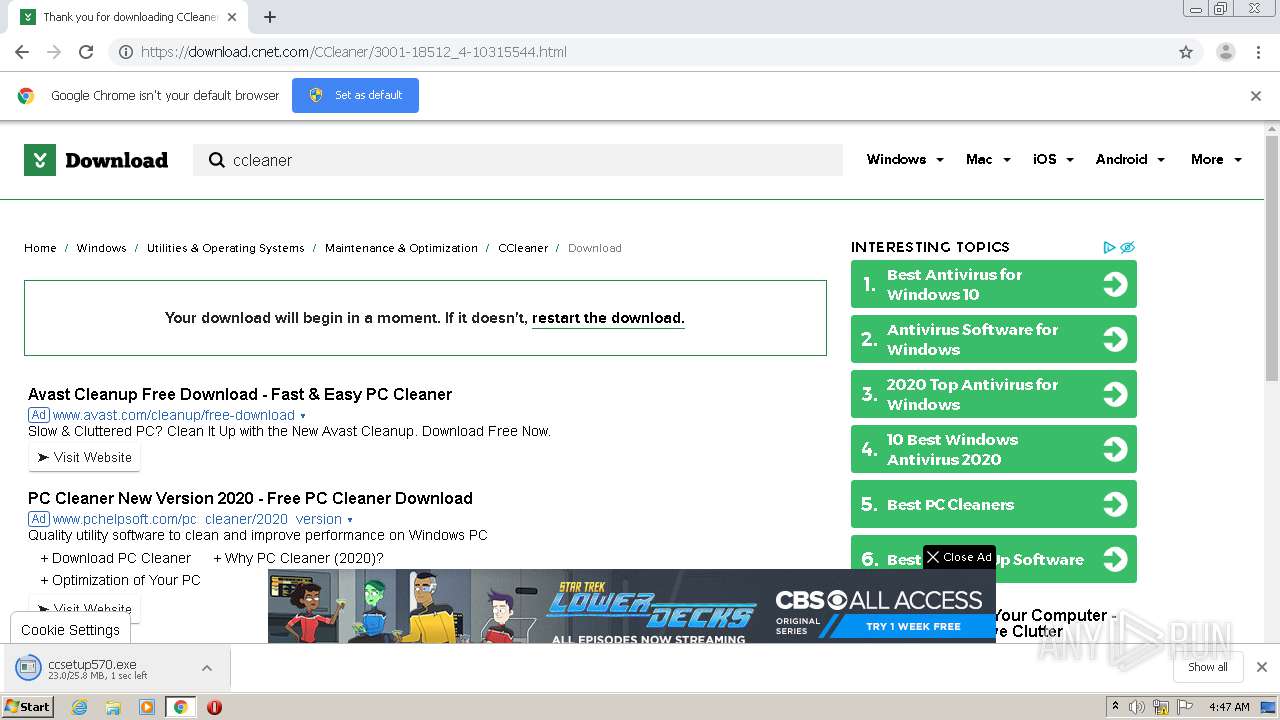
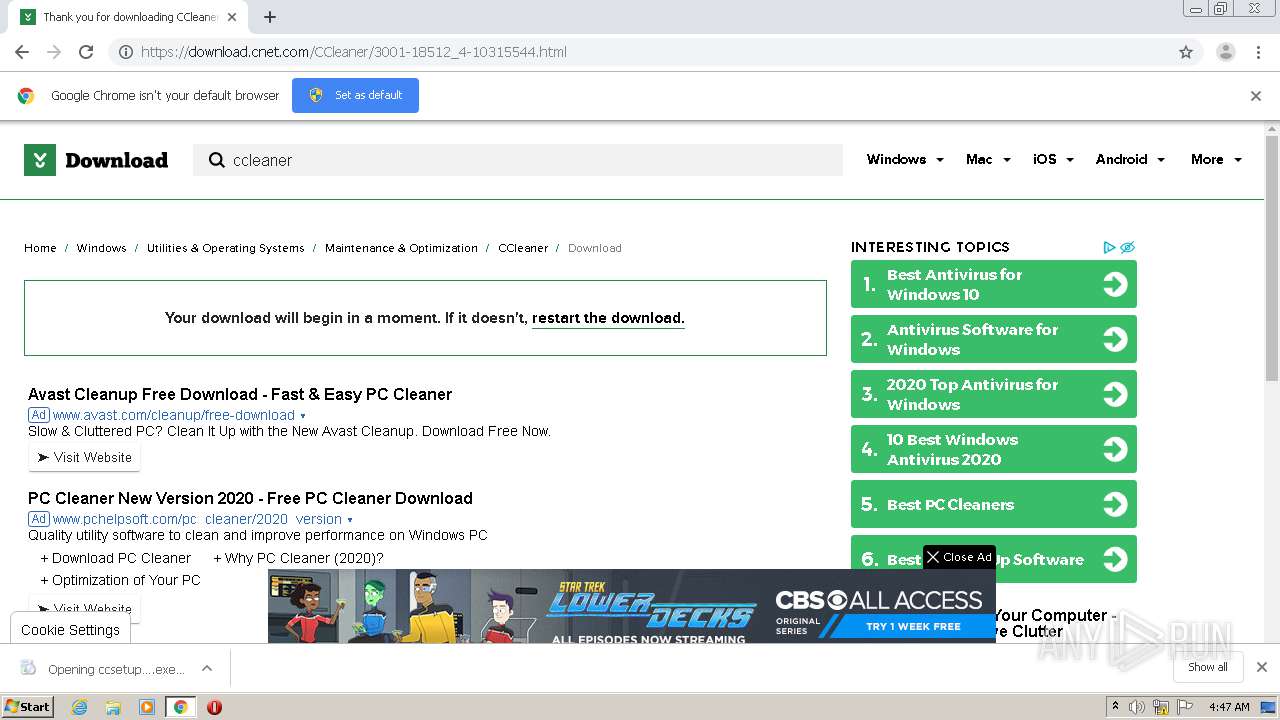
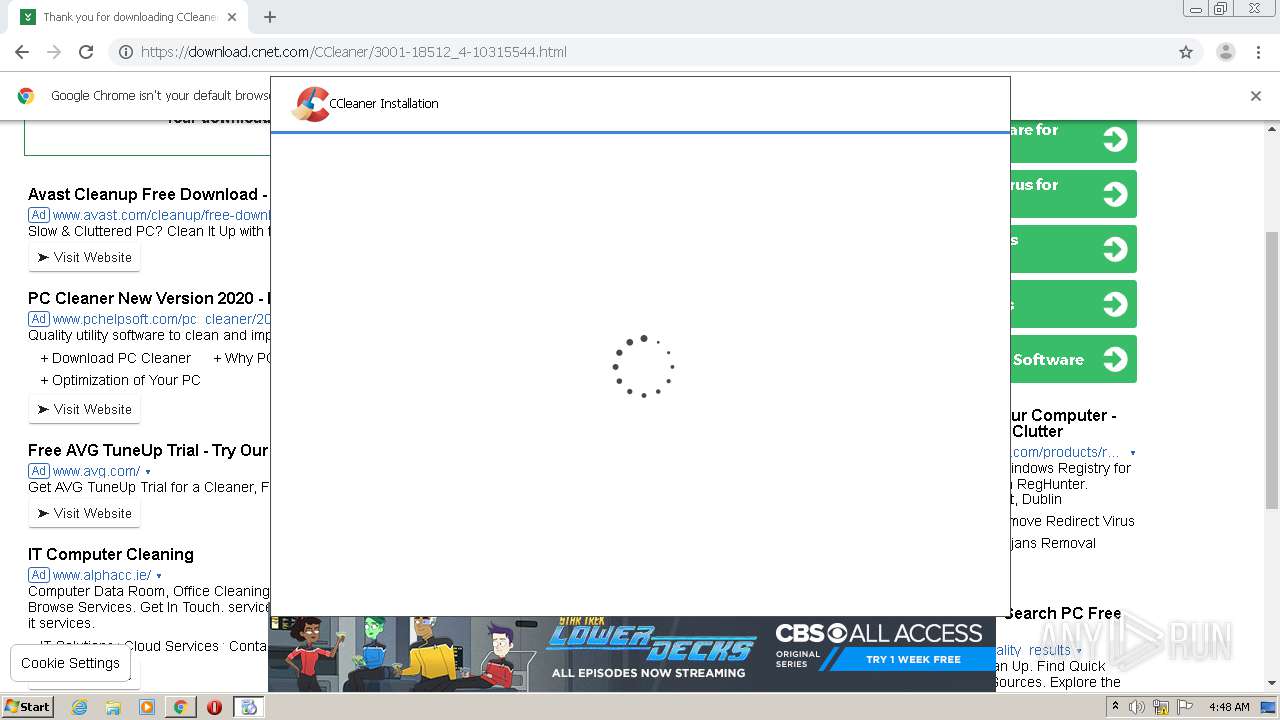
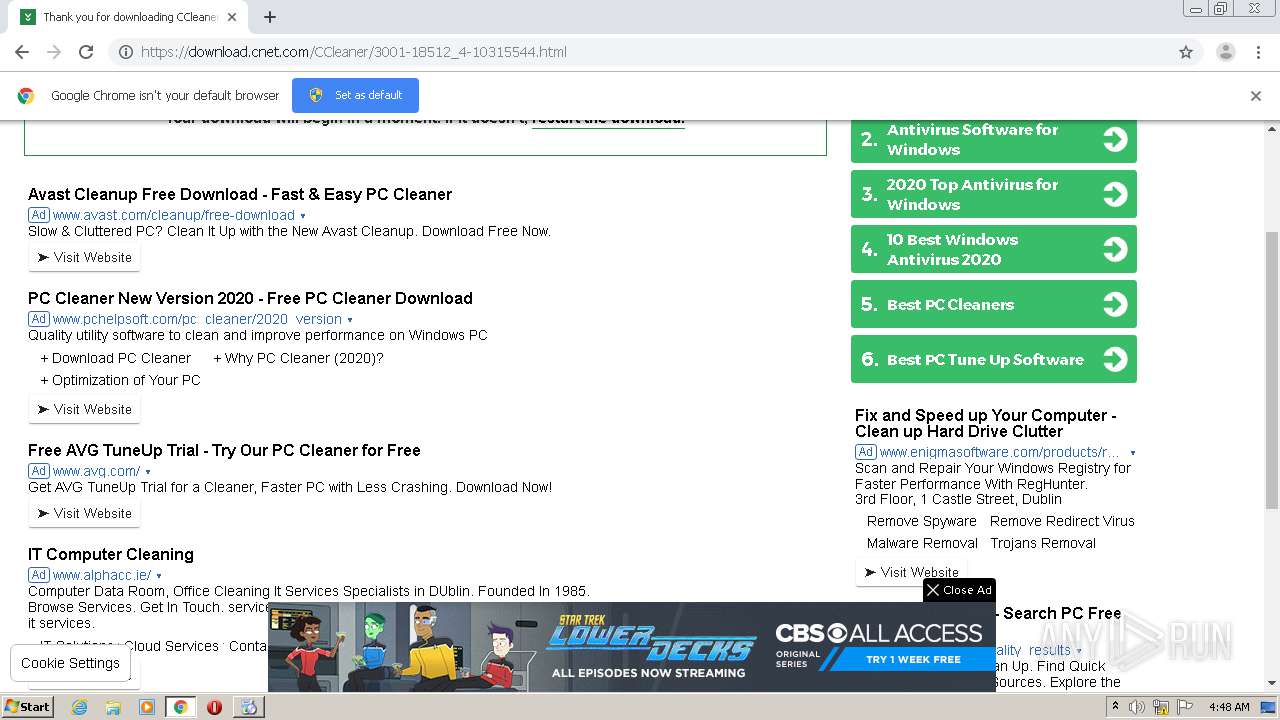
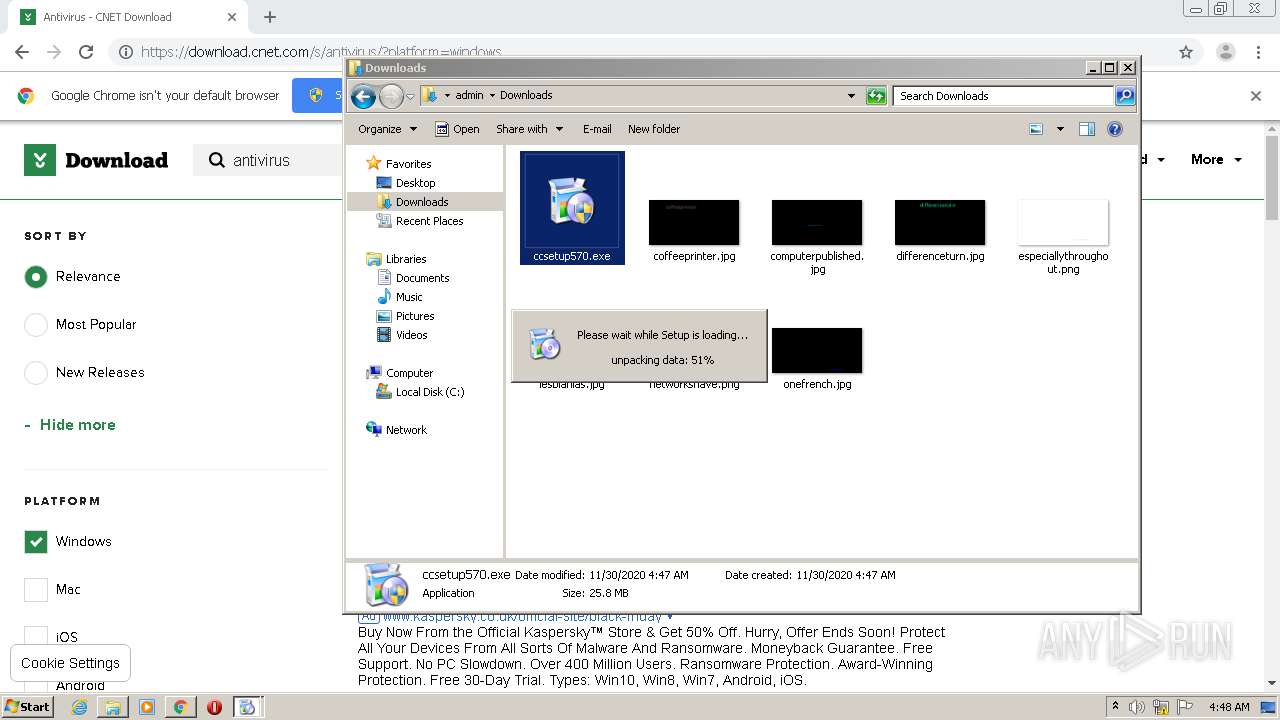
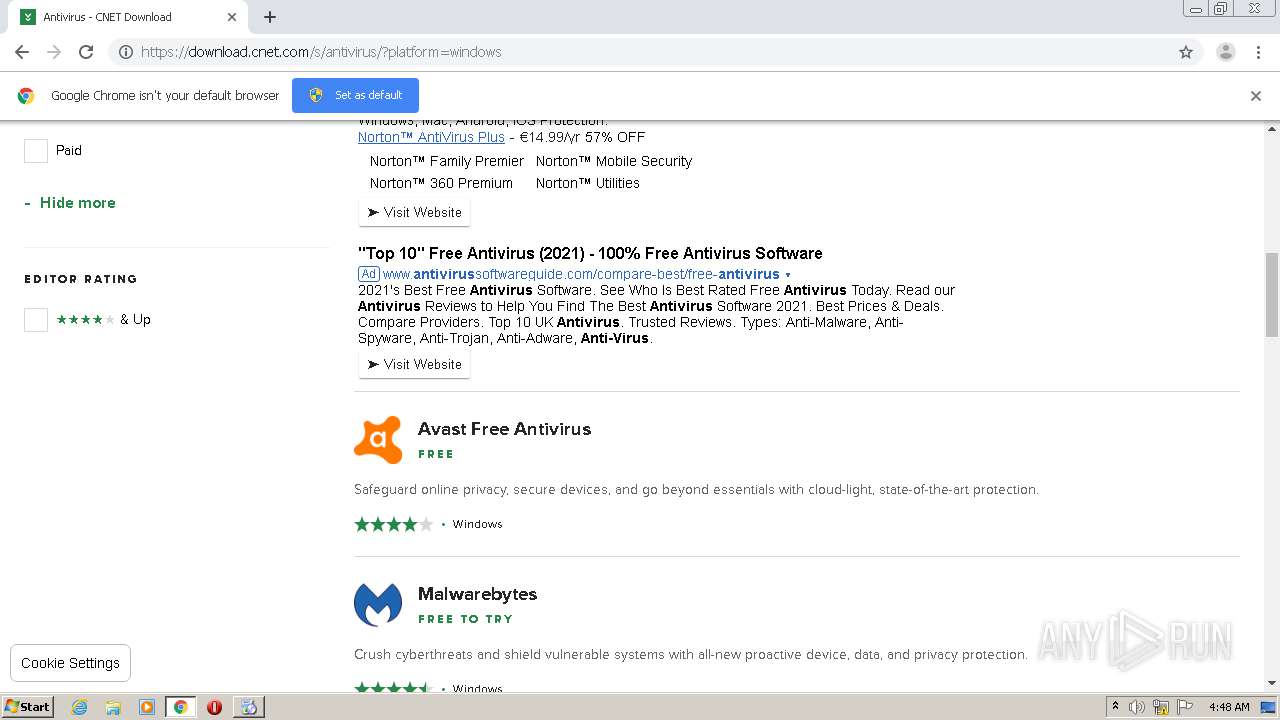
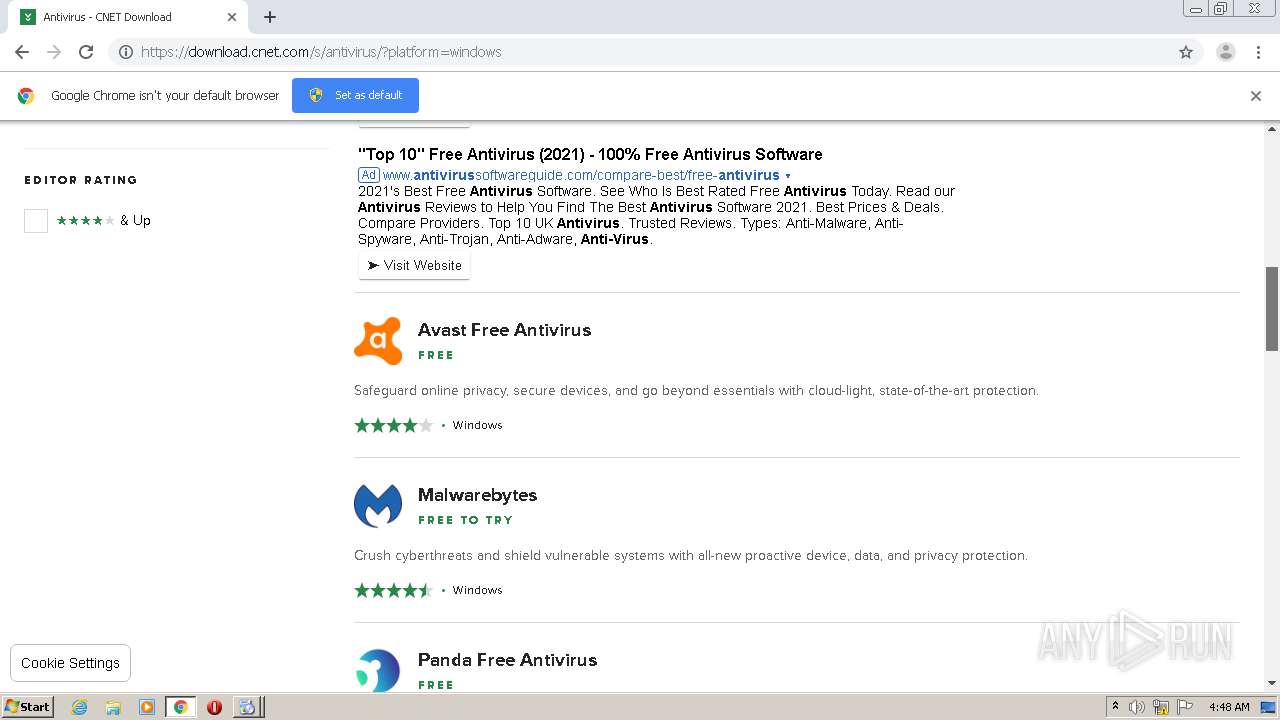
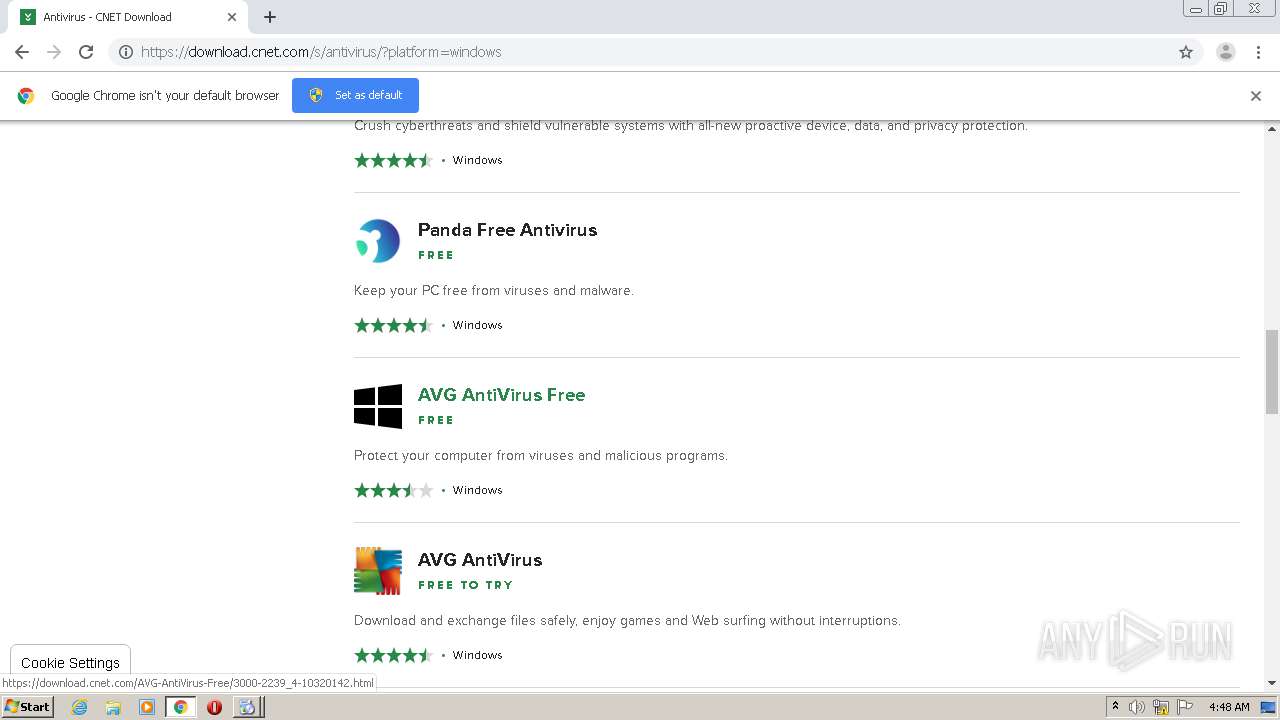
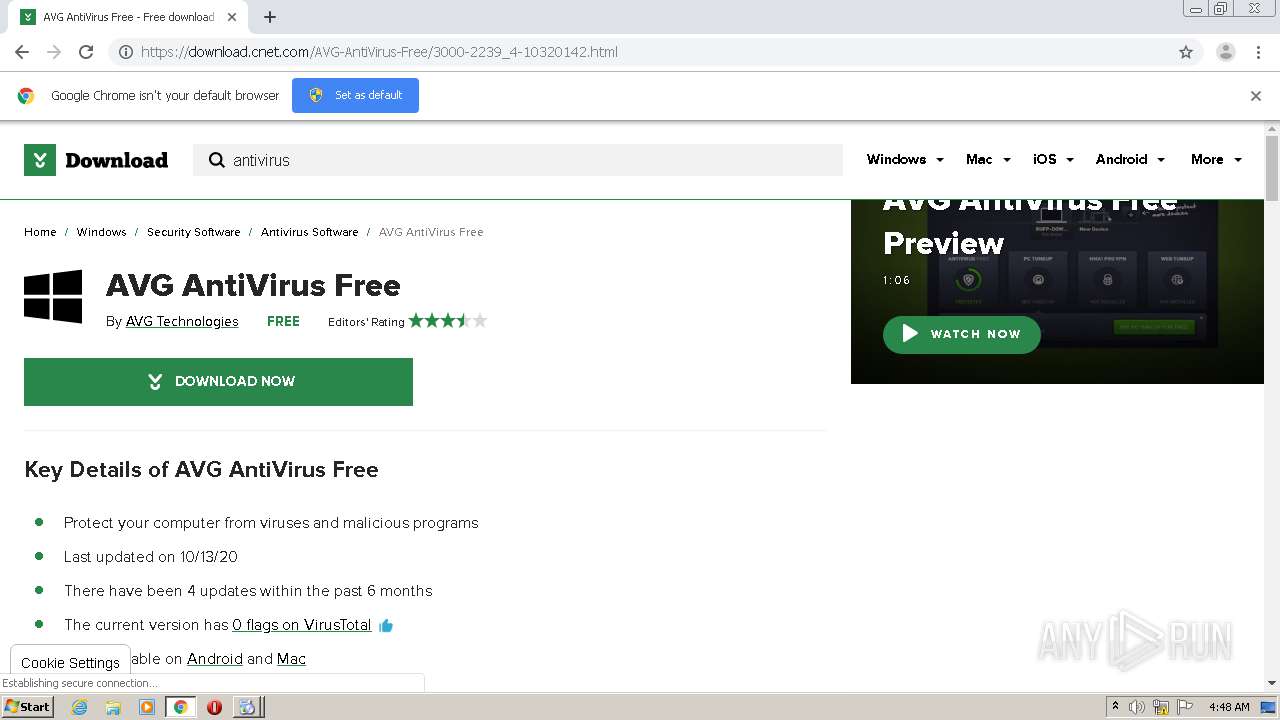
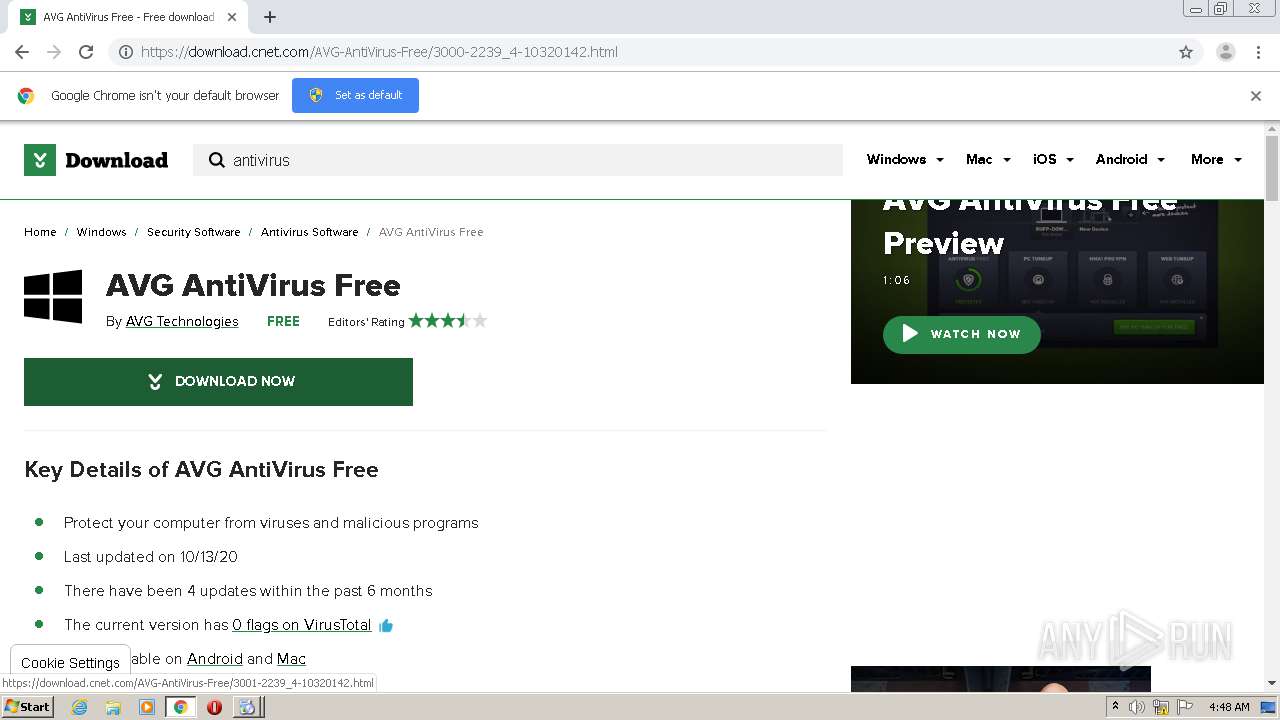
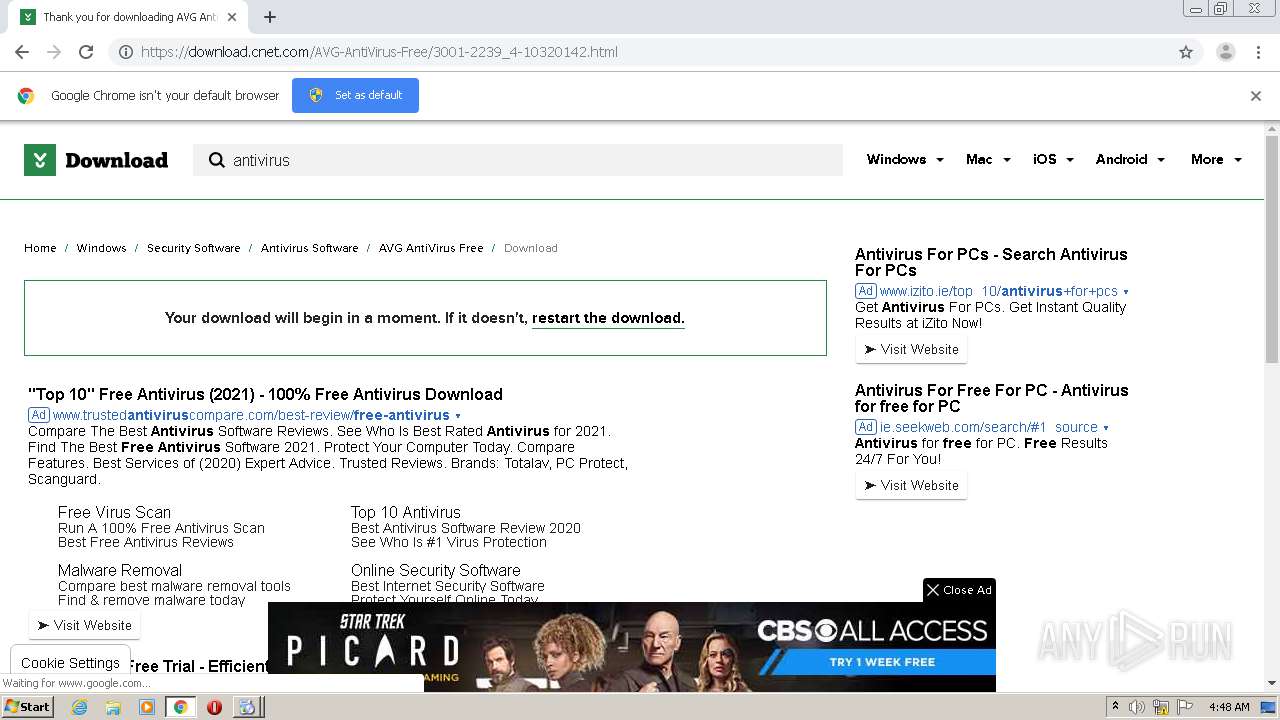
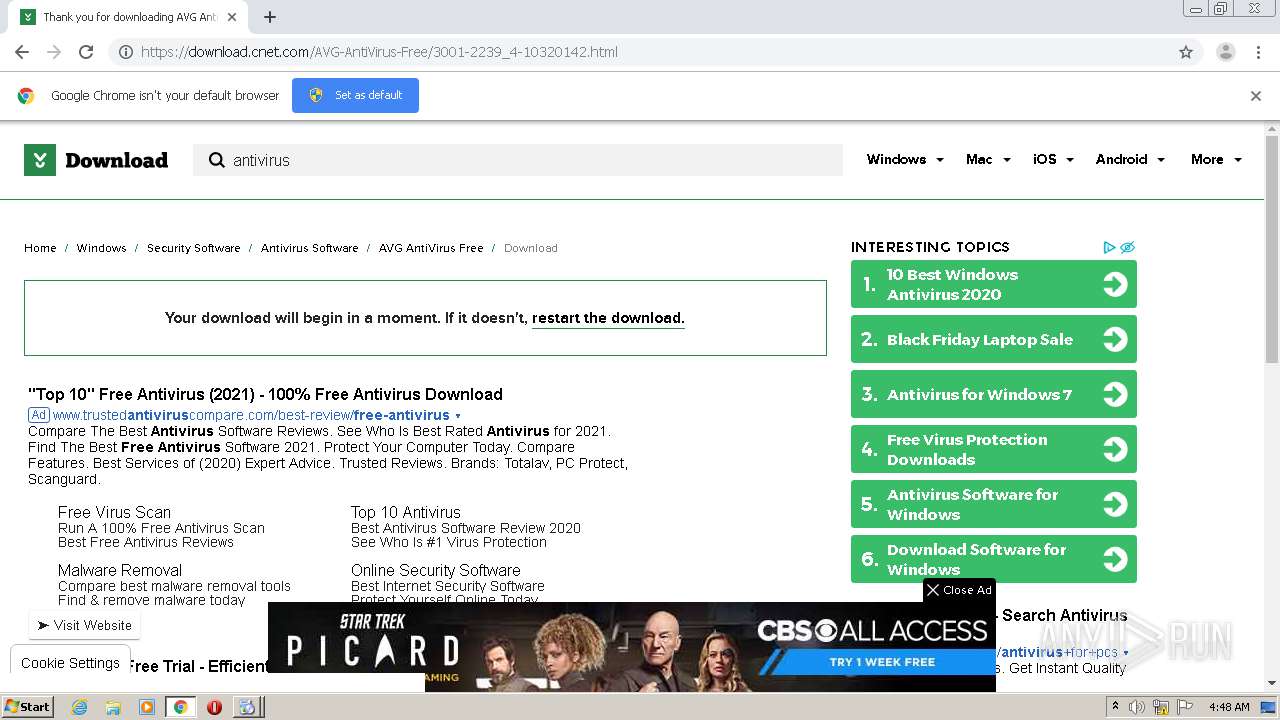
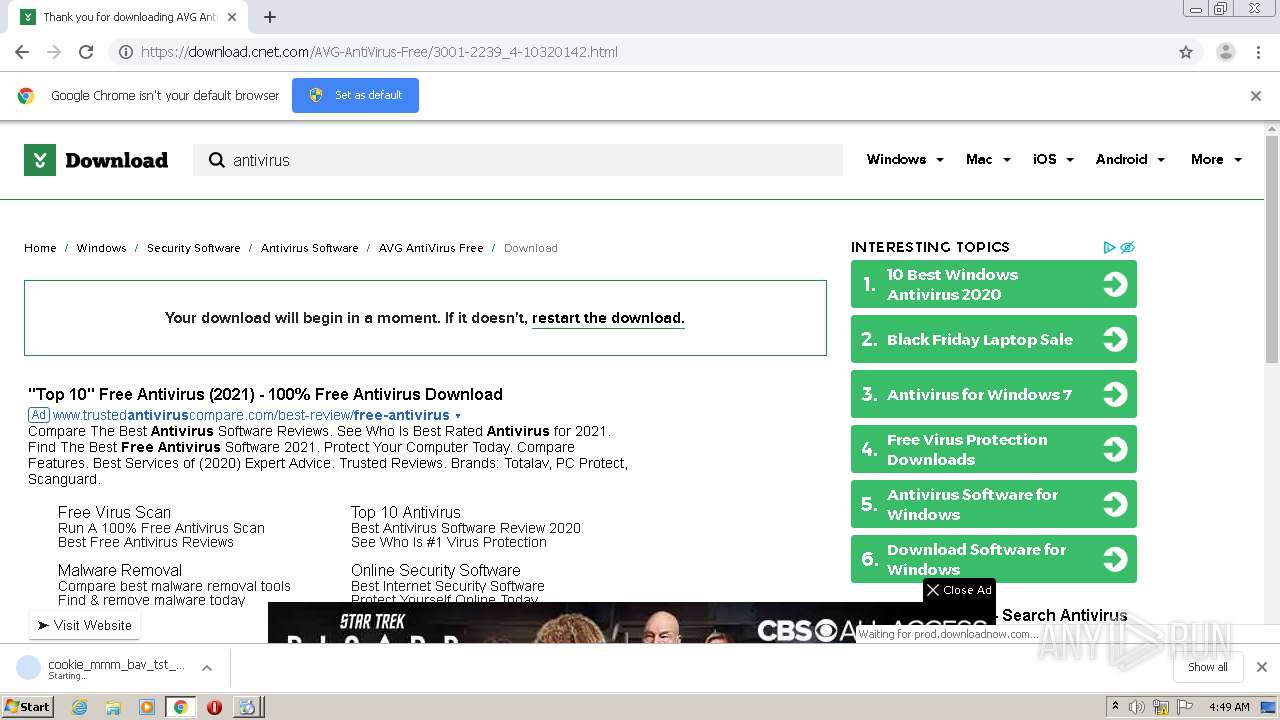
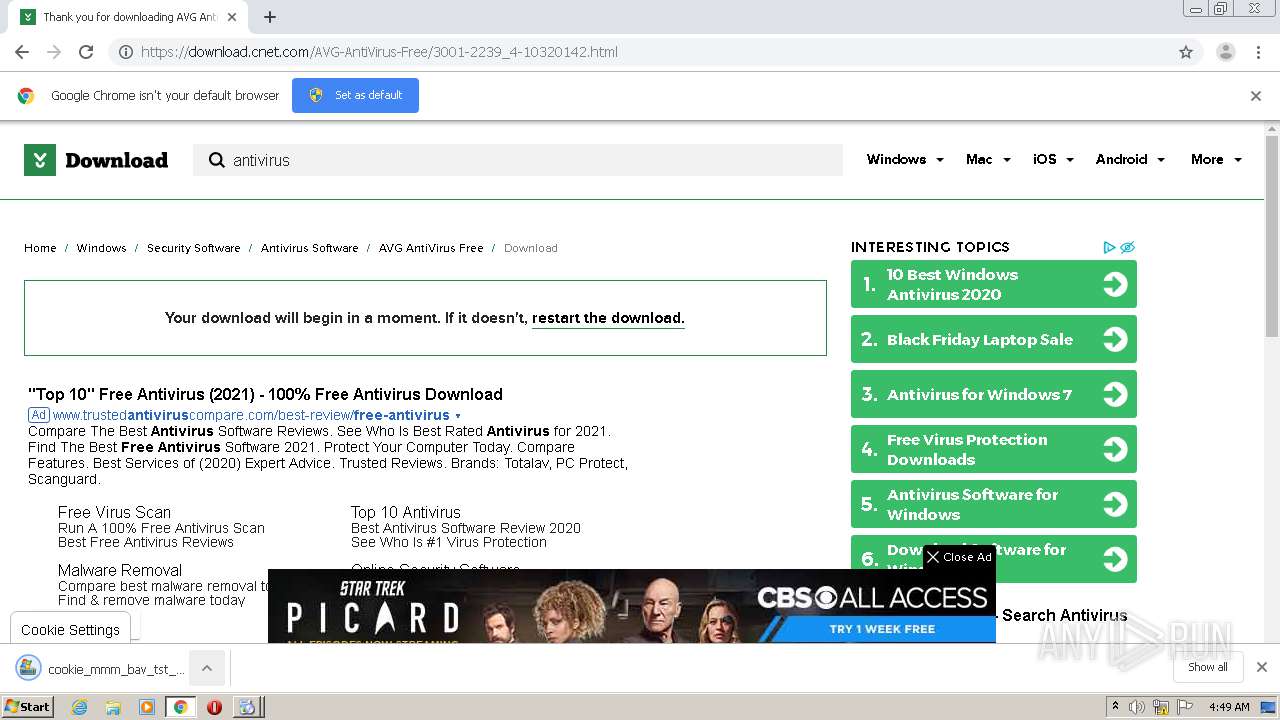
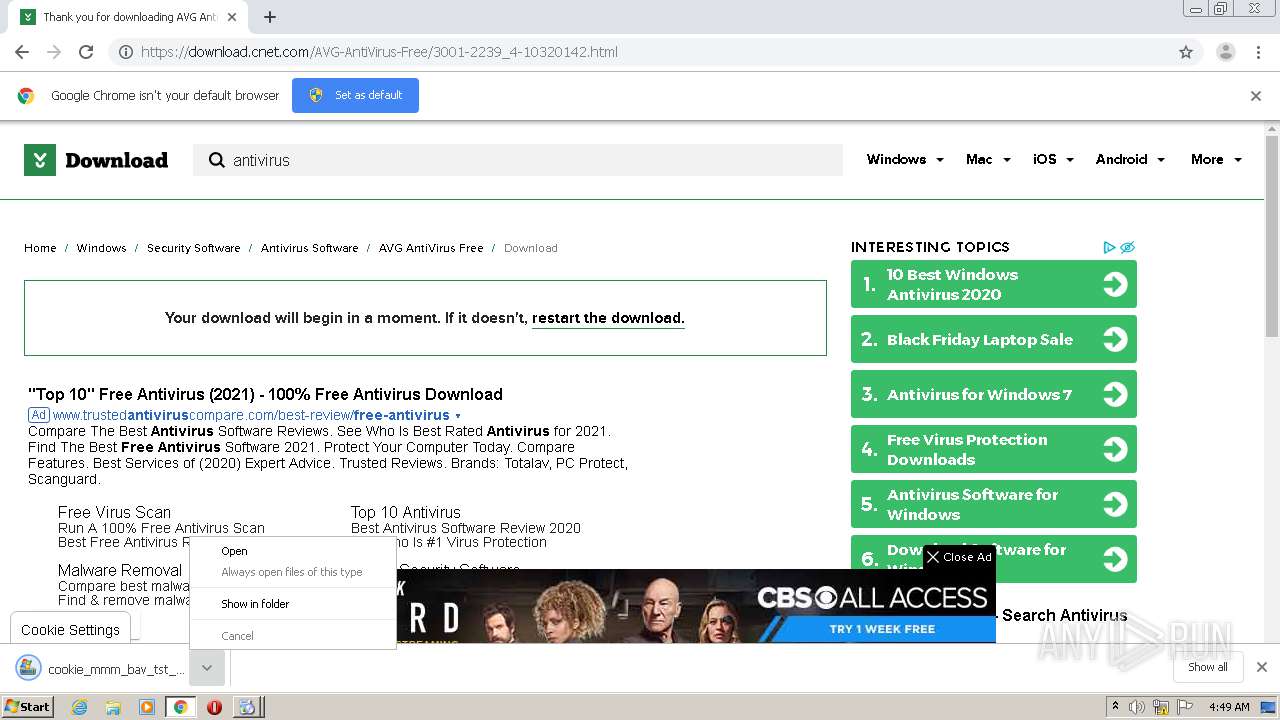
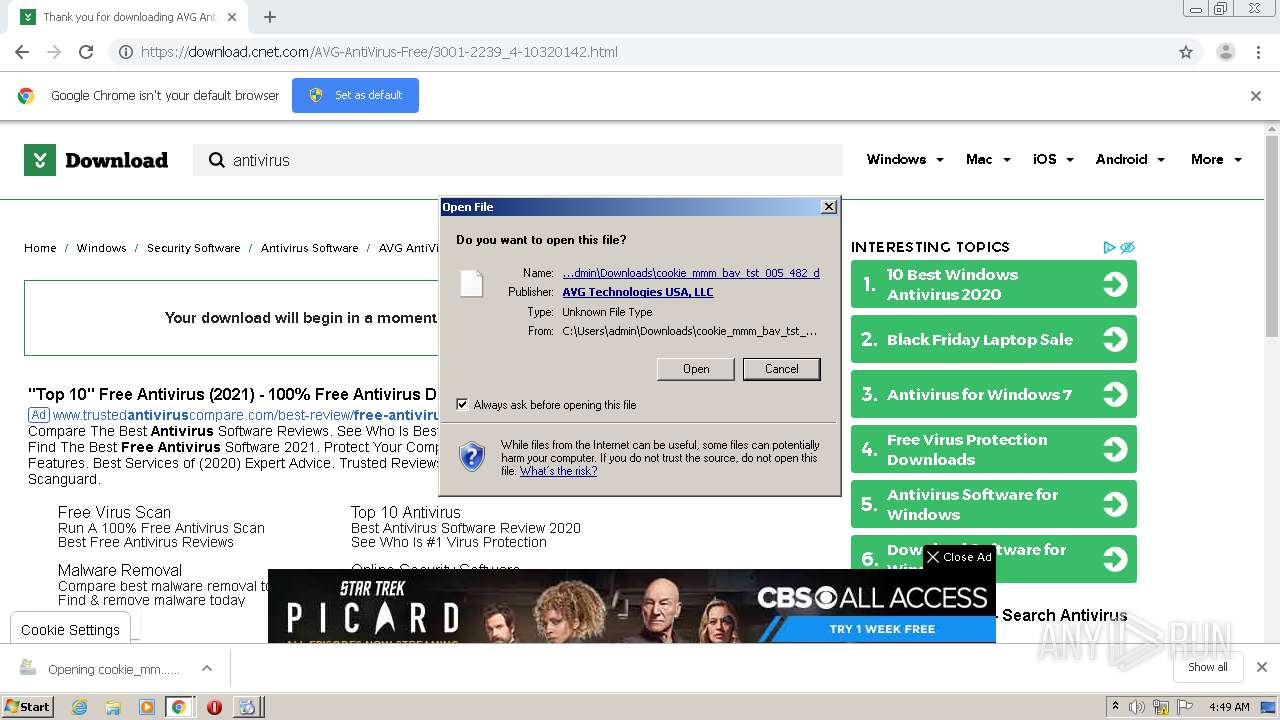
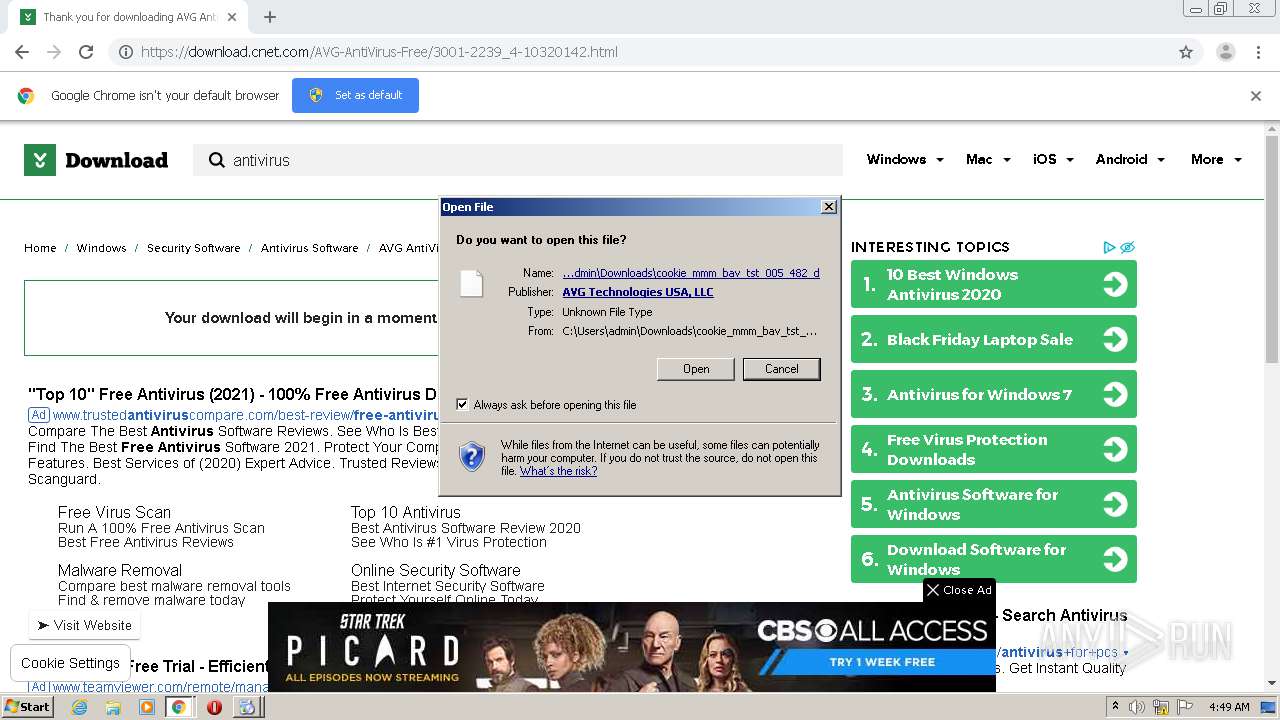
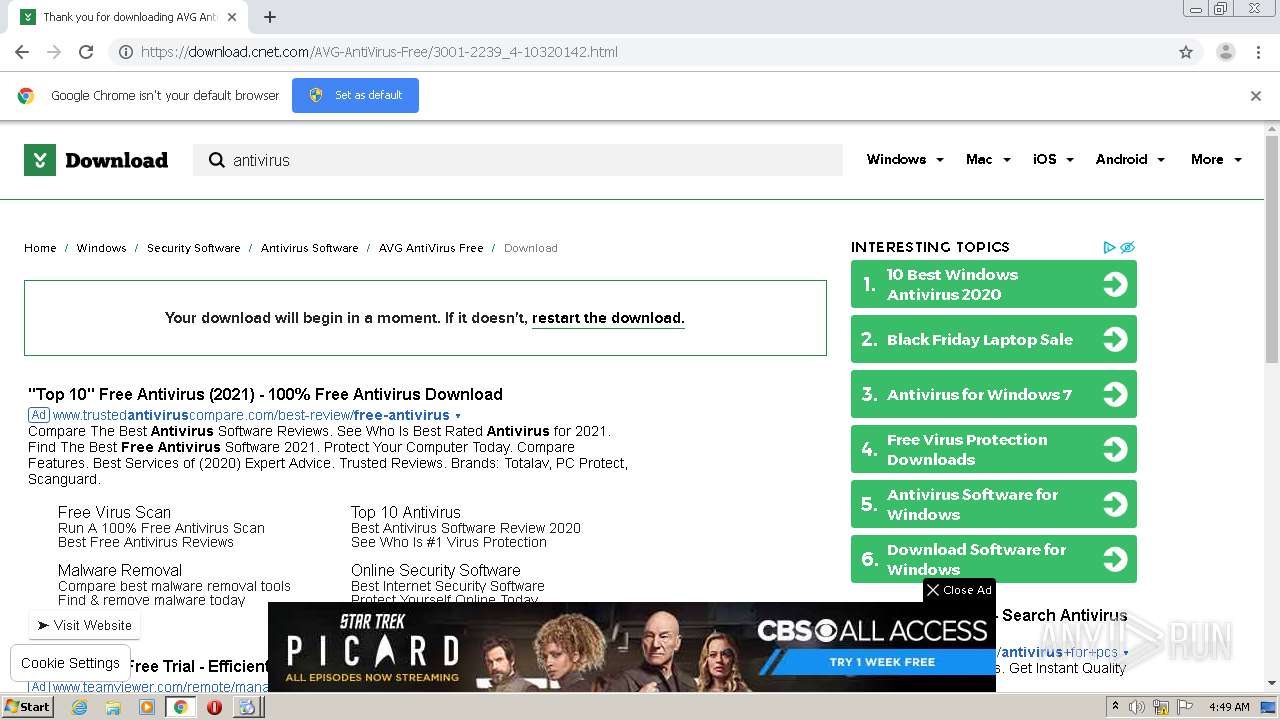
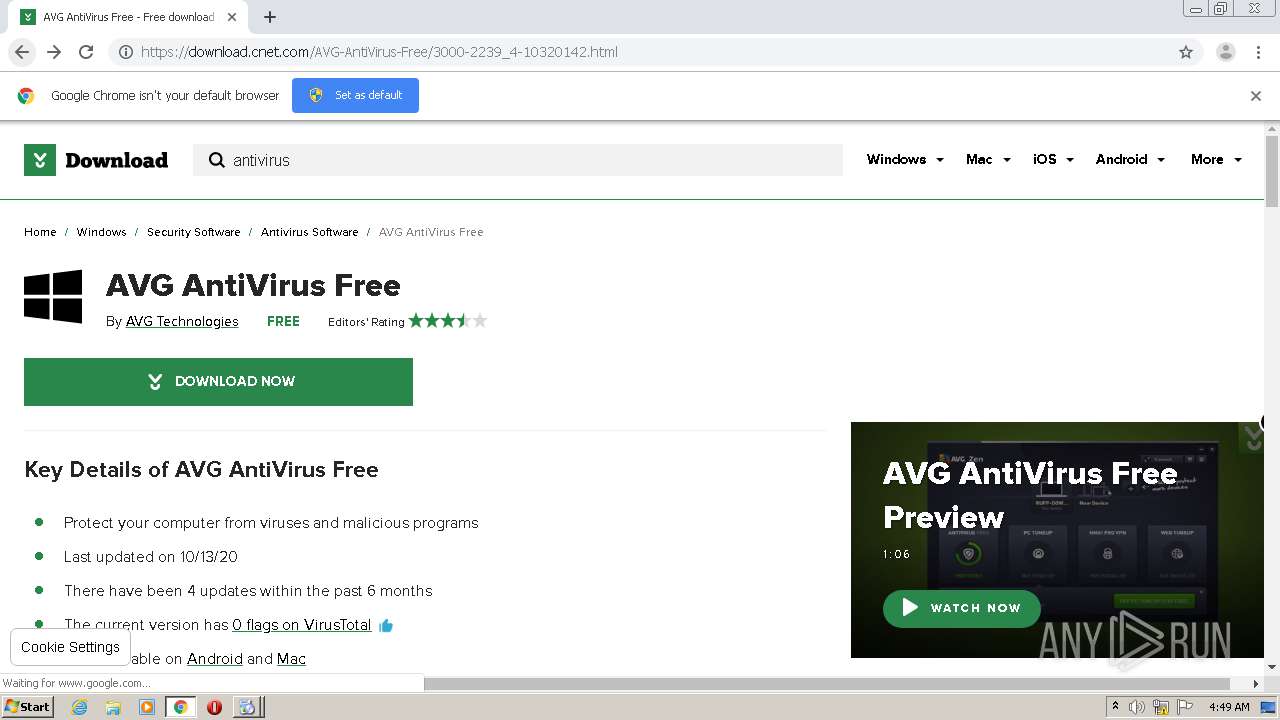
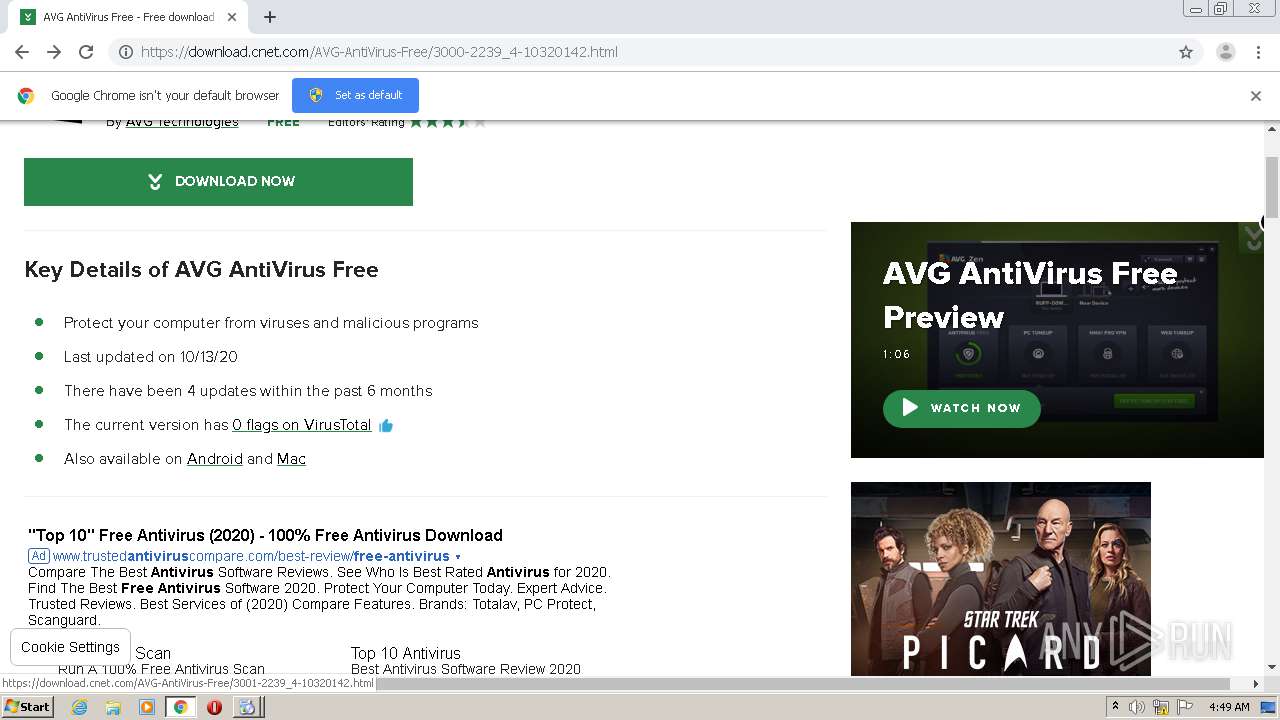
| URL: | https://download.cnet.com |
| Full analysis: | https://app.any.run/tasks/ba28bdd5-6cca-47cf-9eab-e01fc699e51f |
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2020, 04:46:44 |
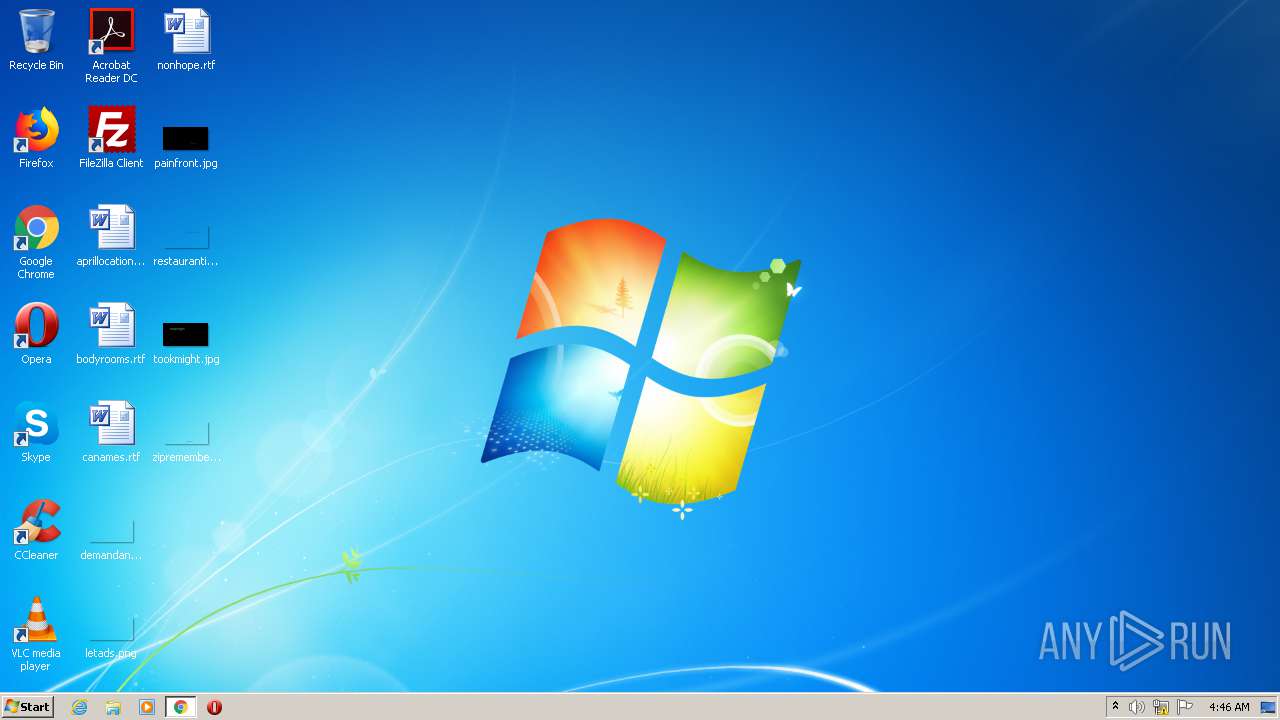
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
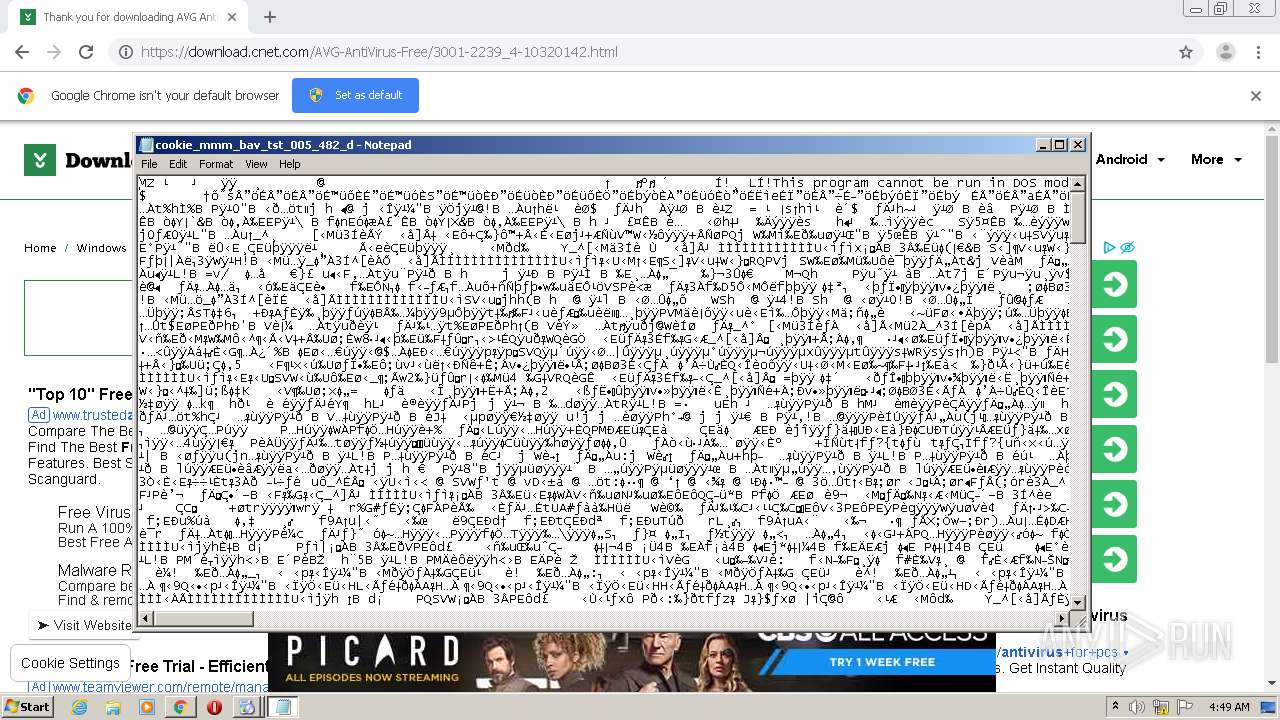
| MD5: | C723A854F6DC861558ED1F1113640514 |
| SHA1: | EF6B096B4FD229FFA0D2DCDF11363856CD9C21CE |
| SHA256: | 4E48F50212796E0E285D4A35AAF822C2DAE1D1325360CE9FB956BE82F03593E7 |
| SSDEEP: | 3:N8SElbKn:2SKmn |
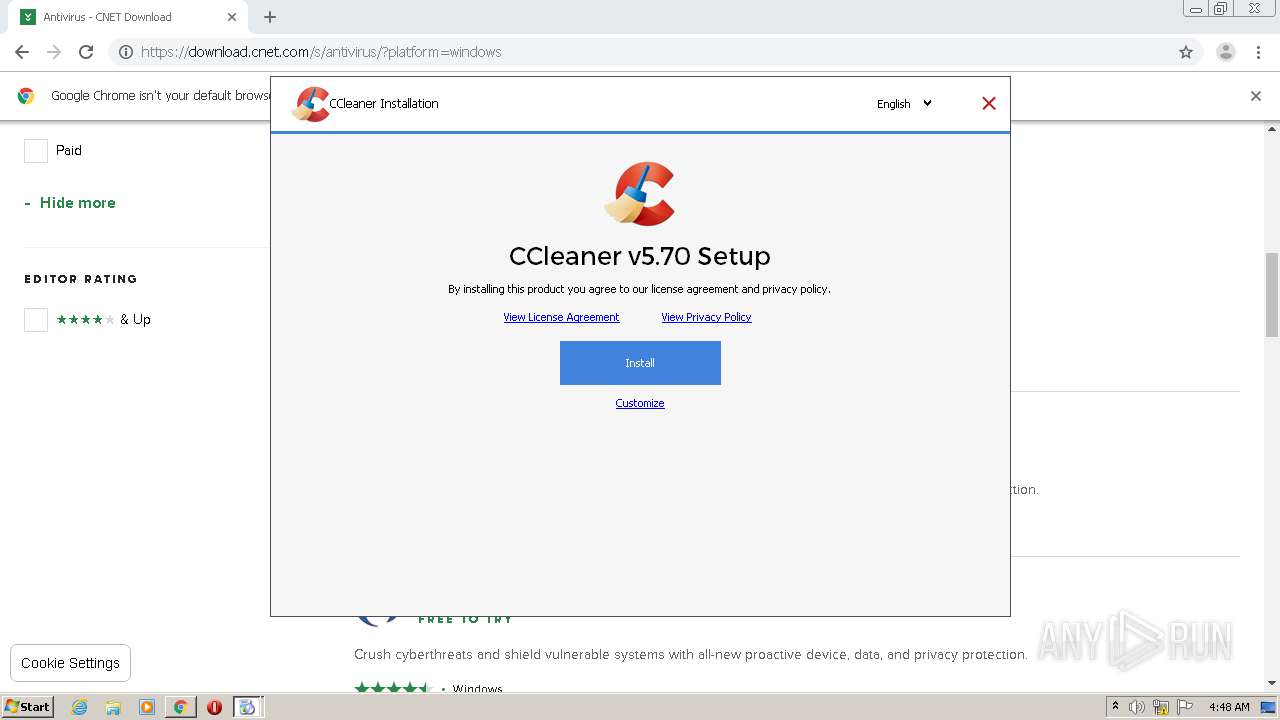
MALICIOUS
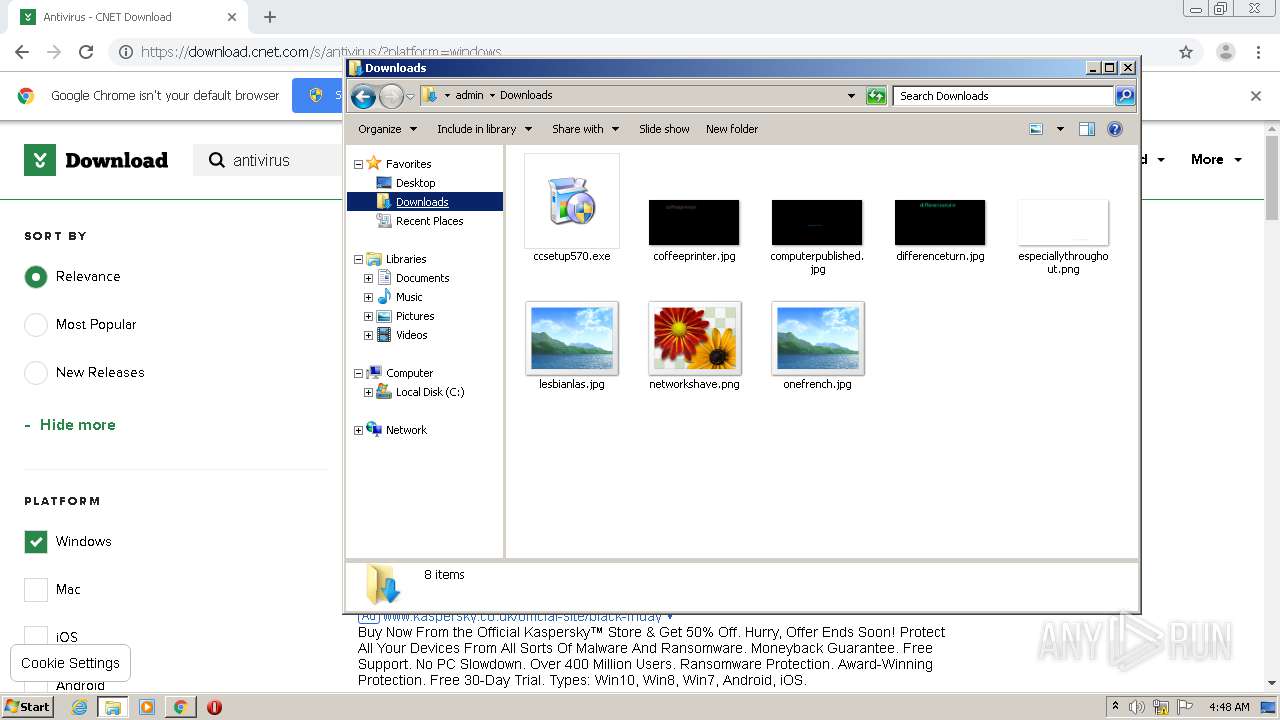
Application was dropped or rewritten from another process
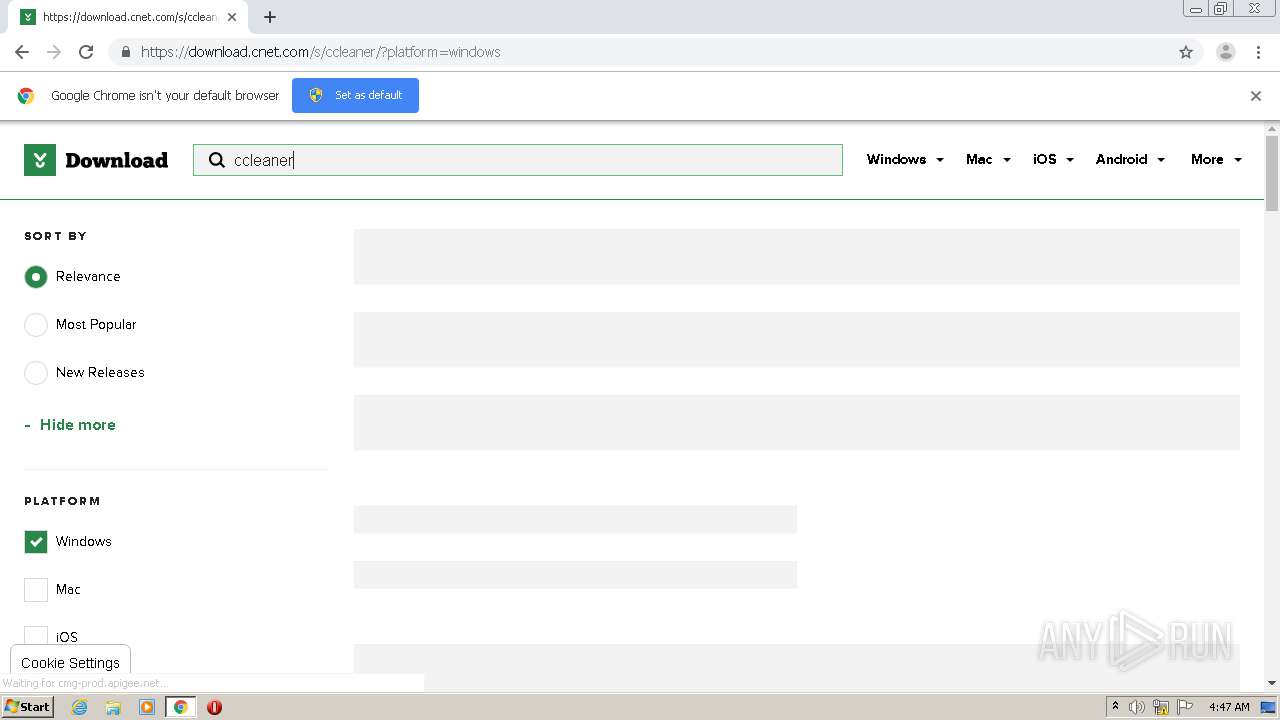
- ccsetup570.exe (PID: 3052)
- ns311A.tmp (PID: 3424)
- ccsetup570.exe (PID: 2128)
- ccsetup570.exe (PID: 3608)
- ccsetup570.exe (PID: 2204)
- ccsetup570.exe (PID: 528)
- ccsetup570.exe (PID: 2612)
- nsB156.tmp (PID: 3576)
- nsB8C8.tmp (PID: 1012)
Changes settings of System certificates
- ccsetup570.exe (PID: 3052)
Actions looks like stealing of personal data
- ccsetup570.exe (PID: 3052)
- ccsetup570.exe (PID: 2612)
Loads dropped or rewritten executable
- ccsetup570.exe (PID: 3052)
- ccsetup570.exe (PID: 528)
- ccsetup570.exe (PID: 2612)
Loads the Task Scheduler COM API
- ccsetup570.exe (PID: 2612)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2820)
- ccsetup570.exe (PID: 3052)
- ccsetup570.exe (PID: 528)
- ccsetup570.exe (PID: 2612)
Reads CPU info
- ccsetup570.exe (PID: 3052)
- ccsetup570.exe (PID: 528)
- ccsetup570.exe (PID: 2612)
Reads the cookies of Mozilla Firefox
- ccsetup570.exe (PID: 3052)
- ccsetup570.exe (PID: 2612)
Low-level read access rights to disk partition
- ccsetup570.exe (PID: 3052)
- ccsetup570.exe (PID: 528)
- ccsetup570.exe (PID: 2612)
Adds / modifies Windows certificates
- ccsetup570.exe (PID: 3052)
Reads internet explorer settings
- ccsetup570.exe (PID: 3052)
- ccsetup570.exe (PID: 528)
- ccsetup570.exe (PID: 2612)
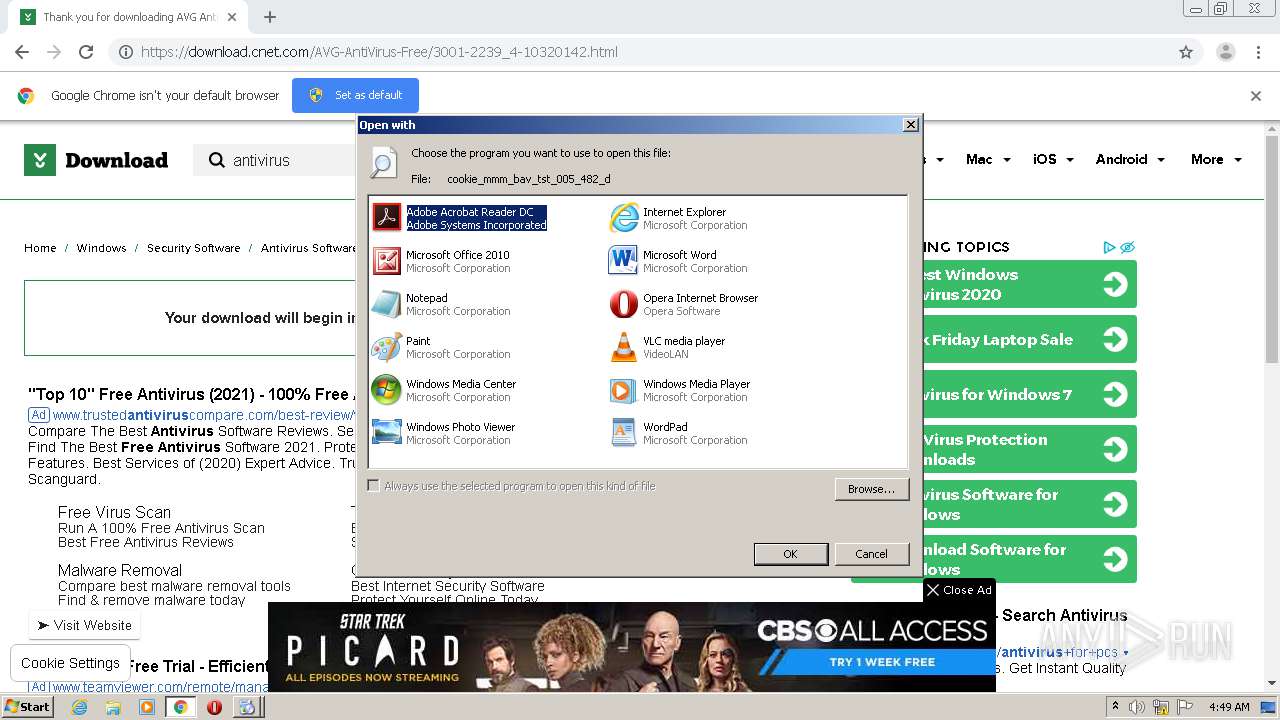
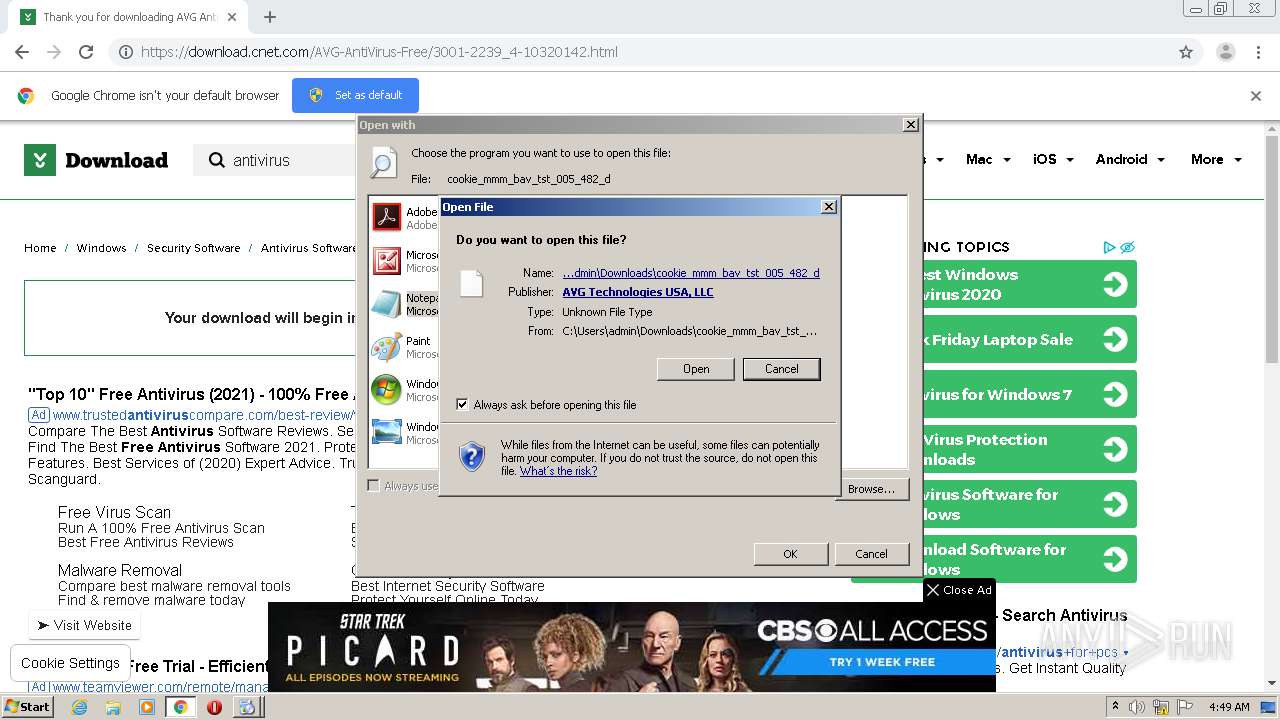
Starts application with an unusual extension
- ccsetup570.exe (PID: 3052)
- ccsetup570.exe (PID: 528)
- ccsetup570.exe (PID: 2612)
Reads Environment values
- ccsetup570.exe (PID: 3052)
- ccsetup570.exe (PID: 528)
- ccsetup570.exe (PID: 2612)
Drops a file that was compiled in debug mode
- ccsetup570.exe (PID: 3052)
- ccsetup570.exe (PID: 528)
- ccsetup570.exe (PID: 2612)
- chrome.exe (PID: 2820)
Creates files in the user directory
- ccsetup570.exe (PID: 3052)
- ccsetup570.exe (PID: 2612)
Reads the cookies of Google Chrome
- ccsetup570.exe (PID: 3052)
- ccsetup570.exe (PID: 2612)
Executed as Windows Service
- taskhost.exe (PID: 2376)
Drops a file with a compile date too recent
- chrome.exe (PID: 2820)
Uses RUNDLL32.EXE to load library
- chrome.exe (PID: 2820)
INFO
Application launched itself
- chrome.exe (PID: 2820)
Reads the hosts file
- chrome.exe (PID: 468)
- chrome.exe (PID: 2820)
Reads settings of System Certificates
- chrome.exe (PID: 2820)
- ccsetup570.exe (PID: 3052)
- ccsetup570.exe (PID: 528)
Manual execution by user
- explorer.exe (PID: 2532)
- ccsetup570.exe (PID: 3608)
- ccsetup570.exe (PID: 528)
- ccsetup570.exe (PID: 2204)
- ccsetup570.exe (PID: 2612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
89
Monitored processes
41
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,9085025538288244065,6167555667365970395,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10759786264425637212 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,9085025538288244065,6167555667365970395,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3293869036529415443 --mojo-platform-channel-handle=1384 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 528 | "C:\Users\admin\Downloads\ccsetup570.exe" | C:\Users\admin\Downloads\ccsetup570.exe | explorer.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Installer Exit code: 0 Version: 5.70.0.7909 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,9085025538288244065,6167555667365970395,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6727430906088326572 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Users\admin\AppData\Local\Temp\nsiA520.tmp\nsB8C8.tmp" C:\Windows\system32\ping.exe -n 1 -w 1000 www.ccleaner.com | C:\Users\admin\AppData\Local\Temp\nsiA520.tmp\nsB8C8.tmp | — | ccsetup570.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,9085025538288244065,6167555667365970395,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11067953911279203518 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,9085025538288244065,6167555667365970395,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12474000518477072634 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,9085025538288244065,6167555667365970395,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6659714207251260229 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,9085025538288244065,6167555667365970395,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=113955548212130657 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,9085025538288244065,6167555667365970395,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13984702917358109742 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
6 383
Read events
6 145
Write events
228
Delete events
10
Modification events
| (PID) Process: | (1796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2820-13251185218625125 |
Value: 259 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
213
Suspicious files
203
Text files
121
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC47943-B04.pma | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\74132c9a-922a-4ba8-8aef-f2802626232d.tmp | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF154223.TMP | text | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | text | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF154187.TMP | text | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15436b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
153
DNS requests
103
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3052 | ccsetup570.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3052 | ccsetup570.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3052 | ccsetup570.exe | GET | 200 | 151.101.0.64:80 | http://service.piriform.com/installcheck.aspx?p=1&v=5.70.7909&vx=5.35.6210&l=1033&b=1&o=6.1W3&g=0&i=1&a=0&c=770&d=2&e=31&n=ccsetup570.exe&id=003&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-HZ8S&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gd=0bb0ff58-08cc-4cde-902d-9cc186ff3a35 | US | text | 4 b | whitelisted |
3052 | ccsetup570.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3052 | ccsetup570.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3052 | ccsetup570.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFcLuT0XSrlKAgAAAACAVZE%3D | US | der | 471 b | whitelisted |
3052 | ccsetup570.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
468 | chrome.exe | 151.101.13.188:443 | download.cnet.com | Fastly | US | malicious |
468 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
468 | chrome.exe | 104.16.148.64:443 | cdn.cookielaw.org | Cloudflare Inc | US | unknown |
468 | chrome.exe | 104.75.88.141:443 | c.go-mpulse.net | Akamai Technologies, Inc. | NL | unknown |
468 | chrome.exe | 142.250.80.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
468 | chrome.exe | 104.20.184.68:443 | geolocation.onetrust.com | Cloudflare Inc | US | shared |
468 | chrome.exe | 35.238.168.80:443 | cmg-prod.apigee.net | — | US | unknown |
468 | chrome.exe | 151.101.194.202:443 | mab.chartbeat.com | Fastly | US | suspicious |
468 | chrome.exe | 23.201.170.188:443 | tags.tiqcdn.com | Akamai Technologies, Inc. | NL | unknown |
468 | chrome.exe | 151.101.129.194:443 | confiant-integrations.global.ssl.fastly.net | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.cnet.com |
| whitelisted |
accounts.google.com |
| shared |
cdn.cookielaw.org |
| whitelisted |
cmg1.cbsistatic.com |
| unknown |
dl1.cbsistatic.com |
| whitelisted |
c.go-mpulse.net |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
at.cbsi.com |
| suspicious |
securepubads.g.doubleclick.net |
| whitelisted |
static.chartbeat.com |
| whitelisted |