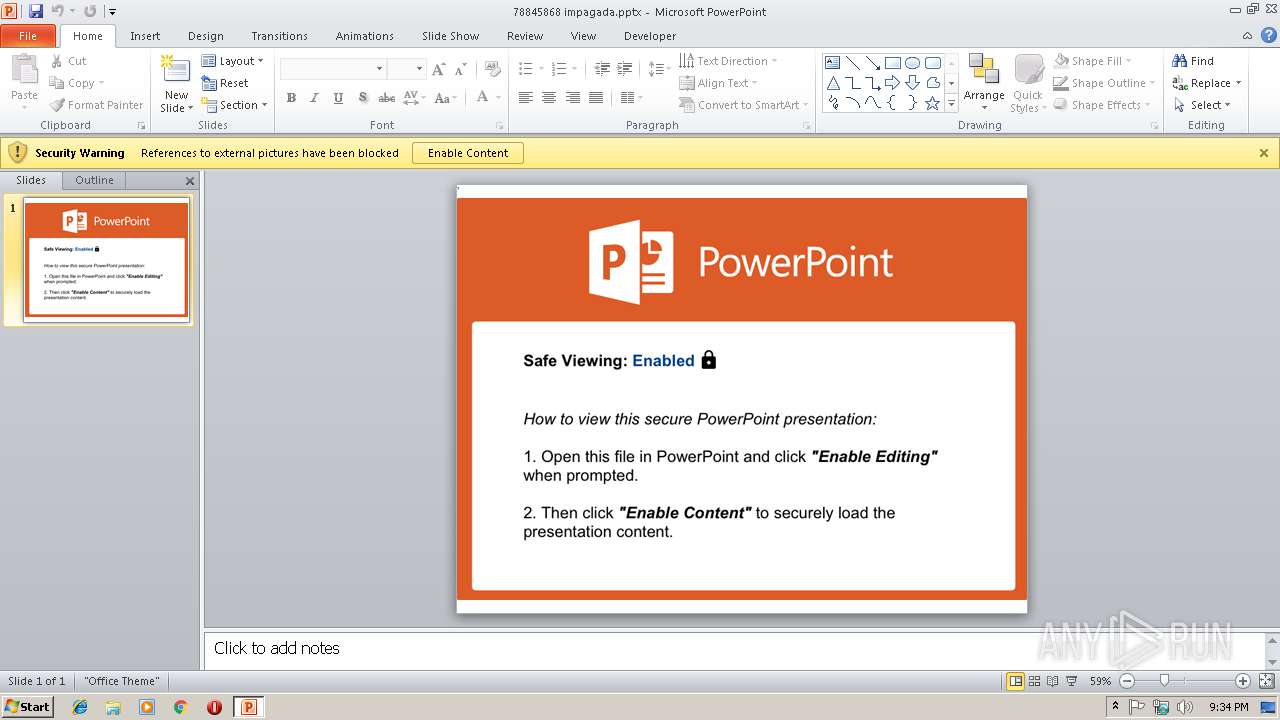
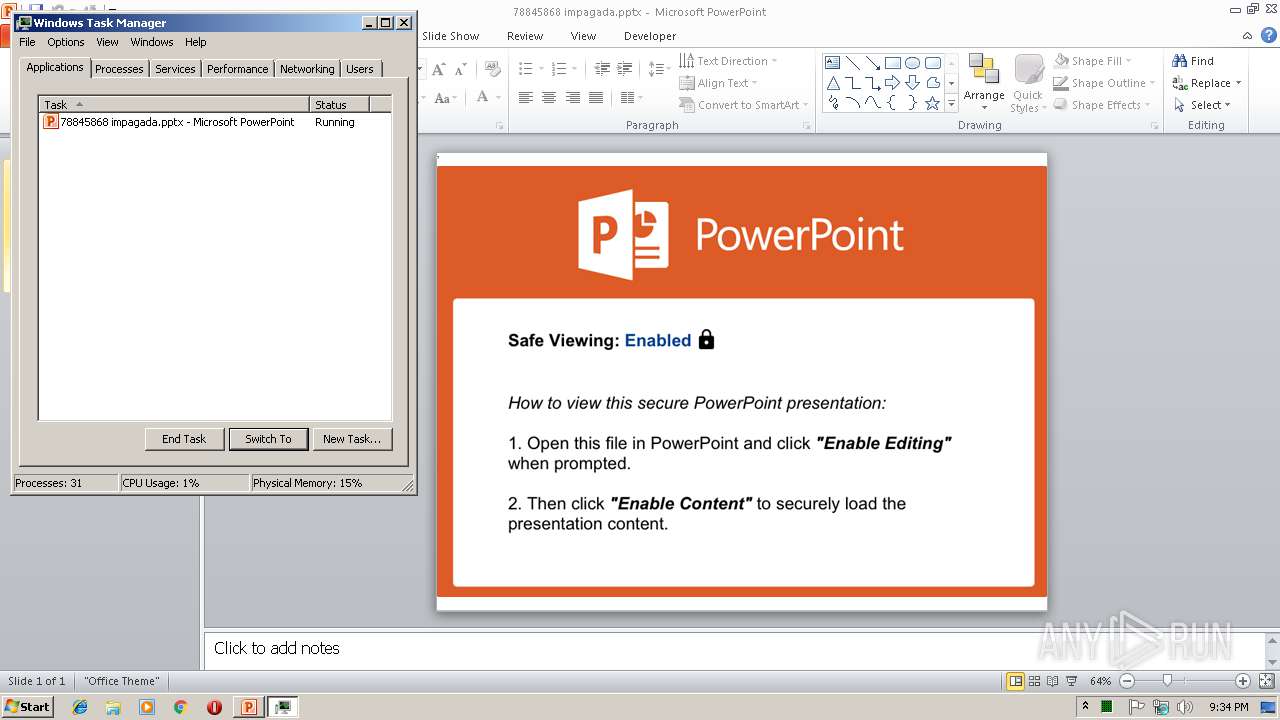
| File name: | 78845868 impagada.pptx |
| Full analysis: | https://app.any.run/tasks/51344cf7-40ef-47ba-9e04-06d8a6ed90d2 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 21:33:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | EED4A2A5A39B66BD4A30F8EDFA2B5114 |
| SHA1: | 3864A64E24782326DEB6F77F459C38CC1328FB3C |
| SHA256: | 4E10FF76FFD4890956B16FCAC44C0DA79499EF87A0C21961FC1DCC4C9AA4FB91 |
| SSDEEP: | 3072:uEbWXxjHYm5sk2P2ei1EeEji8nGJgvhf58mEFhPgM4Vl:aBjZ79z1Eg8RvNCvNgrl |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- POWERPNT.EXE (PID: 2972)
Unusual connect from Microsoft Office
- POWERPNT.EXE (PID: 2972)
INFO
Reads Microsoft Office registry keys
- POWERPNT.EXE (PID: 2972)
Creates files in the user directory
- POWERPNT.EXE (PID: 2972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | Open Packaging Conventions container (81.3) |
|---|---|---|
| .zip | | | ZIP compressed archive (18.6) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:10:29 18:01:09 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | docProps/ |
XML
| TotalEditTime: | 33 minutes |
|---|---|
| Words: | 7 |
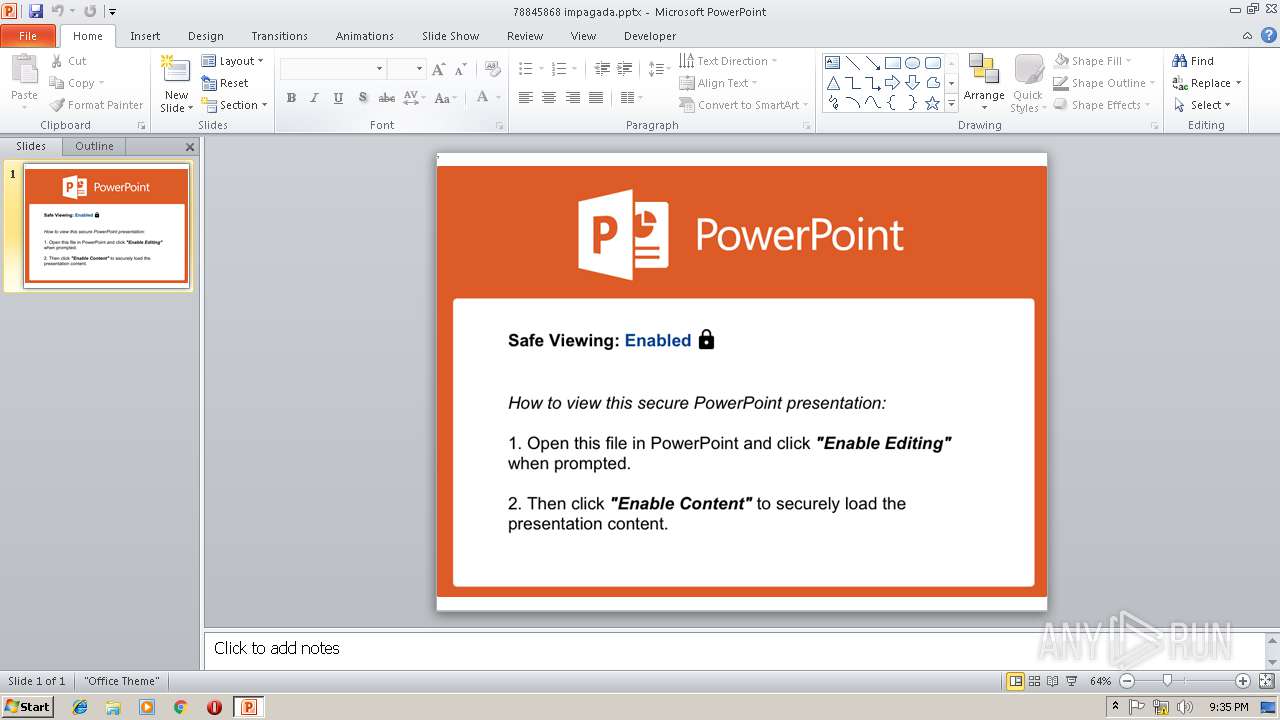
| Application: | Microsoft Macintosh PowerPoint |
| PresentationFormat: | On-screen Show (4:3) |
| Paragraphs: | 1 |
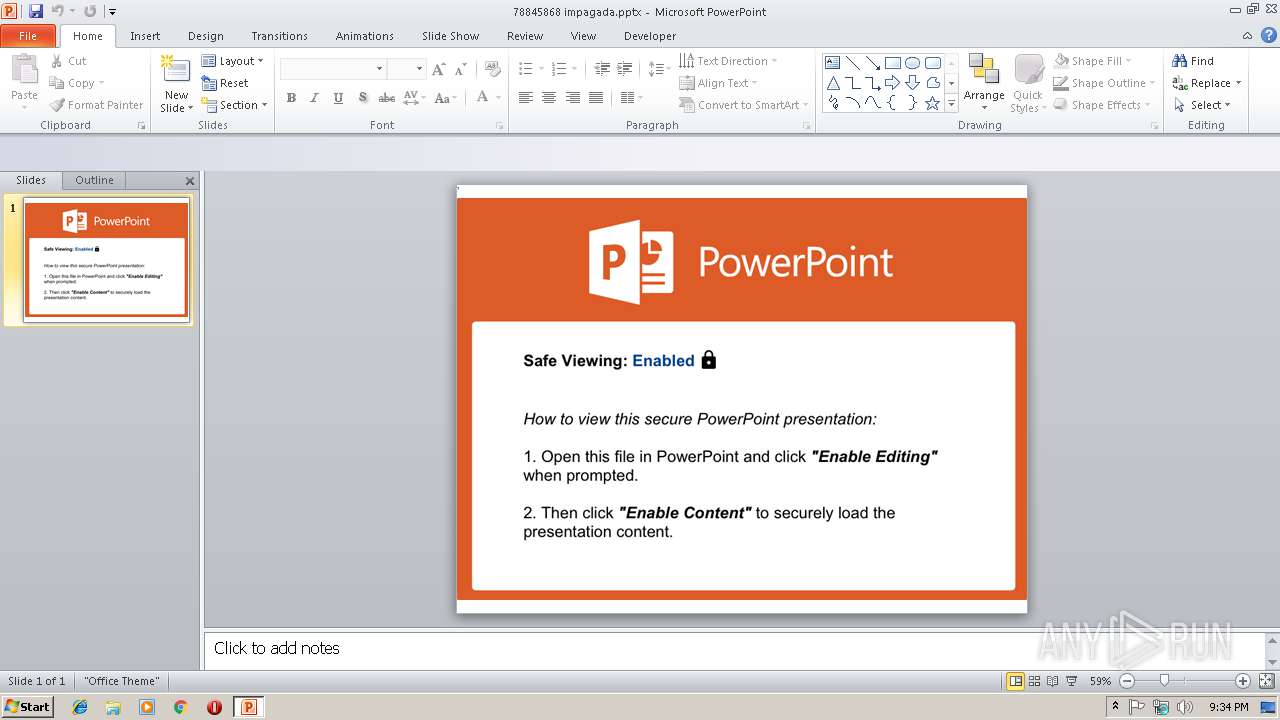
| Slides: | 1 |
| Notes: | - |
| HiddenSlides: | - |
| MMClips: | - |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16.0014 |
| LastModifiedBy: | KB4 |
| RevisionNumber: | 7 |
| CreateDate: | 2014:07:08 19:45:52Z |
| ModifyDate: | 2018:06:21 08:42:27Z |
XMP
| Title: | YOU MUST OPEN THIS FILE IN POWERPOINT AND ENABLE EDITING TO VIEW THIS PRESENTATION |
|---|---|
| Creator: | KnowBe4 |
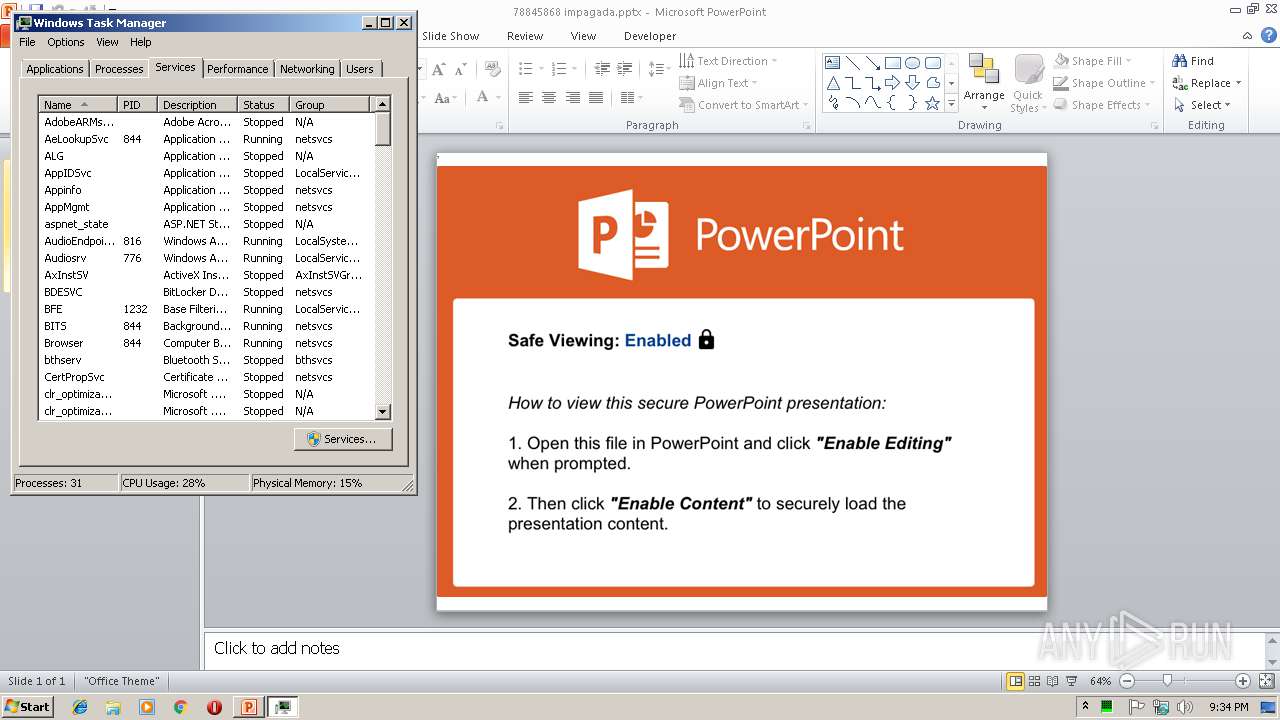
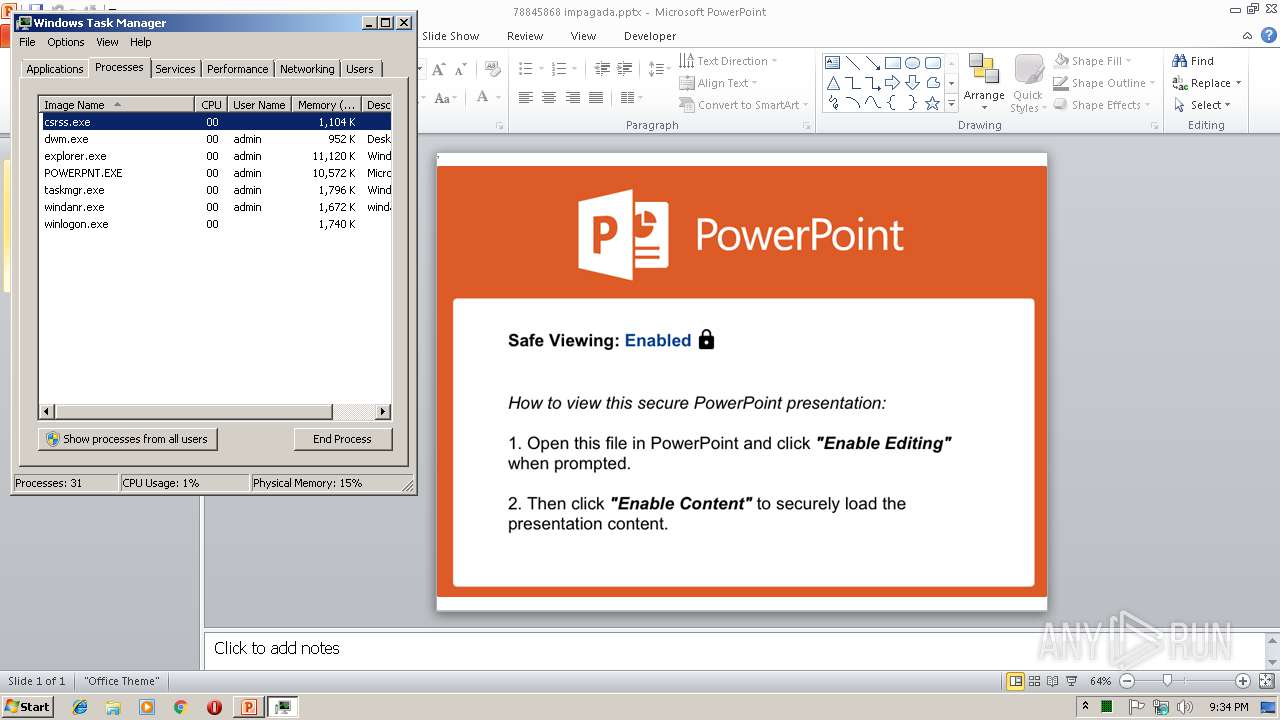
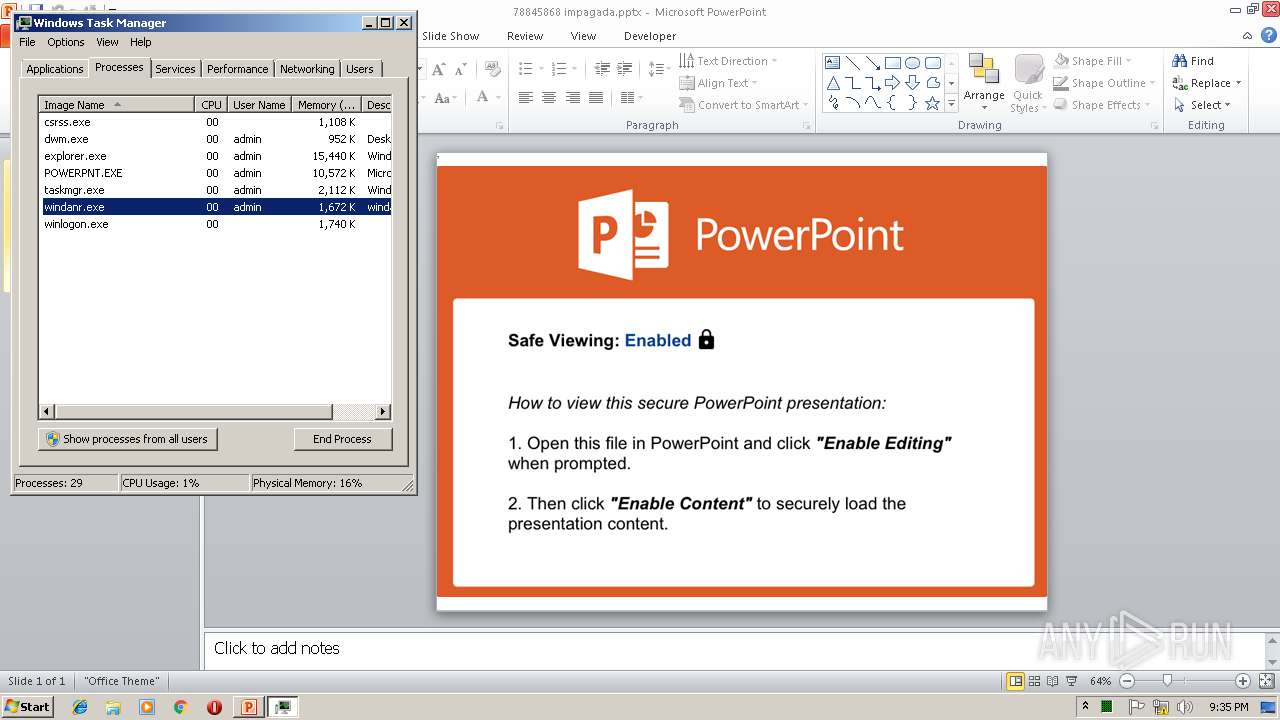
Total processes
33
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2972 | "C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE" "C:\Users\admin\AppData\Local\Temp\78845868 impagada.pptx" | C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft PowerPoint Exit code: 0 Version: 14.0.6009.1000 Modules
| |||||||||||||||
| 3824 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
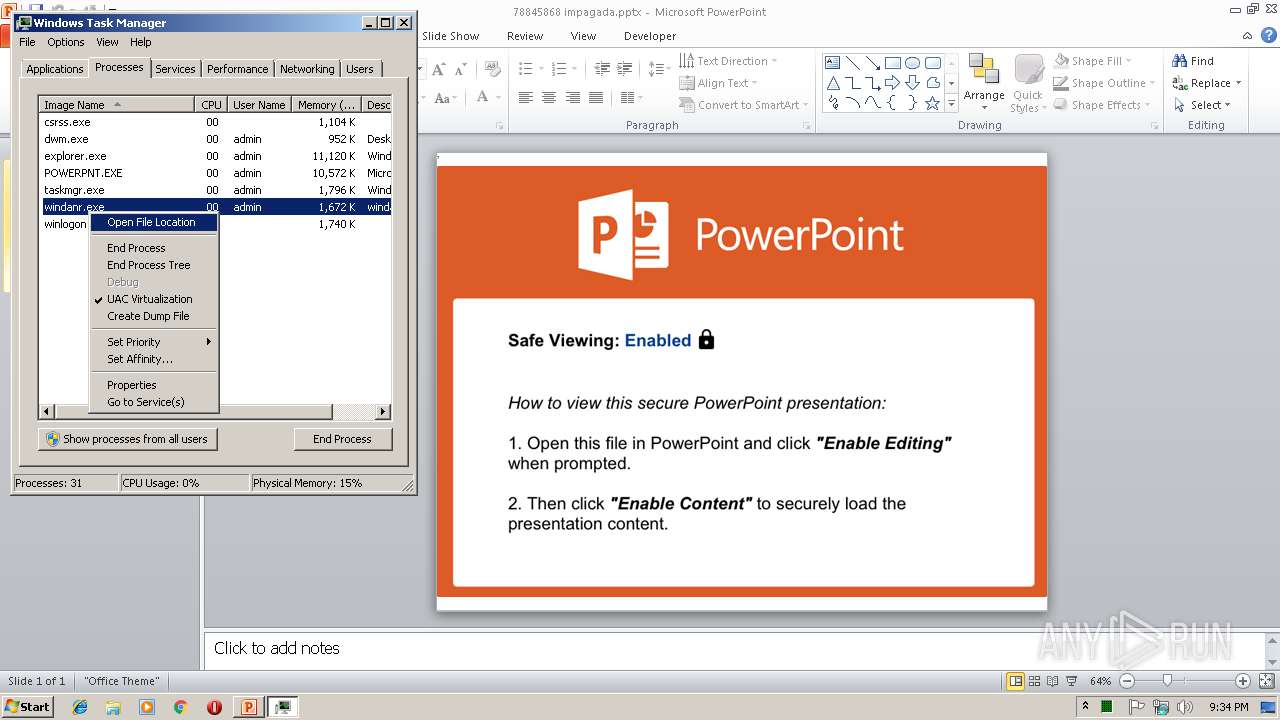
Total events
668
Read events
639
Write events
26
Delete events
3
Modification events
| (PID) Process: | (2972) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\StartupItems |
| Operation: | write | Name: | "7% |
Value: 223725009C0B0000010000000000000000000000 | |||
| (PID) Process: | (2972) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2972) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2972) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint |
| Operation: | write | Name: | MTTT |
Value: 9C0B00002AB1B3349AB2D40100000000 | |||
| (PID) Process: | (2972) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\StartupItems |
| Operation: | write | Name: | x9% |
Value: 783925009C0B000006000000010000008200000002000000720000000400000063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C006C006F00630061006C005C00740065006D0070005C0037003800380034003500380036003800200069006D007000610067006100640061002E007000700074007800000000000000 | |||
| (PID) Process: | (2972) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2972) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2972) POWERPNT.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | PPTFiles |
Value: 1312161805 | |||
| (PID) Process: | (2972) POWERPNT.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1312161936 | |||
| (PID) Process: | (2972) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Place MRU |
| Operation: | write | Name: | Max Display |
Value: 25 | |||
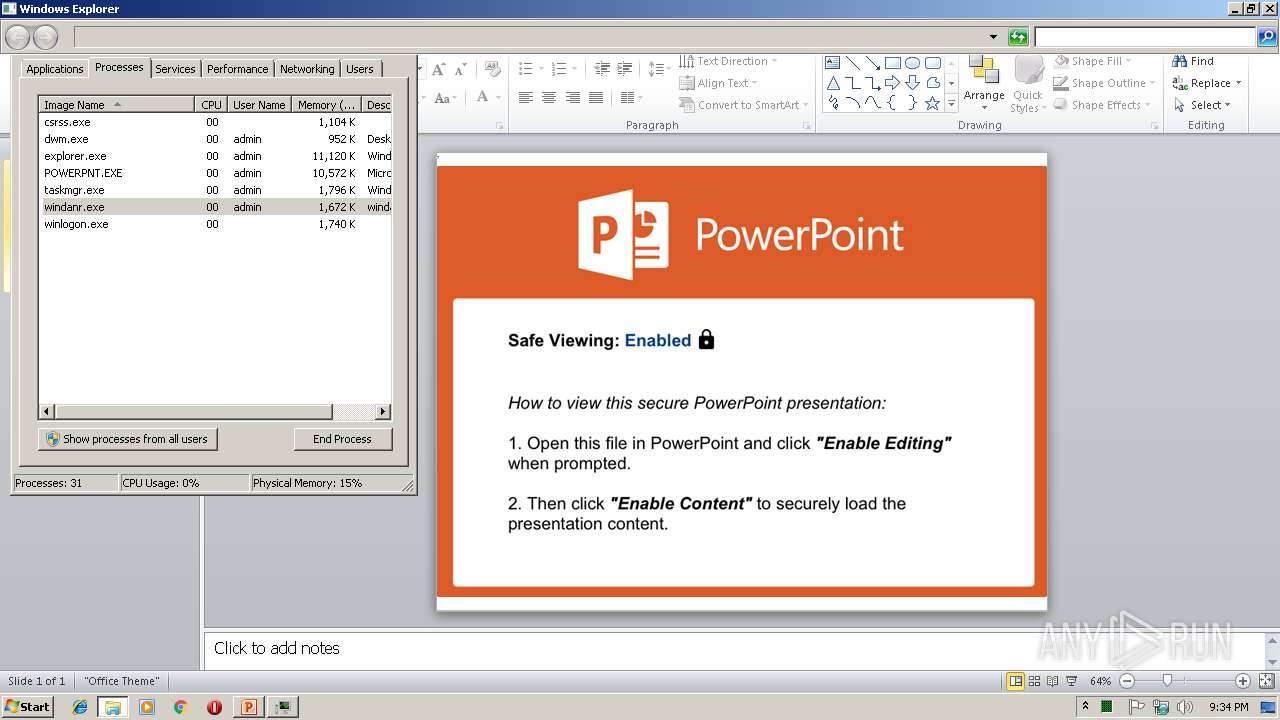
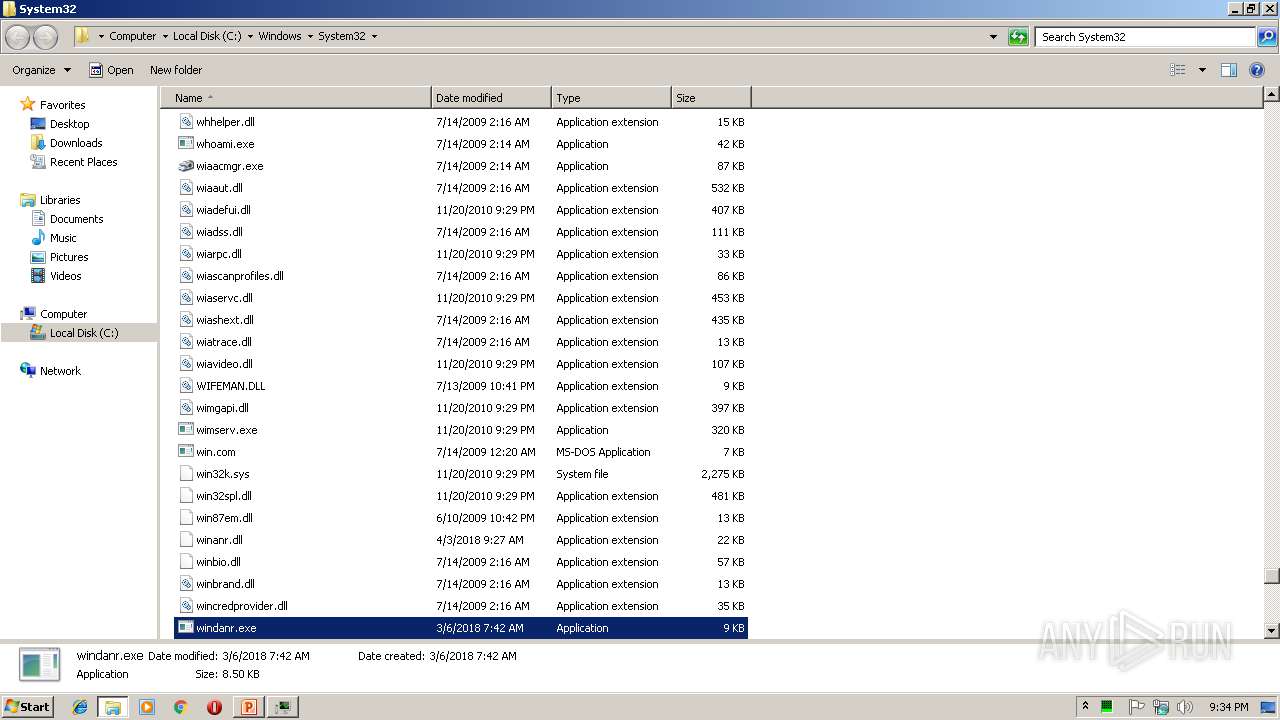
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\CVR97E1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2972 | POWERPNT.EXE | GET | 200 | 52.5.60.200:80 | http://en-us.secureconnection.moneytransaction.kb4.io/XcmVMjaXBpZWb50X2lkPTkQxNjYxqDODUztNyZjYW1wBYWplnbl9ydW5faWQ9MTc0VMDE5MSZhY3Rpb249YXR0YWNobWVudA== | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2972 | POWERPNT.EXE | 52.5.60.200:80 | en-us.secureconnection.moneytransaction.kb4.io | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
en-us.secureconnection.moneytransaction.kb4.io |
| suspicious |
Threats
1 ETPRO signatures available at the full report