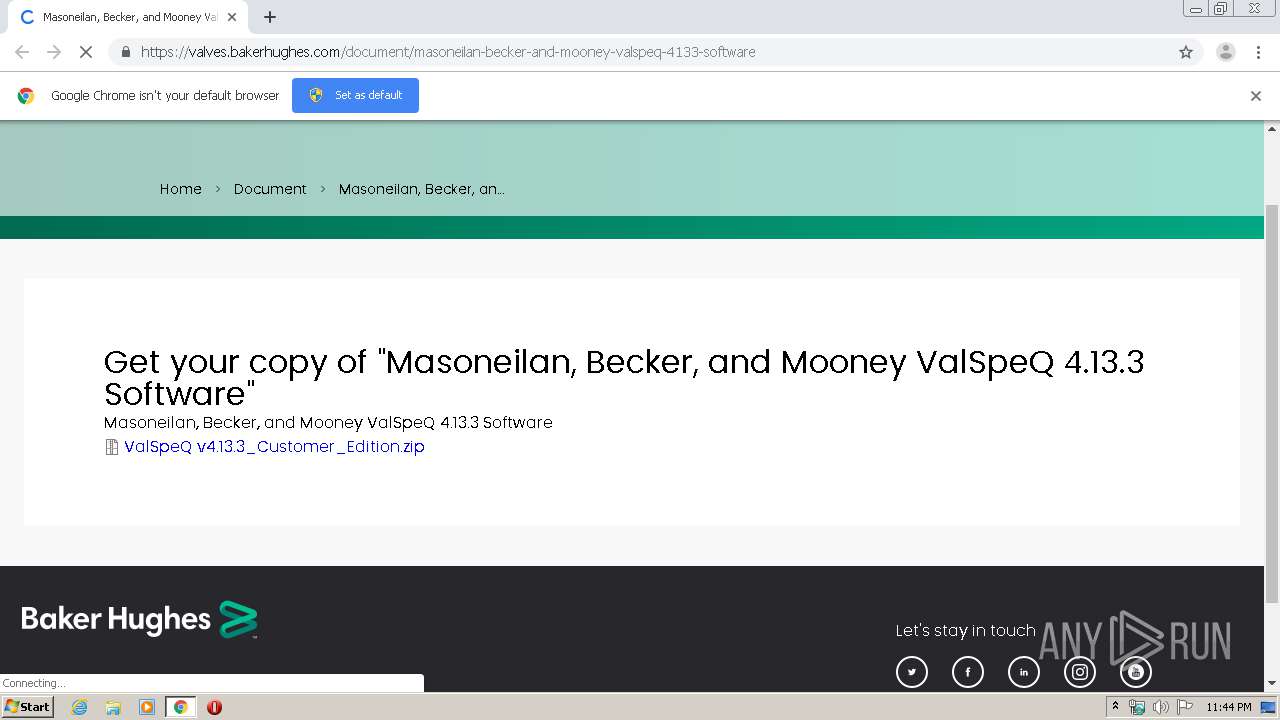
| URL: | https://valves.bakerhughes.com/document/masoneilan-becker-and-mooney-valspeq-4133-software |
| Full analysis: | https://app.any.run/tasks/2e7de9a1-8485-4d4b-8917-3a6a8f1663c3 |
| Verdict: | Malicious activity |
| Analysis date: | March 17, 2020, 23:44:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3FE52C422773919EE56CC64CA50E645D |
| SHA1: | BB9B92C7182E95623A2C8C5B36C41442453FE574 |
| SHA256: | 4E1B35CB696EA8FA914D4C605C79D8AE30EE250CE8AA82F5A691064AC9A20B2E |
| SSDEEP: | 3:N8+MMHeCWZxKJRaiIogANr1x:2hCeVZMJxNz |
MALICIOUS
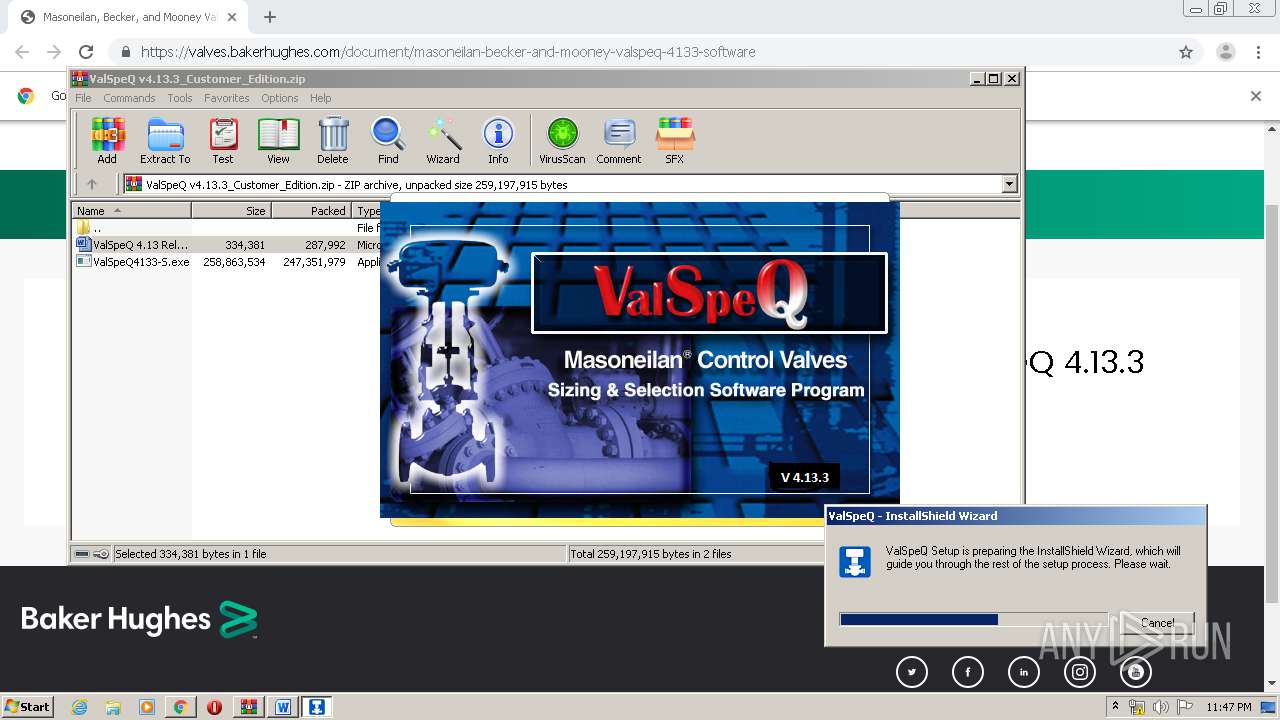
Loads dropped or rewritten executable
- ValSpeQ4133-S.exe (PID: 3544)
- DotNetInstaller.exe (PID: 1520)
- DotNetInstaller.exe (PID: 1508)
- DotNetInstaller.exe (PID: 3444)
- DotNetInstaller.exe (PID: 2660)
- DotNetInstaller.exe (PID: 392)
- DotNetInstaller.exe (PID: 552)
- DotNetInstaller.exe (PID: 3988)
- DotNetInstaller.exe (PID: 3328)
- DotNetInstaller.exe (PID: 3548)
- DotNetInstaller.exe (PID: 3816)
- DotNetInstaller.exe (PID: 1696)
- DotNetInstaller.exe (PID: 1900)
- DotNetInstaller.exe (PID: 3332)
- DotNetInstaller.exe (PID: 608)
- DotNetInstaller.exe (PID: 2568)
- DotNetInstaller.exe (PID: 2924)
- DotNetInstaller.exe (PID: 3064)
- DotNetInstaller.exe (PID: 3732)
- DotNetInstaller.exe (PID: 1740)
- DotNetInstaller.exe (PID: 2724)
- DotNetInstaller.exe (PID: 3732)
- DotNetInstaller.exe (PID: 2336)
- DotNetInstaller.exe (PID: 1168)
- DotNetInstaller.exe (PID: 3808)
- DotNetInstaller.exe (PID: 3268)
- DotNetInstaller.exe (PID: 3852)
- DotNetInstaller.exe (PID: 2372)
- DotNetInstaller.exe (PID: 2876)
- DotNetInstaller.exe (PID: 3360)
- DotNetInstaller.exe (PID: 3004)
- DotNetInstaller.exe (PID: 3024)
Changes settings of System certificates
- DotNetInstaller.exe (PID: 1508)
- DotNetInstaller.exe (PID: 552)
- ValSpeQ4133-S.exe (PID: 3544)
Application was dropped or rewritten from another process
- DotNetInstaller.exe (PID: 2660)
- DotNetInstaller.exe (PID: 1520)
- DotNetInstaller.exe (PID: 552)
- DotNetInstaller.exe (PID: 1508)
- DotNetInstaller.exe (PID: 3444)
- DotNetInstaller.exe (PID: 3676)
- DotNetInstaller.exe (PID: 392)
- DotNetInstaller.exe (PID: 2960)
- DotNetInstaller.exe (PID: 3816)
- DotNetInstaller.exe (PID: 1544)
- DotNetInstaller.exe (PID: 3360)
- DotNetInstaller.exe (PID: 2960)
- DotNetInstaller.exe (PID: 3024)
- DotNetInstaller.exe (PID: 1900)
- DotNetInstaller.exe (PID: 608)
- DotNetInstaller.exe (PID: 3988)
- DotNetInstaller.exe (PID: 2092)
- DotNetInstaller.exe (PID: 3548)
- DotNetInstaller.exe (PID: 3328)
- DotNetInstaller.exe (PID: 3196)
- DotNetInstaller.exe (PID: 1696)
- DotNetInstaller.exe (PID: 3004)
- DotNetInstaller.exe (PID: 2848)
- DotNetInstaller.exe (PID: 944)
- DotNetInstaller.exe (PID: 3332)
- DotNetInstaller.exe (PID: 404)
- DotNetInstaller.exe (PID: 3064)
- DotNetInstaller.exe (PID: 2568)
- DotNetInstaller.exe (PID: 2924)
- DotNetInstaller.exe (PID: 1740)
- DotNetInstaller.exe (PID: 2276)
- DotNetInstaller.exe (PID: 2724)
- DotNetInstaller.exe (PID: 1696)
- DotNetInstaller.exe (PID: 3700)
- DotNetInstaller.exe (PID: 2336)
- DotNetInstaller.exe (PID: 1168)
- DotNetInstaller.exe (PID: 3732)
- DotNetInstaller.exe (PID: 3828)
- DotNetInstaller.exe (PID: 3268)
- DotNetInstaller.exe (PID: 3852)
- DotNetInstaller.exe (PID: 3808)
- DotNetInstaller.exe (PID: 1672)
- DotNetInstaller.exe (PID: 3732)
- DotNetInstaller.exe (PID: 2876)
- DotNetInstaller.exe (PID: 2996)
- DotNetInstaller.exe (PID: 3768)
- DotNetInstaller.exe (PID: 1348)
- DotNetInstaller.exe (PID: 3260)
- DotNetInstaller.exe (PID: 3268)
- DotNetInstaller.exe (PID: 2372)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 2896)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1720)
Reads Windows owner or organization settings
- ValSpeQ4133-S.exe (PID: 3544)
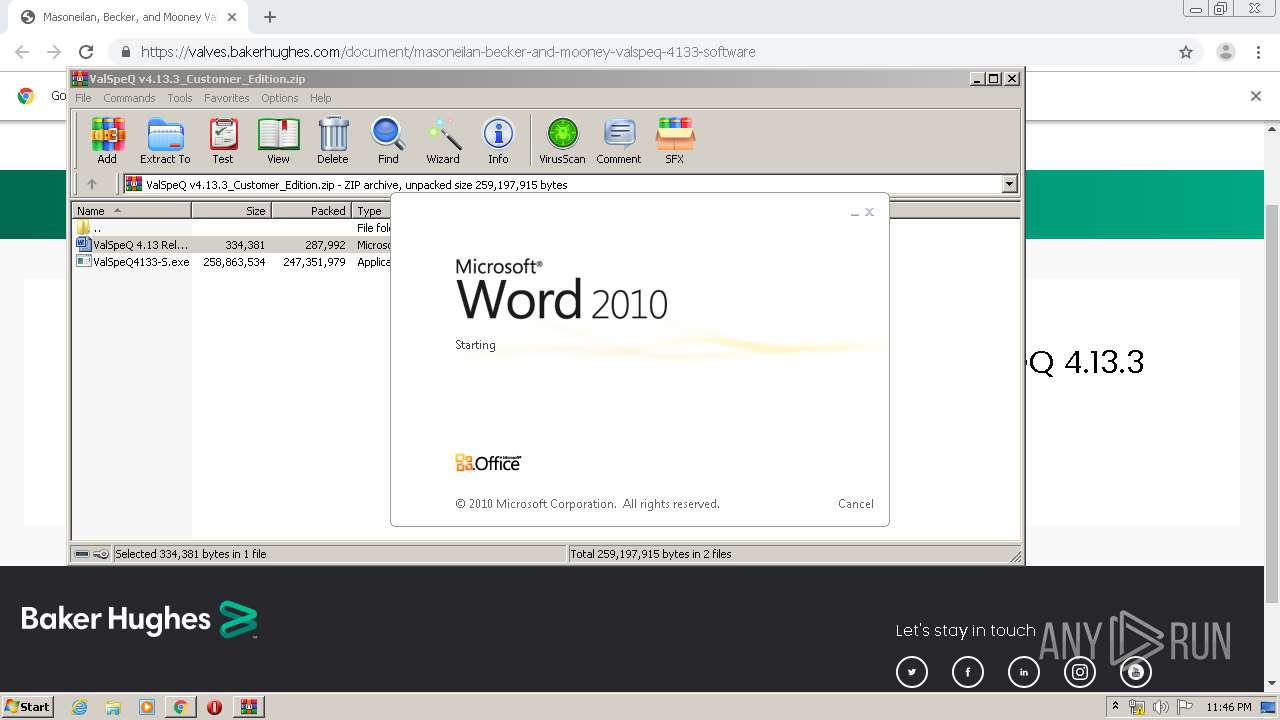
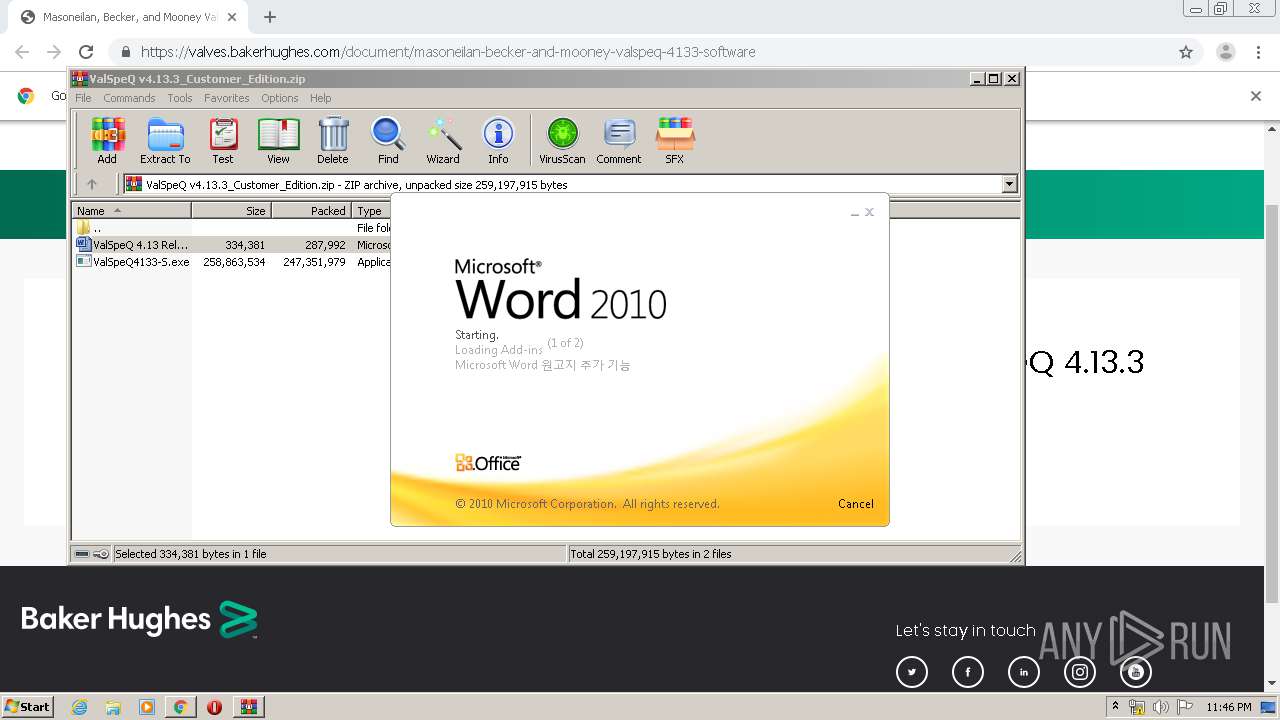
Starts Microsoft Office Application
- WinRAR.exe (PID: 3724)
- WINWORD.EXE (PID: 2896)
Reads the Windows organization settings
- ValSpeQ4133-S.exe (PID: 3544)
Reads Environment values
- ValSpeQ4133-S.exe (PID: 3544)
Executed as Windows Service
- vssvc.exe (PID: 1232)
Modifies the open verb of a shell class
- ValSpeQ4133-S.exe (PID: 3544)
Searches for installed software
- ValSpeQ4133-S.exe (PID: 3544)
Creates files in the Windows directory
- ValSpeQ4133-S.exe (PID: 3544)
- msiexec.exe (PID: 2424)
Adds / modifies Windows certificates
- DotNetInstaller.exe (PID: 1508)
- DotNetInstaller.exe (PID: 552)
- ValSpeQ4133-S.exe (PID: 3544)
Executable content was dropped or overwritten
- ValSpeQ4133-S.exe (PID: 3544)
- msiexec.exe (PID: 2424)
Removes files from Windows directory
- ValSpeQ4133-S.exe (PID: 3544)
- msiexec.exe (PID: 2424)
Creates files in the program directory
- ValSpeQ4133-S.exe (PID: 3544)
Creates COM task schedule object
- DotNetInstaller.exe (PID: 1740)
- DotNetInstaller.exe (PID: 2336)
- DotNetInstaller.exe (PID: 1168)
- DotNetInstaller.exe (PID: 3808)
- DotNetInstaller.exe (PID: 3768)
- DotNetInstaller.exe (PID: 3732)
- ValSpeQ4133-S.exe (PID: 3544)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3840)
- ValSpeQ4133-S.exe (PID: 3544)
Reads Internet Cache Settings
- chrome.exe (PID: 1720)
Reads the hosts file
- chrome.exe (PID: 1720)
- chrome.exe (PID: 3840)
Application launched itself
- chrome.exe (PID: 1720)
- msiexec.exe (PID: 2424)
Creates files in the user directory
- WINWORD.EXE (PID: 2896)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2636)
- WINWORD.EXE (PID: 2896)
Dropped object may contain Bitcoin addresses
- ValSpeQ4133-S.exe (PID: 3544)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1232)
Creates a software uninstall entry
- msiexec.exe (PID: 2424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
184
Monitored processes
86
Malicious processes
23
Suspicious processes
13
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Users\admin\AppData\Local\Temp\{8A8743F7-962D-4596-A9A3-5262AB25CE6A}\DotNetInstaller.exe" "C:\Program Files\GE-FPT\ValSpeQ\C1.Win.C1Input.2.dll" | C:\Users\admin\AppData\Local\Temp\{8A8743F7-962D-4596-A9A3-5262AB25CE6A}\DotNetInstaller.exe | — | ValSpeQ4133-S.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: DotNetInstaller Exit code: 0 Version: 20.0.0.376 Modules
| |||||||||||||||
| 404 | "C:\Users\admin\AppData\Local\Temp\{8A8743F7-962D-4596-A9A3-5262AB25CE6A}\DotNetInstaller.exe" "C:\Program Files\GE-FPT\ValSpeQ\vxg.dll" | C:\Users\admin\AppData\Local\Temp\{8A8743F7-962D-4596-A9A3-5262AB25CE6A}\DotNetInstaller.exe | — | ValSpeQ4133-S.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: DotNetInstaller Exit code: 0 Version: 20.0.0.376 Modules
| |||||||||||||||
| 552 | "C:\Users\admin\AppData\Local\Temp\{8A8743F7-962D-4596-A9A3-5262AB25CE6A}\DotNetInstaller.exe" "C:\Program Files\GE-FPT\ValSpeQ\C1.Win.C1FlexGrid.2.dll" | C:\Users\admin\AppData\Local\Temp\{8A8743F7-962D-4596-A9A3-5262AB25CE6A}\DotNetInstaller.exe | — | ValSpeQ4133-S.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: DotNetInstaller Exit code: 0 Version: 20.0.0.376 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2952 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 608 | "C:\Users\admin\AppData\Local\Temp\{8A8743F7-962D-4596-A9A3-5262AB25CE6A}\DotNetInstaller.exe" "C:\Program Files\GE-FPT\ValSpeQ\VQRCodeGen.dll" | C:\Users\admin\AppData\Local\Temp\{8A8743F7-962D-4596-A9A3-5262AB25CE6A}\DotNetInstaller.exe | — | ValSpeQ4133-S.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: DotNetInstaller Exit code: 0 Version: 20.0.0.376 Modules
| |||||||||||||||
| 944 | "C:\Users\admin\AppData\Local\Temp\{8A8743F7-962D-4596-A9A3-5262AB25CE6A}\DotNetInstaller.exe" "C:\Program Files\GE-FPT\ValSpeQ\Vreports.pdb" | C:\Users\admin\AppData\Local\Temp\{8A8743F7-962D-4596-A9A3-5262AB25CE6A}\DotNetInstaller.exe | — | ValSpeQ4133-S.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: DotNetInstaller Exit code: 0 Version: 20.0.0.376 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,636083941521690653,2799474172643377514,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13072028745657413283 --mojo-platform-channel-handle=4700 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1168 | "C:\Users\admin\AppData\Local\Temp\{8A8743F7-962D-4596-A9A3-5262AB25CE6A}\DotNetInstaller.exe" "C:\Program Files\GE-FPT\ValSpeQ\Lib\MNLead.dll" -r | C:\Users\admin\AppData\Local\Temp\{8A8743F7-962D-4596-A9A3-5262AB25CE6A}\DotNetInstaller.exe | — | ValSpeQ4133-S.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: DotNetInstaller Exit code: 0 Version: 20.0.0.376 Modules
| |||||||||||||||
| 1232 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1348 | "C:\Users\admin\AppData\Local\Temp\{8A8743F7-962D-4596-A9A3-5262AB25CE6A}\DotNetInstaller.exe" "C:\Program Files\GE-FPT\ValSpeQ\Lib\ValSys.tlb" -r | C:\Users\admin\AppData\Local\Temp\{8A8743F7-962D-4596-A9A3-5262AB25CE6A}\DotNetInstaller.exe | — | ValSpeQ4133-S.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: DotNetInstaller Exit code: 0 Version: 20.0.0.376 Modules
| |||||||||||||||
Total events
8 394
Read events
4 067
Write events
4 212
Delete events
115
Modification events
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (604) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1720-13228962260246375 |
Value: 259 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
137
Suspicious files
92
Text files
336
Unknown types
56
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E7160D4-6B8.pma | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6c036650-cbef-43d3-8e4c-46634cee261d.tmp | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66ae7.TMP | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66ae7.TMP | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66cdb.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
81
DNS requests
48
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3840 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
3840 | chrome.exe | GET | 200 | 173.194.138.201:80 | http://r4---sn-aigzrn7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=185.192.69.22&mm=28&mn=sn-aigzrn7d&ms=nvh&mt=1584488596&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3840 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
3840 | chrome.exe | GET | 200 | 173.194.5.42:80 | http://r5---sn-aigzrn7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.192.69.22&mm=28&mn=sn-aigzrn7e&ms=nvh&mt=1584488596&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3840 | chrome.exe | 45.60.13.171:443 | valves.bakerhughes.com | Incapsula Inc | US | unknown |
3840 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 104.16.96.80:443 | app-e.marketo.com | Cloudflare Inc | US | shared |
3840 | chrome.exe | 172.217.22.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 104.111.236.174:443 | munchkin.marketo.net | Akamai International B.V. | NL | unknown |
3840 | chrome.exe | 172.217.18.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 172.217.22.14:443 | www.youtube.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 157.240.20.19:443 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
3840 | chrome.exe | 172.217.22.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
valves.bakerhughes.com |
| unknown |
accounts.google.com |
| shared |
app-e.marketo.com |
| whitelisted |
munchkin.marketo.net |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
400-zoj-998.mktoresp.com |
| suspicious |
www.youtube.com |
| whitelisted |