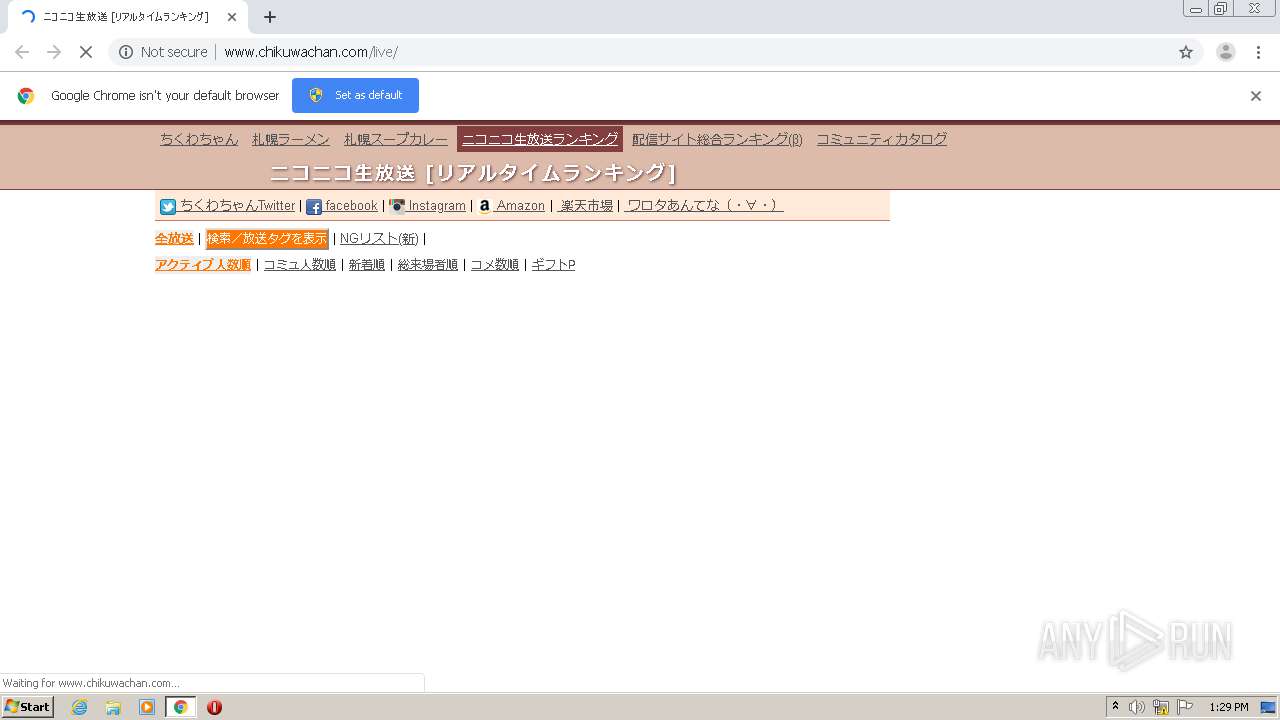
| URL: | http://www.chikuwachan.com/live |
| Full analysis: | https://app.any.run/tasks/9192055d-f19c-4f96-bf2e-05988836a4fb |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 12:29:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3F899D0ECB2A8B0E8475F9D500F257A0 |
| SHA1: | C591FDF6CABE552F5B64E2AAF68D38B1B6FDFC42 |
| SHA256: | 4E11D6F03015349EE15B233731F4D0C52824789DB652AA077EA79915576DDAFF |
| SSDEEP: | 3:N1KJS4f3abTKJMM:Cc4vabTKCM |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2116)
Reads the hosts file
- chrome.exe (PID: 856)
- chrome.exe (PID: 2116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
13
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,4880462932541664264,5189237460012092762,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=4851775438656515079 --mojo-platform-channel-handle=1588 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,4880462932541664264,5189237460012092762,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2143792026123540090 --mojo-platform-channel-handle=3472 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2092 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,4880462932541664264,5189237460012092762,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10060696314384427118 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.chikuwachan.com/live" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,4880462932541664264,5189237460012092762,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5745846230491670910 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2976 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,4880462932541664264,5189237460012092762,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=277989810343330338 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,4880462932541664264,5189237460012092762,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4972738797934881959 --mojo-platform-channel-handle=2464 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,4880462932541664264,5189237460012092762,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10685545826024556990 --mojo-platform-channel-handle=904 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,4880462932541664264,5189237460012092762,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16201961408071419965 --mojo-platform-channel-handle=2556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
584
Read events
520
Write events
60
Delete events
4
Modification events
| (PID) Process: | (1260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2116-13245942566676375 |
Value: 259 | |||
| (PID) Process: | (2116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (2116) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
25
Text files
249
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F747A27-844.pma | — | |
MD5:— | SHA256:— | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bf34a525-897b-468c-b146-fc87cc087aad.tmp | — | |
MD5:— | SHA256:— | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1aabd1.TMP | text | |
MD5:— | SHA256:— | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1aabd1.TMP | text | |
MD5:— | SHA256:— | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
66
DNS requests
47
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/img/site/facebook.png | JP | image | 465 b | unknown |
856 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/live/ | JP | html | 59.7 Kb | unknown |
856 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/parts/chikuwachan.css?20180217 | JP | text | 5.10 Kb | unknown |
856 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/img/site/amazon.png | JP | image | 3.09 Kb | unknown |
856 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/img/site/rakuten.png | JP | image | 676 b | unknown |
856 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/img/web/live_title_bg.png | JP | image | 12.8 Kb | unknown |
856 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/img/site/warota.png | JP | image | 702 b | unknown |
856 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/img/site/nico_www.png | JP | image | 124 b | unknown |
856 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/img/site/twitter.png | JP | image | 1.49 Kb | unknown |
856 | chrome.exe | GET | 200 | 172.217.16.138:80 | http://ajax.googleapis.com/ajax/libs/jquery/1.11.0/jquery.min.js | US | text | 32.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
856 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
856 | chrome.exe | 133.242.179.25:80 | www.chikuwachan.com | SAKURA Internet Inc. | JP | unknown |
856 | chrome.exe | 172.217.16.138:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
856 | chrome.exe | 172.217.22.34:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
856 | chrome.exe | 52.119.161.4:443 | www.assoc-amazon.jp | Amazon.com, Inc. | US | unknown |
856 | chrome.exe | 133.152.41.15:443 | secure-dcdn.cdn.nimg.jp | Equinix Asia Pacific | JP | suspicious |
856 | chrome.exe | 133.152.40.71:443 | ssth.dmc.nico | Equinix Asia Pacific | JP | unknown |
856 | chrome.exe | 153.254.173.147:80 | js.gsspcln.jp | NTT America, Inc. | JP | unknown |
856 | chrome.exe | 216.58.212.130:443 | adservice.google.com | Google Inc. | US | whitelisted |
856 | chrome.exe | 172.217.18.162:443 | adservice.google.lv | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.chikuwachan.com |
| unknown |
accounts.google.com |
| shared |
ajax.googleapis.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
www.assoc-amazon.jp |
| unknown |
secure-dcdn.cdn.nimg.jp |
| whitelisted |
ssth.dmc.nico |
| unknown |
bit.ly |
| shared |
ch.nicovideo.jp |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M1 |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M1 |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M1 |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M1 |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M1 |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M1 |