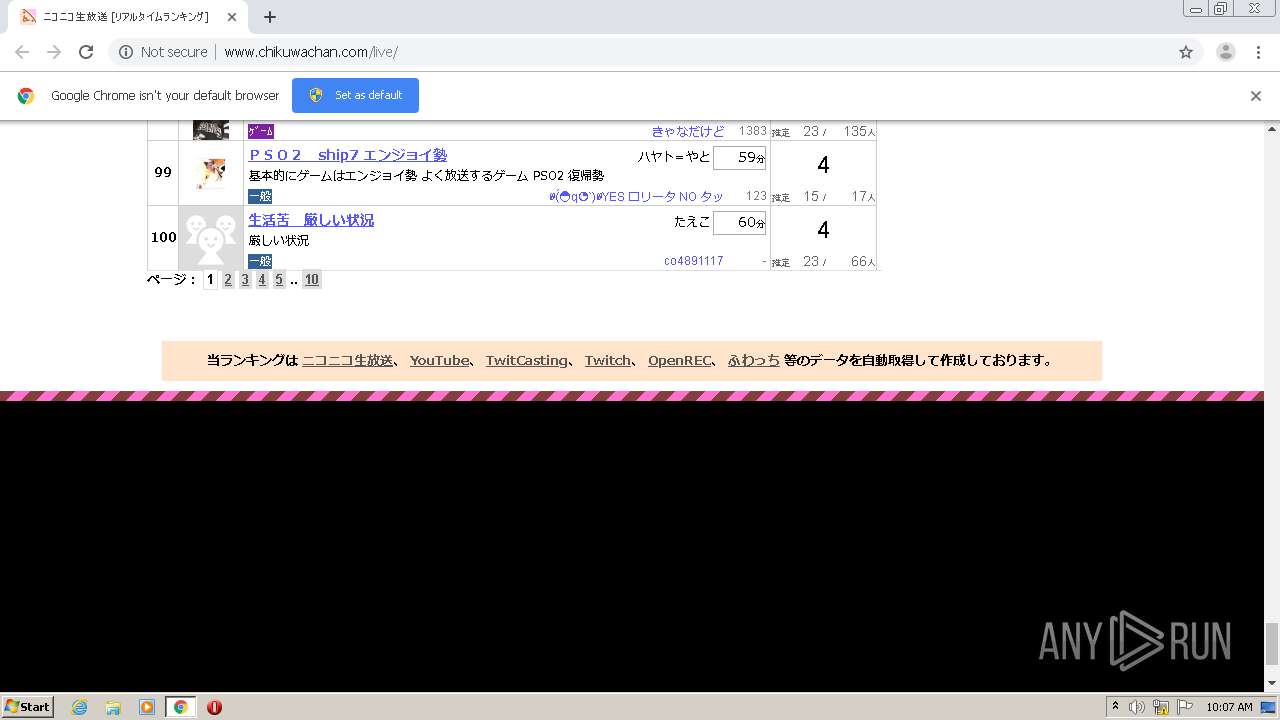
| URL: | http://www.chikuwachan.com/live |
| Full analysis: | https://app.any.run/tasks/1546bf64-4aad-42df-9a39-158104e110d4 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 09:06:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3F899D0ECB2A8B0E8475F9D500F257A0 |
| SHA1: | C591FDF6CABE552F5B64E2AAF68D38B1B6FDFC42 |
| SHA256: | 4E11D6F03015349EE15B233731F4D0C52824789DB652AA077EA79915576DDAFF |
| SSDEEP: | 3:N1KJS4f3abTKJMM:Cc4vabTKCM |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2572)
Reads the hosts file
- chrome.exe (PID: 2572)
- chrome.exe (PID: 1660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
14
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3874757413083592949,16259894619027875138,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9658256123179046198 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,3874757413083592949,16259894619027875138,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2192435305204345089 --mojo-platform-channel-handle=2124 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,3874757413083592949,16259894619027875138,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14612175719222348478 --mojo-platform-channel-handle=2588 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,3874757413083592949,16259894619027875138,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=550944965963903929 --mojo-platform-channel-handle=1620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,3874757413083592949,16259894619027875138,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3598957622966087808 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,3874757413083592949,16259894619027875138,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6298027399802247793 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3874757413083592949,16259894619027875138,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12604273970999234924 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2368 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.chikuwachan.com/live" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,3874757413083592949,16259894619027875138,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3181331653678317089 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
580
Read events
516
Write events
60
Delete events
4
Modification events
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2572-13245930406927500 |
Value: 259 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
23
Text files
274
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F744AA7-A0C.pma | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bd8baeeb-5bd7-481d-af8d-9980020e8aaf.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1aac4e.TMP | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1aac4e.TMP | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1aac7d.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
60
TCP/UDP connections
66
DNS requests
49
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1660 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/img/web/live_title_bg.png | JP | image | 12.8 Kb | unknown |
1660 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/img/site/nico_www.png | JP | image | 124 b | unknown |
1660 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/img/site/nico_live.png | JP | image | 177 b | unknown |
1660 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/img/site/youtube.png | JP | image | 527 b | unknown |
1660 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/live/ | JP | html | 54.1 Kb | unknown |
1660 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/parts/jquery_mods.js?20140429 | JP | text | 77.0 Kb | unknown |
1660 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/parts/page_live.css?20200812 | JP | text | 29.0 Kb | unknown |
1660 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/parts/page_live.js?20180620 | JP | text | 13.8 Kb | unknown |
1660 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/parts/chikuwachan.css?20180217 | JP | text | 5.10 Kb | unknown |
1660 | chrome.exe | GET | 200 | 133.242.179.25:80 | http://www.chikuwachan.com/img/site/facebook.png | JP | image | 465 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1660 | chrome.exe | 202.234.44.212:80 | imagegw03.twitcasting.tv | Yahoo Japan Corporation | JP | unknown |
1660 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1660 | chrome.exe | 133.242.179.25:80 | www.chikuwachan.com | SAKURA Internet Inc. | JP | unknown |
1660 | chrome.exe | 172.217.18.162:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
— | — | 216.58.212.170:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
1660 | chrome.exe | 133.152.41.15:443 | secure-dcdn.cdn.nimg.jp | Equinix Asia Pacific | JP | suspicious |
1660 | chrome.exe | 133.152.40.71:443 | ssth.dmc.nico | Equinix Asia Pacific | JP | unknown |
1660 | chrome.exe | 52.119.161.4:443 | www.assoc-amazon.jp | Amazon.com, Inc. | US | unknown |
1660 | chrome.exe | 202.47.25.76:80 | js.gsspcln.jp | NTT America, Inc. | JP | unknown |
1660 | chrome.exe | 172.217.22.98:443 | adservice.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.chikuwachan.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ajax.googleapis.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
www.assoc-amazon.jp |
| unknown |
secure-dcdn.cdn.nimg.jp |
| whitelisted |
ssth.dmc.nico |
| unknown |
js.gsspcln.jp |
| suspicious |
bit.ly |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M1 |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M1 |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M1 |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M1 |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M1 |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M1 |