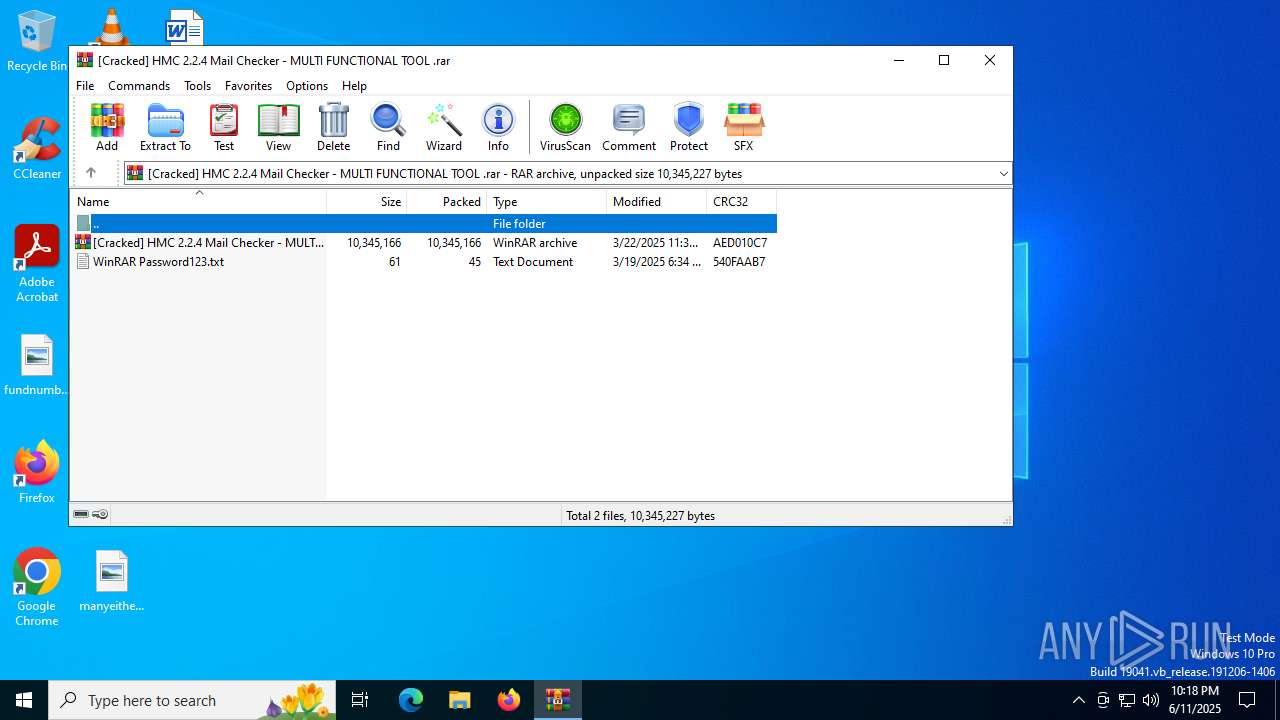
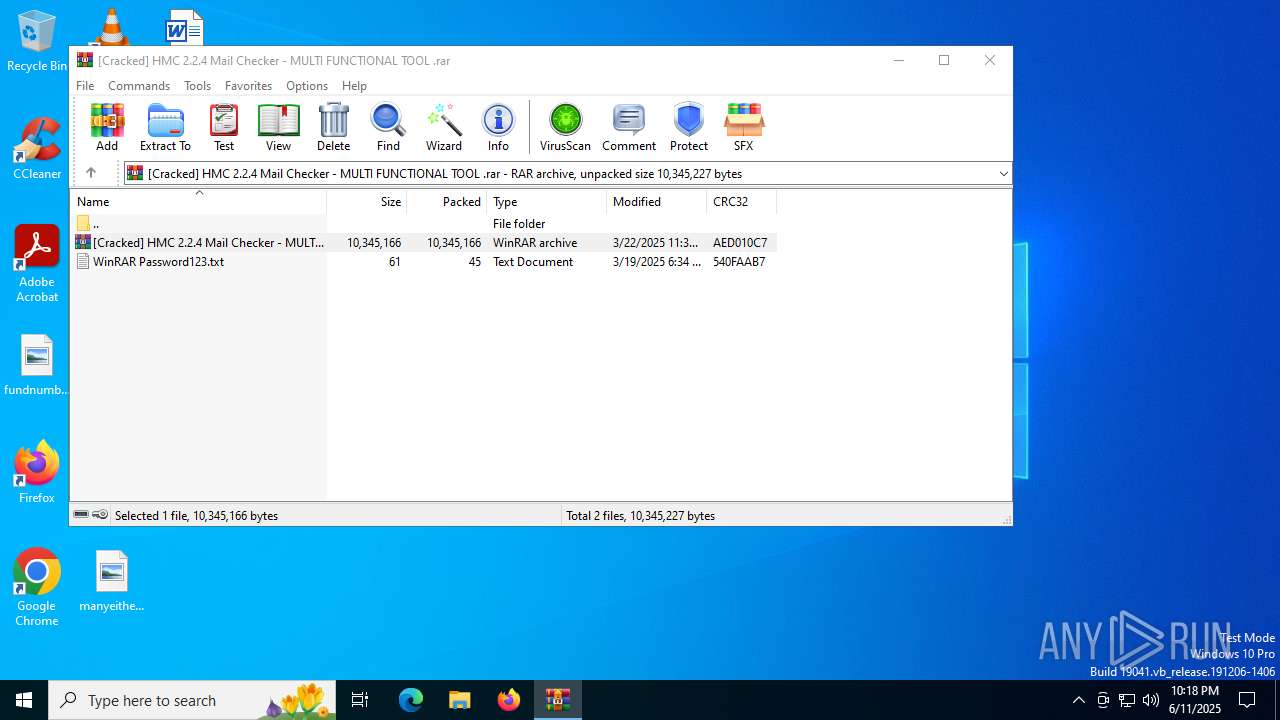
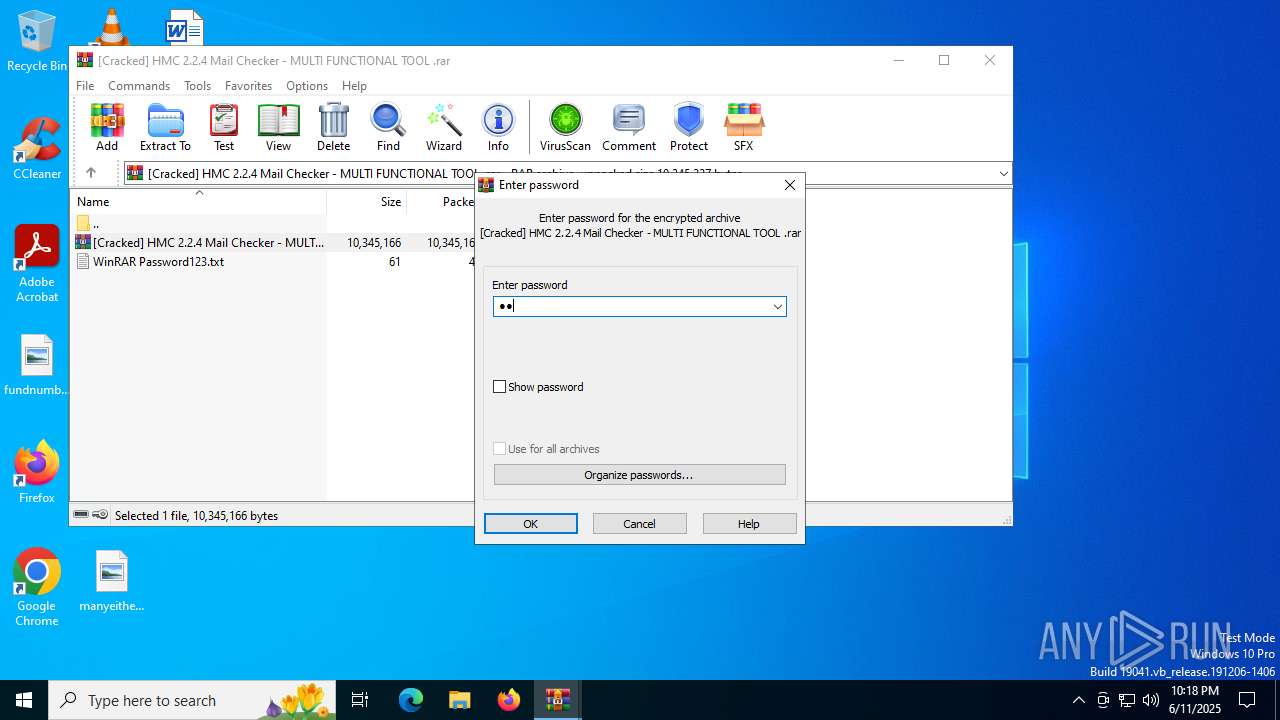
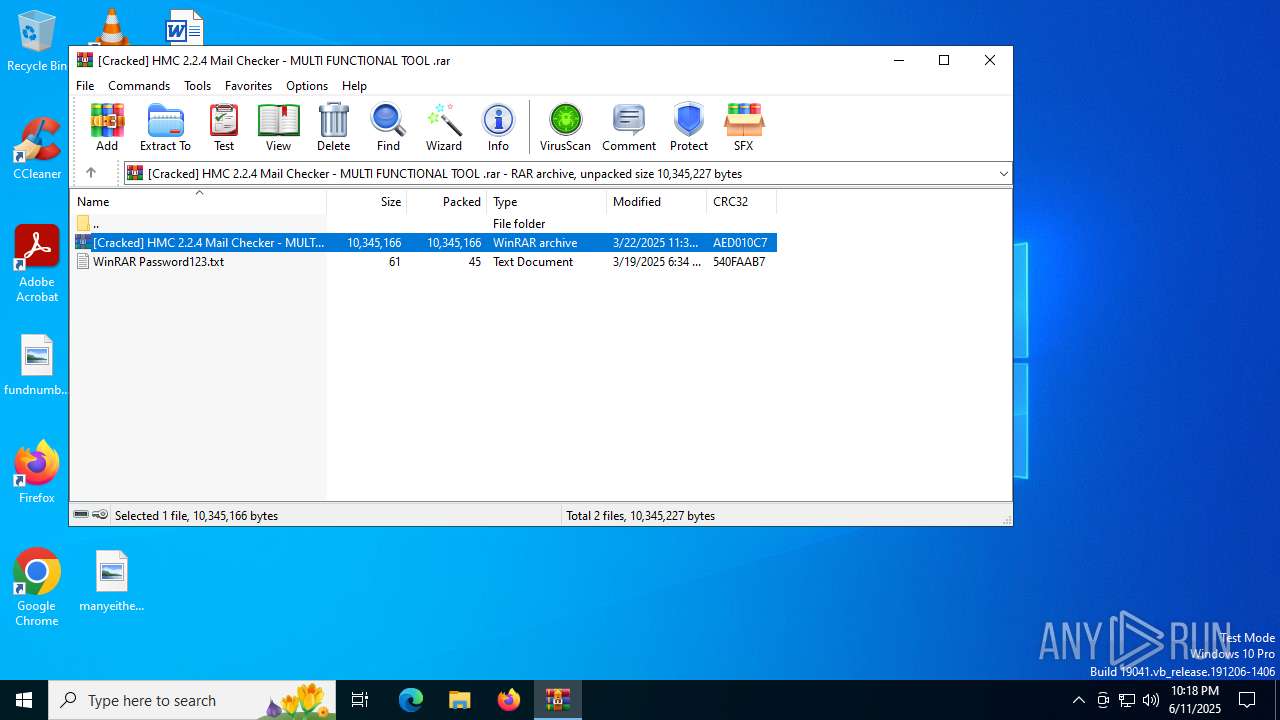
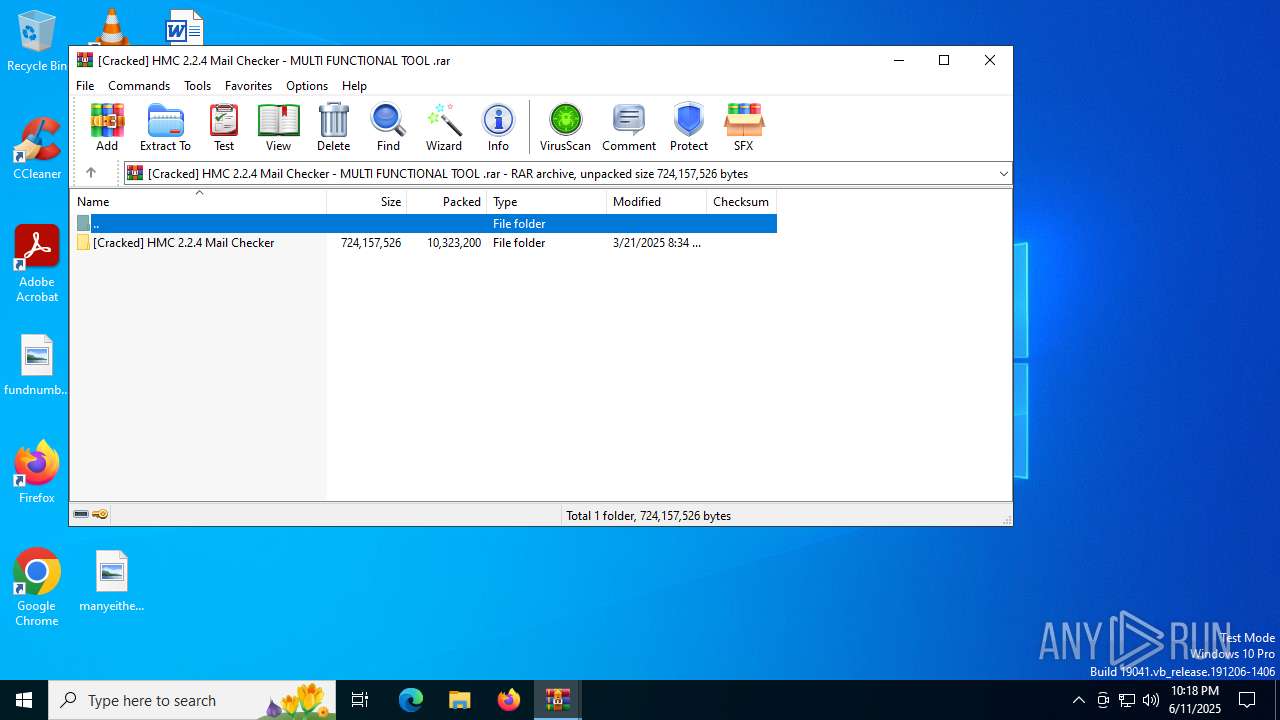
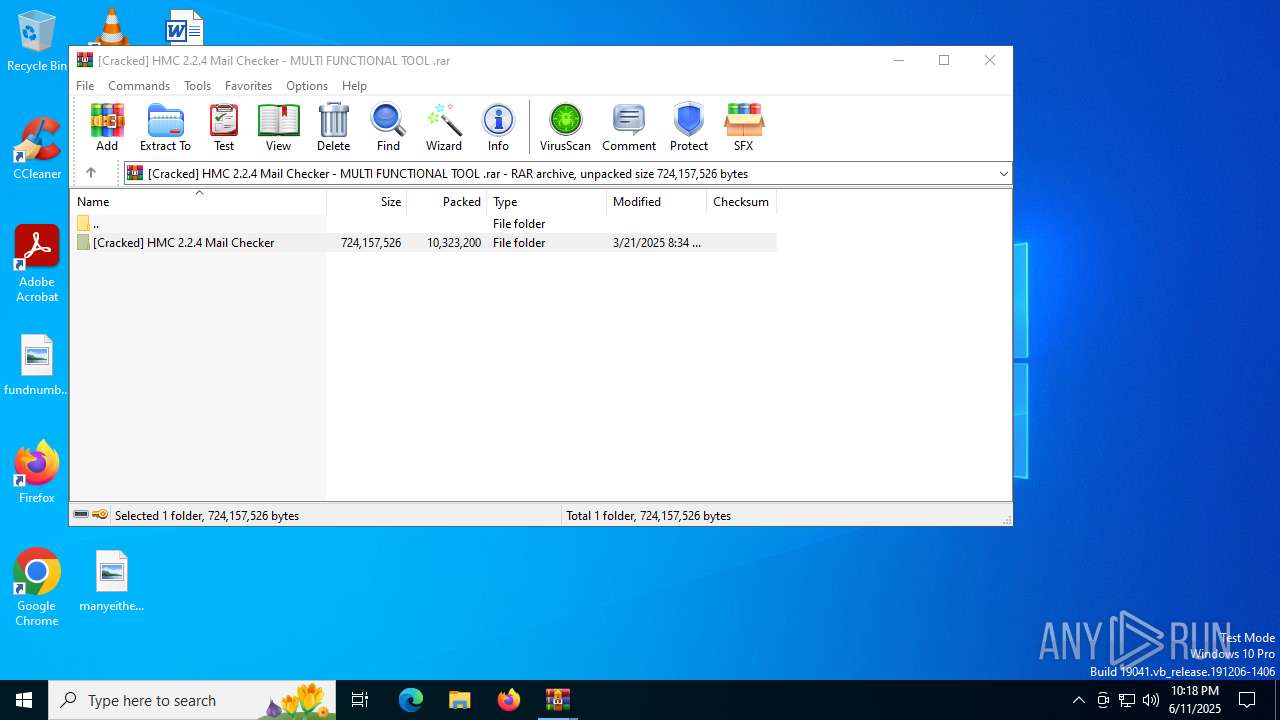
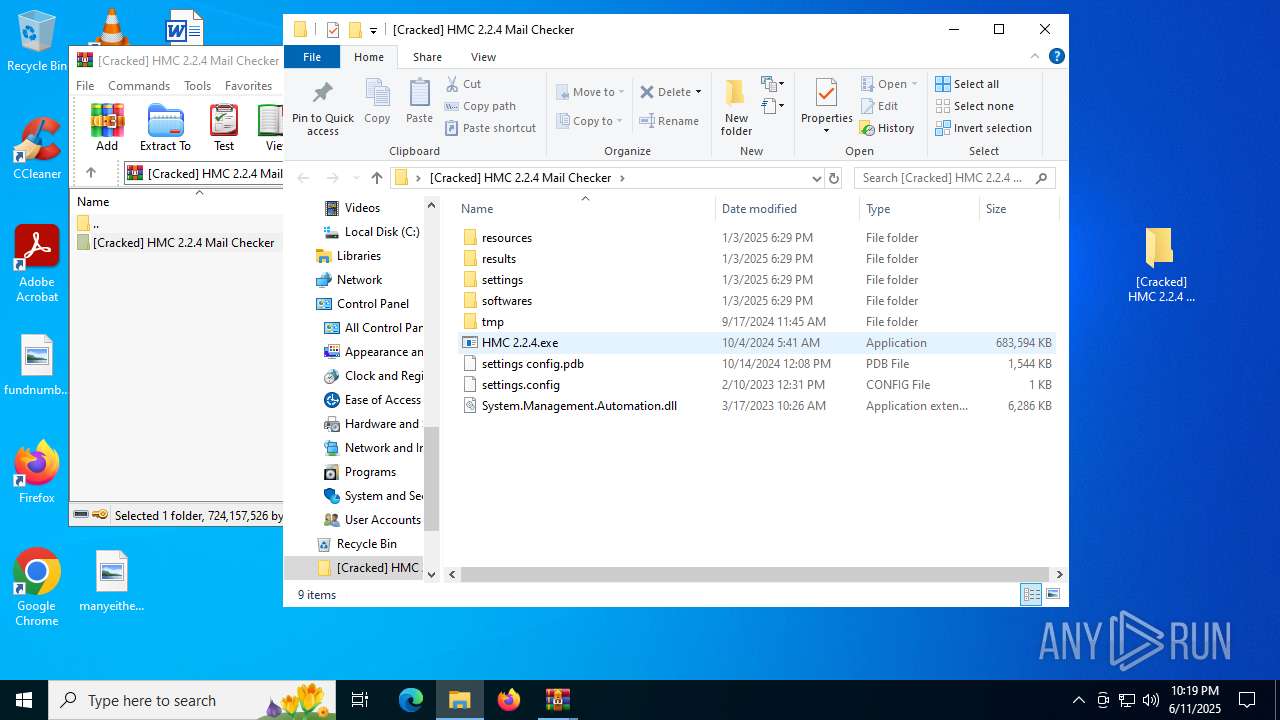
| File name: | [Cracked] HMC 2.2.4 Mail Checker - MULTI FUNCTIONAL TOOL .rar |
| Full analysis: | https://app.any.run/tasks/549eaa91-3cac-42cf-9bfe-04f8284a8c10 |
| Verdict: | Malicious activity |
| Analysis date: | June 11, 2025, 22:18:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 3CA42AF0C193FD482053DCBC9E93B60A |
| SHA1: | D721F90CA73E5909DC9960EDAD3676019E6D6B70 |
| SHA256: | 4E245EFDDF124CD763697282082EC8C44C2149DA09E419D9C5A15DEDAA453273 |
| SSDEEP: | 98304:62qXtzJvhX96XdiZ2jtjoDJdiYDx1GanIPMlHcHGKavrRiPFWLgEQd5TsHkUBMmD:jdxre30oTDuzKZdYPFvWvbj |
MALICIOUS
Changes Windows Defender settings
- HMC 2.2.4.exe (PID: 3092)
- QBFRMDZ.exe (PID: 3956)
- QBFRMDZ.exe (PID: 6840)
- QBFRMDZ.exe (PID: 4312)
- QBFRMDZ.exe (PID: 4380)
- QBFRMDZ.exe (PID: 5168)
Adds path to the Windows Defender exclusion list
- QBFRMDZ.exe (PID: 3956)
- HMC 2.2.4.exe (PID: 3092)
- QBFRMDZ.exe (PID: 6840)
- QBFRMDZ.exe (PID: 4312)
- QBFRMDZ.exe (PID: 4380)
- QBFRMDZ.exe (PID: 5168)
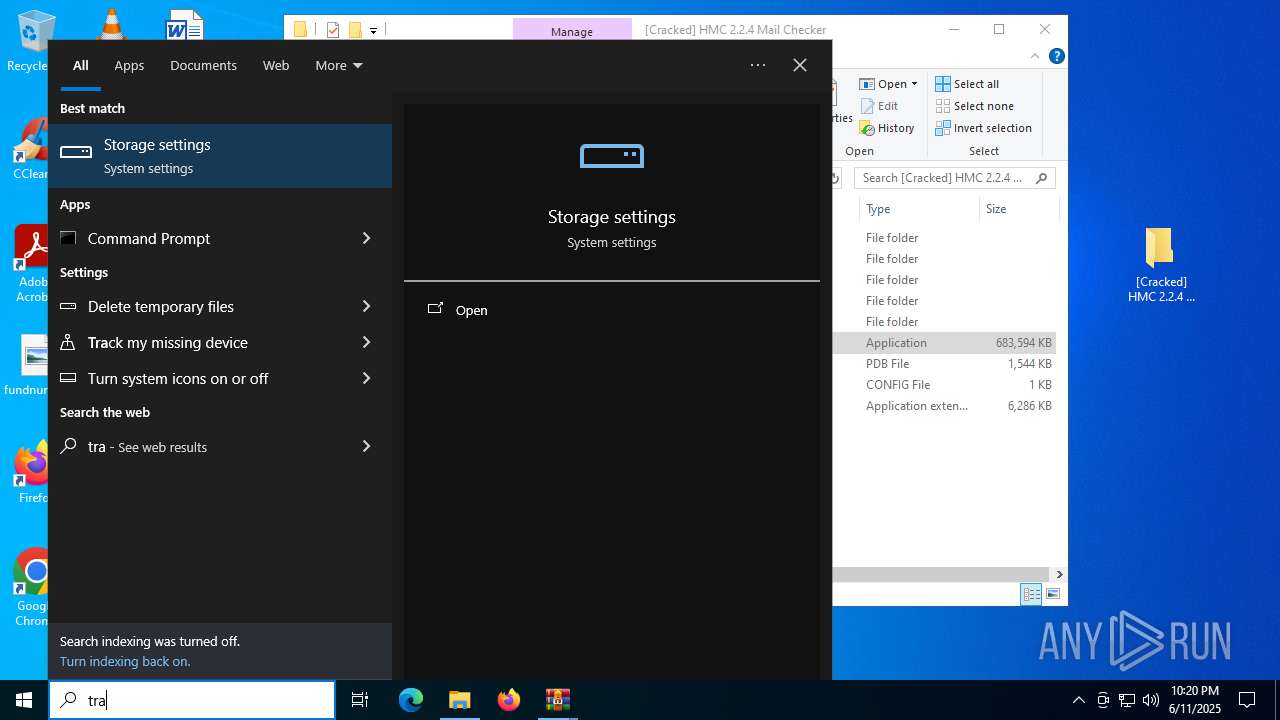
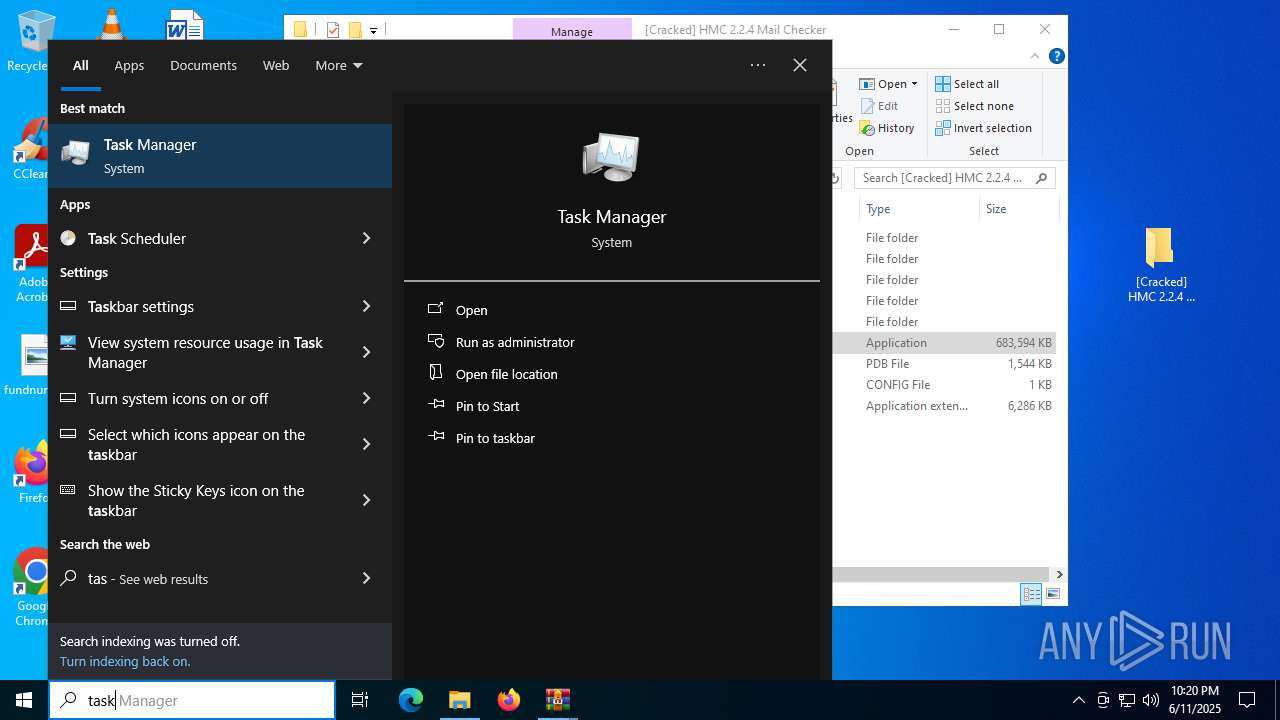
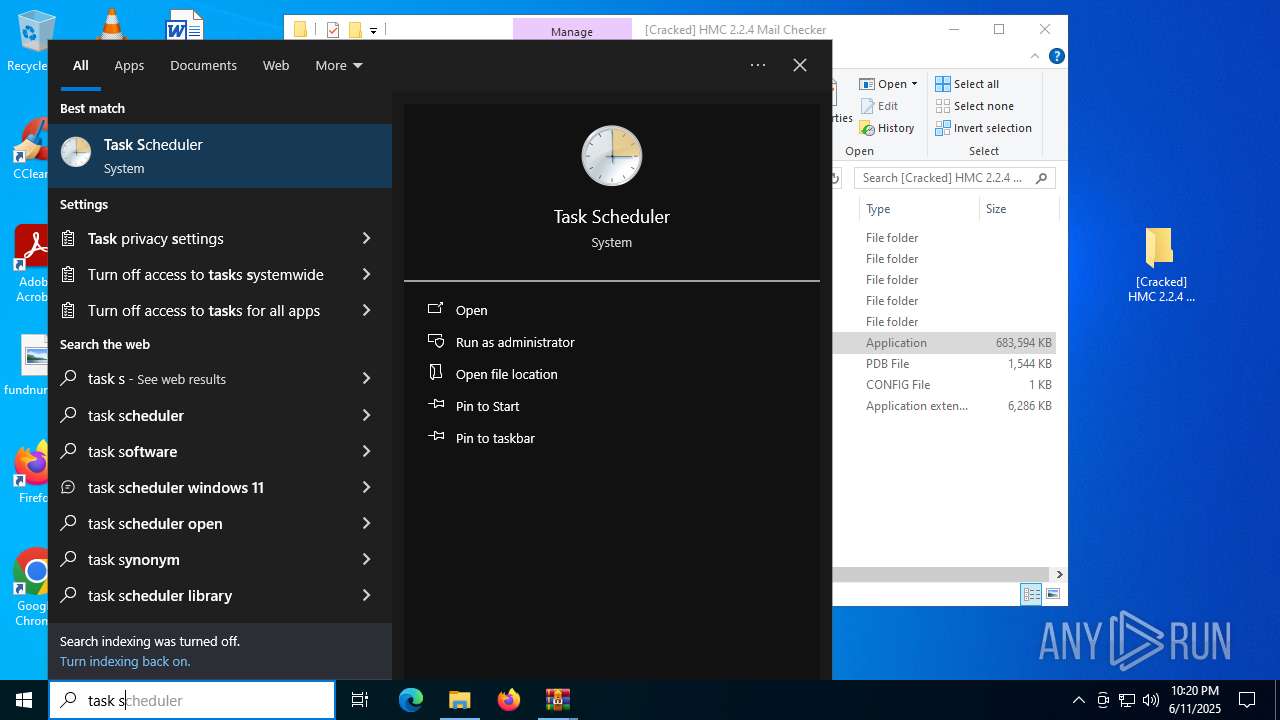
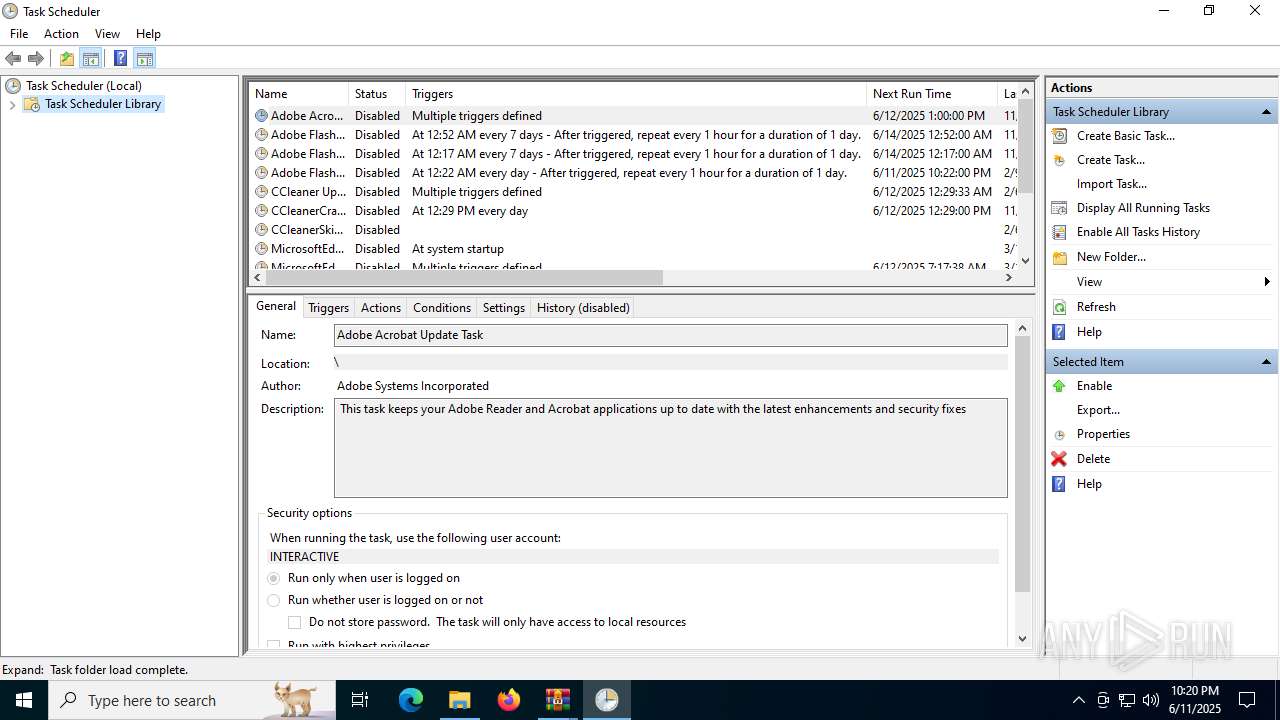
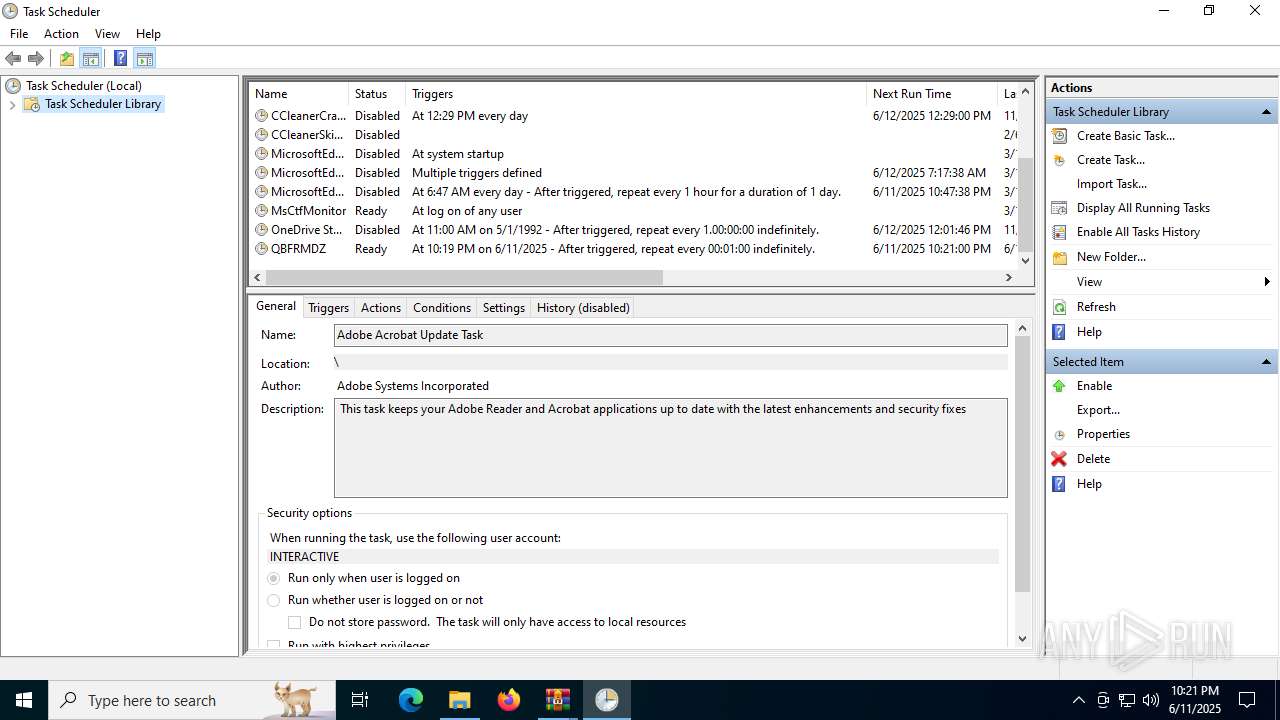
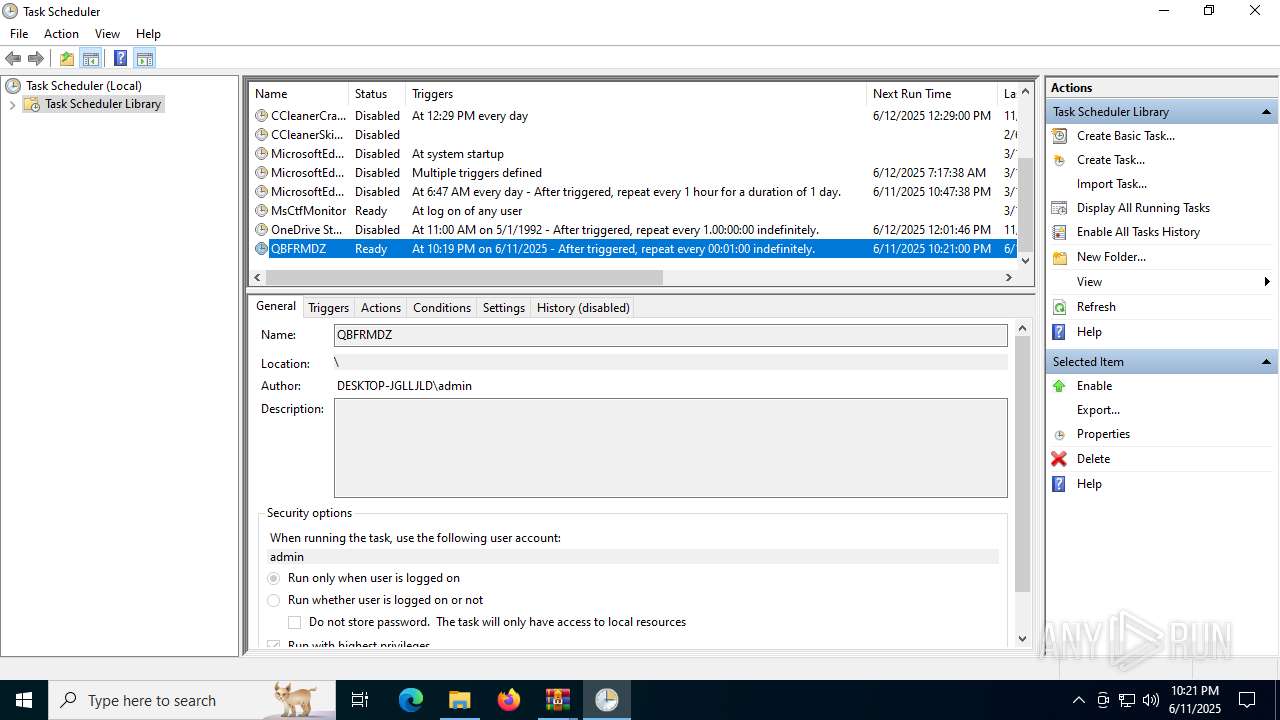
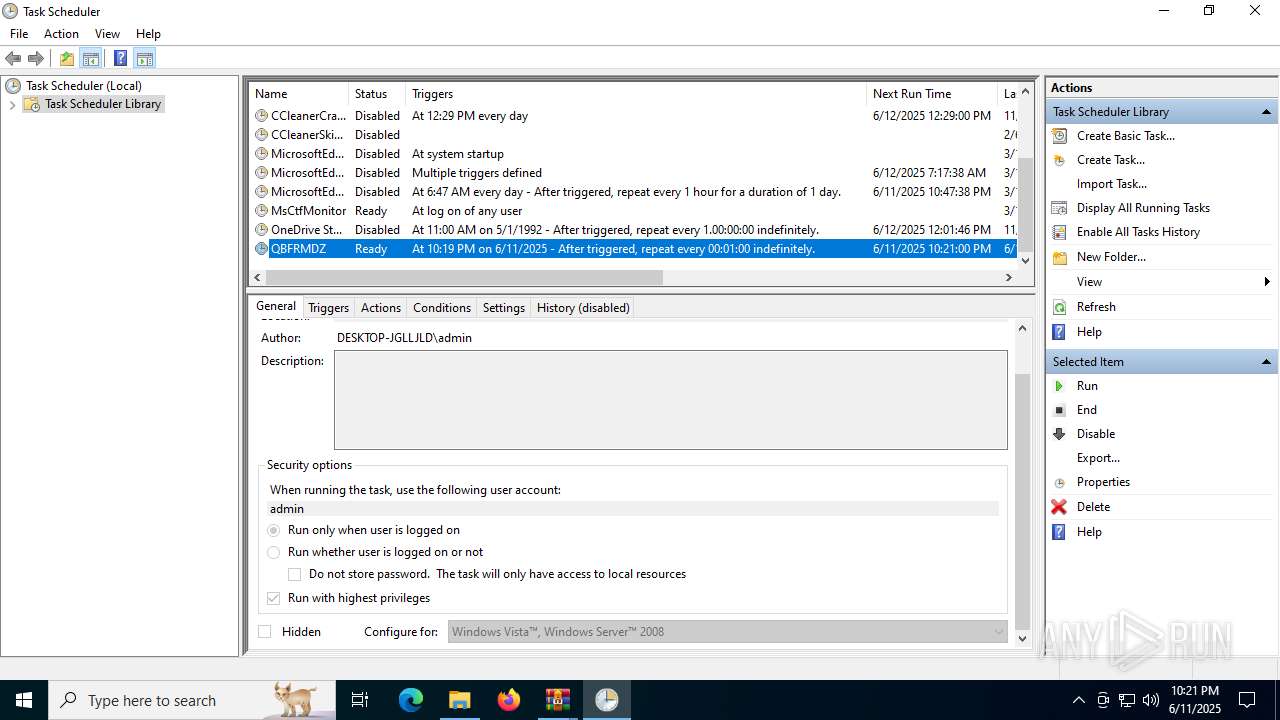
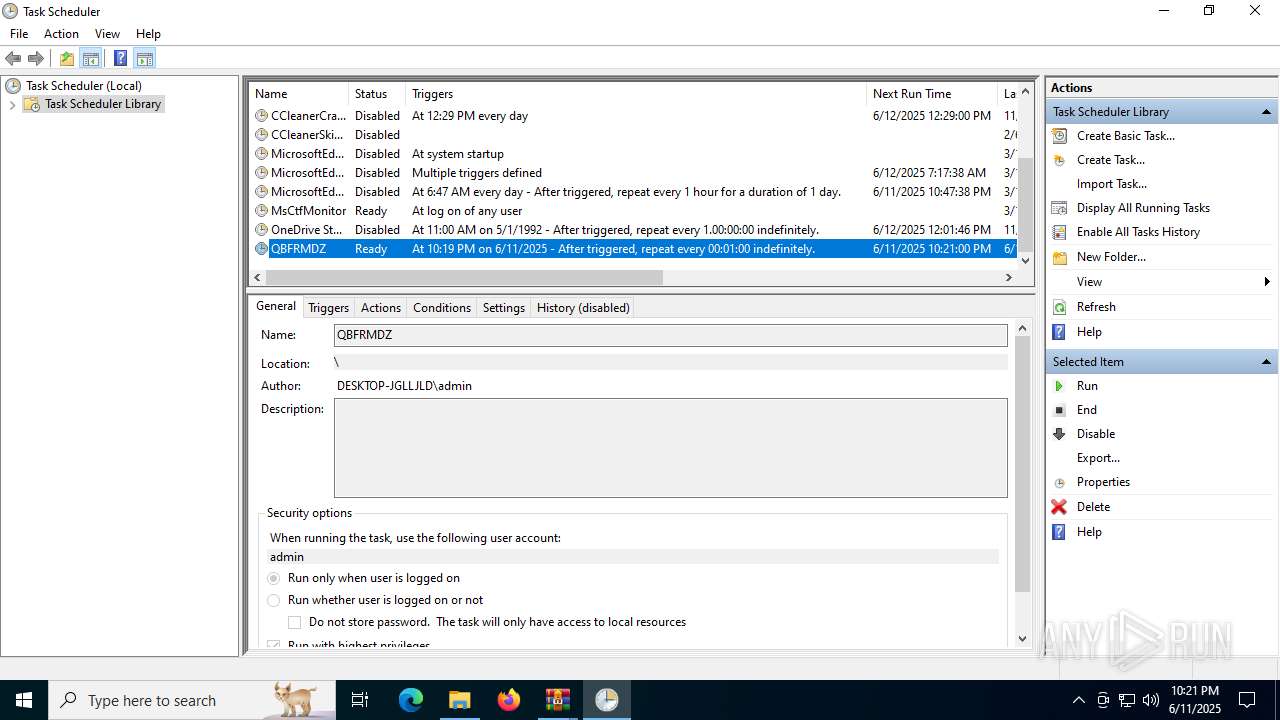
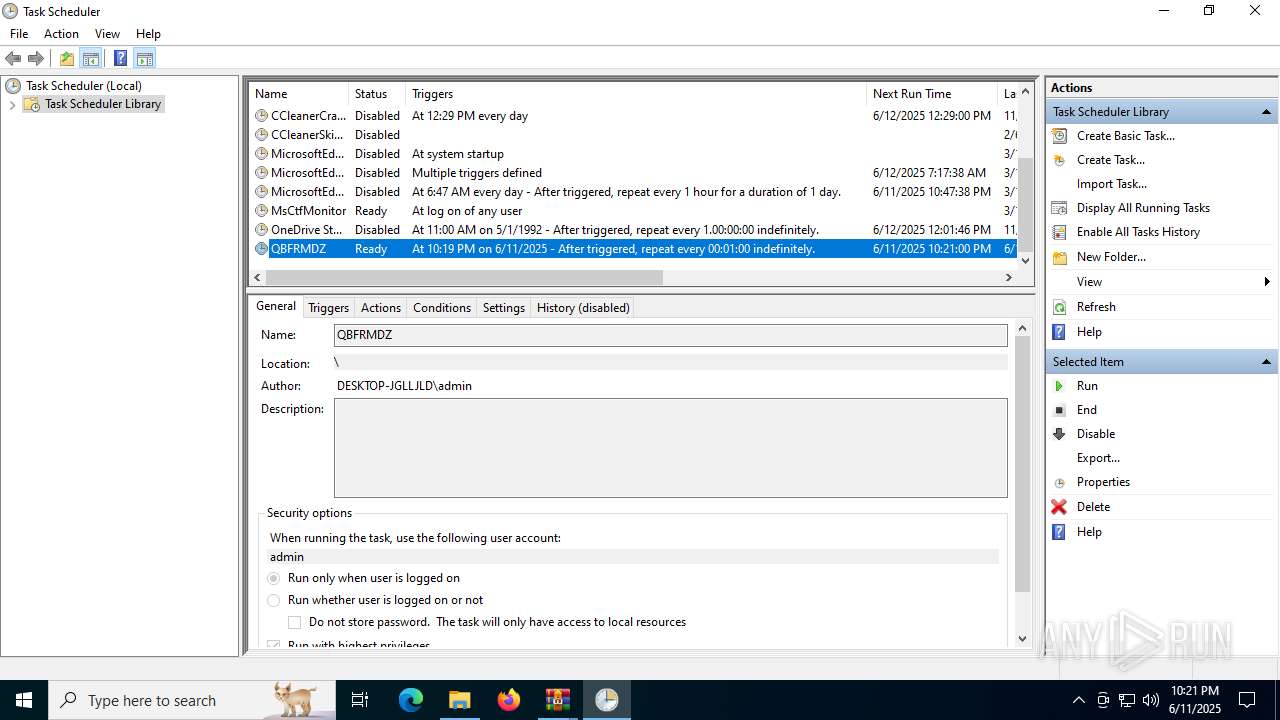
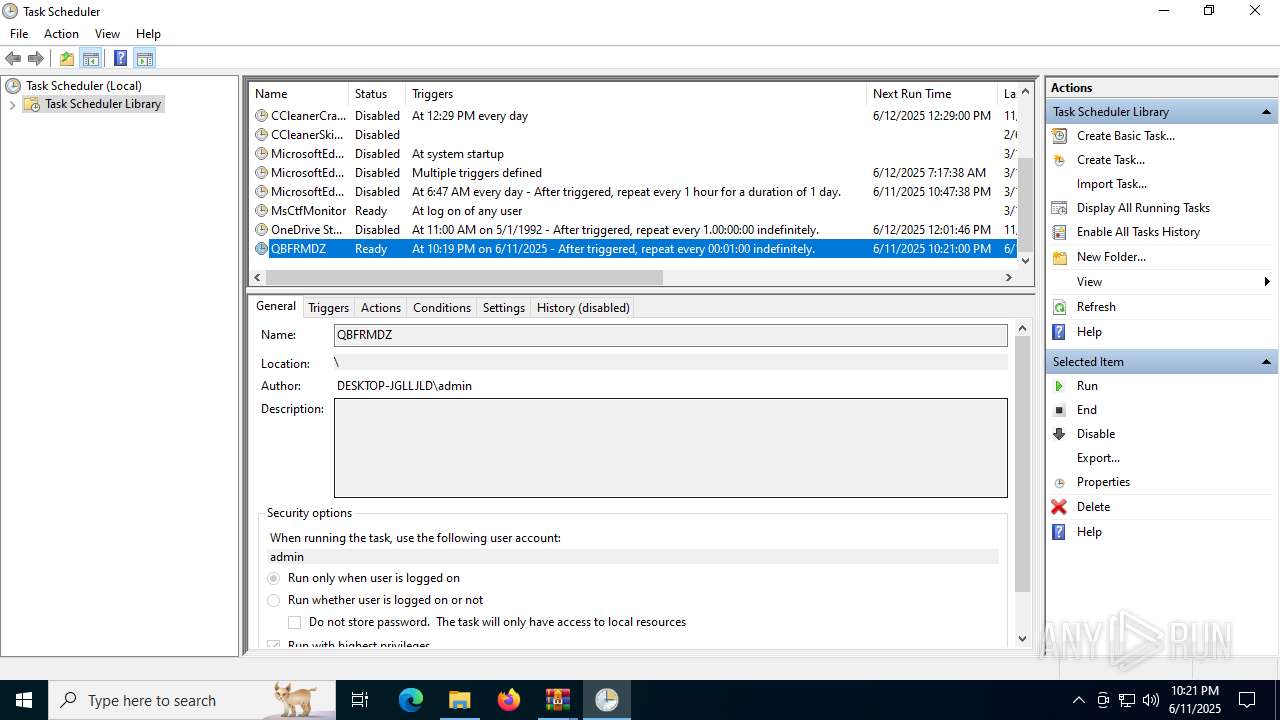
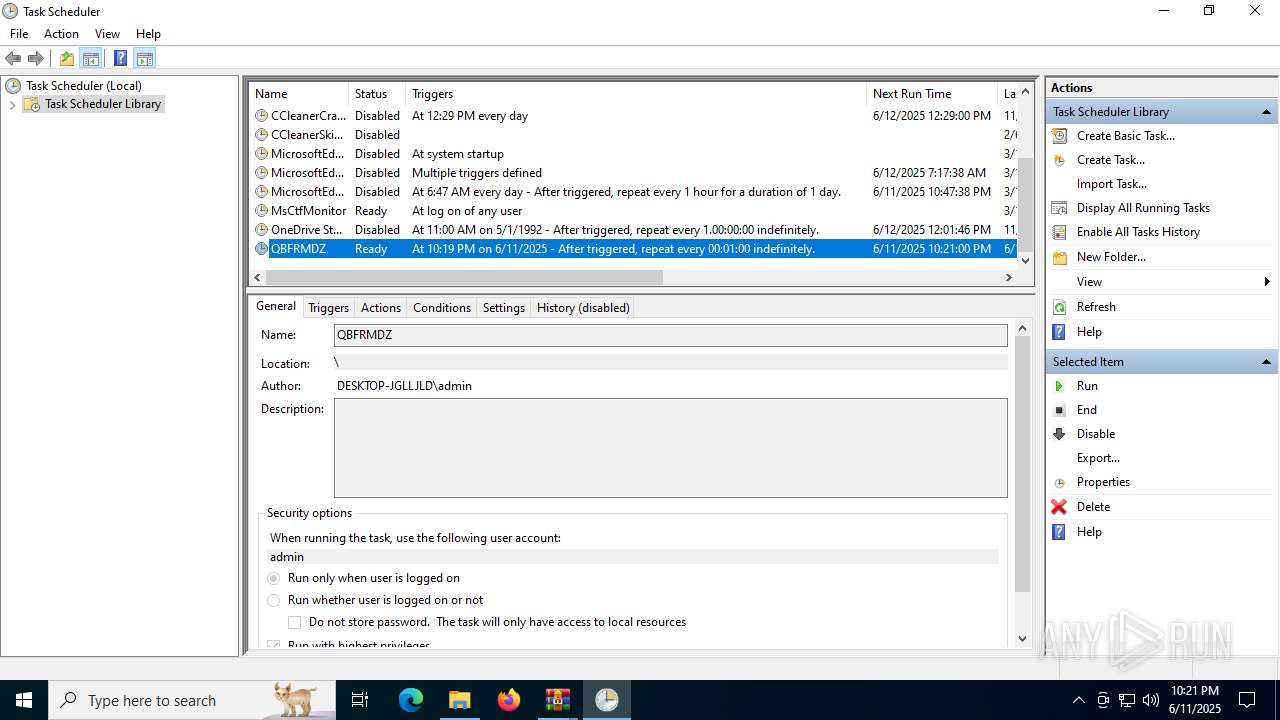
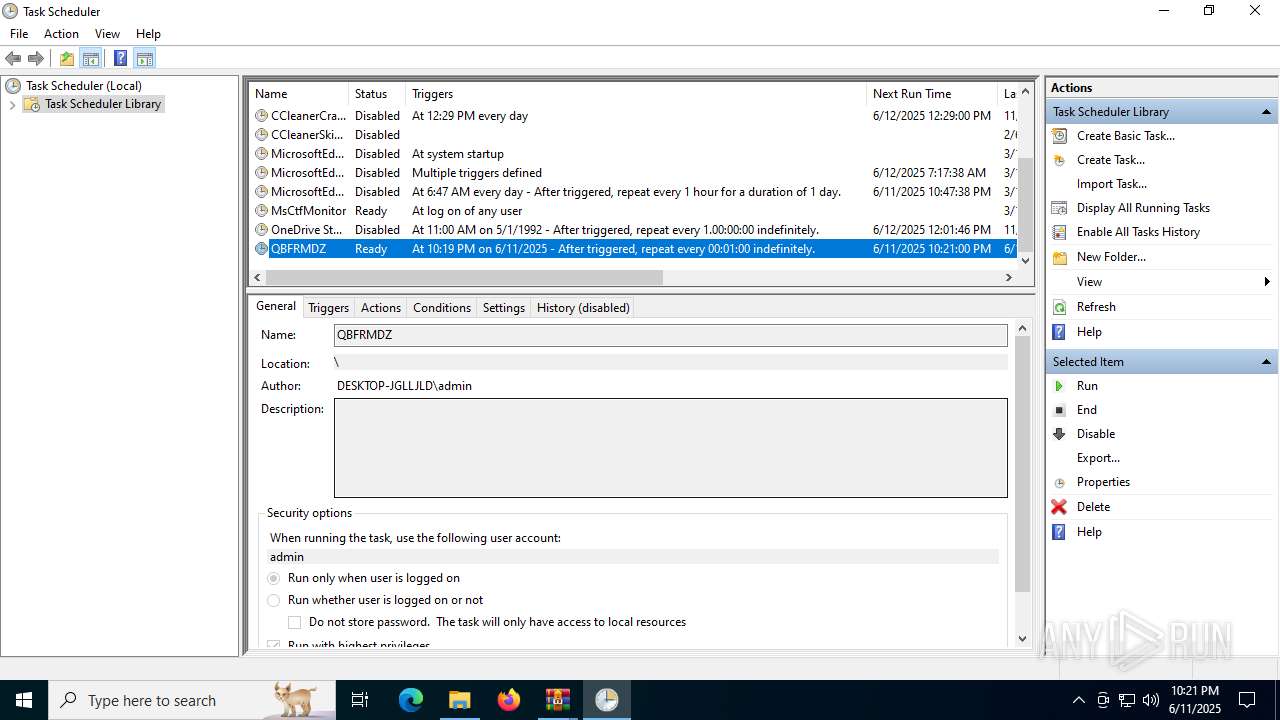
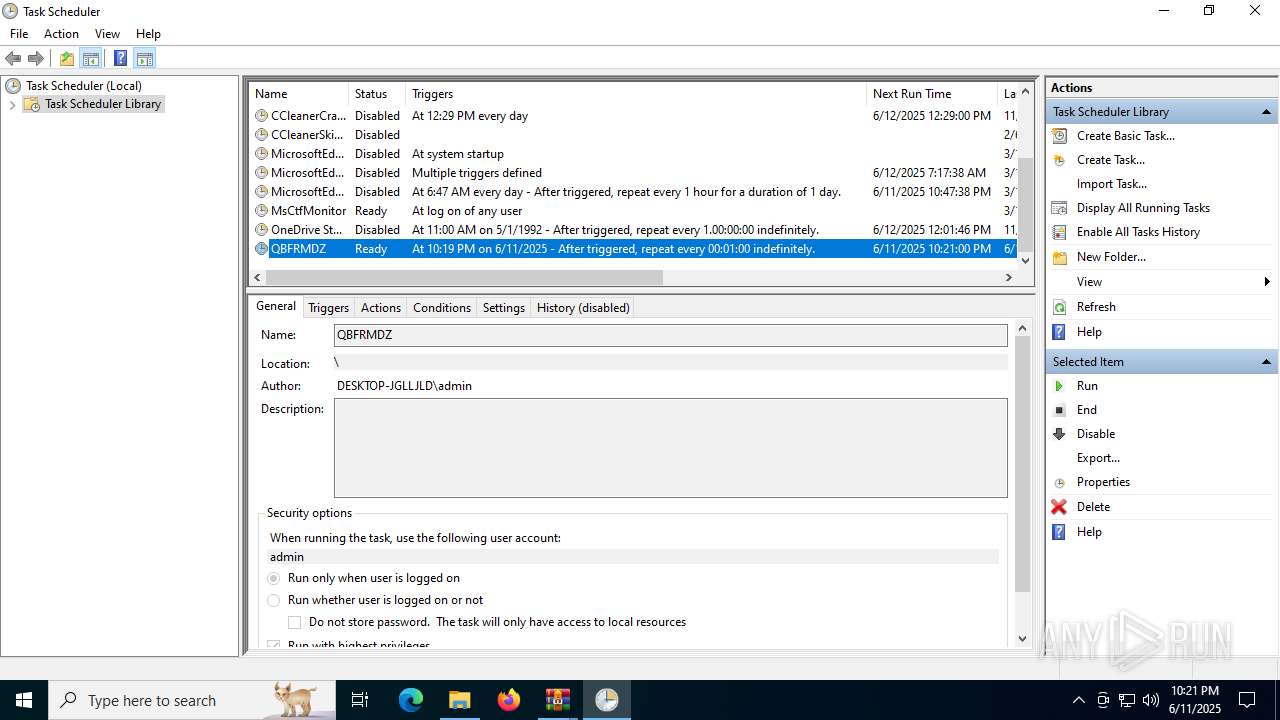
Uses Task Scheduler to run other applications
- QBFRMDZ.exe (PID: 3956)
SUSPICIOUS
Application launched itself
- WinRAR.exe (PID: 3752)
- HMC 2.2.4.exe (PID: 6264)
Reads security settings of Internet Explorer
- HMC 2.2.4.exe (PID: 6264)
- WinRAR.exe (PID: 3752)
- HMC 2.2.4.exe (PID: 3092)
- QBFRMDZ.exe (PID: 3956)
- QBFRMDZ.exe (PID: 6840)
Starts a Microsoft application from unusual location
- HMC 2.2.4.exe (PID: 3092)
- HMC 2.2.4.exe (PID: 6264)
Process drops legitimate windows executable
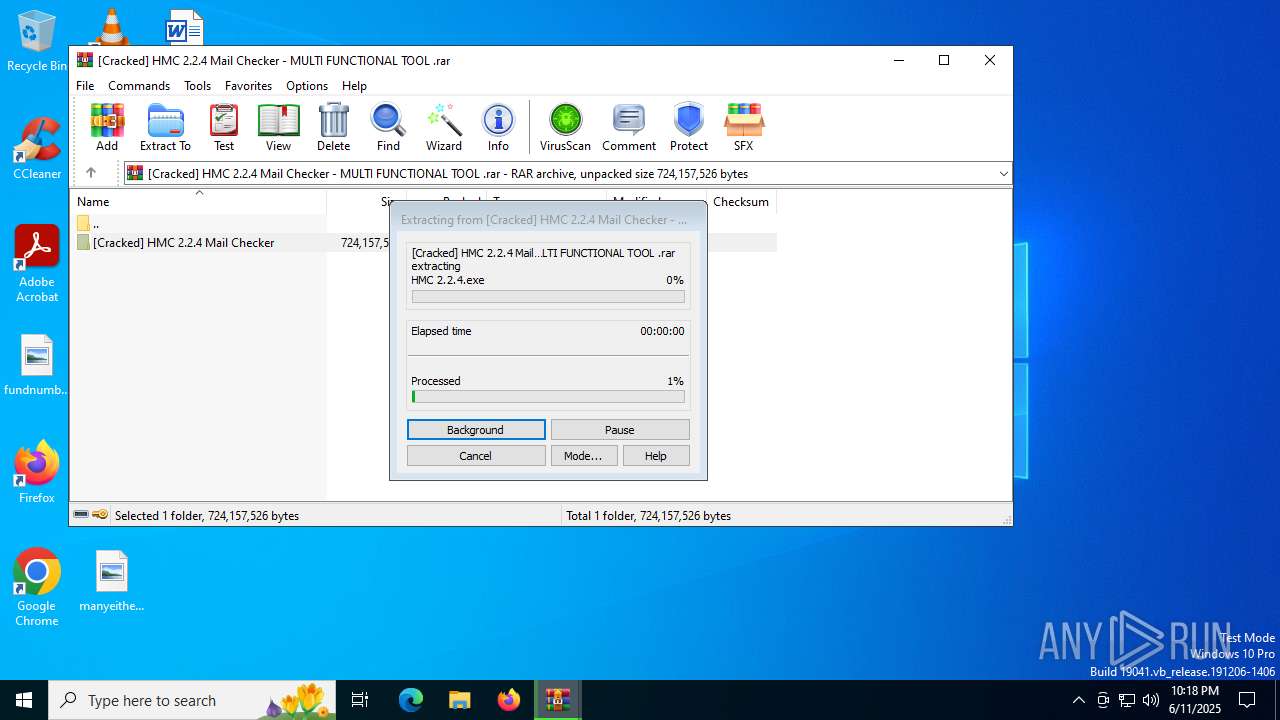
- WinRAR.exe (PID: 2628)
Starts POWERSHELL.EXE for commands execution
- HMC 2.2.4.exe (PID: 3092)
- QBFRMDZ.exe (PID: 3956)
- QBFRMDZ.exe (PID: 6840)
- QBFRMDZ.exe (PID: 4312)
- QBFRMDZ.exe (PID: 4380)
- QBFRMDZ.exe (PID: 5168)
Script adds exclusion path to Windows Defender
- HMC 2.2.4.exe (PID: 3092)
- QBFRMDZ.exe (PID: 6840)
- QBFRMDZ.exe (PID: 4380)
- QBFRMDZ.exe (PID: 5168)
- QBFRMDZ.exe (PID: 4312)
- QBFRMDZ.exe (PID: 3956)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5708)
Starts CMD.EXE for commands execution
- HMC 2.2.4.exe (PID: 3092)
Executing commands from a ".bat" file
- HMC 2.2.4.exe (PID: 3092)
Found regular expressions for crypto-addresses (YARA)
- QBFRMDZ.exe (PID: 3956)
The process executes via Task Scheduler
- QBFRMDZ.exe (PID: 6840)
- QBFRMDZ.exe (PID: 4312)
- QBFRMDZ.exe (PID: 4380)
- QBFRMDZ.exe (PID: 5168)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 2628)
Reads the computer name
- HMC 2.2.4.exe (PID: 6264)
- HMC 2.2.4.exe (PID: 3092)
- QBFRMDZ.exe (PID: 3956)
- QBFRMDZ.exe (PID: 6840)
Checks supported languages
- HMC 2.2.4.exe (PID: 6264)
- HMC 2.2.4.exe (PID: 3092)
- QBFRMDZ.exe (PID: 6840)
- QBFRMDZ.exe (PID: 3956)
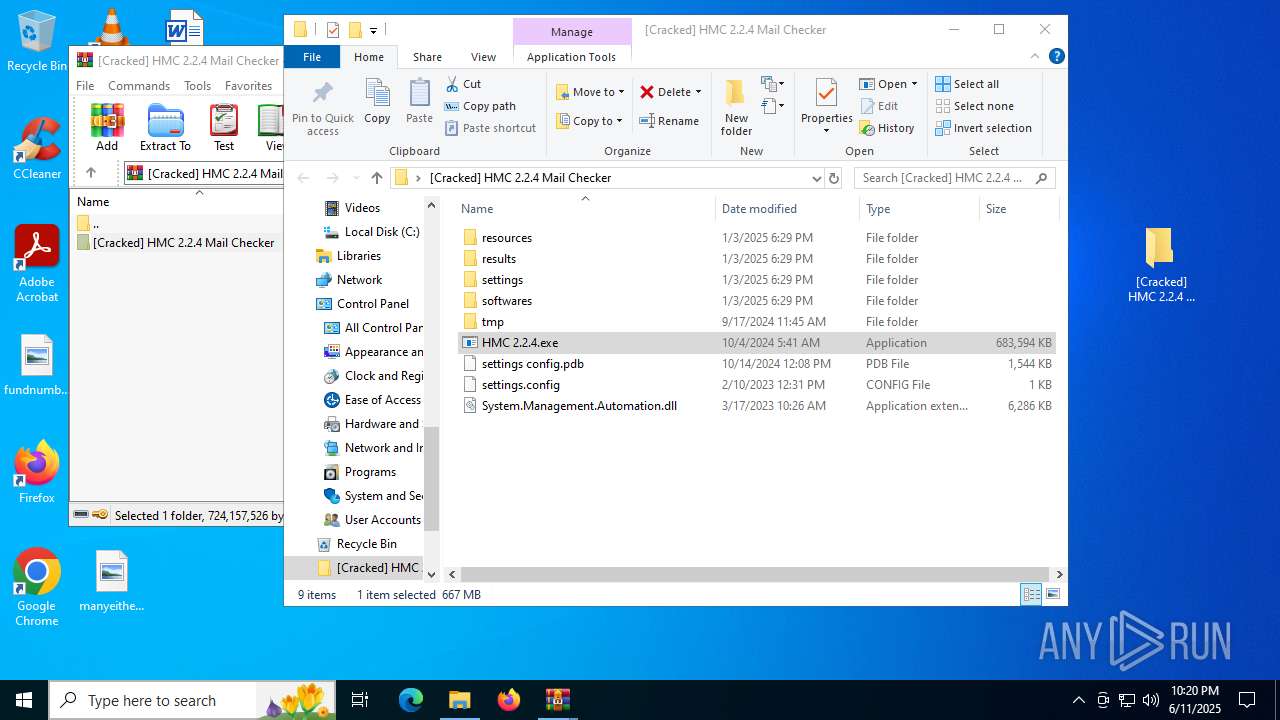
Manual execution by a user
- HMC 2.2.4.exe (PID: 6264)
- mmc.exe (PID: 3108)
- mmc.exe (PID: 5908)
Process checks computer location settings
- HMC 2.2.4.exe (PID: 6264)
- HMC 2.2.4.exe (PID: 3092)
- QBFRMDZ.exe (PID: 3956)
- QBFRMDZ.exe (PID: 6840)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2628)
Creates files in the program directory
- HMC 2.2.4.exe (PID: 3092)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6104)
- powershell.exe (PID: 5244)
- powershell.exe (PID: 432)
- powershell.exe (PID: 3628)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5244)
- powershell.exe (PID: 6104)
- powershell.exe (PID: 3628)
- powershell.exe (PID: 432)
Create files in a temporary directory
- HMC 2.2.4.exe (PID: 3092)
UPX packer has been detected
- QBFRMDZ.exe (PID: 3956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 45 |
| UncompressedSize: | 61 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | WinRAR Password123.txt |
Total processes
188
Monitored processes
42
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath 'C:\ProgramData' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | QBFRMDZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 504 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1192 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath 'C:\ProgramData' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | QBFRMDZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1800 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2216 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Roaming' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | QBFRMDZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2628 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa3752.12777\[Cracked] HMC 2.2.4 Mail Checker - MULTI FUNCTIONAL TOOL .rar" | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
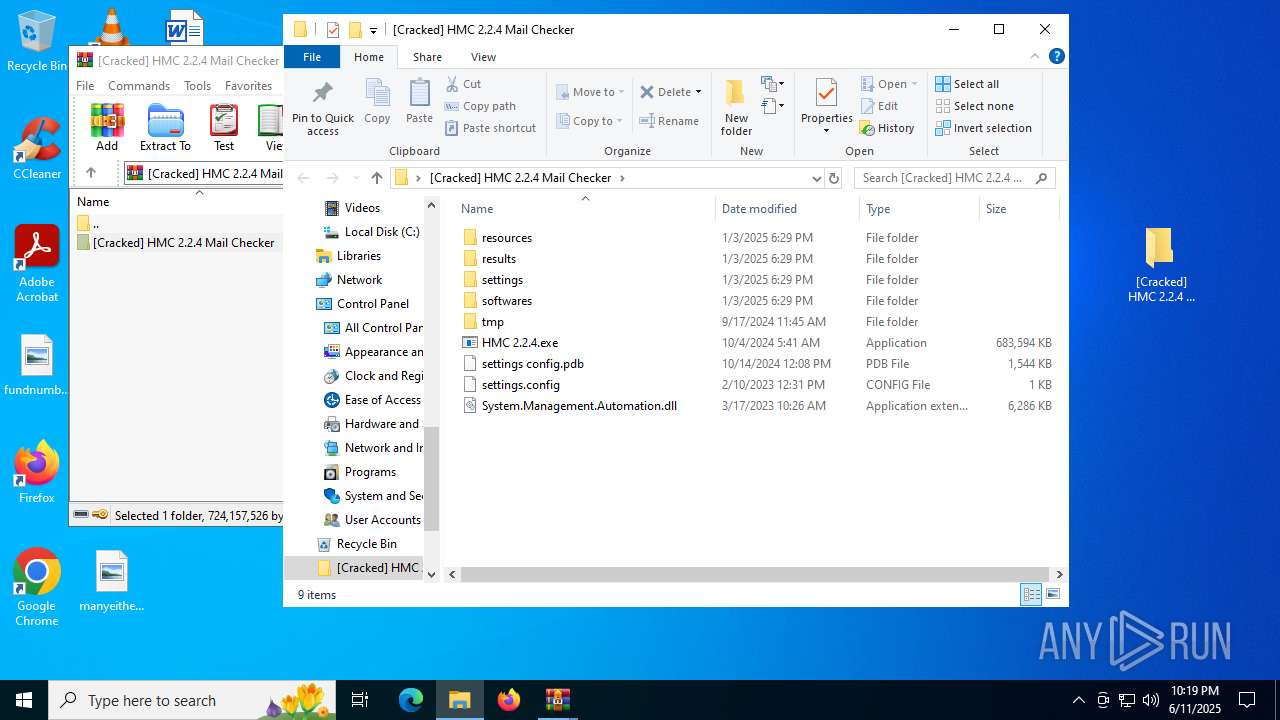
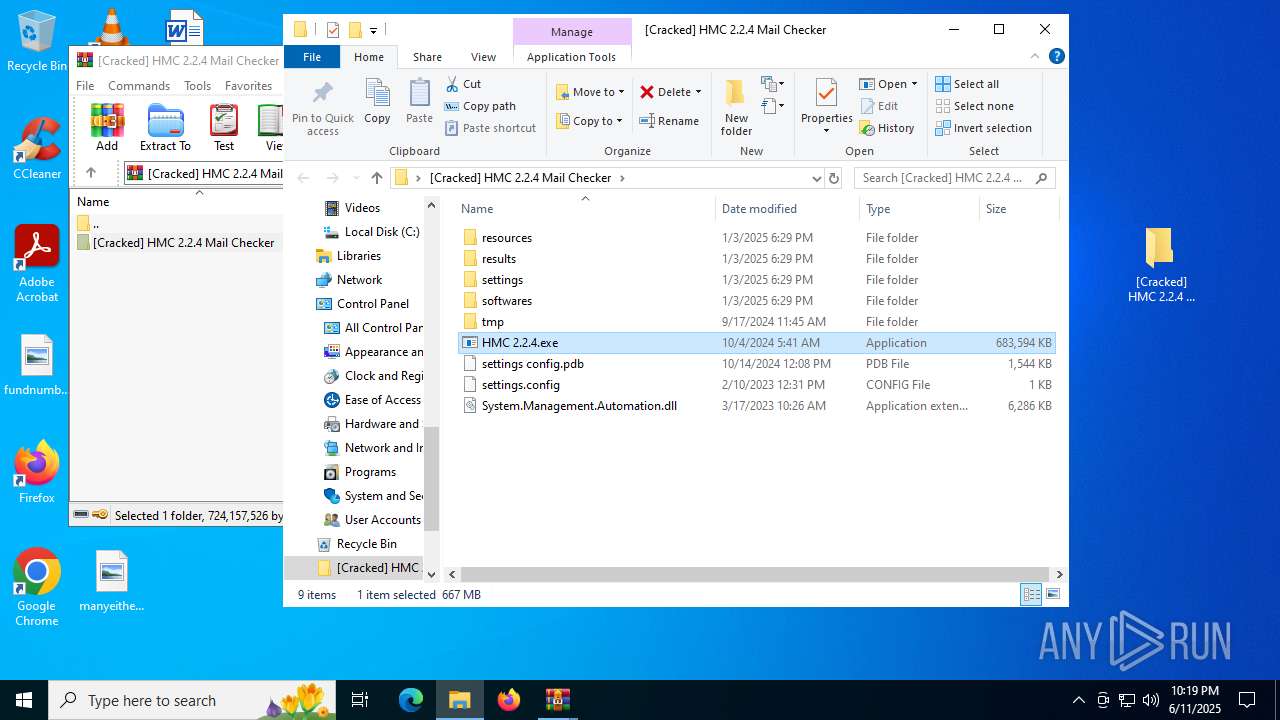
| 3092 | "C:\Users\admin\Desktop\[Cracked] HMC 2.2.4 Mail Checker\HMC 2.2.4.exe" | C:\Users\admin\Desktop\[Cracked] HMC 2.2.4 Mail Checker\HMC 2.2.4.exe | HMC 2.2.4.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Logon Application Exit code: 0 Version: 10.0.17134.1 Modules
| |||||||||||||||
| 3108 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3388 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Roaming' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | QBFRMDZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
69 744
Read events
69 725
Write events
19
Delete events
0
Modification events
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\[Cracked] HMC 2.2.4 Mail Checker - MULTI FUNCTIONAL TOOL .rar | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
Executable files
8
Suspicious files
6
Text files
133
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3752.12777\[Cracked] HMC 2.2.4 Mail Checker - MULTI FUNCTIONAL TOOL .rar | — | |
MD5:— | SHA256:— | |||
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2628.13294\[Cracked] HMC 2.2.4 Mail Checker\HMC 2.2.4.exe | — | |
MD5:— | SHA256:— | |||
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2628.13294\[Cracked] HMC 2.2.4 Mail Checker\resources\10_templates\ua.txt | text | |
MD5:03E7FC279AFAA4231ADF9F4ECD1D6B1A | SHA256:7BC5FF849935D69DC90F0EA4ECB74A0A1778D04C68D3A85D32FC601A79883F25 | |||
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2628.13294\[Cracked] HMC 2.2.4 Mail Checker\resources\10_templates\kz.txt | text | |
MD5:A6AF90867F8FB74E8CF1F9C3AAF97AC9 | SHA256:E99B21943B059EB0D651577C52D0EED7A084C2CBE2A353618FD0F0589D860DC9 | |||
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2628.13294\[Cracked] HMC 2.2.4 Mail Checker\resources\10_templates\by.txt | text | |
MD5:69094BEC76456C12076CB5858B9F2DC3 | SHA256:9D25B699B50FF76CA7A403BCD600DF2F87A2B8FBB91BF77CF5E3DC86DD5C1F4F | |||
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2628.13294\[Cracked] HMC 2.2.4 Mail Checker\resources\10_templates\usa_alaska.txt | text | |
MD5:77369E37B2AA1404F416275183AB055F | SHA256:4332CD76590D0EFDBD8D067ACF531546DA2BA0A67C538440E7DEFEDBEA48D1DC | |||
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2628.13294\[Cracked] HMC 2.2.4 Mail Checker\resources\10_templates\usa_arizona.txt | text | |
MD5:EC3A647F8AF9553BF83355C98FC4331D | SHA256:B12CA9F390DA8FAF62B5F2A3D9127DA77AFE8A94D105CBAB2B744F9F6C13A04C | |||
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2628.13294\[Cracked] HMC 2.2.4 Mail Checker\resources\10_templates\usa_colorado.txt | text | |
MD5:60BCAA3CD399C7DA6F9224F1C151A546 | SHA256:67A714BF7FF555E5F940710C680549CB1D5996D2DA1FC941EF35614E348AC436 | |||
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2628.13294\[Cracked] HMC 2.2.4 Mail Checker\resources\10_templates\usa_alabama.txt | text | |
MD5:35B87BE39F60FDD25A5472E238176E43 | SHA256:D545A6A27097C3FC8B4343CA091CAEDFB124012798CF1FDB4F4FD513E96D02CC | |||
| 2628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2628.13294\[Cracked] HMC 2.2.4 Mail Checker\resources\10_templates\usa_delaware.txt | text | |
MD5:996009F2374006606F4C0B0FDA878AF1 | SHA256:EE47968EC53BBE68EAF52703D6CAB88D710F59DE77EDF4826B4CCAAD0AED36AB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
40
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 868 b | whitelisted |
5904 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | DE | binary | 471 b | whitelisted |
5284 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | QA | binary | 408 b | whitelisted |
5284 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | QA | binary | 420 b | whitelisted |
2596 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
2940 | svchost.exe | GET | 200 | 72.246.169.163:80 | http://x1.c.lencr.org/ | DE | binary | 734 b | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 313 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4880 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.48.23.177:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5284 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|