| File name: | Coronavirus COVID-19 Update and Contingency Plan From KeyTech.eml |
| Full analysis: | https://app.any.run/tasks/23990ae8-fba6-4e4c-bb92-20d5185143e5 |
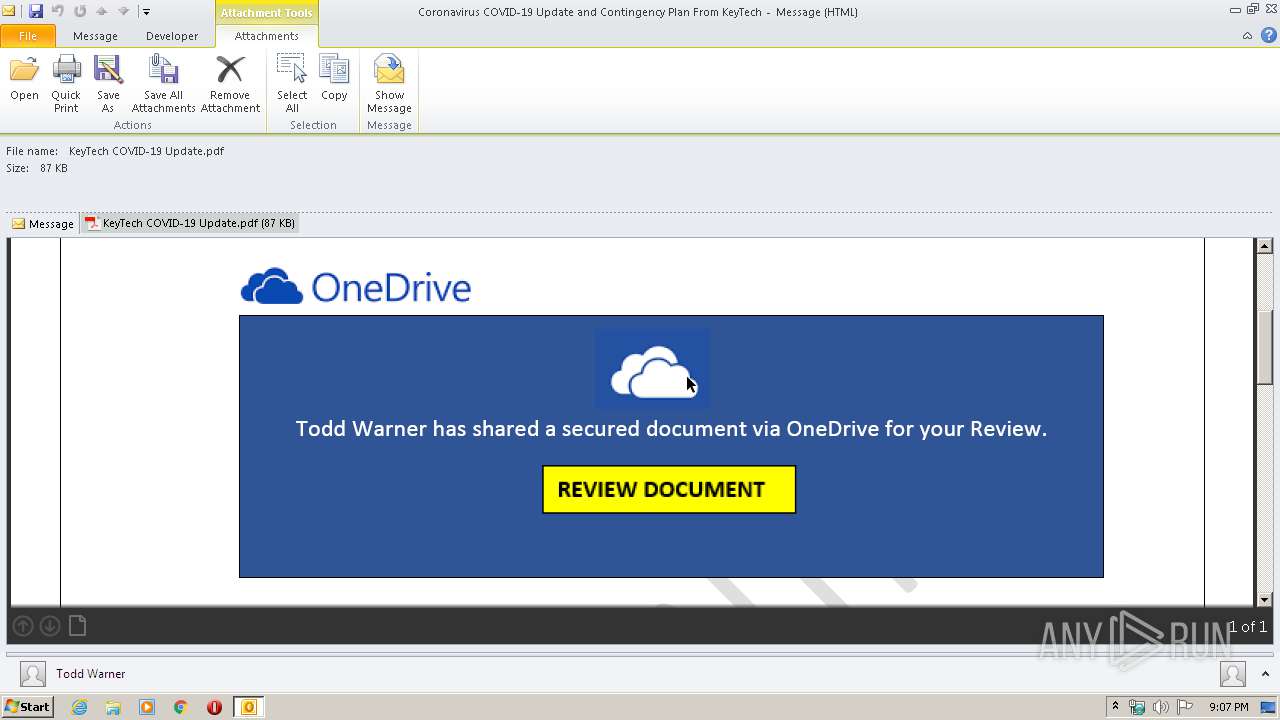
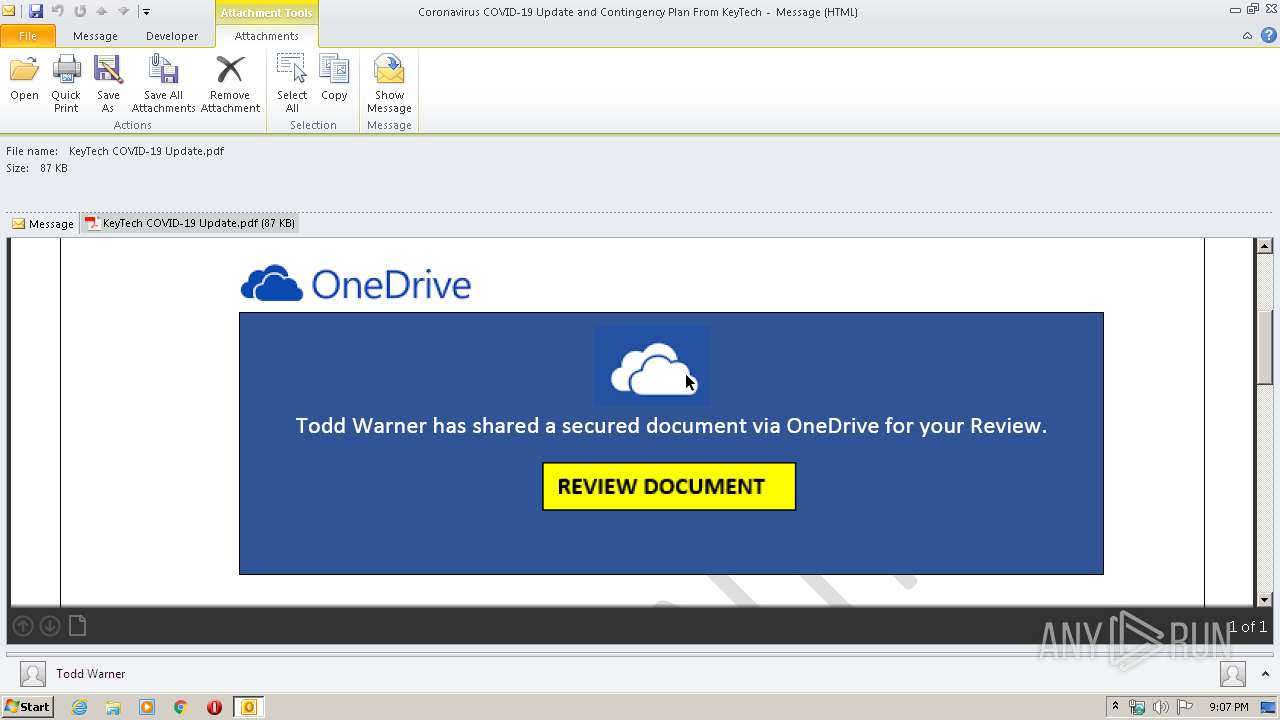
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 20:06:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | SMTP mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | EC26F76B2DD657C7163A3B839C24BDB4 |
| SHA1: | 6A9C8F644D0949296BB981499F958C120CC300DF |
| SHA256: | 4E2E898D59CF6F76ADD6DA93C7E6AB02812FB42CAB9A64DD33910ACA3217A0D9 |
| SSDEEP: | 3072:to3nsQmudApiI38baVBT5DeuV94+TD1CicAf+/3K+QbBw:u3dmurCTcWCi1CNAm/iK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 3776)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 304)
Creates files in the user directory
- OUTLOOK.EXE (PID: 304)
Executed via COM
- prevhost.exe (PID: 2068)
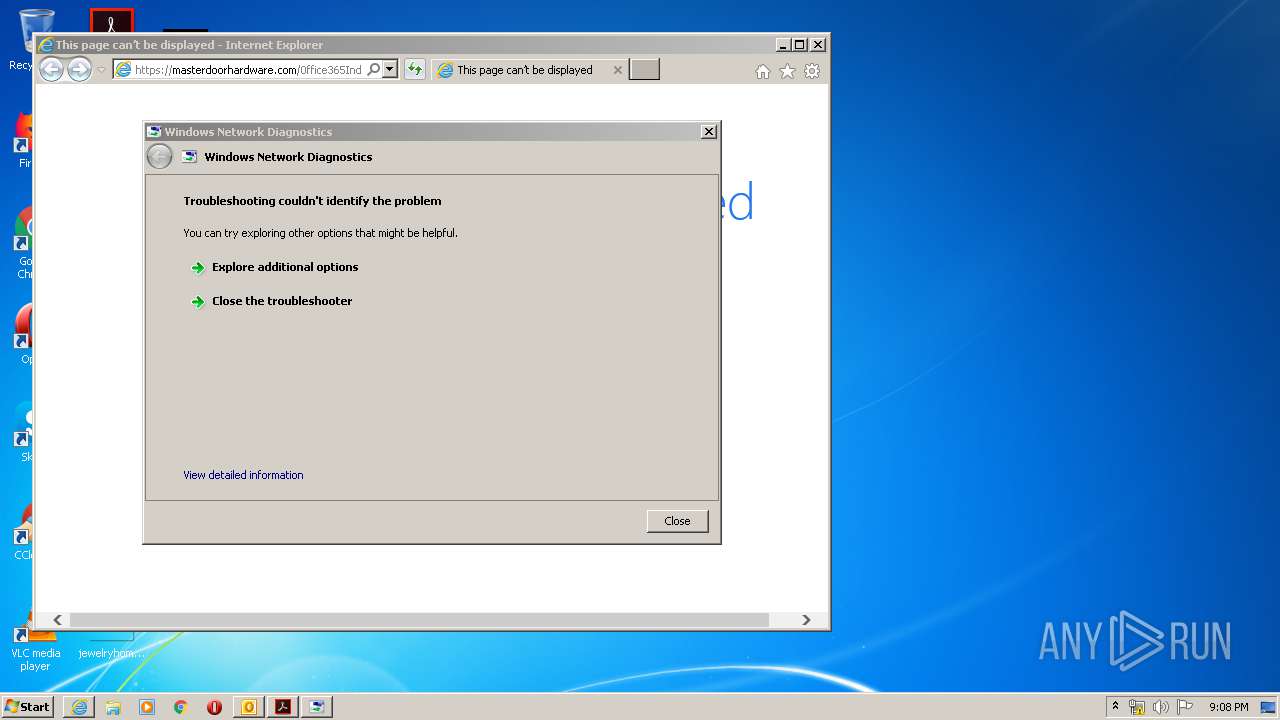
- sdiagnhost.exe (PID: 308)
Executable content was dropped or overwritten
- msdt.exe (PID: 2340)
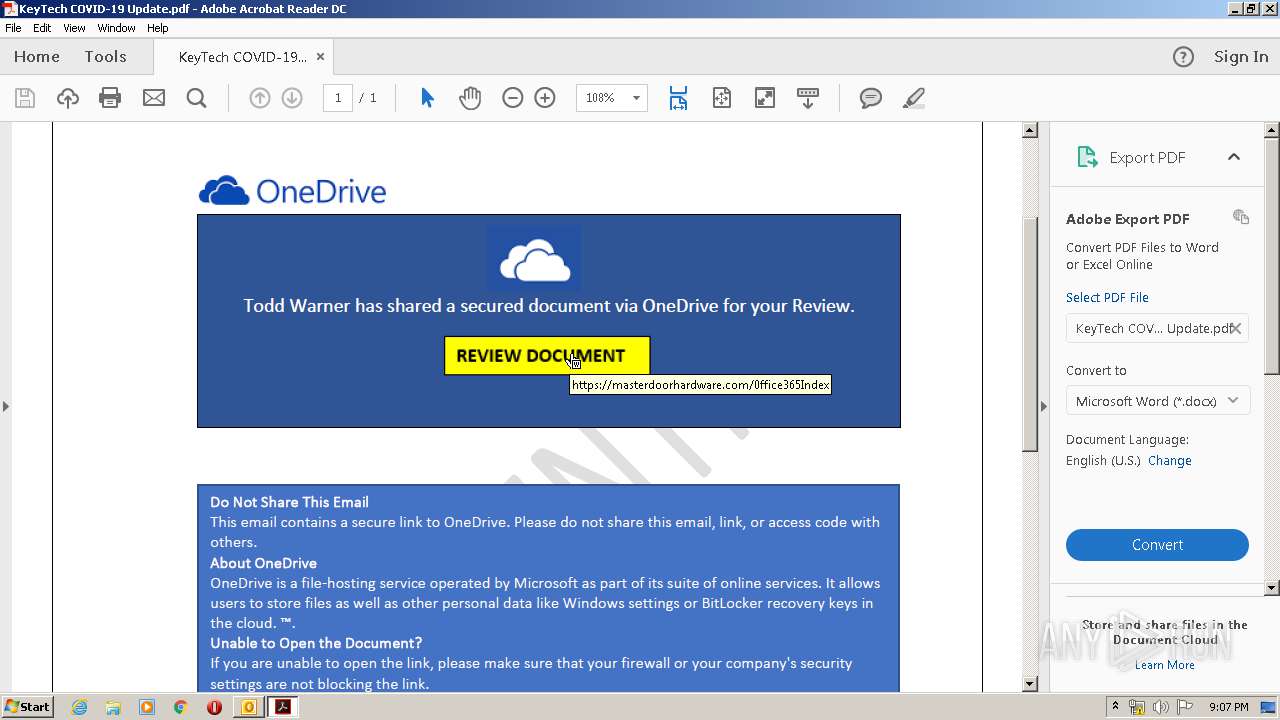
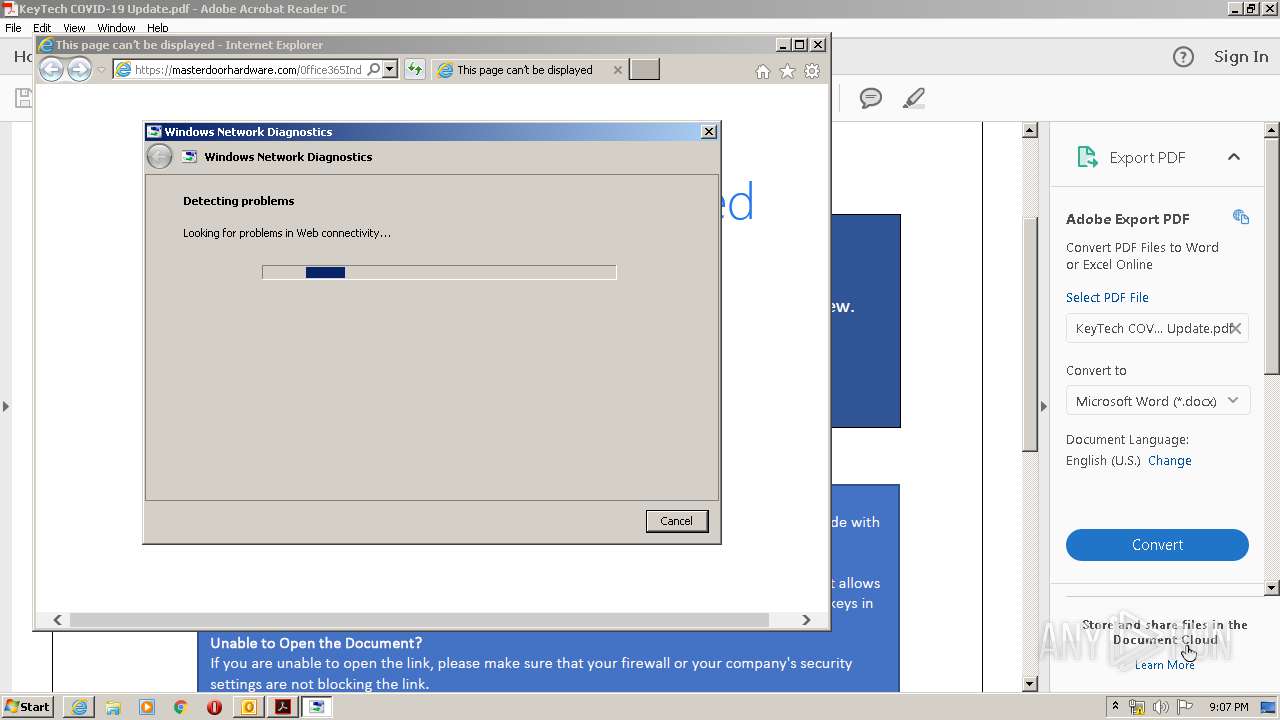
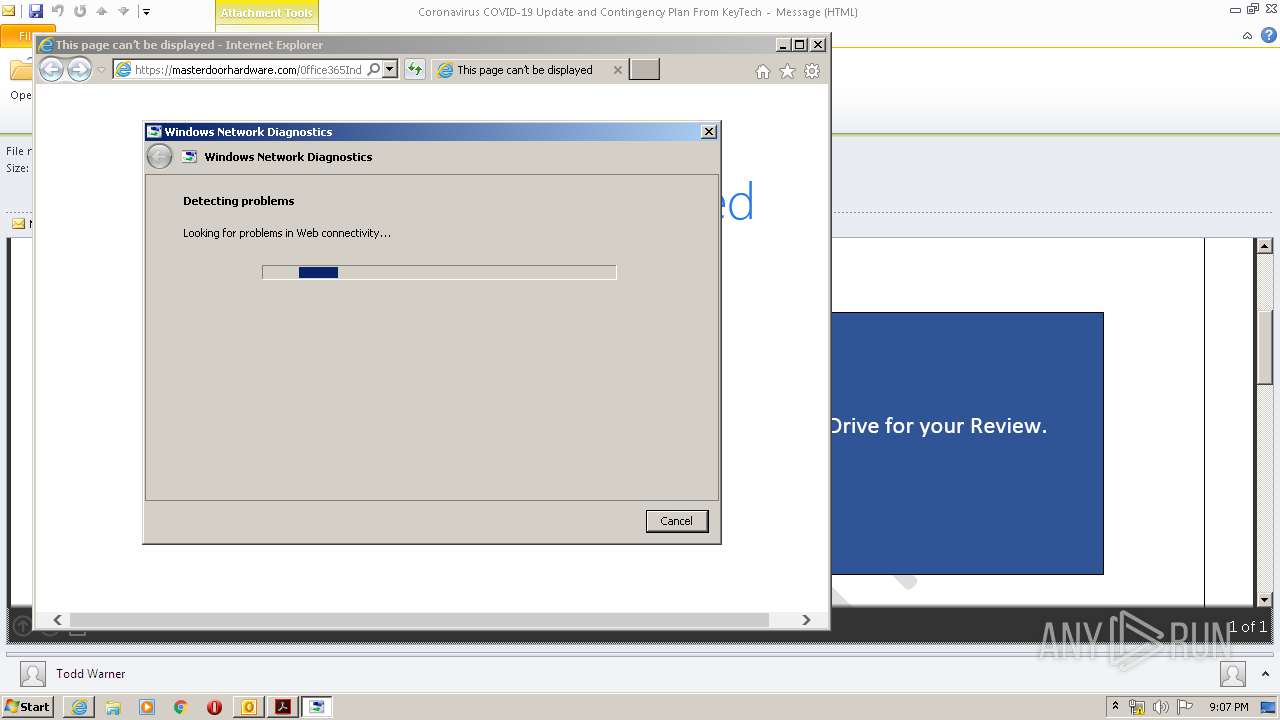
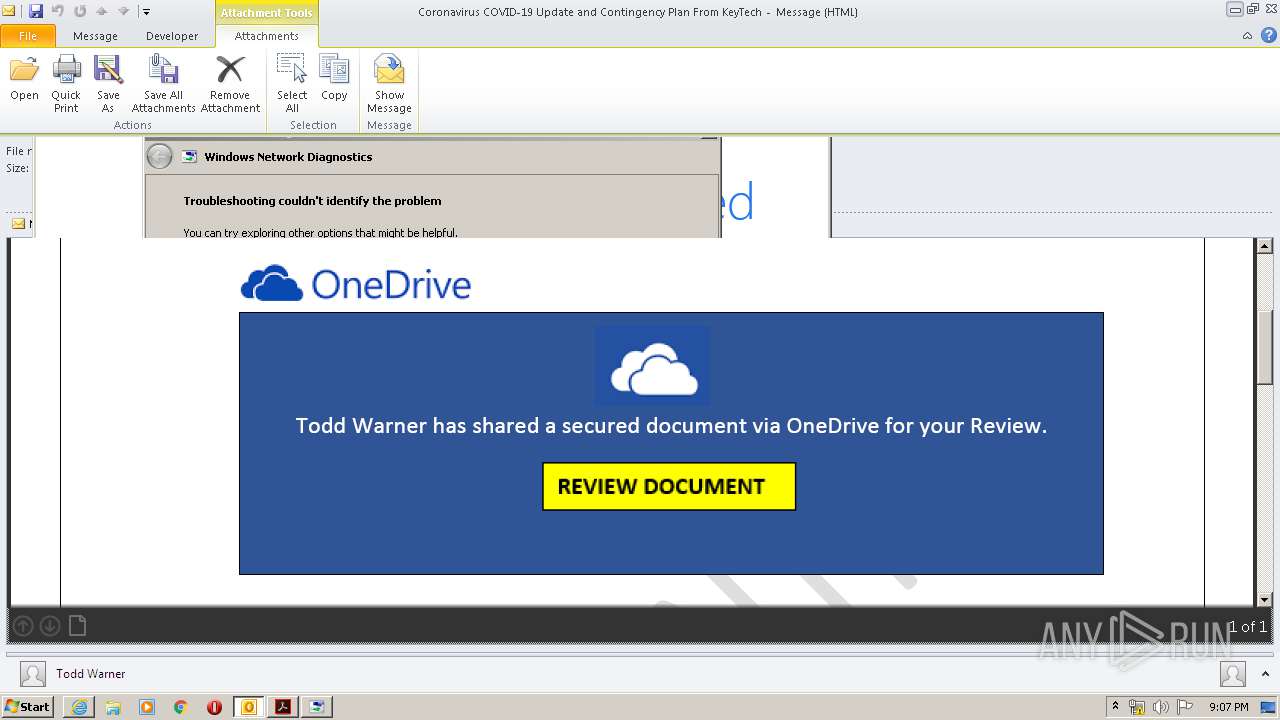
Starts Internet Explorer
- AcroRd32.exe (PID: 3776)
Creates files in the program directory
- AdobeARM.exe (PID: 2600)
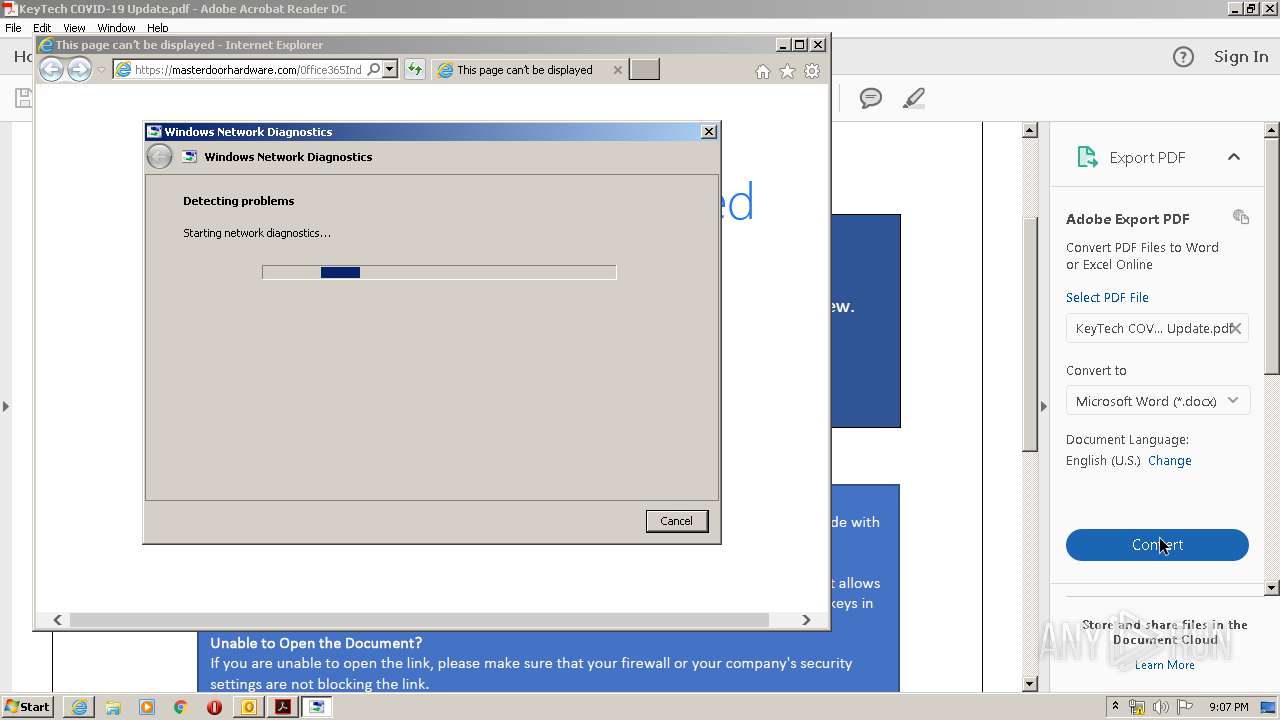
Uses IPCONFIG.EXE to discover IP address
- sdiagnhost.exe (PID: 308)
INFO
Reads Internet Cache Settings
- AcroRd32.exe (PID: 2904)
- AcroRd32.exe (PID: 3776)
- iexplore.exe (PID: 576)
- iexplore.exe (PID: 2124)
Reads the hosts file
- RdrCEF.exe (PID: 3556)
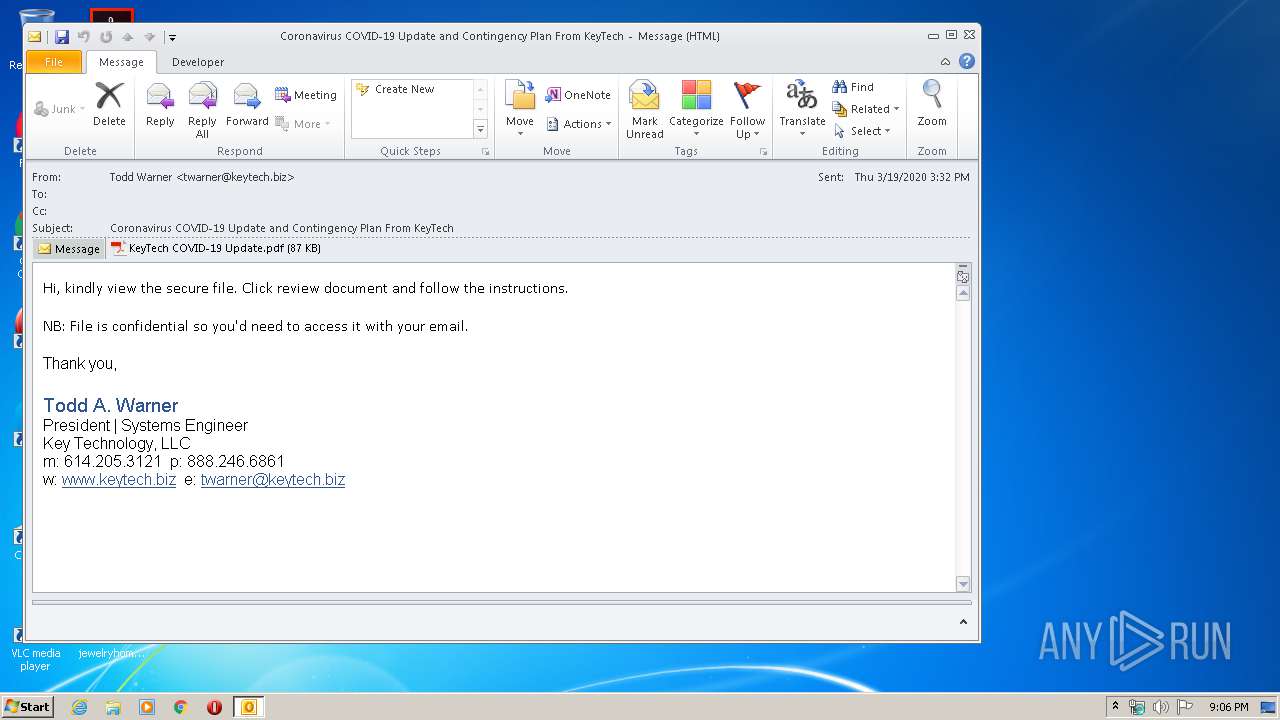
Drops Coronavirus (possible) decoy
- OUTLOOK.EXE (PID: 304)
Reads settings of System Certificates
- AcroRd32.exe (PID: 3776)
- iexplore.exe (PID: 576)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 304)
Application launched itself
- RdrCEF.exe (PID: 3556)
Changes internet zones settings
- iexplore.exe (PID: 576)
Reads internet explorer settings
- iexplore.exe (PID: 2124)
Creates files in the user directory
- iexplore.exe (PID: 576)
Adds / modifies Windows certificates
- iexplore.exe (PID: 576)
Changes settings of System certificates
- iexplore.exe (PID: 576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 7) (100) |
|---|
Total processes
57
Monitored processes
18
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Coronavirus COVID-19 Update and Contingency Plan From KeyTech.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 308 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 528 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
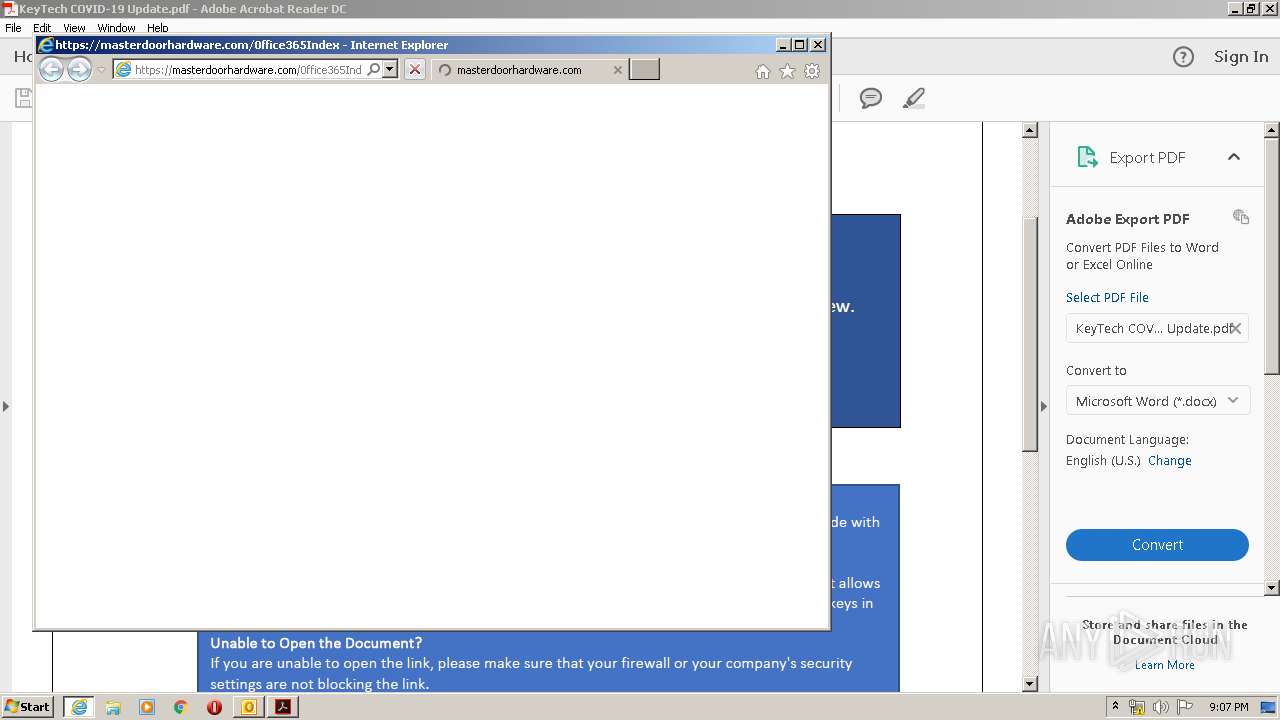
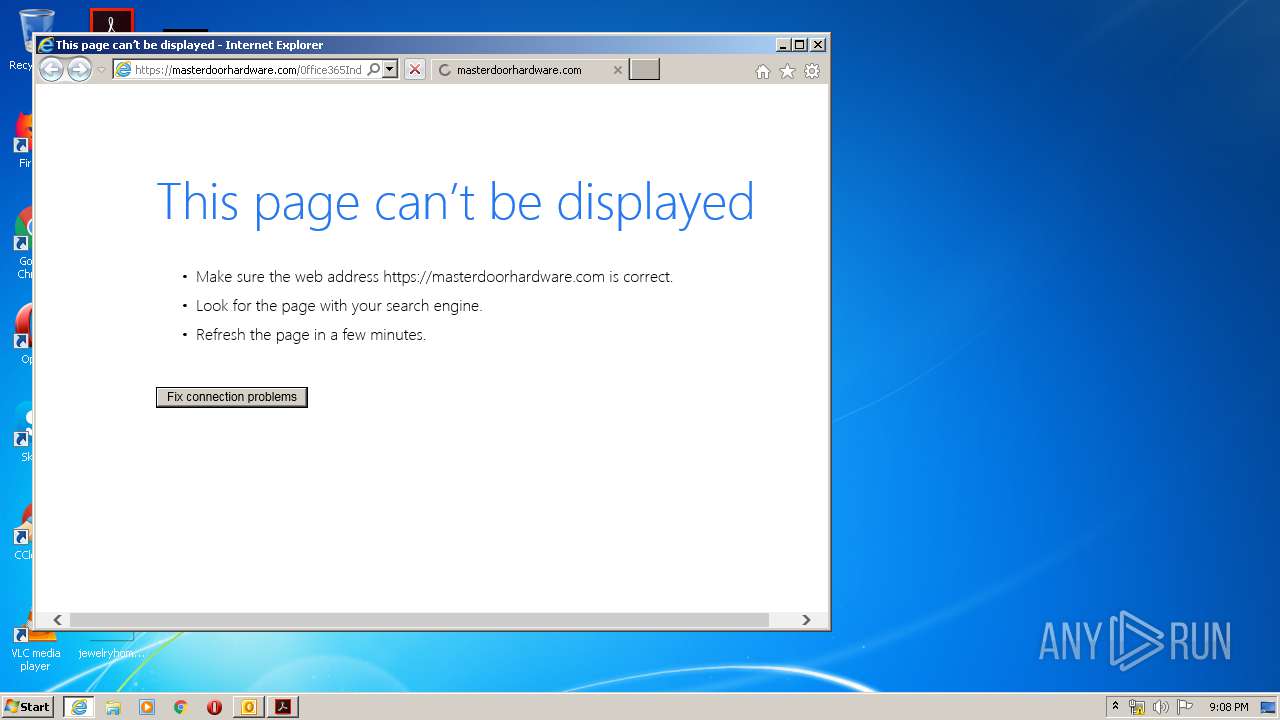
| 576 | "C:\Program Files\Internet Explorer\iexplore.exe" https://masterdoorhardware.com/0ffice365Index | C:\Program Files\Internet Explorer\iexplore.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1740 | "C:\Windows\system32\makecab.exe" /f NetworkConfiguration.ddf | C:\Windows\system32\makecab.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1836 | "C:\Windows\system32\ipconfig.exe" /all | C:\Windows\system32\ipconfig.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2068 | C:\Windows\system32\prevhost.exe {DC6EFB56-9CFA-464D-8880-44885D7DC193} -Embedding | C:\Windows\system32\prevhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Preview Handler Surrogate Host Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:576 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
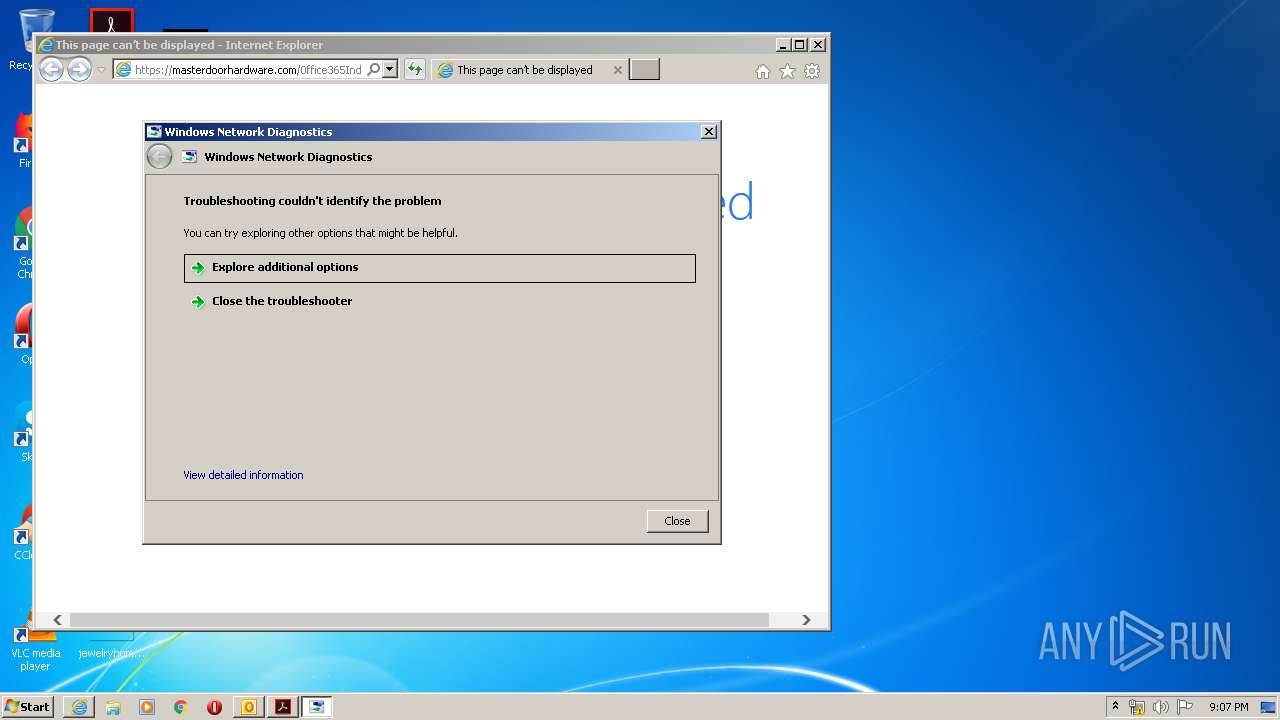
| 2340 | -modal 66328 -skip TRUE -path C:\Windows\diagnostics\system\networking -af C:\Users\admin\AppData\Local\Temp\NDF8408.tmp -ep NetworkDiagnosticsWeb | C:\Windows\system32\msdt.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:15.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.27.2646 Modules
| |||||||||||||||
Total events
9 921
Read events
2 514
Write events
5 145
Delete events
2 262
Modification events
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
2
Suspicious files
24
Text files
92
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6B93.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\EFUO3N6C\KeyTech COVID-19 Update (2).pdf\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2904 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 2904 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1vyn969_1ciiy0e_28o.tmp | — | |
MD5:— | SHA256:— | |||
| 2904 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rgj37t3_1ciiy0d_28o.tmp | — | |
MD5:— | SHA256:— | |||
| 2904 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rgrcmdk_1ciiy0g_28o.tmp | — | |
MD5:— | SHA256:— | |||
| 2904 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rmzb52b_1ciiy0f_28o.tmp | — | |
MD5:— | SHA256:— | |||
| 3776 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\Cab693D.tmp | — | |
MD5:— | SHA256:— | |||
| 3776 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\Tar693E.tmp | — | |
MD5:— | SHA256:— | |||
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
38
DNS requests
15
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3776 | AcroRd32.exe | GET | 304 | 23.55.110.79:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | US | — | — | whitelisted |
3776 | AcroRd32.exe | GET | 304 | 23.55.110.79:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | US | — | — | whitelisted |
304 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3776 | AcroRd32.exe | GET | 304 | 23.55.110.79:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | US | — | — | whitelisted |
3776 | AcroRd32.exe | GET | 304 | 23.55.110.79:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | US | — | — | whitelisted |
3776 | AcroRd32.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
576 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
576 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
576 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3776 | AcroRd32.exe | GET | 200 | 23.55.110.79:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | US | compressed | 9.54 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3776 | AcroRd32.exe | 23.210.248.251:443 | armmf.adobe.com | Akamai International B.V. | NL | whitelisted |
2124 | iexplore.exe | 52.221.234.78:443 | masterdoorhardware.com | Amazon.com, Inc. | SG | suspicious |
3776 | AcroRd32.exe | 23.55.110.79:80 | acroipm2.adobe.com | NTT America, Inc. | US | suspicious |
3776 | AcroRd32.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 72.247.224.199:443 | ardownload2.adobe.com | Akamai Technologies, Inc. | US | whitelisted |
— | — | 23.210.248.251:443 | armmf.adobe.com | Akamai International B.V. | NL | whitelisted |
576 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
576 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
824 | svchost.exe | 52.221.234.78:443 | masterdoorhardware.com | Amazon.com, Inc. | SG | suspicious |
576 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
masterdoorhardware.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
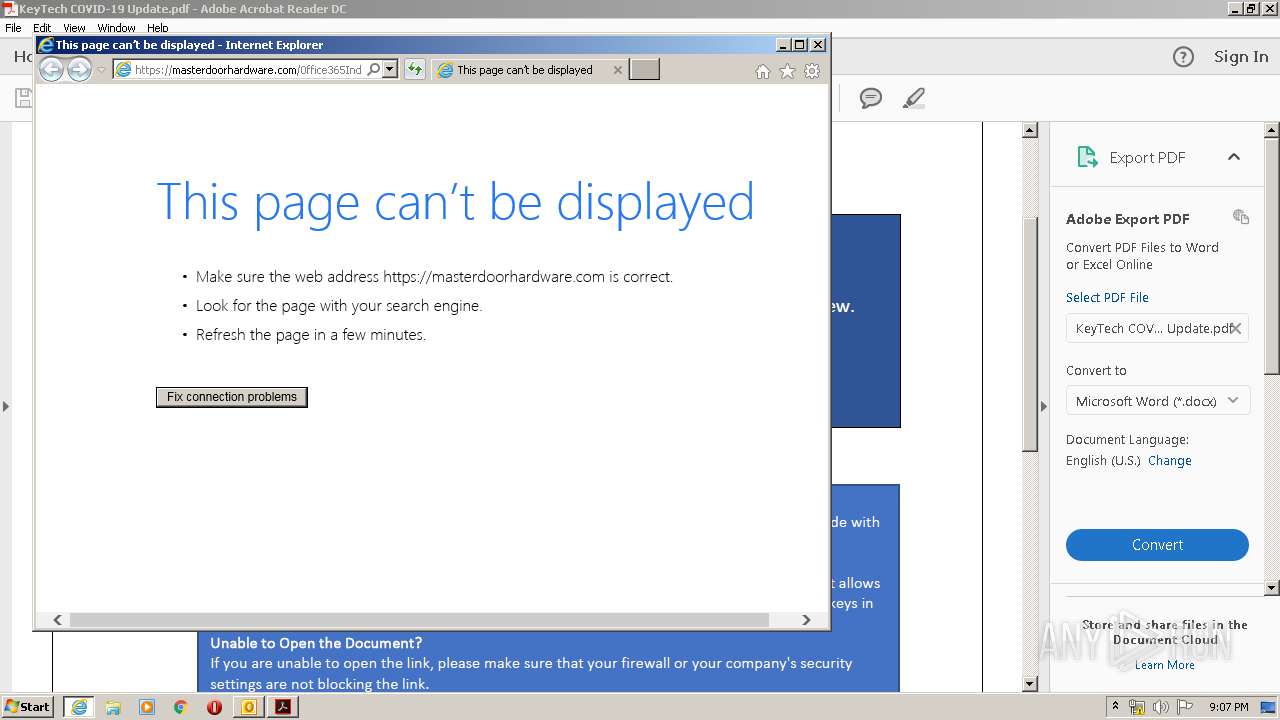
2124 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2124 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
824 | svchost.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2124 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2124 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2124 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2124 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |