| File name: | test.rar |
| Full analysis: | https://app.any.run/tasks/9a443122-2af2-4485-8038-92c14b88ebc4 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2025, 19:26:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | B92B894CE4368F90FBB8ECAB45BB2F49 |
| SHA1: | 2B9CBDA7F00F3BFB415F61494D0830D1B72ACE54 |
| SHA256: | 4E2AF3A5C2640CBFC8C98B04FBFB08E4F35C357AD1667BB59CFB77FBAD4D93D2 |
| SSDEEP: | 196608:RjRMQI3+FORKJwzuG/Cyjfy45/AqqQL99:RjyQgCORtH6yW/qqi99 |
MALICIOUS
No malicious indicators.SUSPICIOUS
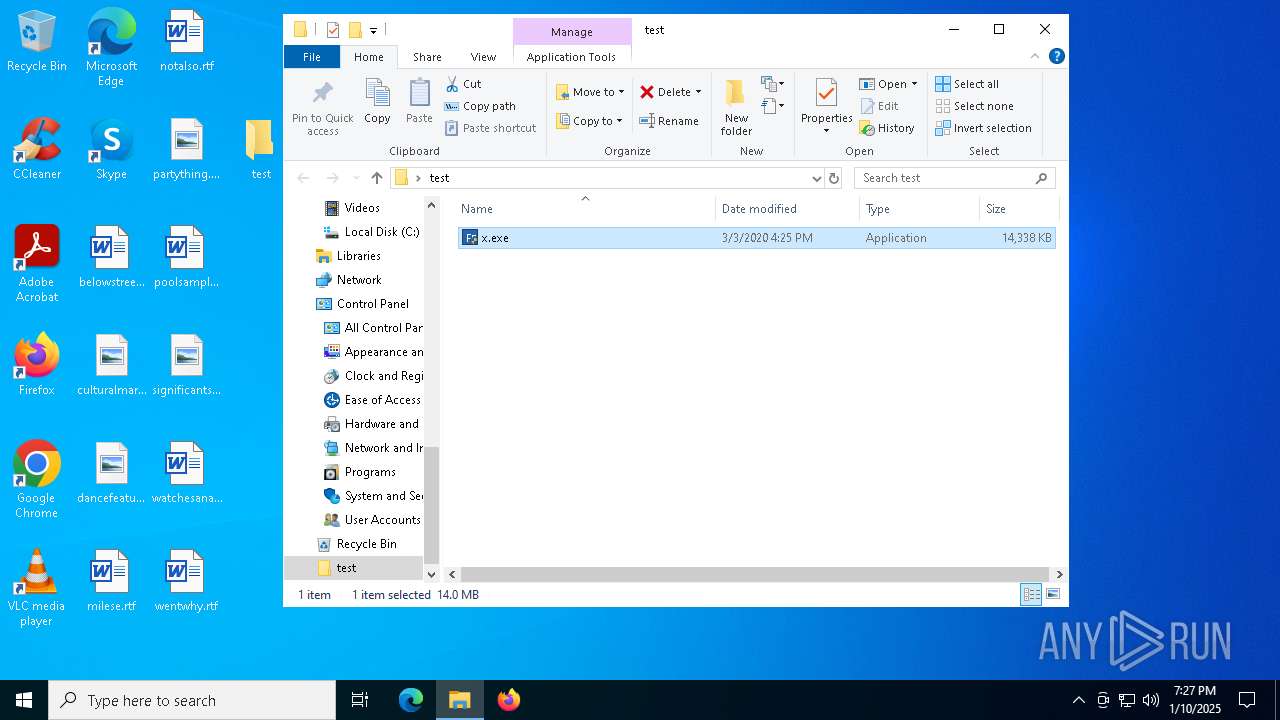
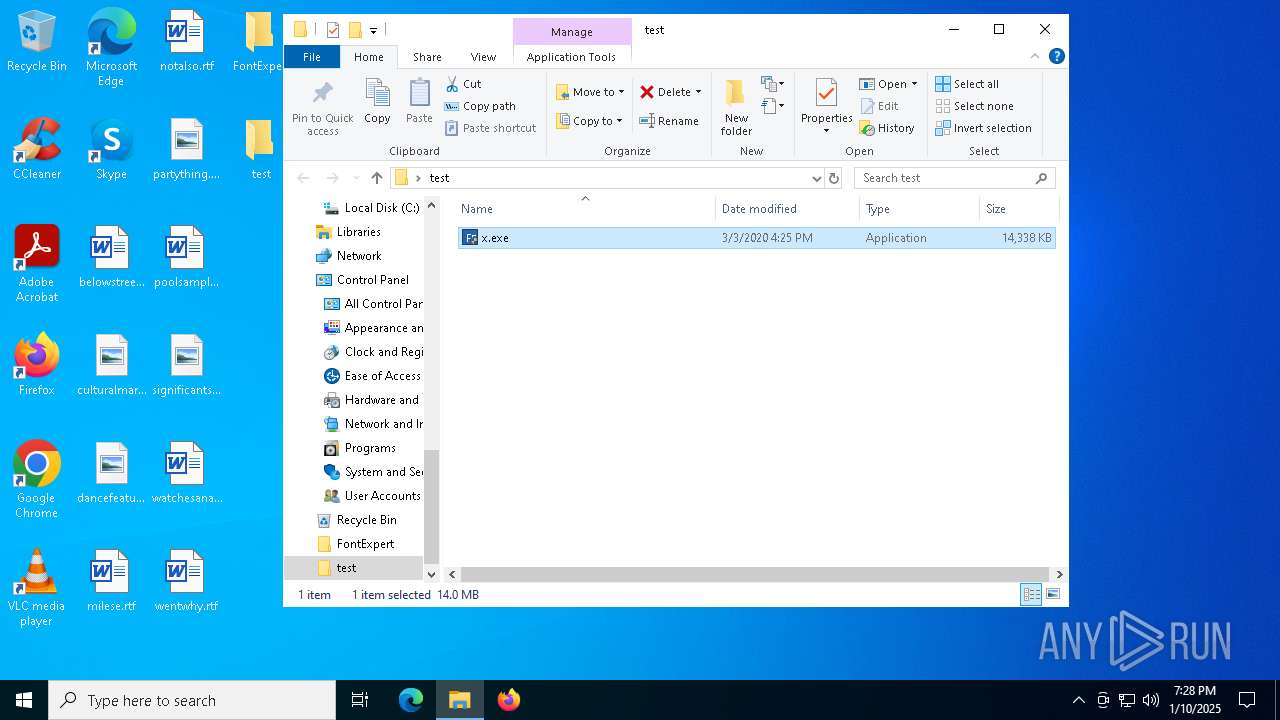
Executable content was dropped or overwritten
- x.exe (PID: 4740)
- packeg.exe (PID: 2672)
- install.exe (PID: 6552)
- install.exe (PID: 6244)
Malware-specific behavior (creating "System.dll" in Temp)
- x.exe (PID: 4740)
- install.exe (PID: 6552)
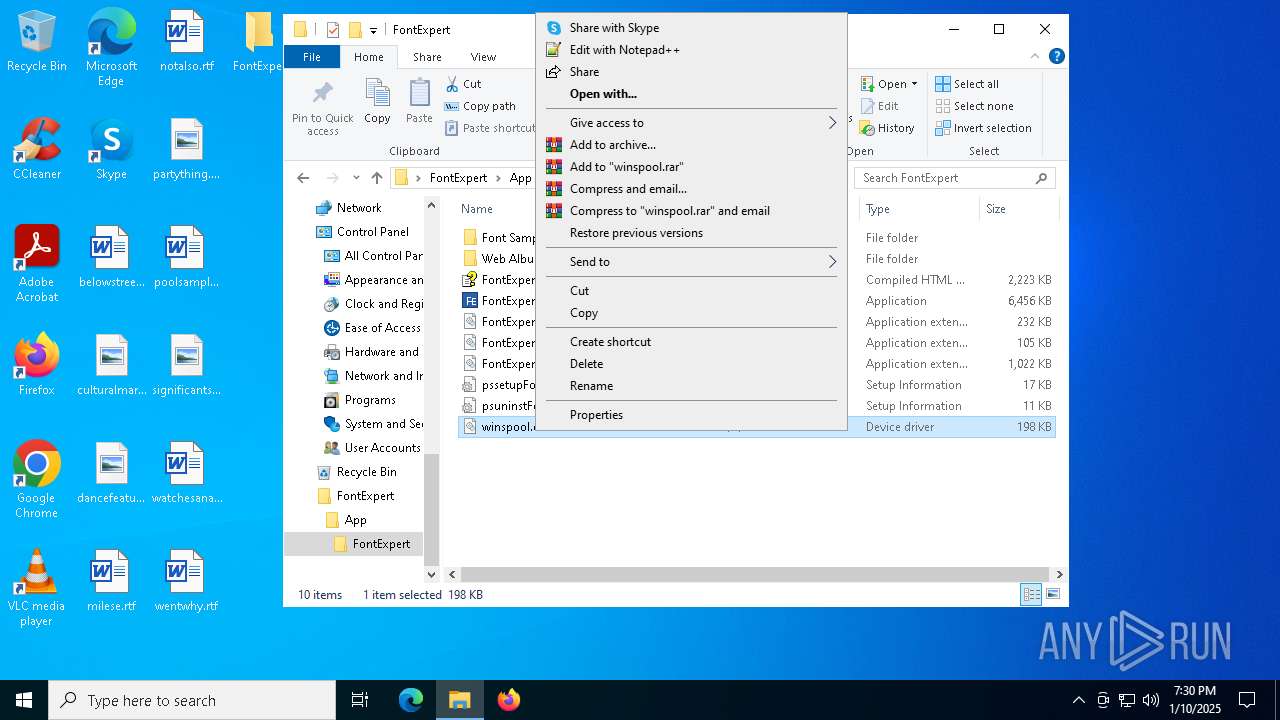
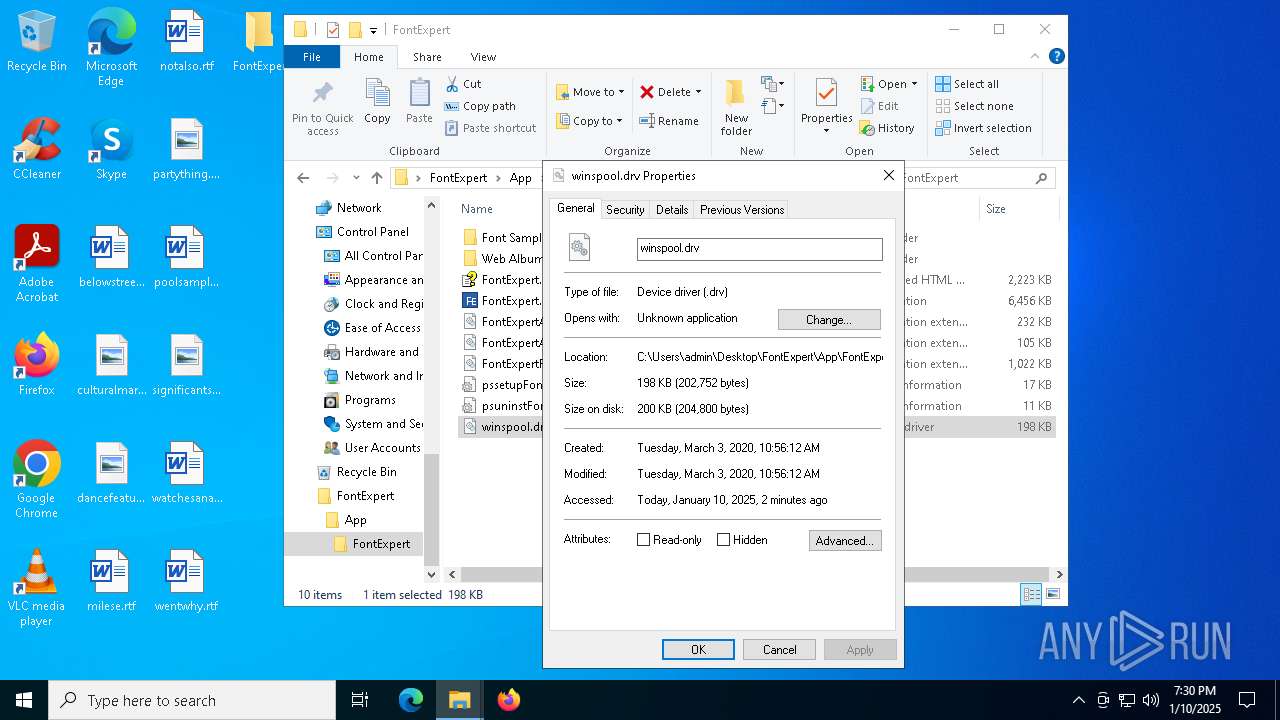
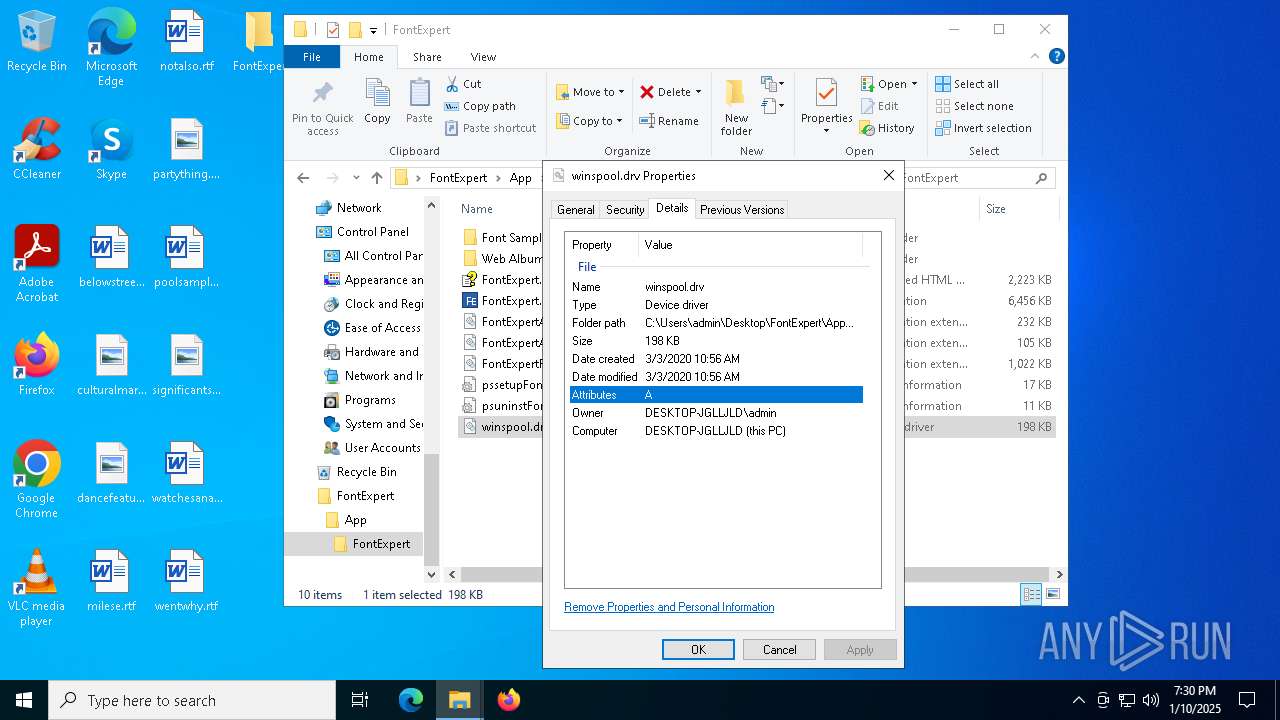
The process creates files with name similar to system file names
- x.exe (PID: 4740)
- install.exe (PID: 6552)
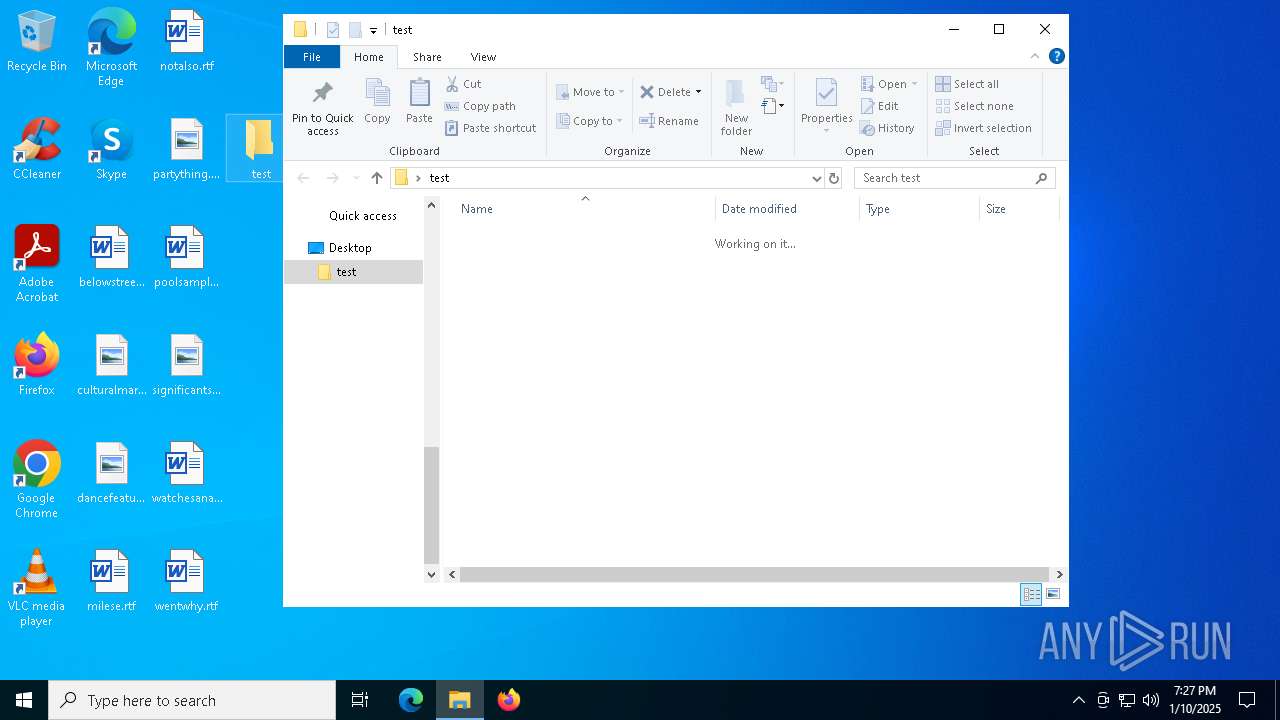
Drops 7-zip archiver for unpacking
- x.exe (PID: 4740)
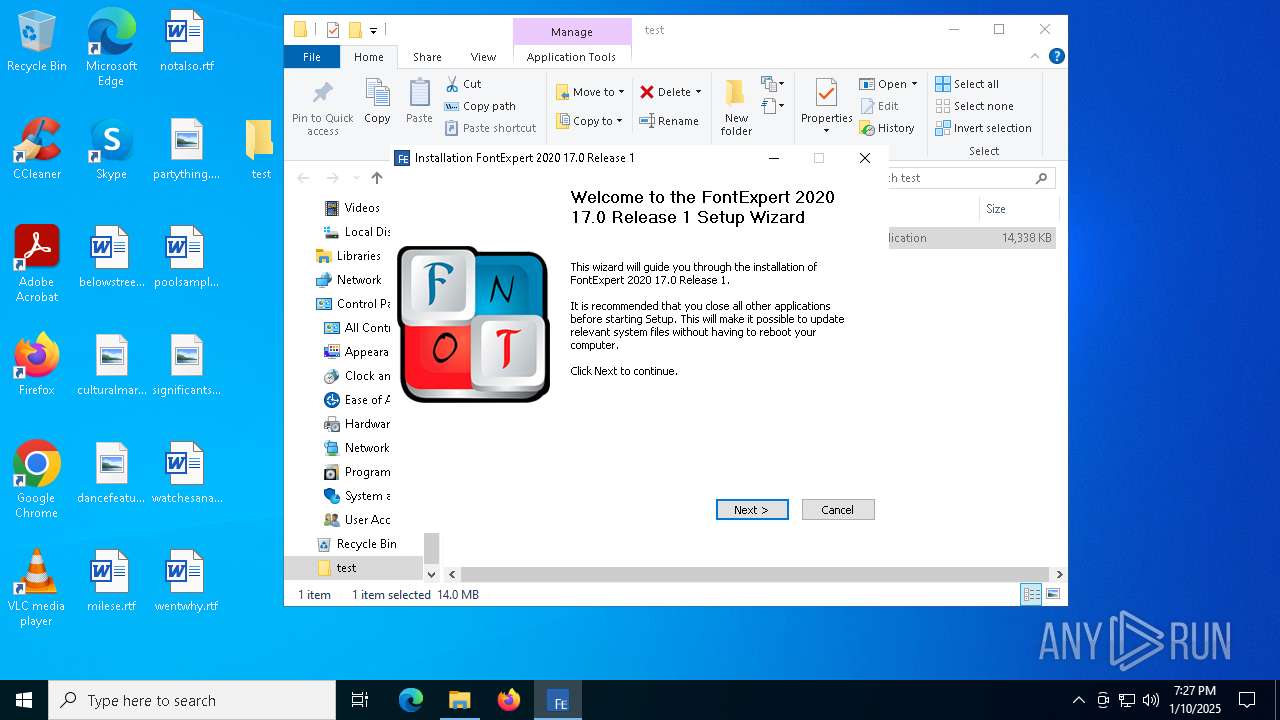
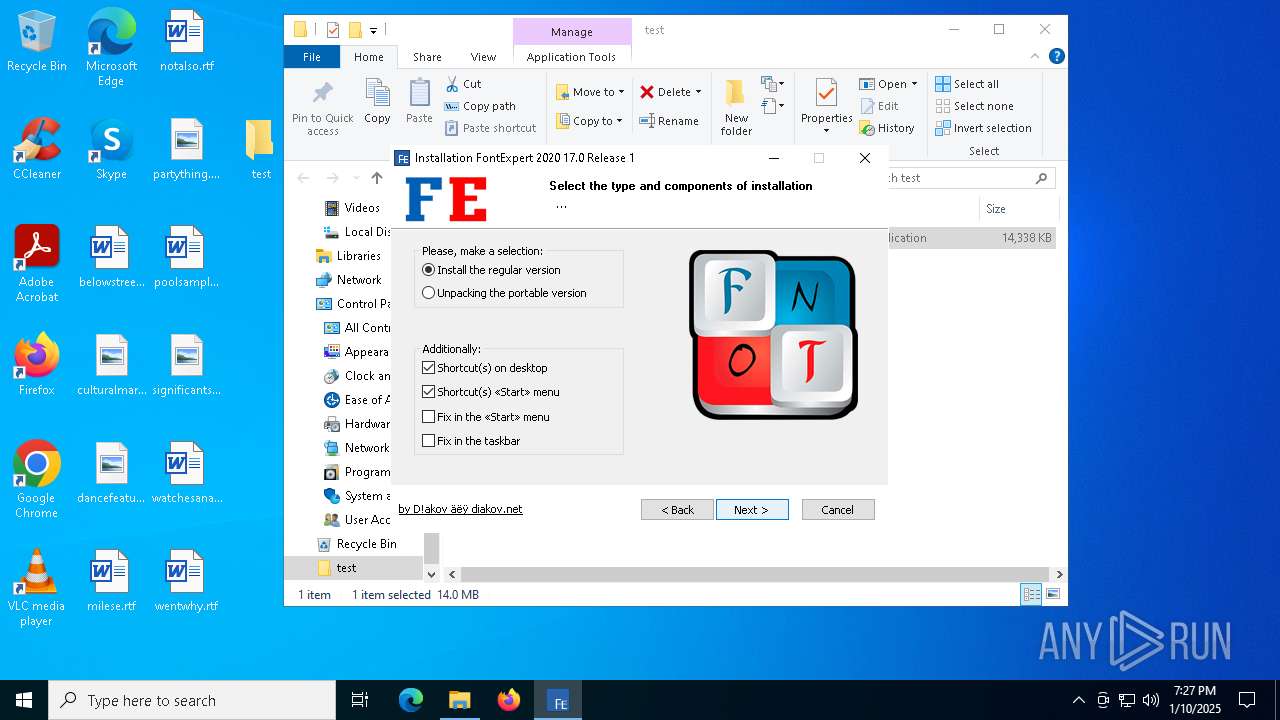
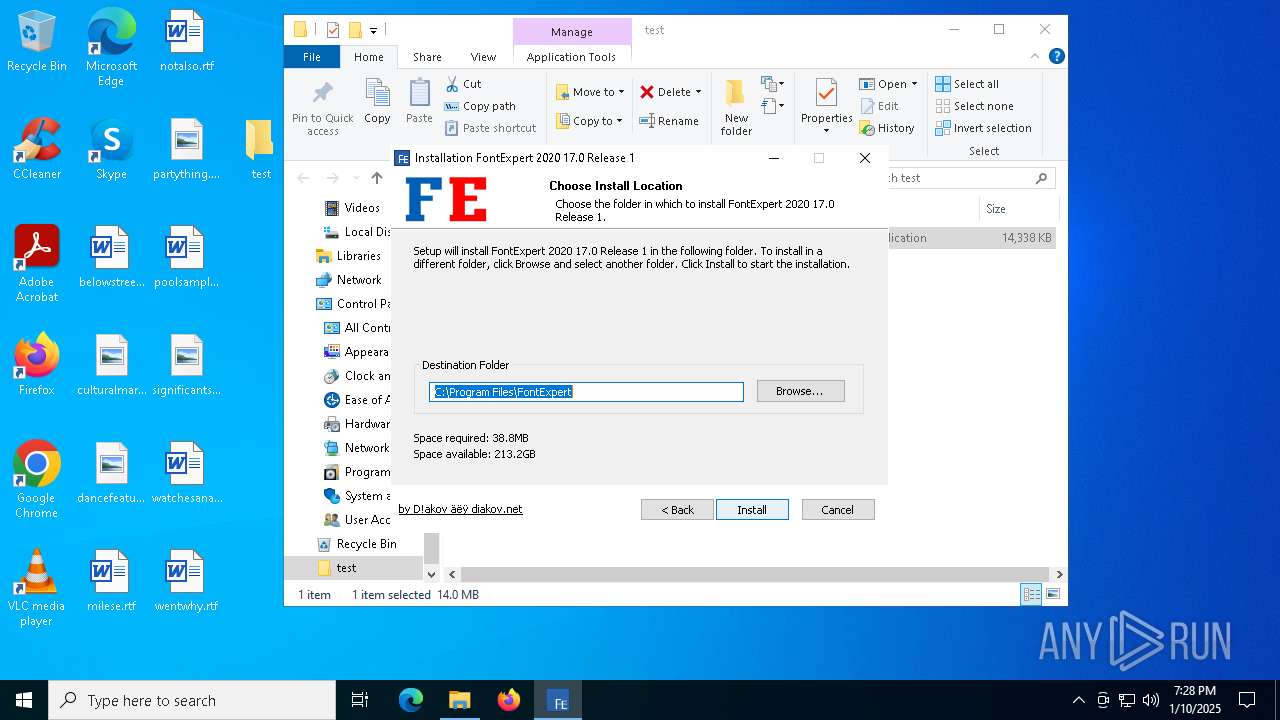
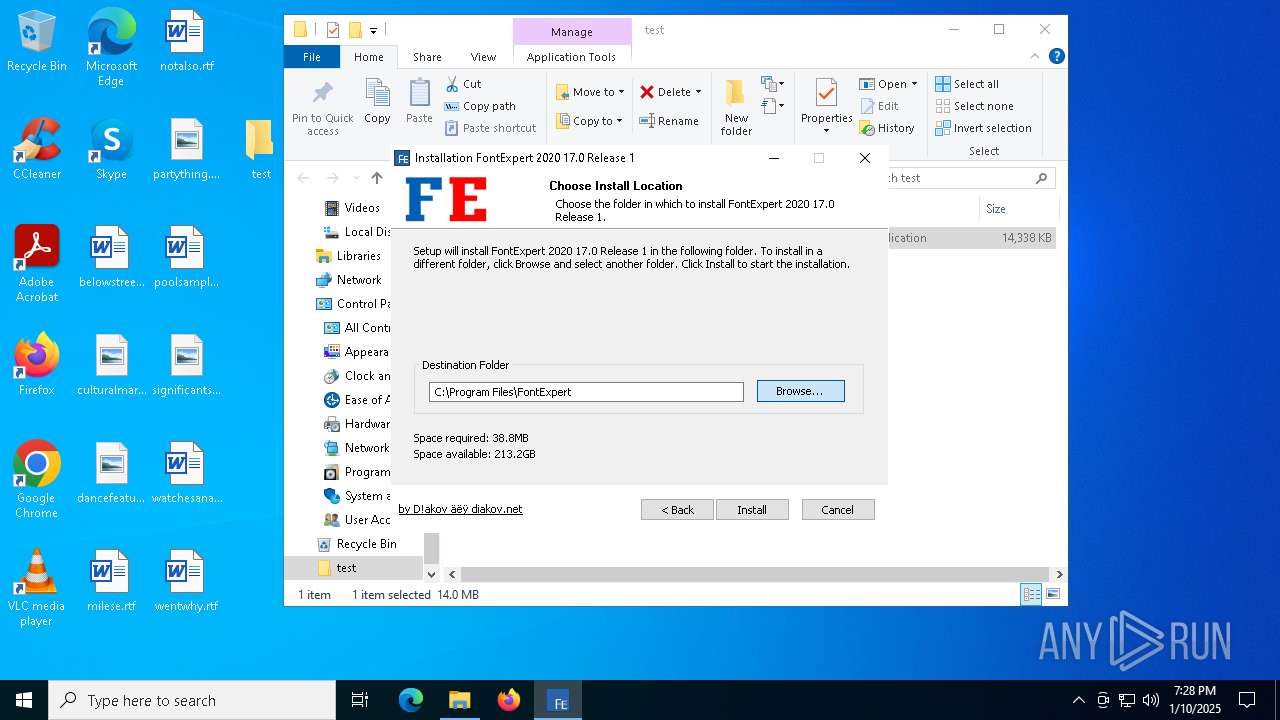
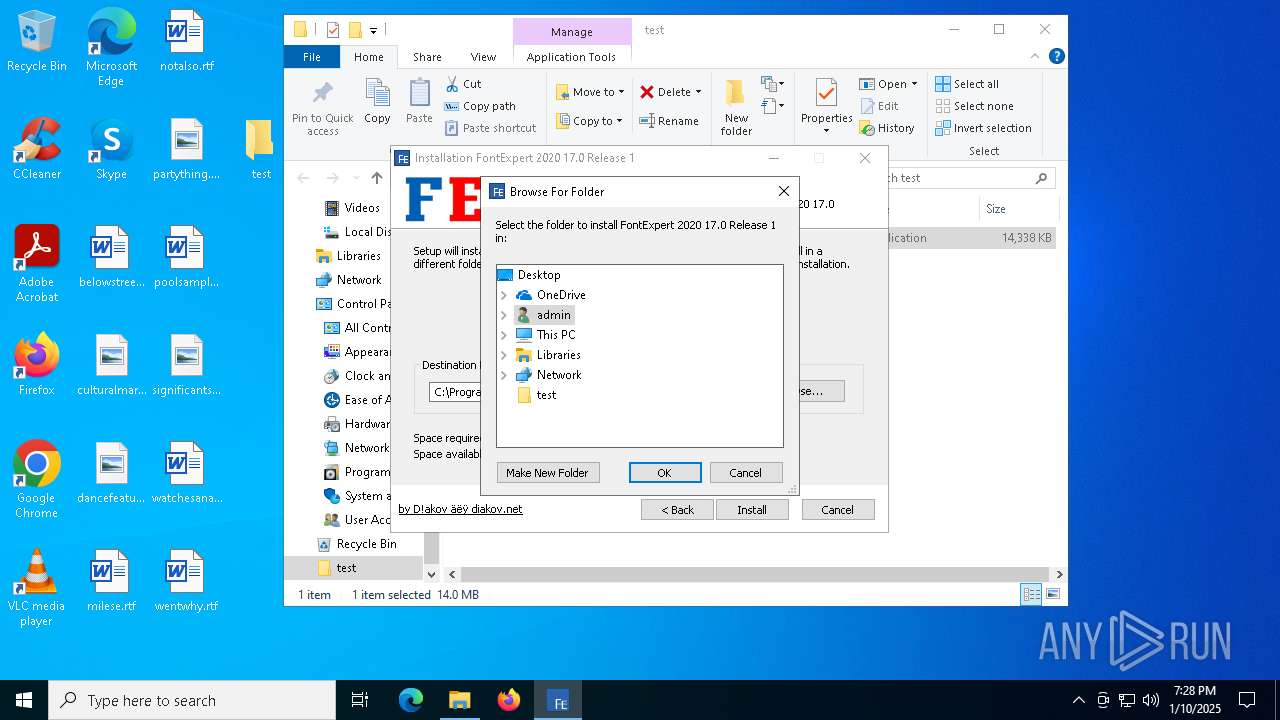
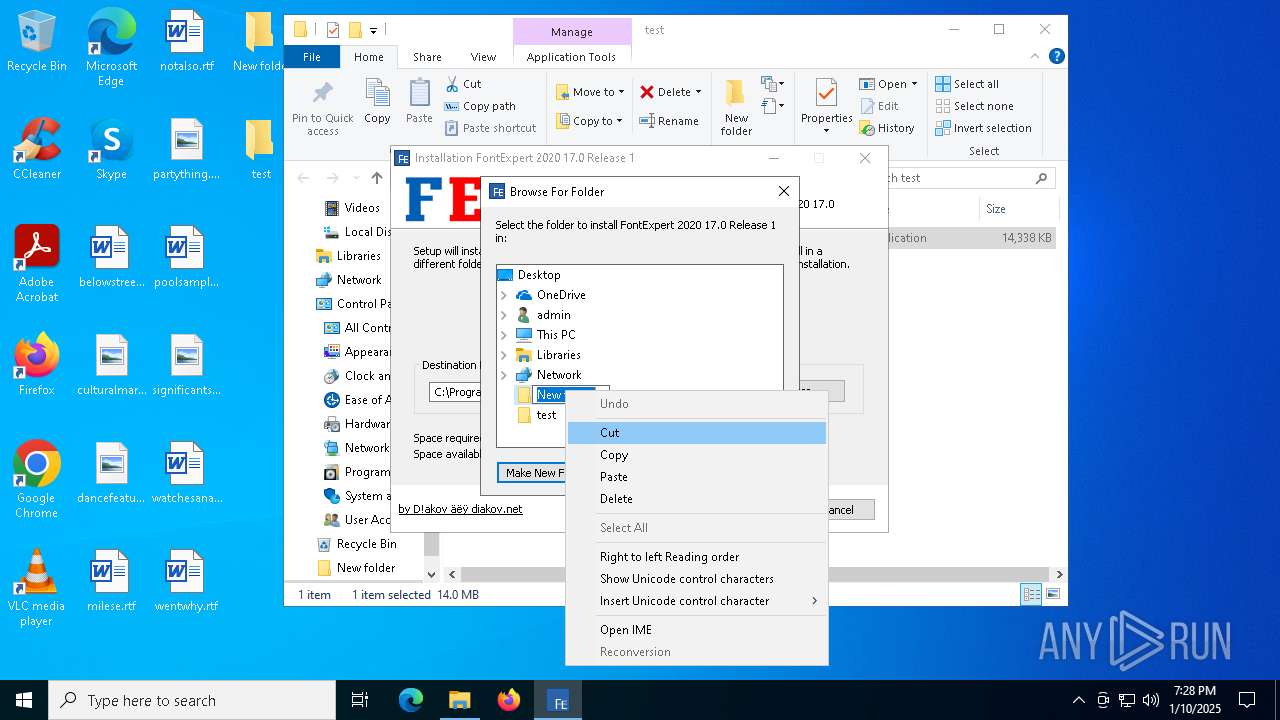
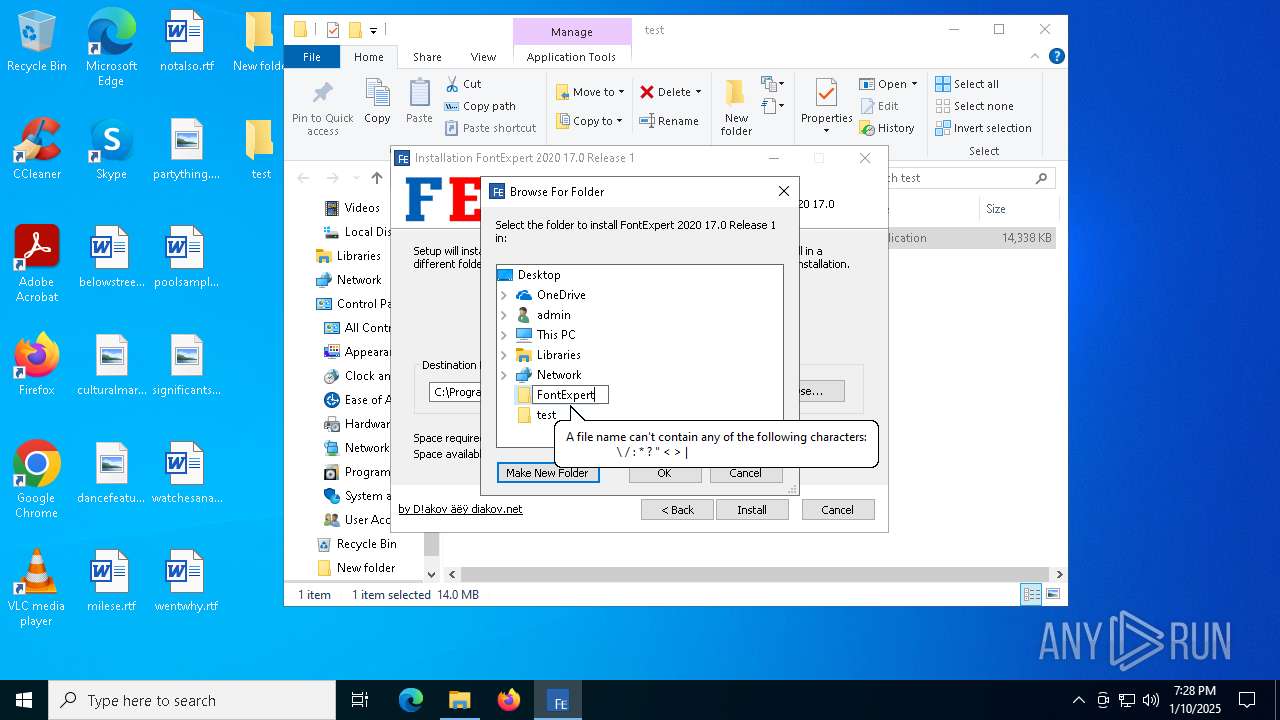
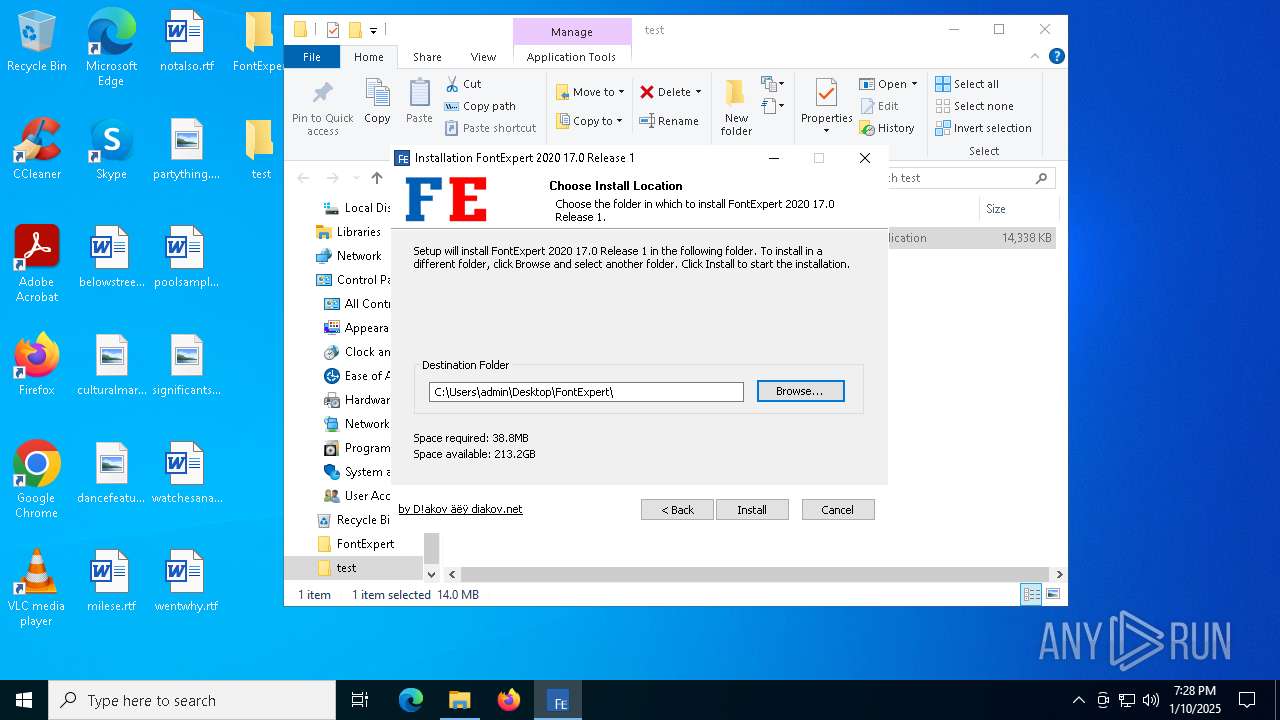
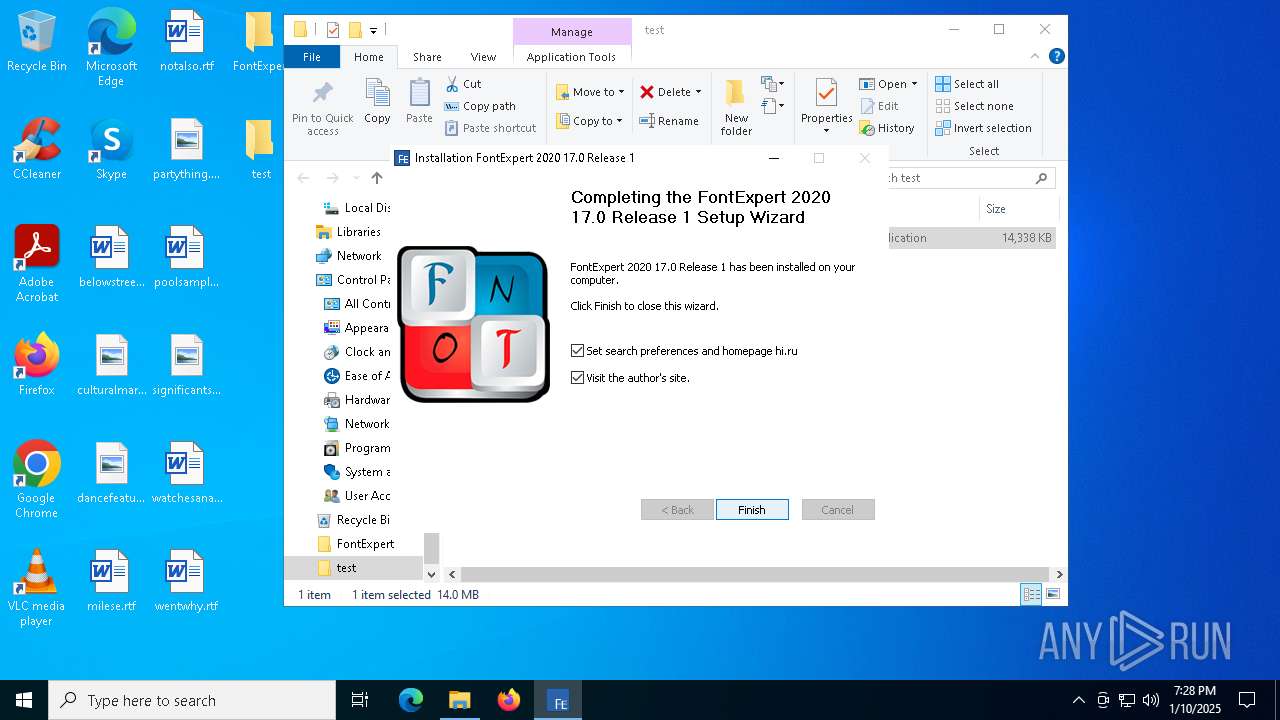
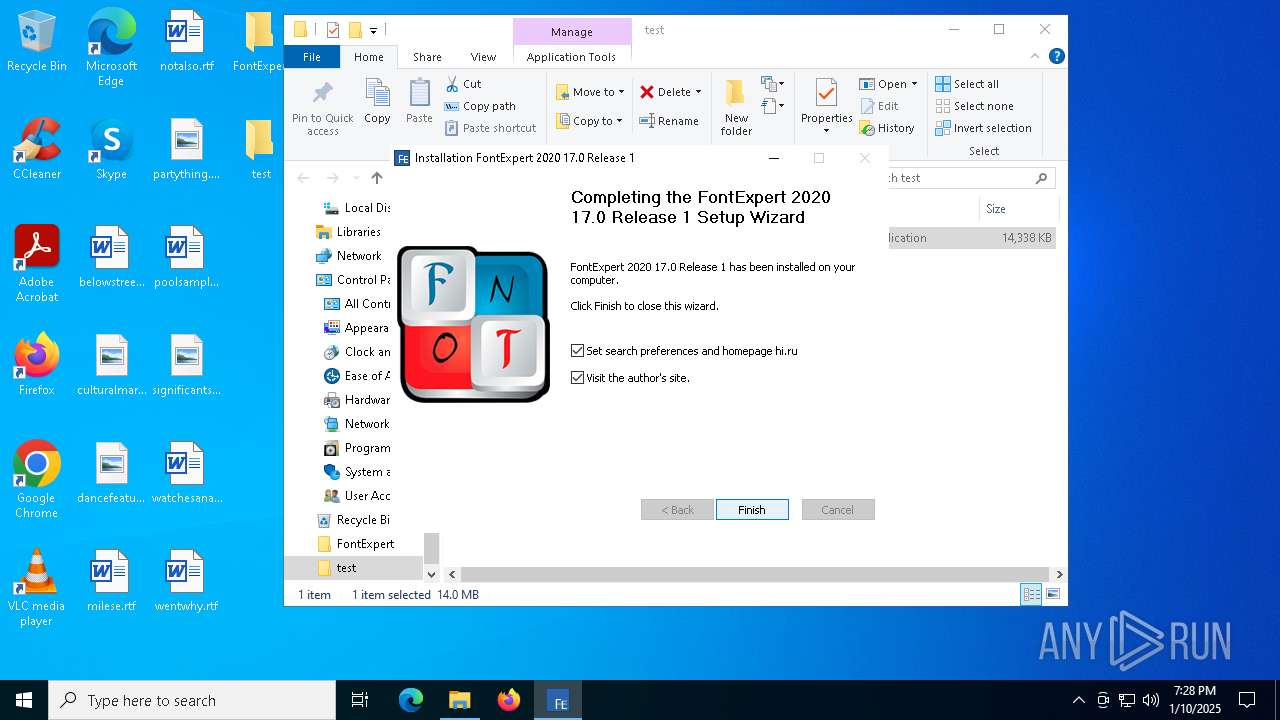
Creates a software uninstall entry
- install.exe (PID: 6244)
INFO
Reads Microsoft Office registry keys
- explorer.exe (PID: 4488)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4488)
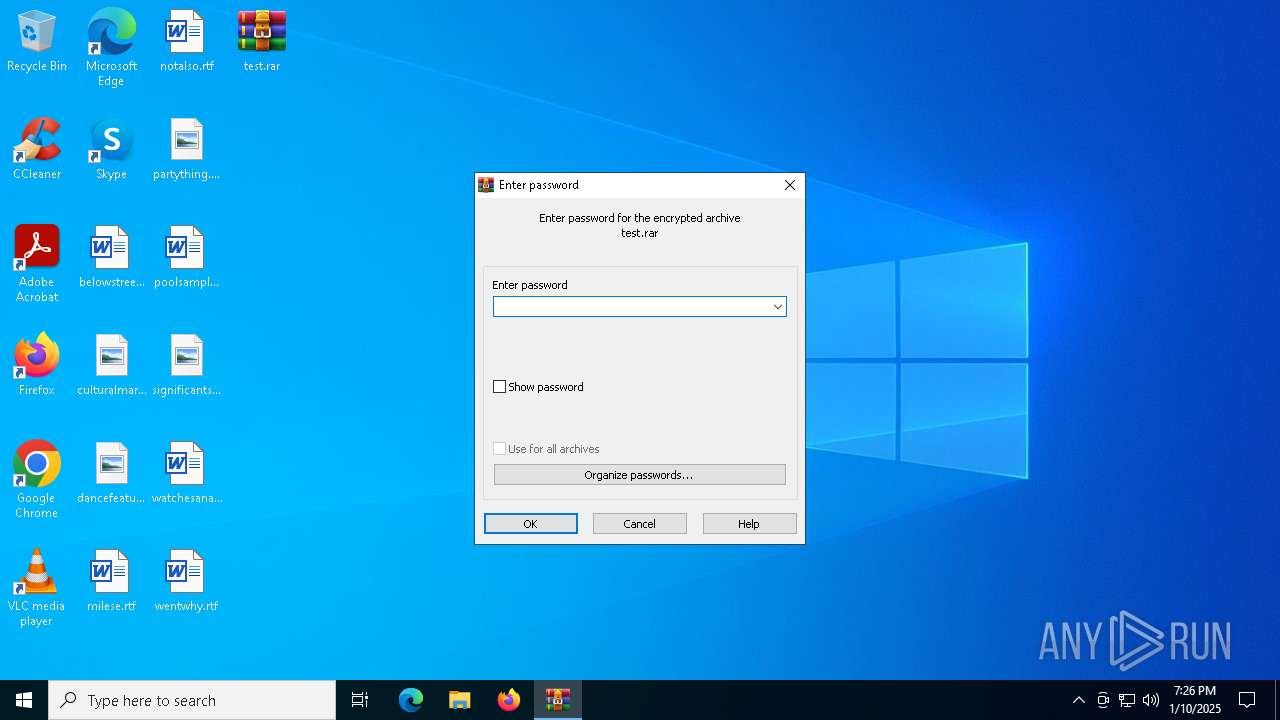
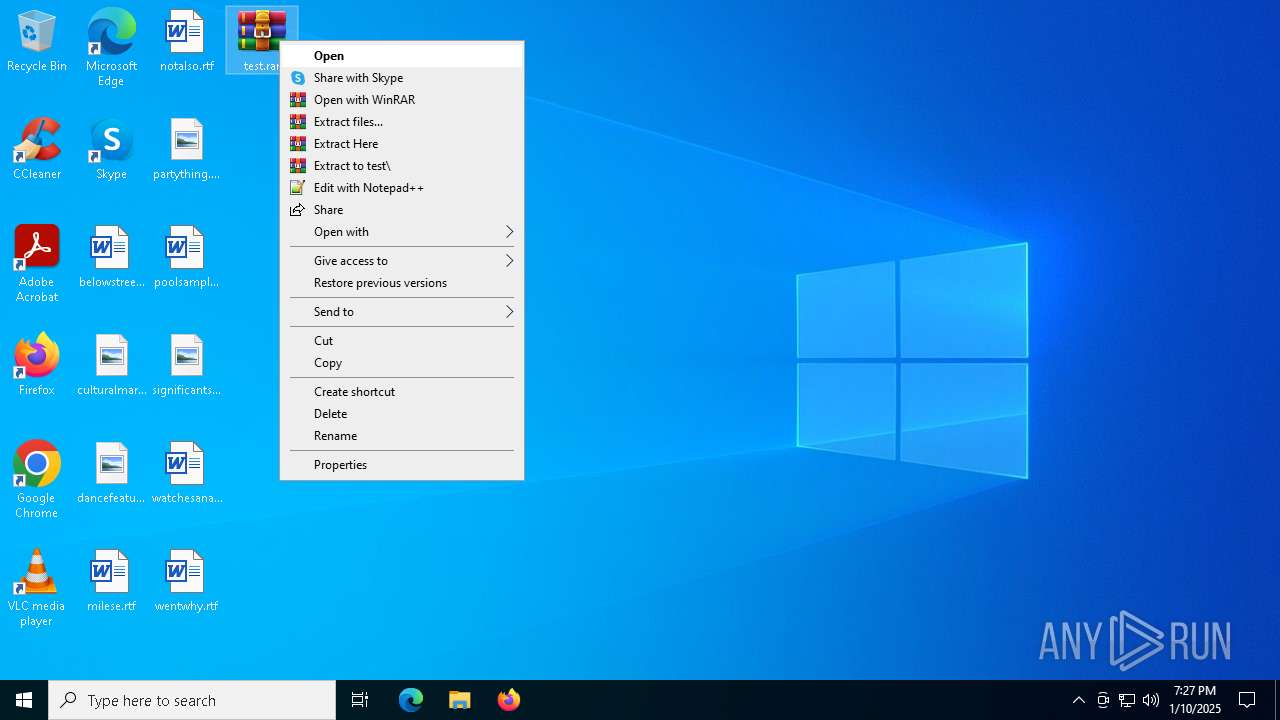
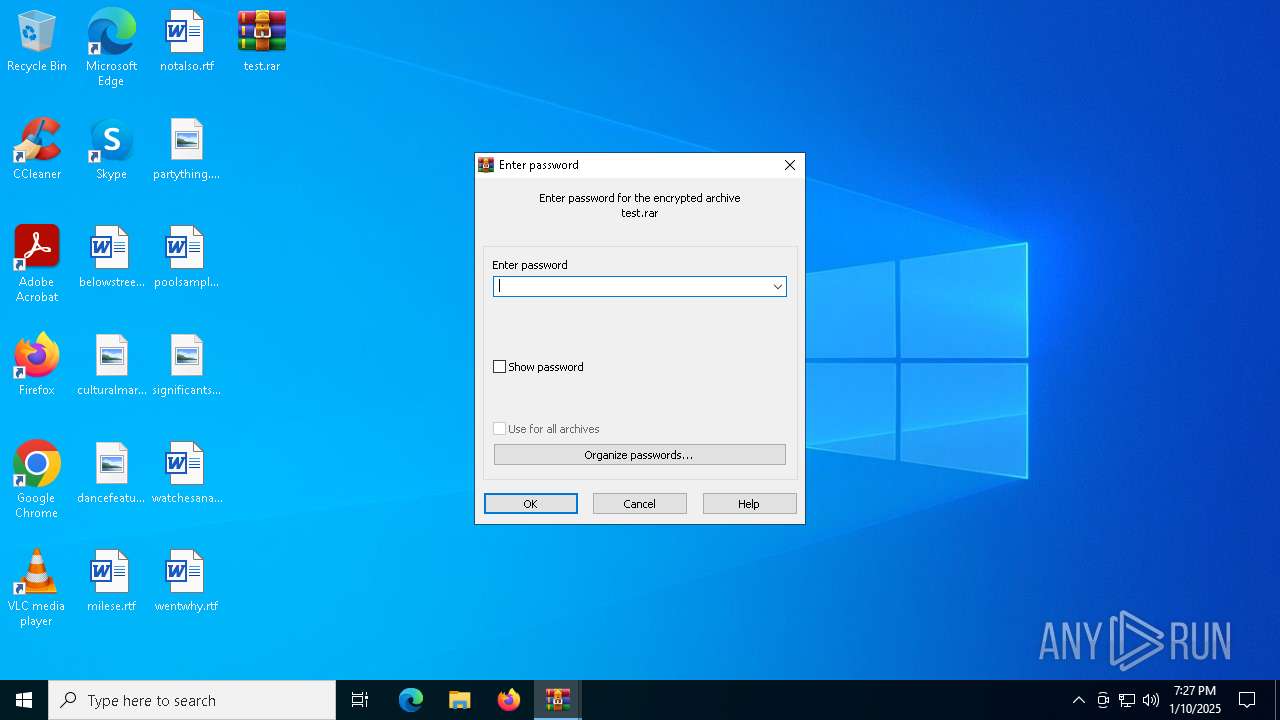
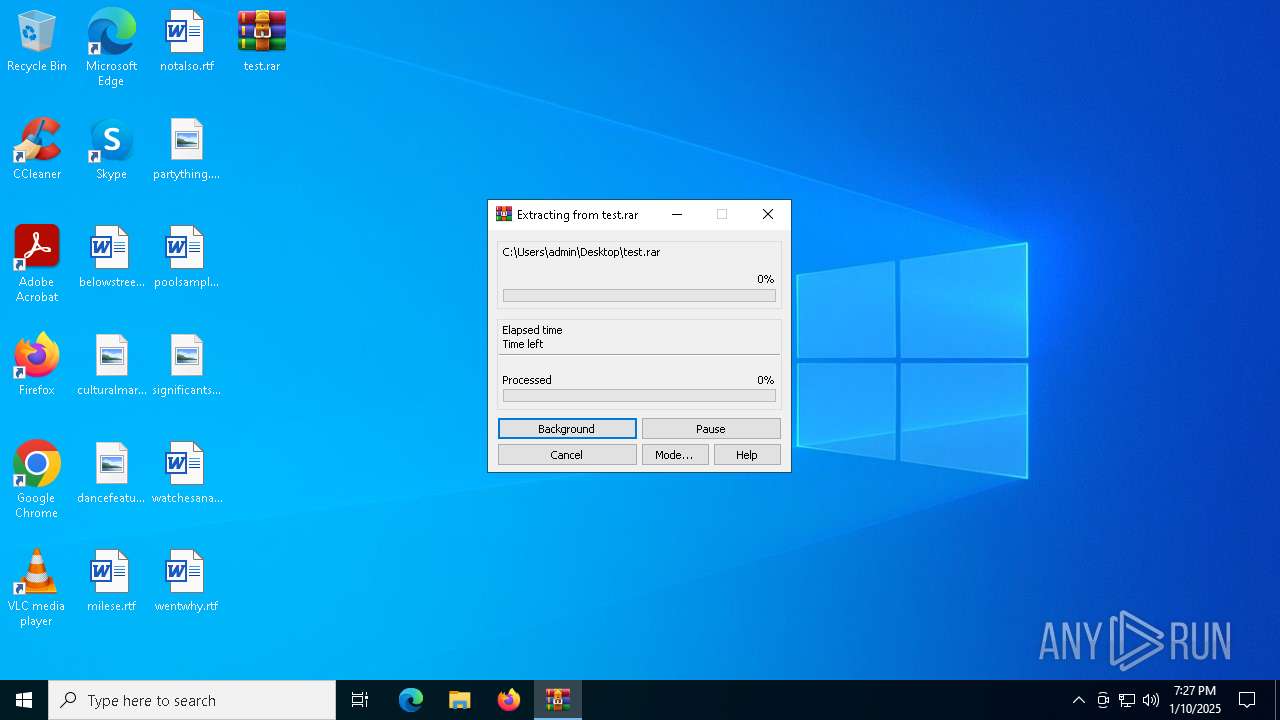
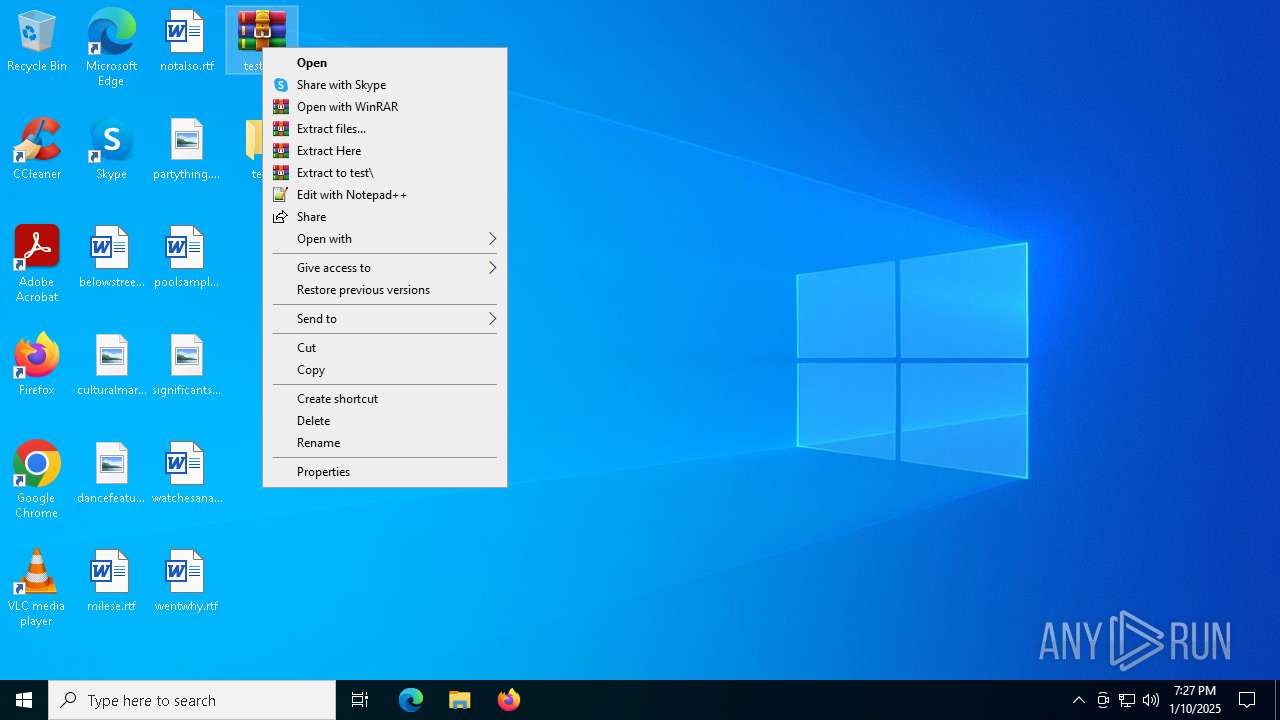
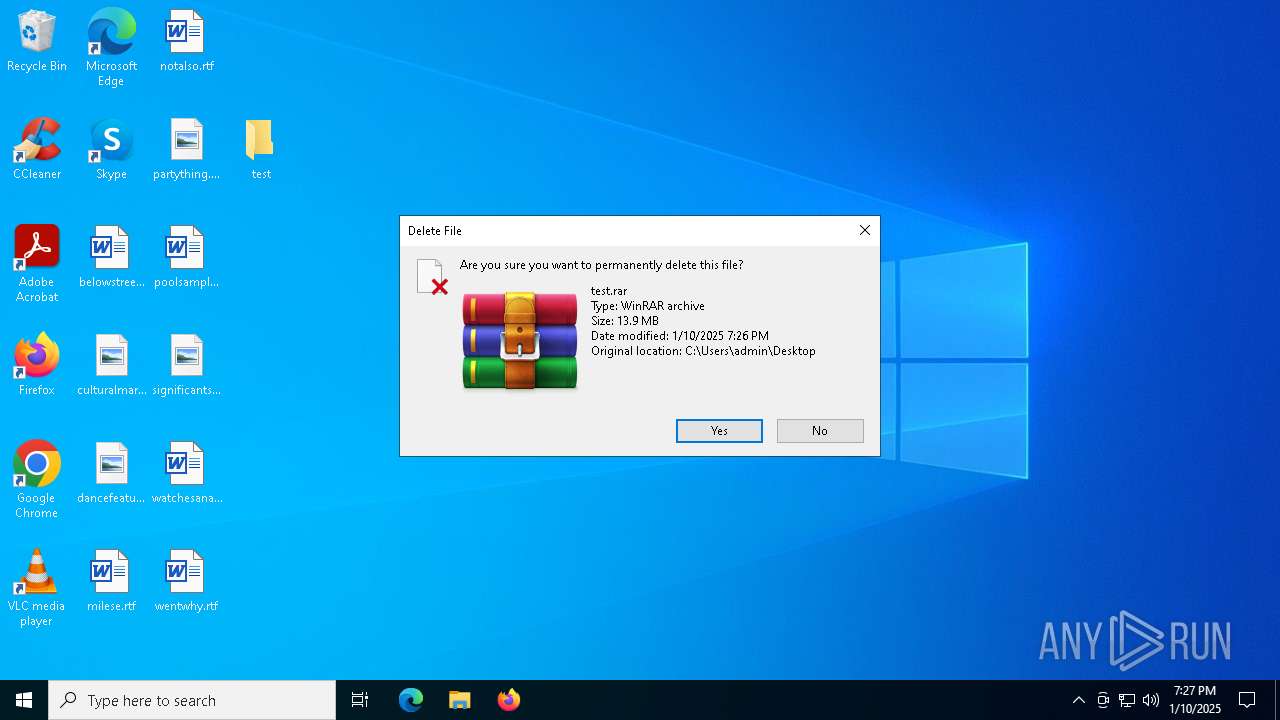
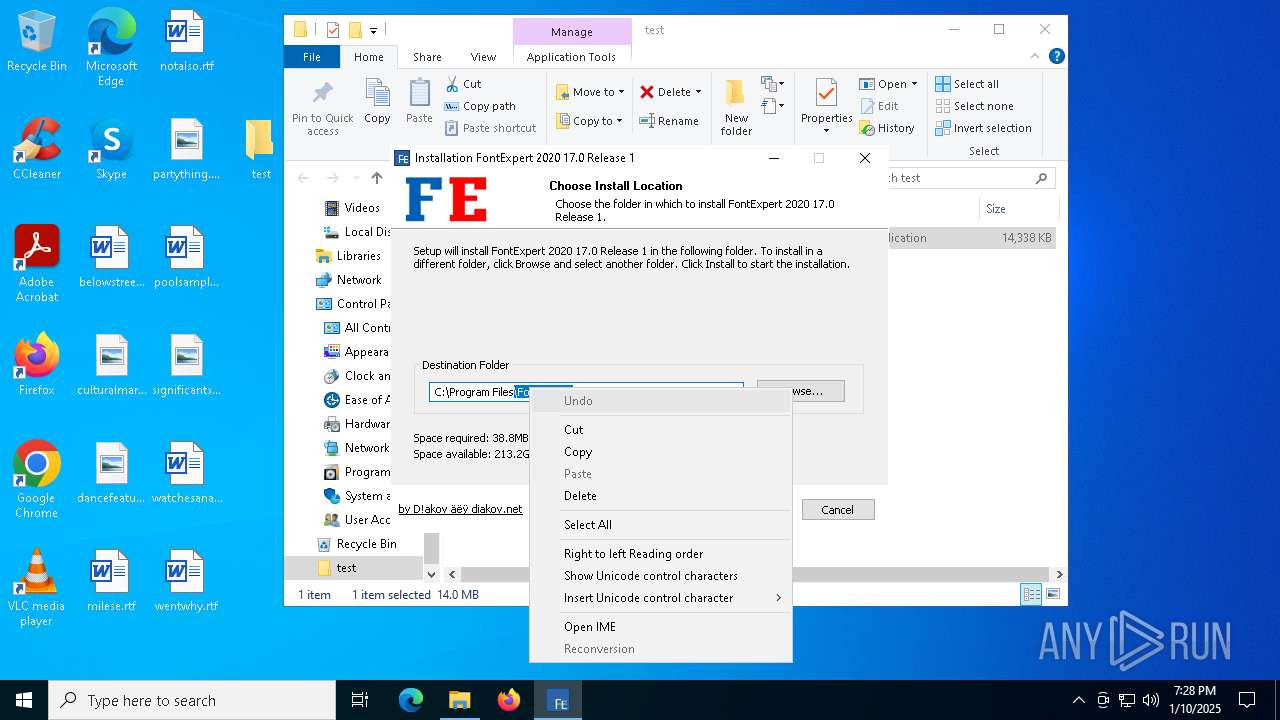
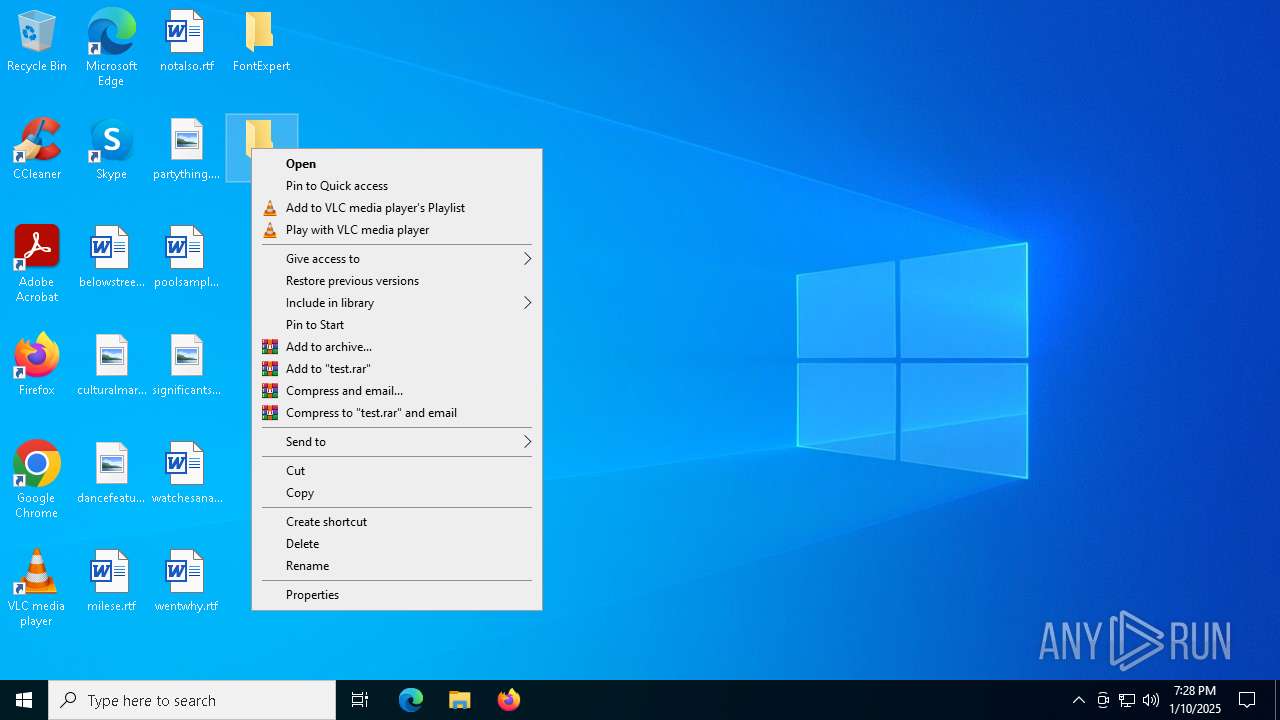
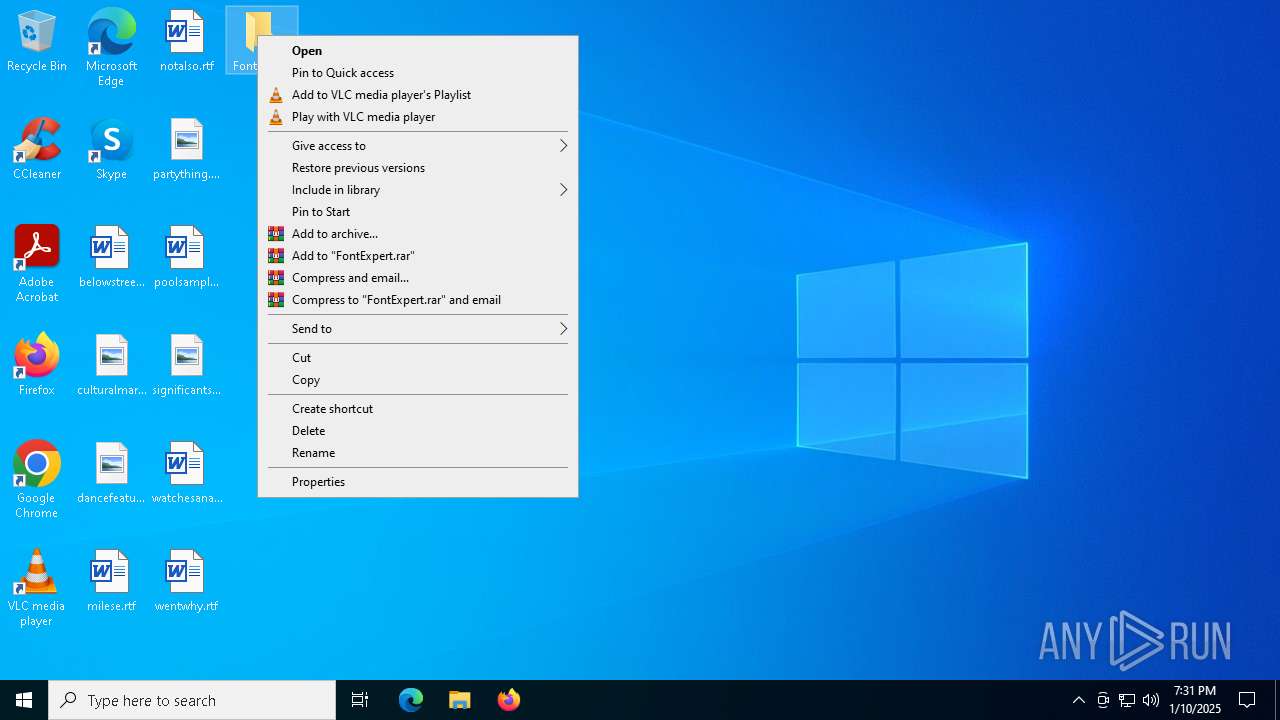
Manual execution by a user
- WinRAR.exe (PID: 6828)
- x.exe (PID: 3188)
- x.exe (PID: 4740)
- msedge.exe (PID: 6908)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6828)
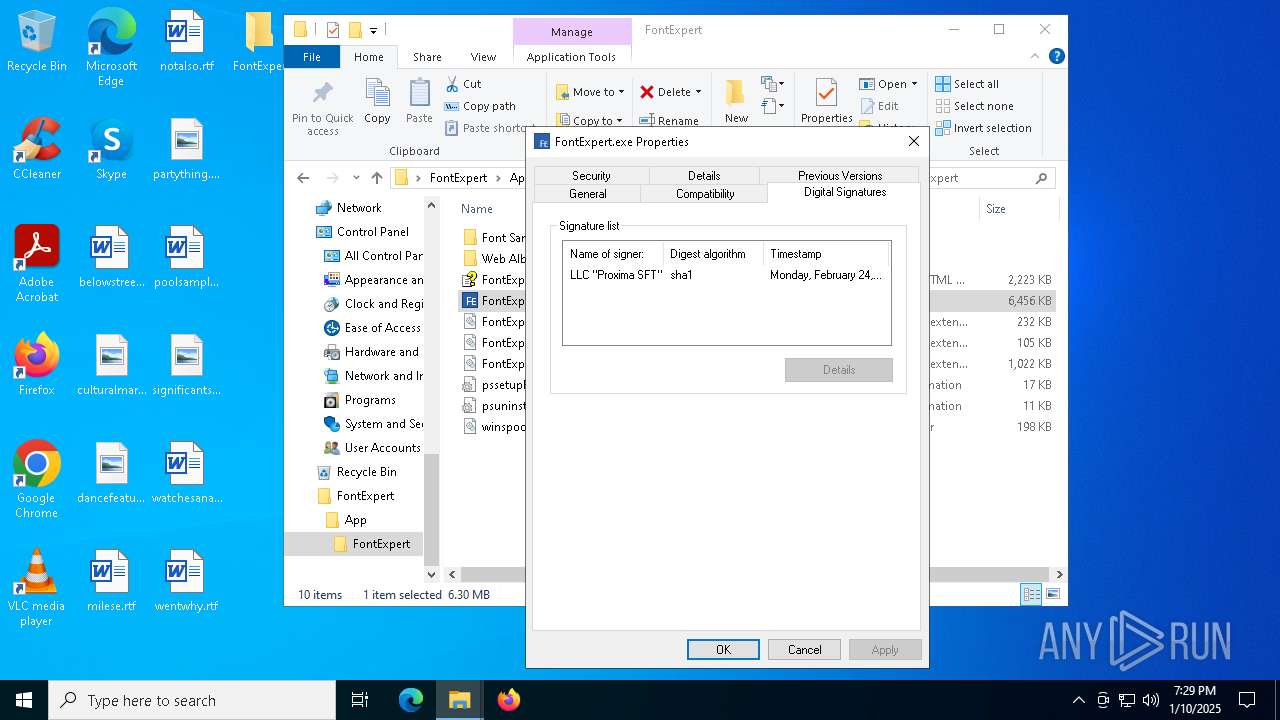
The sample compiled with russian language support
- WinRAR.exe (PID: 6828)
- x.exe (PID: 4740)
The process uses the downloaded file
- WinRAR.exe (PID: 6828)
- explorer.exe (PID: 4488)
Checks supported languages
- x.exe (PID: 4740)
- packeg.exe (PID: 2672)
- install.exe (PID: 6552)
- install.exe (PID: 6244)
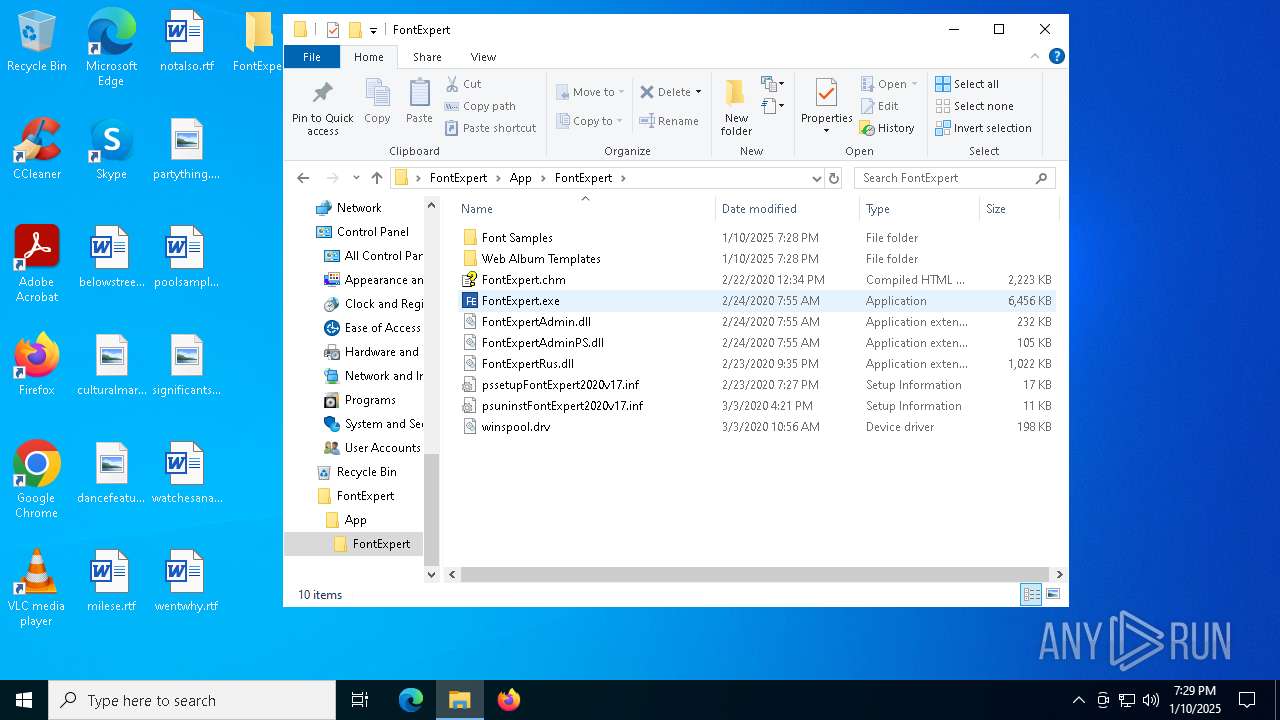
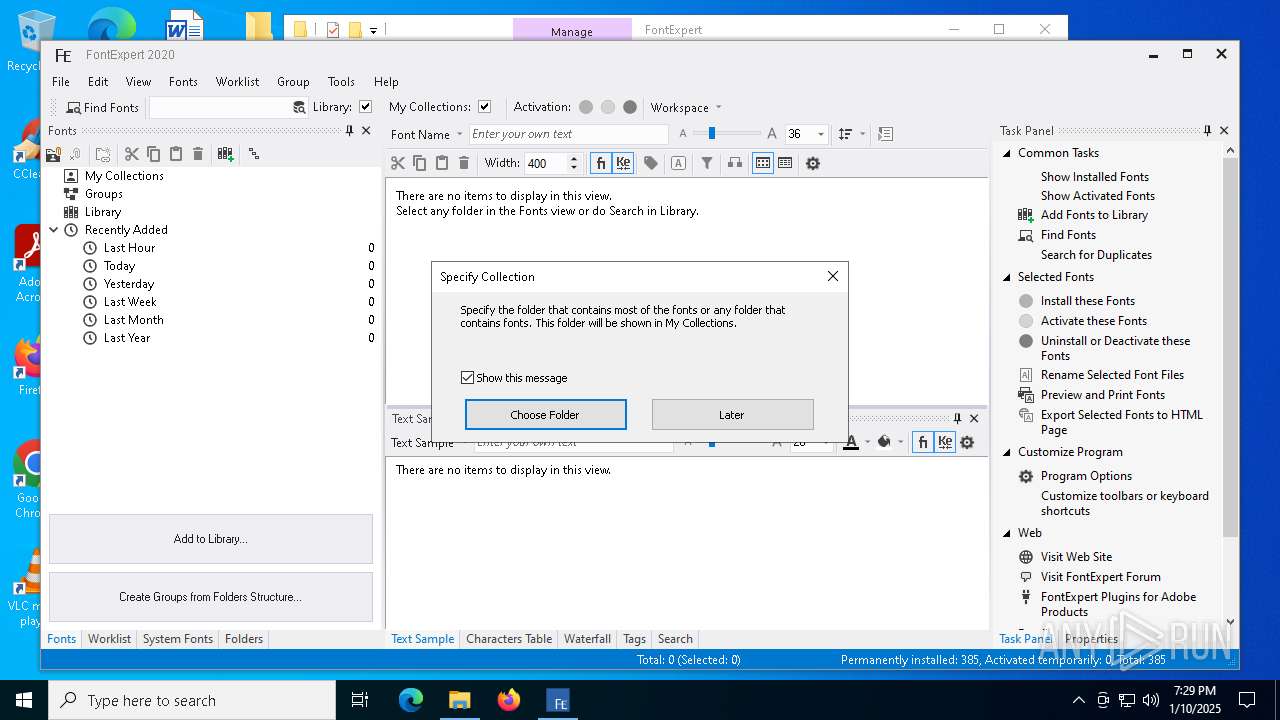
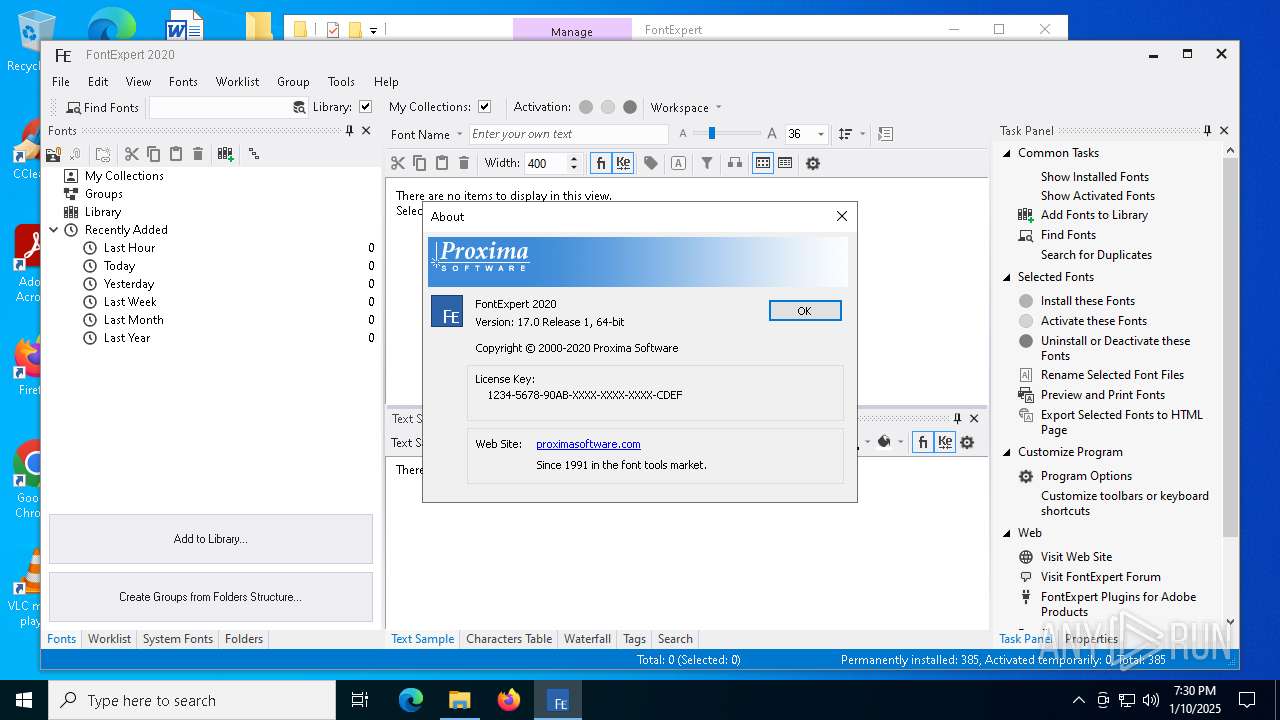
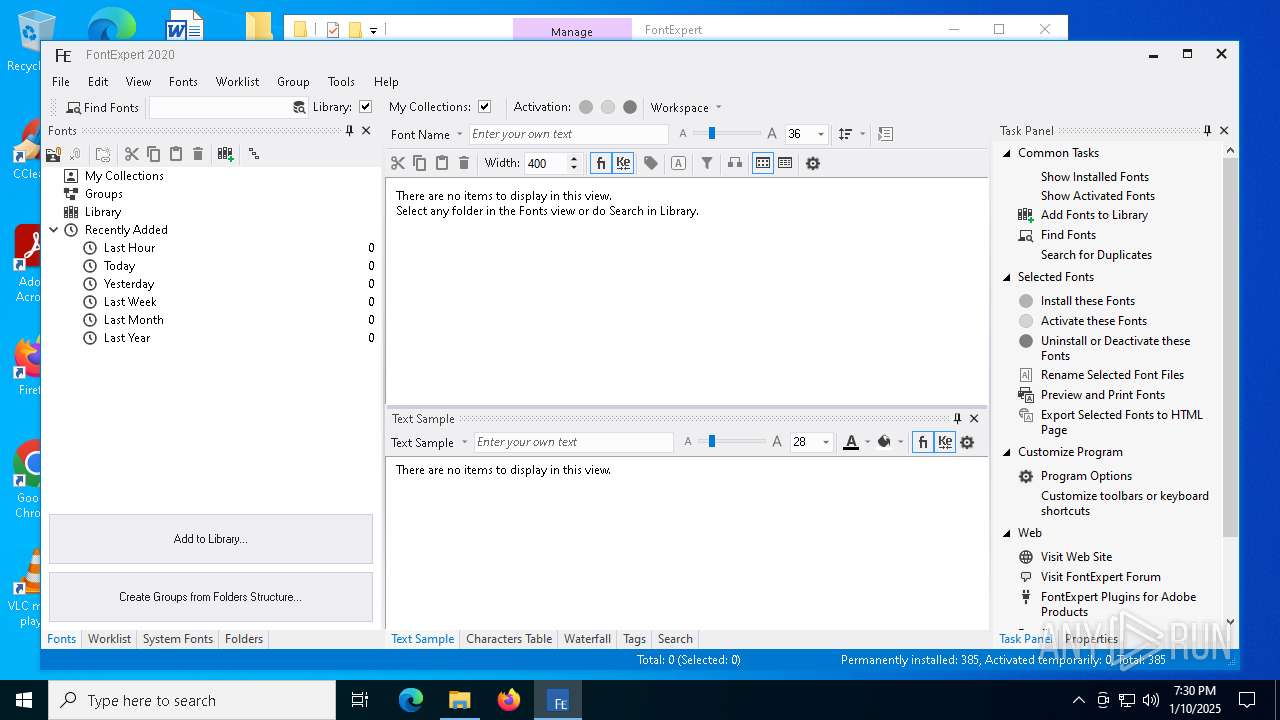
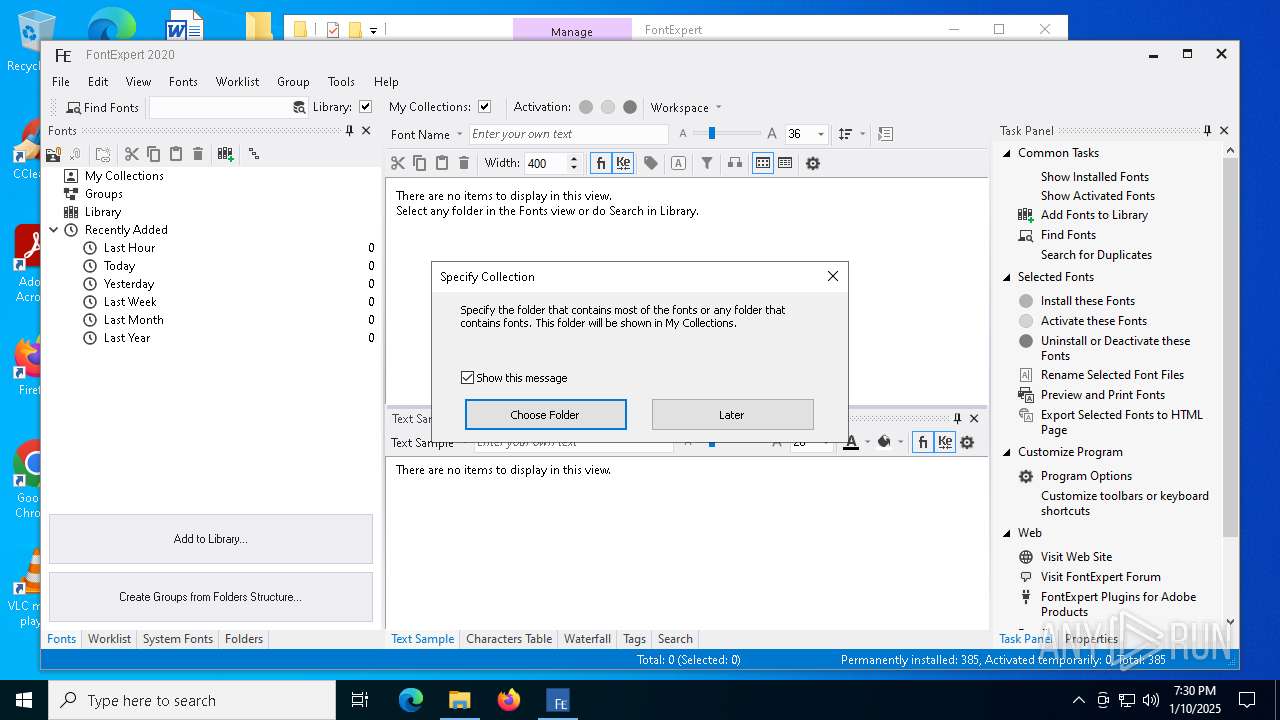
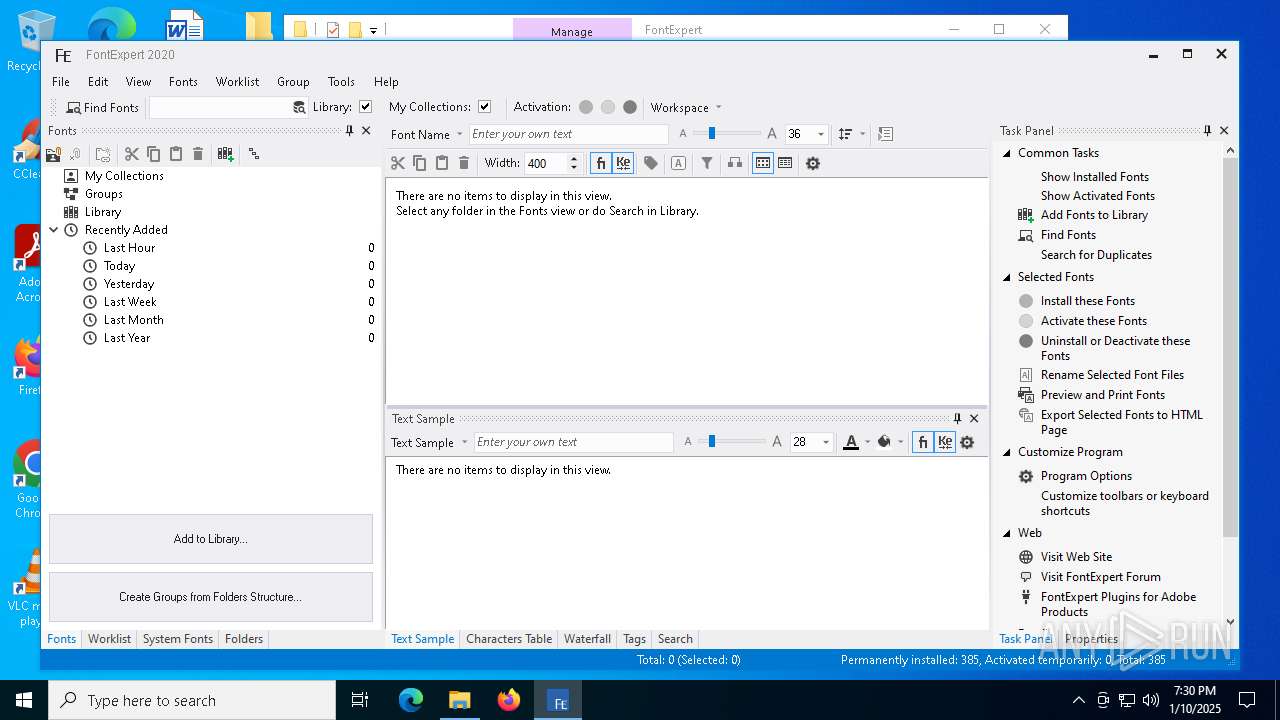
- FontExpert.exe (PID: 2076)
The sample compiled with english language support
- x.exe (PID: 4740)
UPX packer has been detected
- x.exe (PID: 4740)
Create files in a temporary directory
- x.exe (PID: 4740)
- packeg.exe (PID: 2672)
- install.exe (PID: 6552)
- install.exe (PID: 6244)
Reads the computer name
- packeg.exe (PID: 2672)
- FontExpert.exe (PID: 7028)
Checks proxy server information
- explorer.exe (PID: 4488)
Creates files in the program directory
- install.exe (PID: 6244)
Application launched itself
- msedge.exe (PID: 3092)
- msedge.exe (PID: 6908)
- msedge.exe (PID: 5208)
Creates files or folders in the user directory
- explorer.exe (PID: 4488)
VMProtect protector has been detected
- FontExpert.exe (PID: 7028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|
Total processes
199
Monitored processes
66
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --mojo-platform-channel-handle=6308 --field-trial-handle=2360,i,11867600637398239682,12832558400578098409,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 936 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1140 --field-trial-handle=2328,i,6055499467219094106,6845478790307434975,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1016 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5236 --field-trial-handle=2328,i,6055499467219094106,6845478790307434975,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3356 --field-trial-handle=2328,i,6055499467219094106,6845478790307434975,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1544 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2596 --field-trial-handle=2360,i,11867600637398239682,12832558400578098409,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1580 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4100 --field-trial-handle=2360,i,11867600637398239682,12832558400578098409,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2008 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5220 --field-trial-handle=2328,i,6055499467219094106,6845478790307434975,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
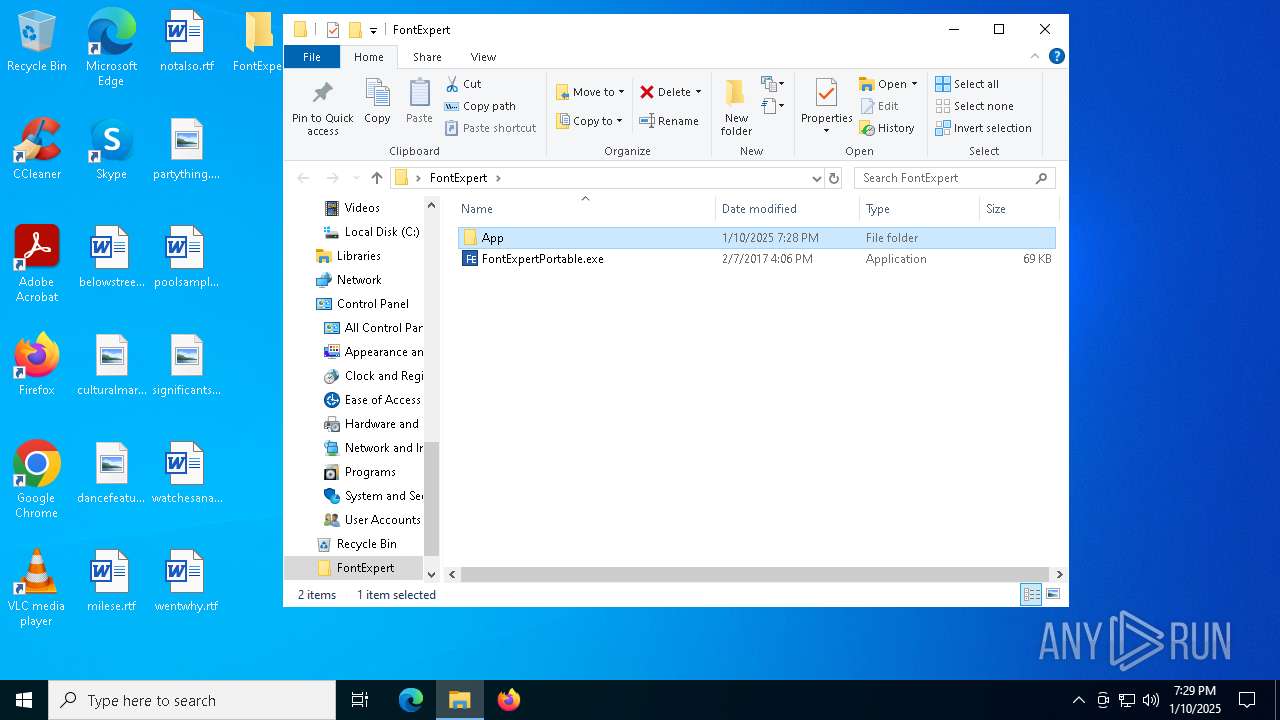
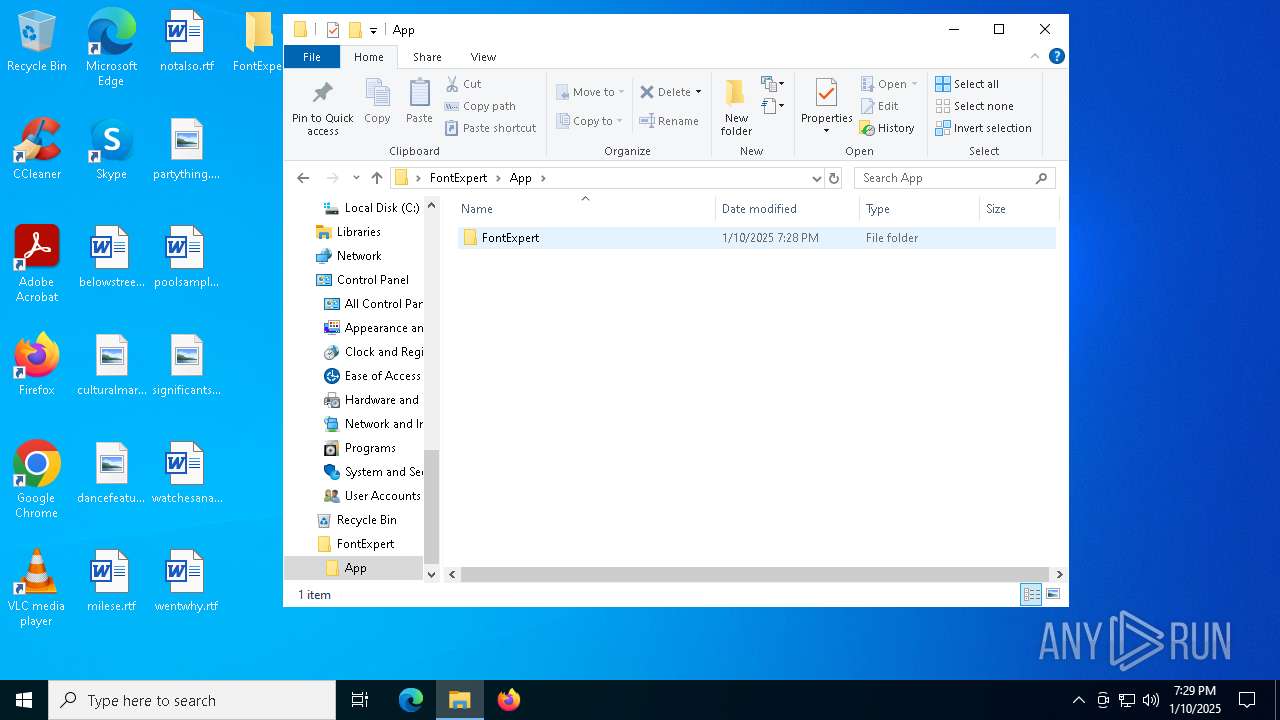
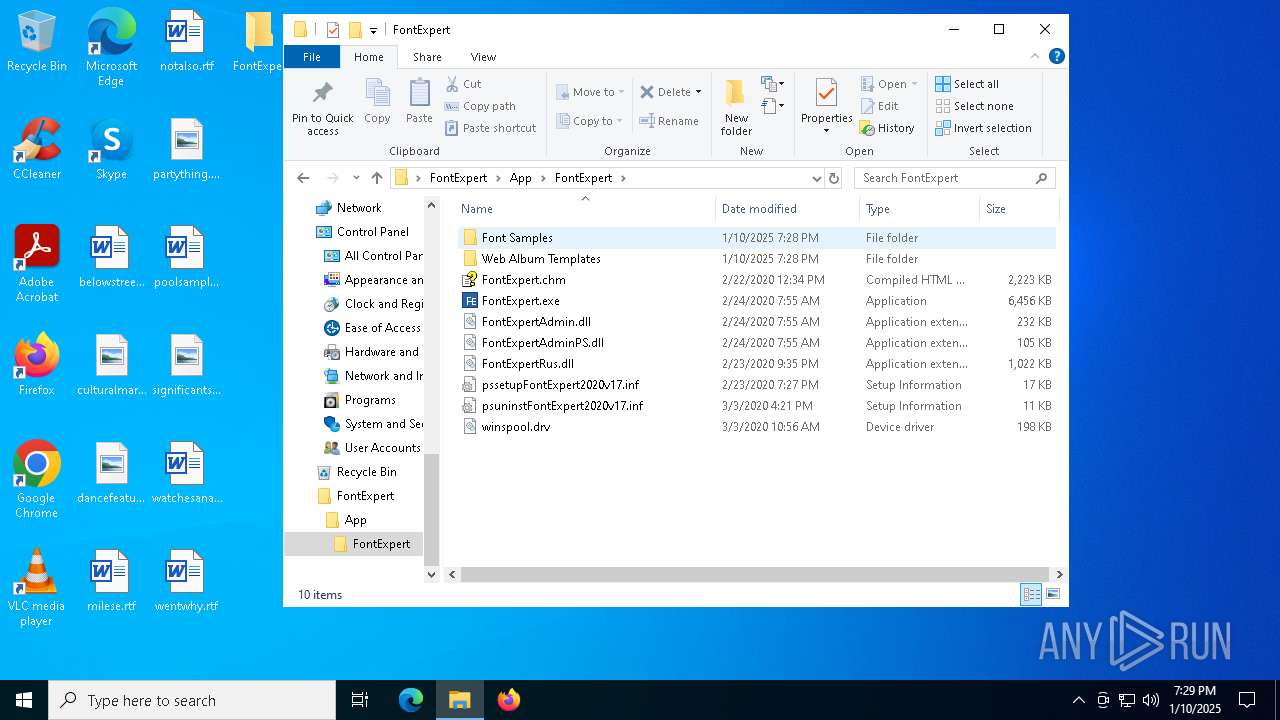
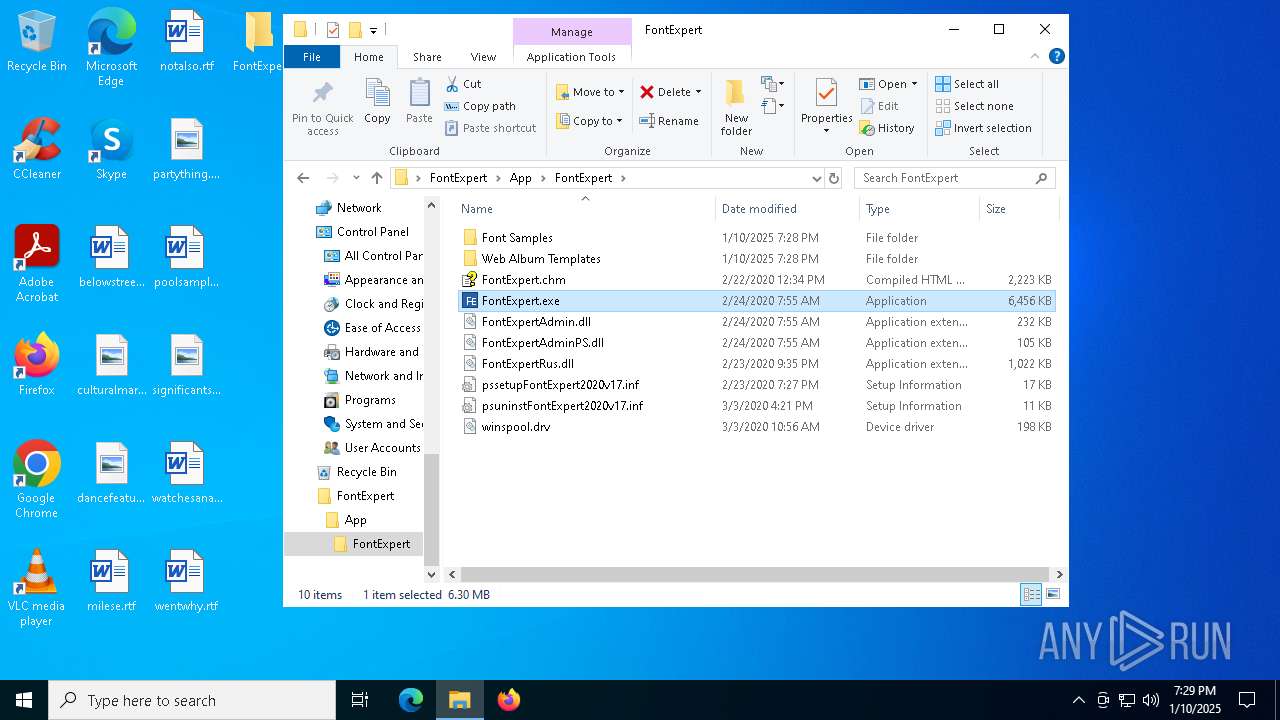
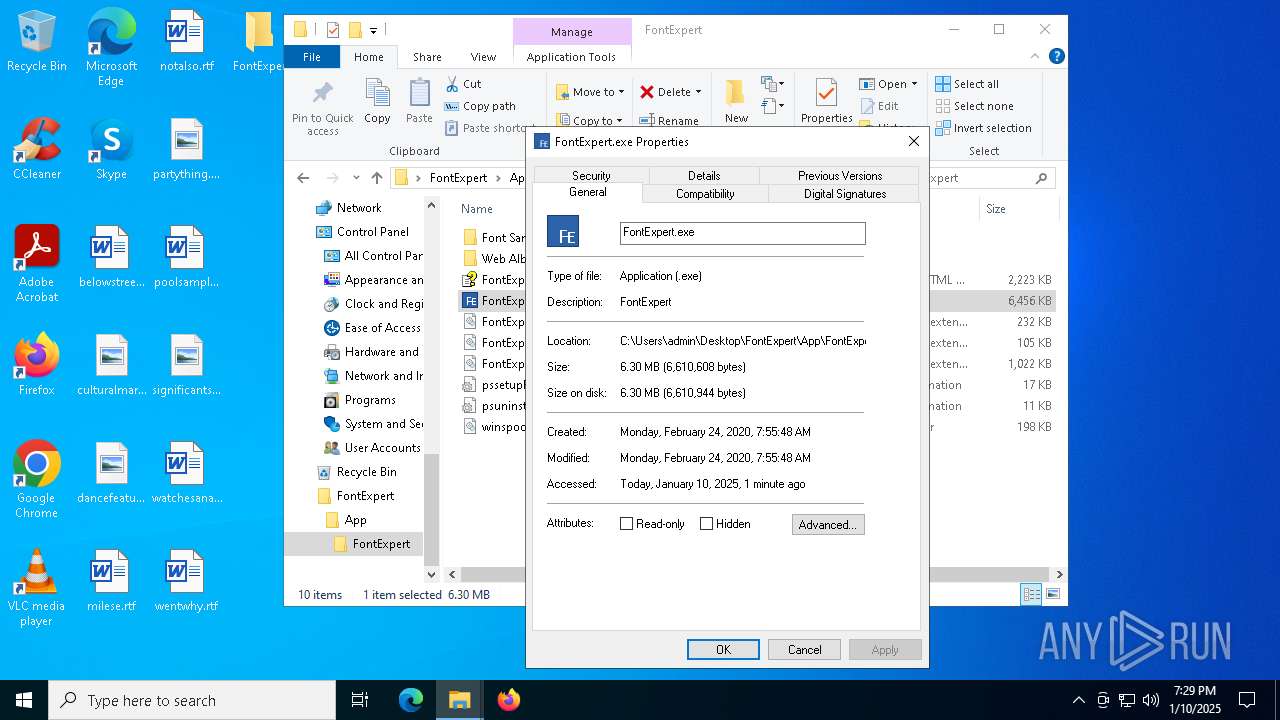
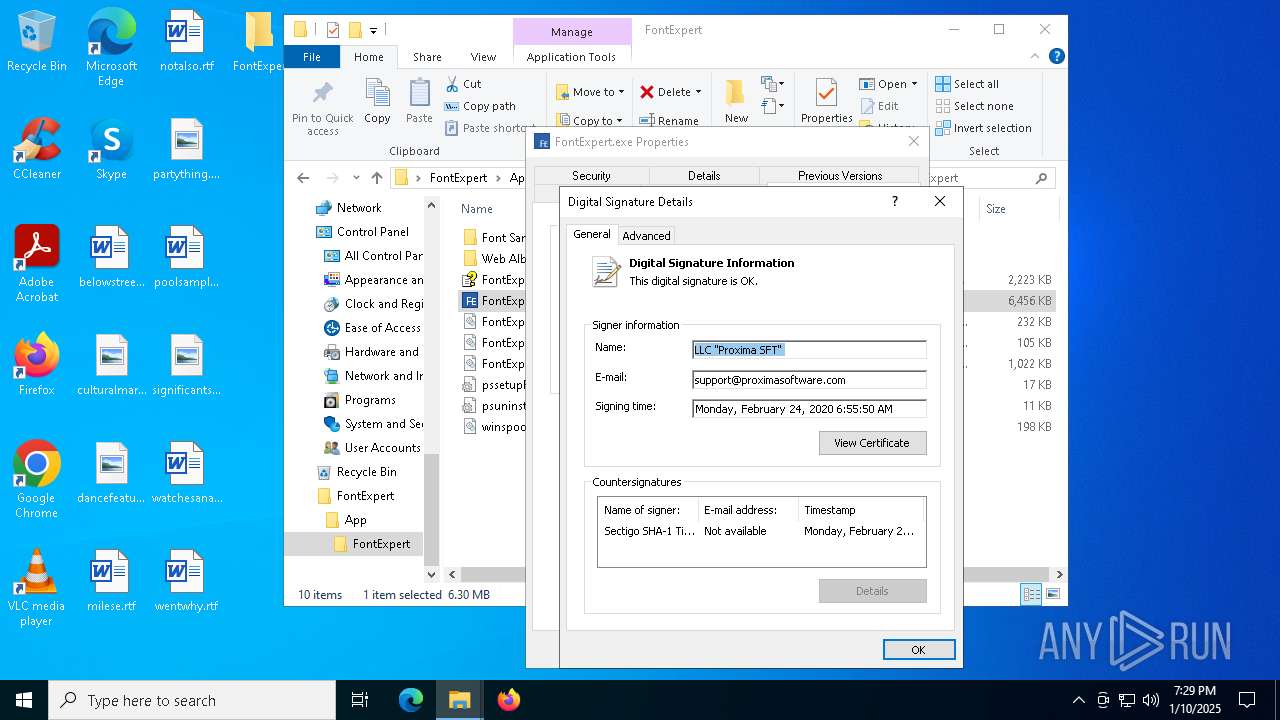
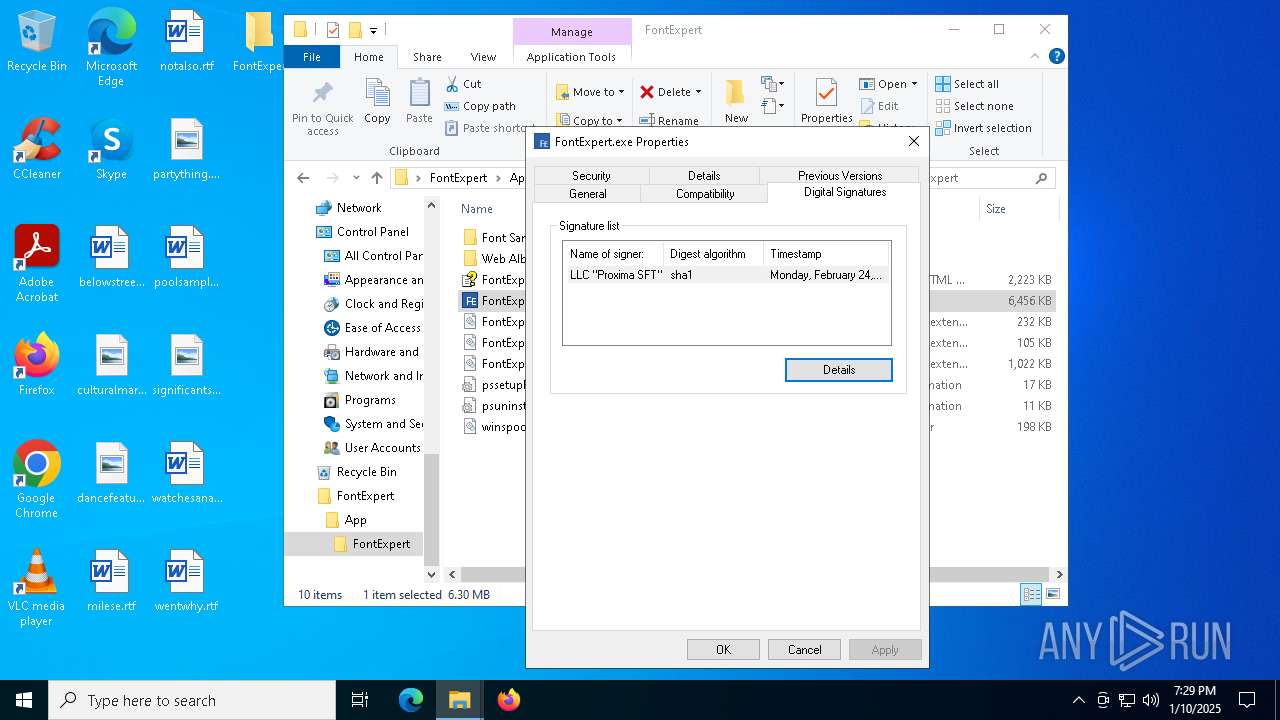
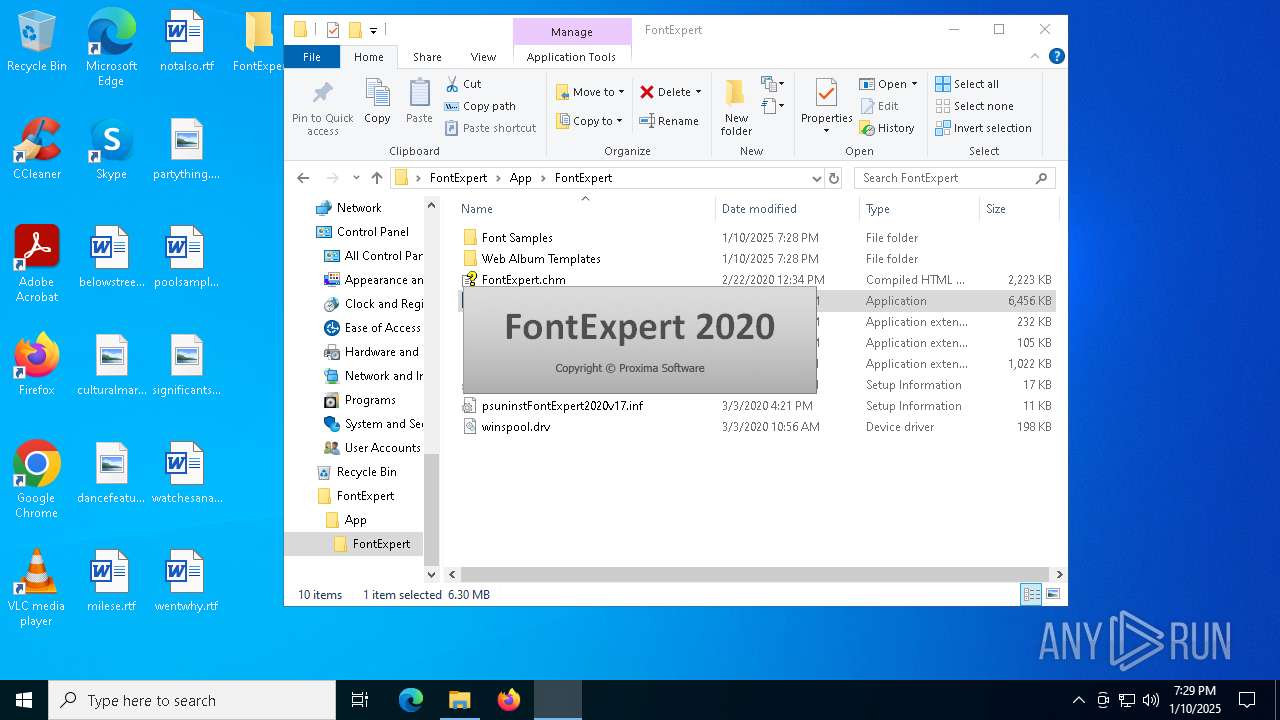
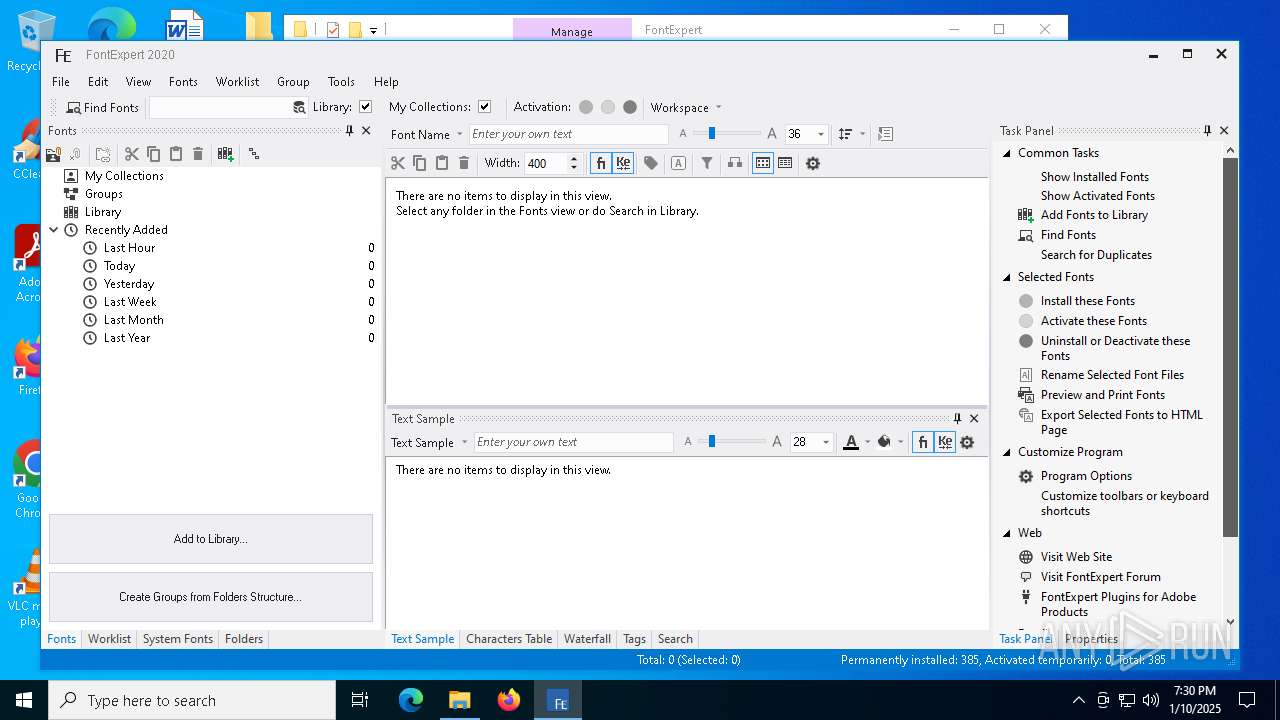
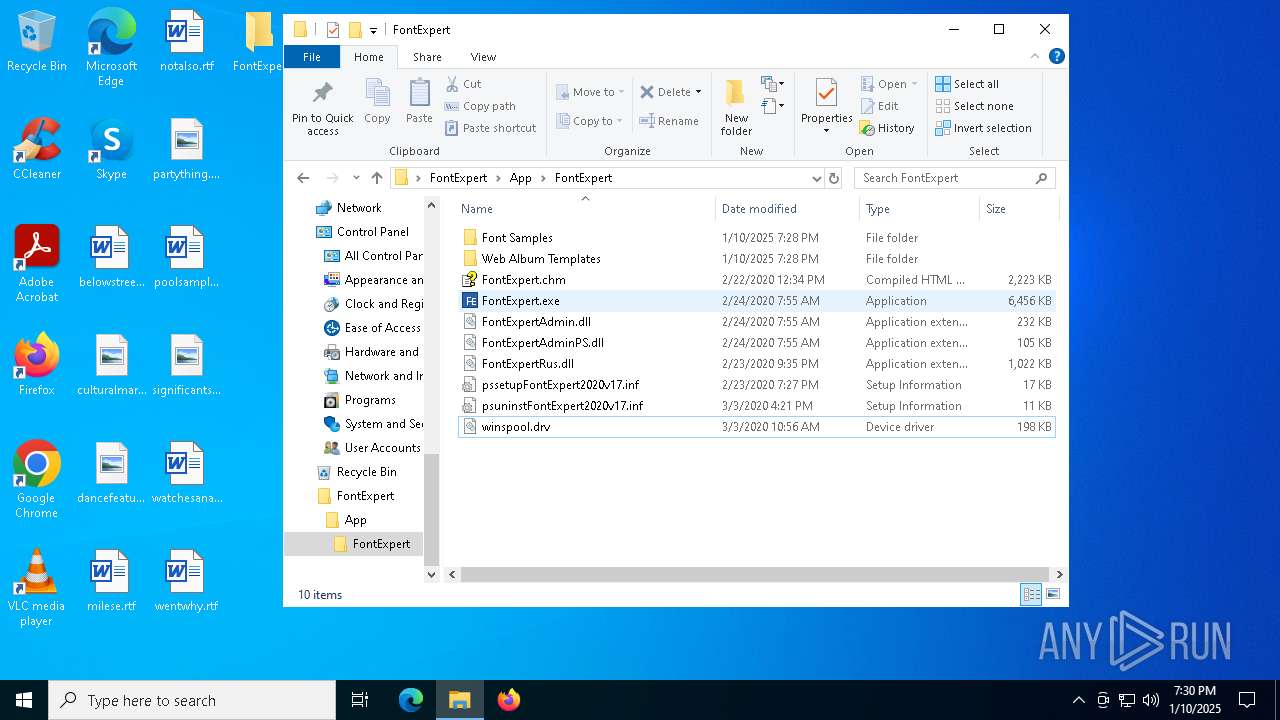
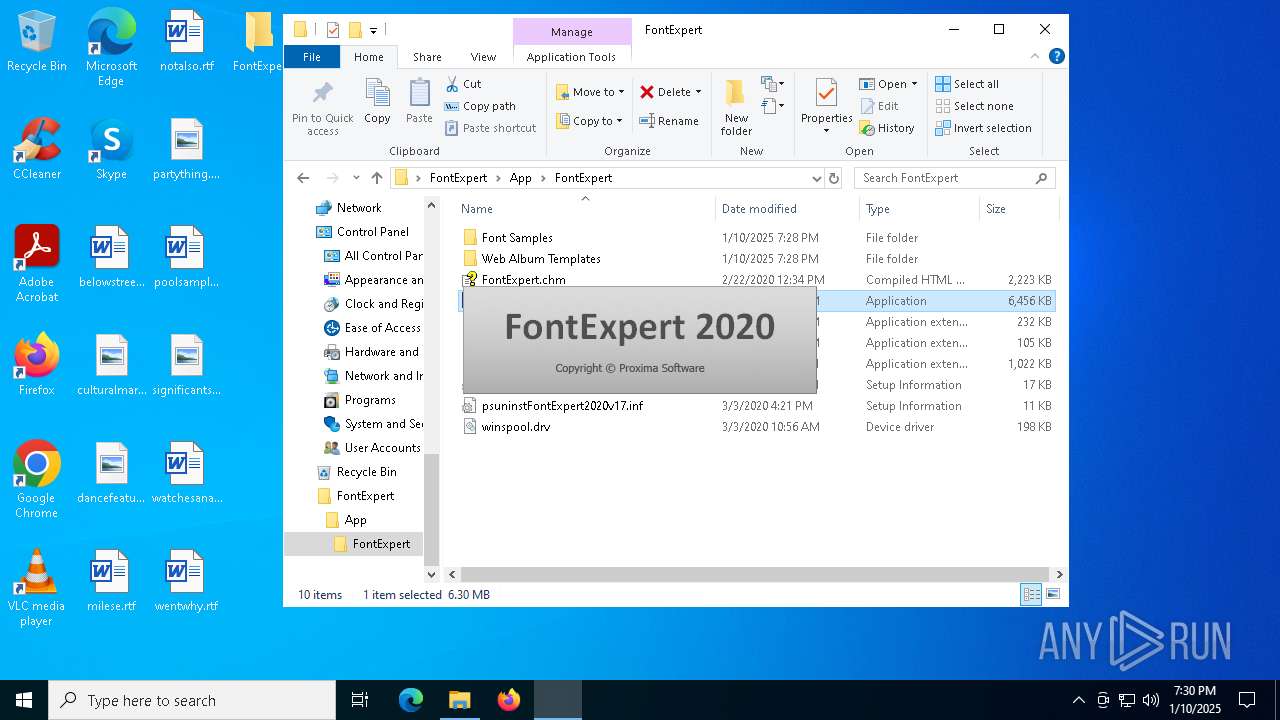
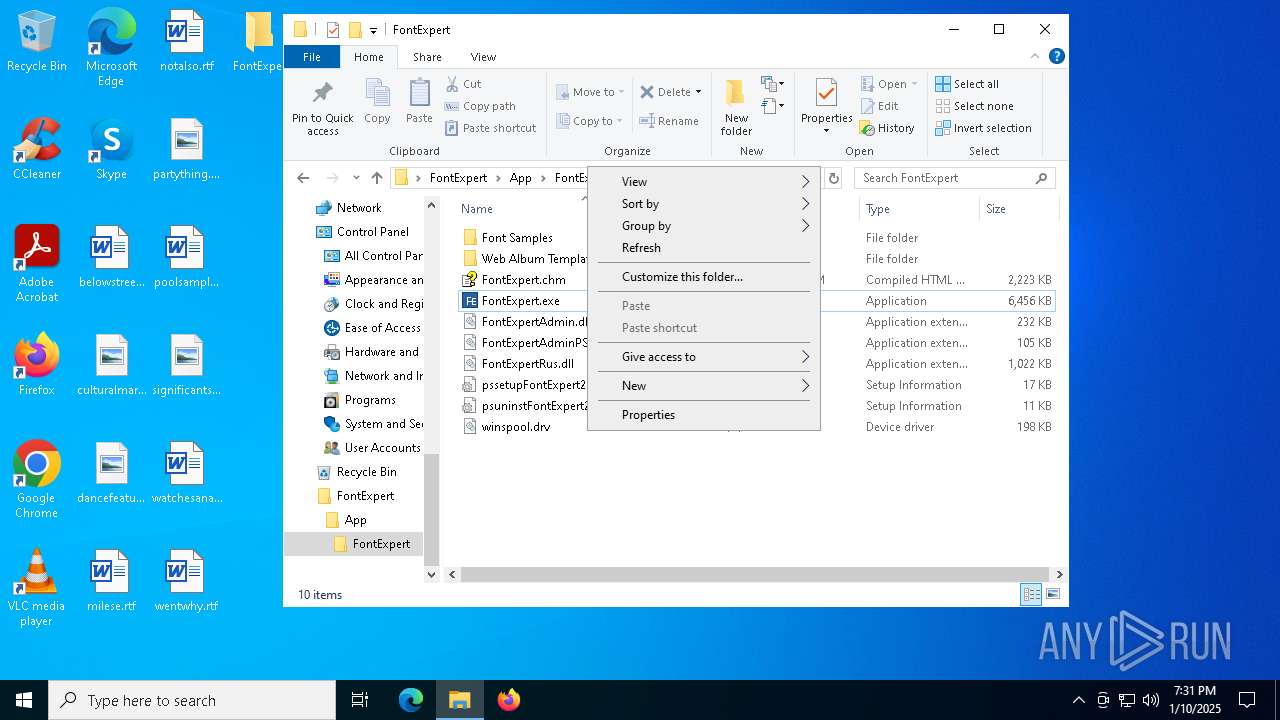
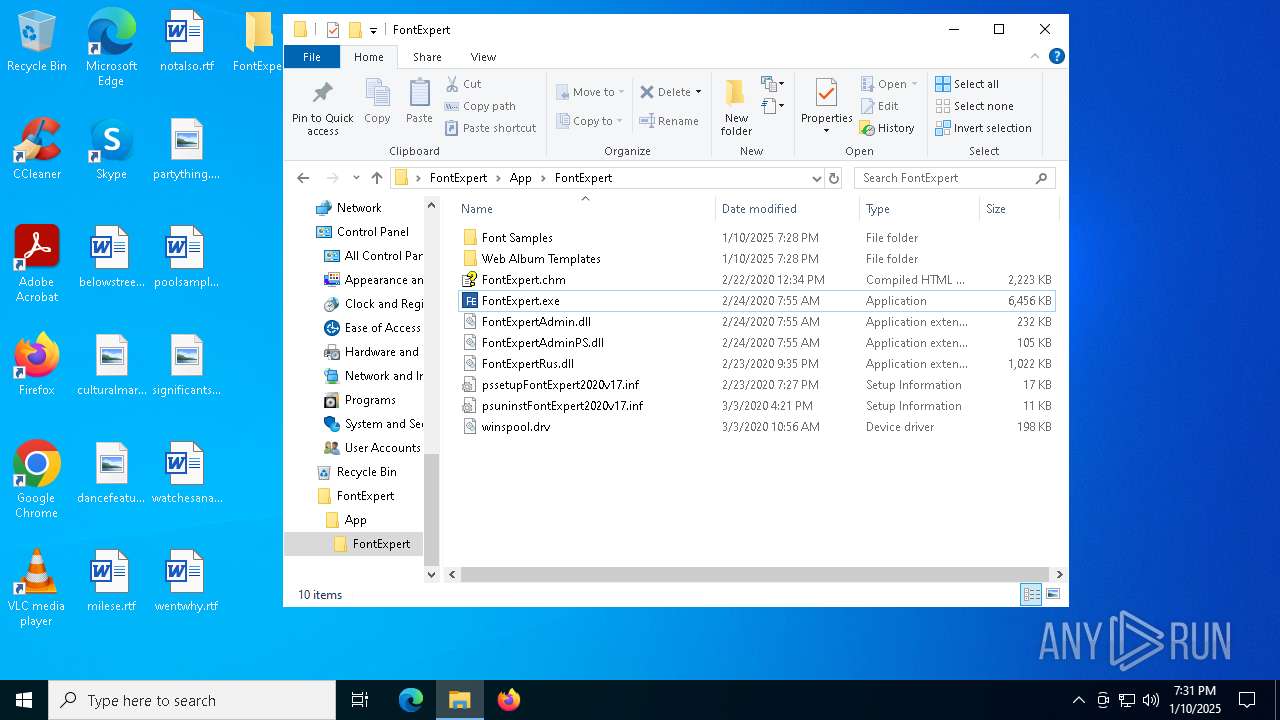
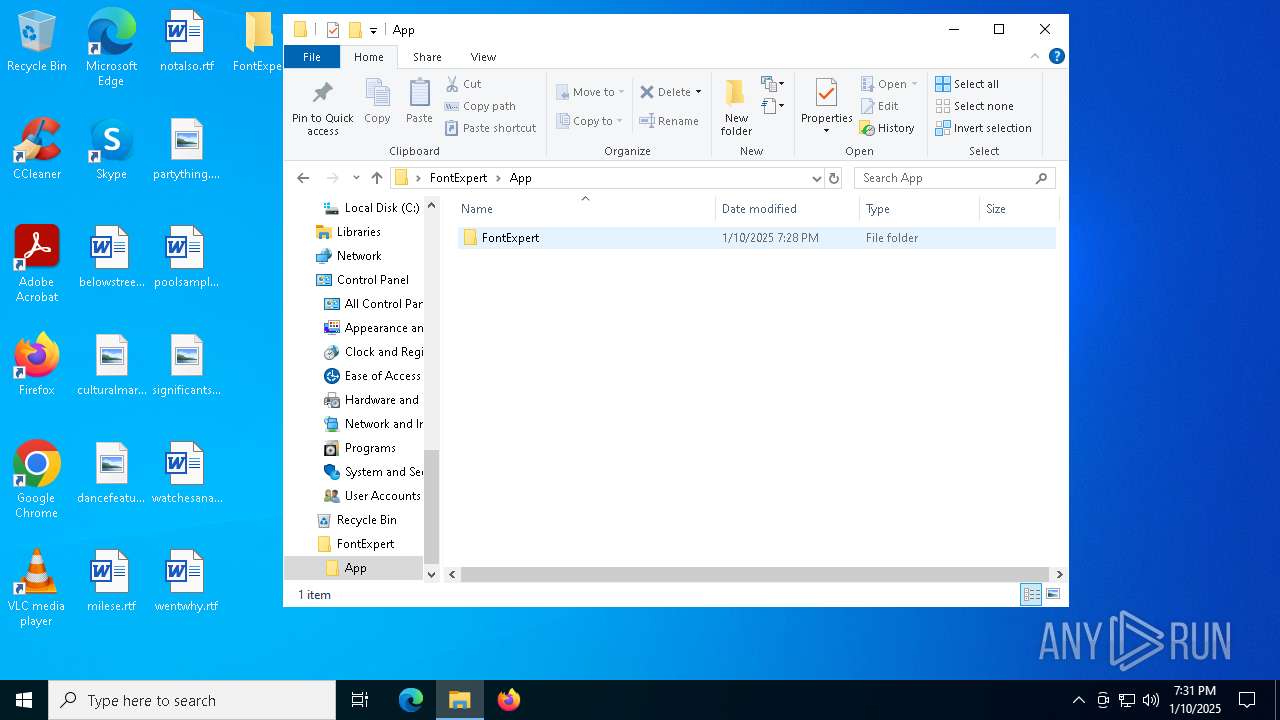
| 2076 | "C:\Users\admin\Desktop\FontExpert\App\FontExpert\FontExpert.exe" | C:\Users\admin\Desktop\FontExpert\App\FontExpert\FontExpert.exe | — | explorer.exe | |||||||||||
User: admin Company: Proxima Software Integrity Level: MEDIUM Description: FontExpert Exit code: 0 Version: 17,0,0,1 Modules
| |||||||||||||||
| 2084 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2812 --field-trial-handle=2360,i,11867600637398239682,12832558400578098409,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2276 --field-trial-handle=2296,i,3523383542983983325,15250703872892007128,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
66 146
Read events
64 634
Write events
1 422
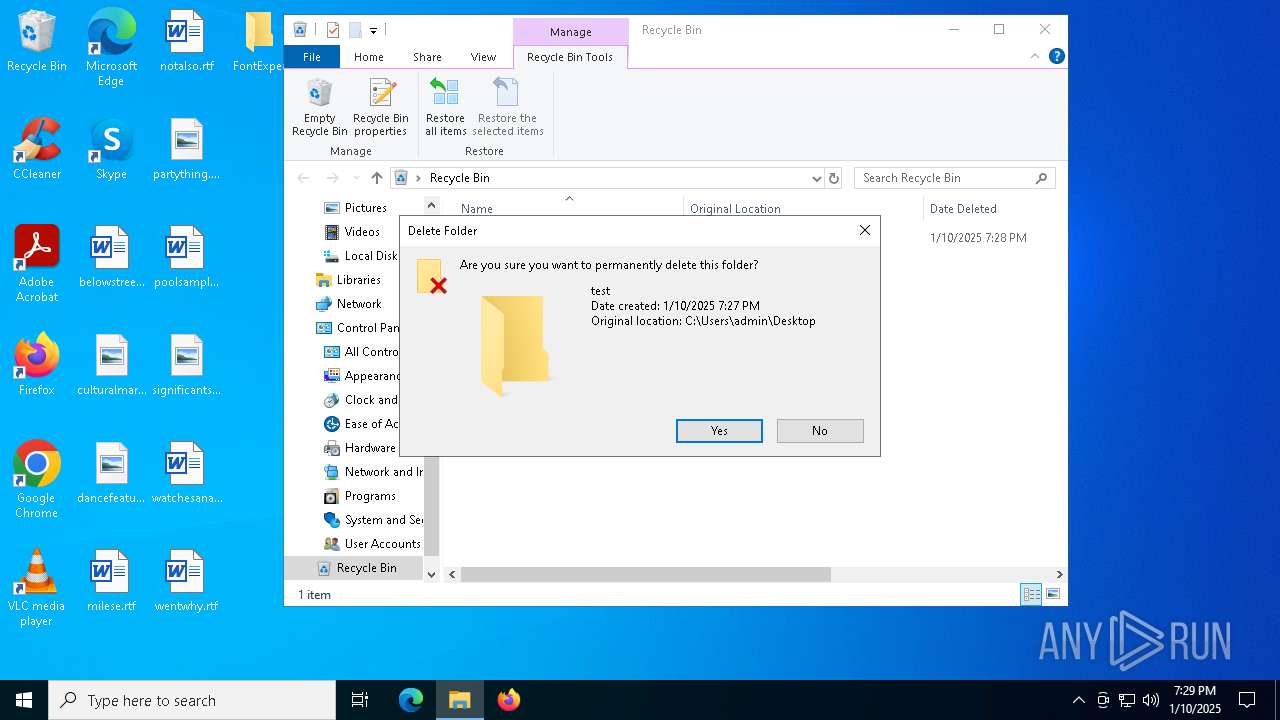
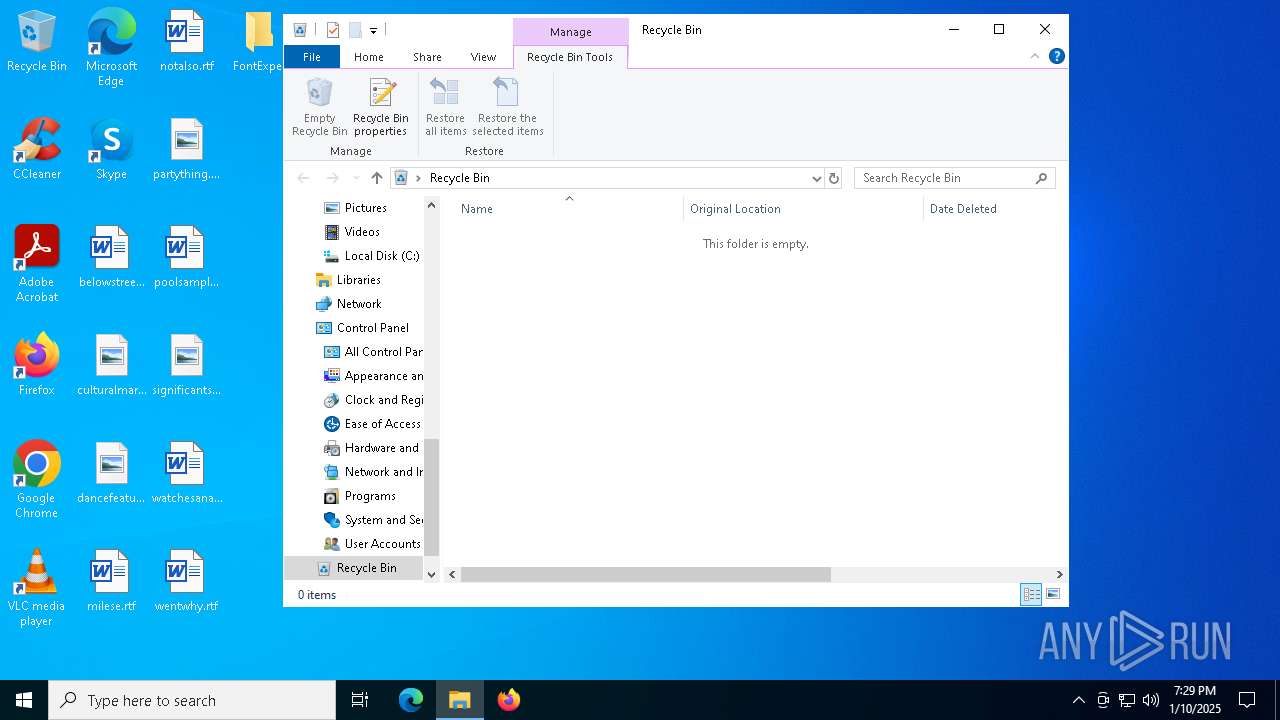
Delete events
90
Modification events
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000702CA |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000702CA |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_0 |
Value: 4C000000730100000402000000000000F0F0F00000000000000000000000000000000000000000005003050000000000000000003B000000B402000000000000000000000000000001000000 | |||
| (PID) Process: | (6328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_1 |
Value: 4C000000730100000500000000000000F0F0F0000000000000000000000000000000000000000000580305000000000000000000180000002A00000000000000000000000000000002000000 | |||
| (PID) Process: | (6328) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_2 |
Value: 4C000000730100000400000000000000F0F0F00000000000000000000000000000000000000000005A0305000000000000000000180000006400000000000000000000000000000003000000 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
Executable files
31
Suspicious files
524
Text files
137
Unknown types
5
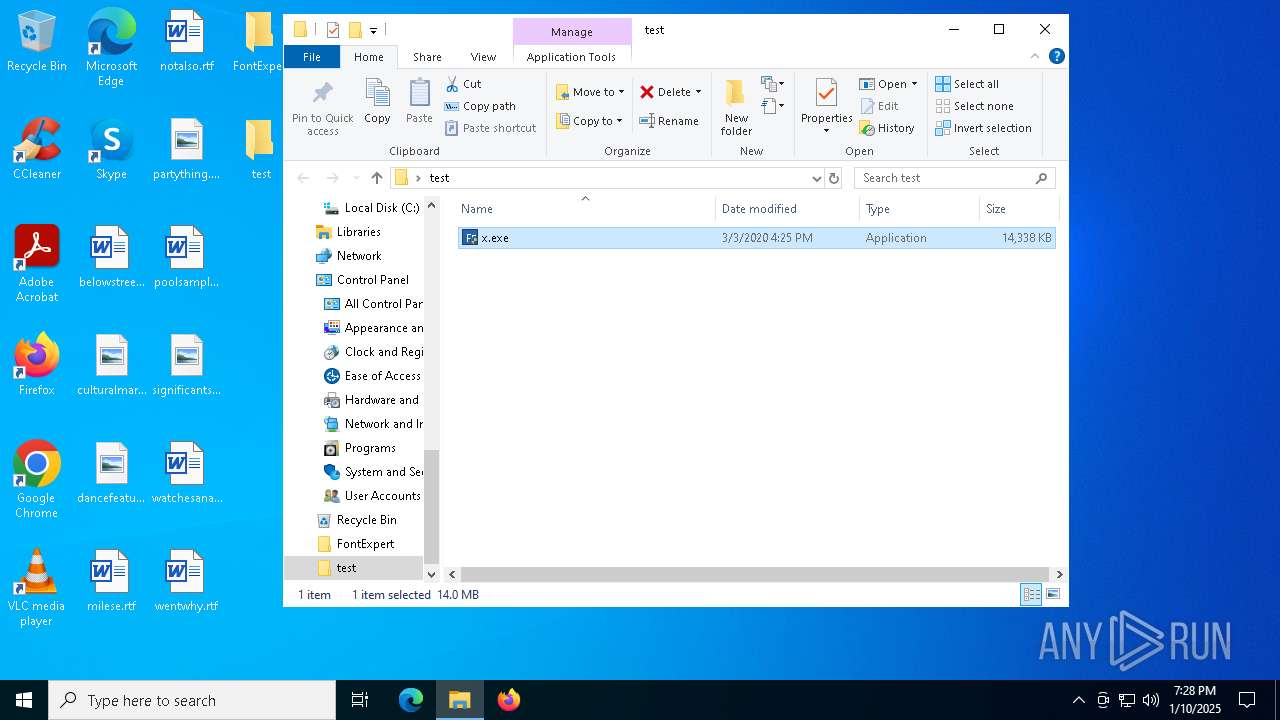
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
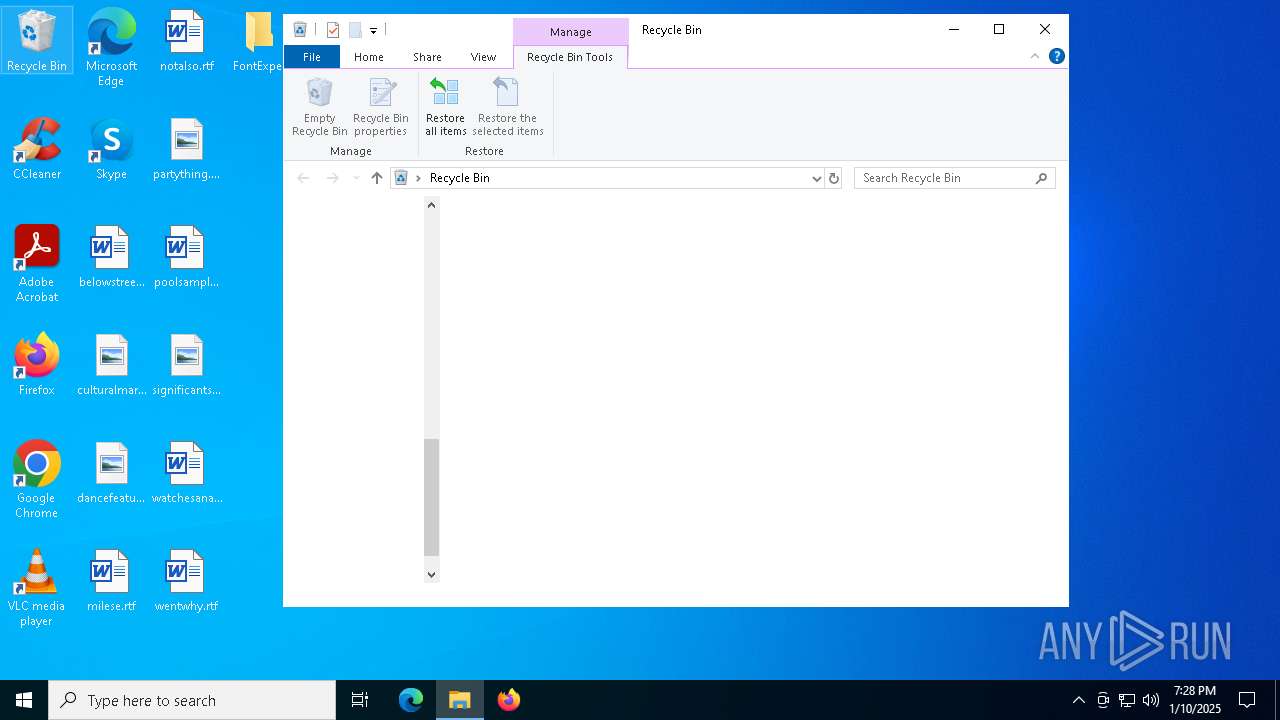
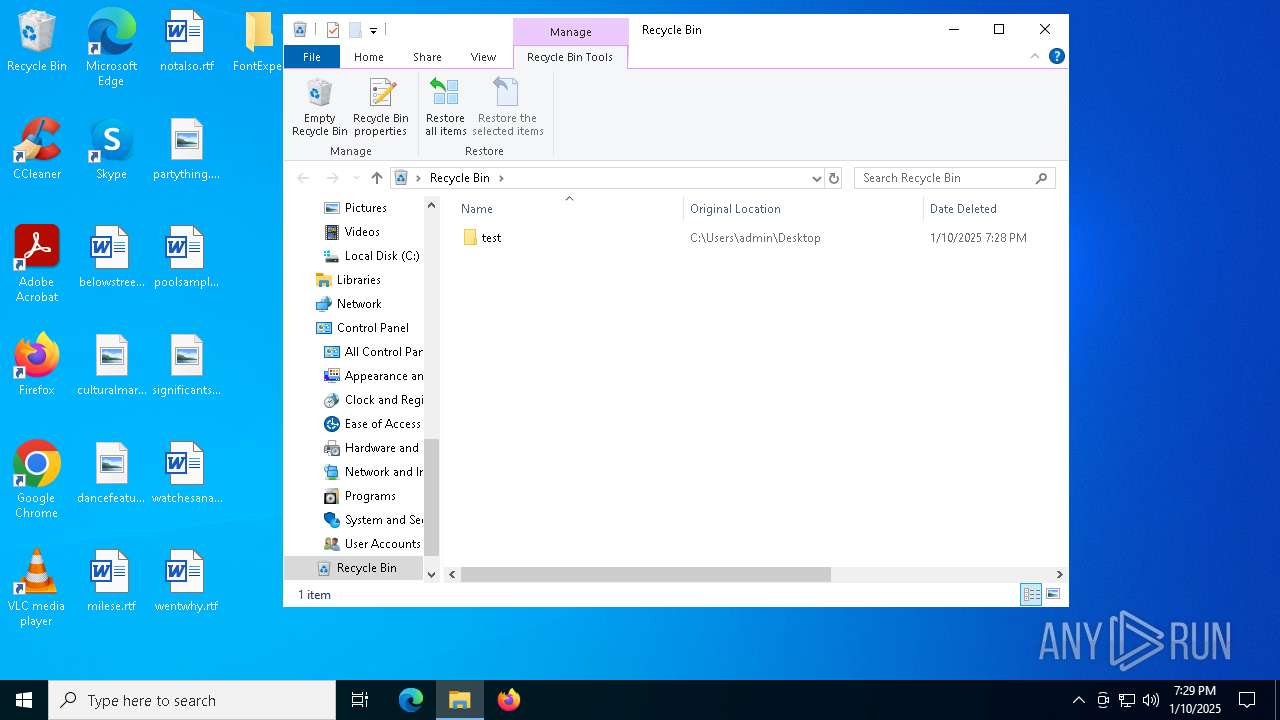
| 4488 | explorer.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-1001\$RSJOTDS.rar | — | |
MD5:— | SHA256:— | |||
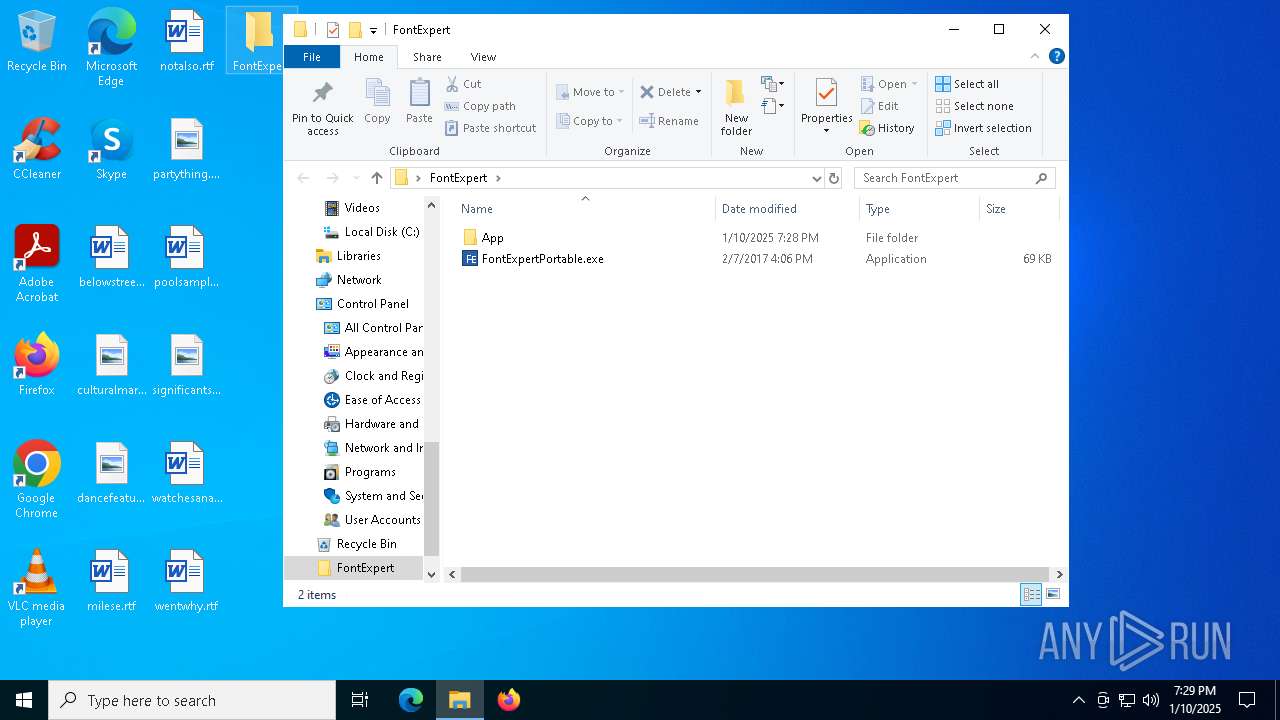
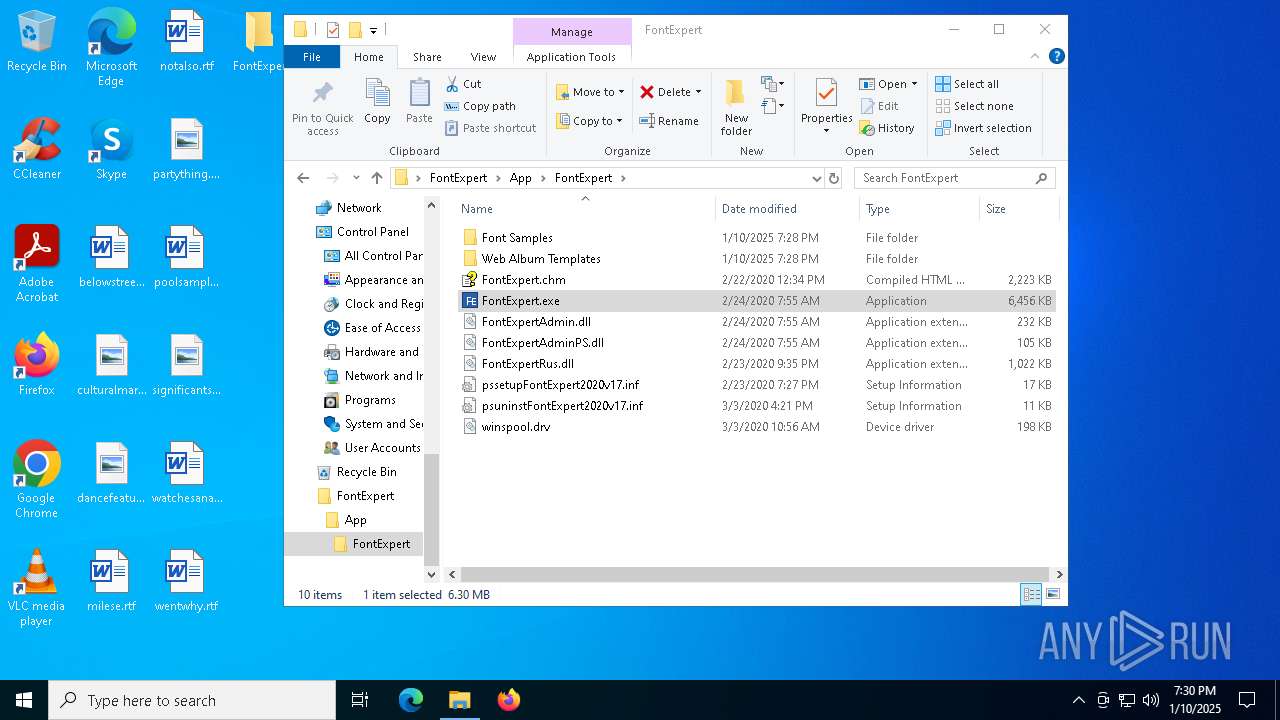
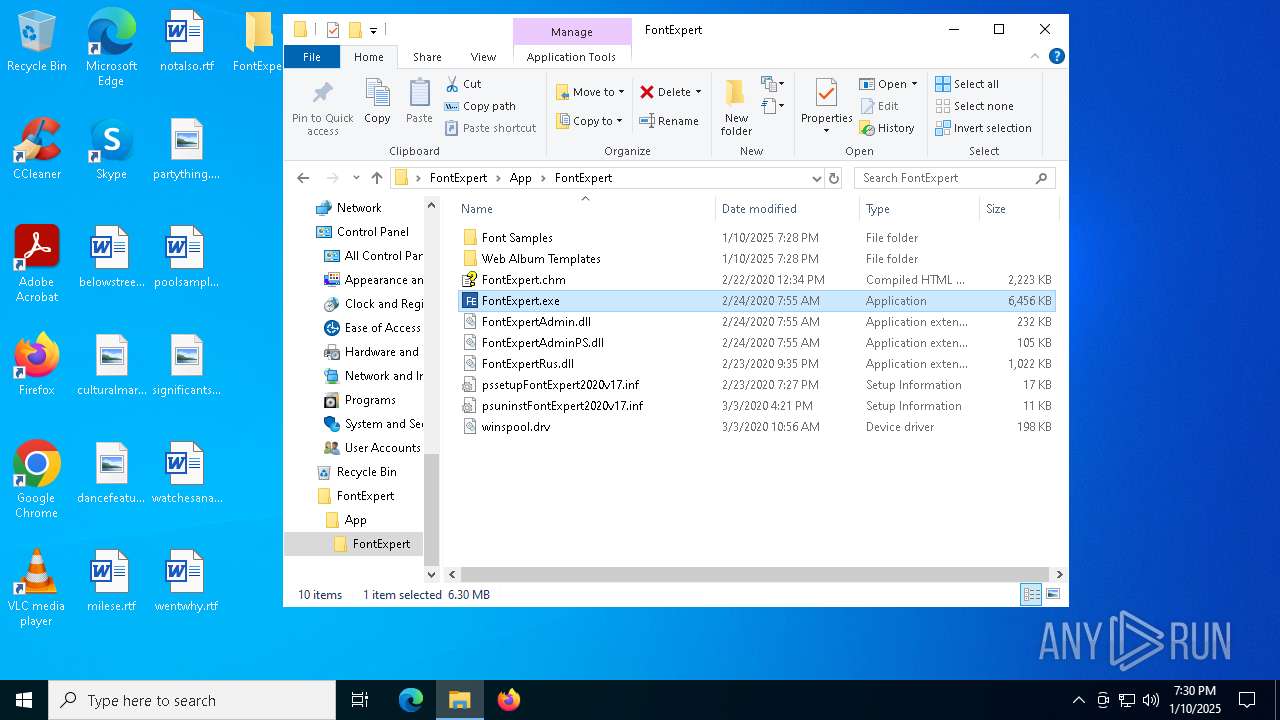
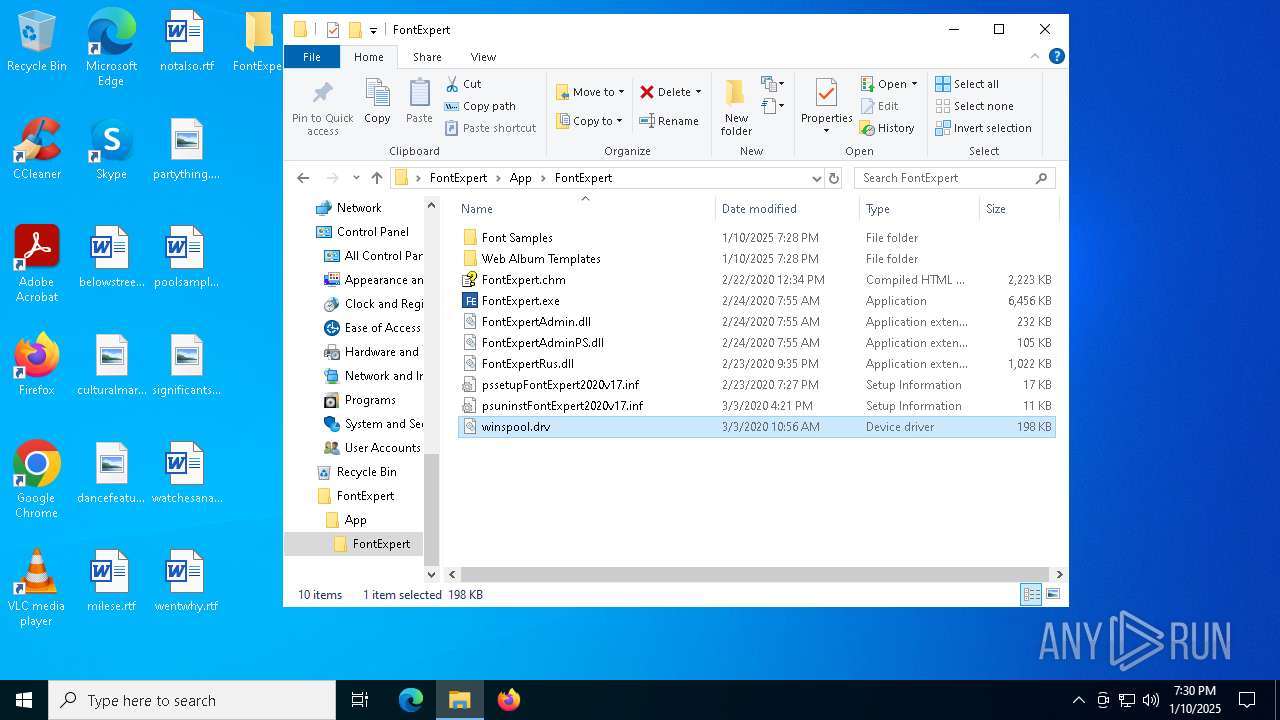
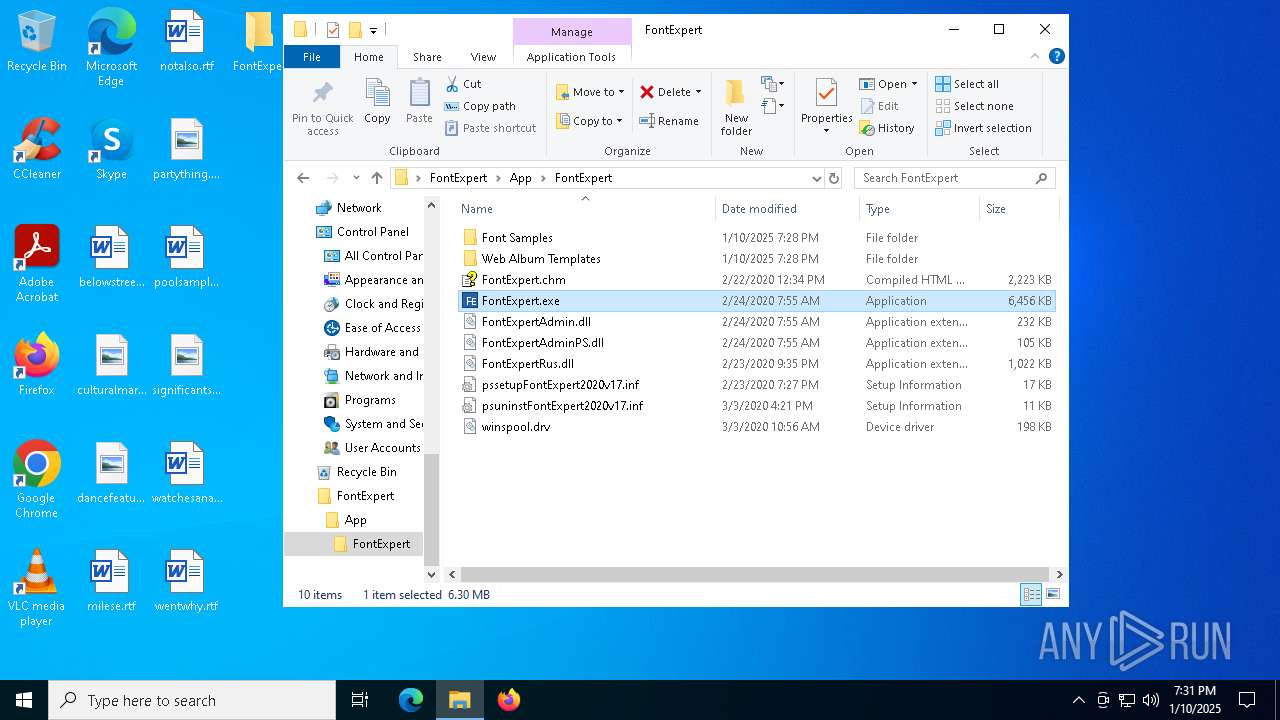
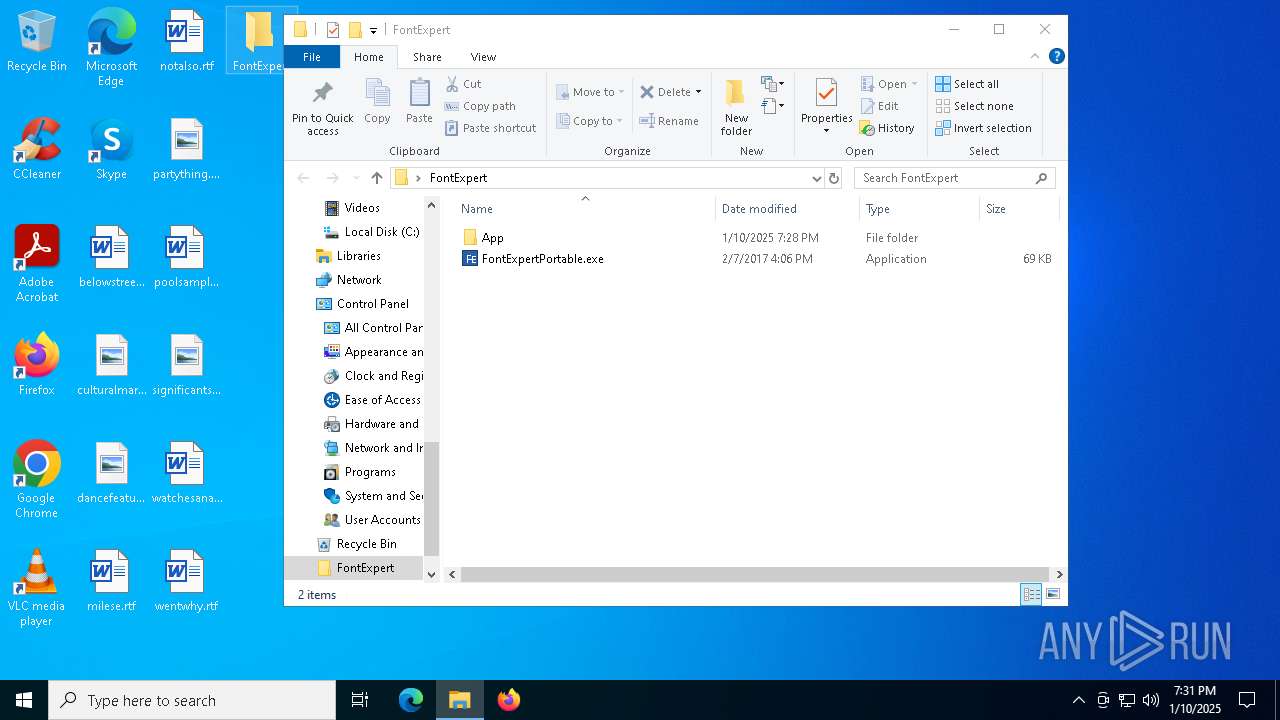
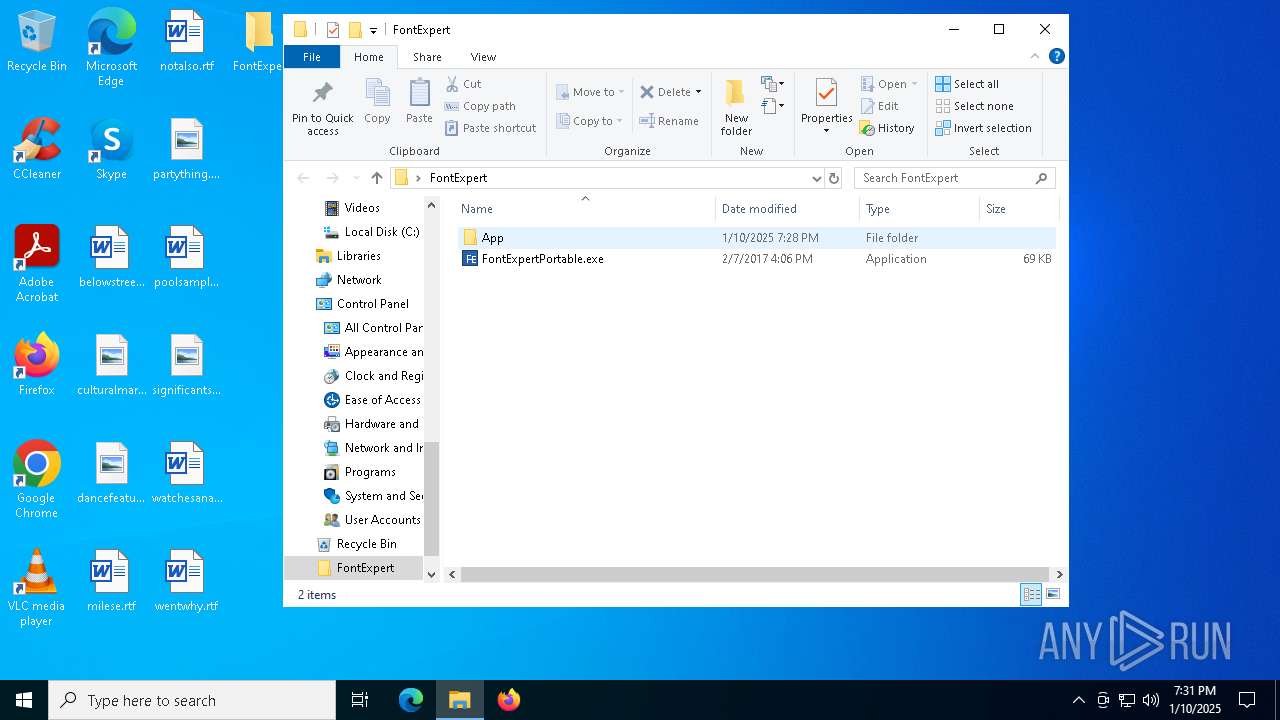
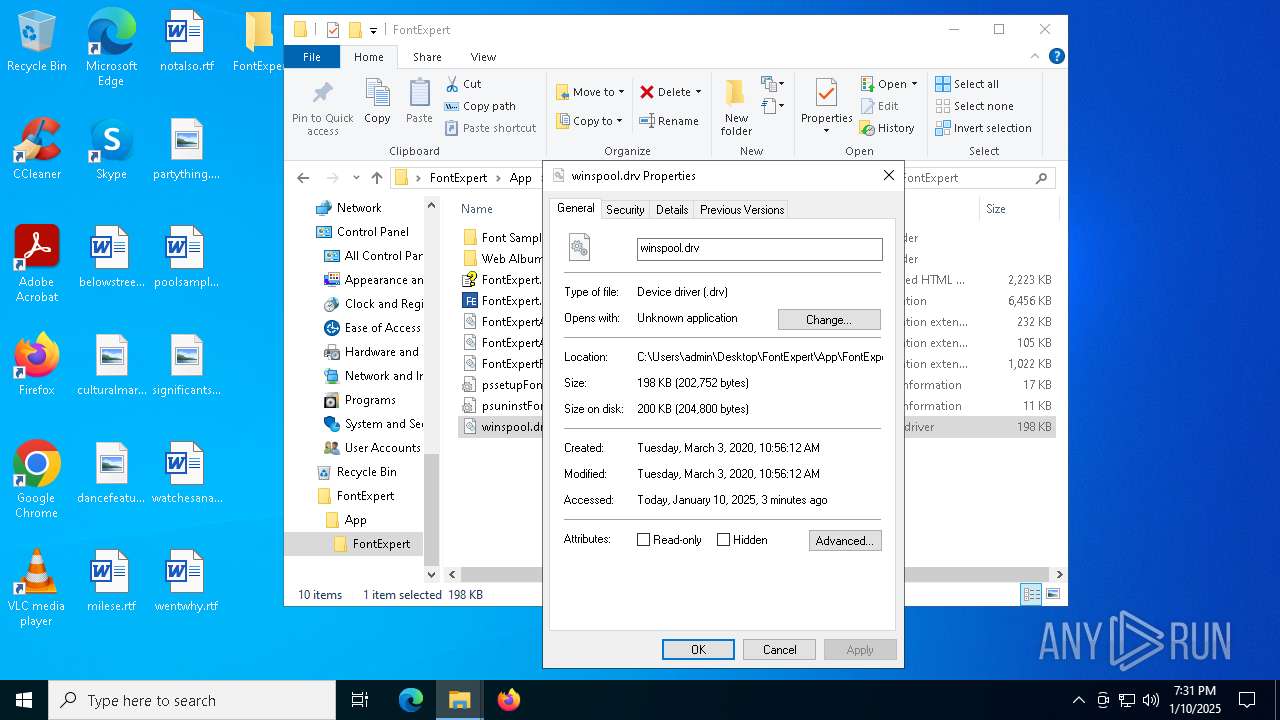
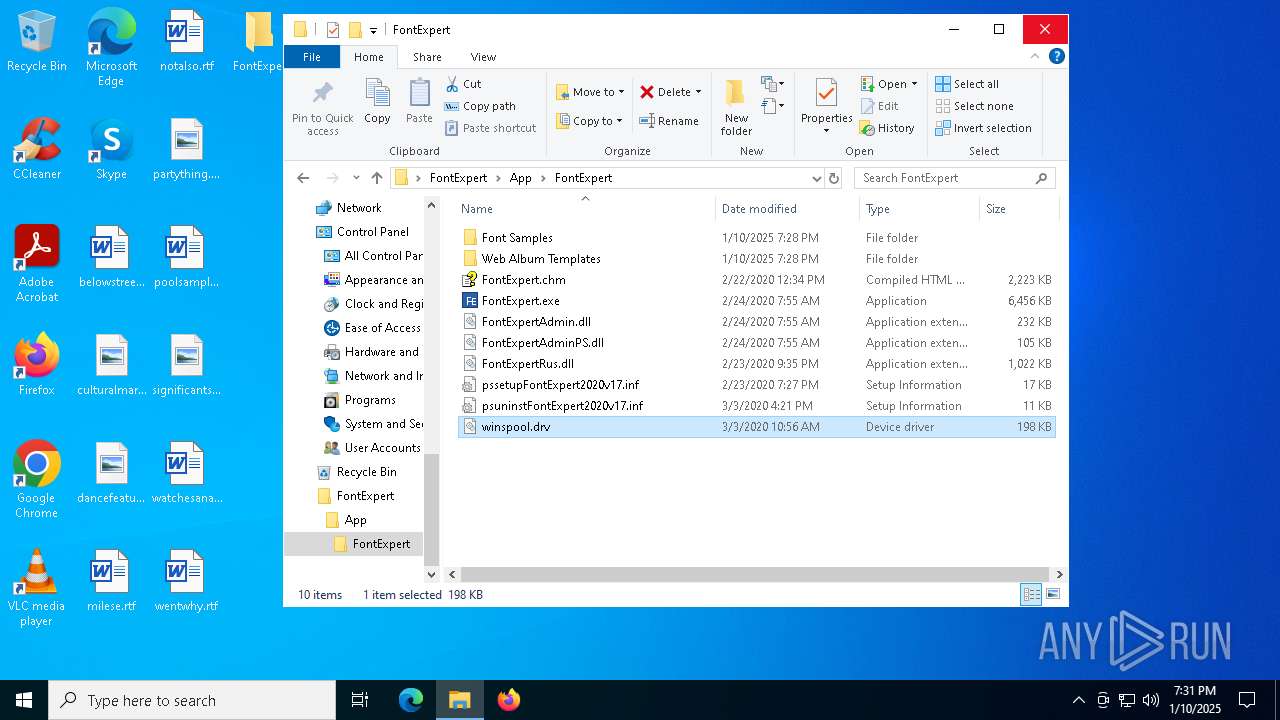
| 4740 | x.exe | C:\Users\admin\Desktop\FontExpert\FontExpertPortable.exe | executable | |
MD5:18E25EBA5EBD3A9B400657B3E6722B9E | SHA256:CD7A1A9124B0652E8D1A428BD959683CA1F92CB7C730097DD27D3310ADDA7805 | |||
| 4740 | x.exe | C:\Users\admin\AppData\Local\Temp\nsbFFE1.tmp\nsis-r.bmp | image | |
MD5:E0F6D1919734B498325CE459C8F6994D | SHA256:3C6E4748F25607AF12306691D3ED7CC241A50EE575F5B98E9352C3EBF7F0D8BE | |||
| 4740 | x.exe | C:\Users\admin\AppData\Local\Temp\nsbFFE1.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 4488 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
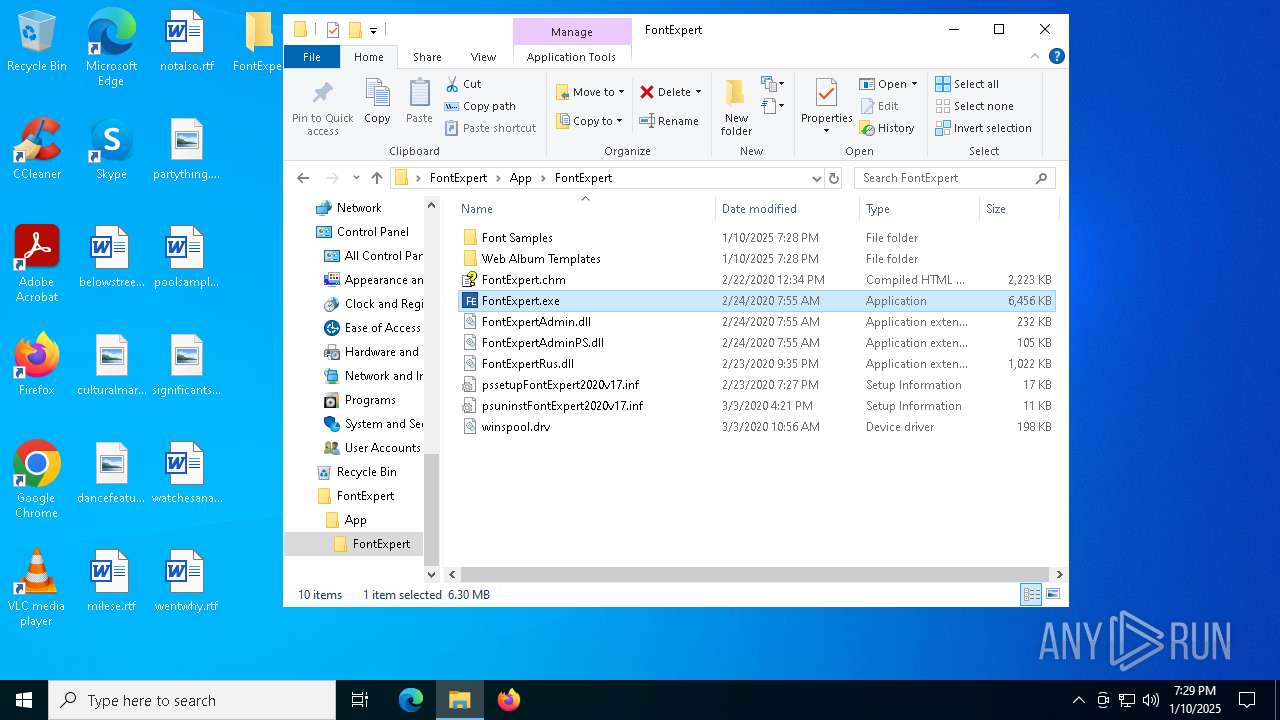
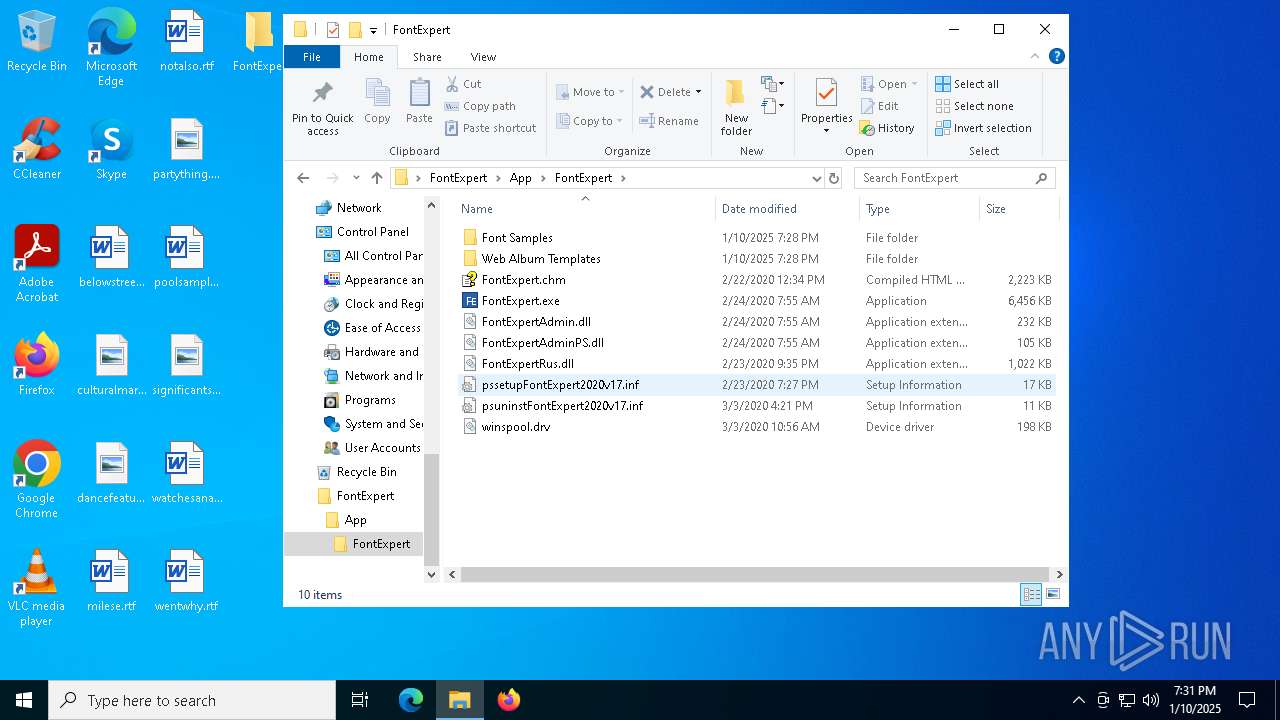
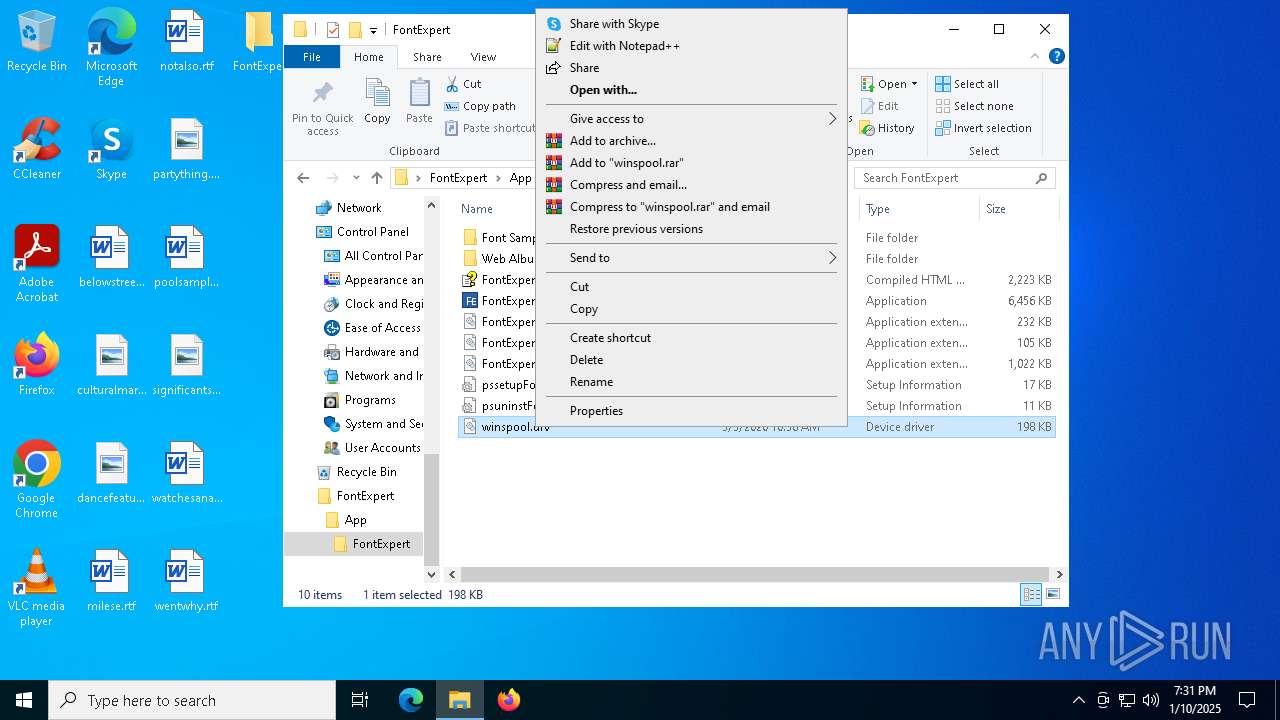
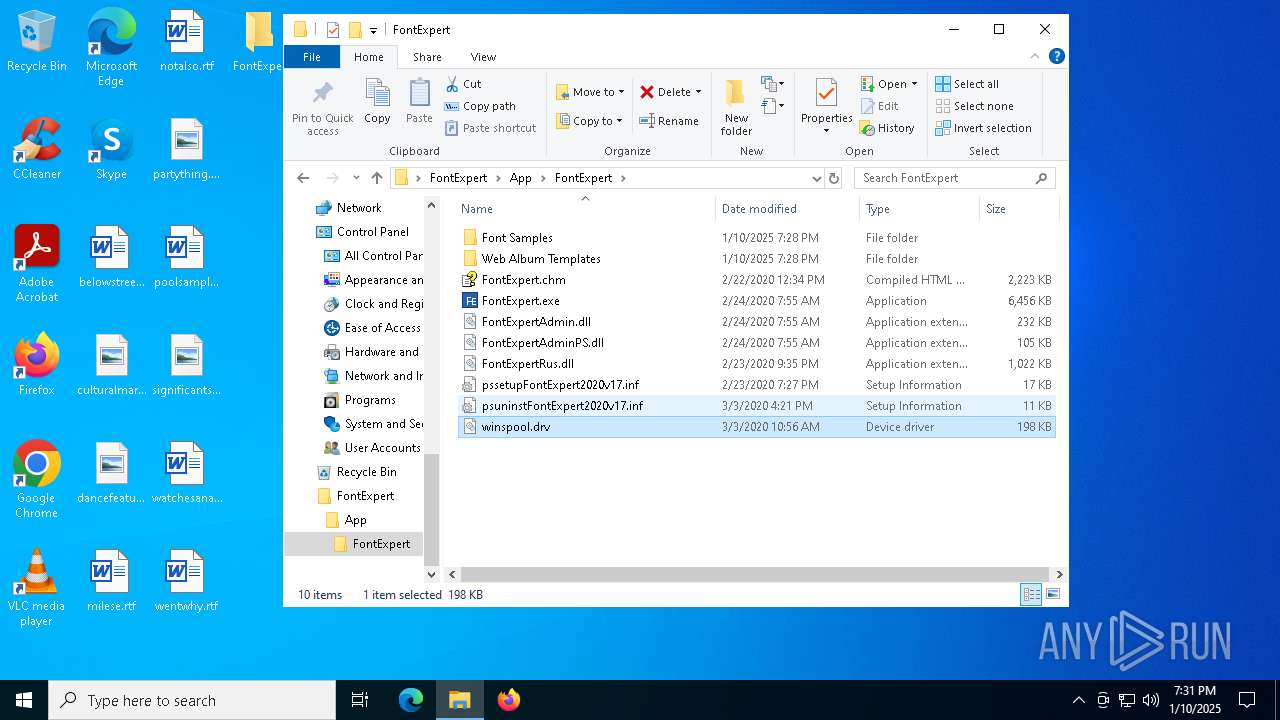
| 4740 | x.exe | C:\Users\admin\Desktop\FontExpert\App\FontExpert\FontExpert.chm | binary | |
MD5:A58D9DEA0341C48343F3B06151A6C191 | SHA256:2D10AAC66EE5E48C2357D9FC19F83E1E94BE46E4E920D88F43FD4340E225F430 | |||
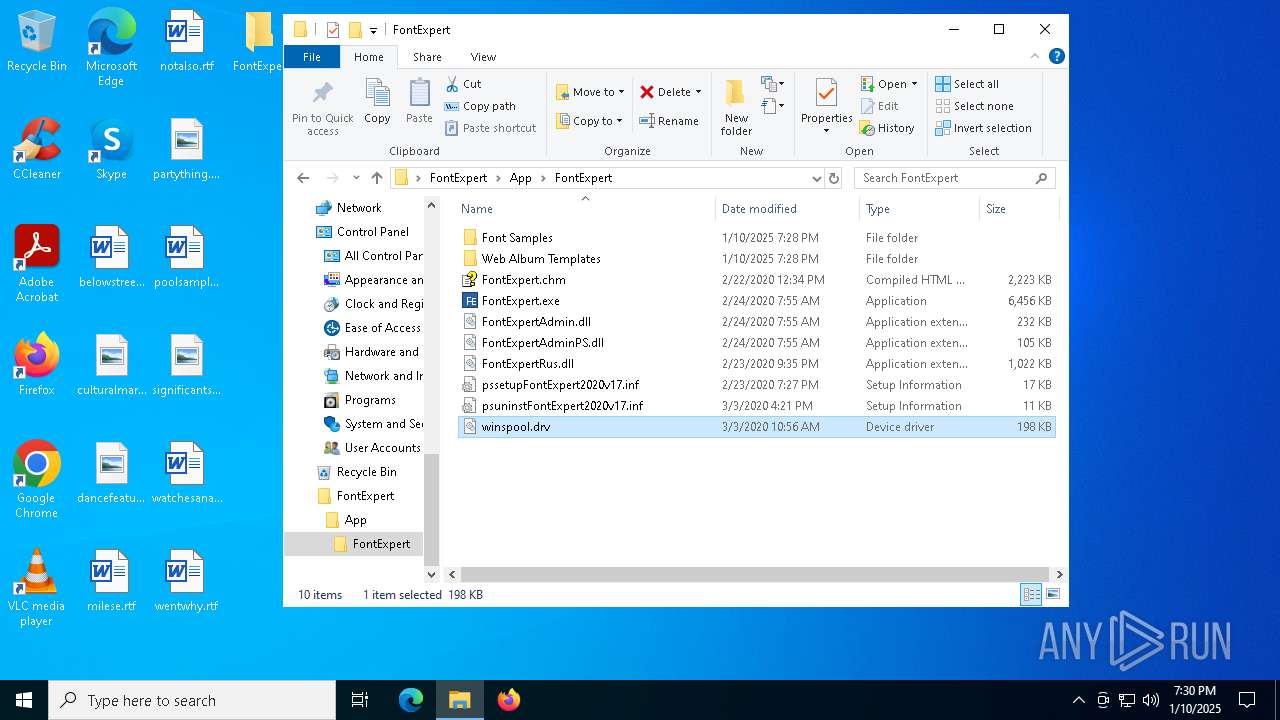
| 4740 | x.exe | C:\Users\admin\Desktop\FontExpert\App\FontExpert\pssetupFontExpert2020v17.inf | text | |
MD5:E3F139670FD5940952494D24FDBE65D6 | SHA256:AE3D7F0A4DBA952921F0DCFDE6DF694EB7D1EEC68EE152A067B608CC2841506E | |||
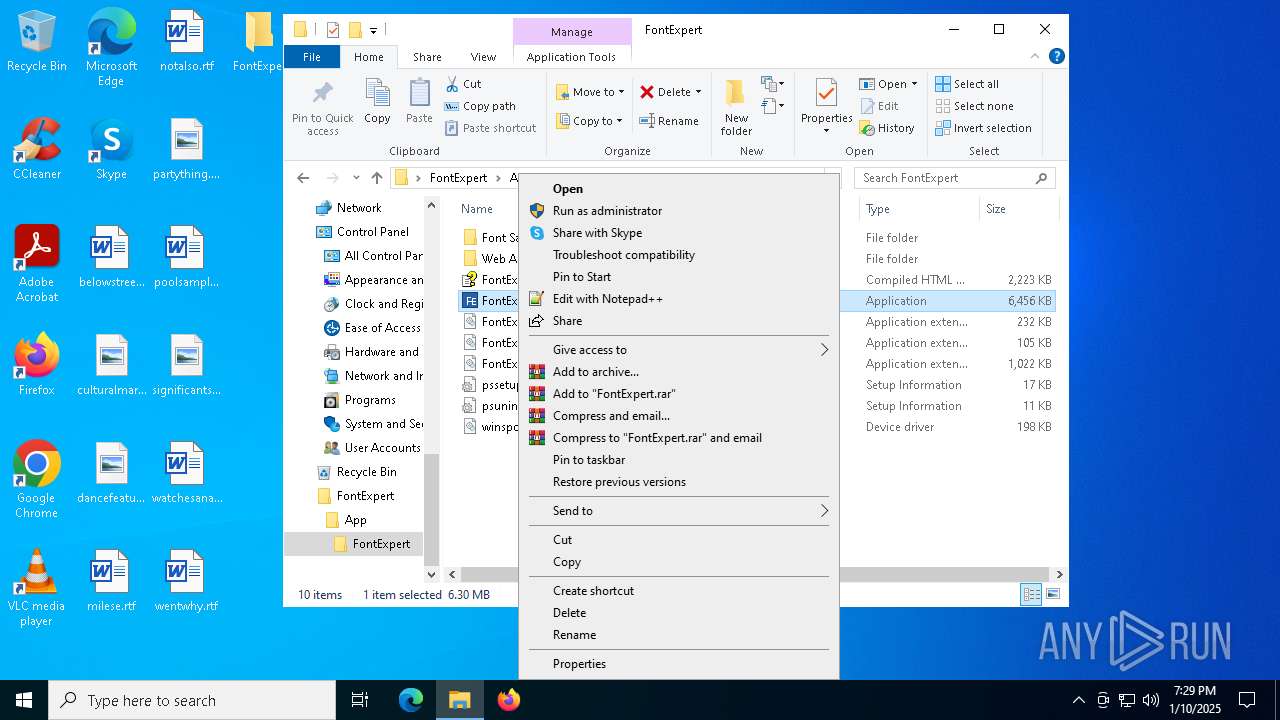
| 4740 | x.exe | C:\Users\admin\Desktop\FontExpert\App\FontExpert\FontExpert.exe | executable | |
MD5:E773BD0181A0A9A65929882F3AE783AA | SHA256:329DA6141069356C334C321125E14491164105DC73CB4AC2A46F31110C4AE84B | |||
| 4740 | x.exe | C:\Users\admin\Desktop\FontExpert\App\FontExpert\FontExpertAdminPS.dll | executable | |
MD5:5793EF283A67A919EB5E290796558787 | SHA256:C3A595104C6527C38CC2DA0827CDC6C366F61CBC44D10EEF1E8CC3FC9A159BBD | |||
| 4740 | x.exe | C:\Users\admin\Desktop\FontExpert\App\FontExpert\FontExpertAdmin.dll | executable | |
MD5:89128B8EC72DE33A0C0B4144D7E4ADD3 | SHA256:44593A93E31684784385AF759166C299EB0FA508EF45C60A4C5693FAB837E30A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
140
DNS requests
174
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4500 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7136 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7136 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4488 | explorer.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | unknown | — | — | whitelisted |
4488 | explorer.exe | GET | 404 | 172.64.149.23:80 | http://crl.usertrust.com/AddTrustExternalCARoot.crl | unknown | — | — | whitelisted |
4488 | explorer.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEC58h8wOk0pS%2FpT9HLfNNK8%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6068 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |